
Phishing Analysis
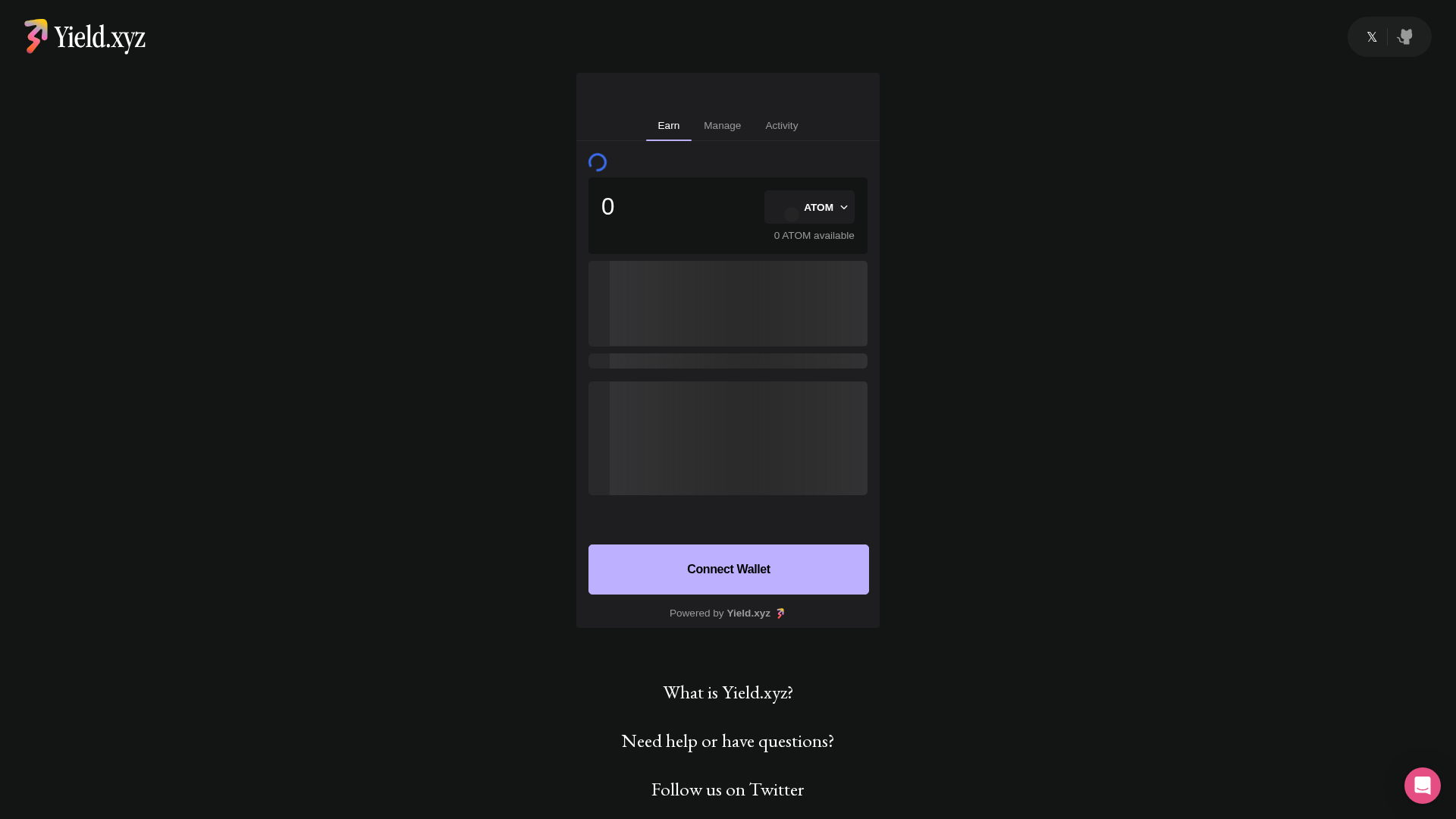
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14D427270B211E67F022389DEF67617D962DEE2BDDC224444A6FC87F583D1C9AB913406 |
|
CONTENT
ssdeep
|
384:WFy+UXDfIuTiCpa5w1SJDyHUmmFkQg9fENvbfDXgW09j:WFy+UXDfIuTRnSJVQENvbbXgWe |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
887722dd22778877 |
|
VISUAL
aHash
|
8018181818181819 |
|
VISUAL
dHash
|
31b2323232b23231 |
|
VISUAL
wHash
|
9d1c18181c1c1c1d |
|
VISUAL
colorHash
|
380001c0000 |
|
VISUAL
cropResistant
|
000430044e300400,31b2323232b23231 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- solana_signAndSendTransaction
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAZAAAAGQCAIAAAAP3aGbAAAAAXNSR0IArs4c6QAAAERlWElmTU0AKgAAAAgAAYdpAAQAAAABAAAAGgAAAAAAA6ABAAMAAAABAAEAAKACAAQAAAABAAABkKADAAQAAAABAAABkAAAAAAbMW/MAABAAElEQVR4Ae3dd6AtVXU/8J8QTS+WiIhKlSZFBNFgw1AVlC6GoigqWCKhBDWKGkxE1GAIxKCCKAKKiKCAIFiASBFBaSKIICAi2BLTYxLz+7z3hZPne+/c+859p8w+d80fc/fZs2dmre9a67vX3rPvzEN+/vOf/7/aCoFCoBBoAYEVWhCyZCwECoFCYAECRVjlB4VAIdAMAkVYzZiqBC0ECoEirPKBQqAQaAaBIqxmTFWCFgKFQBFW+UAhUAg0g0ARVjOmKkELgUKgCKt8oBAoBJpBoAirGVOVoIVAIVCEVT5QCBQCzSBQhNWMqUrQQqAQKMIqHygECoFmECjCasZUJWghUAgUYZUPFAKFQDMIFGE1Y6oStBAoBIqwygcKgUKgGQSKsJoxVQlaCBQCRVjlA4VAIdAMAkVYzZiqBC0ECoEirPKBQqAQaAaBIqxmTFWCFgKFQBFW+UAhUAg0g0ARVjOmKkELgUKgCKt8oBAoBJpBoAirGVOVoIVAIVCEVT5QCBQCzSBQhNWMqUrQQqAQKMIqHygECoFmECjCasZUJWghUAgUYZUPFAKFQDMIFGE1Y6oStBAoBIqwygcKgUKgGQSKsJoxVQlaCBQCRVjlA4VAIdAMAkVYzZiqBC0ECoEirPKBQqAQaAaBIqxmTFWCFgKFQBFW+UAhUAg0g0ARVjOmKkELgUKgCKt8oBAoBJpBoAirGVOVoIVAIVCEVT5QCBQCzSBQhNWMqUrQQqAQKMIqHygECoFmECjCasZUJWghUAgUYZUPFAKFQDMIFGE1Y6oStBAoBIqwygcKgUKgGQSKsJoxVQlaCBQCRVjlA4VAIdAMAkVYzZiqBC0ECoEirPKBQqAQaAaBIqxmTFWCFgKFQBFW+UAhUAg0g0ARVjOmKkELgUKgCKt8oBAoBJpBoAirGVOVoIVAIVCEVT5QCBQCzSBQhNWMqUrQQqAQKMIqHygECoFmECjCasZUJWghUAgUYZUPFAKFQDMIFGE1Y6oStBAoBIqwygcKgUKgGQSKsJoxVQlaCBQCRVjlA4VAIdAMAkVYzZiqBC0ECoEirPKBQqAQaAaBIqxmTFWCFgKFQBFW+UAhUAg0g0ARVjOmKkELgUKgCKt8oBAoBJpBoAirGVOVoIVAIVCEVT5QCBQCzSBQhNWMqUrQQqAQKMIqHygECoFmECjCasZUJWghUAgUYZUPFAKFQDMIFGE1Y6oStBAoBIqwygcKgUKgGQSKsJoxVQlaCBQCRVjlA4VAIdAMAkVYzZiqBC0ECoEirPKBQqAQaAaBIqxmTFWCFgKFQBFW+UAhUAg0g0ARVjOmKkELgUKgCKujPvCQhzzk3//93+1XWGGFX/ziF7/yK7+irNBRcUusQmAsCBRhjQXmwW/y3//937/zO7/zr//6ryuuuOKv/uqv/uxnPwtnDX6lOqMQmB4EHvLzn/98erSZIk2kV7/xG78hq/q3f/u3hz70oTjrP//zP5NwTZGWpUohMBgClWENhtfYWkuvfvKTn2Co3/7t35Zk/e///i/CkmSNTYC6USHQQQQqw+qgUR4QCT1Jr7CVgtmrhz3sYTjLlFZ3JS7JCoERI1DeP2KA53p5c1j//M///Ju/+ZvGg//xH/+BsAzeDQzner06rxCYBgSKsDpqRVmVUSHa+pd/+Zff+q3f+sIXvvDa177WILGj4pZYhcBYEKg5kbHAPPhNJFb/9E//ZAJLVvXJT37yb//2b7/zne/cdddd559//uAXqzMKgSlBoDKsCRvSbDpukknZFP7nf/7HSFAha6/8/Pu///vjjjvuuuuuM4d1/fXX77LLLvIsM1na2Kx7sHfuhNUY2e2zDA1K7rAQpAWaBjTgQMkcXw6lbG9zlk2z3gzgYgI6lE1jhzzcsC3axsXzM3dxNZfS2N7Y/L/+679yZfWaaZMraGDaUSWjaLPoBas8FARq0n0oMM79IgkbZMS/sY9JK+V/+Id/+LVf+7Vf//VfP/fcc+VWt956q2kskaBSYccdd3z3u9/9iEc8wrBRbPzjP/7jIx/5yGkNDzpSDUoKUA41KMMBPghCAWJqUrYWxKMJLTGIs+BjcwX84lxc42gYJ0zkrGxp7FJAts/soXPVaxADp+wWflp34rJaSoHdy0+VRNKmx1lOd5ecW/uhIFCENRQY534Rvi5x4OX65PThCQ/7L33pS3Kryy67TBiICiEhLEWIGHjWs571rne9a+WVV3a6GoPHRNHc5ejqmcglqiEm+ECJ+j0Koz5MwhcQwzKOAhNTYI177rnnvvvug5tDzjUb+OMf//jehdv999+P6B1S6XTtIWyu8Pd+7/f0BK7zhCc84VGPetTv//7vq3dNd3n0ox/9mMc85nd/93cxGpOpVACbbkZZs5BmgHRNm4tPq10m5S9FWJNC/oH7ii6lhEQGd4KB91900UV//dd/fcUVV4gi8SZuVWos8ISuua1nPvOZRxxxxGqrrZazJqzGyG5P91AGkqIpFghbIQtoOAoNN0cxCnfeeedVV12VBAo33XTTTbfccstPf/pTkGIT7bNFWCTlaq6g0p4JFNRoCWSnuJ2Cq0nKPABZf/3111tvvXXWWUdLncS666674YYbauNcNlKpcf4zgWzo0nU0I+3IsJmPFy7CmrDVxQOn59miwuyVXl269OUvfxlb3XbbbfxeF52Y0UZLRzNaUd58883f8573PPaxjxWronrCmozm9mhFHoRK4IARoKSc1EaKpNLw+ZJLLrn99tuRhZTKNJ8aiGmMSvBO+AhcEdDP1KSAodzC1juqoNJRHKQ+TKes0kVyrvtirrXXXhvs8N9ss82e9KQnqdQ43Kelc/1DFWONBph5etUirAkbPj15wkMcCs6zzz777/7u72644QY/BYDYEy0CQwAgJkMSgSoahYQNZ73vfe8TM9pMWJPR3J6mYROpSngZJqGwD33oQ1CiuEzqu9/9LjTAiCDwfi8/cq4raIPpMI6yLReMvA6pt4WJ0E3qsY9TXMchp6RB9hqoX3ilBZxoCLnWWmsZLbLRHnvs8exnP5uoLst8Ia/RADNPr1qENWHDJwZEIP8WBmGrG2+8Mf/5LDht6qVXIiQPEJVNjmTKWZg997nPPeGEE6a1J6c+ZelOX1gB6pxzzkHo2EFWBRDsg1lgooGEVBsb8rJHcChDA3vtWRpc2dSkoHLhGQ88IkzZKS7lFJfVDP5pr3Fq8FGvxinE89NmhM4QT3/601/1qlcph9cm7GHTdfsirAnbk68LQl7Ouc8666xjjjlGvmB+N0mEaNGAiGJSPIhJNTpweZbFDc4Sz4ZCT37yky+88MIJazKa29PXhdGEsZ5hsgW0cIBJJokc0gBl2KtXwDVJmtTYMJfGslSH0tg+ZS2V0zjlnJIGuZRr5twwIBtpCX97NVra0oZp8KO8jOHsXZYR3/a2t+2www5pVvuhIFCENRQYZ78ItxZ1SQHi1jzbaAIT8X6RcMEFF/zVX/3Vt771LTSkMkE1+3UfbLHBBhucfvrpLijq3EjqYWJeCIXvHmw1+b+UtREM1cKEptCgLDllUnRXhgYWRsr2Ghj3vfWtb7U3tw001GDv9MkrswwSSNN23XVXzJUBvjNInik2lqIsEABCZT+BMKjdl0GEqWpShDUmc3LTcJO+VxdtxOfGnmQ9/OEP57JGgh/4wAe+/e1vC0XenKdOA0nm4ltvvbVlEDr2dPVqBIl7DXSdUTcWmW6BdFAqehKrpuQsJkDlwhUU8IGVeiv7JZuvfvWrQfS9731P5CsgNQWxreWoRR3K9SlCIzLvtNNOe+21l3Gi5yo9zoKGTM1PhbBV1+w1FBCGeJEirCGCOdOl0pfa80vtOLE9b1bzqU99Clt97Wtf8zODPgE507WWdiyXfcYznnHUUUetssoqfooEpOCCS2s+sTpEI3pRKjLFznIoASxcBS2ZwKLym9/8pvX9p5566g9+8ANQoG8k7qhyeC3KTkyHQW6MgCS8zojiL3rRi6yh22STTVZddVXKwgFr00uZJ/zwhz+ExiCXn3dti7DGZPLEJKe0uaX0h5tyVrnVscce+/Wvf13OpY2jKMbahTnEJL4T9k972tOOPvroxz/+8a4vVFxzTBou223QqIf9hoGaoyG0JZIJSV9aW9T5uc99zv9LSqmwlUdv2tg0pg5wMnOk0EqGFRPE+siLmsz0mte8xuDdxDx1UDaLa+Aof6gMa2Y/KsKaGZ+hHRVvYoz7ZtBndGMoZKb8ve99r1XXvFbewZX5q5YKg944US0Z4f3ms0zeG32ggK5lWHIKk2vi00MDIABE0hQW++hHP2pZv5WfIAp9QwMF2zsFenSEjHNBNAdCHxTSobQPVSWTooKNRsytR/nDP/zD7bfffptttnEjGZZ6eg3lplN8kSKs8RlXXsAvOWWmls444wxTTpZiY5l0sDiLQwtLhUF9V4T/6Ec/4vTOFcxPfepTJW4dXJ9FQnxEQnIqICzB/MEPftCa/ksvvRQfaWBvrgqLKQAEYWmmAL3mMixih3zllabqdCHsa9xntA4Encruu+/+nOc8R17MEfVhkqzxeWSDdyrCGp/ROGjISKBm3spkjSyDE+MyAYy2FESpELUfSDLneqyGs1wnTyHFgOeGXcuw6AUEvIOnyIavLdY3YyXpoK96CZcGDqF1A2eg4W5UpWALbcEnzDUQRBNpTJG77747/42AdpkmL9tQH+1U+p/Qt7zlLea2MBrVJiJnKzctwhqTpRKK/FXImbeygsHCIm9ZQF5qkhYpk0aKgX0E50CSuT7i88+69q7gdPHg398sXBroOqNujLAIBgcMZf3nKaec4n/9kBemVpmnBADxM/EMCrGNwsLg4hlWyupHLeqwrs80pEW7hKcaNWmngIXtacfusuyNNtrIoFhhWPedyusUYQ3ZrMkFOCg35Zd8FH1kfJf9Zz/7Wf9M45m9rlUcDvn2S1xuUuuzMCbdIWCDBhBsCrhJ6vT9738fZXsOqFIAi1jNlpB9PlboYLwoAikDxB6GPApinAeD2yM4MEIsjxdR3ryCabBxx7yCZm7KikCxau903iYXUOZhXI3nfeYznzn++OPvuOMOfiazGEOUXnvttd6tbMEXqSQ1OvBQxty0W/azqOyOWLt3CpURtOlzDwGf//znm8KTYApCLZM99VrO58ILXvCCd7zjHZ7DwMSUFgCxlawZevgLMlnYAUbOA735htWKXlEy33Qeqb5ikifZ4yneZvIYbaUzxFYnn3zyNddcI0TVaMApk3aNTiRebomAybJNN93UJJfbyeyMvBalklHc3fXFGwWTLPjp1lYtmLx7/etfH9IkmKf7eBxc2G0UYjR3TWh4/sBehvOm5GVSoFMZnmI73mXjQmp0P4isOR2XR+AirOVBbynnci8+xLHwkQ7QHjehLf+y+zd/8zfWW0npQ1JacsdRB6p78W9MYXrbP+XiLN5vFDZqR3df4eTWQKAphvISmI985CP+H1BiJbuEDLbKc7EIuRQ0518V63AejxQtJAaR4aG82GQ8t1lAVAsnGbSJ22gwajt2zQJFWEO2CB/S+/E5iZVMHkEomFq2MMrbmjic+9nzs3SeqRmyEItcTvISeXCEaf4tttgiz9SRyCKthl+kdXjKHh99+tOfNmn1la98Rc6Fvo1oNMhEDAlVDl+CNq8ICs7jlV5G8f59kgt52Ra2SqqedBV02tjG0OF1DcWadB+yRTiTSYd4kgKaOPPMM0888URv45NxcEcdJlfTQ2oj0xGuQ5bgly83qfVZFMyYRW7lLRRm7vxjIAQSbGREo7jMPjggtV8WfJ7+4iE6s+zhIz+13MGbv6SlkHSIz8BQvQL0Rt3hdc0M1bMN2SIClbfZsBUywlYnnXSSyRpZvZkjMewQb5PVy8W44JBvv8TlMKaRlzvaHLSU/MADD9RdL9FwyBXURE9GfB/+8Iff+c53GpASQ6QJMMiAIpwOBEPmId+75cuFvvVqIXQMZdLT+x7yXRIOk/lH8M43qopVK8MasnfrFUWpIY+U4WMf+5ilRtYNZo4GZegVURW3S27PHUftduQxrBj/+izxRk1sBQHBJqmkvqEN9cWkvE/I4U3qo/jkFEO2RJuXSzfGapDR4fEcQPn5uMc9ziotM/GApRls9Qf20GtT0TlKXYQ1R+Ay8ZlukG/JHbhaiMkVRaDHYSaYsZWEQmI1amIaVI1hrc8SVFIkCoocceVnuFiOcPjhh3vUoAZbEU90gQgOItBP0CUaE3KJQ/Ua2BZVB5haqklakaMpJ6TZQiWcUSFOtCeDPcFc1iH71gObplaW+h+m1Vdfnb7UhDCV44fw0R/QGsJaqlRYFMOpKdek+xxNKQBsgiHxkG4w8SM8rGDwPUHrrXiShIsnzfE2IzvNKNUwbcstt5QMJrZ5vADADgPdk+LCwykJHgU/faHa/5r4125QYDHDUpwlqxJjjtpCVaBTSE3wtM8VIoaLa7AQ4wUUpqw+G/pzTWWnuLX41NjGBNqLZ+391JFoQAYt1bS7IV+rbQ0PrXXwrzz0pX5AoFR+wof6NOVvyu0qO4PklWHNAM5Mh3hGEgrRIiQ8h7bPwy/zVp7ff/WrXxUwahCBQ8JypsuN/RiR3HP5358FhF4Wgx2MU9C0YeAnP/lJsy3p89VrI4REnXIvlmACIkTmWSqKgZVCgs0hvOOoE/Ep0sd6QBaixE69KGUF7bV0SKURt6OB2olC2u0cTXnsGA/zhrjeuB6kXuHvvTQ+8ubqfI9qQKA7g4aUWYTKXfO3YWFRhDVHJBMzvETYJIp4j0kZbzq2gsHCP3GYaOFAOIsPzfFOIzuNCoRfzvdnCQy8IGxcjY4U95DB5J365G5094SLEqbSsJJ6CcITn/hEK4z8dJbHEVZaGKJCTEuk5jqJPUeFqBN9D1XWJsXAXOLT1awss6jNx3JQJCtkGOhEt0vEaoMZCcYuygr27W50AR1dOJvnhgcccMC2226rrIbWjqYBg0KDH+LxdpWdQfIirBnAmemQqIi7YCVRpPdTMMfsCbT1VsoJGwWhkrn2mS439mMJe9GONZbz/VnIJbR15513GgibvEvuQ3EgKGMcUSQp2GqrrVR6dYHJ4zXWWEOwJTtAeTIIbTAUJMSevbJNNGZzC+c65KeWN998c76aA3yfyLZmwiEvQqCRcxOxTneWPToLbY0d5qHdEEQmCrkTPPUEGP+Nb3yjl2KrpBo1YWIPBC3pq9nQ7t2lCxVhzdEaXIej8AyOotBbb6XPT2zwJL1cokUU6fnneKfRnCadGcr7s1ASrpEWYRBs5ROwngkmipARBHyn73nPe56pYq+sk1WBC+8gnUQUGPEdlIQZRRNyIazoHUZzllNSr3E2PJg8wmSclwvLwjDXueeeC395GcxDcNooJGUbDZbjuCocrAvRR4LI/UDh09Nehy1BBk66BIprZk/Z1vXth2kRVj9kZqnnECIBYclQeIl/EjQU8kxQpT5fGDtfm3iPgOFVs1xxvIeJZMJo+d+fJXJEkdcZe+huQX/Ii+I45c1vfnMm9b3zK3QDFvVuLeoUcJa9K2ivMqmTml5lQNZAexuEem10AJq5oBpWwHcQ1lsIXTPTzGEqTRn+DIRAW884aKpT9IURCKNjr+3XMfj0tDd/eFkjKOCjDVvYc8jW9e0XDUVY/ZCZpZ5bICbJuXBadL0VvxFmmV3mNwaDGoiurhEW+cXz8q/PQjS0szTURLsUAHdYMWRlvxEf3R1FJThFAZUDBDhunQBT7qGsMsylUkG9szRLG+Vs6tXYHLIFWNiC3V69GkYxKjfD5dGHVwOqxFlSud69WizQrudFIEVbUkj0JG/1lm0dA3yAbJsCZWcwUBHWDOAsOJRI4Aciik9kEkFEKTsqGDq+3moW9ZY4vPHGG5922mkmwikuPUFqBo+IhvqJebrb1Kj3bA5DCZhPfOITIDIXduSRR2644YYZji1x7TFVSC4yHle46KKL3v/+98u5CI/gIgFRYz57lVEHI9jSIPqOSdzluw0V1lxzTc95nvKUp2C0IN+Tn2ouH2VTSM3y3XOSZ9c6rFnQjx8zuY2j82+hyyEY3s/ur7eaRb0lDnsY52Ounp3jI2QkVdSN96ZFoKF7B4L4t+EF/9JsGYc54EMPPfQv/uIvJFaTDQkkleyDkNjW7P522223zjrr3HrrrRHYnjqsqQHtY1M/nWgv5k3Y5xHKEth0sYIrGtd73IGwDBiJmJ5GV6pMI1sX5Z6rTEVYsyDHIZjcnkOjKt7M44WxsPQGAnMlhh6cQ02obbLhOosyy3DYwM2aUg/dvD8LZ1ENQ2UyCBE4qkbBIZ99lVv5p+6dd95ZD2/2V0sTK1CC1aRwWBihC1ZFMBl1iWSIZLHlvvvuS2bTQN6CkMEpe8Vw9oLchrykln46cVLyL4OJfqmJcbduQ6rrHbZPetKTjMohQIUp46mezkVYPSiWXhB+zM/vBaHu1x43oa3zzjvPZ2m+8Y1vCIO4iDa4rHVHSd5hxRPO2nzzzU3MU5/KJnpTBhMdb7zxRnyNCw4++GAfqnIIJjYBI/IlZYBaOqAjrmUjUolhjGN8hGp7XyeVbf3BH/wB8dCWR4oIC0MhX6ewMhWEPSPapJaOjljS4Vyey5GcwAgLF/tEq/QwnLvYDULBrftnEdZiZl38p8Dj1pyYZ/B+zqHgcZi38XkmqDUPEOTaiFJddys98+J6PvibIhSktTVN3p9lKbwAwERqwt3C25S2xMrAav/99zfp6xA6M9UNCnGOLJKaPXjJsf4N4bKXAm5iEcLQSI0wtgTsyU9+sq8uY2TWJLkMxSG2s6d7UmlGbCWw6UgvYvNMw17snCW4QI8Kiymy2M+x2mYYNyvCmgVF8cnpBaF2fELnbE7aUzCzBlxcDCebUOA6Yth+lit2+7DwRk9k5NneLC7PkpUYKAFBMkI73bj0RFRYYIWeVMIhk1zi31miHWjKE1GUMCFcYrCan4TEp+TBR0RiKY8FjJ789MJ7h/IkV2OpGZoT/w0RFpmpIJckNvBpRF/dTIhbTW+LTSdilCHetJ4SzgImPxCrUm6eoR9rbr3VLOotcRjXoCfpFQ4SyfjIwNDnbfy0GTQJj3yxWWAARBt7EY7LUkYNEyQskthYDTGFpAimrJKu6tEZRVSiY08Y9tprL9mWFa1MrIF6LRPkS2DTxQq0yxD0IjaS4qs42tyiz3xEizBXRA8IXVRjmWUqwpoFKr7e9HqrWdRb4jB9jZX8c5+9SLBhH/mIN7Jz/WSaiMlRE1viRKUgtw9PyTcddRG8sMS1x1ERuklkkiqRTDasKpjVJ89SJjaSkjJ7bTS9tHGUvs4ivP04xF3ue0RfJCUvRsQkx1OGAiYZFWhhU3CfYJL9ct92YhcownoAemEpr5Y+sLp4S0olv+DZWvD7KVtv1c/j+LdIzlFaJ4AFuQdtV111FZSSnqRjB1Tiv9/Vul9PBf9U9OIXv9jzTfoKe5Nx+AsdUxYU0REOIQX77itFQlr4jAWXZlAkhch4cui7Cfn7CdlGN9JP+iHWMy03ZdQYmJtiK8EpIHXOvtVs/aERBJNb9pIua4h3786lQkDSDZFpL2K5O+9/yUtesmhfDSj1rbMV2FnZKi0vw8nCy6SWnEFaTbvgYDaA3Q2TZS7dsdTMkuhxPcDlujZaaEwFFDzzWd0/WpPuD9hI18ovdaQsnchkaYTl8FSut+rnmrgYVfFsfIS1kbjcar+Fm5+O8n6RrJxBX+vcjZGZ25PQtdZaS5LlDRAeO3iqoIamdASFPcrmD9wDLP2g61S9HsVCB7bzeISCybBaNxaEi7AecDNRyq7iU+/KL3W8HBd5+e//qVxv1S+6gGDTG2MlwcnjTUu/5jWvkVxk3Qand9QhW7rufpdqop7dqSOerXXwNi6cZfbnMY95jAwrXKYb05nR1KYZcJrQK4NZz7K91AH5xlj2TQg/g5CTefY8g0CTOoSkOK7Ewd5Mlvhk8tNPP/2EE06w7Ei9AOasXDbzyo5OStSR3pdedEwyZdWS1AphmdDJyILHpwANiI1UkvFcPHbESrQ2KpRJsb6X5KgBgrJnCFnJRd9W2Ap0EkOe7JUV/gPcPxv6rx2dMY3Gg+ro7tJGdzE6/XtXzkMx/a0n9xwUK3nh/wc+8AF9lK6V+wpUjTPJpaZ34pQVeLkcSmqJrV760pfuueeepnX4Ooaiu6PJMsJofrauPsKyURAZYav11lvvL//yL0U4f1BDTanWguRqkS+MNKGy2QwMy44+fO81YellpyDDKsJ6wP04q5hkV4uMeLD1VtayWySZ/0pRz30zs4PU+HcTXjsHIUUmBb1oSWJlW2mllfLwIRHrgklFkVqYaw636NQp9NIb2TAUwZjeP3J7X5CX5HjJF+ujaeZOd9XWHBDVKMWHvQjX/5DpXWjXKfDnIEwR1gOgYSsWFY1YybvojAQZ24hAuKrk0MyvKdrycw5At3IK7fTD/p/5oIMOMo4wfWNMBBOxGih03aiKOhkbtqJXPzlpIYxZ39wlB5BSUd+8z+c//3mJtvSKxZ2LtnqK97tUp+opxXb+tZOCZuVMa3BmWnRKyDkIM+8IS+xxShmTCEzS5KcI9FOsctmPf/zjvqvuf7JiXZUasDo/TkvOPQWcRYUkjIiY+onVhO4RRxyBrTSQWci26EtxvgUQDZJY2SMy+zn4XKdOoRrdIxLtuARPUDAQ9u4gKvuZo3wg5NUp+fsJw6xU4+d50v3yl7/cv77GdjRyiDra0N3PHgL9rtad+nlHWDrSdDWcj50EpHE+o+IjBSsYTF35IguXxVnJqrpjrSFKgoaMghOcClxZRunp2Nve9jafNjAUcgg4EICMbYi3buJS6Nj/6/zRH/2RwEZb4AJCQx1VuhkCkx/gskWO7ScKs9dXsSyjK3N1tm7CKIScd4SVV4iwFnqKqewXALHCCmeddZZv3nh9nRqxahiYzKIVWw4kJ335NG/G2hxXNPqX4Fe/+tUeC5rEcak4uvp0wgNdfAoai2Hzd3vvvbcXtvQQaIi4+TAT0yJZFYf3nkX/q6Arkjj7adPGXjNbKyZrRtBhAcpgehU2U8BHaEvOZe8/b4477jhfP00D4YqzdETDum/XriP2wstoCxrY6hWveIWBg2RTfALEnszaaNlQDzwsnBPnXqF14IEHmglK1xVMhnWLkV6HyXqdDT4y/8iZzXW4KeMmsYoAjjZExPOOsHQp3M6ekQyCpMp+ehuBzygY5MuqepkFG09xoOIpjMxx+Su2kljtsMMO1DdkyGjCOChH7RsK1CGyQAjdN8pssAJCS5nIQhrq9UkKXsLhDfcXX3xxXrKohmV5u0IR1hDdZsiXQlLYSjQaG2b1trG9Z4L+T1C4ZjbHLSUamk3xkJB2elqk7ImYxMpjQeu8M8vOj3v9s7KNTw/ZDJ2/XPIOkYyqzGRZ8U/klgJ74SiPHRkaK6UrooJ/iaUau/PtuDciZuLOG+QBAeddhhVKEqs6HHGY9Vb+n9lPk/HqY2CHmFO60YohB5UzPrrRRhvJrXbccUcPxUQjmubiPJj6NsMiezW2Qa/fevseNxlJebvOi170IolJQ5kmk8mUOTNFiM2Z+bbZjyuvvNJ/m6nPIXv81ZB95x1hiUD2YyfdjvVW1rLnpXTMybS6UxsTauOnQuuB109+XLzyyitbGrrPPvvIrXS5lBWcFLcpg8i5nB4OKfe71HTXm9OEgPfPeITaUmCvsAIPZzjWTI5sVMG+dDGkkHCxrJ/RSMtWjDi1AZmJGCYRe7oXP9kmbMVacgf/J+jT6lYw+MmijqIqltOSmdnV1pCD9nM4ulAq2lGfUtS0Nxw+/PDDpVd09xMImjnkOhBTE0d3dAGBPbhSqd9dprKe1nDL0lmrHA444ABgquFUAYoX9UZVXUOAGxOShEzJiAqR0E9r332okXYa6KjUsHjX5O8nTzOC9lOgX73RDceSA4tD2US6lISfmZr5s96K+nIE3slloWFv5CtZ8A3BrbbaCiwOcW57SPLdfnjOt/qwNkBAJMKlJy984QuNDbkQGM2EQoyPcS3dgMpW8OEA/j3WTFbPJdJDtyL/1BIWtmIJ4cowukE/BaqCHtIKBuutbrnlFoc4os4zHWYrNhtITvr2cICGCMx6q1122WWVVVbJpcSbZgnRgS4+xY0FNt9I9oGzEBOeev3rX5//hVYDMepjK05l3woUSJa3eyDuTfYSRp03XRqSf2oJSxCyDUskv1DwViCc5d2S/qs56624Gr+0546tONygcqbz55TY2Tyd17l5JpiRoJ94XANh6SjCsg16/WltDwqUZANRXMiTGUnWZpttlrXHGsBNgyDcCg4MbRgoyTr//PMJrw+jiJpW5J9aB+VGbBNKwlPSKPHpmWBvvRWqSqDqZFiuFYMNKmcYOeGHrbwxxvdUULneFUT2LshrZWFTDMKgoGkvDUFVoST9Gf+xZA9Kb3rTm0DKo8DVm9LiZnO4xUROYXSZo/cUepO9oa6H49Sxn4gwc7jp1BJWJhcgwu08kNaHWMiOsHyHXbphcUPGRwndhhxuUBun/xRg3hgjtzIStIIBd7uOQ/ZiUiHMxXcHvf60tg/RYyjhrQwxBRPwPrFj+buwh5v6FHSNreBAhVDt1Vdf7T91hIn5OLHQivxTS1giUCcpFNETzvKPVNjKuN3rrtiM/2mQzEJhioeEtOOgG2+88cte9rJF11tRWTRm8gJQCbxWvHYMcvKNQOdeCrgJYpIsiFnikOktZbg5GhjHINXy30KqGJ694447vHNGh21RSxHW8gO7vFfIzJSY1PudccYZ/ovKF+j0isjLpYVosiquppLbLe/9uno+BX1N3jdvDAbN4hn/InEgCDlbFE+yoKWaruoxbrnSzwEET4ErVMWXFIyp9XlAE+1q4Madxi3fXO+n90oIGGR8+9vf9qEKnTdF5nq9cZ/XfIbFADDjNzbhJxoVVNoU/PzKV76CsPznjWbpM9Ml4jKc5RQOp9m4gR/2/ejCEaOLLpTuyQsMh9/whjfsu+++AozK4tBRDpqfmhFEGQI2DYYtV6vXC5L2PMSkO9CwEqAghsWe85znANxAG2jqG8pQqMD6DE01D6BuvfXWUHMrdmo+UBET6PkQB/LluBCQGs7kObSnISeeeKJlcnyuIa+ag/dgK/qKHx6p8+SRpu280enP//zPn/vc5/ZyAci4ePZzuEudAl6J6q677hqqwl/8ite1ggzTpy8nNhWkVzRqKENsnrACtyfNUneeJFdPHyhozVhZy37ppZeyjehFatOdQfBFm8iRDoDFvNXrXve6nXbayTJRldxUXPHR+GsrAdY1OQFrGshXKsDY27om5AzyhFtJThF+oi+3XCOJ9gxndedQ84SV4ERPQjGdhkQDeaEw/zPl/29gbaJdT6KBUVJ3oB+uJLTjgjIpnEV9q0M9EzRvxTXpLv/iqcpcM7Q13LvPn6sBENT09awwmEvtGwp41uchAkH/LXa8cKatL5k3T1iCkN/YWEJYSm5NrivLrU466SS2kVUhLytNJF+MNK2hJWZEDs4CiHcwYCvvt1IDChsHVY/QAaJgm1YcRq1XoPNSVtNYymK+R2GjvvVQri8cbOKF8NzDnImoURjKxcdwkeYJCwfxGGQEd3mW5MI0sw+xnXLKKaaxZO+iNMHMSNqMAdOJ3AIrGfZmvdX+++9vkiXrrfilQ0RKXIW5hNlEhJyCm/I3OBtlZ8mlHkL8h8Wa0C7pFVFFyoKubMUVb7vtNjl4E8ITsnnC4ise1ZtTBz3a0lfYm2n2CYmMBOVcjmoT8mrFMIPKuSDJXGEFLyC33spz93y52giRX6InQSW0sJU2XHbQi1f7RRFI2m7mgYPxNx4I20UbdLlMWm5ABR0YOZV9yqAIa3wmg7vnstIoexsD7Lbbbpaz4ylLeO1ZiD3stZziISEEfPvTpJX/E5RjYm02wFZUtmFzPyGgGfJqaAgwPk9atjvp+SzFAqM5rLXWWguSwXbZzu5EK/TKE4SG3kvBNJZyJyRbBiGaz7AgLoNI1iA+3/rWt95+++38iVU4k+DUAIv5aZuC5IJSBrYU4W2ZQKGdgiek1lv5yotDNkkl3bOaIekVyuYPzhJgMFkG36gmS0EApDhL1+hfnZ785CfzNMBCeClNO1nVcwOeEEfSnwkcwqqxKWjDSbqpV/OEBXQ+ZJNGoSqvYQhJddJbhiAUfWu91RBwnOslhHGiOr1gL/7ner1xn0d43ZUuzR4r6f/EjuWjagSOLQV7qnUw82qesMBq09FZdeVbEr7K7Y1FasbtCGO8H2eyuaHEStpY663GiP2C/wrgXfYIy32VRX5D/pYBbFSgBRfSBfrGNXUcsikgtfhYB/VqnrAk59iK08itPvvZz7KBTsM2Tice5704Ex31ilxKJl/rrcYJvnsB3x74DGEwxdPSeYxZjDnfTqRQATGR30Z4nHXhhRf2VAtnhYg7qFrzCyn1DxA3y/7xj39cmQ1QmAfPcJ+zUbt8IocLW3Ep663Msme9VXwrWmNwOIS1E2Bd1qgt2eCZ9MTeew7MFfK61DShiGAhLfeItJzEuO++++7jPz3VHE2DDurVfIYFU6B7e8zll18OZfFsMsu+Ce+Zg5AoqdZbzQG3YZ3C35jA3gW9BsNqrMT2sK4/6uuQlvwCBEOZsaJI5DcSxFz2aEs9MaLjqOUZ9PrNE5a0/IYbbjjnnHOCNdAZw7T0oEC00p572Wq91QTtBX9RLeC9FN9aZYHt5wTlGejWhA9hCRMbyXXwaqyDUVaw9dTRYKCLj6Fx84TlDQ2+KPGtb33LulCclcfMsvQxYDeRW1Cw1ltNBPncNMFsLw2xOld/qb6Dgd0PImIvIKoHHxEanRgk2nuZn6dV6qNgL/Pqd51J1TdDWHCEJmT1APhIIYmrnsFcu7V8EBTMmjmUCZ1JYTqU+9KCmhTRJXIpuqNjhVpvNRR453wR5uB49kKa15lPjGnmfMExnyh8CJw0SoEuOFfgfPGLXzS8VUMewxRxlMxrzOLNertmCAuIoteaPY4idKEZbjLrrJID6R/sNaOzwqyad7wBtqr1Vh20Ea/jgfExYW/roJBzEMlX73SHtBNloS1dpp9zuNRIT2nmKSE0OQc0FUJeAD377LOvvfZaSYcH/Co9H0RkyUriVSPFbtQXp0h0iSdZb+XFod5vlWEIBQGCmrmXbQr0HTWeQ7k+i+gvAzjwlUV1BwN7UGWvv/56WtCIgrRTFlAyr671/c1kIoKWcwBxQXQufCeRHOSYY44xj+CQfxvEXx6fSXEVtBzUYF1rz1E4Ta236ppd+B6RwlDpSJTzs2uiDiTP/fffL7jSCzpxUTUHus6oGzdDWNCEBc+QVmAl/YDlud/97neNB2VVAhvWygpCPXCPGruRXp8KycnpVe+3GinUA108GQejKOggcZbyQFfoZmP+lhEMvWjkZ2Kta9I2Q1jgg2OoKpHsjVcyKWUjQTylgWfMhkveCaXcNaAHlYf31HqrQUEbQ/uMARPVPkea+dMp4KywlfgKW1EQZ9mPAdKBbtE5gfpJD8pwlgbAveKKKyy/MnUFXxmWIaERImcy6laDxfpdp5V6vmKr9VZdsxejyO5JxRstqclrfLom5BzkETWyxZxIweQEOGsOlxrpKc3M9eThK6oCJWS9/hiFBVA8lXloKYly3tvHACMFbtQXx7y99VaCRGBIJBE0TRMzdLeFx2GiPGqR6vpBAOZMAHDdpAxLgbO17m9UQ8HCJ96lIMowl4jrlN2bybBgZxpLxILPR2vvvfdemMZXAM2HbIIZvkm7OoXyDMKkK+Ml/ING1IxelPWmYy8jdEjyKB7sQ0w07SWbjlK52GoGhId7KMQEdrbwIVJ+GJMN9y4TuRrHc1/e5R8k9ZfK1JyIJDPctHMC9ZOVfwDRLJU0ynT7TTfd1EH67yf8DPVm3MQA1TzuNLZFPYhJ+/3222+PPfawls+4g6Z8iPf0kvYZLliHRooAE+RpGjOla/RzCuzC8fSCNoWUuWUR1tx9Se7NM5zvq0S+rw1N4T33y3XmzPx7BxfxsR+DPv9gRLQXvOAFhx9+uIXUqMq3JDxSwGvKGnRG8HkqCEsJY4Ed/RW4Yu9nu6DQIhsVQlsKarqmUTMZVsbS0itz7dIr6Su/sXUN0EHlsUBf/4ybMhLUb++5557vfe975VaS82Tm9shakoW1B71+tR8uAvxQz5EcRGCzkXIGU8O90ZivhpsSUPbhKdrZxizGrLdrJuBFrLiF5g9+8ANvdJVe9UbasyrZ5QYGufRCWxTk+ptvvvkhhxyCrUzoYjGVCoLE9BxeEypd1mU+yJY0hKW8Q4orxiIdzEQGtQWNbBgqCkYjNYNeZ9TtmyEsUW0ay7jpuuuuE8DKfGUKMixdNFbynRt8ZDwovfLNO8oiMlMkjqIt+kotlVWO2iHq+jMjwAryKfHsBSE333yzgp9T0JHgJlpkg0DyrNDWzICM+WgzhAU7cWsweP755+sH4Cues5phzJAN/XaGgdIoE1UveclL9tprL9pFL94jGPzMcg0TWIhs6HevCw6EAHPYuKJvCNi4pZ8DXaGbjblcnC3q0MvWQVGbISyUbxgohmUiYhuaAng6lu0Z2/KMbbfd1v8208hLGjhNEi4MhZeTZJl351Id9KF5JRKqYhruJ9WyKfipsnUQOCHvWkyRDnJxM4QFTf8Jce6552IuLsI/MkhsyFHSZZHfeJbYtJAn+omSjPV8TmLllVfGTSGphAStbVpyHTSNrxvSdypFZReb74rffffd7Cg7NqKPQzahL5LV03MnW5yQg9HINxbpohBGdlQ5bTqlVzOEZVhk3HTppZcmzwqgsO4UmjMIQ2CuEPahC6riN+EgKdV2223nE/N+Ii8BwFdmuFQdmiACuhPdhsc++cK7nsbPxRKTCYo3662JipjQFldEuIkg3rjuuuvqO9ODKvBAbTqoVzOEBVkI3nnnnaI6gMK0oZ6N7UlrU6CLPeewTIEWpg98sdmTQaSmUkjM6nbVYFII6GZsRu7exyLgY6+GMl++R1peJ4gEVDZaeDwdn8whe820mRTO/e7bOYH6CQo+z2X4ShIQgNoA3a991+rZPp0z+Tk6dWxcBEntuOOO3MUUlTYU5ENIuWvylzxBQHb84x//+JprrjF4V8NqTMaOreAjZLgcD7TXfRKb12ExGVZiKr2mcjc1aoaweMapp57KMxRgKtrtBX83YV1SKjTUoyqOwm84CmKyoOG1r32tnwYX2iA1zWi35BWqpgsIsI7cyj+HsRE7ckIJcmfDe0nEEjjqORuespKGH9JCgq9SWQMbjZJwLXmFydY0Q1jcIl8eBHSvf4D4ZOFb9rujJL7OM8xSkV+3zN09RvBkcLXVVlNPL3u+4prT8V9Hyw5OQy0Z0XpRH+5lKSHNLRmLcVtRgcxhJe4nfBCTnFGZ/Nwve5U0KsJaLptmPCXU06FB0+UC9HJdd7wnYyXewOk5hMJKK610wAEH8HgPlWWOVMsShxoSjtcsA9zNv7KedtppYjskJeZ5ZkMdJ69DWLborPuky6qrrmrvEP9UL8riqCoHgGYsTZvJsG677TZxHkDNVSMsPxsiLLa3RWwu7h0MJkG23357/9vM3emFquxpxIcaCoCxeGmHbiKYffpE18JGSbIEf0MZlkeE0CQ8RRSoYDC42WabYSubn9ThpQrctUO4PyhK5wiL7UEmpAEKQfgqwO4jH/mIvCM/wd2Wl0CbLpiI2CiJjr704/8HjzrqKD8domBvLxjCyw/aqP5OAAFep19kCCZzewGcTOrII4/0hkgrbFQymX1brkhafMTfaMT39PoSfN/Ko4uffM+h1CcSJwD9jLfsHGHFD8LxIAu4QPRcRoT7qQFAE9LwnVG7Dh3MsyRuIRIIb+Jghx12mI6V+h1CeXiiiGcT0hyMyzGTzpITyovPO+88M4+yEnbUfXLF4d1zHFeiDrF5IId0P1pQYe211x7HvYdxj84RVhINOVRcQYGjqLzrrrvse5M7uMzm0DBAGMc1MtCjFC04Db3856Cl7eO4d91jcATkHcxkL7yt7FWw/9CHPmTGPRdTz/20YdCG/DABhbDIHMJV01DH3znCkrLq3OwByhU4R/a6ArM8KmGtzFEQlpaDu+JkziBt0m8yk9+Twcc//vEqJyNN3XU2BHSNHC/hzV4c8p577vnYxz5mPCi88RfbcUhtGJQ3zna9rhwnLT+kjr6TdrTYYost9KZdkW82OTpKWIiJE9gS0gaDPEM50wqAppcaDWZTsCvHyYxqCRzvt1jUdLuBYVfkKzl+GQGWMmklthW4nwg//vjjDQkT23wPbTGlsEcBcchfvkBHfxGYLgSmgpyRT/ovC4WOiruEWJ0jrEiIsMAKUwXbLbfcAtmQFy9Rn7GVNkto1NEKwvN1q0OpIwA23XRThNWQo3QU1pGJxVioSgfpDmasrrrqqs9+9rMcjx8m2tGZIZWjSE3lyAQZ8oUp5YoLo+p/qSBVXG+99RqKo84FvMCGKUAV7EGpB7v66qsVOEq2HNKsIUfh64SnkUh49KMfjaoUeMyQ/bEuNyQE4m/ZeybovyzENvPl4QnH45bxVT1oQ3YUNcTOhnBNTZCfLkOCbeSX6RxhJcEOYYGVx9jLsBSAwVHkVvaCX07eENA04iv517Ndd93Vc5kEw8gtXDeYKwJoiI/Zf/SjH73wwgvRFq8T5Da20+Ukt+KfeqO53mTc54mdCMwbke+WW25pPWBDmX7nCIvtxbZ9iF+Z03gtsgKsVbKwozY9Hgcat8Hnej+icn1TubSwsNgadxpxnbler84bDgKoR7eHgwSwjVHs02viI5OMvjzI/fQ0VjmwnaNubC9B1ncyq8qG/JBqhKe1jeQ77bST7zY11PF3kbAW9URQgnUKJqdpgW3FA+e2KbSVii9qlGkqMwRiYpF4WkI3BgpJSa8uuOACXYufU9DBSKbyiBNHUxN5ybMa0qtzhCUY+JBNIZmUUAdu60ESXejlA/Q2LpKa1vVqXX7eJddgC6ZZmHYsmIJQztO0j3/846eccorU2GoG2bEGreuLraIIlT2q3mCDDSCQcGtCtc4ZAHa2UD76zzYFjkKR9N7rr7++5zJ05Ci6uCa8ZIqFjLP1EithrGwT1d6DfMYZZ4hwKZjV7eyVGYmm0aAvV6QLHb0WGRGjZgq2olTnCCvcBNZsHEhNKlvBdKlypt/mK4997GMtcJ8CjZaqZnOV6TOYg6cJY2bCSmGo97znPVdeeSU/NF1lZprtrEdpTsHFBKadCRbDQG/s44e0o6wUcrFmnf3ZOcLiNzZ4gZL3ZFPuLILLKJhg4PHCIwoqCxKVy3h6NRspAuzCHJzNEx4FDwQPP/zwM88800/2koyYwFKWj4xUjDFcPAHF8QwGN954Y8zlpg35YeeGJOGm9HjK+Zn9GMw5ulvwe74SwnKXhAE1R3fHuvKyIMC12CUt43V33HGHNaI+f6nSeND+kY98JMIydLKO1FBxWS7b5TZIitZrrbWW9YDklF75HyPadVnmnmydCxjeA03xzHviQCn3JG60IBXnE1Tj8TZq+jkFcyKNmqMnti6EURbMWi1cPGn0Zxj4rne9i4Eys5PhoWYaCOzeiY0WkulLryxooA4KriHhcpmSo4SqEL+CkG5ogD2D5hyFOj5Dr2cLc4kTys5wSh0aIgLAxzgBPD1isl22MDxnHXGra/RM8Oijj04zldxPY4fUJCkeokgjvRSBk0kJH5K7Vzp+yipbBmiNuzZAsG+o4+zckDCA8i0eBkqbQhAfqYFHfXFacH2LD03fKrsdXxn1Tev6PQTErbDkXTyKd9nwkb0swyF2MaFuGOixoBfIaMZYvXNbLFDB130sCkVbSNnCIBrRXXYPh1e+8pWm5KSTXFHB0fhk9zXtXMzgJhtkdWsg7vVy3YdyZgmjlGV7JkQ4BwUTPDOfVUeHhQD8wR6egnziU+h6ZCaGf/azn/nnG2+1tajdHRe4YDv/bbNUiKhGR1p4gCCUMLKfYW3jQa+UAUVPx4YIunOEBUfwxWkQFpQzfbBUqzRUmf6N33jShK1sVMt4pCEt2hVVABNe/wf55LY8TUECErayov2GG25QY2OXdjWN5Can9I58jJrh5dRTf5999lGmI001UMM5W9G3i5PusMNZgIajTkCh1xW0AuuScsYnuI4xiHJ+8pUlW1bNKBAAOLT5FRMoh7niWhdddNGHP/zha6+9Vgxrk6R+FDKM85pChi4GffE3BdRsW3311U23B4eor6XMa5yyLc+9OkdYKJ8/pWeIk0HTJxuWR8kunEsjnmFLwCiQSmUXZJsPMojeXs+nYBgoeuHvm11efOz9RSwi4wAFA01BhkVBaiJfGmEreT19vZz+sMMOU0iIoS3BpZkxYys+0LmA4TRA7MUzZJU33HDDVgDtJyctbJyDRlHKnsf0a1/1w0UA+AuBf+BTtS5uTvrcc8899thjv/GNb/iJp/CX0GUUZhru3cd/NSRFEbRFcQWqeZhgdfvuu+9utIjIRBmVCdZWRtk5wgJu+jcQIy9w86F11lln/CYfxR05h2DQ27t4aGsUd6lrLokAv1LJqRRsfOySSy55+9vf7nuXBk02Ea6B52WmtDw4W/IKbdXwLuHD2RCTCPJsgY5nnXUWBcUUIlPPGxVgEt2bULBzhAVQ7xGGHZeycR0OtPXWW+sNwArcwMoSSeCbQJmQBOYoqMq/0SaLpJHKVuRvRU4eAtVFuwRoq+RXCuLW3mYk+M53vvP73/9+HurHnZLzqpkCu3A2WoetEDT1t9lmmzwrpL7IysBQQUsNWrFv554SQjlpyIJ+cCGO+MsiN5U8KVk9iG1qbNBvBWtyChiPmRWoWRnWKAwnArkEz8mkFerhJMpSCYBbBPfTn/70M5/5jGeC3/ve96QeU8BNS4XRI0I9vXVY5q2ov8YaaxxyyCFmsqCx1PatVHYuw4qrgY/bAVoXwc/groCw1At1m6M4S6EVoCOn1Yn33XefMjW5DhXakr8JaeNCgZefyGSxlf8K5C1i2OrQk046yTNBVMW1mtBoDkLSl4KiBgLSq5133tl3T/KvkXO4WndO6VzAIyno8C1up8Dt9Jn2atJbBruEetp0B80ZJCGwLYQlTkhOHTUznFKH5oAAegIvh+FI6c9CTEZAZtnPPvtsbOUTASZ0jI8cmsMtmjiF+j72E8LabLPNrL2S3QeQJuTvJ2TnCIurkVUkQ9xe0m5T47OjmEsld7Tnam15WzpzTiNsegr2s0rVzxkBONv0B9xGgTvFVTjP5z73OeutrA7NxdVMcYchsYrilPWNcZMq0JBpzhnYjpzYOcLiajbg6hySWOkWMNRWW22lnhn8DJ11BMGBxKCRh8rUGeisarzsCKQz4yRcSMSaRsjssv9qxlY33nijnxyJd7XrRcuCBjo2EqS+wNlyyy05HsXVLMu5XW7TOcJaNGtND5lOcocdduBncUSuZvOzy8guJhtd1BCbOsriSnmxNvVz+RGIh4S2grlJQ7Ps73//+5Nbpc8zcuQ/U9xzwMGw1yv6/viP/9g7QuSb9G1rULJUZ+gcYcFUSJN1wVDwYQ+Du8DmXhtttFG8sDcw1KYhhxM8FKFOzJCfSzVJVS4PAunG7G3QthTmy1/+8tve9rZ77rlHAGMrr+JTD3/D8zzGWZ7bdfZc6vM3b23fZJNNKGsTWTUkHL69elG9aCcJbuRlMMXVZLbaqHFvheFLMJorRmby33TTTTfffDPa5T0GJqO52/RfFZIiMD0WZwBvUicMpYCMFlLWitZbeb/Vj370I+1hbq/z0yNqj62mIOOgJmNDgHaU8lPBnpqWWx911FEqxU7aTIFbdC7D6ocpR7R81FE+mmcfrML/+rXvMHJ69gAAJrlJREFUWj2/IblQ+c53vvPNb36TP3nEPgU93qRwFpaIKTk4GVCPCRpbILUKyXorr4ux3kpulYidlKgjvW9vNbWHnmhLaFi3CIdVVlnlU5/6FJR081YzwCoLO0YqzBgu3kzAS6x22203BgBKqErwp4MdA0zLfwsyuwj5rXTX/3MgNckTl//i8/MKAEwfoDOApz4AWwlg9ToDzwRPPvlk/yeojW1aIcLFmMhol1PxLmHCwbxzzSgYc6nB3SIFbTk0BTg0Q1hw96+bIlxfmqmHtsZTJBdUQktccSn/iUqjtlToVMyDEaTptJJocww1wtLCkU9/+tPWW337298WtIJ5CoZ+/cAXC8EBCCEvKu+7774eDnIzaFjpLvnibHh8CvytGcLimmxjOYlOg4X0FQxg62fIrtWTP4kAyS+77LLbb7+9axK2JQ8fsHEAUaoAXqxk4x7Wsme9lXqYq2lo6mBQK8gokZGMMl9OBMgrXvGK17zmNaDwjzgYStQAZwFYU7GsvxnCEuePeMQjTGMxCTP4yVPtBzXwpNqLnPRvZDaHRQwO1BDhTgq3fvcFo5jERGBUEJayCWWTVllvZXgIXvEM+Yb8pJ++/erTf1NWPkX9vffe+4ADDjAkVON5KGSkovYYzRWmwN+aISyu6TNq/h8KT8VN46n9DNm1emHTE4nkpt5NOvRqqjAoAvGB0BY8nZ71Vscff/z1118PbYGqUohOQZTOAI55BlPsWbHx7Gc/+3Wve51Pi6OnTMZLvjwhRV7+G1ezRZ1whmt2+VAzhMU1eR7DKMQX9RtdRnYx2YgtC6ACv1H2ZqIf/vCHi7Wpn8uOQGjI3oa8xGfWW919992JXvlFciuTOJBf9iu31TLUrPPTlxsMmjMxB294iMhsPO1Rj3qUSJGIJWra0m5JaZshLE7pSUdemUgNbmqE1ZANiCqo+I0ZUJJ/5StfMbNAqWjhKJ+zlyyop92SppqfNSASbwKP+sARn+IwDKUAtAWMteL/rbeCYYBVcJZD2ArsraNHC0yUaRB6+annCxHD5AlPeMJee+0lw8oIUQ2sAh006J6apKJNQ9EMYTGPUH/iE5+Is/SZDCDRbQh6nrSgy1uYwPMkj3I8d5cFSAesGHJUjcikl7mYGi32LBvcMg+gEkQ8wRbrG/LMk/VWRnaGddCAABzQEM/xbjXkpf61r33tnnvuiZ3RtDBJmx6G01RohrC4LNeUpDzucY9bY401mIRt5FytGANJ8S1dHM4is97yE5/4hDLyRVVcLVPyGnBKyrai1xjkBA7ohCg2hxi7YyueoH7+rLfyxAlNc3veAgFOAg0ImLF62ctetsceewQT/qOZo2Owy0Ru0QxhMZLulFWe/vSnb7755ulqdCYTQW3ONxV1FAkr+R+dyy+/HJGpUa+S/ylgrqT6c77LNJ0YuMCCs2BFNUELq/m23orWNo7hlWqcHyzSK533/vvvf9BBBwkNTwn1c5CBUjrFaXKDni7NEFbsYW8Scf3110+Hw497mnS8QNTQUGTmYXzOv3oJPHmiDfnytgx1p7iHHNRMMLGh8kQj9BK6IJpX660oDgG68xCuQn3vYDASlF7pxflPPEp9cvlBcW6lfTOExR76WLaB7I477rj66qur4cfNAP3gkJDDZYDjhZDXXHPNxRdfjLk81jFIzNQMh+OXreg1ajlhBQ2YoC0FpD8/11vx/CBg6soUp5HgoYceKr0yQvS4GT78Cm3JrXjRqI0ywes3Q1i4ybQFZ+W1/rHTYxFDJzUTxG6gW2Ol9H45i1fpM02XWjckyedwdOGR3C7PDQe6+BQ3DlWFtuBD0/m53gpJ8Q1epGPzXWFr2V/1qlcBhLfgLHTGu4CjgW2K50CbIaxEuylqzMWJX/3qV6+66qoNjdWTJvAkDsfzOJlHhJT62te+9tWvflXZP1JwNf7H7Sg4xRw0kGpJou1tofX5ud6Kw+jk5FArr7yy3OqVr3wl54m3cCr1+nL+w5HsG+rIB3IGjR/4f5FBTxt/e50Jf7Ul7+W+O+20kyFVJImR8JctxkMQ4xdyDneUZ3ktpFdiUk22L5VINuHnHK7W7ikMl/Bj2Z6tGVFYJiADjjfGHHfccd4Yo327ys4gObtzCQ3gYM8ZUoaD4bCU3Fp281aaOTStIMyEzwzHOnUo2S8P1pOwHPvJihlVWc/Dcg75ydjIK2bulPz9hCHtXXfdJQ6T1Qta6lCqX/tprac180FD+klH1lRjCxTyC89b/J+gV7Pn66fTioOFGgia1jwBCApgkTFBxly7/xPcb7/9hEDYSuW04tBPr2a6cWbjyuykgLzY8nnPe95TnvIUg0T2w1/6HA0QFvLSoJ/CXaunERXOOeec6667jvxckL9Sp2tyjkEe6jNrL89iRySeEbRpPuts0TqUIGYbgzwTuYXH3+iJA8gouXoPDY9o5FYvf/nLuQdS4/PwMQCciJATvGkzhMWbWQgrsaVNb4ObzDuqZzzDQIZMLq2mIYcWopTyFeKPfexjPJWP2qLIBN1i/LdOskBxtmNBAsSIUgyLvPN+q1tvvVWqJZKnGB8MhaZ5hW5Mv8vVla1gMJ6wUV+9gWFIzc/xW2qyd2yGsOK+IaxENcu98IUv3GabbXS/uMzG2Br0fH2yyC7j3ZNP6Sq/9KUvffGLX1QQjRkHLeMVpqaZ+GREgNAICALVnk3zrWbvYNDA1rPy1Ci+qCK0Zn3ezskt3IGAWXZfvjESxOncwwoY7REZV09QLHr61JebIazkTfZcNj2wJEtBnszAyoxnY2aG1KYVyxGVwPzSezJ9ikoSQfLQbisqDEXOmI/ibJqglTgr9L4nKO9w1KyWBhoP5aYdvAitLWHPzICeeM011zRv5TUMPFwP7Si+VpBm8hzj5Q6qMFKRVjziiCNGeoNhXbwXwwr8VYTjKZazgtQbRbwST2WIzL5HasO6++iuk+BMEFJEWPo0kywjuozuvl27Mn1Bwbj2ZJNqmVy/8MILjz322Ntuu81REeuQgmBm/Z4/dE2R5ZTH5AbVuIGCF8C9/vWv90wwvVr2umSeDwrMlSeny3nHtk5vJsOKN2OlzFWxGa/V4dibycrso8pwWSZEmrBERrLEJq0pCQ/CvNsvQduE/MMSMgQtVgFiL3cwQH7LW96CtoyMGF3npB5QSTSGdd+uXQcHYSu5lf/wf/Ob3/zSl76UV5uxklomvQoIfmopF+ua/KOWpxnC4tCc1d7oPZylrM9hXaveP/jBDyrrc8S8aMdiowZuWNenDhV4IZmVqbDLLrvcf//94pZGNgX3CoU1pFc/fGhKF7bLEwbNmJWaFGfWPBPUwAPBd7/73R6HSSjAor1OSMvkFxr3u34r9VSmlI1NmZjulFKZNwsZCVoa7Y0xGsBEdkn9eD5w4IDF/ERhreg7LDmbIax+CjOzaUir3n0amlH9XxXrMnO/9l2rJ3P6T4JxRE+vdZvbbbedL774aVwQl+XTWk6Hg+IskSlvsk8Q0i7ZsazhJz/5yamnnnr66af7sBAq75q9hiUP47Js0iU+bPOTffW4HgKat5JbpWPWBk0P676tX6d5worVLciyRMUaFmHA9g1ZRdCSlmviWXm+DtZTISu5fanpjjvuUO9olNLTtqXaUq0gQUBPtGY4QauNAsWxtoInD+edd5706oYbbnBI46VeZAoqcTGyxkRhpVCVkaD/E8y8lUN+qtdRZcZjCrRefhWamXTvp6qMmruL9pVWWklWYtW4qI4r9DulU/UJXZEpXBFTFpTxUaNC0zf+a4fLOsS/7Smrv+2U/IMKg6RoZ08Xukus2EuBBbGVf1HCVrfccgutRbJDrevbDx8I8NJYn474mg94v5XFVuZkQYStpNt8O+CE3Ptdbf7UN09YTCWYZR/2nqr40m9mZ5m5CStyRH2pzUiQCsQWpYLZa7/wr0kcr6Yw4EVk1Mm4qQm9+gkZAkqIoqQUjARZ8Oyzzz755JO919C52FkAg6XfdVqvZ2jmZn2awkEOtdZaa73hDW/w7lBW5gzGhgEn/N66vsOSv3nCYm9DDBHO/BYE219wwQU8oJXRBHdERnIrAuty2ZUKNi9RMTfniaG+11MFX5rj3BlMDcv2E7kOfWUNDEQdkZkswx5VeUKKrZAXwdRoMxEJx3NTusMhCChsttlm5q1e/OIX09q0AAfg0uolngrYHG7jEazjd2mesHi2joj3JxLWXnvtb33rW1budBz3nnhcMzMUXJP7UoSbclnZogcIulkxbDLL4iyzG62kjT3tliwwFpNh3vCvaFRjlt17wVhNGQ4Oya0Y1FEd0pIXmYIaOuqo6GvjtJ4Jejqcnw7RWhl5QUDGretSOQVaL78Kzbxepp+qTGsT5OmQhbQhof7Kvt8pnarnjplTl2EJY8EsVjEXb8ZWhoQqha43THpwZpVsp4SfgzCMFT6SOSJrP8XkM5/5TKTsJzvCwQQWHCCDvFrJlAeFgl5oSOpkWOCl7HIrVoYMxWnNe4HAmTXgBn5yiUFvMZXt257BZRJGZWZsxfVTZlr/d2ZkoUYDe8Gf2RANumZFkotMUpGQeOiJwGrUC+mErqO33377tttu60k/h+bZul/NeuVkIvZJTIKDNmompS+jkJOQZKBO7yd56MgiDER+DKXZFVdc8fjHP15emTRTlDrqFKdPSv5h3ZcW9GUROCgwkILK6O5Jkfey77XXXowFJfpCw6Hk2s5C4vk5LHlav840EFZswLoKTM723MK/HPWiN52Vn2nTis10wja+SykPjO69995nPetZX//61y164MRxfV6eSBAMFMdxol08OOpnss6J6EtskiAm4GOf8C91CEx4Gnm/lTFvolSN//32MSSVpKWLWWdDYPuJCD/cm/I6+tpYCkG7OF6WN9V6qzng3Pwc1mI6cwuBaltnnXXMDV122WUix0/N/Ey/vdgp3fzZ65l1uUYEnJ5/e9TtRSuc3jS8SS6sRHiHRDhqWKj3ArIOx+ECBBHdx6+jW5MEWxEDc/kZ9pQykNaKDVONxkSU0kCloz5cbEGD9RxO1F7CZbiUCB+//MO6I1tQkEa0RlgAoWwe/uabN+zrp2kBlmJoP4d166m8TvOEtbDr+r+BQ36yPf/w/w2W9tx8882CIWMQHqNBE4ZEWDyb2ARO2FMqk68WVVq94ah4zvyXQxzdpkBHFGYv5kWL8kT0TUplj63Ij3eUSaJw2mmnsYv/lbNElhY2aopq6vjopP9jt9id/FFhIsIP8aa0YEq2YBob9Rk0I8FabzUHnJsnLE6wmNqhJKMMSwE23HBDPbbOXDCLXiMmfd1i7bv5k/wGDqTl4gKekMZHKqOv4aEX0Qhsk/GGTo7iBYeEvTbOUoaDwqQIK9PGxIA5qqKCPMLrKLx9wbhviy22eOITn8giGtjEM+ZFW1R+2tOepo8xW6eeCpOSf1hegbDSzVAkifC66677J3/yJ/5PkPq13mpQnJsnrNBT9osqzzn0bKZ+jA3FiTGIXj2us2izzpYFeQKYx6MhcgpmQ1r8RS+bo77BYXPUc3FHF6RYD30okqK7vTY9ghu/mmQgTIbhqAd/+XiEl1uRxPtS/CsVhtVAGDuErbSkgqNs5CGvPsZUXbQYv/BDvGN0pAjDMQc6zgoGeWWtt5oDzs0va+inMxcREvZCwgKfN77xjT6oxUsS/P3O6k69GBax9jxe8Cdv4vSIjFJSEvU83k/Tt4YYxxxzjFktgyw1khpaa0AdhYkoRdQQkHzKhPonPvGJq666auuttz766KMJTCrkq5thDoxMoygl6UiqKC+WhlxyySXRYiIqDOWmdGQmWlCtt97KldWAiNYa2APBT8gw9FDuO60XaZ6wEpDJsOx78ckDEtsZBvr238EHH+w/DdOy++ZMGKMqIZ1ZHqMq3kzB+Hc83qG01Oz5z3++z9WZBsogy7l4bVL6RnLPNN/61reaSpcP7rbbbu9617uILSwND3vjQRqlsRpPFUzDU5PtPEPceeedrefovrFmlpCNDP2w1SGHHPKCF7zAT+25JULPwBkCaBosfgJh5qvN86PNE9YM9hMb/EAw2PiE7vqwww7DWeoFub3ATn8uPMT2DJfq/qGQtWGgRZgGHV62Yw5bVKi3URCjOapAd4XU9+aJ1NioqYG9cgBJCgA9p4NRe4f87J2ocXAWaQk8zdzXZzUM/QzGXcGldt999z/7sz+TCQ6KpJUc/j9JbEtAEJkxvqG9xLNr9iIPBKCKmmEIE4kVlAKgp7qM4g0cGhj80qIyqUE9Ie2nlrCEJb/hFjo0e34j0owKvbvju9/9rt6M3wstb6Qx8jJv3boDhW7EA9awN3MnQszvSlg8j0M3ADEKczSG91M5ZyWuQORQKF45LdNGs+QFOStXcMjmXjY1SMpDALTiy8yyKhQjYjVwooWRe++9txTDT5Gc05dx7yL77LOPBNl1yMZM/i3cMHPQ6yzj7ebcDGGF0OEAT9chKmICCLbaf//90TeHpEKemabNnG83b0+cWsLiEDbew0vs+ZPZXHuLqt/+9rffeOONyQswl+D86U9/OgWpOBVoij6onDlsPOW//80cSUm88sH7AIzFKN57bhXC4v2oBDg2R+HmIjkEHJsGIs1Rh9JAWaVDmnle6ZmGj3FdtHATqA9/+MP1B1qaU/NA0PN7s+xuobFtoGDDAtI0n4259tprSUVBSulgjJ4Gus6oGwM/4zsKIqnM35HWf1P5hAQr5IODcENY6oEzapGm8vpTS1hyAZ7BuXm5uOIo9hyFJ33hC1943/veZ3pFaKmRd4gK7Zs2sEzEMg60ImAo7id9FcwKGRsii0033XTLLbcUV5phLsnXAvL4xS9wkJZQCqH0Cg4p20AHHJQHTBAlTZCl4imvlFBjNt0CXaQfJIUrMfQE7r7jjjvut99+xqcuYgsVDoSzq7msxyaHH3645Q5IwUZgYgx0nVE3JpLBIEfCRJDkWgreb2VW0asllRG6hEuByyXrH7VIU3n9qSUsjp6ZDsGWgBR7PEkkC6RLL73UYzUjRB7WC9SmDZwhGBUEg8hJSMunBDaasKkBBdIRRU996lMNrACCv/T8/o9vtdVWkw3JvETUApZa+A8Dria6jL9cx8S5NMpEOLhQj3G0FZ4mBIEpmTLwdK6WDiW5gLNYNRhcb731tEF/YjhXHghn8qA/8rs7zrr88stdqoMdDFiASUcFMptlf9KTnmSW3ffJ+SEYYxomABH5aTEQDtU4CEwtYYlPrsOB6MndeQkXEb1ihtOox1YWMV555ZUiXEDaN+0TlKIm7dKH20dxlVIS2kFDG/Wg0CxMrYBN9PzSLvswS3Bwog1QYs8m5ExRydec7iIOKbhmrqygAcxdVsFRbPWSl7wEW7mpGldW6cp+DoQz8pWsOYv5jA294o7JQr4DXWfUjYkEEJxlME5U662klkaCsFLjEE63BwUnhGrXMsRR4zOs608zYUmyEsCcCV7cxU+VYozfqDGQOeqoo4wNhavAGBamE7lOqAez4AUKIg5jkOSYyhFJ2INCqFA29OGsnrRIx6aBPaxSdq7wc6IaJwo/9aEPV3BUJmXI5oKANbUUbjISPPTQQyVxGqAqh9xFOSbo3XFZCuSJydAuOqCUT+defPHFbrosp4+zDQlJBVKL+E26WcEAInBBQGILRggEVWWFcco2NfeaWsLqBacCj+frPClRJ02QTXAvnnTdddfxLeuqW+/xBADthARNpUKoSo2AUWmMRmV7P2ktYcnUXthKM/HDof20KeOIFBZWLGC0VNqHqjQIc8kU3FG9m7oRtlKweEo3gDRtbue+mrm1q7nUoIHqjswkSSE2O7qvEaglXd4f3akgpBdNIeCZoCWvlnFQOfpSnBaLIgYrGHZK/laEmVrC6mcAsaobFNL2XApPWZoodTd/zKu4nY1vJTiFnMp+l5pX9QBJagYQmZQ9DM1bicZkQPZGPQceeGC+q55wHR1EHn2agw9REoYkki975Di6m7oyrnFTWksqk3LKMSkblq/1ViMF38UXdALzbePTOsOQkdmrNddc8/Of/7wHZ/F+Ti8A8JrwkyDMN3D66SsghSXQ5G6ZzDKOFr1mxIEJKItCDQMtOLKmYdRsRchzzz3XPFFyLn2MpwFGoITpJ/8Q62mNvl2Qn7ijnxkJZr2VFWeyTv4jiyfeEO9bl4LAvCMsrMTPenmBCDTvI2XwgSnPziDCyTicIDQMUSgvCQIQw0qC009jtIwrMQX+Mt60KNQjPNPM2EqzMRCW+55wwgleoUUeNrVZV+GJ56jtxTEyoHZHtMV/QCHJ8qQVWUvVpV0Ghg7ZAteoRZpX12/+bQ2DWkvgGfFhojwsV1aQPugkn/Oc53CyO++8E4Wp5JocbgyxN6gKk2oPJbiJRpjATcEeZ3kUaB5QrGoge4Uk0h81bkZkuhlJljXAGBMmbq2SDKPGB2HR2o1sNOVRcqust0KjRqY8B5E5hNl51KjlmVfXn3eEFc/mcLxKWbalIA65nZTKW3oNbSz54f029VrOK4fopyx85A6yJ1kMHjeUth7VTw8ExeoOO+wgOIGJwlxBlI6asNwOcRi/h7OYzB1HfdOoFs/hGOntZJd/+qd/uuuuuxIJiS/M9hZk8RoArfynn0fNrX7eERYfSq4u/EDGsbCSFY/KQpHHb7LJJhtssIF+2+pq/WQ5XBwLUHCTPXnxi0EQGCWh73znO/1Dr9dXARO/i1URi8U0GHVmYRSGONxFUoOzLLv379bMN2p78RZQ0JT6cijvxvA9QU8tsZUODwggQuhw0BKlysLmFpl11lIRmHeExdv4lgDjbUYQXFwZManXYSrLHWT4XhKgxnOoUQfeUq3SwUqBh6QgZqE8iMxw+5Kgj1N5NAE3gQpPWEEyCciocXMXd2QvpGBsaDLLBxzRFpoYKXoIMZN0bmQs7KnoTjvt5I6hKu7EbezBpUGx1dBtMe+WNQgkPmcTfqILoPpqHSYn02fah7zU++k/5nxca+igt3hBiIlA6NkMfwyC/DePnAL7Iyw5hQbow1E8AttRx6o7shQBMv3vjibd/SdQvnQ/OoSpiSslUHq1Wm81Opz7XXneEVY/IPrVozOv3/Z/c0nydaTiM6m+AE536txePCv0u1TX6gU5dWhBMGV0I/6TLqEh3K1SNmHMhYNoihrEqpe9+Be5jIDUuEKn9BrW+iyEqBuDgKQSMmDhCUmdVGKrer/VROxehDUL7DzVc5+rr77a2zL9ry+qCiXFg01YIDLZhND1eNHYRIoxyxW7cRgBJa+kjrK9aIxq4hND2eiojaNIDW1tvPHGb3nLW3zXI//t7Cg0nNUNhR6QQl4sz/L+LJSKa2jBKMaw4eVlFxVhOYV27BsdUXOWVmGrer/VsiM53Jbzbg5rUPjEpGkaT4L8g5hnUmZ2M/OFpJJziWSDEaFuWmfBeKkRwkoAC0sRLmWgDmKyVy8y1VPWT2UaeS+NmZp3vOMdHqFqb7GVBrgAKXRNX+NEy1P8r9W9994bopEZMQ1pBzI91WiKlIOMn7hbjdeK5f1W7M4BqB/ENBvo+tV4bghUhjULbsI4fs8jRak18RdccIGvKlhaLTbEM39NtqXAoTPlPMtFO3CYXniKzJSiCO2M/ijip0o/ZSVSLQ/gxL8Vofgr0Sv+kbhcQ6xSv2uBygREle0at5rP8pNe8KbLQKjTS88U4+qNaEr9er/VQBiOonER1iyoctNEskJyCjHwgQ98QFb1wQ9+EJcl8sWwkNAJD9qTz3L7kR0WihkACkUk5T4IiArIy8IF78byxUNftbCJ0l62hY41Dk8pZMA4MhnncmF6sQUulgt7F42xIQPNIQ0EDu1oqsD01hLX+63mYo9hn1OENQui2MoISFrB6QVzcihR4Z+lvW3Zy0vPPPNM4cG5NdBYm1mu2I3DZE4kG9qQKIkV+WmBoayu8jELIWqSjrIaJMVA09oLYKMhoyT7DmZYeRRAI6tJ3/SmN3nnXxQcCHh6hZE9iICJTFOaWe+3GgjDUTQuwpoFVTkU39Vpi1JBLkR7gyn1/inE+tITTzzx7LPP1lImgtpmuWI3DpNW7iAfNENHC0Tsv+EMA7082uS6b1hQ0ybnomZSKnGLpEBBA/UhL5h0Q6EHpAiZ6j8M6HQeRu7+bUi/omZQOdE3vqZgvd9qUOhG174IaxZsBa0YEKscV+gKctErEtSLefxl7xIi/4gjjjjjjDNmuVxnDhObXonJjHeOPPJIq/xVot2kismtULC4lW5QHA5GhZT1UyGDr87otEAQgrHO8q/PYmgKsm+tt+qUfYuwhmyOs846y+vrBDxfF89iXpDr3qUwGTaKdmQR7nPv8KAwS+aCLxxyis0hmzaCp7d3QT/TIPW5iGvalF3KXtm5uQiiUXZZ9b1DbkRCIj3jGc8wbvLfSLls2kzfvt/6LCCAVPdDZfkj9GIgZW/RkWx6Z84uu+wCTykbCgPm9IHTkEZFWMM3lsi3Yst/rnhKpatXFhXprt3MYIr3CwwkgjUQmYINoYgcBcwlZrQPHyEdhZQdFVoLWi/8SERv77LqtVRwEZdNTUhQxqRABrd2HaEoa9DYP8F5MSbOch1JFqlkUgldp0/ZBuelrs+iNbgCMuggDyKI+fdSU3iBCGLqoZfOYMqQaUudIqwh2wvviH8EwbmRzqWXXirn0jlbFuStvmaLVDokfoSKCLEngVPESUgnjOMUlb2tJ6WjKWtvE2kJNkGVgkp3lwiIQ4MjkYaS7L1cQQS6u5WfPg+h0lGXciOz1BGDAE7v3WuaCuzCBAcddJCPj8AfIJS1plSPEjKCgALQICxB9hk0k1/+yUENrmcIV5hWcBoydBHWkI1l3tpTRd7Py+3DOMri5IYbbhAzIsT/6N5xxx3CI/dOUiMw/EQ0wsmJ+vMcdQWFcJO9xrmmyhTSAFvlRNdJY5TkiZ5XKcin0Jlnf9Z/oi3CyCCcFdLUzLlC1E1R2LTGJGVpvdT1WdSHBtwUGEWaaX3sYYcdtv3221tuJtViCwDqBmLQ2KX2E0GgCGvIsKdDDilwcVfHAqhE/6xSYKCG66+/HmGFX3yzB3/ZzG2LCrGBktCWfl5BG1EkTpzei5Yeebm4C2YL0Xht8frrr+8tAo9+9KMxkVO8/2T11VcXhLm762vpFJFpn3xNOY3dV+WQEenG5WjKHLRbbH0WhBEZOgOLNobGPlItETNvxSLaQ4YGjtpYJIh1Q6f5KEUR1pCtzvWNsHg2ikmfnBvgAtSDOJCIenGSLt0qTY/e/XdegsHpavz3IkZDbZYOGEWKHKdoIGb0+RhQEicLWGXhhptkUi5uM+Kz4FO1GsGWu8jpCOMQSVxHM9dxFHmlnLRCJVIj1ZAR6cblYpcksIutzwKFTQNoeE125q2g4SfZQWcPSTVsZ98NheapFEVYQzY819cJowCRz8u5O95BFunh8YX7YYqwlWbqnaIykWAvqGwO2URRTtFGtGhmn1u4Auay5WrorHedhJZb21xKAyeaq3IpjOlExKQy93IF9S6rpbLraDx9W7SWLsGBmr31WUzDQNCQ3vqPUWyVZ4JGgv4DEQ5yLudCEn85fVrxacXiRVhDthQCwjJc3Ca1yaprVBLiwBH83k8FW1hMSzXpw9UQSFQkQrRxSFmlE7XRQGWEdkgh+7RMMzXJBXJNp+eUXDMCOOS+mEugul3EDrXl4lO2py+eikUQNIhkr54berUsGpLDGkdbweDL8qAIN2kAHBuOAyBqC7NPGTJtqVOE1Za9StohI+CfJb1X1v9OmmX3pmNshZXCWUO+U11uGAgUYQ0DxbpGswiYIjz44IO32247/z4p/5JJSYork+qsPYuwOmuaEmwcCBgmGz6bLjQ6NsEntzJA9nOKR8fjgHVk91gwj1tbITBvETCZJZ+y+SdwzGXeygQW5pq3gHRc8SKsjhuoxBstAibUPQ8xDDQeRFs+9aYw2lvW1ZcDgSKs5QCvTm0fgV4ylYKHiZawobD2NZtODYqwptOupdUyIiDDQlVWopi6MjxEVVY5SLWW8fRqNmYEirDGDHjdrlsIWIyGrSy2yto3a7UsGc1/BXRL0JJmIQL1lLAcoRAoBJpBoDKsZkxVghYChUARVvlAIVAININAEVYzpipBC4FCoAirfKAQKASaQaAIqxlTlaCFQCFQhFU+UAgUAs0gUITVjKlK0EKgECjCKh8oBAqBZhAowmrGVCVoIVAIFGGVDxQChUAzCBRhNWOqErQQKASKsMoHCoFCoBkEirCaMVUJWggUAkVY5QOFQCHQDAJFWM2YqgQtBAqBIqzygUKgEGgGgSKsZkxVghYChUARVvlAIVAININAEVYzpipBC4FCoAirfKAQKASaQaAIqxlTlaCFQCFQhFU+UAgUAs0gUITVjKlK0EKgECjCKh8oBAqBZhAowmrGVCVoIVAIFGGVDxQChUAzCBRhNWOqErQQKASKsMoHCoFCoBkEirCaMVUJWggUAkVY5QOFQCHQDAJFWM2YqgQtBAqBIqzygUKgEGgGgSKsZkxVghYChUARVvlAIVAININAEVYzpipBC4FCoAirfKAQKASaQaAIqxlTlaCFQCFQhFU+UAgUAs0gUITVjKlK0EKgECjCKh8oBAqBZhAowmrGVCVoIVAIFGGVDxQChUAzCBRhNWOqErQQKASKsMoHCoFCoBkEirCaMVUJWggUAkVY5QOFQCHQDAJFWM2YqgQtBAqBIqzygUKgEGgGgSKsZkxVghYChUARVvlAIVAININAEVYzpipBC4FCoAirfKAQKASaQaAIqxlTlaCFQCFQhFU+UAgUAs0gUITVjKlK0EKgECjCKh8oBAqBZhAowmrGVCVoIVAIFGGVDxQChUAzCBRhNWOqErQQKASKsMoHCoFCoBkEirCaMVUJWggUAkVY5QOFQCHQDAJFWM2YqgQtBAqBIqzygUKgEGgGgSKsZkxVghYChUARVvlAIVAININAEVYzpipBC4FCoAirfKAQKASaQaAIqxlTlaCFQCFQhFU+UAgUAs0gUITVjKlK0EKgECjCKh8oBAqBZhAowmrGVCVoIVAIFGGVDxQChUAzCBRhNWOqErQQKASKsMoHCoFCoBkEirCaMVUJWggUAkVY5QOFQCHQDAJFWM2YqgQtBAqBIqzygUKgEGgGgSKsZkxVghYChUARVvlAIVAININAEVYzpipBC4FCoAirfKAQKASaQaAIqxlTlaCFQCFQhFU+UAgUAs0gUITVjKlK0EKgEPj/VR9auOuvjyAAAAAASUVORK5CYII=
- solana:signAndSendTransaction
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAZAAAAGQCAIAAAAP3aGbAAAAAXNSR0IArs4c6QAAAERlWElmTU0AKgAAAAgAAYdpAAQAAAABAAAAGgAAAAAAA6ABAAMAAAABAAEAAKACAAQAAAABAAABkKADAAQAAAABAAABkAAAAAAbMW/MAABAAElEQVR4AYTdi3IdO7IkWD1ISaeqrln//zeOzZj17ao6okipl7sjk1unrtlAVBIIRHg8EEAiH3vz49Pz10+fPn38+PFXy8+fP/3+8OHDly9fXlt0PT8/49GFgD6esaF//vwZj/Ly8oIBRdGLTcG/3puiieHHjx+0rK6pgiHl49PEQWmtC+cKispTC4aX79+pH0hkWzSVnz8/DIcNmowk+Pb29uvjhxlc634iMvQDnqcn9XHqwkmcnpfvP1D382gMIdomQio4LZ8+fvb7jz/++Nc//wn2yx9/zEgMK2NLveIfPv1aFBCGs8pHHY2hY5jbi+HT0/MQ1MPw9kZsno7tL8dfHHl6wnzHQZ13isqY4agrcER1hqXx6dMjA5F0NZi6FkCiIZYu4nojIp4NOMzZn2N/vv7xlQqyNyX2f/78888/Pzw/f+4oRJH4ziCjVpN4QamujFdzcsMUTiXGNoveAk4X+5Hnmq7wXGUmxeGG4iK//0YX2BkTtAaf1K/X1+evX6QuhmH2+PPHy0uEgxe6iSLsIXz+/PTxS7ouhGOz3s8nJ29jVPRuft1KCf768KbLHFTnfqPxRpgu9D++fsO8okn7yp9//llzTvxjQYbl59Nz8lNRRxnPXUGnAfGeL58/JHPQ8XR4D+C0O1LHQqUMn34mH0McA0EVaAYdEQ9ORBSTC+W7KVxmWm6Q2eM4vRBGCdTPX3FjHaOSB4cyOqYh6l3R9ViwKVarJRYe/AoQUZ6ym39djugK+oWa35pm5CqpV/WaVGiqV1sMVpa4w7ylMOgiOvGw1aSJIzOMCKJyVPh1zd7RJ4X482MnYXsRU+BnSkR4CDdO/OoAqyT6jDAVLRlUXhlWVT10/K2XDIpgowFeBfPPt87DWdMjut/PX77UiDil4jj+1cv414PxG/g6cArRNDqOiEFZ06+AXuWWQhgDhOVWuj59TiLreHpKDjYL+ftoz3s9LlS2YzfkhNGPBa4Oso1jp6szMOKNCQPQZ5dky6LQLvGq5hzeXnMiVFiE81YNdoIoyZBruo4+kd+O5tWlq849GRSgphWEubm5lzFXHmzryNQFZ6+wZ0wHrgJNrFhx21PptMYZgTsC6Xtvtkc0EgQw6fyQ08/OAQNE5BQSjqTdY3YZ989nxLGtTJfNyInsLGz0wvAzxl/I17hsql7jtZgcuKLcyI+OAFkzEajxdxYdv66AE2f2X0Bmw9Oy/h7OUcGNQgyW+q1YfUCXDwE4vXWArObE1Q2tujKeWwoyIqgdD4J2h2pN4srQ0CcbqI7PRkMVfSY5qhNReXs9S776tI/OjvGPOMwdp9TxBgnFin7hTnAttt9Sg1pm/OLTz587CTMlCPWIdmyBehgVvV3WYrO6QpZ6PKm3TEurTdCr9zBgu8I+/r8c3xr5QOOkrkdabJtvztsvPLPk7qrcOXBQ4cWr3THYNt9+vIbZyl6uzWG9WcVW5ggja2fWAZuyBM+y2O1tnM3kShg7auHUq1R2Edhxg6herSdKmhuC8cyLd0e0QTWwE7/sCpnIjqvM1TBcM3aUc8wIJj24jkWWg/j0yfWHs+zZIBTts/Pi1kRTgXM8xe6/oqu2vf7CQyxdiw2sLk6LWMgxryrOfBzJdBYuopocj+9NrdtUdLPjdk1T16Pv6wpau/SGoxufd0q7NlTjN0zlOjNrQTABSW9rUkvwxkE4qV1laxNxdL0KZrJbH0YfLwZF3XH0VVbPWXHd2iOtQgCoeoy4FiBEitelV0XXjjHhGmMiY7sVqyhjGBpvCSqI60VPuUI/fmxDMwATR0nArkFdIOAM5K7czeionbCjq0oKUF3Vvq6xOd52osshzCOuMuSaE8tjADZgmFJC5L/AwknvQ5SqPGbgG46gjBhdSulcHkPwbs4PQTbGMBelMU/8oP3HL3EbDc5ULGWOuvYNoapyuAFV7ubdmwqbO5oZHQG6CrBly7sV1zD9ZkP5ySIaylkiYgmjwt+H+FhjJzu29id0Et1xplKqRDxDfAX2GjVdFDplOw6E6lV2vMx/T2bIf4nbA76d4AkLNhrTFXsyAx8BMYUBet3RFR8RHibz+nXdto3ieFeStB332bmmOiSCk2Xt6nNWrxVEnmgqBcvsc73547VXr7VrSncUOGG5dU2qWuZBs/pycID4MeAUXMOh7jy9DcGsQrkxGaOp6Br4zQNNnWplDI632epTh0elG90StEea/F2/IQaX675C3AwRu64RZh9OIOrc0KUOZEWdKbc1mmMuRg5JuzqA/xbEc7Op6IKAOSv0l+fVJ5tjz1mfnuNaxT6/vSZGpJKFvRqKCjcacorPwEep813M1MhVI0FQyqenmLE6ECV7KPcUvn5F/63kbk7lZc/D8CxBs8q0DAvOcbCKONK86Hk7wXQl2sGzSF0DNl2SPrsyRl+n0GNbib/Z08ZOSOG/cPCrL4H+k39ojrcIZmV0UugJTqZhQvSIMJ4E8y6X0gdCoNb8jd+84vKDU+O5A6WCMmMcReyus+S2sGwZw1yrpuhJr6Jr0yn8HVPB7L3CsM3jmtR8eDhRkR2Q5P21RSDXi8HOsecnK0SDtJ3fsTN9Uinp1BmI//LdXGbYvRxjpEVU7+CgnHoyJYXZAXwvaZr+c59zYpLcuE7t7c1Yr/KIPCL6XaFEUxmb49GYdD8FReGSXrvsza8F3K0roq8/wqx3pczv812TqYyURSoKhEGvC+VuZkbUvIGMDjYLykh3h4qyhBgfIBTojjeorkezxumIx/FmW4qPiN6ciVz9DJsu5YL6vFxGwXyzrXnPlghsDb6GH7PCOHTKCapcmGHWu2YZyxzyRZfJRzZdOB315qTfeTLKQaiJ7J94OBtoO30UPJbpH9vNFUrcWL6uHC/8aOoiSUl+gqO/a/G70ugMZ+3ZkW8qQqfMpJsnfL+XBA1CB27g+glGU4vmoy+6NjToF8uJ5D2Uo1OK89ePN6GDeNRe1q6J89Cv+N82D+34jm1nl+IEVgQG5URS7FlFHOC8vpFvLSoJzhWU2bnjCVG7zKpwNiy7UDsuPxi/OAxpGh0RJ4j/gC9trnxGnFUE1V0quuU1yixXn+AQtNZ7Hye45rQX53h94z/y3/VHKeGdim1F7X1QAP6HwnfpBWHmzVNHV7Q4yI4+A4pzNg2Tv2W31dKcurlgMbnXJvwjqkBbXWXLy6RGn67h38cnHDPuBhrfza2i3OFmEGuo2XFAQ0DEOcoccOyZ5H0Uy8K2e0/OYr35IZoJeE17sgq0Yf6lOV3MmofmXPg+5Sps/GIUnuzzoitQhcgZL/PX3fRzLyUT46MnMc5UZ4v7+vb6ubcqImHCb1lhCQYG9ayQu+4EY3w6HFSB0PXNgxu956T64dOTBesVhWf+zRhZkIYTTh6r5B4HkxQ4svzXx3PmwazY/VVLe5/ddsyctCHBq69bPo6WJ3y/l8z8zNDw01qD86yUwv7gNmxZIJSY8DnNnlcTJ5bVUboySpj95H/qEehT4Ds9WBuMnvB0P9LrCLHaKYWKFnvcB75GDZlUxk0E2PDz1bWWXI6qX6893cXyNN02YmcNyaQ6tV/ADBoDwhOoY8+IoFQ4i0qp3LBnei8VmeyO64pI1/23rKokEk951jzKKNpzZOgZkaGMVdIxTn3+5CogZnR90y5gVF4WioZ6g9/wS9hEvZa7CAjacvUtl88ZxkT/3KIKiOdmkUbk3LPkBM7euBZkZi6XrFbRy4PakAOxlUdnKxgQheOfP+V0u+jp4pQ6qefnXGFguWV1ueQkpaKLlK7VxzNBXYijo1RPRMaz6axO17ociaCsnBsBSMotr/7161estw6UNWc9+rqgVPuZhwPFrDJN2EbUHAU/a2bZYMePLZWajrMaEprRI1vTB4IOxOppwoezXf0d9/A8qhgCug71GeyIX3O6dp0VFuPRxx4U43dpGcGWmtBhhn+udt8nRpY2HPUOOImZGu1qNQl9RMdZ4unADDo66u/Yxlmc9wGbXyxkcO6gr/sW/o/K05cvGOkiqFPdEb4tfYUjEJdvqLKVmoDfPGSAKGiHP7MlzUNctpAoG4T+ziEiF75mwFeKwDAFQ84xuxDo7b9Ow8wQBTsfLqEAJgKj/H60KHz4lHMV5sejJi20i8CbhwbM7lNsl3jYkkKdh9hicRfckxKbS5WF8OPlzxOrWVN+dOMBh+Ctd1BrAi/qLkvz0oZbCiiz8ELK7xl5pBo5bCLwet6c6Cy4w54+j11jPJ7d+eafSJoat1+r4DVjcv45D0iQz/C2K0MwXbNHPvv5/HzWgfE4rpedFC1ow2EApf/+979VUGbS+HdEVOYjHgwQ5qkjHhQFj2NCWoZR8K9w4ZkaAoQxffv2jduauq1Z3pJAVBcCTe8uwMX5v/7X/8ITyvfv4BGpccQ8/rGJ3B9//G10WuBQP3CAqzgqszLGtU5FYDsGM0+X9dtDfczJ7HqOKGgWOW7Ek2f9ee2L3qfPX5y71YdMauuCKTEtM0buTpEcYn34WUjvly9hSG9GmHBSo4bmiM2l0M9fX799s9nODc6XFynYVczVtGEwrvkhlebHT1++flPpJu7T65/fdT09W0riLx6rbmZOTpIZCw7+/O7sKvTZT3GBMQKbrp89cTG10zjGKFZDLzFhf6TLrSSBXkuSs/WbH9s8Kp6enl9ffjhN16kY+YneOMh9l7TPeani7efTtz/QWfXtj7+9/nDPKAx+YsvTs9+Yu0NJiPxkB5o7R/WdUvn84zV6k4SsDD3hVWonxbHdIPJ3y/01H7DH4Wc3KCMbaEP85HncsZn2qMt8LbJK6k3F7CllvaAlgEbw7bvV2T4ZAwNibfz9JU8Y+CLZsG+4dgRZykenK1kFJiFM3ngf6gunPc3sHsokN3FyN23qRDwpbNdcuyHHOCP1EQFJaiV6pkp2gvEsP8l+h8ZV5BONZmk8ys213J16/uMPUcCWMCZsFQL59ubVMOkqykRFJcZnR5/AgJz2+qX98fXHS0ZNzU+j+uXL169fTOSXmowaGQwxqfvg5YfRUKnCrFMSUpYmkV7f/vgj74LJqk1qdZwWB/NCXRA21xDxKIxPzK+loLBhEwWc601E+mhFrzooBlh/jARKSJNfnfAKGXzsEEQAWTL69AHb3vhCbF7lbUbMQBR1DDEtzDFlREd1bBhYhucvBZGiWtR4Nn2j/ccPSTNBINhgL4LN2uZ9DYBMRVcl1ZiEeQW/4i5rcLadZIyoWWcFsaste1TGT5wntrkZwYZIjCJcBrmQVBhONc0XvoanJWg1YF0jDpZZmrPw7p3iiy0zVl3Ikv1VilM4b8GI76dQifvG8SLifP7yldcxlTHo7BNQWwxY9WvqtFIxcHNWncv1blZu71NyzAxmRRgWXy7xxNMPRSOi45wBUZB0Ocxr0kMjZiKYh1ME2vODfpXVD6U5lh4Mk00956gM34NGdmblb1ElbhyD7OhM/vTFuscd/eFsgaQZzsZz2cs2bFnKu5jKQLwYmDzmaugOGqVvpcUvYi1xY5mjkmE9J9220qWChx20mDhy8jIpIZolYYZmG3kZPAILldsAdeat6UgWG5FcsnXzAiNQCd4p6rNzXRB0JJQz7BqF8SBjICKVEpOf2euMMsGhOa4ZqPo+cM0xY7iNVLn5xzwpxFUQSeV8OOd1ICnjsDDZPa0rCvy8vVmLMVjnSFpZmhpRc0vNPk3qySpWG+IrOFc0dU3qoh3t7lHOdL0rGCLe4/AxGI/RLVgid3pb2VmhJ1Qp5n6wuwCf8LDDwom/9iaxVfLTDFGho+NCrTHOKoEob7Tf7Q/kk51MmHqSSa9zSOwJZi19H3s8GDjLcnVHZbmuoivuO+7HPaluHGRob+NYaNzP0usuSd/PRH87b6JH8LHU9EdCMBO09/F+UHQy5eY/ljSxGBazJXp3wcZDfoWzvviNGYPKxiVdSjWtmiOG8WEdc3nMReQY2/DiERzJotVxyEavux1qEs8GKHgbgoU37ZqRX7BO9Fo3NHYvNoYW906MbLSc6llUYjxZSGOhBcJ9yQz3Nl+Zp11vqUbxo5dAKrXn5w87XBmQvV7h4YlGtlo2X7hFTzo6V0NuCtWLnCzoSEhq8q8P3YZntBeo0vXa8oWpBacCHNr2ccgNp/QLbFS7c9pNwbocNygxo0XTsmLyEpR45i0ytvU6hn+n+Y7+uhyNiwUu58urIE47k9ijnjXBqxI/XH6dCwh42HEqQ2aJCubp0syWotFA6ehn5NXHqYKZOLNXHx0l/FyejAaUUdX/9re/ff/zT33E+GmDtwcNuras4kQHnZcvOvdQNIemDo1lzhbD1LUCYQXDTFFREB1zrbEgNuI35mPgbnFXZYKTZCNe7fj9TppVMlDiZTZgACj6DRwjY/zO9pXBGWOyoiVYLI9IcWYkBl0Ec23SBQiba0Ynwwzb16/ShoNzZBbuiIhTlEgFtpfSUWHFt56yCkN5aLhFskbEo5z5Y0YLS/iTag07lTV7vHAuBmznqlNPSn5ZIJofaXaYJho0LvvJnYvswLfbjYMSI9LhD1sDzpgMykSuWMWX4sf+i3P8a1L/W4ggtmTor13DYdiATmxD3Dr2C6r2a1xDLxPuXiDyb+Flea79KxZwTHUn812z4OFvfeDquJj0aFXjf+YIBtdjY3bELKOYlt2r+dm7cpSaXjWp4ItS9RHIvIwHKUPQ3rhrJryd6pGMMVGxolcZ/fOe7Vx5O6n0dlEYjyMKl4n/ePletKMRJVgtDUkOk9LF93veaep64M8aBBcP/kmVxyFlSi/s82bpkBExDI34mB+71pv0u/D5haicfcqNvg58WZV62WUATDP3tmhgvbthBkbBg/k2VFOBODsAksLw7Zu7ToIyB6ozZ6F7pI9jOpYtQgInwwYCXxe1iMFtvGAqOtEwRbCK25vY6d0sEkWLdd8H/iWu4XyYRUNAVMhqptSFm6IStJVQczljlYxnbpfwyz+LjnsrNg6WhjaHZOrH7SRWOUnl3J1lKFsxU8VGzUQKfO2Mlm6HImKBSIS3wNWudBPLA8Qm72nG5ASgMY4nqRO4zP70JSeMCJ5S3iBYB8vckz/J4CT2oFQsbfZ00xXO6Ygl+RcPjMH8G2KMa9kwTdsZiKJuXZ5HE8GughMxY122qCjVQfCLlko7E4JojWCMRMweI79yVDeBk3iWqvjYn6UEFWRQii83pj2yLbW9IIXaYq3n2DMmM/M5N7MzlEYbCO3aGa+MbkOSjVvalrPoTzHvcvBouuDJ2hmQAedJvFvX3/72D/a7CVKsYvOd3s64el9idCZQHm7bJia20HsREaAYlrVP6mW6Pp/0TpwrdQU2/q64oqpcQqqX+4ZDZdNyY4qhagG7SshFg+2V661cjb280BP+O9E6Q4lMar3TBQQR5pq3VeU98lnIcLSAXQXDZ/c4NMY6lNVZwBobK3lJgDyV/k8Yj4prRqB8cz5BoX7+LCiakNl2W0lE3RHDo9Jp3JEKPOoqCbr4Ju4+tJmHA6T0Ih51UdFXtyqcjLAq97RvO4tfWGZMthWV3QkhLrXMEkRRm507HvwkWZOOcKIUNHI5dXdkHEfHr0uZ8ffxxiS23lh8hYuUBWw8cFJpdkLxsKKt+B56T+CGw1t36kr1HlkUQRk9zIpmjXE9gfmiHfNQGDP6KuqKbsbNQvQsSdewxrALBZF2Bb9afq5SzUQPeCRmCYaJNM6ro43/Nn6USF2AhNJcKf/Nc1d0YltTkmYoJdg2ercg/Q976sFGpH4x+GJES4lrjVLPTteC0k3H6FO6oYx4x19uRKyewhYFSyiC0pi820kc0RE9S1aOKW5h2CvsTiWY4ItAxct8sqho0UMQz9y5MIKDuOZAKouQc2fVhmcFNR33+JaKcrS/D8XJos6brCAqpphLB0fbmi0OFtvi5UDT4qMy/snSMCMcx7zZh2d0RJiOE1fR1ensLF/HkG4UdWLGyXFXf7qsX2bLeNJ7Tb8p2JHgCnSciqbFmorVS3sfM1ITHP2WBY4+kBDLpjkGR/U1gV8INF6ZTXs9x6N3po6fNR/zHlNOjzkN+pd7W85g2PIJ+JC45hGeHVO3mUmX/yw1KmifDFU+hSM+VNyMl1UhnLpeE0ksepXd3/0I+3W3Epti65bTbRcHnkacF3Utx8biHTPwLcn5Jn0NC+nKSqkw5NKSc3dTfSrurkWJbUssKbIKiuWc4ERuhPKfXQPiPUA3YIiXJYgpmn3Je2hMiBUfToJCQI/H14mtMke1+lSE2NqUrnXXU7nyJ5xzuRFfk1MjTp3j6I9HICv2JOj34Irnxm4gtyyiycKqLJSdzJVyz+hchZRTiKAGcII4ta9TWYjf//x3Q9QouL3mt3+/soqFviuV2h+kujbb2KNiWqvsYqr9wSTrqGRXnWE62scwr/ViC0In2ip5wvayTVlsHL+jXrtYv4kkN9wg6zKibtzGxoxVCIYhIinDcbyD0EBl7iAqw5+4etx5e5OKGFIJRq/d9CmoK4xije/NsLWhLJup3m63bDFruARdKs5PdYI4B4KBJnvUXlWckzwiBkWF1EBu/og0TWNQh0eXQh1z0QLYhfLJk51cunMxgzTVOBmAG0Wg//w//8eG1QAiDgH+XIsBDToRsgxlCtMb7tyD4DsEzDHJ/wgW/Nps0Uy2jwc+vXmxQ0Dcueiba8eMGfMQT+B0uQ5k+Y8Xi8hPL17IrKevCWZVBJPq1H/98j7LTv5SkNq4n/eHfuyEPUfOcX7tWMNi29X0O7C1JNFrrhM8ih6ADo/IM3Vzr5cJoHZyw9AReE9ETQCCJKQPSAtc783RuyBACTcHMyJ3mdIdwyKLOjQYws7gXbfeAiqXv8fHelgyQpQ4AlTCcPkLefQDO4N//fr67F3HdClTMl/kpxxQX1ZAIyj+Js3rp4/edMiLx03JqZakRNiGEyWOqEuM2hOeWtLMaSRqNmYqLCPAldhAXxNelwe6iEvvzVj9afrlhxZpKcWv4YbkqogZeap+zcSwtaBA1qeFuEKLQu/jFAtDBxXPk5f1GdYhnUjsvW5kWyEsCHLVOsAwIL14CGCiUSl06YQNcQWCQu9wVDR1xbWuIbGz4lQj+t/FODP945evf+BeB0msJHEjqjuC0KuoREfPB8YSz8uf2Qey1SsOGBBZXPGoGcKf3//MlOt461JRQCkYXvttU9/++AOaV+O8yhT7uvHRG53NYPeAMwa9JMTQK3PnneiCRlSFtR75qMxU7/Ckbg2sRofQ/Ux7j1dPfgOZVX85eggAZ4avS0MlA9zzFr3EY3Yz6fO3rxQtO40DztSrN2c/N1J+vn569rB1LHndiTi2HHv5RjwXtiji39eyaIzx5cnKyFPMjQxMdL1bYY8ZOG/VFgjQD6tA7PdzKT3NojvAEnllsHFKuT5Mq6qLyFa0rJ5P14LbsExXfGmyHvB1BQj1Aq+Pt/3CyItca1+JRxZFLCJQpWEoFHx9ElQFcd6FV3Cq+rfj4tYhhBMTrpKLtozVz52GfYdUIt+5NI2YGaaoiG0yza22TMvP2Qv7IDF77Mb7rg8ca1goiqlUHLmKbp2ZkcNJPuTB74H9wGyUJHAo/LKExf2upHHeTHECk/99CglKiRMWgr/9g1WL0gP4p394dU55e8F1K+JAZvXDHJfGXpR7/f79+dv799YF2d4CnHSo42LEI2bQm1ucjaHm4ez1WrLWA7reFh8nx1Gos4z+85//FCXiSdHm2AWS7FXHNik86v/9v/93YtghnhZ0JXOegAJIm+TKiOX5jegG3rqwcd5I89kFkeZAVhlsePIsDszJLRQNvVtxd/95WuSuirfg4GDAqag7sq0tk1+OiaQpZ0xHC+DpfZjYF0gmp1XNTzKJHZ3haHeZrGCpIN5QqXi38HwWLOzrmrXydrbd9PWeY0167wIeHLt7tM3w6HIq5ZLpH1XwLxWbMyiW6RtQvlDtVDhTE5crmCrLDF2xSgBzuZq7S6D0BuqKYcJ1RWyhe1dd38bfah4h61UHq4w/XYWlLndbZvmMb6hPtAGt1PJj9o8DMsPeAQPq0udYG5Pq3Rju+uhplpNJPI1988ivzvnxO94lbNf4AtHUFR1ZAzKUzAvItaVKb21Y3IafD8hbadi5yO8h75WfeBaDBSQrWsQSwOUqLbGnTNQNP5W+HhU6htHrThj8b/Eadyw0AdqlDsmMnZ0Z3Ru8LthDkDM6jhs4gpJfRqkoBDfno7dni9HHH52LvzWjK2m0x0G+pPNOJ+AraBbQX/2CQL2Y0XGqrEnjVOyoqVh4xjbOHenam9tzExEPZoJWtSzqavpqW5o4YmXXizB18ZuwHfpln+HLxRpmCxY2/IZzQVZDd8wNoe7qb+vX5W0m6z9MxWTTqxLLvJKdZsIYzP4MnIkSCo/mKKCGtq9aiMaKMbj5GcfyU0tU4mEuSZja3GLg9cN7rBNATD3mK0VYtVFjJ5gLMsERhNjjvzSKaQvFSc3cshFkW87rCss6mLjIk6fPch+U0UgiTIsgHk+vdpEHuyFrSEN9d8TGNO9AGDVZDUx6xdKYtLG4YoqqCPgAN0yJknaPC4lcm0cQUNJUOlfPsU05kDmcaWzf54deT+ry4brSwcaSGCMOhq9SN07Mq9Kboj/qeiwxCH5YkyWnY5RjHrZ0jEpU78Uj+mFBfvyJXN7IS7yHnSedMUz8s+RpSrpOiGxgDVHTKTorFbGUCEVSiQEZgtqFLRGbepUrByJATT6cmqRrVEdTpdpYSCElEe4Gc1pi59LiaAtOaFkEMnsVNdiGMsYlSjGvw/spn2oAOKuvhWNa7HTwDCHa81qhoWnWvZsdKD9ba7DRXsCcYavunR+9XYmGN8s300uJo8eeK9+mN760mJA3D0KR3g+gFAsCM1Zyb4gbQDfr8OJwnIk37io4ZY4uUuH5eCrquqbP8ZZCzxWR9uXt3cUId4uso/hV0SHMppxnmF5Hxw8nSdMBuBHajK4WEnE3P6dNIlk4NsS5uS/2u2XRyYWzRUXX3QztMiORKzgCqLmlH/NdNPGsGRV+whEeASIYosa1NiXxxnMBzTAtJ8ekUYS6jndQZhtDbhUoykBUNnZsxjDB41js+L0AjCHtLxx+vw9Ih+D0xsaMbxS1pNIf59n3VfiCB5LqNSVU8StsUz+9D5Uwl8dxBhx3HniIl+s6NMgh0nUveeucdvWJ3IL1LuQLY7LeUinvCV3C3TMoogiO+dY+jWsyFad6lo8cereh1FtDKrnGvQLb/REWpYIJ4z2aIdYXlSGkknqsONGLhOa1walavUnuXMgczhuz7Gfu1MbcOmBPRGq/48rvgXk3gCZ5MtnfRrAeDMdxFRm7Csy7ok5wCOq1f15EKufUq+jawoKQvhqJuDhrqr/fXVo3aEV9R5Iquddb9wTFpbdvmvrgo3S9SzX1ru+6gmn9lpRwLIQLkL4Zhkg2gCfKIbe6Nzu+4VxBnyX2rnllTPi7jiEqeBxdI+bEMt/wh2g8nG1MyJ1yrp1LJqjb7YndRCZ1tBStQBnLdJVpAR1ns4diT+tkaray6A1xopSbb4oeQcp1a09iYGeosUwwmdctCMsjSQQlE08EhlY365S7dL2AzccWo+u4OjxGKuqOtvQjgowJW1I7/ICHlYndQqJBerj5HWFESKbWuHJEIZtOU7JrIOKxJHxxLZeEfykZFkb8BtRxGd/ZnNaqm1wt64/BQbZg1ADVIa7792OzaHHYcHz+dJ6WiBZBQEcgv2tSaCPGBbGypNj+9OIJi/2p24w+smNqpHvigRqYvUhrlK54uN+0P/dAEd2QIRWulGZFa7s8TJBzxuonEMOZ2w6E8oDoizvcoWN3TBIljZhX+TTkyZOzImeLryPJs+2hF1Jqkp7sJnBkd4GU7IiIIqd8a9VKtq1NYE0fBYrG3jXTvPSdpVATEUhWgMbEZzA1D1sik3XFwebjll0FcfN9/LQ8MuQ5RjMWLIabZzbczdoWdT7Mn8cKurfNmbB5Mh2DLk7SWYUCRo+id4iW7R8/cs2s3AapD+1WNgpd5urzU27yYdBaCGaGAN4I056m/106U99YRtXRdVf0ZuQ3qar9imiHv4Gbrkq/H6boXV1r04Vp9LtS87MtRVG/j2Gj3M8lkjVCnVV8zAkwtqGcyuq5SjoPKKCFn0Jp1kzLmkaLXUBx0OXflAJ5LAU7J97RY7D/jo2Y48ooWx/Vo1S5KpOlaGw5FgHb6SrKwliDrwXr8m5aMotuvetaR7cjqu8IN9uRzNZGlWrGvcez6u/BGC9aQ5Irl1CaorN8CDN+zEf2NNJy8/CnU9i1Ko15LkPGsOMAc3wY3FtLeBKuZGkwW6KkocvadFH8Dr1llqNsNNGMiOJPIxyOS/u9WmEmldLrhqCp7qGHPMxg5B5Nc6evQQDvk2xmLdozAGN4a8wMMAmtnOu9tS+wmhTqUqK5hbglYsTwN1vW62Ph4xnOZB2VKK0l6pNV2YJ1U24tVgP1gQBcBeV8ykRt1JsJBCZNFXF0VFC2rt10RljuTF6Vm2e9iet1DXxDFYX6TK0tiwA90UN3ocpC95nzNMRNljRqVe6M5Axv5EqSA32iFEJSaJGG4Bzl7Jgc6EYPPbcfeNuzfQCdSZ6yg6uM8AUPQEq9Ww0N2noM7OEJNWfO3Pf/BeeZTcTqdsXrb8BrFr1Awp9r/tg0WNDNlt6hsBH0ZDM6ckPETxxK/ptGfQ6lD0rjTz4oPl0INKfC+t9NkJsQ0ZVJk/eb2wWN491Gye86dg7ljM763wjG/hhsu+EMqerOwr3ux4uAM0uXPVWZk3OR/dj7d4/4DW74gw835e730CxdKB2UWAFoDKWzQcEvo2SJ1es3C2eVqPtgoNVcM1h9/7aczoW3rtnw3rwsiWVK1TVm52rdmcPqxYDcIMvdqJiWo/9ke7dFvtfrhDTrQXoc/EpuKJUYKa9oGIJlcvqaEvnCiHicF56TqBnBCDX7/Y7ex2Lzl6a0w43RTxD4nZVdYeSRNUrRjNKsXBjxJySmknn86YfskJi9c21ekcXFmgpqH1kCjRYGiEyKYbg2NCavPYqZW9jkeccwC4V3Xrdc7Fyri8gYYA4WZYsX+q4hBrtoT8RGKgmQQJ1CVjMP+ECjUYPEiK15gG6BWaAXRV0ZdDdWPkOQx70zBc5wq4QZvnfp9dZJMPbl0ZuHFXlBNl65ifblG351p4ucaXqZDTO9KXmKk9lylWm5Wv394FgGP2eMJlBOn7bRkQ1aQ1BMTC0n3TI8h9JfeN6bq+N4CH3MoqWzN2OuDOHCKXvoGIOGuUkQikmF4uf6m2Zli10lZix8L8tEXFMbPGgZKftnX9I2tgKOP3nUgi3vlM026rLwwY4R/dUDC7PuPEzs2ppxdRvRA99rMwgyPl5ma0aeeCxNyU3iXrQW9/eD3isUh1m/YYpJsYnOI6DWjB8/Lcwob42uuvGXMVJsUo94PU19vLEwnsY25VZR0sQd9c6vm/OgFTb12VMcrEFqeBOQzv4go9MCqwvHDIhZVdrfOeimK/Z06kIwX6Y3xIEcV4zJ6cKgDCpsVgvnklbacwwVqOjv5CWpEnyLWV9zqfZco+UkVAT833+84FMJeL5Wh2HGMC+sR2Mdys6zEYCGbYWI6DrOnQOLsy8z4cGsrBcsXxT8il7gc8TxLohUa2Jw1FxRh3/iVstHR/n4/OUbNcw1K1DNChBjnaE3hMoojhgUO5rdw1OHwL6xaG6YdfswEv6vX/Kulvlm+umlCzM6Y8DeDggXv01QPKJsvxtdYOeMRr9TFL99XYgheLnpfMa17+2fK7U+Dcy9l0f7W09Yp/QgM6PvGQX2WtQn5egLzLa2ek3sj7//nRcGwPu04saFgxDITmZz6T3sxZjlzmNP/eC75sOqF45fb3s1F1