
Phishing Analysis
Detailed analysis of captured phishing page
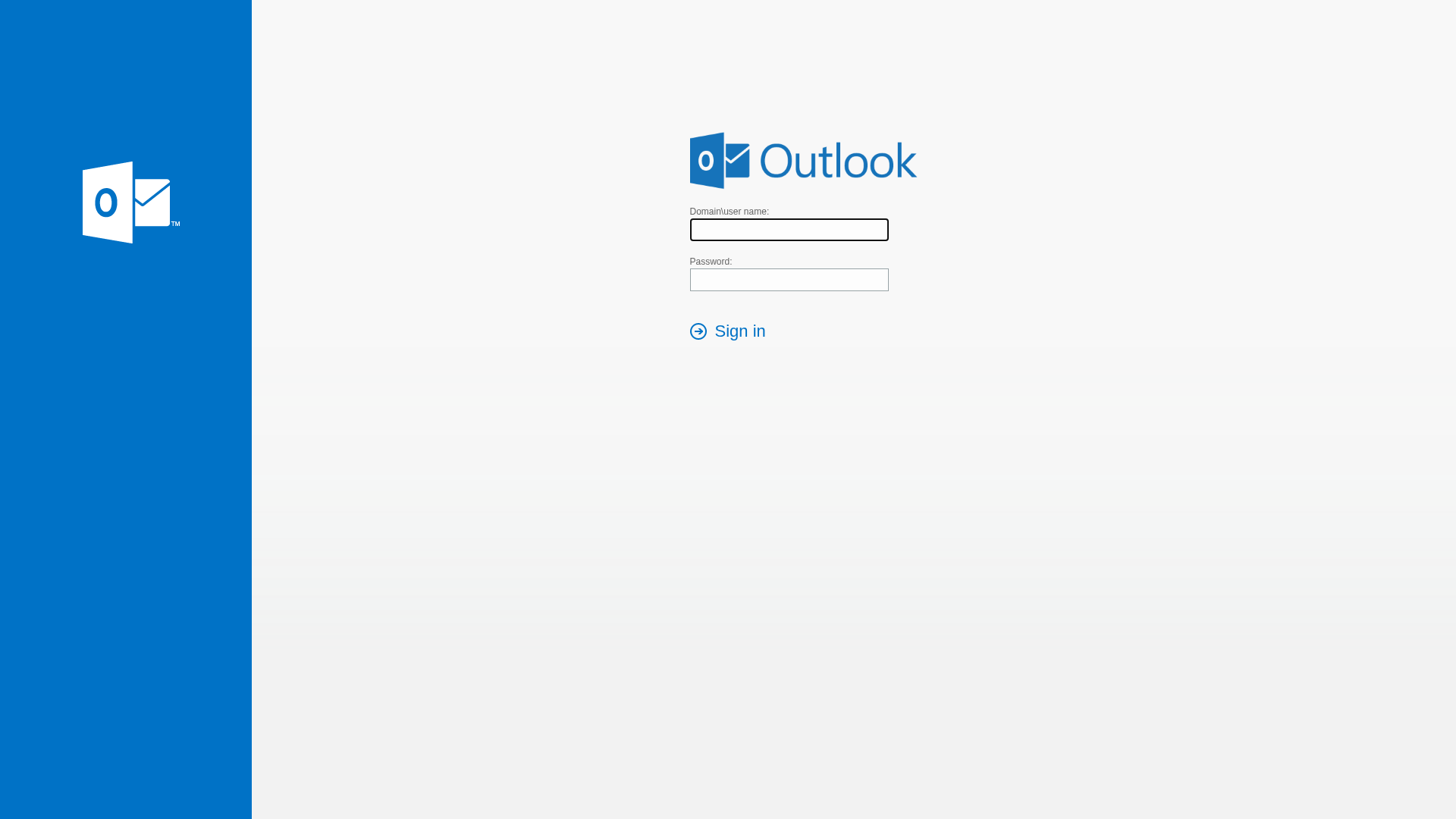
Visual Capture
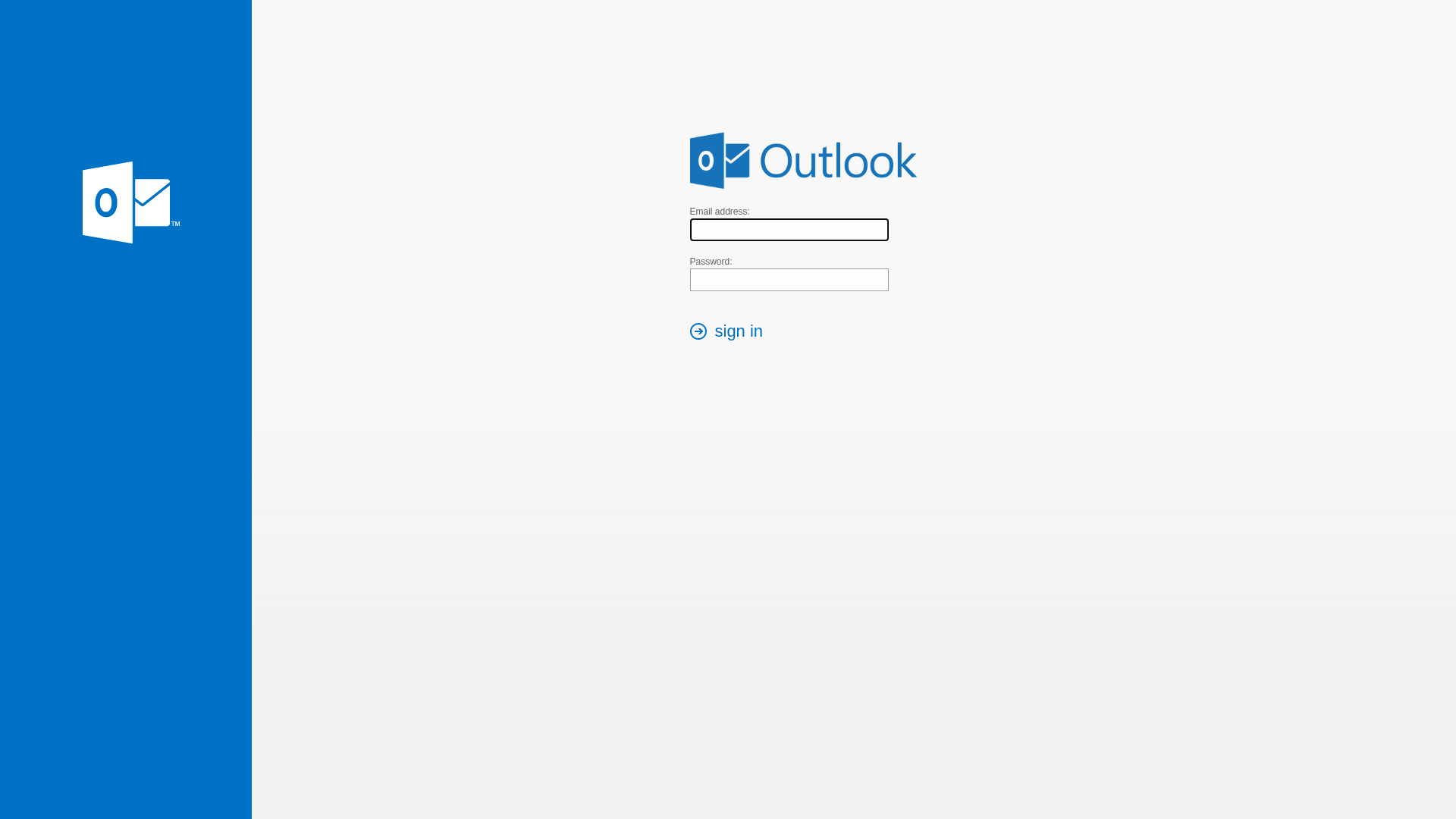
Detection Info
http://www.5mp.eu/fajlok2/email/index_www.5mp.eu_.html
Detected Brand
Outlook
Country
International
Confidence
100%
HTTP Status
200
Report ID
ad96f2a9-5a5…
Analyzed
2026-03-18 08:58
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T10951EDA09059AC739113E1F86AE4AB9B3287C305C687254C63F4C36C2EE3C5DDF66669 |
|
CONTENT
ssdeep
|
