
Phishing Analysis
Detailed analysis of captured phishing page
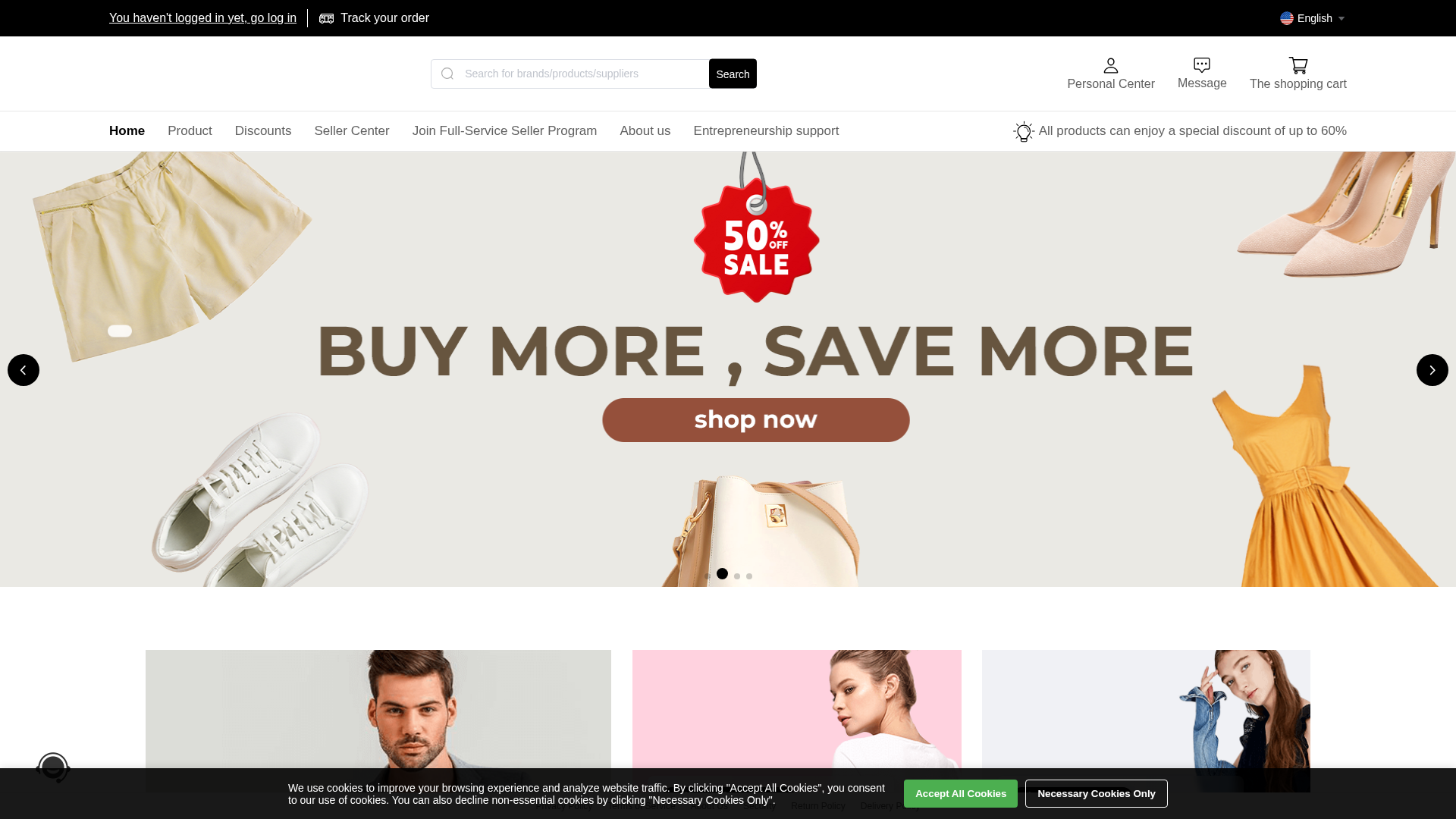
Visual Capture
No screenshot available
Detection Info
https://www.efmhyj.com/
Detected Brand
Unknown
Country
International
Confidence
100%
HTTP Status
200
Report ID
ad6712e6-665…
Analyzed
2026-01-22 08:24
Final URL (after redirects)
https://www.efmhyj.com/#/index
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16CE3FC70D695613B063389E4A4722F4FB2D7F31ECA97890067FC43D96FEBC95AA04486 |
|
CONTENT
ssdeep
|
1536:nqV0A8p9xRcHS9jP9rQVW3UT6CLyMrGc9sPtM4ublAjR7ICBirwvZhfG6pa7AjVJ:nKiQ47ICBirwvZhfG6pa7AK2 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f6a51add62a80376 |
|
VISUAL
aHash
|
00ff77c3e6feff00 |
|
VISUAL
dHash
|
c56cec8f4c48352d |
|
VISUAL
wHash
|
00ff6641e6fed700 |
|
VISUAL
colorHash
|
06e00008000 |
|
VISUAL
cropResistant
|
4d6cec8f4c482535,0000009393820080,010c686969697434,3535253d3db9edec |
Code Analysis
Risk Score
100/100
Threat Level
MEDIO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Generic e-commerce phishing site
• Target: Unknown brand customers
• Method: Fake e-commerce site promoting a 50% sale
• Exfil: No clear exfiltration method detected
• Indicators: Generic template, no branding, urgency tactic
• Risk: MEDIUM - Potential for data theft if forms were present
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- /api/category!sellerTree.action
- /api/credit!apply.action
- /api/credit!check.action
- /api/credit!bill.action
- api/newOnlinechat!unread.action
- /api/credit!beforepay.action
- /api/activity/lottery!getCurrentActivity.action
- GET
- /api/credit!beforereapply.action
- /api/localuser!get.action
- /api/credit!histroy.action
- /api/credit!config.action
- /api/localuser!registerWithVerifcode.action
- post
- /api/localuser!registerNoVerifcode.action
- /public/userOnlineChatController!unread.action
- /api/credit!pay.action
- /api/jscode!execute.action
- api/syspara!getSyspara.action
- /api/category!tree.action
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/620a493ab40c.png
Apr 03, 2026
Unknown
https://cdn.gosafemode.com/screenshots/0dd104c2bbe7.png
Mar 29, 2026
Unknown
https://api.huiyi321.com/start/
Mar 08, 2026
Unknown
https://tiktok.1d2by.com/start/
Jan 29, 2026
No screenshot
TikTok Shop
https://www.efmhyj.com/start/
Jan 25, 2026
Scan History for www.efmhyj.com
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.