rO71fvYhLzmVdieDe0nUKVbcZjuHJiPOlSqtpLMK3GNeCM15ybiaEBuN+SAyvCUqcBd+5Txxmea+VSR3RkiaPijmbWOGxN3DjROx0E5YajMnGVnOG+5w0YIIgq+M84ToVAXU9dMyXcPO136kfTfxQgCtgk2+xhm3qjsVhhUAkDZ/mOoZy8hudR2h56Y5P2jhmFK52mEFHlPm7ypwu9ex+/xulIU/D303Yy3PDl3sC9PGVACwA11sW8tsUkTQYoCVCip2rUtAQkN9g6fLP2hz/m2K6ZR8HkwvyyTyOe6x6ourAlpDsfCIiVy+Yg5x2vqtfCriDHrL4hKPkvKzORIS/Ta7X0fx++bkk/eKWWovU6KgQIbgFKZLpc3qvYy0v+fuIcnCKYGdNLMCoagbmc13Nxj4OAMosITPEqk9F1O1DcRFSXUfSxw/FDuJe8yL6PZse4TGSVaksQ0ab0t/WlBuhKwVNFMyaCDfqkWJycUN7zIC3MKwUIRQEz1SGWH09UPEzCNXeMg0XRVFeAqIubo9m15noD1XGLprLtqNc0NHExsBkRjrrKa/Iqq4mj5SkNpZ+djLJjWugZbCLOSBfycByVMPyllA3G6Q1uCq4dE9UmMQZWGcgAyekqmp2DHP0RHiU4OWTw+iuwpKKjZU456t1Jxf3keYEPEcj4VUgEpJGRY6qhoEvX7MlSRgxdHC6l6AlImfEHpNpz1Nf5rCK+Z6J2AsSq4LjEDrIS2BYmLZ3WvI8YIqW3/OizAbT6nA3zbNhR65ySE4RjwBQZ21hepaPUBtq3k8ocviYPonyzkLG4yiEl8VyYVWFoUd1LvNkZL0rp8RzCtplC1/P5i7xNPa7FOwwUOcadPkS6cBZU2OEEt+VDLwp+RdzRNy9U0I/WhOQYfBOnCwNHxoYyqahuIs3HqZgZurJFAndzbzJr+tvFjposWO/gXKDUOJrO1NXr4YHc88OdGUcZ2Qj2mVR4mmToq8OZoTvqTcnZigNizdtEHM1RZuSOTD0f/2zgxg/f73MGK29QRCQHS0nuZkX8ygZBI8XCrgs4st9AYac1TCaSwx2dTclAsaiYQRxnIFnZ1xruse+allxiSrKwKPUF3EyVheypU27e5NQsQ2KrgJCK4uQn5jRptvBhnPbOqiY3bKfC9ktoccmfAapHl51GIdZeJdYmj7WNzvEGb7Jhd5ES2IZlleT0PM/MZENiyKx+igBKmpdThjwtV6mstjPImpAzdZYnt8/ybZ91jkmxQmS8zH0tLkyveFyHz5kkfWd+PBKPXIPk5XWWl6PaN0pgK86eimcdWSlvxGtnRqvlnaFaDkN6n6yeiagXmjJGMUVJVlxuVi+WjEsul/IrBkl29czfRlm9PO2bVrq6EJyL2LhofQupzA41eyYFdaMZd1nuwkxaRqATm2LiePaAOthWMGGAUv5cUGSXFQu54JgVMXGIumvgXILAkfsYMsHtkQyubOiVYObv0RJVwZmgkb0Q4kX6LnsOf32CGPkHhjUT00Jt+jve9EEBHz42FHaN4daCYi3KNvjuiEDF7sO4L5aM5L2C3kQ8MwVFxRHlLig0sW8mavK8bB2qK46HP5M8IVZuBBWYLj1GVA+WOE9Rwz+lYfDTwFF6mgVST1PZkcCjqRvvu7ciDoPFmfquWaqU/dD0OrLFTMWQ5e+zZ+SXlihMBuELnuOZvWki1xL3jgOl1KLGBEB9RIxgzdA7M2R7BCuiq79jxKKBqxLH8jKM8PvxUjfxuDDM6MqKgxtxaOPJSvT7YMWkLuJWqeyYbDmZ0XMAhGNtobCFYUqv2y6IB5D2jG82C4rYGsDYk2N2BCV3Jq9WpomPEPyry+f8ct5M6E853lVLonSFaPUpakJ2bkc0htJNXjUoFFy5vb9klY51TUn4V4vMu4qG8XA+igQu8fTb8YKKyRnKIjM7iJVS9y6R6vjNpyOCs7kg19NVZjKpaDc/S8tQRsTOxQmyc+N2WZfBFcFkdc66p2jSf6JXU0fRreIudJHfoxSD80rPX1eAsTlOECb9ca2YBupSeFJ39C0a5YphSiyxw7L91tAdo5neW7zQfa7qBtoSs+Nt6N27iiDCUSc7g1Tos3Wc1gTx1ATik5tlWvhji5vtfQSjzR6M4S1uKtkjhCkRaSkxC5Nx+9zve0KOjIglZj1B3StacuKEvtLmwPm4UCQSZUl8b+umgcgJn00JQ8LkS7g9P+hDH8bEhpROlR7woEZXjsv48sR+hG5YUjteZ7uRj7YvMA1d0zfbLmHcC2bdBAUlS3kEO/OTR0zppkAM2t0JEMUFuStYkTKdSrp2TKiiFO7ErTZFR8NY/gTyHaQsp7f1h666WyyQ7MKm0he0+kgRTsIfZUVMvxJfBluD7yRel2OugNz/6h9iuadxxPZINBjHRpUTuTwus6lIIm6lm5Z8APDsTKv4Vh1L9ywvidhWHJcU+96rS29mswRI+ZA/DHPoi0KfnXUORrZRPAtKOMMT2dZ7Eo0HZ7dCIG7MHnkS8Xvnq6Nj1/tfL77jXyC7wciGasb88uWRuXxW4NMTvJ9xJHFibL4i5O2jv33T1UfdVMuOLdthW7FMmaXwiyuVzIUkcfeasRdIaB1T+13cIzp2TjnuTnS0zwi3Pk7ME6TDr3LsqanqK6wy37fyoMyLQW3d2JTXhXMlLxAo4y7a9BrzEB1vFHsrlN0vB/QohU7NKCqzb2isGXNyql0zQn3jpJnoNToodiid9hlFgHce3zu7oyXuURsesisoUVrPp30ggnsYojRfs3VLxYxLBM+R6q85NYqHFpZeI5rdRIdBIsRhGyQh2nUuT7C5PlJu2FiYJfs2YJXqokFw9gLqGYIEp7LxTVTrUEQorbNUptn6bIu/ZT7N/kJYsz2p82110poUGZrQG/lEpJFEx4a4yiFuu1qExWj4gaLodhYa+5WalIpyjZFhhvb22qdRNUXn8KfxtuQYUJsxsIS/txa9hzi9tQpUjDHQvo2gsNhufBUFjuM0Bs1P7ExXZbW6zFl7rgcFoXdEVNwZoXi2HfHGAtCQ4+mWnvsqISpy4a7UADAJgiKxA74FKybEiOi67uk0ktG4zuit8WtOo+PWPlAYrhJ35JVmUGP/hKIiupuuuUbZbj2nht47jwGbh+Efmg/ubOqRQ1SfrjVxjdMRJcP0UHAqjASld5Wbf+bd7OO85/sWLDykdE1Kxr7fw4q+opPB5N7WsEa8xbg/UPwXXHy7V8SZpdfK4ymaFRRlzM5T4hEP7Lyu72+BrwwzdvUjXeKQoXIDJTlG6MwExMzh7FakQpghz2Ag0o0lOWup79pke6u6G3d0dydSE0qo12rE0/69YI8ZGXVDYeeWSZ6RVtA7POFpRQJCCXFHPFdXf/e7rqiRSvGHOn/jhDvJ6UjtjlLoubrMWa2jH8NKjNKWqdsRISG4vDgc/+EO5r84iEIKfy1alKM6iY9ejTWl9fd4ZXEMW3+i7mLOTCNlbOPLKSIFf+apxOYLWbg0o3hQ6BVEHXhGUBz0orcrrHorNcEbLQwr1DSNpy4aOw6ah2HNNXS7h8W7ZpPzB3bm6uxnusla0x35lYNt468s8oHIT7ce7MseJELHVIlbG/JYZoZN+/Dr38nnMdTGIxuLOksTyQLWHBHNCCYJA51FOZi+feHbeV+JFwloHGiXWTzc4uReWMKaF7/LlWkY67I+ZkVIKgJ0hzGv4AXGDTS/jIHwqJjg21hgMwvCnLIUCkObVb1aUuMsUnrVkaOonI7qSyuVlU3kMU/pRO4FRzMvGUyYzFhZA/12bNpRFAzbWKjsbn11xHSUBNEmw2IHwUPin94J+vniyWvNxdDfmZzKTJkgengQXRI6AzcW5XqIwuUnMwQYpxFlM02OufuYTGtJT1YWDi0QcyHzMDFMJuwWmAYtEe/gje0wV526jzI4eiqOWaTA+oYOnb6qdYIiYA8FJ19o4yZAB15XvJj6eiJc4X/UwWJN10silb+WIof4m4sXny/5+f3PzJwOc4QWu2ZAwMldpT6f6+V1hf8qKPNxhAkRFjeCDMrlkpfhci+Z9jyFLGdXFuOSklHIGMVeYGnVldH7La8C1STONOgKhenWtfDqypruhEFrRhtImDLtTSZfyZvbNAhOiUmlnNOez/tBGe5rRIbsGFk/D/Q08/fH4rTVhSGvH200zMmcEqOXLx30+NHAxUh+SAkXTvnTEolXwJcrV/yPLzErOxeiCURuqqSEO06dIlKIeByRMBFP6rV0ikwkxisFy/KwBMMlqRKr3mu3bsN5/fefmmVPKA5UXsXIimPcssTSFXURrPkZPtl5NbpbeXnxhR/kw9JliMT2TZriFFORoj2Zo4stKjI/IrWBdutDeaOr7FMagJtHfQbvyIuJaKpoKhma1u8uiiyO9GKj6IGTIm9I/ZE/REg9ji/P+fti6j4beN9jio07fQw7T1Qy5xW4ZIlgBk2P9dhju/wpuk7EcHrKY0A2wFuPu4DH1izVX7IE2Gf2S9EscMiggt5Rz69uo+QD0/0PZaVbEs83yJzI9AXRQLg59+XLPlYm3P5mSH1tIvZhLcdh3I+0NbtDv/CXslWXF3YsfLU5BiQImQz+Ekvq48wZ1Qa7ffc9uw4tHmMN3/u4oBQgXlmzTY1JeUn22bdyJBhuRmzqSMGP/hRgvyNM9CgVkcak0Tl5AzllAXFkSUOaaPeUs5H2XowIZIEuj4GIEjPhKV9cRyJStQRDZrUkzjeESG5r9E6qTk6fX3xzWTy0vHKaRzsmoQNXZ8GogFFKOwf0deWX2fjzRx+10WXmiLn//vpaPle/4yiWb3QZ8QiV+sAFZF2UVm+xfZ/ii4ShJgtfpm6WSCHJ1Tq7H1IryPzcZoES2ujPsT+N4ZYkY5OpU9kvX/O2c6brQooqg+0E+35KHOz+6A741nGmJiZ+xoHn+59f//a3zbKId2nzGMw9WZxQMWbgmN0BevrSLwhsHWbC4JMhen3Xgq/J8rkI+dNVcnbKN74Mh09KksdR6hacls2UcxoqMwZKP/jLPSLTdM03avkbK9/y+ZAZKQP+/ve//3//7//jTSZE/OyPYJ7nuveX5QbnEmOXI5aJmKdXSnUKZMrXzedPuizO7wkjtQByX3BUHPMHcb5/d6bL94liJTxnJglUE32x1aRIczya7aI9wd8xxBCy1Dtm3DPyKTtj4ySVHELpsrJBKng+dSBAWa3yAltesxj/evFrbk0CAWHHopNMb3S2BL+TKel+TCippuodZmSVS0T1YHL2jh0RP53fGMuenXBoH06GmQ3rAhyP6+aAHe9CygKq+R5DnIKcs+3Z2ngUcGmJWfegxIaaFwv3o13ijX8qI178Iy5vNt/muz8w2UjntBleyXG9jtuPAbMnsz1niG1Vog1P6LfGJj+Krpi3yl0f5fG48Bo8qW1Vsh5+6MVVN5XI1djrkpMNWTGTTTkxnAvHgzcouqRESAxoWDQkvq/AxpAOW8LZyxVnqdrZFbo7xgkmVTDl5QDFECrZ8ikWi4uy/WAmxc+ffzraBd+qOzSZ5JFJOQlWdcIe3P+xXKsGweytutbQn2nfLIKTeELoRgNGbEMZciuaOaHWBmMkAxXGxI2q7qzNwv//W7iWRXu6uqZEnbz1EnzmZW4T4Yl2H8Lo8EdZy2zbsmU/RjDMvXIciC52oWjelqgrfyEWKrGE4Ha51eof//iH1cqa9eP1+/Pf/x5vnS4mLLmFaQskii4qalsXmqNsuSWZAro1jgKD2kF8j82smRtwsF+L2BUXCdFR8ZlyutThjL+qG0Og+cvJZ2COVfPaUkJb67N/vWQVtqXp0V5Xz3UhJt/4NYTMOAiytTdf7vTappq4tXtLYXN/WhbiAMXrIiyZVg0x1GqMX03/X/4khlg5l6B7UiMZ03g4t3B/UjNVb5q3SRppH2+v1pWKv9NjWAsoG4W77haurlwDjqGm6PVbiZRxymcV90HODX1mCEqjNCRc8K/VM5+mamHDzMioxM2yjfmw6InH2HJheIwU5DB3ByRFmHMBsrzn3jNah3zkgEgbDSFyHDXLRZ6CTXVvV8qEfhBiVzRZhm+AKMokHME0W3Sb7Meq+CltWaKPFpuafqkppbUaWEoniZEGx+IY6pigkiKb9J/1pUWNp5A7E5M+/B0IGqgCBD9TRgESnID1XlpoiusD6Z0FxXbPemdRMIOufZ+de+1KxjMb/1QLTaWvQ5Bb5oX4cc2VEv4mbhzRVSl7J70uBTMp7gX3lp6Jlsdc4UT4aGw9IShS0r6FnN8Ga/rv43o5dbtgXVII0p6zuhq3rRR2pJoLgb7APSjGgLhBDXozcuhaqxBXcbzVlxEhw9tkOW7MbjcOpkjvynBu2OAUbXvLRf1OaZ03J/Ewr6C2xwHhRr66I/ZQ73ljTF0gBDwM3exnvB/KuBAy8G2o+02ho3o0t7QZeijbxkomwAksp3MlIY9EG8PiHM6i3QiPmAn+ZTj6unbED6G0o/GGWnhPlthNYGqqjZ8gTiUG8FQyPYQRpy4cp3cKepzMrA3PQ9H/0PotOOhZLgUZz8WWWHi/T3AeiFevZ7I7qzxAVl3svPTOznp2Lg5w14yY+S75WL+pIz50RSQ74pzLxU1kjTQLAfr8kRvesz+URL1xM/q7tKw2nH47Kn7DGXybR/EAw7FpRdFKF1b6KhVL/Bj3c2l5mNAuTXQZOD/FMYX1PSpKPWYsIOeYuJQtdhZTSk4jOtvKHy0KGbmqgp6k3StQufEQ4qQSiOuDxjSGfnXh11VA9FT04lkEPD9QVwa1irrefgDuy798t/KXL//+17+evnz25fEekQj7TlaxcnBFzL5Dxo4IaBXHwLdcjkW35ye6Ztl4xs/UjHVeLulzjroRTgP089ePjz7MlV3s5olVqa5FFKa7YvRMy4vvtGYDjMS/Z/VZhDgbk1EhuU1uV2ocbCS6o4CNX1eC6OPGQX84aU+arAGgku+/ssNIyIzPT++/XEWwoUy7GyM3DF4dRC5G2gUuxtykPhbwAkTkcQpUthlOGL51QCMnZz8BSCjqSFr+DzZLfgLphlwR9AT/veSKoOfxqSXV5kvv2cXwhTJB9bc5PnnPjpHEk+6ikUUk36ekbsSiWN0LGXBydmMHYi+gjm3Bh3qYj5kZgsYh4YjSlaCmpJXIq56lMIRcsuAI/rtIOiDk5pHqkQ0N8RxVFL7oTTxb3JeLL3kRUoIB91tTluUeVuq1QuegfBevilIVmU5YNI3XAawBrC7Xee1AV5qwcjvPWPugy5Oz/W4irTdenWioeMRc0+k138LZdYZ8Lsm9L2A2dFbvJBE7FFpXycyKwhiX1anI4UdPu70s6UY4pu/u2BGez8Wf//dODU6UWKD9SZSU3FpS0E2fnF5jrCuCfDeDUpbwuFVVtbFqZf4ZjtqdmARcabep1K6NZkA3cP4qTyLQEcSLiJ0ifymCCxHpFopeAI793qsNSacobpsxHSAU539HQDF0l7I9rTBCpGeo43hWccR/U+7mKINyhAzQjhZ9u6dwsuG8Yqd1hjhnOaWmB/cqIVYRnNXXzJkv1xIhBiX2XLG7+f6jgg1ObZcScWGUMapT+yh0mh3sMa+3q0pny8WNM4nW1x1dBQyWLnDpakll+GrXDGRBfg7uFoI2buKlApvhuFswQANGMeQr6lHdexwnpBPIRiELloKQu7xKEVASE01Qzap03QVPw3IYLvqculr9jdSisXua652guJ/T1F/8StMqjfe38eUFMLbdDq5y0uABJHQ/5f71Jj7B0XrX3vhgC2e6omz1n/5MlGcNfU8RJXHY0pCT39aOYtWSSFl2q27iEempwmws8mPypJ6bKdu+Jeztram67sLUZMVU1MK403J+9V5nCB3uRCD8WcFjbWVvf6dF9ywcTjiveKKo9oiWoj0vTrPhyhLbfRbZxVxFYSo6zjUdN0aWKnXOOl7gubibASqrr9exciF69GdL5Qa/Fem//uu/vr/8GyXXI9aOAW0RsYwSsp6NeOkQomBZg7OiBzcGscPKGFzudgAAQABJREFUIEQd6DuMPe0suPKqs3o+x8Pue/x5K1sgCAWKAUHDCgpMb7Mk6FWfcTr3SjK6oEKvQauAhQMZXveLmYRKdV8LUFkHmZPHSoKYODp0vIecJBP4bBslaNX1MOYMiZdeLjPi+xAC06TnRihp5jQfDfyKhf4b2kYrdvnaiVmS/dNEHOnKOTlGnvlWIkLtGe64TyjgnvMH8qLKPB7t1dYEp5MkENRG1jO5nPRyrmeT4W7uEk7c9M/hJmIs/70QfCQkFMRaRl8c/8KjXxwWtzAENsmRjEoK/V5mc1aZ/+jiS/ZoZ34mjmFJO+/3Epx6Y3E2wr3V1UG5DWvSeoOiq8/sn6LAdbzI7hl0lh62f/ZdBDX+ugGXSOZdBEHy8CTDtduD8ZE5cS1fP9vfOeoGlL2k0myPDx9ss6Ove5Cs3TglWNzIZXKLPT8CqGM+ogcYjj/ffB1Qtl3RFa0UyITGYVGp6QXZRsbDrWpF9y8KItqHPwY/M3ErctD8YLGJsW79+ukdgOenfMeB4rtZEvLmmmTAXBVZmO7cYPIswrdeFTmJzuvs5uyb+trQ6INzjD29PaWCH6aiYkGMfVun9LnLZTFTUEYkhlUXI+wR8t+LZF2qMJeYd3lY43t2HHECXNFUweOIrsTWRCH9tMTkMugA0a7re2NEnK6WcNsy525mWbrkBGMx2DIPOdcP0ZgFq+GLmJKgN7Zrrv5A2RKTW5gXs9wZr2O1Xa3oT0kqnkuttm/MmhSG8Z3OWlUgcgKSQI0JoNOs9oia2Pyw34u1hdUlDNgzELKhTxsLnAMJZaEQ3jm7wITeV5Mfm5JbzgF0U+AMH5syLFVtoLPnpSwZBYCnmSemxKt1DTFXW7nhLA9EySc/fH8zei6KpWwezGU9thgmKe06eKrXMVhrZWFhGq5c8sfkn7n+iDfRtT7HUXzQ5LovMYcTFtaKWx3fRHFcEDglUGfYSqwCYXdu7ksSlcK8gZDhYbiKWKnm2L+/qZ7tP57rD0T9++XPBot5/dkQeJ/UQxXxB9qkzTQjfCEDJLXjUdXlyVQ6zcqZdGYqTsTY4Hcbo4QzxJPPGMIj3Z8tkBKyAbmmm65IN52iuIMd/oeiqSzQcdOS3N0ZNdHYH3+iy32xNKVf3wgzc+m6nnpf+YyDzy0wKXknWNr6KI939eDstjDMP0LoGbWzXCQdEVG2yXL87//+729/5LuReZJ3qejQzaRLJqtY1pRs4aNmCx5OuQBOso2Yhzv7mzxPnz19dCVGwJDhAcfqDCScT59clErr3Dqxe+4jjAQrU9/lRh52HC0mQwuElSZxbjqKOQpPHDOefWW0H1bv6PJ5OZ44KLkVEdvurwPsEvn56zcDsKyywuODJDZPT/l7gln8Ua5Rl/cAYkbmTyYW7vMjynE0b2ORi76WLcTTiyhupglA33LoY03JKsx5VJ8dHbbYWX8xK63m4E/FBfG6EGPCuvyh6fARXPLFtPorHmXGmcs6xIozMeN6zZa4QtKVaSdhoIKQJQl+e1Fe815UHpD6cgVe0+VPwHot1l15+4Mc09ujb3B9/fWDBIoXaHLPI986bJJ/+PBsSXtKDWfeZLDwvOXlONvTRHLL3KmjWL5Y8hOWs0f2T65rfHlTMo1ttTTDn7ixGcUqf49U/EoRhAxHm+ttwl7XuTj07mTT8fK9awlmcUKPYDc3RWtwStEcZk8e72awIZmZ0Vz0Tgwvm3tSzsbopg8n2RrMM+Tp9cM2wZ4xGeT4LmcMqDdPjl/Y+G64s0PqWLeZGG1l30V8J2aY9Na2GVBfA3sn7WzzZ0HDuhxofJihKaeW0mcDKIEbJbfAl1eMxAaNqjvZzP54dwUBQ1aDjA7UzGLNgnsPM+uMaYJOvELZsyJaE1Qyg7phkh4qeDLtdBQ9C4emQgBRYcr41KPJVa0I1qUEVJSq6cU3GQqlk+Z12wvdWkhkqRTxJFs2/0yL9XE1MQ5E3cBrEEp/PxXgJltPMurJlQqT0/a3W2eYI1iyOnExKnpR60LidY10xq89OwvSB1MWBHZjn1pEAWY3EMF1nX17rJVrsSoxCcOOFXw8NC0ykBwTmoq4l53NKRtynCl1sBixWsmvi7ghKMEmpbOrXeFT6c9C+o4w2fRfFq4OeJmRwOx0nTxa3Jzm9GJsMCjKaBS/UyGDE5XRGx7i2U7FhUTgkqICBaJHChBKF8vw59LTiWS6k+hWnRyEMQmdVA6aNn7lYB7q6UvHXh8rwubYiIVqdaOTas01yIwBG7PzP+YtVbo8RfByLMvgQcarUV9T8XPSDz96KUXy4iicqitU0FoEO7ytp1sZw3b0lRnn1ZVcys+VpVATYDu2KzRD6JWd0exAHGVVWtXbVVElaLWrA5Lzdz/92h1NlsL9mOxurNfrmNEhSCVh7kJZTM2h0WYeLhSJiWJW9hSp2oAgp6QrnefDed3AxRxEx+BkNc6SdAchyF2YqkU1gGaQ4VO3vJzvt9JIZGu0unDxjczgCFCQRw/GKSsGlgN0qYda3LNZywqqOFsaLd7kO39J9kxOpNmZdN9gamOOh1sgymEi0bOuEShNJS86xp6snbk467YFqV5ngLLROxkRQwn56bRMXCntM8TsmGjMSa03jKjvrq3R5x6DsoHbqFO3cNsJxIYaksoKJnuG3g7KNIttAY4m25nYwmavOBmMK8MyE2igJity7cwhQauuAcd6uhKcLSsJ5iwMA2YCPWZxPPHZbE/e21yNmNENMlM4lY8/ZB3M9ZoR8vd6+xnJ3pC5PaNyxsSGh/Le2GKh9zbjfwhM3YnqlN7pSWXIqSnppWRbm6Ddw7Rux5qw0IVmqNoVsY7F8DORQj/rXSxNQN2pw6YnBCBJnhPD3EPJqqr48Kt6WeTHsrxoHVAiKRm+rnwbMoR+5XcMjk8Zx0Jgjd40ZVfMn6F+u/gyDJKhLgey6guR3a5ohDcX1clPwdiki/crsdFWNi7Ub9SYJp+jdh6E82gtAaLh9CkL9HMnGvPmuw7JGg+Y1AkSIDX/sbv2vxb3+CMA7gXEPfMjc1bQow3jJ5dTmUYtbAxcjcg5O3iJ/u7lVYEdU2dTb0wRwtPHUVOvHgTAY9bMclsm9Y5NOLMPokBXbDj7tEQ3lGs7Noiyny69k80yQlOfMeXKtyI9hVo0Mjm7zmSUEu5aQxAdgvVx0Ql+gI+5etXHnHWx/sfoe5bG1SZZ/cA/kUB0k0zE5eGfL7nUOioKSGlmdQ1wTJlJ5Fwqfj6PvZFjQINTliaHmrJR7/BO18g5XrFW0wpCQWJVKpSf/SNrJ7VKe0NYVB1D32O7Ioz5HU0v+o4X0GOTeBAS1VOGGUU9i4iPOEB55Em96iY7ydV3zFCqXeXmF7oxb1BWD9SMvGDRJxpT9/PAgyLhcgn5kAb4SUVvSyZtLRxQmkXUOctVwJwdSnbSybP0wsH8kN6b/EdwmBoKzjUdyw8j4FWddKtJ/b1BTAxjRV7BPfekju86Wg7C1fQ77PtV8EFchG72a0Ngy2j4qI5fMybC8TnX2oqYjQ+lguFlcMdLPTzOVNdf4dtXV0v5MB/+oL3HGbH35eYsdySMQM4ax5OitmyXOLtGP5ZEZQqisroruTNtu7yApVNXvGvR9ttxaZDXGnSHrWpWwfHlS+7p6OIS4n0lqb6LPr1kKwU8TzGuJjhXhj4B3bXpx7/dnWDfNYYMtUd7c+92FqercclZhxtOSnq6mWHW7VjGJgIiNLkep75rq2rzxzVTVtk5eYUuzKDYmTMYlH4GPUObaeJ8G+xsRfdcZgnNjoRApKYaRC8zA5aI9XcWEchKQPjiQcK1S4+eejfeY39EDz8NedOvZ+yB5hj3mRU7AxveRC+DlheioiXEY+SVXsaRJT39ZCLF2JRIaBYQSMS75kLJ/XXRlg1NCMGx7aJkcZyZtbneVh3ZlZmUOtOYV3sO84JD7QaRH/U4NiTAbMOdUUQuWhx2Xy+jEzeTkNwrg28g8zuDjvVSGvFMrZUNH9JOG/zNfYaITWPzqnU4Vr+cIgr+qd/A0hdNYpiyHYqKZu+dZW98mbqJJLXLKZAMiG85xLUMSmFEI7YBC1PHIiJKodwWVs3CUBtDz8OJTpCaHU/6jbbvGxSbrYwsoQUnEQAXyI14UGp2jvEuNyLbW6uaJFwUl95CYah7URRf0+QyJhEQsI1LYCRHfinRXov5Facg7L4k1PobsJwA7ojVwhgY6aRV2IxyhypScaO5rPdmGM/WpTLkrpRiVMnmE5WFWBf0eLvjZO46RHVER2VGjFmTEVMJWnOrlfrNltHagCHR1kDfBgmdoCLmJ6VBx9miPaiEoJ4fysn44MVjTTixzousvTuL/9ILId9Shgf3LFFfHGtnupRjAMCc2c9O4RKZoGMXmuNR9F52yrwhIFaoiQj/wHLylBim8PSycCDv5p02u1rmUa/TL4zjdbp75kQnFBtOjJfmATpdl6keBxgnw0TUWZeIoRK3cYY489qO/GOJvvecXk9pIc62jYL62b3W/Ug1/BSpb0zxTO+I03usvc4ltwqVo3pq5u8VaggZr3aFs9b4da6VihI72+N39DZz0nO7PNd27KJQud8OMe9KYDMUjp3CQAJ/WdW6kJ5YyewbZcvfOBEBhlk5ele9KOaUS3i0nlrSd+K8adgNyK1m3eWIg4F8Xzd/06KxAn+ZcFIyETyCOaFeZjdcjGDGbwtTgnEG1AcAL9D8ri05Gut7uIMezBy/fMmHnzGUElObDllnUMA6qrdJZ15XzfqyjnKHTaUcMVTFMQxOT6623TLq9Ha0N8GtBOS6aadZtsToXN+Bu4ahUt3fAm2J/Jb02tcNUmkN9Hgi3vl0Ylfz0oXekTbjuHyGrCaC6LyNrtSNmbwVfcUVkB/Cnl5tMIrDyTTD7Ed3MoTrh8evMoPtOLB6N5UyGLEwi3Y2d2JFStyEYFfQRBorlnQDn8fQLSGfGEJYCW8N1ry5YAIR8Z4/M9jpDGNnwccPr2CymsdEQYmgJ24ZunA9HkU4XNd5rzG08WCSVd5vHfPvCk4wAnLbc+JcerU1aGlO8FqCAzViogNjBkpDBiTAzAgo83p1kxO4nwjl0Yxeu5n6MBcWnxhM9IrbbdgqPixdOzN2KCManrPv6N4nNz2jNmZnQiuaSnTOMrmRp2bbciUiKQlj5ir7pU/32xVo/Xoai2XzQlZ4DTdJFadSZKDj0ZjfohI7xSvdsaJWqdhzdQM0I3cdGgb6skO8+bmVdOVW1BUiR4WF6YrGHQOl/HhxLZfIK5m/zHDnNeWwpeOIBLNLRihhFfV8LQS6yyxEFbF96ozyFUw3gspDPYD/Q+kse/FtEDUyGX4W1nNDLBDnwjMDsztf0Yr15mbAfDHfZpNFB7eFU/o8rmKwNjAq+S6LHy+eQMDBnCErSo623NxeQnA7fVkpf/SponPc1As2WfeYvvtqi5YY26IVHP8LzsIbDTGP3lIyAGD9z+JRP+tJXssgmsjuS2DznOrsLKzhHbMOXqh5vYNsztJZppNan770EiAqTok71FF2XYpGnwHNi3wWseuPesTOTx7l5157YcOWOFBArxRroHppvK705rpUPtHu9NDEwetk0PnJAmfyTJ/ci7FoJSlzgeOYj5jkHhSQPRYg7d0pbjnpdKRIb6Y1nk9fuzR1soBKurgE9j0/Po5j3cpSUamMcpb2UoKQmfR+dGGZXCqlq1Kk6Nxrc+gZLMjxLfFMPRXH+BEfs/hmqe3KFSND6rkwvbt1ILIKflFN/Elk1eMdlgAdqDzaMNRaSn1Pn/qSWdibCVyIjohHEIMQjBBFttZvP/0RDWaJLgZZ7V0xcyNztKIypanCkN6eh1+90QUXlkqdrdlpqEQ2/2P++0zBPSMdmQQ5zIrfObfKq3w9UUmxtdbHkpwR9y4r6nGkXJGVPzgE9vfHi8YXbFVMDbPjVO/NNbc7JhAA2oj0nae2fuWbxcOWnQjKiaRFoRayxjbn+iiYfkouRzIWrfPwoeCJtx2IjYXVpgE2thuqREsXvZ4l0mhEvoidNo5sQh5Kx7h3wfGdjUOMtaxgzt2yD+d+Fpurpk6y8jY0mXgmfCxIhszCjBCluhOvDF/SNAtiPz+onnCkKxmgfMz3NzW3LsronVr1qQhEuB/39poFS+JaFjUG0PL6Zx901owAiljruVZnTZkybBYsw+C1jD0YvdaLiuDKluQYEKdnpMTbMtSEAOzto6Y7TpgUpZLlIMsEcw5xNx0Kx4QsZN5Z8hTpXcOtKhMvryrnGyzyr1MpcckOYroeDCPGocy/YoanFMieDhtKji4sEiSvqnhZrI//G4pYmp2tnMl7Wv6CcR/xRWcWyfVmlVGrNfGr1G6LspiGni2SUeByv8HKHLqCnzizPRZmaDp2570/mSCqiG8/PCSJ0QkB/jlgoTFANT0ONlsClZ1+rwrLKa8Lm0/AiRvAXh5cSZW1Tvp0ULIUmdjqnd5uYeWL3viLx09ibSOS4wyOHafoc1+LwTMvM8VmIHukpN6rv7v3H/4mE7qiB02ZdypZyDxQ79q0M7Gl4fNHb07uD2JyNpGpd+IeiSRqRz+51wkSxBYjkPSGekoWr3i0yPWBAHE2sDB3t0yTfB0ein3ApSuXZgqpoQxbqphlI+ol6yjOL3/+U2PrSRMsa7/IiGdC9DErhkEh2PB/eHm9vk6rI05Qbwayz/2wZQkTBNSE8ZfbrllBjkPv+VDEnH+SSbhnQdkOM6kOX2iqYFKjoY154vjkw71X0VzB4ozBpszJiIOPoQoHCpzovHOzMAOTxQVxA0YR/rw9EFJKKsXMKUj0R6l3g6NRdmUMj9dUndliCjfn5GS+XiP3VtNpdpppcuPCh9yT/2VcdGb9YkLGNKdDv+yke+zZMFsSQj0lBKp8vWXA8ywlSNPl+i4Y/m80pWS1N6ioivxytOeqRUlQG6rYGT8irSD5v1qPhthvHrXF/cTJNkQ7bILS33C747Dmp2dHsaoUwMBmDcsqbD4uJPyt+7gr0Nd2qu8MVusSqIqmEHp4aUi7ggbTb5BblDJQtdPbazE73F3aoMTZzETVGDWvcgrJwhoLTd2OWga6mmqYakrq0auW9Ns3ysYjMU9ByjRofMKFLzJEzot9DUdyMPOQBbxwnjUPkz/Fz7qe8Lrvzc7sQCOudENXsGNDot+RQsSvZSK4skKU2ygJka6ZHd6UQIUYtvqS8x9RhrQv/YUNlS2LUKmCHO/OdLMchCGxlrjF7tjX2ima5eoz+72ZyZohE4ebGDaBuBe73SUU6E5VvVm9qFvJOplsGc6hOadk98OkuDLkjCbhoO1vKFyB4FusaCEWBQn7CXebQZ+JKnU25lYiD+ay0WoTET+QqewyHpOG5ugrIzTzCaWcanK3Cwj6NRzkllUZ7YxKP3N3eEhSZNJiqTPxLBp1NLND7syxG4jrHVrdmNGzJqVU6KSOemk5kPWf32scOnGUGAMujpTeaTbRIjitoo9w8YwxcyIUuFsujxXJuaiKzMY+1mVhCGC9Ty6m29E3QDKvs8fwd7Ngu9OnouWJ7AyPIiI181D03bZ1oLKlKHLo8/qHL/grG7iWti5/L+bwtx7mmFalrcj9OQ4wla07XV+kBsoZ0AhuHIKVgGeYrhe1spxlr+lmc8MWuWPqojdLGs/Qm3Ugf76YgxkUxZtKMcxKlE9MRl96hIRUSs4trMkpAznhWrAyPdgT0V5+DW1C25F1Ro09gsT7NLYSVZ7zXPz79OtHbwxm2PXWnkbA5wczfCycIzVIXVmSj5Bj3vPKHEwIoHSKabLfxAnCVXripCaTtoI9GzJjgiOWmf3FyhynNOvXx1xLIVsULlUBmTEDrFKOpDR0q74fwXoP3YKFVLRsbL0R6ZQNJ0FznrOP7ymcJlEZpuPt9eD4Z/VAZJvePOOqMbsBVCcyasw4BXqbnZAPS4/udcWUDIHTVBy+ZVVWKFahlUgy8SoT90kdDHs9D2UFyy4JCabeY1DgZKtxjdmgDGNObV9BlyUiS5REB/h+2vdO70koqlPM+ROy3EIZSd/xvdGoeFiDVsrFR+uqOd5szc+LkIkUwZtxJlWsgNckLMUhxMXqzPBb8uJ44KEzNixKHYhacQ4E1M5zhjuYwT/FNN7Mvgjh9+HRxyZKTUrXKnevSk4HErBXGTgW5DCI6lari/td9iFoMPXvqLKUDaefOZV769a4awZe/DFmyEM7zKU5JCRB7mXZOVfOb/NC/p5empj/W4D11v2mtJzMBCsFr8IwqRHk20hYDeIdZ12Uc/9ocVrKslI1jrOjXp8snSM9ko1O/28V+Ds3wOlNNwroDUezF/nGKP1uBQXzI4Npa0pGRaTibN7FcgPOilscCIncFohc3PXxkb7qwh9ZS0m/jEB9UuixqW7uGPqDSL/x4N1OvWRx3kvHPfqI6lZZSx7Y2NYyFWngWNnoDWvdFjhNHjrige66VJeCwqJWDfM5qR56ssBPiP3CgwzgUVEBh+8v+RJ7lcGOrP6wqbUSF79LipUW//WSQW6ui5wfyRzZRIp0/ptF+TEWcgtZybxKV9IomDn75XfyR8HElV5H3N+jFJOLiHnGz+UjXuQOTzM+10XvwYDOjChuKVuuo2pjNTu3NANrcZjYNebgp9qpdSAT54293twCT8n83mVmxp4Ip4DkZ8YVTz3OKplGgT566nwigr/