Phishing Analysis
Detailed analysis of captured phishing page
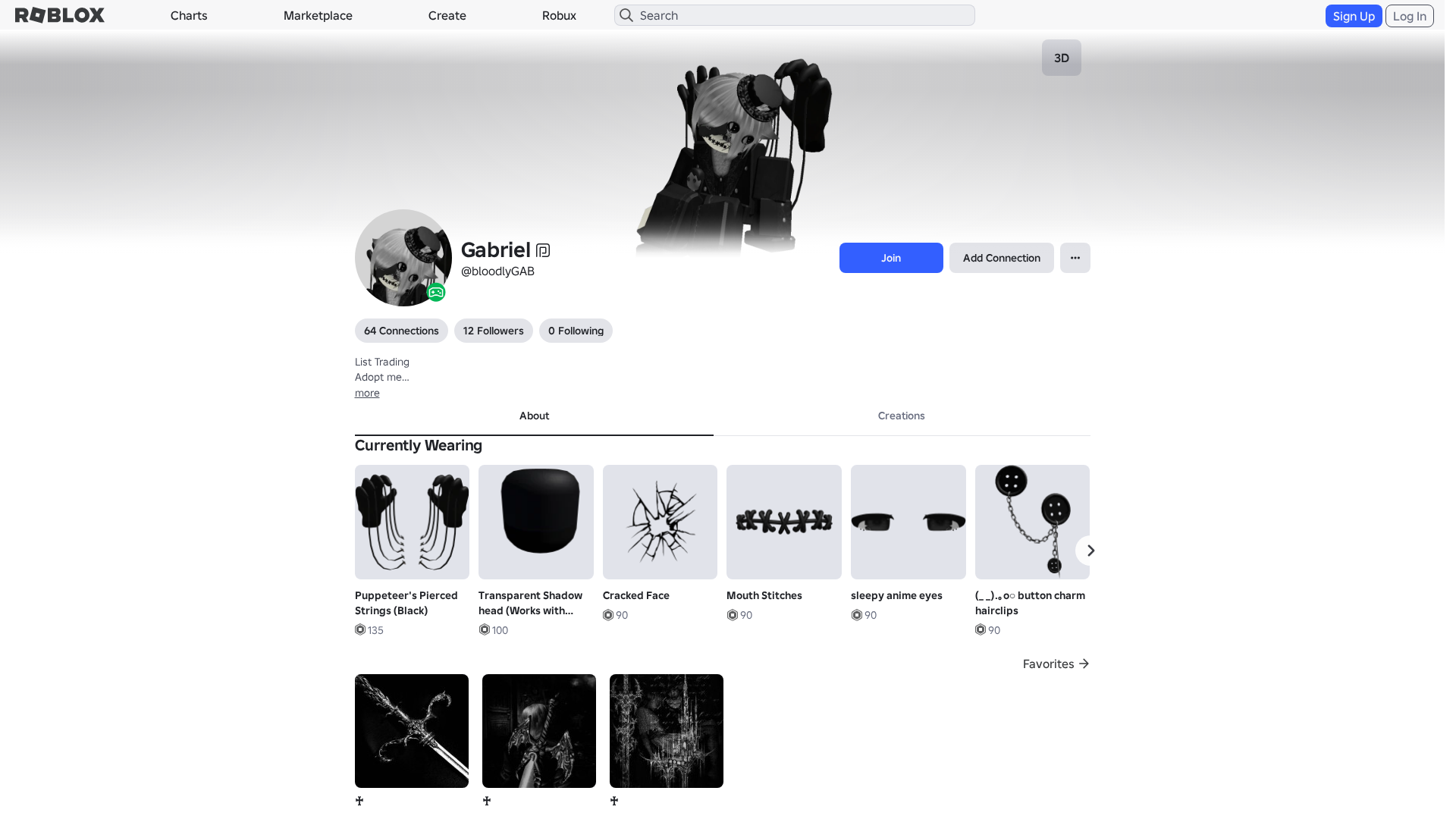
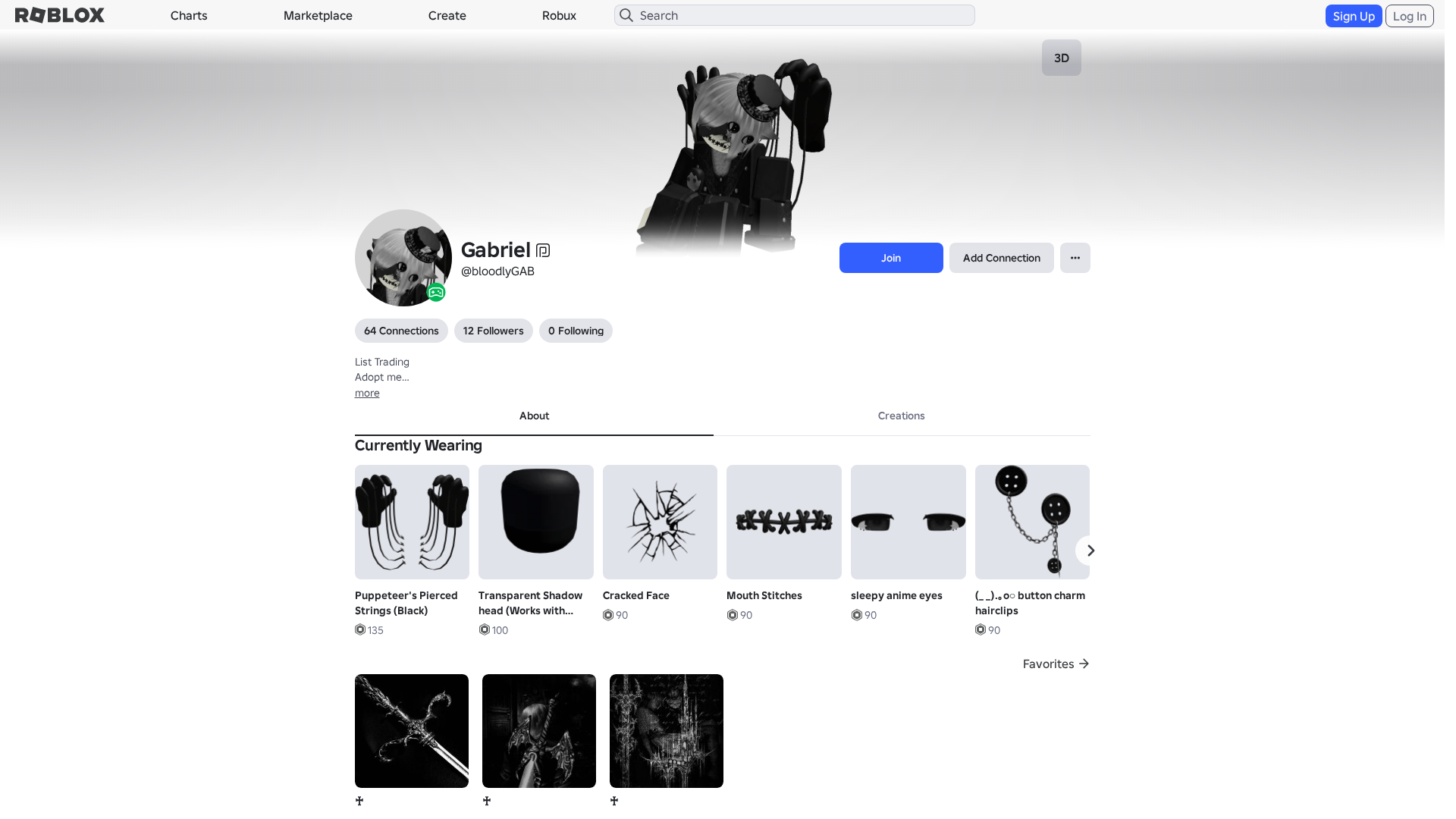
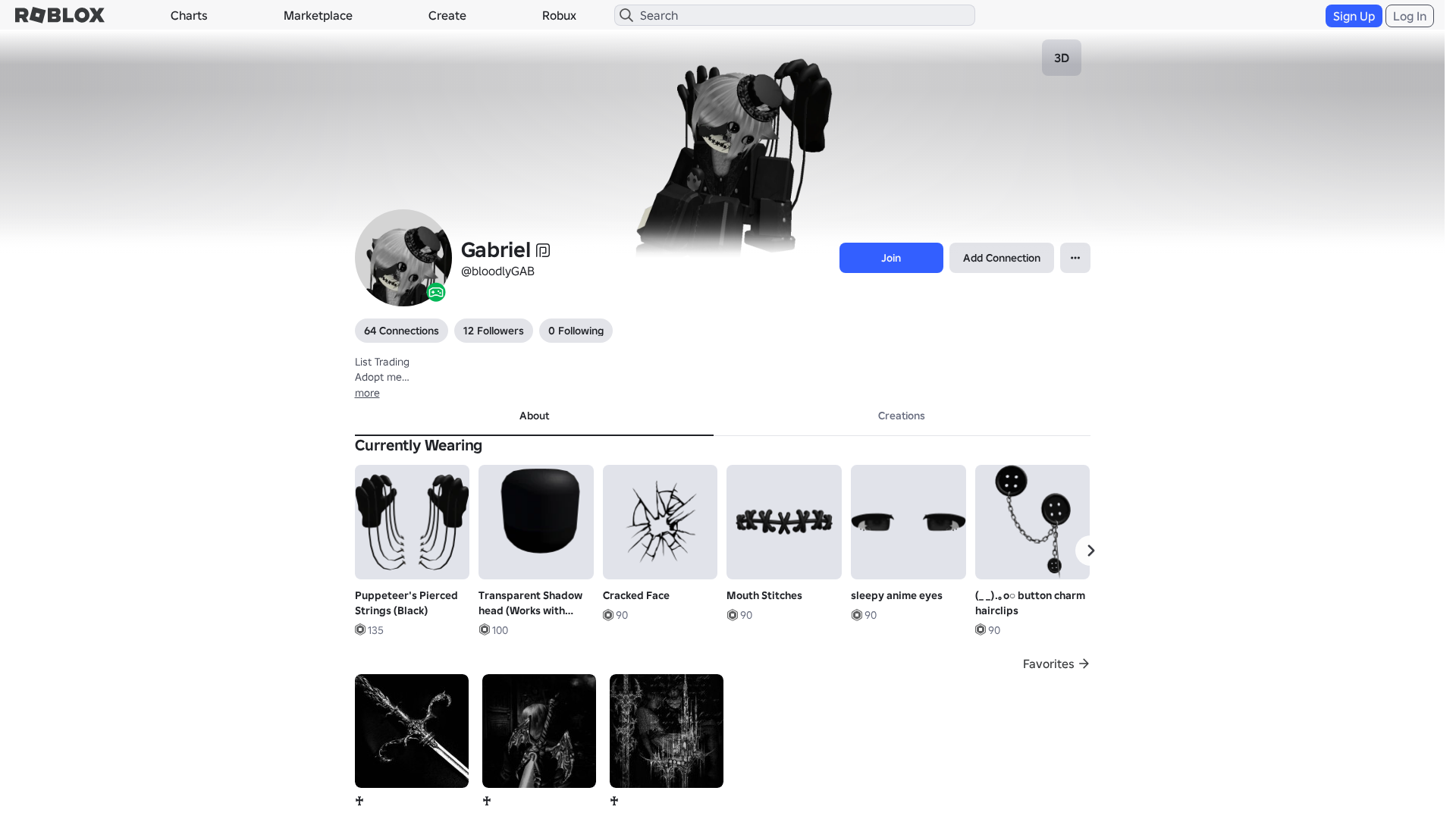
Visual Capture
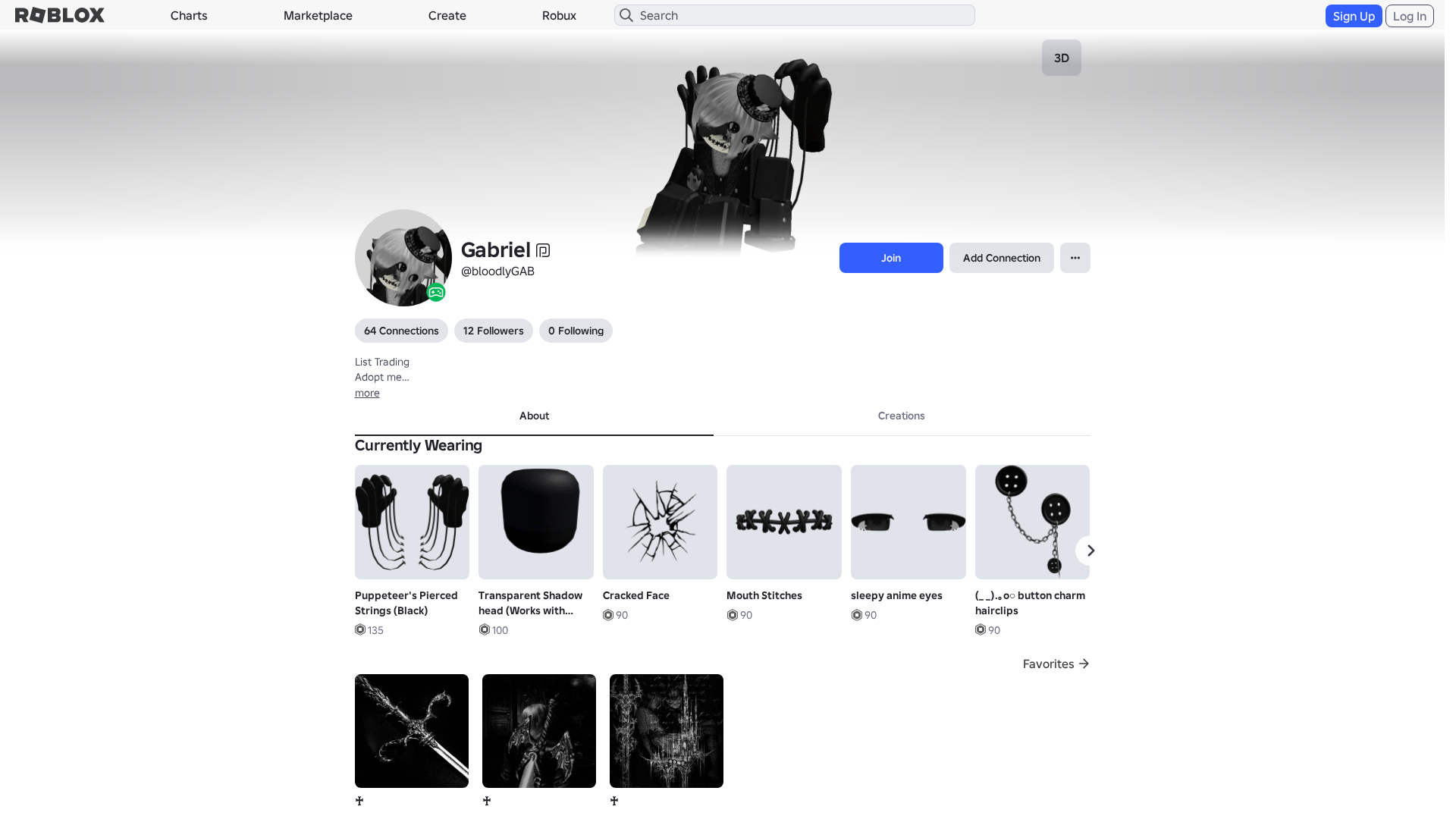
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14373307292142837617B79DAF064672AD2D7C70FCA4346E1A2F8D39A0FD6CE1E86344D |
|
CONTENT
ssdeep
|
1536:M+cXWnurXlOenssg/gg0wgLCg1Sgw2gNqgD2gRegbURglfgf+goigIGgoIgN8gcU:VcXWClAKBZkFvpAWSY0gfebWZ5OWnqSX |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b046334d99ddcc39 |
|
VISUAL
aHash
|
0024c7ffcfc3cfcf |
|
VISUAL
dHash
|
eccdae2016161a1a |
|
VISUAL
wHash
|
0000c3ffc3c3cfcf |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
