Phishing Analysis
Detailed analysis of captured phishing page
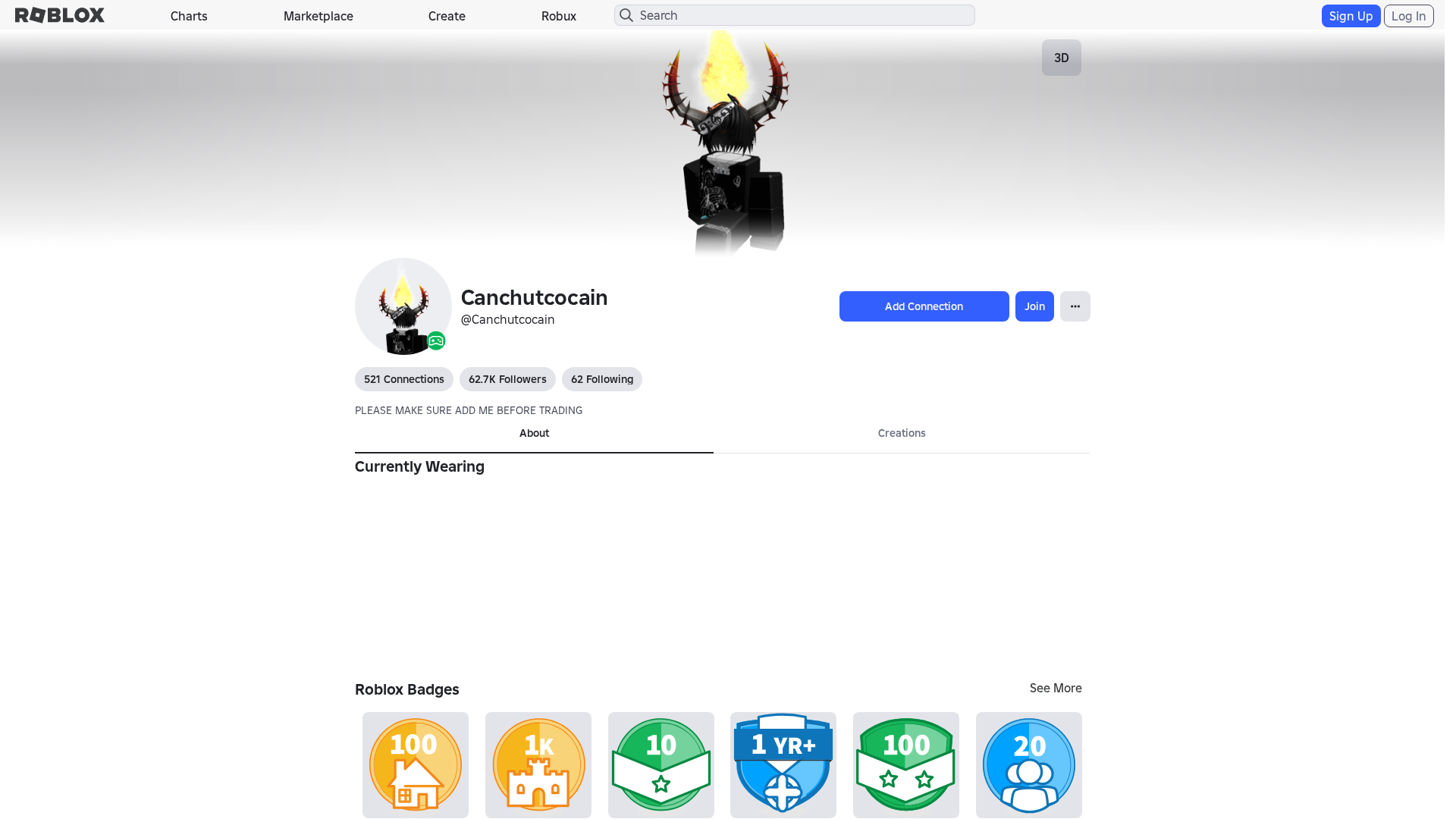
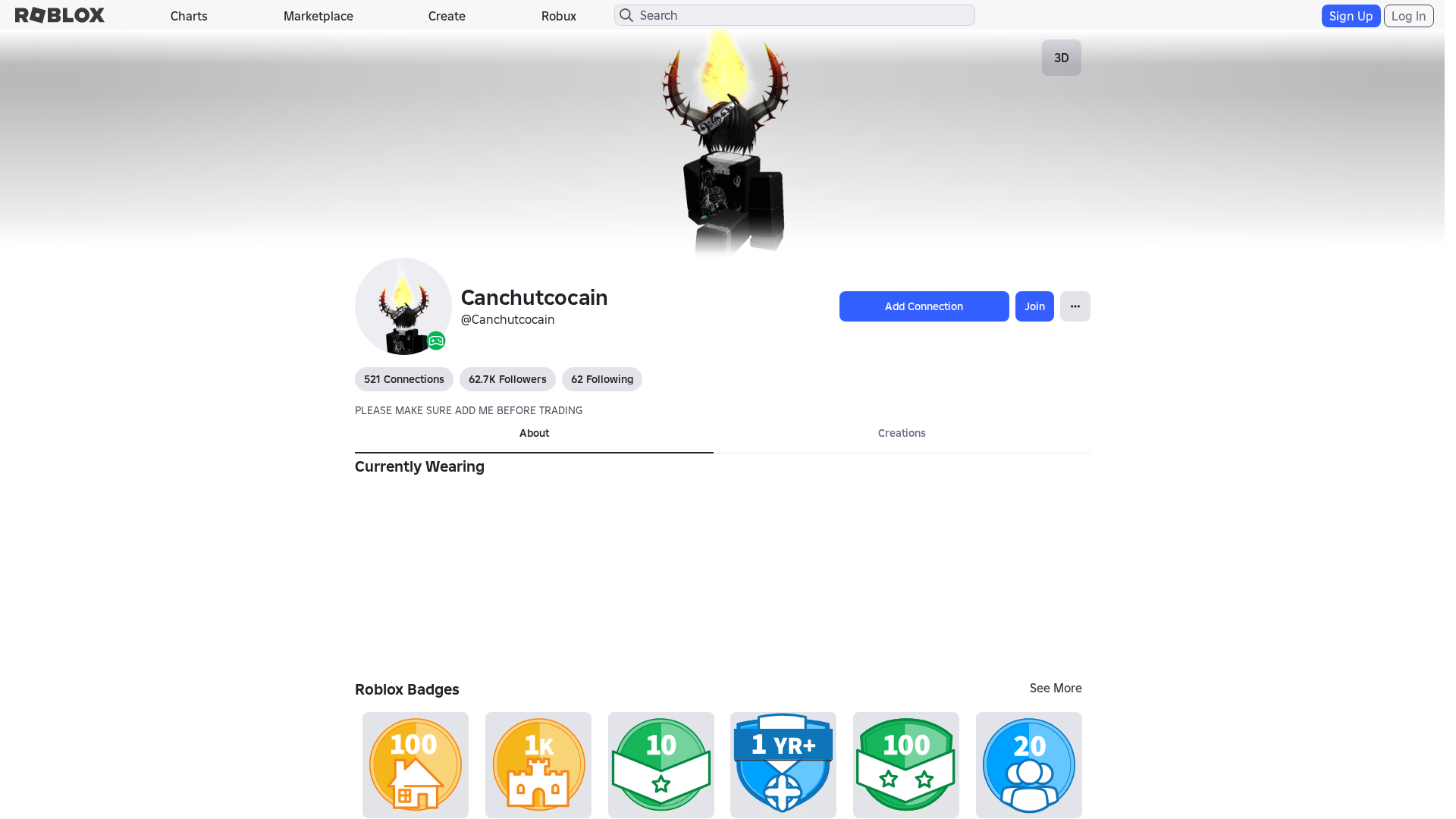
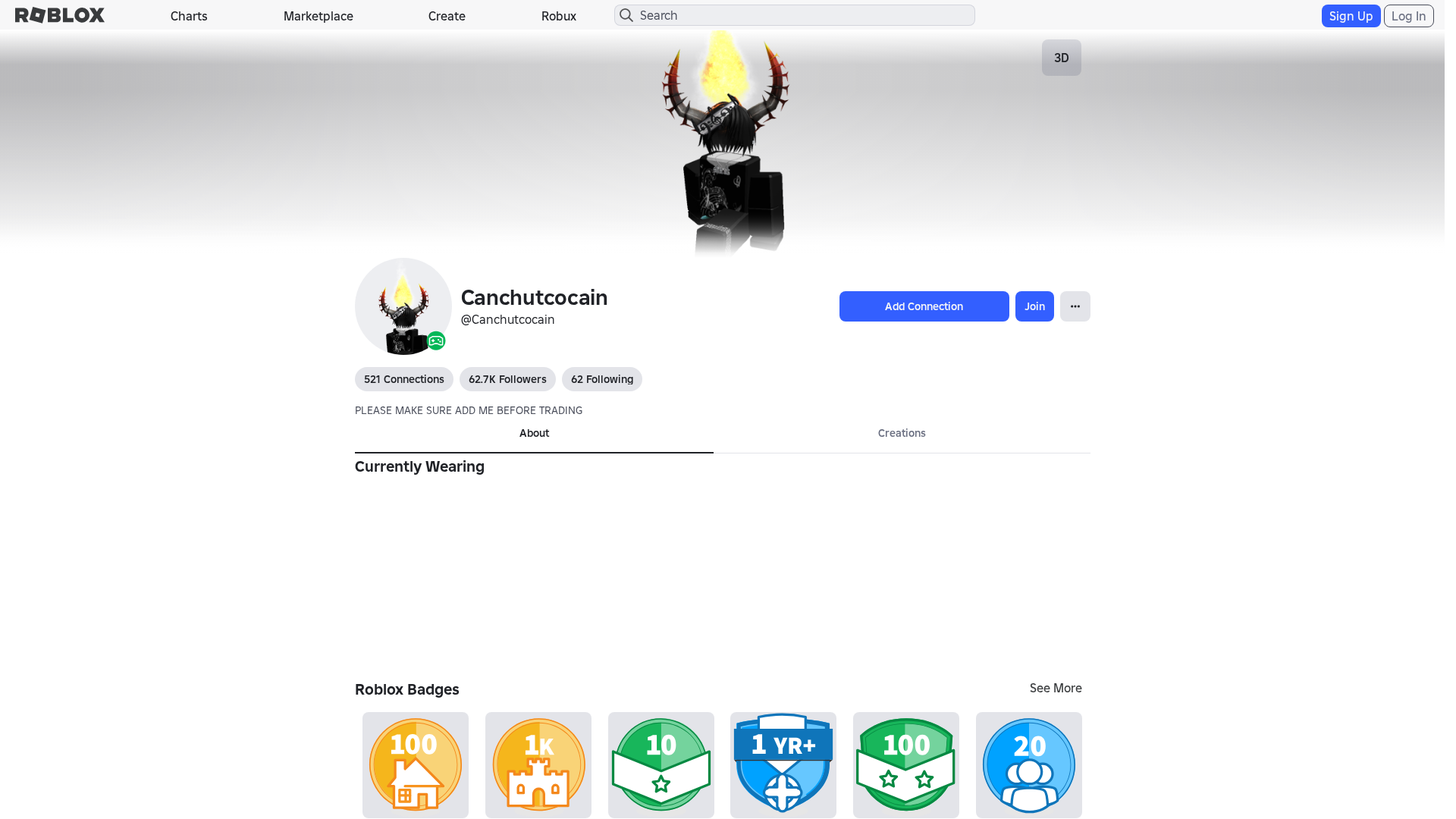
Visual Capture
Detection Info
https://www-robiox.co/users/1513784932/profile
Detected Brand
Roblox
Country
International
Confidence
100%
HTTP Status
200
Report ID
ad89f677-88c…
Analyzed
2026-01-18 12:12
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14B93B8B29251243320BFB1D9F1297709A2D3D74EC68287D1E2FC636B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:qQqXWnSraG7uOmIor1BPmzzXXMd6MiucCOK:tqXWdG7uOCvmzzXXMd6M1cCOK |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a412679b389cedb2 |
|
VISUAL
aHash
|
0000e3dbffffffc3 |
|
VISUAL
dHash
|
e8e8ae3638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
07200008280 |
|
VISUAL
cropResistant
|
e8e8ae3638002606 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: Roblox users
• Method: Fake login form stealing email and password
• Exfil: Data sent to unknown server
• Indicators: Domain mismatch, obfuscated JavaScript, recent domain
• Risk: HIGH - Immediate credential theft
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- /login?returnUrl=
- /catalog
- https://www.roblox.com/info/blog?locale=en_us
- /login?returlUrl=1513784932
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- https://help.roblox.com/hc/articles/30428367965460
- POST
- get
- GET
- https://apis.
📤 Form Action Targets
- /search
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www-robiox.co
Found 7 other scans for this domain
-
https://www-robiox.co/users/2106893633/profile
https://www-robiox.co/users/1323157586/profile
http://www.www-robiox.co/users/1882339096/profile/
https://wwww-robiox.com/users/9511334/profile
https://wwww-robiox.com/users/291474384/profile
https://wwww-robiox.com/users/108009807/profile
https://wwww-robiox.com/users/1010449667/profile

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.