9dRZhF5tIi2StoU5PgFtOM1Y79SENUwQunnjalIjB289XMiDxRYm+Y1K6hjlS+8M2rztAQQxfRDqGdAbtAiEjCFsaulUML1hzP78SI8xxtjCFymH3CnXkHc9oOuEKOj1aPvKbGo78nE1LUPD2Plrml9sIwY0RKan119seCpkHVfuw++4LcNn9UYI/wvmfE3xT6lByqZuO3j1Jvs4flFiVaFQ49KzElVoqlq59RMoYj/BkE9We5FKX1o/5coHkSEoW5cQtTfM3U/hec6MgxfeIZen4tUcBMcbiIA6+BIYLQYl5lgu8mafbcCEmVnHnGIuSZvlUlOG8vuWjgaOswlRsPnKfe2BKqYejsU7MG5aMVus7B8aEA7FgdGM/nnnc6E1XeMNdQy8tIWQR7Dxr5xIiIvf8icb9QBBWa6WxrGNszsLsHM6la1zgRJwIhXGnabAAHbfozRsNsQnzFG/UY7G7WHkYF7z6PWsZiTEB2sBGKrE6ak9MF73CvrNdWgMuM3uTzjobhPdyGeN3SwAjGO8OKa33amqdVLUK0CJvnF0ZDnfM14hgv53lu5g5FnCyGocCai7odlGcyRxV2Xwa9FDQ08ria1bxpY8dG0zJ4aeRjxXCNTPeTRpxXjVu712UdE1EIXXo6plOJtV1Gm/HYHVF3VUy7vnJGVmgkTdexFWDFE9W0onC/rpTYoaIatTYl9Bl76CKOf/v0UdaHRVjhXPYiT+1rJFhiqQpmwVCOVghFj+6LvGwll5irZg4okqCeu7DxGqspQw0FBrZinkgC0UHPZrfS3jzPTG+KOZ6xz2O9r5SAri4lD/m1qxMugRimVFDa9VMsr7e8PrMyh8+RN0yjxrIfu4F8WGI0QcDW+iU9iNnCYHz6k9sX6tYQbYlzFPgRnZKHo7oWRTffpjD6oPrJi2f2tGskoD7P2iVpn7H+zLuvqPxztN3hZ+/ZGvKFFC7SdkpASEjskUxFCWw94qGcqYootPX2y5hOlS71Z0JlkUmcr07m5QxLoFqjiT8mQkcz3dsusea1b77KVYncf2LyzbDpFJBT2QHujtK9qtV2mNORgPPr2iZ5dEELUcIJk+WoYyf01lU0NYIEIm1lQ1zJIoUjaVOl2q2jazN0Z6BpihISltqqzSyQ7rwgl2pMhQ5MymiOGNGBpGUp4/ByX5tRicorVK1U/2W0dhEklqS2QgvtxLwmcvdciacpTT+Bsi5RibQFZtOlxaNSFEnNsBlXWxLj674lUWmpbQoR6ydqQSqe/BeQfTDtPU6dAKGMd+FM9Eghl7ETLnqKFq8aslwp2CjPMzzIpcbNb0Yb/m2WLUwJ4lZnhHB3MDEF4+40o2I3Fmf1k9vAriHVebek9YbJkMKLw98LqPuRcRXM5uJjV4SJbJ+JdGN5S7u1JUstPndHe7ucIUzpsWLjFT/4EtWAJHJc0PbLufT2JBQ+PbRfIjNMJ23YeN+7h3BDXZgsuHo5U4ik81ixzRa+kE3TasExKwY4tU/0bQgTItjk9irf3mGG8GW6A/GWaDVt19DAaP3PGLUEVsZ20zSnMXQ2KOOTveWGJTxOyaxunilnrNBwqQAatTwRve9OcoGtNML871gJQaV3/VqZJYfy1TtBijhJg3ZSmqagVCaphGJ6ocJwwiByCXgmRvjsXAHof6CjyLaO/9rdravkDGnKZvroHqaG6t4mW+OrdF/PWQCbG6DCHjYsg/3vVHVGwEVjTEUYJyDL+FTbiKQyiAXBA6UWMWk+I0tIx2rLLxJr+0Oilrbkse5sRuE86Oe+Zevi6kIO5KrYgh7W94slOVJfnqsMa+zYGXJDSZLHBQvXoSn3z7saLoS1GdlWL1XN7HlpnT9El753VFmnf5FhmSGzA+7ecjZrMJ09NFNHYveeJXghb+S0bCcacDNePPQO3BeS5k9ghYflV3tRJperjeGgbxLAktDBVsNM2IW0uw0N4ilxIZbtk/rY+uvfG1JhkPJK0reUD93UaLvQDKmSjt87AIVNJeggdTFubFOH8K8bJ7nPJqSTWL5w1SEyF4mFXB87w4+f/26Nz+vrdN1D6ufeVxG+TYRL1JYrX58/+4r+wqRUK/Xb5RM/OrKwtSHZogYrHVvry/HnGYpts7r9IrPwSmoQdYc/urRkdUik2VJPgZahm81+qZD4Z5RtiqpUBDPRelXv60hkyHvjlq5/vnPfxLW291Wvu+NLE6xU/n+8t03e73++efTt29eXOBV9xKJcvBrbpj93b1v37xa4lZfVocCMpS+zvYEXcGpEOqvM9ipb3kKZN8e2oO5YzDmnEp9T11kW7IrITQb4ooZfvzt+pLr5kxg2mULNn81xPy1ZGTHewZmJqEzGFpPL363JM8yA3JU+krEXKY/fiWA5/F8EGpYnIW+94PwIV+DZxkJzkreYCosBWNY780ctvLwqT5O7rrlnPWIMckDHrGEeb7YvpGPL3AWeZ5m2M0ACnrpZ0ByAwLez+cv37Lb96w228QsVecfCG8b+ZauvNXtVRLff+UBLqJ4IopJotplh7/9KrQEpOsgj3i2+iMlY9hlkXwWblbSBlsY+y9T3+YhC+awdyR1sijDHW2mEiwWnpviiSSbRKp50h2Kodydpv1lPdnoy8sWQ9EQPYNjEh5NsbMD0Q/ryZwzoOKZZfqkWcYzWRa/Xd1obghMMOY8f3368a/8jYJ7vDAobJN6XDirCUUb+l7EzSRHnHGTa5YAz+AI+oEGIL3Zwk9weZNADEdt7yd2/n/gVOdv/njo/NoGepoKWxOYmfmCXNOyJy0BLYUBWWJq0t/+67/+9a9/mThP+QbEvK2pe3+wq0/6rrcRc+bYpV93oI1bjW/c/L3Sr/27n90nWWqAy2Nm5B5WI1V/TdlrsceUwKHEjiwlWfQaqVmvnty5PLFbjb56JW4JXTiWOH6lUEc2ZOZuLyatioAYazwRINMo4Pc7YjsmtU+Z0h7zxPTmLy+2DHNU30U6X0WOpBoWkYyRmRuMoVgdKHtiZkpydwMZkVNmYPAZtp9MgCI6Wg7g8OcqaSpd5gbyAJbsTIRjoaPlQ6UW9rog0+4g2wzYz0f50OJ+fqyDeErGqdgG5Ro2Joy5dgczhHQyNbDJF1+nl9WgP7yWDD17d/kkUUu6GjrpMjWU2LPdSk2Oc9hC7FeFpG7H1ziXHhEVA52ln45ZtdPQXffnW231Cl7+wCakkeWl3VxfXr2PWY79y74PX19w0Qc0iwZhUDMs4xulMDh+7N9qGBWUSsf0OflxsOPeZNBF8KKLvHX62XcxZeKQ0y5yBAAluLX5DEJHH74vxltq3fMovDEu+Epk77JlxxYmQxWW/GwcO/WCel98xZu8gHqYtWIv0Ar2UrdWMawTuyZlad7IZwJmGrIBpm8rSEUSZpRrXcbzyVluRlZzcNYrCOrWIGcCccNjN/Pl6zefYMm5AXRCclbeydaYs2ABoZi19kbxMQobioQx5r6+9boetfRq1eNjQC1qir4T/Q8f8lmclKRmJtXV241VZPRNE681ZY/CRwyS29FcItmYZk7q6/k7fAC9nlJt0WF5ZosKn199yeTlQCavevEzyivC2h9ZA6o2bGKcfomUkoRuIZnbNcTz35qZ+DJ3q0Rmr5NkFu4K5fybL+zlccOYaabUkljAHnBquTi6Sud/MyXjEK8Jlzv8VFRzubtKIs42jhjdKQLSmTD3q8UWz9STh9XV+RgQaZqlaqkW8GhUCnvdPApo9caj9rOku7z/y9679dqWXPd9c93X2pdz67uazZAOZVuRLMQKhMC2AjiBkxjIQ16Sh7wE/g75EvkAAYI85SEPAYIggANED0Jky1GYxFBC2HBsiWJIkBTZJLt5+lz23uu+9srv9x81196nuwVZASKJ7FNnn7lqVo0aNWrUGKNG1axZ04wmL9o7aYuGIMFgIK61Z8kHpqmZuTKD48lspMVBGKOcDqEs/xASfmQkPSzjGg1JtK401s46juIj0ap0XAgWAJB4mhJTfwAQNBP++OyYRZlmVgovGFh+pFFtemV/8V9uF4sSQcKpnV6X8bgetC0azh1BqXMyS/NgqH0qSVQpYvswK3GBtSKWdraHNRDWRTW+Hi9ZSLdl457oe3CbeVOazF5Kuy9Skc3vyq39RdvkGsSm66TGjYlcbbP5VhE6jQkp2kqRTuSW6tvGbDLJCw4dAoXkFEJu7mhX1C7uQjAwTMEVN6NRk2fGWlHZamGVf4DpCUKJURCwM0K25tkomMlE5fGnlM3qSuuT8em+tEKaESGlIQ1SxUprKE4i1qNWYIgzHS0DEbItAwxxbQixuilrVXG02gpdpDNUsdhvGQcMBWmaV7kkuYBNRjNaxbmnmq224yNMpDKAerLA46ejKBzXVBqqHbakIRe6aq2uShYJBVxg5mdcLUiJOQVK5/YEXzncmoJIEQAHJn8kmkBrCDWIacsIdnz1eMFY8NVwSqfX7QClIZRYvEVaShXsaZOCMkaWIzVVplYJ1F5QgCznHWoBkp+yQQyt1ga9GC/9KuknJTX2FOqJ2H3ibjbOFooA4SXWAC1FS3FWOMJYTP6DJq7Uay38ovw+roUsTjkzA7zuVEZnAKCWMuJcqQo7gpQLEh6mohRRnRwpqV8DqslQ17IKZk0YlFylxwW7wFMcUIwDCFXMsMpmRfzIjEvVUGlnkTEbClG0grbLA2az1RCGVoxXSAKfFQlsg0/cMwJ/5IHKn5aw0KxsmGWDLXrHQeLUSzWiEUYAUtAD2YJGAItOgo+olOf/qdKqOrrmbgn/aGkfqjngFeBUtQaQ6Xn2VRUtZOWvBrn71FUpnyOdrF6QWy+8cuAk6PNUnXhHFO9V/k5USKEVOBmBVt4Aa1NCJoYTF+xJPLUXfgic7gAzWf218apuSZc5p9ySLlCrjjHjcBPqgCap4IhwW6GAlLkTg1JlYxwFRE1HWrwvxK99f+9WyW2dVw4kreWQVuyU+ue+KgCCzK7mUxxVtvrT08QJNlBauWJ0W2XU2uoNTOKRZtoTtVFmtB9yKC6WmJQkhgtEk64I/catwAm2KSpbSlGhhDl4ljEAKHW3Wu41s1K4ij+eXfSQuhiv5K9/vdCTUIGsNLPYhcLAAFrXGujiJeTEu2S4BLcWA/mp1QfK4rxLuKzhQtXG1dtK9c5go6I82jJdM4lBaCkQSIkXBozW7hIBd7S6NE4iDdHuaBEMlG6LiEHScFpNQpVN53U+BY/ZNCtBhQsKbR3GCKkUv6UxWD66o3oQaRAdG4JQWOyUV6Yqbv0DP+Rzb1lEEjkhpkcS9nJHQfGwAa8EA0rCXgHS4sBUcwAm26rTLu5ErduorIoKNkJANv0joCzFQiR08GIpwWb7mIJIiaVVHPgiNNhJrQaSSz4101O2tha4wK8Vh/6+H0EGxaKVpvCmaDDBggSblfKwyOXXuDsqJiRCUqwkzS+J1Ukig7WqCoW8rrAEssIgL/w3HZmPqaWWalRytL9mUwu//NmiHqWGDBPhwdDkyTDevp9icdbrG1azAM05wNFBiME5oQbKiMoQPCrXfNq2xaeNzTYBgAil3kAHXq7jYfWFxUC87BSYGRcCG4tupgzJrz4XWZQnVPGKcyUL7mJcgSwTy7SfOOmuI6Yg3zMglJEmhVxuuTJMBFu4Uk2SF/LX66dCpX8qkVtxCVwsOeVbZZAUwZVOi7htzKunIfprTYHNIq9SeiLNbbTckSSGE36lXqgkGpH+sKvAWkq1iBl9PmORmoq9zitoArTxnMNjcEOGAPyZjHglTeJaqKZxUxmnWyIUgMWkE6ELk0WkSVIvhKk6DXJqDGaUV/ypVLw6CsqXQamPGMc8yQ6KA8looqECNSu5dCwVCqymARDdZTDx+Be/VNG7Y6mIN0LQQ2otpmbEsRB4Fai8Q0488mbtVNRG7CiMKRosa9fItGHPhqjzSp9Z9zgGJzVayXMYaJyhDlRrCJWxdjSgyaeJNIm76riqkWvCHWaqKTHjKqtYauDHUAX7eHO7uIU2cUhq2hKrW2hPV3DecooJOPNHO82CJH+45Ne4dda1508I7muHvQwmKKJSQW+eiuD61ecXih6JBYH83O034gzaUxP0pyolNuHESROT0hrV0yNZDjkSTJQAZn94WXq7LUPRSDJVuvgwBTAVsBVJlle1rCRxFpAMcREvoxNRk3rSbWE+BZYIKSQ3BhmTgUNcJK48bXEgpSeSLtJqXnP52NDgS9sUqWkqPSaAwo0YizQThNbHVu+4VNiMh8+nXsptS3PHeQV4GrAM/oGtdJkRYsRTqJRpDSg04COQT5YUw2JWHPMhNoEp12optRd983FqYCpto1ekn79WkbWAEOjq3arU0gDALfQyLxJVippkNcwfrLTYWNXQL5wKUOnkoccpUgM4wt4Q9D+V79oTkkdiipiJSkiTdFaD4regjGIIH9J8WWCgXEqXu+4tifo7kZN4plFvl9omsCxTutRAOcda/mGJ7D6KSYCSYqQwl1yBLFl3F2txiIuR0K1Lj5hIiKiAWPN9FywitSZKaLkIA9/wTxYFalC0CLLnj+BYS2cxbqUKccZVa0SRVju3FRKanRmwOFtdXGIrXY67WQ2kQDVKePvfPU2qEp3kYlFqpM67VZ7etgKtE0IJUsBhM/nPfcmD+IVJejrFivjv4hw+VVQX6CJGDwXVpkAot2QCSTFG/f2d0Nwn21rDZ66SEq7aZ+k1VtplDlm6nhmiMiQcMKmHw+R8Xh0KbQ5CIUJrgAeaTqEDSC1UNNXPRAT/iSTbREXNnJpcxBRA2zhaFcPWIrHQAYGnRXkC6dBBMB62F+cKC1eyXG5grX02c/sJp0lk85jGmCxzeeZgdUguieAhLuryywBQk4I6bD3FC0Yk9reMRAGymqFcNrGLH1SQJ+JtZ/2FympaTzB1lQYGhK1EkSr9KcqHThc5rLRCUyeqqHvkGDcBH9pb0hQrJzW0Svl2lTg2ywUfQ5NDu1HBlYd2nWfmlVQBrRHJ9FUDxUvISENYpNRQX4LfUsMDGE7iacFMSlFfiVWRptKEKvkDVSeGVLYGpBkOWFISWYJll9J4UxMK/nS1h+x9GDem7fHCx4fjejCa0mhaQxfTsaxncvYwlWr9VbDigOtfUOa7inIpptppUXgopxurqdkaI68SB2pqhWewJnoiQm5RD65U0+uwzze1JmpvGNaaGc75fB2sMbQKuVXUVTOhT2hKTIbmlYFPT40Oob2Aw2Nax7HfjH+RPb5Xcah3y9LL5NIfJ7sGKuknCx+A7zWo3uABA5Mo6mP/53a9sUYCZNpfIRnTt8PbtGJyYiilkuz2Aaqa8IItHUcZX7rGKiEBloI2l9jIPfGTu1STi8tdbBGwC6Q2HLBiHBQ2piB7CUoUMyI0gtbOfHuPwiV+RNRnUlKLp3TZ9jYlpDTCqcrTZBVCSipQMC1UMBwEMiMmpYbJkOAwYNmExdkClSSQUmUbbcPJGfeEgkuqZoXPdmE/iYCLLEhkkCDiLsGxB7bTiCRCum0xDl/TttItWJo2qwQgoYraLlDpEC65wNtgMPYLdeBNU1PEUlZKQPOhHHgKev436WltEyY+96Wm2TyHF+mpShsGoOlQ+qm2cYTEtAv4jJySIYu9VrBeCtSRr1IFWnDCUWnWc1F5G2yvzI3amt2A4IQtIigwKKwFAXcdxJ36YY7p1djgLxUSG38plYs94q3YUDxnVsYUGOjpJdV99Eoh86+2DhPrnBrCXkhPCCoUi5zW6lu/HFO0vHKFsXQfEwr5zfmGiIEv6ADq4o5mk/5kOkl7kZOIgcibtqSX05AxGylsJrVQBuFx9QBzR7uogn15UIJBhNHIGx8c3vtc0fZlLIHbWV2iDBuANQpgxryr47SeKce+28bEhGmAudolh8BfTa5FLhnbhxJy7jB5OnTkDPimgZ/tdB3DjKw6QRnzYk1GnjbaBCHLf/SutA/gMLNYeuQ8rwrmQqZfZ6Tf89q/hqCC9EhSMaqaBkK4Kp1cXMgTRmmpvmpFqi5uXETDYIkP/k/GeAw7J5KFttdBELm2CO9hV6wGbAQ5K1DiiBWmAsWJ3uCpHysBZTJgU00k0/DJyNPVpS2MdScXCPn6L20gzuDhcCslEqBoqJ5MlABo7jKU+BK11oaAwopQYB9NzKd+Ypp0XLDNdh2QIR/rdGCRA8UDbgLELRUUECmyhiuYsFwwnU0JSRE6QTOhwKuHYVBLD8eD/Z6tPRUlowgFWssVRlN/tbBH0f9SL92p8KVPvErVeDqvdt63UIWN3FO7AI3BogkWrHQdmVOo+Csp3MQZQAMcYml89I++d1gHpZSAquQOpFHXfiGGPL2gBLJA0Qc5gBNGafovrv6JzjQKTlNdT5BW1ACvQMDy5R0HJBAcgfSzUd5iBq0HhmNbEZkJpZR6MJhOCHyA+xQSU4U51dge+FSKuQ36wIRfDHpLE4ARUUq4IOWNFp1Ldn2QEmKE7lUaGHXdRX1AbbzqZwug04ooi6USJ8SHjagNe0ysJMyUKlgaGnAu+eOxzHGPbQs2TWUsGtCxJrQGxGm8IpqgP0AFVmjIZlEQWgWEhWzFjK/SxWGKN0dvhSFS7oMgOgekNoFrSQLzTqo22ez8iBS9xcbp00XwZEYsll3cY7CIwUJ+shLpVYBL1aXavQ6BF4oALiiveAimWgBK2IqqKBSNjzU5AVNQ2mt2KR4JozDqTo3ECZTE0ToR4LGOkT2QCKOma+mALIEs5Jpyx/04CpgOTs8RBo+lGTX5n7pOpdT9yB1oCeCpZaJ05ZGZBFVoN2FKP/ekgmawCov0xpkCqLqL20aoGfKIxTmwS3dhUoL5o5mZBlRTEaV0cRrDRUtHQHykOVyzOKEUgMoKIcVIOXVGwTRAm1cBDNIAHhdxfcLqfWagxbJUAbXULG2AvYLSriW3t6191xdyriFbEQAGGa2BCPy90GvKD2yGji6UbNpIAs2PwiMBhY20nuyq5q6yEOne1FONiajHVdZr0c2VuqyAtYAen2ps67SeDNh6OALQWEQqGPIkK3NSbhtSfxL1ElTKa0k8+BAyRKIRb/ODqC6oevZDSUwzIu504KGsj9VTe+wOvQPrYpIsqNLwg21W2fGg1GsKQTst9alCzZiCFqawJA+4fLc0ggVNSWitCt9092g/yJAdMOjUNTAHebRXsOJ9RnUGf8BMzK1iKFIhS1Rzl6hDGq5Mk/DoDH6UNZB+F6g7kEmp/XRSKDPBnT8qg0gsRAwKbYl/lIbpC4KhWC0tcFfHqnkZICW3LLWZYCp6KAJzizVkJAtIuG2OKagYVUKDZNAhyctdMIRCBJiUMiLIFbdId7CBpZCHdAnQMGFKaFetN+HLsEV0s7w56QWogHGe78EzOcQqQ1d0VFY09QOFddwFEmAvTT4pL2jYagsSWFlbUtkkkS6QsZCh7hUe0FKM0JpNl/VGlKxU0qoTPmp2VzMxCmbGBEIMyCmLshavP0fOdGehk5lhVstNJyWRKqwlnVCoIJoU+l9s9goNcmBnbeK+JFVzyOWt0+CQZiJViodyFQnypFtL6rkjOQkKmRnAwxPQYklb+9UDtbzgvBY9XPWYSpEarDQUQGvLXbqlzI11MGYWDawC1hi0kEFG2ow8g78UMngwTwpn4gwGWq4mbdaJ4JKDl6feJh3IUzMtRTsKsYMEDBVsMFUPk36SXSM0C+IUj6gA5FEUCcW+OVSlADj5k3OtOZLRqhQnVSLuZmNGJTAVxWBJrU+yk5JuDiPohi2mgh8wuqpIPQom5IimDs23jyIRUq7JTmOlCGpJI0IybWd6AxEkaiJDP/1oPcV8/JtsxQDcYpFWSEpjbJfCgxNHzcBLCYmnYONMCYUReOUTFRJXQaGe5FddvA5U5JlVeICCyXokwRzVMK4Hy0vpTKloOLSW9FGdLEhpUIpXVzWomkhQWFvRhD+wNKLpexUsDIAVZFECDjEWTmXIUAAnzEgCVkqY3rIDUyM6kBXRCMrnuCPVxuBBo6wvWcMpC6Dpr9QSC6Q/xK75bfSOXNex8okJjICGE8gGBwqYFjqYvlekAEhXoLSyKwxT1WGP6DEieFZJLl0SKjOKJcXuNc/n5AVBWcerLAbhYMgd/BI1oQbjoKk5giURurv2kEeKskHg1VZ4wYQZjBkBzCIEUyBOFwcaAlebmNqrq1S1ykMymkVSIL1Juhacxbh4p9h3qnZZEIfiVBDMweVF+eCnEQzlNM6KrbMo0DxVPFf00xNQm1YlT2hRFjxqE/ynqy/0EjL8gpM/dEJrUo4C5ikFRZHWwg2JiLelEpLLPQtoEMkf8kRKEUyEvV94NBrGILhDRdvlRPSPshCP7jK7Qe84rKTcllhGO5zisdvZ810CID5JhQ4MBxRbaRwBfVI7jVuB0kNpPRqraGHRGfxpXT4LYTZctkyMO48+KKP3BHpZIZJcvQ1GNRydCSNIoO2ZE8kLGsGHdUUOT0BMbnZ1oGklUb5fW+mIuILlnTYxXCxnjSRG0myLCU6bY4uy6kQVBOFzlW5vqFFKijc8JUi/oCM+rWrwPhgXjW99slnD9HLXob95iWLSkBpQae06jYfN9nLqDW9llylqASwVadQNtZEUl+FtGkGO+JuyRkwCOFvYIyRpj08wsAHO310dBDz4BVdHwJ/jAK0uno3osGvSwF+ww4ZwArJTienELRtJBiGNKt9Kr5MsbjBYVQBoAkCEpI8O29aGU5YrN1YpGDASQahsrvGATncFJjz/LOXodKKAXJqY8jaVwE8VuYexITP3yMH8dVSYNLQQA7pnv4b9Jf4WlM/GwYpwBZdA+v9KJ6ES04mJZ8y3yqbVRmmoEoMgSyECpkmjoIuzEOydUAJQhbVED5N6384GhosWH5zkF33CSIlcEpG6xL2iFUNpY7MvwWICpGBqCWRLzEK4xUIAoBpTJBHjk2dSCqzDCgRkbQgmwAuNr+tfpiNzocGv4+DR7EMOnKoeL0llbCsgYcMlrMmYh2YZ86maIBNkA+TDbKQZO2JycqGLOO6Yd6pKrhIHy13ON8QoVPUaCIY2PDJsBeLuYj4pWaPj4HObh0KEOJ4UWGt6QQwGe4QfpUEKK6Dp4qls+x2PTxhDVqfgBEtGGFQ39KM8wLoSHJbyXrI7IKmmukLD3VSdGF0Jhka6HTbQjKLXkRdw1OPyEAaUYtCocjjRKJso1TQzHEPCZCk+svZNbzpFaHgPT4kEy94LpKWTGp57OeCDHvfck4gQ3GXRkH7aVLleGacnMRGBR+spUsaOwgFoCDAjVHoqaEQXDJRKu0aGbAxQbAh9UMVIQ6+lNqGKC8iXVvJiAClRBBWwqNUcAnwqQ7wB9Si4JQDgf4pNZsaVWX5bI8Fll95bY+aGUDjUvz6QEgfllvcNaQbU9GDgKyZDEMilKoOnBKX/SjLJ0Kqn/UGfWsBDoIMJLmoqc5l6FBNDuh1kR4rZykCszREtOBWIpKi9BiQ1fERuJR5b48KcIgZAnoZUm9R5EHABuU0gpkoCD2wipgBc5imSCh6Yam46sWoEWncPUNedUXUfyREa98CmBSFR4vSqCCRyJ4XWJb5Q69M60OBKYJYAhkaNLzChSk3AX7HNkKo2N7Q+QuW5HU9s5YYhzeF3JymQpc0tiSDRDnKUptLoXtPeclgAy4yg4ELqLbhHa8+Ngv5qBT9OZWMREHEHAu6pisLOHCDV5wyghFBNl6ME2Sx1eGfVtAtqIz2SwQ5vTEwZSpDTaPMQjDIZXvW2oIFkF8Xb8hBIbUZkQRdTgbc25xCgkCjpsSEU51a1oB12ZNWDJ07MoBEPndAG1VyElpllWguqtUY/qhiicqDbQUg5CKSeUI6tFkhK8mue3WmHhg/6Y3rZptlR3tog70JzFeWVYon3hma0/gIw1ocfOC3XuQWR2CL51hNpNLlhcy7FnSIpP7ihWhakcCzS162CLG4aDxm0JdEm8EmTlOKhYBAnp9mukbmxFTp44LgRsGIaLLAAQYZK79KyQKdzcEgpdLAASIa0wIStqRBgTM9k5r6Egkxy5dmfcOdEkBXAJlbmZjqxxTNABYNuOjy/Xk6BLP4U1D6EVVg7WUOHcUucOka1PpdFjsBab/0VE4OkyFM0K8hx0xQxZeQU7DbayyiMmuqtOlCgILwclhFAhZH26Ezrkoi0/SHFyYThij4mwFYKnSvoQkAMkFVaM2DoAEzDJkYJuY35U8jSEARII5uJpApmKX4NShX3RLJVEhIIWWRq8qEAtgBtLZHWp/9VRaR/d2TKGV0F0rbZCmiAM7ChJhHE4Z6TT54bnj5Gq27QonQKVxvHf3tfPKIiwispU30WOzpmXdtsOUGPWEVuZJUkRHsPjA12LmaFkQitgAs0j1M9fDYPAdDmUN5KspINLlEEp5kShU3ycVVlaQNw7igcPct+Ll1LZpdJ4thfq0FGGaxojs9EaXumvdBM/VpzsEK6uLmgIpQtK2kaGaVTLhw3kuwmcrR81ossVWnSichRcLP3Vv1Snm11cBOBX3Z61UeDiBR86gcqsmERkPMHZIvTZSRQo+6igochoL9jODLlhHASGBW0A3ZGYZNEsWmAEoktbjYRhLhO6q97YOkanxWQyAL5Zrnhh2MayYWoCuFNRgmaKK2npzQWATLAQgsZr4pI3RKhCs7nIl13bLp4QGXl7FEsFQx9QWk4mM7nQJfPxrYUuOkJVmz+zgdTG1spIB+Pg6lrKxJD81DzLAEAY6NTt7nBrjBBFi10uivfh9lNTlkoc+pXLJR7SobAwhXT75pBIoHnwIXVK5TA6FLFjH3KFCLC/qHqIcTQSYFIoZAW4aa3rsVdRSEH7IRsvVJyaa5uLbT0dkGjYFMFqKZRbyqqpoEbmh16WsN1cNhNKUwoAUAxafTaQFLs3tDv6kAtBYIHsuMfaZUM4BS5t/kJS10Fgz6piKLT4orziQ6mULPLh3Qxz+9n86kvwa/Xk8XcTTKuQcGOWstmiWA4mMzWt2M+npm67E2ISkvZ+qbE2Ld2Kc+tVeA88+aAGrtJP0VnxKNaohHotp4UtPnCrSVxj46jWb5Px63rWc6/zOKdstnUh0w6MfQAx+PiQGkM92GkK0pMx3yVDy/t9rhadZO5H0iAk7iEIAO9baY2TlPIlk4waRdFaSnbwbMnUpAMma8A6+5n6JX5dCh/spV+5etElm0kmRsnR/HW0QQLyqIspQdkE82L1YILVoJRlibkk/pcdoJZ6hfViZfGQfaNOBIAAEAASURBVBkxsCGdoSfntFhDeBJOQmY6gVPGMlgKb10NxnpDccBItRU1ZoQ26rELaaNaEIHMWYbIAxgYh2VC1rPZgYURoO2kaAdAhag5ROUdO1LQomyv3bOzbLudnJ1JWILEVC1QRidQUVoBb4mXbcF0EA/t7vQgCg277bbfEGujSIxQ2+T9tk0ViSOqICHCqNMW3bmhVgIFLGW2dHNLFrg0gVpodzNbcVDrC9AnjLdQ/GoAkmC6iiF9IgmqBhg8mo8CJctVSvnvn2ip16oTMd2ICS1e6VV12gmvLFhxfi3i5YRNAvzIQjqD4g0dtLleIRiMFz7v93FrbYzwUpLAaB1kyjxTiYy0VkSgmM3U3jGsK/OZ6KSY3TTgy8ze1DN7JEMeAsPgZJWgKnKoncms7CKXguCJfqllNAbHwawTu8EDEnoslYaMaC0YYxNH3WTBt8lt8nG0oexk0Y3mo/l8ffXCYYWTqn02p5gCgd+xH01jgKS/GgUqIoc1Dzd8FY34kK3tvMEeoWRvKsqCeNAQGqN9JYwGCKiNkjSWEYCNLMIfKGUNLfsj1CmqZbH49rhk8Zsdg+TSPOysrQYdozbnf+BMwR6vLhvNx93kHD5o5yIebWJW3XSbfV6IKqlsFtNmCZV+w1hwG/NuLXQVC6B8dal56DExlMQDhMFxo2Cv8dRTThCdg81QeGCR7iUEoytchZRZ6CPUjvhHCF+1lPYyJtq5LzGsMgWrGwGiggLsJVykMA0YShYg9ACv92TlfUCTKWlKUFuO9sVSBCxeI/xMXdKj0UxllFLMQnKu99GaCpXSH/GMqeKWQBZKIbnUVSnECKSfpmtpLknkKxsAF5VFeMNMs+WPOBOIp1LU1BX24Fac6ISKU0WtfbZ7UkOnyuRgl/KVgjmEg6LTtWx1IJGpQGrkPxTbuaicvWiAFK0tyZalQZXsVc4DAC3WLmSIiqSSByutSxyRCQqnlD8UDDLb4Z/1BH3SuTc303J+yFWOwjtwpWnCpyNEiX6iYYzojtKgT9lkeOElmOKrFcX4Bll8itRkYgKiqBTmKV6JmgJabeSKYnMjsVZBP/CRYp/uW2mMC00u/C6Hg4cMnuWlg8zKcz3S3ZbEj0HkTI8qRPhkf+tDUzkjGJKcyk/PhnMtoPb0gI91nL31VWjhPRCG2tAAHwRIM2lxGmV3h2Qquqxd7E7nqaW5sXhP0D5017ltCyVcAZjPzvLQKmO4Cons2j3+weUS96RrvG6P04fnJCrgjKNZFSaSeedCZwSpZQPmmMmaZ2zibfG1Afd2c9K5zAtbcbR4NYcDjo44iakwlKaz0VLqjU9kCwkA85uHp73xcvJNpaYjMhlCiNjvuVIIAGWdNCek9DWq4jhLczAcEmz71AppRPEQfKx2alTgybZuByMV0t4CJvY4VdAU3HlrtCLQ8OOHa1q/iIh/4oiCgA15Dg65irxRQhmg1yMjqqXDAL0pGKSmi0KEACRaL0VEaTBi2RSXiNpfaRs0PaFNX+uw8cTU+tOmJARc3w0e9imFNnNqMMvbFgTIkzp+W6V9DnVhsLQ59BAMce9Es2KuYRFOBU7V4P5RgKzyA6sAcRpggQgcvQI66+OPFCt2BCbQBnDCDOL8t0gxI+wwsazeqWpSQhzYZcoJOpQVeSnFRYPotfVBuN3zwXJIRnQaGO+AFNgI3XdCzC2BdIqaiJGV0XfnfpBKFWh4GgXXgFWlLcUYqxYhWxpc00VErlkxYUSY8VBrK4hrJwaFTRblj9O+7922ssDTwBhErwAX/krnJT4xi1ilSGKa4CkIlKMFwlc2Iz3dw2oCAs8MeIK48cvkDvyrF9cdbz/M5t0MT4EzsGQN+s+jBYd/OdjwhA8iDMy4G7EIwiKerj5lJhxoZ1fqr8hQRct9M6Nuyls4sH+PFkkPtYx4QojxrLoABFimIFGcksJSAFyU2bSOdoUDt4Ppcdy+HTsesYLBd9xdjYW4yZzGcXSzS+w0G2OB93fAl0SkqU+XxSUzNcT3+TQW0MlcOdpspUoHVQMm+fjSaTBMiu3QjEBN2bWkmG1FUXAowRjR4yFmwKfYp+7903+RETRDoWLdjSUL1NQQLwzHMDYRDipuGFwZTUVcQ3eoj/qEHVobUGn3hSHX4YCgZCcCmDO+CvaTnilSCvIiW0EBMnaEN0PY9wQa+ynFwQQP8oQ0VZMICq7ACKB9hj5VmLgExETa9oAVcMFbKcNPGqilYTyueoMTDCkhLP8pCESrJbeFCmKIlAFpEReQtEXc+mZjxbghVMWVQpxwSrTdrqu5lqH9koPmln1lkYQYKffLFgBNtJ31RxVl4xiHXHaRa60KfmwxTAFPmAU5pISqJEbstFeRZkoiF6k0ve4d/3WJKVcjD4wmGk+QdpIhQ4OTgroAVOe4js5yBrkWPeamCCYOOgiwb9I6iaGBJDqSA4x2FUxqJFUbhHyQZxZ5kMRVUP9IVHpCJ2naOMDS9zxuAx6XihpbYopQnSMkaDIJBQZIWq3EyAfokblYBxBHRGSjfxlLDiwq8WbcbDyebjizg6UhVG7UnT15wtNj1qjpSKcpvr2HVsCRDQ9h7UTOMMgLFladWqwQ8+fmdmIIzqHbbhbdbsJnFxxs3IMzGXuaEBSvVhsaAZGsJ+EUcQIy9GBarnaIIw9wmQdCr4joIgAuLs7oGVe0EIwh5+rQcUO+ZzBZPpuBQ1+VJlJmMZxhB7vNet15YDHNwcHhjX9OLWIhfZRtVSCOL6DmgFEZozojCIHWgYZolFV1nirCK5O0aTJNhpIHzzVPtoZrgUAwyYo/w5X7afgbuqjGWtXUgRlZy7MpzVP6Qkve5Bmu8AdO7Q5V2V+nkP4yPcfI+NoWAaBQK5MUPK/8h6AmElh6GqjilyTYKKWAFXH0WrGxseXWWGfVizEF6H7twtkw1M96W57VK3UyLcSkdqO8qzivNSynexo8GCJ+jIDb+CwXrqZC7qwZqDav6c0lMGU3C7iuIkywWPCEbi8A6GFZ06uhsJNGBIyFqG5PqCkTtGIh1Cp7Fax0rjHPSqToX63Fnm7erDwSOE1ShiuQkjZzB/7CCSfBZct7doAk4MV+r9RXCFKqol4LiZnBzK0pfRXgcfAHSnvqkxqiOS8lpwXEWKcZ9is9qzRQtpkSaQBcQ0PHUwXaU1ZVgPwBXLnZrAsq11hANZyGXs0QVacU9gKhi3myrPJtWcjDVMEfNYElkhBQIzkQiqwpBMxP9YoE65zzDYMRXw2fTT0EltvpdLzf3fjGF13D12U4878G3t1m7hfUMTI08BYvqhoB8zFGxWmV+HDgLY3l6ma3vNpfPdtuluubJe9qdJwkwXcN6E+OIXr7nenZ+XxxOVmcz88vzh8+OVucH0fjLVsOMa0qJpAuyqLDuGQweHu43ex54RmzhXvD/mas5/pssh6PeD6DsetWe3Z8Dyi22R46tte4IozhxOSyd4x2xWrCK/7QGUyGEcwZbOAv