48:LUk1UJhhzazqf9TTOiyXHxnja26YXAPy9uilLM7ay6BLPHwut16:LdO8zqN+HxnebBy9ui9MeBFPwu6 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
83f67709890999fc |
|
VISUAL
aHash
|
3f3f3f3f3f3f3f3f |
|
VISUAL
dHash
|
d0ccccdad0d0d0d0 |
|
VISUAL
wHash
|
3f27373f3f300000 |
|
VISUAL
colorHash
|
060000001c0 |
|
VISUAL
cropResistant
|
a09c989080808080,f184acb6b6ac84f3,0e71710e20000000 |
Code Analysis
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Outlook users
• Method: Impersonation
• Exfil: https://submit-form.com/Qt1PwOP7v
• Indicators: Unrelated domain, form submission to different site.
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- document.write
📤 Form Action Targets
- https://submit-form.com/Qt1PwOP7v
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain Unrelated to Brand
The domain www.5mp.eu does not belong to Microsoft or Outlook.
Form submission to a different domain
Form data is sent to https://submit-form.com/Qt1PwOP7v, a suspicious domain.
JavaScript Obfuscation
Javascript is obfuscated, indicating an attempt to hide malicious behavior
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
Outlook users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
- 4 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Outlook
Official Website
https://outlook.com
Fake Service
Outlook Login
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site uses a form to collect the user's email and password, which are then likely sent to the attacker. The user's credentials can then be used to access the user's actual Outlook account.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.5mp.eu
Registered
Unknown
Registrar
Unknown
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
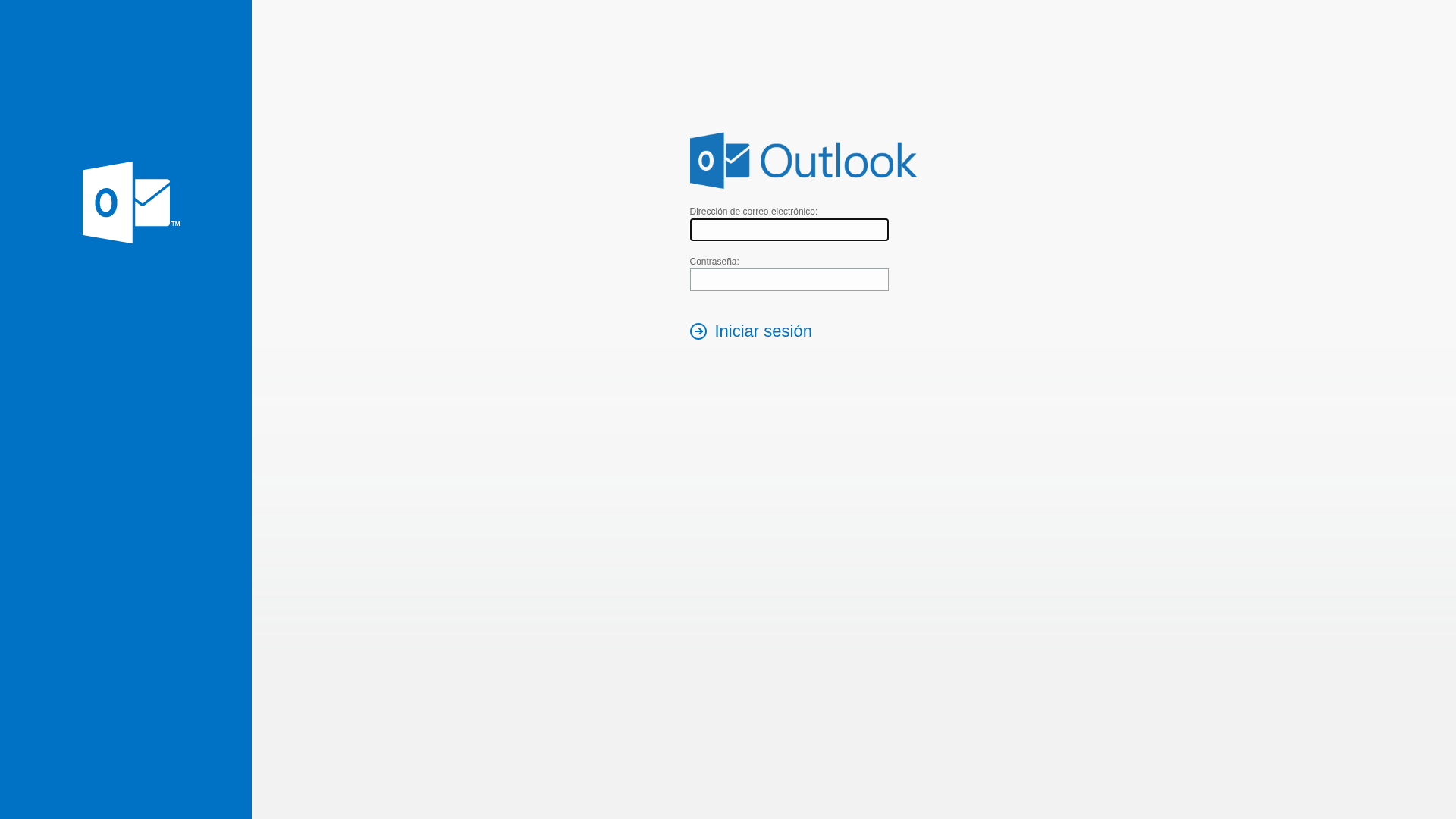
Microsoft Outlook