eccdae2016161a1a,3125253d270f4777,4d4c6cedcdcc4c4d |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/97164262994588/Floating-in-Love
- https://api.injuries.lu/catalog/10647852134/DefaultFallBackMood
- https://api.injuries.lu/catalog/15277607242/Mouth-Stitches
- https://api.injuries.lu/catalog/99453059619824/White-Ruffled-Emo-Scene-Boy-Hair-w-Ears-2-0
- https://api.injuries.lu/catalog/108739206679474/R-scary-doll-girl
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/3576686446/Hello
- https://api.injuries.lu/catalog/125974779288821/Springtrapped-Face-Animated
- https://api.injuries.lu/catalog/14283306993/Cracked-Face
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F240787414796%2Fprofile
- https://api.injuries.lu/catalog/5319914476/Oldschool-Fall
- https://api.injuries.lu/catalog/5319900634/Oldschool-Run
- https://api.injuries.lu/catalog/71302743123422/Popular
- https://api.injuries.lu/catalog/138287250749224/victorian-circus-hat
- https://api.injuries.lu/catalog/3576968026/Shrug
- https://api.injuries.lu/catalog/96242927537422/Puppeteers-Pierced-Strings-Black
- https://api.injuries.lu/catalog/5319917561/Oldschool-Jump
- https://api.injuries.lu/catalog/125491951751014/Hug
- https://api.injuries.lu/catalog/5319922112/Oldschool-Idle
- https://api.injuries.lu/catalog/5319927054/Oldschool-Swim
- https://api.injuries.lu/catalog/18252421127/unnamed
- https://api.injuries.lu/catalog/18252425847/unnamed
- https://api.injuries.lu/catalog/5319931619/Oldschool-Climb
- https://api.injuries.lu/catalog/3576823880/Point2
- https://api.injuries.lu/catalog/96904806462948/o-button-charm-hairclips
- https://api.injuries.lu/catalog/102561820309094/Transparent-Shadow-head-Works-with-faces
- https://api.injuries.lu/catalog/114042415438415/Black-Gothic-Cracked-Porcelain-Doll-Face
- https://api.injuries.lu/catalog/5319909330/Oldschool-Walk
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- /login?returnUrl=
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/80173850283177/sleepy-anime-eyes
- https://api.injuries.lu/catalog/85092320680319/Nonchalant-Sit
- https://api.injuries.lu/catalog/14488197116/Faceless-Dynamic-Head
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F240787414796%2Fprofile
📡 API Calls Detected
- GET
- /api/shorten
- POST
- https://ro.blox.com/Ebh5?
- https://kyxn.dev/api/shorten
- https://apis.
- get
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev${e.endpoint}
- https://help.roblox.com/hc/articles/30428367965460
- /api/pageview
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 209 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 209 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for rblx.foo
Found 10 other scans for this domain
-
https://rblx.foo/s/cyFAoF
https://rblx.foo/s/J3h4AL
https://rblx.foo/s/myroblox
https://rblx.foo/s/1p8tkN
https://rblx.foo/s/roblox-com-users-3324118
https://rblx.foo/s/www-roblox-coms
https://rblx.foo/s/users243671918813profile
https://rblx.foo/s/roblox-com-users-3110201
https://rblx.foo/s/robIox-profiIe
https://rblx.foo/s/LX0Gyi