https://www.5mp.eu/fajlok2/educaciones/index_www.5mp.eu_.htm...
Apr 03, 2026
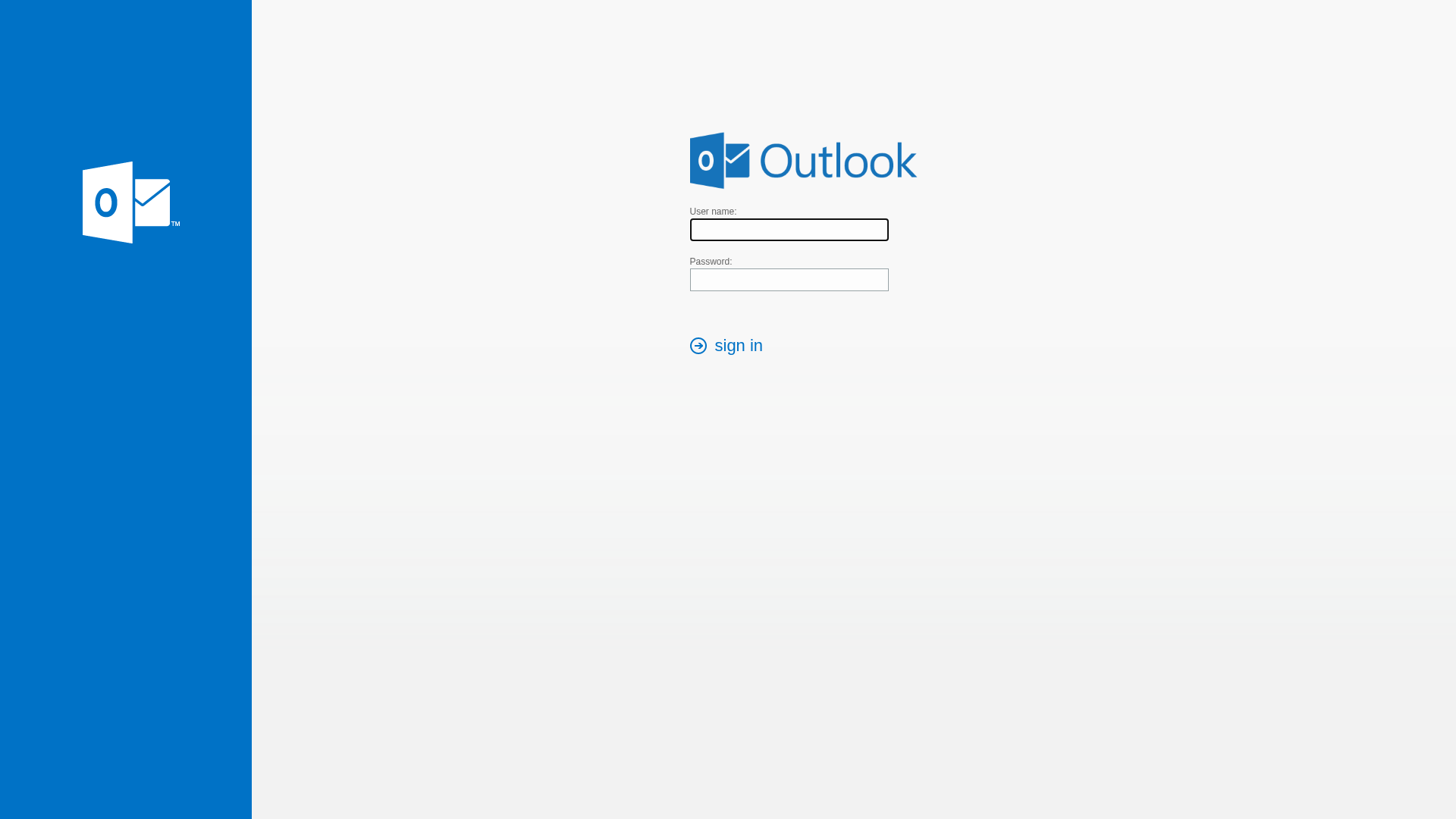
Microsoft Outlook
https://uhphov.softwareupdates.cc/?rid=1O3D6Sz
Mar 23, 2026
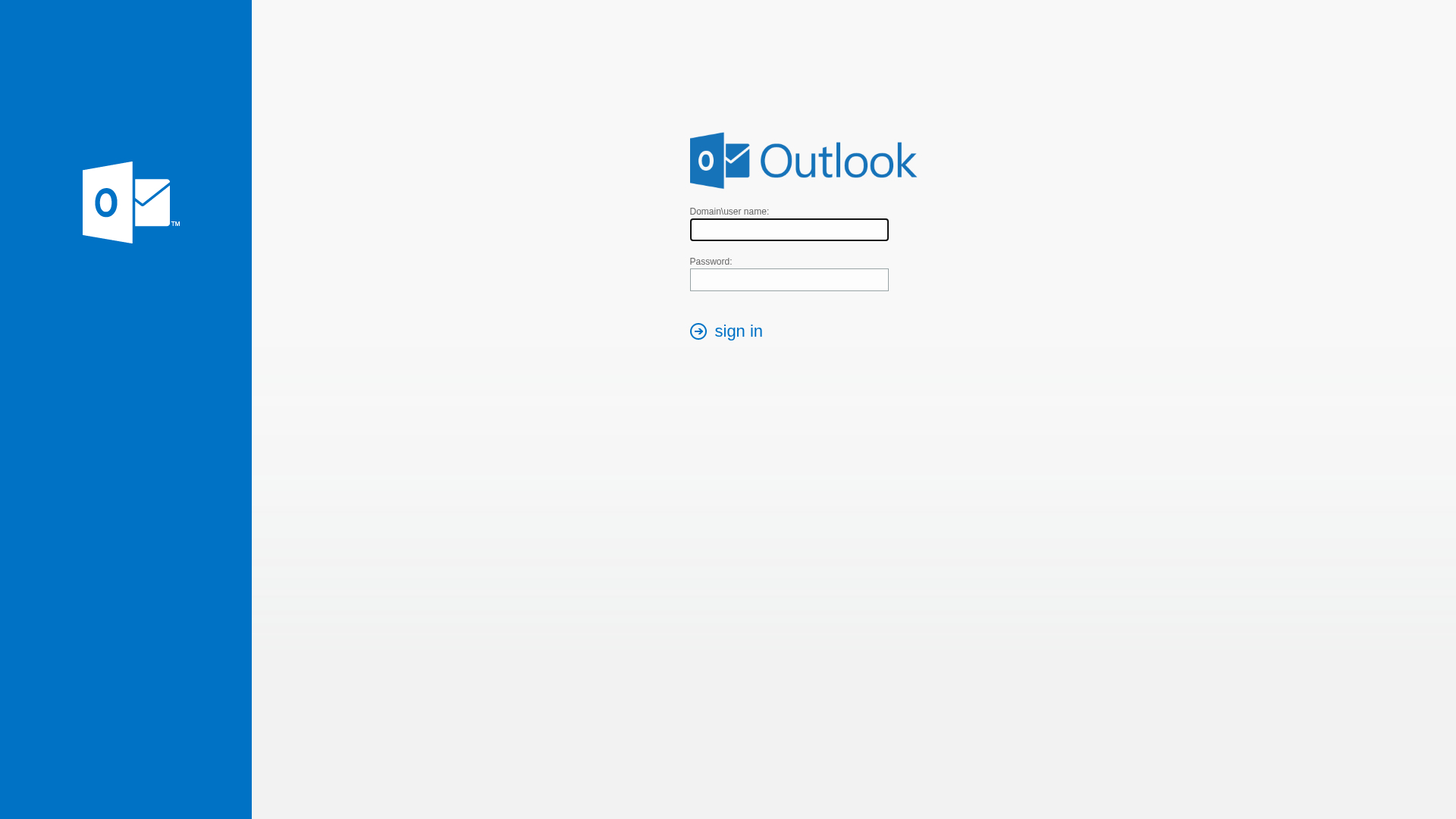
Microsoft Outlook
https://caseagora.com.br/tu-bs.html
Mar 23, 2026
Microsoft Outlook
https://www.5mp.eu/fajlok2/grupovisabeira/index_www.5mp.eu_....
Mar 20, 2026
Outlook
http://www.5mp.eu/fajlok2/igacpt/index_www.5mp.eu_.html
Mar 18, 2026
Scan History for www.5mp.eu
Found 10 other scans for this domain
-
https://www.5mp.eu/fajlok2/thrse/owa_www.5mp.eu_.h...
http://www.5mp.eu/fajlok2/css4/owa_www.5mp.eu_.htm...
https://www.5mp.eu/fajlok2/atr54/de_www.5mp.eu_.ht...
https://www.5mp.eu/fajlok2/hcdiputadosgovar/index_...
https://www.5mp.eu/fajlok2/grupovisabeira/index_ww...
http://www.5mp.eu/fajlok2/thrse/owa_www.5mp.eu_.ht...
https://www.5mp.eu/fajlok2/teamowa/owa_(1)_www.5mp...
https://www.5mp.eu/fajlok2/css4/owa_www.5mp.eu_.ht...
http://www.5mp.eu/fajlok2/teamowa/owa_(1)_www.5mp....
http://www.5mp.eu/fajlok2/catalan/index_www.5mp.eu...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.