1geLqA0iQffGRNcrHbKQPv7LL6a5mhWm8ABQA/Aw3A42120zyo28lX3O7ukXd0oqyMAjHQ5KeA+aXQhQYABErkjAK6TfM95rruk1quvXmERA4n2VwUugBp5UuCYYg4KQ2IRQK+Hp815BJMpgrs0R7qQvIMdVobubfYFKggLTBL50J5iTBTlZI5NXAEmaIxUS4FX8xQakNx4lrR7SU/BWqsgte2TJBCkzNBVuN62q9mM2TIkDSNyKFKlwGzkElyKccGoYcBQouitR1PQNc/d7G72olvabY8Pa7BL2yPEwrjXDojpW1moTGeIRCFtIqESv9HTvfRQjWlYBnTogkC2LQtUpVV1TfYmlEyhXtFUdKmHE5pTekDTNz120XaMgpI9FeAnWShRQsZZElk8EbAROWDKpzFtAvPpDyEAdin2aWQA4C3Qw/5Fgpo3cUp1mSB7msZciH4MFQIY+KvTbsVilvZAgtwqbRzuNSLxOETh8muEeNNJxmCYXZ/TSdr1EiM4XbBTeTG63j86Pu+XywXx4zqyR5fTVy5tnz3760U9e/PQnqx/9UKNjq2vKE7l3flSMjuPAEizk79Ydbs4MG5pFHGHcLcDGBezL7p8td9P5DZNNJA+FnC5kHfHNjg/W2m08hqMIuzdApcxMfCBw8Xj65L0n73zw9hvvXlw+np5PN+ulIjrcL3dMLkfdbHEYn71cUwBfD+OK8mJudKPCg1seOGPxUBjlFp2SKlxu7ZQrX7AzdqUZrOOOp49MM1nXU0OUMa5YJL7RAgP0+TCJCqC2Jg75YePARheQKk+4RF1phdZHUIohGfa/Io8cAkCyfWIikX7Ete2xbnSoThn8yxY/kKqoGCYqtY9zhoZdLAIMJLl2eYQMYOZLxJUpQuTciMgz2oVKRINf1/4ARorAEHKUxgQwl8L6RNt2WFeFzDFtRTWYXIasUxWpRyKVcAlpBTXh4tEDxFCkEu0ezCQuGfmcIJGKF0Bd6Q6qJq4hYkRJnFZrsE43tCEur/XR45VeuABrD0fo1zzgA0hqqjIaQO19iuXDZRZNDwyGrmrf1UIZC3owEjKRJqGoNBafAX9S65Cm5CIkZNPn9rMMKeTcVsMoDyPF1PMXjygixPKTZoZ4KmxI2YPm3jkXEqovYZ8bGvaOvRgOCIjjI+NpMVZ467wBiceUVENovkMi+cqjAUNbYTTcIt7SJjXAi1MnCzWeG5Ea6M2cTlfOFVaCEYCHzHEQXMGY/1AjumFL+c9HTYD30yaySLbIcJI88sV69ju3JWjTeFVmg26hxijeYP9yejYeTg8zVuAHhz/6zjef/sE//fHVJ93uBicGa2WEnUc0hUN1V8TpGl4qUKToj3hzpB34LBteFZbP9rJg5mkkLFbtB0ufjuOK0UitxAa5dHMBJmCwxwkae4quHbSw+UjteslRusiDn5PhETt2yjkVrRnx1mB3Ndr+5F/8+FvnP+ZhpUxmmodxBIaZ5qh7+PZbf/lX3vvKL7714JJ6tofRlr6MawkPMS/QTTovRqvtsNprzSGQBd/Rjmxp2oC3payhHddaM1bBwO8iPQeNcWUeDSwDK24eJkxnTzEibYeAOO+zF5hjchezOXEUAYSaEyI0HpQy4UNErr8QnB1SUOkjzuCMakAA4kWC9EqWYzZqaoLaoQMma5UcBQGZseuRCAEoVK6NowKZ9hj+KhSIhBShRVtx2M4d/RXsJyRFuai0SawJVhEQYCjBHExJu6Mqe5LCQ4gLjLUwMXdNQ9JOgUrZbMUnDmkOWmS6brFoCfgEXC2RkHhGDjorW6NOBsu20N7zB29h/AjeN8q1DuPRFFBWEaWDOqM5FGjyV/aomGu9sKmcRhWs8BAh7JEg2ESyGNRwOkec2CtozTxfrTYHRUWGdNBQQ+6pzpTYIyDBoO9gn5MpF7nHxxMArU4uFxpFd5GZLsZ/IS52sXEl02aSSiKGgz6uEymdX5MOBrI1aCLFBLCWG2uS9SkK004g48WkhQVXMoSi0l9O+jCbOkcAdkMWuVE5PKyxx87NLrRNWyIzXI39+vl4wQSNFfAzBq2zy0fbLVWwMj7frPlsHLM11iMOkwWTtunNZjtYnLFIAn20ecabo4g8Y9FxOx8e5qPdA3yobj3srs9m3fe++4ff/ke/lZ3f2Fy4RPNVxRhk1B3TQ+eSUlk2Wg3ZxCRx90oojr+S1N9EN/qbVCEDW1DZCBEs+1HLFEqSLD0VsLUwDskBpv4oElvvEduJC1hZOGXjbrzojtNufNY9eef9r/7iOx98dTo7f7kbbmdvvPTDWu6roABLrthZ7OZux4jNiePr2XSx3m7YiAjAhD7fXM1GtSeIBwVaOjb74BEQmIVxpJT+IyzC2UEkiCMkCJJ6wUIT+ybYzHE75Nyp4hs6hVIg9iVv8JP9pzI+zEcEsX2xUGjDfrsEIet7yBSrygD5WWzmlihzRnNNvBbIsgxKGlAtmRgU5lg+6algVyqLFOAXTyp36rIzybRLDzcGgmzSBUBCE0HZVVx7h9QYUBXJccCEwPSR4G8nbSXPFpa2us/DIpom9ZOLZur29vxssVqtOBEZAlRbKKEJ0TXRoi4BBl4mEQ6sYbhkAWFiSCDZOUNZOxah3A2YQDG+kIxdxExgyw6xjnT+dDbjo5CnwvJKxiUFtqRKcpVKEquRpfjpxdiIKq3QMuNyhCEaa1O0HjbsWSX4tL5VpLVzbTgpiCxF+04CpgSICI3HuHDNZLPxIqYqgi4DXY7XmhFoaaQf0XczZ76HaEMiIukACmDMHG4JLvo6fWOqwJEq2ivXiSQGtNrLUEsP60+AD7Q4FxCDd8CfexpGbNI9bm5ZKvajpBgswmE9e7hgz95+c5ieXbJgPJxwwiwL+mdgmJzNWRyCnYuL+WqzZKb24I3HN1fXF/PF2XxKn7N/j+28j85njxeTD7//zT/4+u90P/le92Daba+6m6fddDi9nG5ffDTCKyDUmI9QSurJpW+iIDFlTQBsPZy0P6tLMfBTtSEjsMtOcVpHv9LxukO04cDzwfGcz9H5Nznvzh52I2aD4+4w7d7+hQ9++a+986X3R+P51XL78no1np1fLTnBdcLqPa7rBjeYR5Z8eQ6rsbxim4SKwN4P/UF7A2u1un5JpXY7zyW1LEwsICHsgkXMNNVkppk7O8JbCNOOqHFO4yKijHu7DRpcFsDisVaxOFgfvEHEAOfIhsp/8MD9GpDVc/mh/QObwgl6bZZ7aGuwMbEsmpmW7Q1WESNOZN3SmWMiW7VUkoYoFAZNUgUArSs6UrlYUhrT59dvyIJ9rXizetxKHgODbWnhBHM2m2o0Y32oAm6TRQoB0LKbJJIlGhClF7gDgFupojHqxvSyytBJWIbKJg8PCzjFpCerSMBHr4jXeFjgIjDTrAjJdEuVIgXx4goe4zE9MMkUnl5Zo48ptT8khVaPpiVWpIdRWeuBhd40YmIiuJGGdLWmkFJ51FUGC/eYvDhNwojcC6IR59klA+nRcmE0tbbZXUlK+EAZYPWulEu60Y1pmB5nedo4BmP8pipORbKOAhRiCBQhvOfqaIvl1Tjykvblw8frLQMoO8lZoz24zj1frK923eUjuoEnbFix6fzMkuPx9fXLyXQ0mfMlEtrJpx4dmab71Xvjbn5cr1bPf/zD73z4nX+uhdpfdeNDNx10qyU0oIS3m4MHsA7GS3eHQj9uQvFKlkgnhOuTR/JIu4t48+disFLxZy+MH3kooYJpSTFYdCEs5m80OWMbf/xN1shm9ogCu4Y93eyMEYIl+m522b37wZe+9qvvf+2X14P5fnh2zbr+cXpDBxwnvuDPE0n8Gxbj2FeBA8X6HTu5x8PFbLp6+ZKvX7FDlmfJ8BN1ubl6wX58aqET2SzmYhkGyGWyWBysD/MDn8Hyhw5K7WbvkIMgEpxI4h95i9O81T9ggHMx6DhmKRBHjqNQwIYMZhWcpSkxI7X2F2bM1bpXDJadpYrFDnrD//KwqFRliQ2NbsA2U/ROFNSYCdFTJM5OKhJdAnhsAPe19iTYKTSxsUWxrZQQMt7fcbNjoxzGxLp6W6MlYpaQgyh4lYUsnaEc6C4B/MXRq6pJMRHVNRjnBwxEsHes8eVAvqTSDZoPLQgmxjiVosAIPwW4pYC4EsDCL+kE4myzb20lPeaJRILcVPmrkNeWnh8qsDolEYbCRqqrD7g2Q0uaFUKxn3vSEkI7tVLapiRPpEFbEa66bAE4pUhJalRgiIshEgWtKQuLGUqyElZVShPPq+vVHw2fVlI5zBWnCSPFLQ6Unp02y9x8BR7DGQrtTjQoBHHwIck8G8On5ZRUJJZXn4aLB6Oz8wNjw459SIyurKnv2Sy/27384K0Hu/XL8XE1vN3y1srjB2c/+vAHf/S//IMPX3zc3a66jpWXZXeLF7DsRjkg5SVegK0+bKAVA8Zke47KohkOmKSVVZLNNLPsf/UK/K9IuBURTOzP9GIHfSao8lgERQixJpv+9gcdM2N37cK/o8XUJXwM93Z57snGy9FgdhzOtlj47Yvuux/94On3fvAH/7h7turG593b73/l13/jrTffxTj9+OmL3fBsMD3bzQ6b4Y6dH5zNC8OYj7ABpJuf05EMxaur58wleScAQ8QM3e2XTKw5O7vo0W+ioxkA+IvHJM0kar2y3UGDJc0qlNJJJ/BJJCWUhQLGSsVVg8VawoElRQrTX076gxkpZ3ZBhRaua2oOKxjOuSl1SD8GRtsEdvtdvpKW4A1dr+Ov5kblzFSRHMBa4K5HaIq3ySFSv1yD17s+ETwBpDFVpLcydZuTXa20bukkIi1AlYa4hULYQ9IQiSFU+mAyfxjDFBIpCA/zpGl7s2aFZDT1dB6xs2iJ3eKxuNE+9DImOjwLKpY9Tf6blxSNpTFJ1+spMCqhIpinGSK3yroCYM8VfeUfSSy5TM6ELBtpWaKkNFNS6dn2LTqorR3qxWqYCPuSK+M0ebjJLjMhFixwgJ/FQpwfBaItq4Uk3pqcLpg6gDFKjbhIiXYqG4uyOIWD1myWz6dvOc2CxU/4SRFWW53JUmisCzBdrfbj80fz80dLTidjuWs4GT15g7USd2wed4vB7eR2fTk+8DfZXb95PvzRd775+//X17sXP1Usb7e+ucJKNy7Aft0N+DQRdocnXCtWzTW2t92M2eaEM6P5Kp39QXtYDqFkuuQkEtxF4tGHz4Z7UJ/N/P8vxS7+TNBv0T9NkDAYqYdFzy8W5wyfBLqMwYb+Y+iGNVOWiSM3LmhPF5P5xZLnkio/y32T7uzCw+Dxv9asIfLgcvSVf+vffvODrw0XD3/6fPd8PWKNcN+ds6KIz7tf2i/4BuP9CjM17W7Xm+vdga81xBQoFQghIgGXMU3MCtl5vxneMgd060W33+C6IQuuDCGROmJQonuFE0Sas0U+H6Uo+6ow4ycPn1Y7BqG4bNVqriCnLPxxOgkqDarDDzJZfRyBt6vDIsvRs66C2b/RFCOqD0UcwHRYYHiMACkWc7WOIGYrIdgj4Lnno1i8D7Bc5ZMGmUuyceDxPo1oT+gV0lXSqtrFEvihIvvKMLdZUGsFU2OjKThJx47yX1QpBZeckRGKjCKHbNuTr0JUllhSMZarpoSkmKgdkFavpeehG0+tENY1kCWOvVDSfbHo0CIXwEOVsUE+VaRA0IK4kJMFxroms+Fxbf6Oh9YGSZVC59yvvUdImkKWAYaN5ogKj12sPtaKCHXCZ4QHqmgUOxjP8riqITNRMQUFUxXXs1ycyjMsuMot1s1N7aBRJlj4ols8x4JN2nwxjOUyHvAv8XsGo/MHDzBst5ufzqbdlF2r2+X7bzyYdYM/+tY///3//Xe63VV3WHar593mGjmesVsK53BwvGI9JaFW9YniX6Oh9OuE3UD7w8udALxLzAMqn+u5qCZUrlzqtjysPu0v8i/CWb2dFqgfisVxubqmG+wuvBqME2zG/GA9mArTMfjL6/Vuu9IPhgUIJD2ByK31gmeH7LFY+Ujxu7/1w+9OLlz8evTOO7/6N37xl35tddz96JMX3ehyuxhstm7MHM8XaM71hj1ki6P7MzA2yBeVufqlN6MjrdFUTznX9MBGJ2yRpNVjd80EJHosEjaLPlAQ+G4wehBpYaqHYhPFC58jCqUdMQTobtkFm+qUEKyyID8YCOKkUS0GVBePdACqqCW4UTKbJdLtIL/Uwdqhnf8xCpYDPinGiRA0Z4l4cxfAQBBGjRAhwfp4qurOiSomYa0MEQ2ckKXpVGAZJnOk94hbpamdrNBi5skQoUQPCsiS2H8eecTDwh/BPGVC4aZQEjFveSTnHhxurQqHOQRxpfaqFGwngyVldKoTTAmNsbB/rRHSsQuIUUkkCGOwjgyAQMaxDN9PtYiHCSG1tKoaZqoAW4qHKLrDboxZiTcEOq1SLYWyaOBOAOl3Pd1ERMlH0yGPFvEZAO2jbDqyF2H4kMdxuiQUAIuIbCjmgAZIP64ia1tG/OjDwbV2TZj7sodzPKvheIEPsNtt3bjpZixew3pxtpg+fnJ5fPbRm6tP3n80W149/93f/e3DD7/XTQ7DB7Pbq6eul199Mp+zRD98+fFHdBnfQdntWaVKmxSkHPcZPWUUwRdmowBjOBUys/ShFQ2CVBsp0/pQBqu6Iy3pMwoeXv4FC/eJvyONgQbzhHFSZt02wMzQR7Qr3Bf6gsenrA0hlLyjzQYudlvtWddzIKIDa0cNeBlg9uOH84tHLrWzpQMJnJ93iwtWvn7pb/17i8df2nSPbg5nm8GDq9V4uR0tzi9uls9dE2z+FHNDZpYbaGC1ny8g6UYhSRhI5oOMgToILFHhMWFKyLKDdJewX/W3P7g4ClV2EwpMr+KX4X4jgPF9UB0bl5Mw6EvxINtcnbmQU6tI2qMeviRXOcVT0xT0+5Oo1xlM46FYgyEiQucrGCb6B/4ES9+bu4EavMlRRzA0lUsiNgFgqQVBv60UVMKfKtLnEJQFEY2X6ThZRHBFuQpb1ZIFJzQILkORVgWJMIk5B457nS4Jthjx9XKDncLgg7rZe3TU825OrzKU+a4WIi8ocOqTDgmlEimIWWHsCzV5NACAE0ztAqNQkAc+xdE8yMJ6SEqmkxiCkC4G7IvJjEfWElfIaZ3xHswBBRg7lM5Bdq24GayYOvA4o8TEBAvZeEa4qhgdivCqncvkSLBocZ1GGCxXrHIkRrVCvoVd6IZZvNhWdTF/GM7nHHN7i8FyeQuDNWc9GGCsmatRo+3FZDcfrJ88mOyWz//F1//n2+//4fHqYxRvf1idX8zQB/wp7M3xsB5jg9h8AK8wgtDqIxJ2n9j/urD+wGJqYbFZG43tpRQffOkmGGWIdFfm1iURb8L/JiXmfTbQe+D8cwoh7/PqtnMNTg/vBUc71pIyBtIB/KEqrGxtWRD0uUeGMSXKyZGHTGG2lH95gkfGC5T6ZaPRlq1YvoW4Z3zhBYANT6kZMtl++vC9bvigWy+6L/3KX/2b/8HZG1/58OnmerVHDlCIfChBA+SntHjd6XbHcMJWOKdleM8Z/VA5VHe/Z8HxvsGiFH16YNcb4kkTjmu26UMVePnM8vqWnfzZyM6MUZdQ10zVja9Ar/unP0YEY0SZGv9PBksWkYshcJqJuUFsZI1zAvSC9dE6MiwaRyp8Ty4kqTX1FwyqMAEyKF1xdauPqYcIXdSENDUKMA1W9M8FcukHITsycngW1oPSuEH0HCkgYAZQB1191mAd+G5jbSsLEvSNGlL70PGfwE2UQgNFNbzIQZW0QFpDJAUAY2hpewg54IbJDOxhnujCPGcthcU85PIdEA0nGBh1gGk+USwF2AjskYBcqsrmBgaqzNspm5NIm6kSO+x2lR1meIUSWJBZG0ioYjSdOaShzJpdzRZdLCsDzwq3pqSXdVCMJgu3FAz43is7OQc7FzxGs/lZBmleu8B4UUVqhEHDKRaBMiCXVCrwjZAxcwxof/zmW+sdj4GYwzJpOF8+f7l44012ZUwvHq5JZBPIo0ebm+v5k0frT3786MnFePPi3fNu9/R73/z6b3cf/j9MH7vVC9a5oAJWZYED4SAS+Q7PY+6daChv2h0eIXEMyyuWpXgFhYiL8hYxg3MtKL1/imBv/YUJNAW/iWsUtLdZDkI9iTYeM2UHoyq0HUh7sEROdpCTQKlXQqFgOGXK5RI+9y3J6tjQenE7OefN7m7xsHvyPg85ujfe/eW/8e9cXr73wx8/m56dbW4Hz5crtqpw6Bi94vjHGtqL69nlxW61vH3x/OLxk5uba+rkbCc12anY9shzQNxkamDhUjeNP0Yyd2zEZCDtTELjqUF8GhTZiPKjoAg3Vy2RSuot88wEdEFI7mPp0FVdAWRJlSG19IsYkoLiVHGFI+o1dOd6WXR1R1kni4pQtUQwKcHgF0Rd80V5TZfDkBEvDDJyMgTeqjakaooYhzRhVNGYKlK4Nc4+KV2Q5seZnj8AqQUqzI07JnpCN1wUFuI2IkFcvr4Ug1Wkp3oq2G853dgHdrCD512kFGV4ZsDLI/wTne+2z6IkplylWPlm/jBx4qdd4HftwQZQFpNlaymQppruDKstjQMi9ZoOGarDiyBUQ+xemctwq+OLBHLbxFRgSRJR9vVYkwXpGWD0VKgX6yY8+gB8HecyZBYHSbTCnmcYHM8A4wirxfnlio2dpLIpYThaXFyyL+7i8uFm48oEjuD8bLZe35yf8+Rp/+4bl89/9J3v/97vdj/+djdYu0lqc7XgEy0HFmbpKpoRKbHbFEGoNQ3y5QptcV0msZZU8PUAWxCAIleNi5UkDvc7Jv9f9vKng/6Xxfr/EY42qeaNO/yq1+mj4gc3JMi6MOqerU4UeQaCUl6aJIRNp0Qm2pq8doY9eVVAs8EK+ERjNJjNR9Oz7fOXStrjX+gO54MnX/q1f/M3Hrz9/sfXu+vDeLnnzaH5s5vN+cWjzWa7vblBys4Zy28P18+eoyw4RL44ibMsVkZWJo984pRHJU4n8Z0YYx1rEkH7M8XVkDl6QZG2RqnAzFTEiRiaE6NABP9Q5W2TLEpjznbTGc9eNByuWzAlATjmDGOl1peml+GDgaQgtOgyflYgiWMJrALzZ64lrEa900bIQkUzzkEwV6676LOz39yEWBT6w99TioShT/hJmR6eDBalCh6dD4a666ujTDdy4w+BeN/B1oSKgpSUkCgWygPGuk5VHExMUgy4eXWKAyWEPFkQ58yKXK82JTolNHWNqWLCFMMnsxAsxwl+Wb0uoiGByWNZnGKQs0RgJIohlHXEWvJPQRe5aQ5myxq0m8LRomxq1xvNCy7pGZ4N5mAAsLOYqu1jDgjBLs1GxAcLjwTQ7WLOMJwsjpM578LRrNHFo8OWbT0Xk/lic3WTDeicJdI9ejJ79vQHb18sHk6Pi8PNxXH59d/6+93Hf9QN1931J04HQIYQICVYIUjcs6xFW9C6WCv3SGcUlQd9OJkpevx4GS0G3gkQFonpDHDFTRmiuaUJJODCIdpb5K5H9DP2Sxvue1j2pu0rD6taXC0y2dA8c9obSQs7wlvYUR7WiRUC8J/N8pEPmIjaxYut6aXbrDm6YsXuIoQJT5snJuPzh0+vKHPp9q7lsXvjy3/tN/79R+/9pY+ueOb44OOXmw3PZ/ENxuMVm4CvXnZni+7lEjx0m9RRCQ/ReMLLshfiyUvmTOEPWxa/MFuaIa6YDFf0cakYDOlA1rzQngiM4gL9JNIwrJIbu8hVK5EGHjRnxSoCv/c0IQwH81MkPxYLGNfsMYsJ3OJ0aJL4IzipQFnKYKn14gG4MVImYRiB0SwwrcueR2AMwQBWCbEJNFacwHMNRGa1GKmMCFqJFMHdmuA0QIfv25cllRYCBisFS6VNKTy6SKcGECGjbun6CmmGwBZybjzGGySRsNeZSDVBRi6JROF3pRfClPvMxaOC8pxOx7WZXtbi4pHF5IeSKiYen/VoCgEmsTBTzE4kkGjHtDi1yy1vTakCghF3a6fH+DKgYIlopaCYS6wVy2eet+njP2/1hnG+plDDghRHX3azcxfRuymS7U5rJwJTvfIJiazpjh4/ZJX++YOzmyezzTf+wW923/vDbn/drT/hIeBh93LmFJZFDfYz8Mrf2Ma27oBI6C/FiXvHPT1eybkW8UmmNWmznU8jiymeAGDrLOMT1Z+PkDbZfdWiuvVO3ak72kuoK7+Mf7hLPo/gBoae+FCLyoUnOtiYBAR/dDEFHCCL21yREB9iAOaLhlg1Hv7x2sDjB289u37aHa45efrw8tv/7Df/62503nXnf+s/+XuT2Wg1myyP4xtOxbmY7y7f2a+3F7PFdrnc5sBfFBanhw0Wg/kcs4UERmiRIt8bShx6sRxsQKVv8XcYZSEAm9Lbbe5sawmAMq+mJcQDQ5wxjihKXjZWwDwLrey8xVAfDDMA6EYpSzyVcCmuBrGkgzKKNlzMF1gTAkaqcTyktkrBCaSo/XHyE8YX7kouyAJLtTYAw2ERA6Ws2piVm0vAkiTdeCUWjE8JK4l7BKHiQOAZkYItaTYoFjHpE75wz+uMWq49e+04Ecy9enCGXMKn8GDlSawpIQYC/Gmf9VCWGZmrV3SWA5oL8GyoAwMpWF8tgjcadn6kJClAYmfhPkQ5lQNZVYCfRYPpTaCz8MQKmTX2VcqH8SKvPY5HOO2+hwcJGKOFYzNLrRgcNkxrvPB/2DXCe7pzjhRQeqbzwXjBM0TWuZCL2Wya92NYr7h6+/HlxXyyXV5djK6+8T/8F133/Oxsuvzh9xHz6Xw84bnFdsXTqpvr51BMW1kEXLEbm4o5NQURprF0W65Q+9lw6kRayqJCAyCVEZhg6yidqE11388p3Gv7Ke1+JMp7P6EZh1eS/hxvmszcawa9f6JHk12BNLX4MPEVv2Z2YEMYJIfIy8ADdNl2I/LNEUsxj5RUUaBTBTKBszoZ8oT3JLXd8ILdoGSfXZ7zNqIHnPP9lQdv8dttp4O//Nf/5t/5D68HF9/+4bPp+RvXNyvWUFgjw0JQnY+YMjtDFd1Yz0NDVrI0i0TYulUpsZK4Vz5eRKtJZGVT58sWqKO8SwixjnVYYVf6ucdSqAyuPbGkrdLoqdEuEqkawOQy8pqpixC2afIaP5tnVMkBCAyKrgeESygGRnAmce7MFE7MktL+uC1KsMBmEUIJtDklqTUp6IPVKL0HkwJW1NIMyJKUBEqyWz4GK80MNm4JUgNMzALoq39tBU8EK7Guqd50b+NGsQJFItdafmscKLhXrxbp6TjlSHcFI3qV0HsCo38pAUtONNQiXKWQKO3wHLvEwWkF1BeXEv6T78Sw8JBQPWSH8mRFCD2sjKg8CuDTHb4jqYn06lI9M0E+ujcbjB+wBGs/8RaIHxTQK56NOC1ptb9++mgx/uCN0cXk+Tf+t3+4/L//Sfdg2F19ez5aLT9Zn53PljdXPHJiU42iFt3w4YSeKbfSht+LPyAjcm0khi0wIDBcbWbBx0IhoA0iWTQBstkdUqXtFLWDwJW0+0iT/DN1QfaRb5hRg6nyybyGpGoFvkci2iDkslpcSaRXpK5IhzAFIZaUc3SDY2gUmLiG6eSwJ2U04dVn5UwDiEjcjnkdbnq2/GTJntXV6uXy6poHe48enLO6/fTpt8YXT/bz8+Mf/q9f//43Wdcc/JW//q//7b/7yXz4Ysn+1QuWlW7Yx+XC2IzXsNfXK8+qx1oxFuaAL0VOm+V01Ij2E8JjSUmR7vIRIY7GQjMQGED5oKYIwtVWobtYFJ62uxrg+KjdIF2lyIJIGc0YIBPNQxsKgGuQCJw4xxChM8oo2hSjw8qrWSQKqTFqf95CcwoKQW3Fe3G6uk1KW/nBbGgTodk+SxNiIbwIlmBGQtFINNlZwyq4EooCmk7mhfVUBhjnj67gZO875dnQja2FLL+joy/TQqioamrtQF/UoG5WusdQ2D6Xu5SU2G85wjN54jInUzZvpJNSWAo9LBPCL/uMFfA5za4J7P1a7GN5Gq/bApKr2zY+Qw4dUZmE+24rztRM6WHfnccq5JW08Xw44h3+8XG82DMNxL1i00Y2o/FO4Xw8uJzezgeb9x5ONk+/943f/O+7Zz+YnHOCy/Lm5cejhS8zcxQnbwcetmuf8B0PZ2dn2/UKFu0yJaB5CD1t5IUPFmRdWSgK5U8xip8WkXK7qrwwhM2dDRWIwBnbIldNTQ/2UhLRuRMfgYT8k8Kp+J8E+GeRj6rkIYlOgcrAlAbzTFNPLSlyYSBcJbvWPRtppXXNcMGsHvZEuYgyaOFoE9hC4CqAUS52BntMeIiroxCpC4NZcWUlioVTFALrw1yEr3LsmDBhdCaL8eWbe9YQ2ZPKquhu8mt/7z97eXu23rAx7rjdsd1vfMs5zkwCeaWORQEeuvi4kBetXMzC4RrxxtVhhVHQdfKt9bhdOln0ba7If7lI0slSQG1hwSBkVQseaGZ9f5upnBtcFZfol3xgbomXV8tMNjOa5TIWbCibUgtR7U0dUnlBlaZm5ug6CqZHGWSPiB5T+ETpYiz9QpZH8QSt1p4q0FJuWQqxPoKl8qBTFvNcMWWZg2G8qA6MCRiF4I+PlsQUpfC9RXf7O31sYT54RbCfqMAS4GONDAA0WXYPOB9l5mRwv1/wlHfjshkhJsgiOq0A14FkzYTFY4pJHk5Y/WEtyFPy9OxoD/h9yS409AYLhLXcTuO1iVouX2OmbRApMDWxRQO7U+oKchbycKMo1mZPoR9/ikkiOwjZp8P+dYppJZiAMgc8c8M6G6Z4JMiIx3PAyRmLWTwkup1M98wQs0NxwZr7kB3n+wez4+P58f/87f+x+9G3uwlrqz+Z3F7drp5N3dnTbZFaXmM7X7ChYYo7jdjZbXhk7nFG/9hC4dGaeTUhvD3N4EJn2GdbqiOjbCflZGG+htI029LpVNc56HFGU/nfBySXqIPBKfxMGix6Vm8iTaGJbTmHNp3YEpGnnW7czcIQ8NVmR3WYElMFexugfgl3sIarYz4xTT0MI8FRUc3D/2W3elXsygNSxxjKhOLB5fTm2h058B/ck/GC9wmoZzolgtXoJhfnINvf3HSPfqEbvtONHndf/ku/9Ku/fvbwrZ98snx+fRjNH63WiL+PD4+8DunSO6dx8OYzI9yOSSLOF+dp6IJpdLBo+FwQDfL6i/LH00HHc9oEFgZJS7NZ8tCdiVHginJgFhzQtErubwofVKEYCHxITIuWw1K1FEOaca0e7w/h5MIjU7DojesxKCQbYphQRZ8t+NZRLAY1Jh2n0Yrq1hRo4WoEezI61LE82Wt2v2AZLGqrgtIfizaY4crmgHcqxlibgTc5dZNUlbeO6mhf6a0lJ7bYzfMxANfgHWSyQkb1EF2b46GFtrslpOxdL10QrzHE1pR28UO453/JsRwbb724NlwxlfVZIeVLaHHaDaJS0OASOSaqwdgp8LM/S29GuWO5zXV0PWGWBjBMWDc9KawHTzlnw+GD4/icd5Hpn4fD0YYdho/euT17uOYoGFayppMHF/Pb7dXZcPeVtx9sXvzwn/z9/7Yb8KbxcrB9wWlK3e6a1wCRBAQCIlyQuwsy7v595aARdyB/uljx69NlegX8dPrPxf19Xn0+P0/NjL5GGBI7pcdgaZc+J9zvngDcTwD+rlBl3N2fkN2nsI83LKwtnHWP3u2uWZmadO9+9Vf+9t89Pv7go5vB6vhwu5/sVreskB2WL84XtzcvP+Rh+C2fU0NKWTPidWyORT5g2JjZsZ6FvUAB8jAT23HkXS9Ng/unSsUQfCB0vvhj1hijVvEaxnR82KzpYY2YA61G5kx6VmylxDSo6VhaDAmXeFKkKNUoGTKrvskQzIX7s5x4NhNpeqzELceNcOZPPFIUOHv9i00YBI1g4dFoxTjig/hdG5e0sDxAUkkq56GWezIqsUyeVWOdhjOPl4E+9qGWV7WL5db6BAKgWDfNgc2I6eV4OT6CCAIcKE75Y2UGb4zKGN/CCEpb3CpdLCScOpK2xaxgLyCxxvwyNKkAZ6cOkKAsBitMxNd2h1RRIjLXnloo5e9NWTA3i+apD5grseI30RbiBKaiTgPPHCtYPnCt6uFxdMFXWCbnF4ubJQb79o23b5a7N7/0ZU4rn433jxajdx6d/dPf+52r3/tH3ZDF8uvucDUfbI/7m+Nuk3MuwcsIaHeenvxZ1+vwRecAj5RnLNJjbSZnTxCWbvqoe/Re98G/9q/+G3/n6YvufPH26nq1vHmxXj3rJpkVYoh4/ZOtD4flYLfiqCAdLg6tR8cZFP0qG2ai5ongRT/uWVD9RCeGzReT+Zp4FA1d0AlHf/Fo7hksrZDjeNu+gEqoZT7Ea46/VinGBY0TFQELoG6ivMw0NWRNHaOfWCLriumAOvH0oRkgtV5KrOd45Ig9TIfKHmtlWZZsyGrz9yh6mljoXZCiWDUa6inGhhCMaB2BWjlVIzDc4tcAI14C9aSmdmtS8pJLIghpWVK9Vi0aLCqkIGCNCeRWJRY6xUijuamW1bq7x5ykaxzjc8aVE2XDb1MtIVt5PaHeN3KFgnR9ergLLkys7ptM4T4jAodSrjdvPHzj+fUNFu3irYvL6X59/dO/+vbiH/43/9W3NtccQzVc7Ab7a9aqViuOT6D5nodMvTLbtsQgKi4mvA6vOaDsIyHqNoc93GB39iuOxHk+2L349nf/oOse/JV/9z86Xjz8aHD73c3+7N13lswinzMi8nIidoTlC6bDjKkIdDTF5SkwqiyZRiC3WXWD0dQSUewjSDswKk8CuuKYztVxGtia/SZFn8B8VArbUzqtegKrsovDDaWv4qdkHA7wWNaqKE1du43HTFmKVJWjKXRVwNVdAbFNXDGUGBDLJ6UwcI8JY25TOG0Ebk/AgMQj0zni3geNrClJX03sQ0lwVZp4Y7AaopgM4j1dFqy6K3KKcwtYIIneNcSbQm3sLlCwAhgtFc5Xiiz4vCJ3hSuXq2RlZUKHi1rTriCkeVmSwPniCYLL8k7nmHVuDy+3h4fvfOmj9fpiNno8O3zj//ifPu4+7l5+q1tMmCuOj1veW+aEtyeX85srNg72gepCp217HV5z4D4HkA12r7ADfvmMxYjLs/PV4fnVT5+OJ29uu8t//N/9oJu99ev/8X86+9oH3/z4qUffcGgkysm6OBtKFSpXLpBYtFibU/KlvGFbtF5NL4BE9vR3sHGoMZ5ShlFFP1opnMZFnFHkovFTcY3HPRkmzgZRk8B8StfkuU0h6fhf6hkBhCDHJ2iY+UkirbFSbFDeJSwwzE7yW0FNZQgDZwEQEVsl3jNqLKPPT9CsvlkgLg6J3qR8eyKg2oduqXLmSS52Vb+vN5mYWuqD8hRNcbwbCiW1LqEIEEyok9MkNmui2ofOHrmrUWC3FmumqJbcvz5Ujclg0gp8y9XfoV+lx97Vn7LjGSxcuDpyjoLAHg3DMjtL7GznnD1+hwOjn//0+ZN/5ctf+dJb3/gv//Pu8OPbn/7+209Gi265u/6YXaBzvtUCHSyPIR7wgz+NFfS0KaEseqW591r+OvpF44AmhvcRGOp4oUGfZMs5l4fdbHiYDJesfjJX5FHyhx9+tBstxnxdYciDRQ7GwkAw7WJZh9kf8qagqQLIcnk6ilykG6VQP3qtK/Yq5rpI/pxy1R/LI6nqkXHNXRPXaFPSLcWDMB9wkd8q4odRH/KdFalRaqHVcEPt/m8/ThADQmol1hU4nmaGMhegMHcYLF7mIy42ArXjOWH6QODEKKfOywnNN7/lAeZ5H9YOCMpIrGZRS+zOo5RMGkSGVLgWpGVQSIJuV+ogIha3wGRh+GWDmkkKmiDBInkTN1IAojbY+6RLHIEUCDAlTSo7TUttG/+TxbWeRwvWBxLhDRWHh6L2MaLLYYw6CTSUpoong5Fdx17msecd7YYPvvw13mt99slH3YBN6h/PZ/sXT5+CZTEbswxvrzGAeZibhIkd8qganK6KklBc7Kl5/fvF5oAvNvutCiYiyhmHMnNIPe9TLK9ZgVoNu5e308X+5uMzNkJwssyAr3OzXMspWgysjLi8dc+aOptvcE9GnGrDVnkGXNeykDVUzOVm5K/pS2mNAk9NgeiVIMqGTggLHVFwTEvdmeqQG8UnqlJzBWvmXm1NqnWjVal/ZHGNwKtKFUmh4A+0t2YaXPRSOwxEtE35YcMbuURTewyo5KhSpiSApVK408QTKg+zpeXCxJT3BFQCcGDkyh3L+kSAJ4Vb4LPqpu00lINEffmz6SwbFU5RabT90YrpoUqAfwnmmMfF+9xVjtdgLlZSezW4oOIrNQeqAIWvUGQUQhAHObuq+hEmXp6eHp44Jxodu4dPrvk02XBydjbvts8ezG/X29WOg/GGwxs+xNINl7xKOZteb7BsvvUnRx2sGCx4HeRuQ2Or/fXPF5sDPOQ+G3TnmBwOROVhzWC4GQ+uh4NP1t3incslvtdgO5sPu5vnHH/zxsNHe2TNvYGYKv8YdI2wnOOTInfzxBKhXCXt6o4a4bSBxFd5jYoxmyzJT44j66d0qkpFSwEx0wmolkub4HM8VV3L+ErAvnxeOhrQTFKv0fdKgTpTUhpnAFJgybdUqbPqmRklt9ByKh2qNWosW7klrGJks28BbwvyAIdoedGMHyDQaEEe4aGoRIAHgLo5SKZQF0ylYz8rksTYO2PlRsXKwz9SAmZxcUMwDwHkX3LEkIoCliRSLAKJTquBhb35SAEMTAPNpRbyHKDStRpHW5uBRNHBTeKJprND6bFjmfnT3gfvv/fyZsRz5eOjxZYDP+fdzYsfiGQyowN5Rsu7r3tODoHxfPKzbYQDMZ4bAxSorCTV26DX4TUH4AD7rDKqjdkIwBH+B97yYWgcbJ8992BYznTeL591l1+9Pe5evHhxcfFg+fJZli+0LsowixbuaGeKxMOwGh3Jyto5D7u1MIidz9VSCyjjBqDLU79Sw7I2Txxd20IwCwYzmBCFY7RVk7lw8vZJ37EXqpjqg5JyFYBArRivKt+U86R0yL7BA00Kfd2XjrcpUXRQc8X6SUJWsiATV9HqdG6YsXFKD19amzSrR70FLxxHJNdZMRSnGq5uiIC+uFEUdu/CLU4rr3fyJT3fHNyuVqDm7SjMFRg4U6VcJEqyfcu3pfyyBYA5sBRLGeujHtNuLDr2wbVCzIUskCNkZD8qFmjPBjmqn7ojgXTosTFauQGn2aWNIiovjwgZVMTE1+cFrjjeG1LkNZ2UwQHbpYWS+/BUq5L2IhnsgvX8CSgbDF4+e9Yt3uclMUSMbe1sOJ53Rx4Z3nKKN2Ma3+Dm+GbfNEyX1BVrpZulf4vnaUyyXofXHJADyEOTD2Z5g+mB7e+ctrhF5HwF312WCiJQfE79MDqb8eE+3lRl6icA42g8KcXaz8SRgGJTkIHWoIAjm36JnbxIO6k4GcgiO6vaeVUYghJ+8tQdt0bir7HlHtcJQQfYjVg+bsOssACsXHOcEktGJLnk4oM5zGWsGJ/7dvF2Mp/X5icNJh4Zkw3MUOC3HPhFsKjejLWyhkK9KDKBDfwcip9t4eRiYVardX0jkgLk79brUHHnsgCjNekndj48JAmyjcggtZlrzFl7lglTSEH5MWdQZjwMsrEUiwEuI0qURNMTwByLE4aGoEr32oAsxx3XVkZj0gKGUXdUK9NMDBEhg78iPtyUYCkJMcFT8KboVItOA0v7yG1LddJAlp8a9KxROMIsz27iqiggTDw83I958V2W0PGmaJ2l1wrbnzdY4krimo7x9nX4onOgZAQjo2wjd/5EbBQjlmPZFsNIyyDNi6wsTjmiYwEyOXCANAWRTcCCpDCJiKIq0bDlR42wGmSPnBLQgFsdBd33VPelO42IlqjiYLX0DpKivqAx0TKOF+EVltqKhYkBAB3CxPBCeOGkEEF7UcZAz0BFtLpqL79ZMj/RAJ2YP42JVqwVV/USAAO+rpJRGxiEck6lH3QHF/8AK0UNeF4grRdr9CsxZzlEFKLFYlf05FT5UEnTSQW1aamVZOM0gL+aYxKRBaTzF0MjRGm9wEUrMIRkmNJwZsGL1NYeTAg9TiG7llDGNKUoq4UiBXPcqMVmYU+As4i2C+GY8H067JWFcb5dx6IE6whaOljIB6Q4AIBE/nuVYpLJTccUfeKKHDVr9dpmNb68/kH2EA6F3R3UPKlh7MeB2U947V33HAHmXRnelPDjJSPfwfD7u74kfOsCa6QaqIRoUDNAUTRTTYwxJIJYn67KsQmVwp3jsCKcoKZAWeYDpZUtQ4CszGBUeJeMbdSqhi+69QGzELfOSYm1WQO0E1XsW1IPHCWWCF8yiW9EDsaawloZVM7d8Eb9S/lc8KJEXRaAq+YqYYz3KFzMG+nGuWIRswO13DYOl4AOV6/YUBoarS9B8D5iWYJOwm6WAABAAElEQVSGMDhzl7mYMf24tLE91wNPUFE6v4EmnueA3lCTrWoxTzUzIW1I7eYwemA3gsq8CkboQ68NuQWtO7c1F2VzSGwl8oHBolKXATj70VeR2eqgE+4BNR6ERA3wBUqQOOd9GE8YqIBRn5aSH0c9xYUaX1ur1g+vf5QMl0rb0xjeZHbHphISYUNyESAWozkKohYmfPw38CMmvalC6tAJLmiryJRq7IdaACi5anZET01RznPTTiIQzlIiCbRGio8TNP9FSkCYHfDgEWfDoaa4WsVxLpxQIrHut0I5NRccqRP7ot5SoIowv4s++Mb1KbTKcw8weGJtIALDwpyGhrImDM2nEkRsgrXrT30qHRviojsQTpfEKNF6LM6CPU+H4zktRuFgoTyIgKxQt6Llf0uiDflLVaYlYttJFr/MBz7uC/zTTyleyn550hcStKgn2Xh+5LXxPjBRBpd3YkmuVswmnShnJZAGKiZ2gOTZGjdOuUxwGEzJzRBH43h0vOPUWdbeeKjM4aKc50l9kgYxqbR5Vq50nhKQErLLsgXo9eU1B+QA45l+OlMqZIX/vIFRvjnnwDrWkcd+BbQXVWTlVG+jhOoV9inJ0RxTuWm3fsowigGWchFKT4RB/u8BJwpsU15vCVZFCR4ahVBSqJ80vS8x6bnhoxjPIpd6g7p1frFhz1msjtMqfhQKjeLvzlMhF/C6EmEdDu0iiM0BX/vrsnNWsk5IjKR2IEKDSAAnsYL+XoU+JdXUFOy02yLmrNVRbXZ7phyhrE2D2Ozbkn8kBZ76iNp0IfLbVF7up6DpLQSGOMCtVX0pmoX1DPsoZL3lawWvKdRYSMRLKQUhf6CHL9JZ5hjspnPh6YshIoOckEoScHl30ddGdYGP45WHiHieiYTlKueopiqko5kcE3eZALRh6702pcTryxeXA8hClqY4ukhNzs5AnXGFWUllRZioJxehDwCQ5oJMgoKdQKIx7nWqWpLmISF6rSXyD9yOvEIJ7i+Sec+IoI7OJEpQUwqgLD4hwlLEf/Itm6qgwcpdkhdjBYd3Xjv2rT4tcB8saP04AcEPDdH3KsQ8kggFpc19UwYK4GqR3uOQ7ooXJHHQZgUq5DHF4ZZUCpunUXObZdXBApb2FaScdgDVeb25lZO45stZXy1sSYM1VHErkp0qeDGFPEi2b6ThrqkgPxFqvEKwEA0CDLmphRlrWXGshbYs1tMsQRoLqdveIi3c12HUn2oFSWZtnSeLpLjL1Jk6nhSuOysLrNiB2FVRvjWxcwcNFgwqquPjZmdcsTIFp7oH4/c6vObAqxxA0jEEDv9aDgwWq1NdN8NJOXasZeO8YAt4M3+8YUaFCPIw8L55ifQqw8qbNwozNWSkJAGtLjffoVcxbEqifkUVTzIJcAq677Kg7ghNLZQwBbFvZVMjczaK+UgT+RenczoueUilsaj1He0bcNZgcPJiM9Bx68211sG50xKlOQGVQMvWXyVRJj5Py+JHg9GQuwuU7EDepVZKUFO1B5pTgI0LxxxuJSIskWgNZQtZiNMo0OrYfGHSwliaviUFHx8Z2FSaa1jmLQA9Xn7tj1TUslK88kkBv+A8wcRD0qfD0JpojWAFP42DOyAXic9cXIPHNVV46AivoPGtK78HEPPGkYyYLbZeSRKHZLHtGKh6+dNxQUoUsgw83iS4qECk2BiYlvH65zUH2qN2/ZgIiULq7BBJ19HPApcZLIryde/Mz5Sufm0kAhwptAhCpgmIJjjoMt6yG0vLwEKY1pGFYjEz7AoLdjA7faiFKirO0ggpHrXqUpcVitMHAAKHFHsN7UN7OBFAQxvJ12j4v2jQfMUtKCvXjE7yQeKtuigV6oXbNTUI7GqoRS61W/LL7ynNCmbrxjPtHwYSb2Yx6R7JHsxe/EyudXCu2O7yyRs+C2ChhscbniLIJHuKX8RJWDQP21TOFwaTZxtkcvYrdbOzAt/EJTqmudmKZVOhGCOlZeWZHt7KhPO22EGHB0dzqIs+4wAZzuECLWVxE1kFpzVaQFocp9E5MJbHXidgc2istoSPsmtQ8IZSjcwRjFJpH7VLoQccU8ARDmC+jFwf+yL3wJFpbGugI6eH6dmIE99BtFsOPImNY4lYa+RjywwXZZJAXjarOjZV2CcEB6Gf78BR9LCeg8x5/IJs1Fn+dPrntjp6JUdOYJSy5/rxjCxuq+wJ+HNR/QwnYgYcLGkBJkNl17voVpgapifeO2ri9dzyyTfEGYEHVG4gcPFlkHN1x3VUNRBj5IdhYSMvp8DLgRqnxFOG13vRFzSICt3lzuozWBLCQcpqevCJooyUyUQCRwSl26meTC1E5gDPld7h6AXWmDSI0TrNk4SwG3bf7djbyZmWfu0CtcYEqHG0CbKJ16o/FKhOmYqhsCgqx2cqA+5llS1UBcHE+MJLNoEyQyRH01tnhVofNjVHEsat0+ydgigJ1j26uroqhlIJrKKY3ORzCnAJ45FFfpuVEIZotghKMIaNn7Sck0XFr3GJeQbJkaOkaAYtMGCeSDFCQf7yGJVb4dNI3SfOQacIHWAnZPzxlwTwJGI61UiQV7Bz4LYF2qNJgOS6Rgv+AUuLGF50Xv2UL3x23zAL8Myoc2YoPq1VoI1kYmT7kHr7my/QL1tvONCZBsPh2pdXH0/6E1lQYJRSstN9VYQUurVS7qf/iQh/hgAQNLTYMT+WAHHF3GRGFO8mDk3Wc1w8hSEKPIoQkYbRqkVai0bzxeZbNpci5GQLiU56NvNuyyM7nQo7puTesZMkJdVpB/VlnukqDPZQb8BqsGtqDCnCWljnA6RkidtALWISTmBpsQ4rV7sTAKN0xb32ZVOwV+H7AAVaql3p1iS5d1BlDaAOEx9qa22euK+kgEHbKV0nEzTo8qlojHEVKDDrsiHSlx+tTFHGhxyIYMzCbgeKCiQS7DRaksZgF2AZVRFAAn4NRoFhzuI6xsjShDCufCWg9Xa1VhXsOQ2pdIf38LDxVNoI5qXXiXqv90fg6lDXs6dVLfDrIJ8+lwv1qRG8JBxnAADD1SqP4HPh4SqjGllEyrcqDBS0uxLskpr19ymfi+rnM1E+ywe5ESXiPsIpTzABGYrti8YuWaQjYJKrH/gAvmAGtE5NQi1gq8rMD8JSTYks1n9oqGB6dTEAgbHoH9PpFqGgswqq5c/V9xgQfxpCyxsanUmvlLqmQju91Xs/j3hlJxEqXoGhTBSbGsn3jv2h/BcY2GoALZNED2y3MP5Ib5K8LccqMJamDQWc6RtoMMgNW2TRY/dKIsuGg4GKZSFnwWrpYIdoQpY51hgMYmkhUMQdFvSQJVZmcY1XWV3bgJMuTJohj1pw9GDernMIAeVtASYNdkrMZ3AUvFFzPk1MQH6eL/Lj80K9P8H87oZD5hLoxM8DvEuDk9xg1DBtxVU+xkFx4rKd8bPXtLsyX5xY8RkuxCIggU4Nor/85AGRPJMfbgZyYYQYAlmi6uyBxW8UmFfT4GeGfGEF0HcSR+vK0hI9IxBSqEl75eqDuX9dX4vC1fn58abdS8VnQ6CrgEUFxiphQBPqVo1OqMTqerNsTEIPUHenK8ZXM1wfgqVA2oXAcESBc07tZZp9vwBxGGHzqCB4NTQyJPZbedV+62WCPTtZ5THGK1hiXRxdqYZnjaTDemfm2H/ivudMgFM0KcRDBtbEISRYgHGCBjZgWusqC/SkY+ooJ1pt/10pQEkkL1mnBtlooOxOu+fELqBoPe0y5VNF7gp/4WO1CFrmBi7BRgL2q/ymz7KnRnuWvZhIIgBwGAxl7OR4+fwp9qnbz6L6+UxR3l7xEmqwvy+ZNrzWUppkAn/HDCBZCmLsJQkeepvtnSxvFJCKpe1C4tU+3TLYzhlKLVv7Qsl2+8f9qIaBKZWhGp6lJwUBKM21dq2EOtjQlFnlxvbw39Du8uOF/33oAerXEsgPN9TtuFirYAH2NUciVOltuAMEYUfjSSwfRatktZDICYSBZJXcTx+7MOFKX7N6VY32KPAUAYBStoWUsn3Ugm2qGk1O9dxT62DMm9oW7dPMTZMLX+Ndu6El5ld4BWGMKCzM2oHLUSzgUxaXmrkgRlIvl3mhVbK8z5K8p38UK3p8r39f4QBd/PDhQ04UIJUOxVfCEv1x1goYRSihsGDaKIV4kHa/p+yAjMmvVPZFuImM35fnajRCe5JD9bVnBaqEgDZdIBX1yTIQHoCq0wbdgGd1OO8GFjwjO9KuCgOJyHMBG5pd2DBnKCZqAJzGARchP+kXVtiaUQsBUnOKpLiYRXhfnXua/bWueDyJm2JDWgglxoukShV/TE2lQ0ZxARhSXF+nDcSAI5CKVGmM+vacihVScgNPEUsZwKOlg24dIoJZMFvDxLe5ea+7vM0QSq5vX/PAEUdNd61wcOeBC3Urxcn2kUdaW70lwQk86fNhX4iOAwxqPDOo1+YnFGDF4+3GtwK4+BWmNNBKqQLVqWFNEu6Y2+d/0X9h4KNHj/5f9s7lVbPlrMPdvS/nHBMvMSdeEB0IKngJBAc6c+4FZ4IDiUEUEw8IYkAQFESIZOJQMxCi4kgQxX/AkQOFOFBHigEVj8YTEyXn0nv3xef5/arqW1/33ie9+/Rld/eu/nrtWlXvrd5633dV1aq11ltvvUUMYgB1njqIblR97dd+7fve56s+mBXSlVU+R69wSVgLl7R12sIX6Kg7JEhMk0M5pFpm9eDFnhIAlqHGy3A3APRHzd7RCHl2D3AY14DS5Oil2uQQbKWUc1Z2q/hdMzuvj5sDy1+4mZod6CWeQksqf6BtSH6jEflTQqXpEatI3IgyKrvGQ9UhLQxBYxo3Myj2HgFbDzKV470tlDd8hnKWtNyI4L431oMsPPJr9e+8+XZmwiMqtQ1UoiaoeSeVCSmvs+A08wl3DCAZ5RxJcr8F6wO+V6hlj0AGBbcs2IU2o2mgoAf6jHJiFTSysAUlG8nB/SUESujzy/jTqGo49rGbRlsbLWP2aPCU81VCA5/97GfP1EM3qXBkVIUOf+7nfq43Dc8EpvCNN94gWv3Mz/zMD/3QD9FrmBPw9EwG5u6yQfHQIRH7/u///u+Tn/zkeaSe43LHOyzyzjvmKErfxqQ5Nnk7u47ORi02FCTQa+LaLtd1V6BwHK72GTZAQfdZ1wNGr9h+t3d23MCIJw4+yIIQZ4NePcfycA8PJMGtrbE8CQxThz0RrQW4PBn9iUT9kDquN/PiQT64tFzEeHWJ9WSgJz7kFkMakBYxUTRaYYUceayZEGak5KHyd94hcECNcMbVj61Svn6FvHbGK6FeoYo2ZJsU7XRVtSKypcO2EUPcy3WKOULTlleDRGP2bhz6odMT3i1FC3MjyfAB5BjWEtEglg9zJRaNzktrVCryuWVC6RjB5U0KlKXGyxVPR0Y6t+dCyHEfpUrFKR/ytZGW03jYAgo9j4o9UqNtLn3eg36h0kc/+tHz2ostohkVeP36xz/+8b3L9Vk47Iz50R/90R/7sR8rIvDYA4BqO9cVMq36u7/7u7MIPP9luhCXf+9vZdehRjgiFJZ8ne1Z1QFWzVKJgQzVabV0hIbNfixQCFq53Z/dWb4THS87PmT2ffOWK1YCqHN802gyhgLtBnszPcJrZOwUACCdgIBHJJudVgbEehKTROc9viTO2aLPM7MnSERXWnBoLYR6nBR8epw9lsSQWo7lNCBBhlcGAnP08vEp0cNX8OGbbshQF6TjY3F5fCm7YTpypNh4BAly0MpkUxXJEj0qsQ8bKnjCJ3DUliswzsvC23yIAExCKESmMILm9RRUlyzIUCZNq01FlAii2temwYWOVStRxQ92YcEBGHesMbt0uGSQA8lWpJMRXHhooDEHWbxn9ohf279oT2KiL1ZXmSsNPHYNaG/T5GKyyxQxfaoYXGTVA8Pkr29J0ZpTxR9s3P84o/5L0MlAgXCA56bCh60TGuLV1koU9wkvTqntUTgSlCnUp7zQc5rA6U3eLRj5VLqJ0zjAaouIwjMOSJQYnls/lB4BLgtt8c3wzXiwkjCsIaB0FuVEJ0KWI6yzJsQAVPJUcX5o+MmJMZLREMeKTiYJIXoHrVQIe67HoybAVKBhQt6jHRSEtI2nylmmJRZTnpEOlPkdHKu+vF0P1ckK6B6738rTRKL2axVIlXFbZSq2s9V0ZGE2fUDgilS2KPeFGR1YohhKMhKNSi+F9abQbOWZhVd/rzTwiDWAHW5sTA/J0Kn3rAYvx0bTtYhRolCTNeLhNgkWcTD8Xs8KxIlTKmyegVUsGTvHb5hYxK9r9eWO/UvRD9XEMadI4etwSuDhMmQBVx7eDZNwIm7dCb8iVjA/VWJShjjNQFnikTRxJu4WGCOE4zITYQ2ROjZqrLI58VkKQYe7r4XmD7jKlKDQvDv9x8xLeZp3HR2uY4YVT1eOxOI0yfaELkRsJUcDdlYWZZmSBsy0B2hEGVhg0vZO2qs1uKksKxgTIoPBMUksr0IMymiSMjn5y/8KSWxk5NoBYJTFW6u5C3zt8KVj5oTgDkFlAH/PSOZm6nmKrw5XGngMGojpTQPU7OChh+A18aaxNmsBPpLQEym0d4YbFE13AKK4M6LFcTLPEYPaALCmy3ts4g4BqNlbKYH4VHyZmMT5dITUGiVc7PIofERoRmEszkwQd8c1AYBaEUuRABQsHb5Bk4ks6ZTvWhcuYQsiDQgc09ZGp8iTWGHAKqHAWQ2czGYcES2lgMHAKRUlDlP1dGtdiTowOszZIkVCZObMHSBh0pryYjTZGCTVqKUC9AS+gqt/aAyhJyLiScqdWSlCJQykpMZiluC7uO5gzo53ez2v4fNjS2iZErn6q/A2Psnaq3SlgSemgRj/PdywTYzxnsKearakYby14ngrfkcoy/XX8Qi/3LDSf5l56X1ctjVxKVCbMcf9LBrF4goIIH0ShbNEf3MHlgI4SZSutZJuCVVOxagLjviNPhnBkYepwP2TiDaikvs0LQ6G60hMIRmgUEsY8pTHHWe8yxLVVk0h7IH/TqYikNRkxi3Tm2++7TITYYUfYE5m80X4U24bjigg6NS7TzhDKeKGzCA1wrzqtg3CB71t6N0BGhVo5/LAS7+hzjZ4j1LcEf68XwlYYJzQdxVNcGOWDPhBnJYn7/CZBBbRllXGuZ1OCk3Kc5WuNPD4NICBxSy9psZ6YYXtLYYp1EynSe6qhAGFAtxQw3fsMwrjNeAOaM2eMxf1gcGNBCOVtbmQxxMttFbCJEpYLM+XnwsUAD0qdOqPAJusUoAOJAyOOjhHp3mBpCichEyioGGIADfLpCYgyImV8pq+Hz48PpkhYk+GvGm5aMkMadw15RTT1sTXRYkmkCPDqHItgAI45iKcFWaOXZdk8IWF6lFBwQ1HyoxWafisF8rLBaR4PVgqqzIESIskEmAOxndV456GsRzP0DlI9D1dl10acJS52mmyXRVjkJLmVbrSwGPUQE0ul//hApnoYZAw3ZbkGbSNINRpqzrgmOvEq2vAlFJLMPDUW1jEixFc8CD9qKncoRIvsEzGsh4eQS6MOMX5PWvkCy88h5ImAOQIwS4ZKZtUHNDJxTNwQ37EB/KMozgeHh3wFmCe4ubAHoSSup1t7gl5LrSLHpqUGLCkZ6TOsn8qZJ/CCByGBCzX2q/zLa8w1r15OzTBxW0grFOVThAQ1h8hG1A3xAO7u4Y45JGdDeBp7B0L+FQ1ZIYAu/Bn+73fmh0YGT9FwKwyCs/9BR4S7DzZoJYXXCBGpoTRWlR6F8XwGh2Gjq7Z25MGYt7lHmrKrRTWVAEtvjpeaeC9aUCruo8Cpu81+Ia7RXCHuF6cC7MXmvp40b41ardWWe+eRiBjrUQHrZg8gaP2y+QhQyruOuV1DrqVC2PD2qWvneOP7E10V4HYbrySvCFGLqEed6AUOS2CN3Bw3CTrmMHAqEkSLoyx0g9H6c7RHXTCxwksi2qcOstpQMgGCNmHb6ZSzKVc7gKddMh790q/w7NIT1SjGW7sBALSODmbtZq/feKWK1ggs2tJQ3y4MYajhnJ1zX9iFAd58GXu7M6AVOUIKTED46Q7VfbD8Uu+V0vKqMMFeEg22NFPPgkUaSUt1u1bx1/zvhP2cbCMzvcjjq8dHb504t4TZnm8bEsWsIQ4cTUfUyK4HjnP9au6XH9QspvmYSGs6lU17Kalp7lxAp2we7YPPEbD5sxXXnmF1vE0H48xs/mzfXGhhtWM6AJMBWrQLOXziLDHvS+l6YZ4EHu9gTs7jUsNkUBvHs1DmZ2lfXwHGPf3PcsJ28Onp4/EFmdzMDS9gB+fkbtxynQElyVg8Hb3a7d5s9WNrNvwNR3DCTtBqWUVA9P1hX+YpYOmPChiDMrAyKeY2bdFIU/L4dQOJfTthphEQLDZ+cNqChEqgqh4R099EFh3YEne0GKtUyzu+cWNcBAqwHI7FzuTTjqYUjbK3SMmNLuMMhUKIV5oBS/fb9eH/BxMUMExAxXv9iOb6HwyLLf779x8hw3rmAE7s1565ZVaKSKB4dJ5VsTc1qC9ZL+V4s/EgC3htAwAdtRHQihbQkhmvwfhiTxxyk1pQvKqrUD5eVlrfKMgzYeFDYO2FKxJYZQSa6XhapZDJVNJqkAEoSXqS0BJoR+pDI6DLGGGCbdEw8U9d2xLAyEvEgOljuF1QRorbcbaqcFiMlMN1D2wC+mZyhBTqpN88taITBSIEez6+kEaBBbRB0gCCukrX/kKWiVmDcXeR6JhEZvra//sv6MjJAG+KJpUTBBUSpCTONWrJnGN5O7lhLD7aD+fBTg7CRW5GVrj1wjRm6MCTb+WG0/ZKMAhAmEIsxdDNB2SScQRWywdBgGbp6T5Q6jRrUJTOvqyiHgbrgQkhXDhmIA1uMxT0GaiwxgSUS8CPBxdTO92sGFLLLEJRCU5EpX4YyAQJcs1oc9LCYlcNYkipvia0So0SwouEHEwIVDkAIe/IRfVpHCVqMfUlrTqmWnCKDotV2eoaZACcAz/okyndchM/LAtTakoEQo8I0WqMcBRKLvECu4GApoARCQkM2bXhQdZGXKhIGAlAgZ8tEvd5i3VUtwkYDZnyiAd05JyW/8s5XF7+o7wQSwgEReINTWvCzWj0QozIpRgA8QvnrzhSMmZdFApAYiIRi0ZTI1UyGbukQFIIhoDtwZWuAAMI2Q+k/6zXjgNLKa+c4bYOY46vN1WDgM+yxJbFZPPCKp0cuTCjx1DDiUC5nAmpBh8ceoFHocCwKAQr5zR4X7Fij5Lh9hZwqecYkpGYfLT8Y0CIumMAOaBaqFbZsxZWDsU+jtyIrO1RijFnpT0a5ahQm/De7TEWAykB4MCfxIUaCpZcDhGHnmbCQ+LSr5HglPGbkM+JbcFQCU6O0+TTtgw8C0YIGRMRnBhAr+LKaAoZJrPqn5qOQCQfFF7D5EA585fQ1sE9oIk4U0ap7NQgZJGQzaQz2KWKEBYQV10NkZMtCIWkLlHCQ/SNLQCGHQIgoybCDFEk/PoNACVLJO74sIX7kVBpEYliFALQcgS2oiDCFnDfV6j1U7bG6vDKO9Xpnrj/+a4w03OqnuSNJ3pxYBFh6z/9VE3gZMSrHQ3unNEkS2RSgXlXPsdEJEsjN9FGCIdNI12nurHAQBuZoAv64zyYA1kHQ+q5uOSHXBgDLKYYyYuaZKFZyODdTLSflqRUyE4RSg5HQ3DmgBBavhILBvnoGQs2xU/EC1vg8d8dQHuZSquajR5HK0pv8G1naHUftk0MEExyHZjgn1AcwlfsO6OMB5oZDzoW95tD/858ofOcVvWTAowuM+i5/Hvik2vvfYa7SMisLSEPjqQuWiLG2IILr/yK7/SsdswtfsIESgZlH3f930fNYVBkjXIohAZ2vvU0omFIbSxykYV8Y7IxfE+ws9JwTDJ+1uDUpZlxpuAFLi/KG6LFL3pOsHzbwdT+L5Vmevg0sYXBleUQNy8GdRuwMrdunoaRLbEyStM69JlDQ4Kk2FHBy6KlwSwr4fnFDoj2EV6urgDoE6T4oWpENExEEtK+qyjinWVSj6BzLhqjKPKNSwMp65bcTsCwjSlaLsahpNhsW5eVAssjLYH40bWnazMc4E5vQn91COagAmIs3mgAUPTKOgcXvzIw3EOrVRiDXos9WVQyP0VOkqwqjXHEGZQ5j0A8w6oVApgrEmim5R6aukGxQ4IqRQ/P4f2F9r71Kc+RRChYWs16kKNJNIVnTkgYeXXf/3Xmb6pxmms91Mj3BAcYQcYKEiihySBRSHZZt7//vd3atkpJ9JS4lcFnvuEEvihhagRnVQttrtV0YCFtddqe6tz8vtBJhRYKsmox9pUS023kQyFODYhbYxoEiOoE9J+KfmViQiQiQziDoeKjOWtGQAgzEy7PPB0/bFzfAPKaJkoOrXTUz480e0LFiKNsoVUj9z065iLa55jkkaoyUjJMKzaFhQrCghDAkkiHKfeXPOXxIfdXeGO20MgPyskF4L9w1G5ITspW56U9vimQVjPstn+jSIKhgyVjQxMRUkMVgXTGWwRiKmCINEtkk+aVo9ErZBTjFUK/gR5Vv/i+aiUYEHIqFar3ou2Rz2rThVC8GItjIzaPicBWRj4koCiBINrr/WUIyVcGj/4wQ+2/H/+538Qj3JmhV/3dV/XPKcvTqqe295tf1meLjhTFYWkCjAhSd7783UIdQe8AzNwgEwtnRivB7Jqfxc9h97oerhIOejl0toeIUUinhgEIonATTMCcFZR1xHcxZ1MWZBpeaPBpJFFdy6b1NEumA3qk5lypFAhkigoQyiSXAJPEQc2vHMkvC1IpU8KpKIIa+qArpUeuXoADLZ/cl/P4AJgRYqWjl7yXXGOfU22hz8czRA78UnQuYPq1F3ZoOfwChWMXREN4dw8Pv/FV+2P6DRcnocDwxyUSsjowhMBgny75kLNA4uoV1IgkkfzHYafSYdagOkX+pdBFmbWPIir40FEHqqITWQA+MAHPsCUELL/+I//+OEPfxgKZxJ/Hgpjt6shmnETuZWPKeo+bBtcoMnsYIwFGm7wRlDjj/6o9vQO/ZItDsy7JNULvI5EIVhST4jZcohXDhdrjLPEZRWDET3VW151x8obAN9VVTtRoFIEMYv0lOPRFFYEOlcJvXdponSJgUncfPNNwgfDEOtund5KLIPkoZuYoNhIEBbxd99vK5XEAvjyAkDDhw32ex3EBVez+ewQUYV/NGUYYhYjuC8LTfizkHTrFs/sZPOIkqLdw6MjFkHefvsmbfN7Y7xsay7MH3Azi11U4PoF0zHqISxCiNZyrAq6v8QxKIEJLVy7fvNtvh4IvMNO7p9XchXjjrK8D4j5qefZWUa4C5Zr9Ma0zOS5q3LAI010qipS27Q3TYPms5tqNo1TtAJT44jmSBdtFLhFX3RK6jw6C7h3GAu2CpthXtlyjGGbYfFL+56i0grgGbIxT8SaG+bqGJRzytyzkY586VzyIwMeX5uCmfGjSRgtmZkwbMwbK6WbaODpicbP2sqoz4DFu0ku52DSY5eAg4K87RL7NhZwmlFC4sIkHs9v5+s+JK5D3IThFcmi6P3wRLcw00PRZ6DdNz5X34eDIE1YcFhZCaYL/GphvwhHPzKeeOdt91iN7Zz2rC0yoHrRksK8F1TDwIvpdF6YDhh7MwFAJNK4S9gxS407Ejuz5JTw14U6GUStN2/mndxRWcMctALpY9pjCpUQAGO+/XUtBolGYWZ8JUD5zjLuc3vJdSRFZN2uhfNFVQj2EZxsG+HuIX1p7KNHq2mkWSmQ8qUKTHeU+FfZiEd2k+9m0Cw2ia5CiQqceY2yHR1PClIheTras8G8yj5ZDdDpDNBYgMdmiFYEOIaKFLLa1W5i6IfFd0MsME9Wuofn5oW266iECb3cayQpVrdH1sJtGqYZa++2DwACE8gQWSUgkteSOeDZ7E01laalcZY4grEvgKkNmdp/yuPjiBpGogFAaDIHZSWkCfw/PB5vV7ce4Hi9MMfHBhYldSjgKAM0p5CSzxhR2qGqNggOEsyal5nQB965FedSacopJZXSspBpcymEhJIAMVUszQQeISOHsiiEG3ZK34hALegGNcMHJaRFpIw4ValJ8lppiZeSkPcwxAaQga2L9rIjQWegQyTsgufgl1ryk8kmYFWwRbqIVwFrdcHTyzBAIzx95jOfoXO4uclln6EWR5bn6GjmvMQsSsiTnp6YD8v5PtveEoo5e7Bw2CR/d2kLfEYexOAmWGn1wCyaJVtfKC50C0BMae2OU8co8SYczEt+8sCXwg63tCbFiu3oJdyVJz/px4XLqHzJGxcy5loE27MFy6B0y2DigUWWh/cYWDEqBZnrGNc62SeB39RTBiwVfLBxpAlfH+MgGWiRD5EhyE4cRKcuS7CWN4Hp+HYkyjwHksCcicxiZ/kUo+oYx9IRLoM/YDLgonjhMsHc4Qbe80WtFK6Ol0YDmBwr8YjzC7/wC1gGGYZR9CbG0+khkUsDSzlLDZdG8AcWJBZen+e4TNHMxp9XOXRrzPUTUaAQYGCa5E3hWakApbCcgkJgB3LHAbrQSCVTGPOpMoN3rjDkuUzbR8oTgjq7b0W3j0jWUhWBkZwoJrWMntocQiGxcpUsCUuNlo6PUDCTmuJ1ZOjr7qhGZwWllgzRjwmloo8HcSgDIuOU3Jvr1gSe20EOpn9gHR+5WHsrQ7C2WaH5ISyjvoz5ED10VBmP1GRqWXXv9JjJneygCf/I4Cm40HaElRMpIFH0lePMUzuJkbWxXENYlIvGlSQNlEhrR6/MYNqKq+MT1wDDKxJBio4mMR989dVXuYf4zd/8zV/4whco5w7jF7/4xe7YolefuIAPyzBGLHKteR7rIzSE0EVjNNR4VuvbPEpwIisyIwmNOdsIyijhz1SIwFmWQYdmmY4mBWQobRboXPrYKFYGwAZk8xRxkYBWFo7wbz3a/oH4GORKzcbhdTqe7oa3ZhPDpGet0TZpcElJ6MiUM+lEAz3NeGOWtq74itmgxzhoLv65kJaLAIQKVhSOaww50Ocfq5omyjibF5PFp7PEiTe6qvRH9+QEgMUdIGQDUXVMQu6YR33lu2VKPsPapYXCcEqjzOdXjhyXJFeZp6iBL3/5y+1xQhU9RYTiEzvf//3f/1//9V+EKqo4ZXGVHmSo5QzgWUnT3rS6WG+NXPFbRWZa785iWysQUJrozlyTg0gJBmTvgKd0ORxqpFE38UtqJ0OcRRbh0lpPm4Ku2ySNwoweLGDclJACNUdV5RuC8KWeI6SoJSnKJgXboYx0ZqJ+wY9bMz3Xz1MHBBloz3DZs7EAlK3tYFA5G4DI2XtVdI6rDQzdk9+tJkqcwFx5oUF7ABdlQ23hn5WRAhi5SkyFBnexraI5ph1Dz6NVMlPOSdmWrJ6YhVd/L4kG+AYiJkQwwnqJTWyAIGb97d/+7Xd8x3cwsCJUUcsCFovuGNQlkfmBxFg+EttDeIywR016Y5CYLYkJyypvCQohRMBrA7vjrEn3B/TyFLiEL3Up1uV0vAxh4pK+8kB2HDMGqGPuOUjHRJ3ThCGSoPrIA3h8M2Fkh+UbX3LTTKGSEmoAZpqzUCKLFIFobyJKOPRodmwhLZBSJgQS4Ri0KAEUBw7RzHh5/PJ4bQunAENaNoxgs87FkC+f/Ek0iGC9A1hIC7Sq1jJ3swDW6AiODIK9SL59k2J/4LTxSsX2BcUFvoWemLK8ZbNcZWOCx5GxKchh5JOELmNFRvdEBNLRtjx9JRZ87mTdLB1D9wNP8XgsqTyujk9dA/Q7/cUtQiaDXWv/z//8T9baCV7IRrTiSPDq6VOX9kEEwFC9nJJq5J7OpFMYfJepa9UWYp++C4GENlgS5hUY3KkzTyTSD/EQ7rznfQm+IYqfCfg6Gv4TOlj/KPfP8KkZ4AIPihV4Q97kJBiJIKV3mHiHDTMbtj5ZDBwSZzBFYCIPQLssmTzKm/e1wL5VhTHO3Dyha9m8TgkJLIKMmUQ0ogfwlSj11w5vMtI2IsiGBEJjG3kzbpyS1ijPdeD05tvd48AI84hFtcOjk7fftl1Mkk/zTceMz7ubw/2c8rQaAH8JRry5aoQ836iHjokc2e7gg7LG3Y6TwbUnmLGpO+UEm9eQQJI5gDbKIwhsEOE/6frp2G3vXocKROf5lTY/CHvbjY7a9OGBr/CznlgGTTQG9SP7I1uyaLILc7SbzVsJlBJ/YVJHNPQ4usKkaLcKiV89uA5AJwFfxJXnFIuELFxYeGLExDyuc7rziNNrrQKMRJ5VLY6gs/0KOt3rcFEJz2P3+MpjcoYi3QDzM8gk5d4UL06Jzu5ir3funPDhP0BolJ8C7V1vPJHuyFez7tw+JQLw5hGUCYwxC21nN6+GD+Sg3T+GCd69ybcN7uTlQnVq3pUOWCZM19jyBJZgs6PxQoQTH1ntSkYCVLJXPmvn+aSpocoqQ4RPyhHI5o1+5HEG6lKX2/8oV0KBMxaLwD6PFeE7BkRERKBFWJ6ul31YwBdFyWQ/5eOkdSMT5SHr2odVPOxDhvN2QMKhUzyjmzHOuDM1T5khT/XJy5U8U0ZDXgBQBQ2gwD/z1GyuPSpdRVjLvgy+P8jfAaio3BYgpmc7e6It8OtqwL7Wg2PO7MyQRgL6X+5EK3qdFwoKDCI9nZiEGEZtzSkMc2eAHn0hEx1HFzOEeejWq/jRWaodOj2S4e5e9yUQrYBp9Lkoo4Y5djkQrbZvpNEHLlPCgs++5KGSaGVf2Ph8IgXlaEyleUXFlKGUCDK1CgDaOzykj/CyvoWhoyTBZoIHUHWvlulTLbGC0UGL00erhAx8/RGSSNYyfdnSCVq8vgABJ2A54kFsKZD0fTNcogwa3FLrGIra/pzrO8Iikhgu0mpaFQJoY4hampB17tMEITLySCJoy3JKSBV0ORIlWHonDFGrBAiYT1wQPtKqNHKIG+RJU+I78pPN+tvmcepQyhgHvwYsxSBgHTdIU0mNYvO2N9vsNcINE5SIQu8NthZIbySykdmXi0aFYBEARzNnO3fwIbv6A+wXJjlQz7C8/Ut+jXEeXAdqv0bn5cYELgQJNCxLke+CFKew67jpwYkD2TAHi+/5nu/hOR5ia28UXojIpQCeDrKEoVG6wH55lLlA9IL6pgMItyDO8QtOcKB3+GZgUh0kVh14fZwOSY0OUPegMOWxef1tBktGTIwJkgJiLiRdAmIOmJOEM6UdoQoYuxu4+KPxNNvZiyz5cKjPMinL3kt9cxCsLydWLB3AHXSODrYj4c5jpTsKI8o8BaxoWBgrSsiEHVOImBhiLyO2CikTPZCKM+aUFoYfkGUGSSaScgnxew8AD5REHE6z70awUIMd9RkOuUgFsL+Vkk+jbAZqjPsllhH73fmhZpmNJzjaAgVrShvDfBrN2SIuZs9bBmW0s9owVBf1ZEHzIm0tot2USWWPEGBsxSAIN+ueKY7pnYuQDiw9SIRiPesf/uEfiHfQ/MZv/EZuKdqzz1yKwS2pUXjsdji2p9q4Vk7Ov9i/AyNL8MNcoxMg4nIFXtTIlEKOYzxF3tOOnragkuR/0zT9lOQwSzJiCom4WDA8dSY0JlvQwUvL3SrnhiMUtY8gaNxIJMEbZVnOAHtts6TH1HgqCn/CyAhNWqeqLBAKatv0e8N5iGqOsYzWLpvj1JKE2FJDJlILKTeBOOOC1PZ/3aQKVNHJiE+IPDlhSqyICV5IQgayegIUUr5VhIxIs6pngUq0igxlrcQBg4glq9VGXvXzQqVcsW0xWueIehm8VEUXOoILfImQp2tYESORZwZH2IJs4wssumpO1YMnKBOtIAjlX/3VX2XUxv7Sh5tdPjjTRw+JvfU3SWvDcbeadC2WI/Ur31NKAOatY4fHx351obZKEV0YPU+S+RsKJTLKZ0lPodn+QrEk8pQrzExbGVq1xFheY5cHsU0AoAlC7jrJojNH6NsYogbPETv7k1ctjWXp3r6jsGK0tnSQZyxngkDRYBYRBRfDm5G5m6bKKGDtaYSnrJ5SS6ljuXAtEY4jnGXOWN6gQ1P4sfIfNjFrDuMkLEQf3TMu7AqmLH49A8is38k3eqVuTfFsRYmREcufagTWqSanK5HP3Umo0MBV3MyAvK/8HrDn77QN7xH7SFdce+ONNz7/+c9fqLGxz0MWxXkMkCOhpPM+5oCEKjZV4VZEGSIO5gTAhYgDTIwDC5qg/9Zv/dbv/M7v0MVdzLooqacDr41rdaha19omq3SAHMaRM32qP808LpbJDWAQofld3+iUhmqKiyw1LLlkPUnStsdYJPwsHL0/g6MoQdQM+L8kJdowdmlsBSDcub6BPmxmwMetkARDyvpANzEgKryMhnFSMmzWoqTlyhFSMo0kpVkZRnhLlfxIBVr5nnIkBJL6Nogs9fl0DeV81B5a6gv2oWE7pWjIQMv8UXmRWPikSsOJWGHa4ygPVw62KiiscwBQzSIGhbRPdNf4o5coTnQ4Wq2GQSUThlZbwi/gQgSRwnLxVBQRSeZzKuQLk6pbm593yKA6IsK//uu//vAP//DD6QDDsONCkMwf/MEffPSjHy0pwhaBjMKHoEy0giZhi3EWLD7ykY+wkkX4K6OHIPg0UVDBVgnN50i5PdG0YArPKWvK3mgzGgBSh+/dOp8u0TOoEG6nFnN6K/DDE2bXUDIcARih/I1BxjjtgCsk45gEhYoWRGtFJG1E1QcFc2UmzqpQtQrhvWMgErUkgzILVT7KY2xh78YgKFHTbrIWJYwDFZ0AYgFohLuMPLuFTCCXE1c2rpMy8sODvneBRFVroSLtEINhBEpQIA8RCIUUuKsWcE9zHOWrzQAzgov/5M6gqyow2gGHVVlTCAt/vekwuYNiCt8yFXKUqcqdilOMhIOOcC9QikrSWXEATIee5b7eRVWAVbRHIIh60+ceeCSwRsaiOwtY5B9uWARZZpREK+hA5HOf+9xluz/4QBpbRh4bBoW2iJhj8xxJ9S8v0qh1JsoXFxSCel21wWlzq3Rbu6M8WUh0oU+/tveJGllY0k1WIo9HxJtGGTEoMx4imuV0MSGiIxjI8uNCVTkR/fCQKxO2BK7OtkkKETCqypczYgtg/mAagUPDKeUh00iVlNfmQafVHOHhqI97BAgEpyl9X4z11q03AYA0FHmjFjM1tASWHzgjYeTul/FW5cGxW2ZUBAn10hJHVDaJArVAalkuxYwOncT2O4ZwBwYBct8KdtwCgSMJ3MRzmCCbZKFq+BXYYSPL6zRY0mkaJcwnaUwVYMifCuVLjgd8zdBrkUkxk3qSshfo0D7FYmgzVtKW9/RCWhj2sI+DbjEJDJce/Pqv/3q2Nfzv//5vQSinkCriF0c4vvv4C1Ld9d69EWWH8LXhfbaX8gzDZgUZS8YFMN1cj1E57Yr9H2C7wxSzMk04ZnMhPcKEBUW5Q1rvM5Jxo80vA9bxuQ+WLwdi/RTwugKdy3HMnaPjl8C9fQsPyIK1ASgzpCyM3D71riIK1N1gbFJv/tF55E3vpSjHxCZI1I/0Prw17szghoVPAsvLX/M19Cb0btOn73sFsUFnpAMdw0hGUm6xxJehFkYU4rZvfeUriE2e+ZNenHhdYcbCUF2UowIJ6URgRpMUhqgXMWDyGw2a8ACDxdKaDW47037okBZwGZWF7OYP7a8qgJtWbZjsHcRN2hIBvuWgj/YT+zJXrbLoD1Jhoie0YeKypN0Ei1pg9FXakmvCHuOrk/emgSocJXPJZXDEzI5VLUiicIybctbj20GMv9pr5zEEhXEcDxVilgS4H/mRH4H4ecCXvFyLPSedWTUcJK463CROh8ZWkh5uMg2ecuy8utXaSbhqHlChytMzU/0ijIo7oBLCpJ9EFT4DNXokoc0xl1eRLvjk5Xw4G3zbHHyM7uulixJdjrE853nJH/kF4Kgqw3xAYMVxL1IMaWJAhElHci+9hDW4hLQmfWnkEhTStiQah5quHt0NRSfwVUHbBqOjFSMIduRJGlxGXqMq6m4EXIItImb4n2Mz5hfraKqtayFHThcdM/dYyT2ne6BXJ49GA0ziMAyCUfeOMoz69m//dsZZXY3qgAsTOnOAtpWgXQkYr23ARKn60z/9U4hvYZ6N/MbqYs4jBDQWoKumZdttFIV6UMNBXWATsHSoOZ9CUdUV8AQR6IBVyzdM9HI+A3157eltAlNY8SqJ4SnuBqmFBTVqS5NaORYmXMoU4JJaDSGjHAkdzShkWlcYjg0OBIjxfAyNlXpoNdRzF1rovCyVv7IJiYOXnXB1O7/1UZbHTeK0JdJ0bDfaWunDZD9YgF7WHBtSyIQmDXC0uQ++Y5UqeYUjkkcdacHcsREQMahCHqg5Qq4QUY9xmPlviCwwJacXZ0fuOF7l3psGeBiQ+4bQ+NKXvlRKfVcMkYtT5okdLnHpor849vp3P8/OHCknQ/hjmPahD32od4HuB77sJbXGSFnHiRl7XqMlQzn55WbDWzeI+gsQlsS8m8+xWHUTCiQ1hin19TCeh1CYJ/zlGh8iKXcW1eRpuU8ZdKu8lQzZgGF2gntRgtuFzA3ect1d3QAUpv0FsLfOMikuK/IrrZJy9AZf6tKM5MCHEwF6p4LI2JHehE/4bMBKIACYqjEmz6CN4KDD8+hACCrWlAJIxmuUGM+MKKsjPJdFpUpxAKKMiU6JSV1YVJE8ZrOZHUbKKhgC+LBgHoqmTPF4NGdJEnwpSWwvleZgsFdzdfKeNIBpdQmfYVGH+kwMoWin5OlFhvNEH6ooJH8esy7YUwtkbEEzaNQ7D+Vyld9ncks8ba+WPW17W7WsFzBMG89fwAtsZ88ACTFCBi8evnPi9xwaSniWkFrREWbjStBRhiRAhRlcfDKk6GMIvPEdg05EhxooDMHgDHSPlIUpEKaywB+7hgXiriG0kOWt3LTxhQUZXnEEHRJjH1ZoWQetwF93Dmgz1AgZLnSe8lW7E74ZkfsCcAU6eQNBoykNw/j6nvWQE3iTIuuIDuZDs/WpsgBGCLEKyYX10OAiVnnGafVbkCLEAZDQ3/QHThhOKSLJKiehWe67dc1ZReASXlUIP64Jz+qqSJpz+Q4EGsZQrHQQXLp6hYwaaxLRhx4hTtG5gOEV523RAhcwbhSywR2wWunla+4DSDRNFFAtv8Gi46BNPtkxwqrlc8RXat66DejhhlP5N2MofSr/U6PPY87g6fxWxQtSshsR1A+LUJGmM8ZlwMlYL6IqQGGgVo9TrOtuKgCLJbN59+bOrZMhDJDlOBAzsaUo5RAh1EQ8Z6+jRTMoUWA0sSJtaAa6dH83EDBmY6XO1bOkWhjkSEaiZiAbZqMQccGvCWY9K8JYtlQBIwZjFKnNJvL8MhGgFpn8zUpL2h5oJVmSJNPmAeBHPrKBanlm2iUDOMAcF24pcNokbhLw/i3BFl0dH5EGeJ6GKSHzOGIWgyw03w9MEJhYgeKUQMaxi1nnRStkAZfeJFoBCSlWxF5//fUf/MEffERiPlUy0/DQQ+Ug03ytep3WnjXopJ3QnNYvMPhZBS4+2Cm2/lkPXe6zQ96z/PpCnR3/gVpxoQoGtRKNLwtJYf2uvhaXpxaQ0hko8a9SoIRWmBgSTWEAJvJw6SriZOLpmKBW2lbIwKGay+eOtyGUmFcGlqY8fz3Ay/YkEHDqvAxCkRvgZOdhI7dtyy/6nBEqWoAUNwkUiYZFrattFiaNKzIgmX7OYv8CjEhR3BCPQprKkfKKIhyvgvC2Bo1zH5koDECv563NXf7nVutiI8JVegQawKJYvSLEMIDqKIkZIspn0Z1E7zRI9dkdYM5jSS8DDAWWvbiYEra+9Vu/9bu/+7vPg38q5Y03u6WQrRCObrbn2i3GS6OY1txTwSm7dHQHfCsGDwjwojgbGeGJZ6CDPq7cMWl9UzCdyeBiYdyBs+B56tDhnGTVgPRJFYEhs9Z2yfS3KGTMgafR0XoXrAk98xNHlaSsIo6zN0TSUQNMoZMeN1QZnoAEoIm8Aat3DYFjsxmgICsWXEFKIkMt7DEyiLIYf5LBPMiMkThzJ1cIw4ESKCAsS0hwk2EaTCsLwxFqJASxhBCWKIZMSs08VG1Txvd8DDD+mGrTAEI7e0hyXxZNw7R8kZk2HvCe+5eMrUUur9Ihr0gJVez+sDmKxLWCH/og9vPKIR45wjcop8/V8sHhDd4IR7WkrtKj04BdmaXZkuyY3e6OM6D5rnBhbLXGd+EMMGAAgEvYYmjGzoZ3gX/KVZh8fl2X0bCXU/DSFTSAR7AVHOOkPU5NErx8Gs2EMeuYWRICGjtlSsJD5AQbPMZQZfM45G9mMKe8sCE+QAWugZLJoFUyrC4ziMGb+MlxRjRF0jfhVSk6HgHE96T7zqx82QtJ7pyesOmSDJT9VFcGGIqQuHPj6MbJCW/N4/zODe7hug6Dixl0D44Oj19+he8iHxwdd7slW9NJSCql/FivZ7c7smEe2oav4PSZQDLrLqGDPciDJlcE4C1ixE6aFpm5iKU4k6xEXMxFyJl6CroUrKGgBFVTiY/SPOzU92FZNZOIEcBmjfanBGn5G7kmbGKZFxljG/Er62yceInxNxM0I0XIGaQiGn08GSgcWCS70wk+GDSbC0fuaOxITZJXfx+LBugp3mxFtOoMEXtjicqr9AMkLA104JkhPgD40wDZtyMMzjCBMdZW9ZWRtEN8lMo8gpc85upKavx9IzxUfE8WFUxEQigRjbePA5RHW2LYHhxMyU3zT97gmQReOdczcpRi6OFdKxAJ7U2yvSTZ8N+VIru88GHdNi0Rgq4kVrY5BaaK0RSxmXbpyg617MeVChYWCovGiLK8Ums8cyNGOl64BHUzrqonTjYYpxmWJwFP7OQX1GiHcgUd2hAgq0gDYWGtTBocpMgUdnBssgUzPygEvuxaJfcIMFASoskjA2lRHhIOzClqiBbsHrGVXF57kEOGqz+PQQP0AoMvnrCBNt3H0AkTH+Z+Prv2HZ0FLljErPNhL1nN9JGKNQ0zVlenqAUmrzXWrbZYwXFvczwUOouI8Ju0La/G0NUWhjwlu8Lwcihg4DQN4Io0i+Igo3ax6AhLeKSapTppEtxJY5SXtjgqSiF93XKOPmOTBBKVZMlY4EBjijWKAofow1ayxlacIR9t4Bys6i5yAM/pKilkSzA7VsLQR/lRaGQtbnitQ+HX6TajbFMFlANZacnAegvZ/I5+GPU0ku515EIUoCxmz0m2vwV0lXnMGmBUxWshCD1cLjvX64TxTLZY9SqvMXDKQ9qr8LJn6oFIWcOLVStzykeL7qlqkzZ+RwG62joXlox/dd5dUg0HlJNKoI4giw2vVbvkKfDuGOCeLuCS2sGsyJIiauUavohElzVfLFzMGSBeBuVEMQAMO4EfDhi1gCVKIMcrkimq54NAhsRyD+Sg5e089NKXJUCLUeiMu0v6JQrwJNYFrTIuMaM0SyHHTO08bbKW8qWICEqctSQSCgCWEQnxuJJAJCcpB0wGDaCjW3Ih4iXvFN5wdeOeVDEoVMh76vZPF+R+8dXZ49IACid97/d+L1c4uzUG+S4jJgwVX0WaWix5XOKv//qvH5d8j5yuRp6VjUmZJg935Yqe2ZOum1JWuSdU/qacHBqrRxfSY0YYzYzC/BENUvhRUIoLOn5mValQv9Is3xQAKbBkzk/W4n2ZEgpY4EoVgWFKeJl0WCw+IKbw6mTbnsF1GsVoITDOAl2y4ZRyYPiExNg7WjkKrTwNYSzo5FIGAok8t9M6nxaGpHyspqXZc+DXUGJVxvkF9JgZHoNFebMxteke1VBHSQs3VbNQoeFaAKNVAqK8SPfAZ6Jug41jQ0bobPVN+QijpRCRKJNLfxXy6vj4NUDX8L7j9NS4d96QdCZn7WGTME4Wbv/mb/5mU3a5s8o/jXbbFvIddNBCJi5Z3rElwkyUTcucohI86QAAQABJREFUPe0bP6rQqF3Vwo/0UE9JHvECLvNjrqcO4YWt70xdyK1uixus4o5jRRiUe5Ij3OVMaqOUYufOvik15cqUlBgYTE4dlxgczFaMEemMcYXnenbIpYkT4BYo0KwicAoWt/yotUmJc9vFcuGB6XhqMUUrLNWTeucAxEgsNQnONMvVY8s5JkoKGZoMkyTjHQst2PW5JDgMKosgOPZvAPz2hjsUQM3RLqN2oEpwL2ZBiqqdDAGYUk5G8/zq7+PTAJdDOo6NWuxpIFTV5M5j11hGx5Fp/4L77//+7+fBX7ry+OSSSvNN4qagK93EEW52keH0dt7KMI15oGiyDgi02yBaPsYjnscLcXJmWJOJHPnpg+gWGDRG3vp494Tb/VWx80yaixSFlT8OqCwWeCSecCRmCd/QFUbtTWCagGki+ODfFM6CxE9mde3WxByCGKJCgeTbjvjDhgFw4CGbJEbj0CLbG8zMEAkYFBrRaR70EwtjNwbFAssZ3iuEoRGaHLIcQEr9HFstGVcmAVU9Rv4x9uEkXVPakEDnypkYxO0QS7zTwN3HXbMXyWbAnS27p2aeUp0Wwb3yQr+9OyGu/j4hDdBZXWQYHXEWW6o69qcSA+aIqzDIOgv2UpYps/HCFNNsY22L/uXESoPnmBKNe1n3LucaVizWIQVusHQSJ8LJY/dFjD3jNgEcJGBqJVDDZ+P+gYd5fG2FrIi6fxDmvlREKsRcAMnQmFGSKMaBBXZEMgrZfi8/NITld9bh9Ed1Y7SyjsTDz6xrhmu+cIbzuwXEjUhtOVUshXIECe4YBNuldH30aTgb5cpsYVoI9VBw3g1BtkgF155AtPA2HxibC7MpE5lrdx3QudOkTQ28WPIVGgnhai2B0XyescwQTJEoZ9eGgY+1sEjFkUJ7q6z8cBkv4JGUqI5SBy/LTdwqNv5mLgzWVXq0GqCXUTiaV9W5hJLh9OMf/3g7QjPIlZJe6BX7TAEAw1apKlbtdnTlmQiXqtA2ZjkYJWQPxztG2/la3WmxQyEOu9wT4I8ELtGJ8ZTfCLzFlgGDthYbJ4/2Tnlpj6+7cnsjMWmMMzKWQdVdWkbtjYY4kqMiDd5dYHpMjT9uRXe1R5Zu7UEAOMrAZAluO+dqjikkrt81dJChg9hlRWBpbEnv2xwywNouiNIK5O/PYCtxqrEEju5GhSAJs4Efic4vxRv5giuub+F+QgVpofssbXAolC6AOevBwDFyKWfkZZoIg7LCylQpvesRSYhGG1pkpW+hBBZL8tx8oNE0jLyL/bOny6QCqL4KELVKmRR2kovO91c1CxGYe1s/q67+PpQGMFq6kqsg9lcCZBi5c/zt3/5teoP5INYJDLUL5n5WfWEpiFgR1AD42Z/92ftt9X7EZ6DkPo9DZhTCUnH8Ds0QeDzG3Ou5GbmgPoKR2wOmOWcxZ0xYIMHrEk6IYjjQNOu4ozqJb9XtPKXceKH7OzToVYEuW7IRJQEQlL8mO8uxkaztPocCVlFulEhvDnp1RhDdQykURwnFi/07B0wWTmAKSbuNeZxQV9HIwMb6OLNIlTgASMNG1IgyPkxWXIFKJK1q09KOoNtaV9XkwdLDkYrmHkBUI0DT0HVCW8NNpMgqrJjpnnKJhGO6fCACwzBogjWJ2XLyHJtZ5ZWzhalM10finlq1obNDvMq9Nw1gV+1iIhfPAxJrmj7xiU+wW52qRqt2DfHoPG68aHRcdfMUCAsXf/Inf8JjPTzfcx7KM1Ze/5lC7xlkjbM66jW4oWRF+XH5H1ZtxMklnXrf9G6AmHTjHXGarEc3ZAAyIRyd5FPzehbeV0ahZoSKkNaQOCJMWBOmpOBQZP6IpJRm5mQAySkh2N3za1C0wmilmjIO+ikcS1nwJqEBh23ZOQVFTkPZA3kSFHosCcunjkCvcDTJIIXcU1aAhee3UsZxC0Wi0OLai3YmmPzCEVwgpaBOdkTIezpherqwFqsS6anwbQJYQVxgi28BBtY9MDvoq9xDaoDt7MUkPLG+TrRiezqR63d/93e/+MUvYn3ErG7CWp1+HidwsRrCFisVDYLt3/Pgn4lyDa9Wl2PtmaPO0h82PH87FQEcT6wXjJa2cJKgkFrO7ndnCqktYDNSaCicLm8JadJU1WHWYilDd+1iRVSGvczvyICCX4dFgQFsku+mXILxdNoFQKVa9MlQ37fxEWscs9GawgHKs0NbhEJzpFA15cU4uR3HspnhR5mathIY0fIAZIhnSOtoFkaiLHiuBFG3HPm/aUZ04pNTR4dHGYA6U+BlWqI61+Zj9DYsYIllzs/tFRvniI7CZESziAbmchMZEgoxBCSSYJK4MzcyV38enQYIUiXGZwQJXoyhyPAOP4LUBz/4QUxrRTRiEJ1FCDuPOZC1bAZWH/jABxhz9dVa58E/c+V1BHySxQ6+LRFD1p5nJg3CpoFrtGINq26F0vBfEYF1ZkNCVxRylw13XWFCl4hnYPS6xkz1As5cGtPnkvSk4SkAkONI4q+BJhToL7EilXxnSHFxKqJ7nEzJMzxiNS5ytjiMQoqcT/qaxh8kZBXLZ3yyftc6BSI3jxY232req8U1zY99QTQTsQYH5Y7oAqcZxFXyNCRN2tAMIXaMDRYLK4yQifIqtKzVUeKPcoT2LPe8CkKRC6zAUZYApArQfE8p2bVK0TJSG02Y8BRGpIV4lXkkGqCLh4Fcu8ZbFtqb7HEn6JDHr6ilWzvOOo8jTx0yLiPecdeIDDZMCYM1wt95KM9ceTWD2FWXFru8LF6Dy8UpNi2LxaI95tZF3DNhBxa5wE8MWfSXyzSMjGsZiAlClYyGC8O+7ADL+lkW0tyemdlVes6bA63OYn9o2KeTFH89bdPIJQ5k6roVafrsABNJOUnTdBALO0qwgBzdn1pJN0FNMWJqgjWiL962aiTACkwGxRnYu+PeAO9skR8ZqqRGqzhOCy4u6OXOH38hh0grlaDHUAa4MIoY7qMkMrekR8AQZ0ec8+CuWjIrL81SNneVHpkG6He6ko74sz/7s/YUp6+++iozOy6fNYyvyoxQRQKMaEVoY4zGqwGfg2ilQvqbhjrMlaZi28vRaqktAbIvXQBxAcR0xY0DD30mHtUFetzqec/y44NIos8nTYb+BWtJxSn1OzrLzQMhl0YrxJ87EIrLcdFZ1EoHmpHaw6hK02Dk86XFXIwLgW6WEFQ19Taf8rnWpCoCY/xSrKWszNHGGX+CTJSWpKVSxkY5NmBbUhhDO2PLzPsUMeRDgRwgORDmUwEyq+zwdW4YrWV66NZWcH1EKeSJyZ76B6i0dq7ywW5wUAAZTIFSvHeSkqvDe9UAwYW1J2ITVkRs4k1+zOywJQZKZFgyXy/t6xKV17yzEnGKkT5YTANrscAT7yg8C/xpl2FnG2vaZBFs4+0JBFmrdoMOoatHDZiU910BUmLUk0GNY0MDioojCBjHVC04E3lmhRkf4Co+YeKKeD03niLp8ElG3+Gnr6VW75F7qDnUKBQbj8j7Rpikug+dFRmBdfVKMulmQPB3at1hMX2fDLXBRgNVSZiGgXFJycOa2rJxZFeBUuGaFLsZHO05LK9kcKScH+qBCoy9tUeJ10ITACTX2Na4CVFPx3tKfTczr1EPvOOpJgIcZBgQMqeD5w0+JejakhpGUL6zhqygQNY44ohU+NtI5WLXEfSyH0MJIZGOY+pZ9NG7aRdYSEw9Q0legcYOK8SuwFFWs4e27dbda9xq9wVB8ylN9DBfIV1VvAhH9I9S0CSxoO1l1raCyINroPZDBCGygMW3bX7jN36DeR+hCuKELSyH8q5YLbAto8IAXKbIg+m5HDFLoADid33Xd1EOzOWNVm0ARpifRo/V0gp/OhULtLwu+uDQHYusTvuKuldeuXGUh2fjhXicfoPpg4hz1ZO5+uKoBGi2irvAkrtyaxo0X3WvB6VDCQAyjsnjDyP8Bd6FpOgQlcoFV+oTLZzPt3UqAAkAOk6vvH708ss1FXuEyRqPcxIEOghwIejGcd4oe/vmCbcCwbl9cnrz7bd9J10TbwG7yRu9TFhdksroD1Ze0JIOD475EXH4mnVeUjObAQ5N6hFRQsLNYIawxi90lQsC5Gx8C40ZfjBg4VoV5SIY0rS+FEAplo1MSsYW9IwQaq6RN5j0KXwIVEWkEuAAhS/nQ4wQWAeuJF5zIBXi7BQl+vC0A210id1CCIud8C2w8HIhflHrK8PSx4vki5BBP3Q9SsD/m+cFVbzJU4VcMIFC72NyUGtMIX9BGn4UB3TiGoGPYNdpIGRLk4V2Ctm6xVo+xC9bzJo2vd/o2h2mh90SaTnGgFFXE9FC18uwYtU6lmJcFOBhlfSIDotK5/2r9lHcQlIZoMnbbGQx8DEpmV2JEiGYUYLk4xXCh4uBy/GDowQSF37cgSAiCpP6Uy88Gb0AlE2tYrKsH2Ec1fBMEQM6X0nK/Tu6BsR6sRRMNCdjEfgktZwjCRsED+7UJMYaviASihlYAkSdhkXbBsXZ1NVgytFRRmsAl1x44+y2hCJ/0Y7HZAqggIssJ+pfjqokKMXag1mYwW3VFria7bG1HM1UzrTLPGLYtfBM9KqE+7ItVoMC51tpV/XznsEm2hF0KKrud2iICBdtN0vg2BKjJLsjwx8oQ/CidAhVJMQgEa3++7//GwrQRLyPfOQjsGBQ1nHZuv94URZPEx7lxBFoUX0BYdCSiqp91ginrdY4q1IB+KVoa6vQaTqjXRPfqiL20p1+gSn6BJcqPAWQSUkn1YNyXu49LoBBr23hOBulYLn+SWHGGTIkKNCJzct0hcsUAd/CxY4MadyqG3VOwsatTRBI4sKP2VkSZ7TIwjCAZxANkwCXSGsDpKUiE1eUlYBp2t0lnIJCxObtJ4Ap4LgEy6kzVi8ggN+HoqSg5PIieklamlxLJlmFST+0P9ouIO0wfij0Ui6J7CvpEZ+hEnqTjmuIYThD5qI8GJcVBWVCDSKodBnog1NjANVhGmvqhKTGJmh+y7d8C998JuOr4N98kykn27iAfHDKlwISm9wYsNYYexzWiIi0UFPXRmOnOlNKatY2wtP4myeBa6GUdWfmECYLHQE5JdW89ZGEJyG4qGdw1I/Rx6+xAsSgz0CShXLKlN4kjYhARZwFcyFTvvQyQycSJeZd6fLlPwEY7iykbCOYOjBR2ETpHbZxQDnEKy3BFL55HxbV7HlhNUo/NWC1DuQUGLDIS5u2pak0mfNBvlUMzaCQkAldcZFgAC/AXaaMOJdmgIVXbGUcQ8ecO4LeNGZHYj8HnT2wSJKZOQSdDAJOM5lZq/oStEGwzwVkn9oLe0bX0/aaCJlOwSi8aKxhCZxVJ+gwOuNIwmRR9l4fPYCWmQl2MsgIi7hZedi+QJCCJgQLQPB6iKj6APwfJ4hGGC+d5r1TznSK5WPYaD2wbg0kPkJHuXqu5+v6O1k5UdV1HINRE2DGmvg5GRfgO/Bx85TTI50aoCkPWCEbfNSdKr3b/44hAGgvWACwVXwJNIOeOV6DQmsrgwTzg5MxUY4SCW1bAXCYCl5JOCVhhNRlYikrJSMtIWq4Ox5d26e1xy8HUGJhtouLUF9mXVKc3zo5dQlsCgRMdQJAiUcmDiaKFAChE1lZ/CPRHo59fxYAltyfQrQ0Ww+djA93oNaiIFcMZbTSkAS+8pI4JaqYX7x3Qb4IGfq9QQElNE6hrtWtD64BJoOkKhNSEHm4gNLbiHQHHYpgDLiIUMiDbF26IjK2B2Fhp8dzHlzOpwZZM9Umd45AE4Y8esEmBk2zrD4HEIWWb215toZylrR1ljHUKBeYFaIaG9BwJfmsYlZOUGIjDrBdhJruQjmAYBkcUDSRZRNc1Dy/NAcwsLdcwAUxIoVcIIQlEwf3T1IzvN4KdFbzFhHLK0ExrM1dGBgvZHFmkprhxqRYkWzxwB7BAhciAiTZhnMSVaQFuaCkHvRm7jkWrOItIS3cyLPQ7c6EIYlUlVFKAcSCRKx8S0rgyj9bIeQLk1ZYQQl0EMOidlO0coEDCsMSGGQRYmpm0HmIneiVh/kgRH7xF3/x277t26AMKY7MELs5vlFsRa5nrK9iurFEAy7Cq67YrQ2JEWqfgUjB6IVWrS4R+KslaDAHAoWuIekguctPSQWQd2Sohi3Maf1rWYJ8ZnkLKQBWgnGoNqE0zVOe+FVpKeGS09pWQQR59kjJo+IAbkrBNdcmcuJePkzMSRM20jULValxVIYW5uUICZVgRo4lliz7HeUQlT3ED48cYbU9U2jbT1mbwV9PKLNzwCKMydeiDDJzJ5fvAxWeYhJMR1AUKVkz5kJVauTQyx1ui9wi8LuBgpIwCfcQUfhMfB1M8S7V7tNKlV3Cb96BCdvn/4Ax2AVZw+pQ6+HarDllV2fRCXxQ5qbeRakxTGP291d/9Vc//uM/zgIW+Q6soEYV61YQJNNNGOnci3J4qvAx2kpQP2qe1nFnzXwArMIUfYKlZfxtNufbQ+y5xo9XQQcCTJzo0NB3IyjDEm7fgnTdfRS+cZTO6lCklET3kuDWIjyIM7cKQIIKElUsERx7OwWiRYmAN1jJuns6HAZAZbEFZgYia2RwrH9ZGAnZqTHHLkA2lnH5CU03IZHRIoFhSsgfzst1hVtfphO61ZfMoD3ZAO+NVeQOdduT93tkFOew8PDllyXPZDBfauKLmdA56L4HX/pzwOYcBqzQIdkkg5OnyIbyPGFzQzIWZcmfSEhLnLPn6kr05IlCiDBV4P1fpdOqISvRUqdh98YNnvLIfjbuIt8+fOkVJtk2RzgbBRbudO3Yr6chhNzbUv5UmJS8OAetuL3/HtpsZ23SuARuSu7PMmLqdK/LVaAwdPrlX/7lP/zDP2RiyCCLaAUAeYgjIUEKGDoZ44ZaOTZQ3k/80pWgYawPe8Oex1f5vC2r5hk5YJCJEYitmQKDn8Zo65IxVJD7EN8MXrXq7BXQGXUApjtB1MvcfcBUUQoxdapUF8SJKVlEikNEVTqC7il3SjllTJRRBC7JPjpdHvcfu70Uu5rHteOGBin3iNkAXYzeYaxOEKBpbSbwODffWOW1dHwiCUDKSaXDCXxPr9+p5bgAigbYsxlZEVYfJjRwsWrHAwFm30RaWraTtt04dLVve+ePatqTYR4g1MIDxmx8MlKAEgCbTdKOswHCYJJprTgjTAiippIsb0w3MrJPjVKIhA7CuzWNoCRR1FqssGgZI7uG//STgYu4BqSIm6tTqIVdujCMZEYi728aQ4CuDo9LA8Smbp5g2ogFEp4YPf3FX/zF7//+78OSOEUU49vObGuICfgOLAZcmOuXv/zljryGoT8uAR81XeyfCy0bRYks2TJKu2iCBtkfDGOBNcVhhi3xDtsuCdASMyQr9btEm/qMNJtCbp6MMv5QbE3mOqM0iqZoiKTHJXK1Os4blHLQJcl1EwH8OZepfJVW6kQ1gl0mg4ah7JNnNxf14oZRCXL0ZmYEaJUSBp095runt9AXdjBCFSdZlgcUSGyI/4YbGIQ6pZCo8G2uDYtk8GieDEQMTI0UjE1zs1ysSFOwHksKRpLtD3bNpCeKUdRI510D5emv+D12YAkuCZiCkY8Y98OrJn7RCPmmUro6PjENsHUL82PaSLTCCLkV+NM//dN9OvonfuInEOP111+nnIkqHcTbaRhwEa0wGMZcxCwKQXxi0j4CRvGX0pneMP5qok2xRbOzpMbJkRJSXa+F2nDSoLK8o6U5YuMDOK66auqzAzFkdb3ppsODKN+IAamFriT84vglYlXdKvwMJnFaGDUVzMCSVQgBMnmshAM3kVfiiUJUyRKCzTiEZP7Gteydd9xBPwel1BIRm5Yc4IDoaRJ55KgQWBWJU+IfMUWBYURt8933vI87ydgL5oMCX9pDgjVlJV7IXX4qRaTEULDAHgClVpxC7ueVbabW7B236HsVVyePWAOEIUZYjJhKl8hFD7JllPiFLX32s5/l9LXXXqNzOcVOMVHy3/AN30CeDMGr+0sfsViPj1zDATMdvOz0tO6KqQ+G9Q6OseMlRU11nGKc/Kb18nev/B7TjfEv2EJCe1Gu8y52C1KYcDF+hYgoiSyLSGQcsayI+iDw/BKPOC2W1BIHaC9zQ3p5VIVWcUuWPOgeZxW4CHmDCNXgYl3GUAQJqDg7JUwkD2joy0EYQIEIubaTAhJgK0OtUSaCUijTjHTK1YWqKILTe5IEC0luJrhDAEiOZTGOUxFSSyovIGmUHIOgGIVcQJyGROrNlXiPFJqZNIt0dXysGmCUhPmyLEWCEdEHE6KEPH3BlJDMpz/9aSzhm77pm8gDhnUwKCNPXxPvWAJ7//vfz+kzlvCOdX2d5k2JvySar0ecmTYmqsWuNHFLJ5buoT67oO7JFEJ1z4SGyQoGQZATDYpV1yxg6sccZeRnQxZrLkWsN42YUPGCXBaVbYl3T2E5Ak7vu4ZFNVPLcgKTTKWUSvZbUgJo4wgLUMUvWCDdvSUPw1meYk4juVyg5p2qoRxeTrEB2JHJ6WB6nWUv65nbyyBxxJuNqCuPjBATDT0DGQmtg5oEXcnaLWYVJJNKor3lBY4qEdiVuE1jpUATsuUtmpTwVXpiGiBCLV4YG/GLPmqcWsMuYIhTTAz//u///sMf/jATQMZZbKkHoC+WIWYtIpc9o2N4HWUv7K2D446tcKKd2DFOT6d5a+1a+vi/IOuDLbcQuDpCPG6BNVPbnsB6TVHwEbAMUJzn4L0wlumnm4RqYeN08co6SQSQr6hsHA3/kKmoejF9FAoepDITfc0alryLPuWjvkUUtIoS8oc85K73NmW5jqyuSz0htcOoNgCK+D95IGhbWaJiCSeytIoj+xtSwkiKhfdBG3R+kxR3L5cc1ZL0QqqZkI8KOKyx21wDD808xtz4VbLBqYRZZY9qbI//oeJvo65RE1pDsFKIIEp7lZ6UBohQXYHyKnrI2wqMX7zliqETiaEWwygKqSIq/cAP/ACdVidnkLUiWrv5SYn83vjoC9PgtWHTzo963mMcB0fkHl0tVlutbWqiWraRrj+IxPtj7x6aqhkcQRJxiEWkTAsgcGvrVhmUiWAk83YjwIQLoNjBFNjBYg+diooXUvVuuo+eBbmQ0KG1NArJbYRsK7JHRWpA7BAnt4DhW+7+AZpEBiPAJpjOgQZEgawjEPJbekkDHHOFDYgaDTEI/AQ1h23cJ1z7OwCjnatj5uIUwLDoUV6sUDCfd2KfB9ahn6akCWlWG2fz7CG4gOVdiLTfhjbDtcvNENzNzO6VKE78qNdM423ewBozGHqXHS9zAJUd8fZLmKb06vBYNcBgKr2nBWFu3DQkMcWzf2OvDWEYPUtdxC/Mq3lqOW2wW5HrsYr64MRrPRmQbJBy7v1BjC5btWkAzQGCxupr3DSvxWLBO5Pm8ryxRgGwTv4ZSgpfZ4SOXkDC+FO1CIa4hwG5MoS8BBTFoDBRCbfsilBIjbUncCHeTlmMJCi7kB0OaME2pYFjSzno9LKBhjiz0Q4wAVMP4CooKaGmTEVq2zg2Mz5y77YpdyTwpjUwFTBzNFrD1gv3YSbBEhhocneRAAMfN3bwMukjyfoWanY+8SnD3IgUDFUgSiZ6rjGFtLHGbQ3ppFu8MvXYdgNKYReaiCDuViHkMnbzdUC+iisbJnhE8i6zWrsOCem8vnyCyMjElTbbbPXogI/P9BBPj04IhbdZGWHTBS/Wwj0svc3u1kNej+OdAVI3XsAJg5LCi5RoPqokBNCD2BMDHyJFCx9CDXQ6Ha31YP1ZeIIsIybyXTVvntOaHzM+mAJMtOouB206nsyRVHgCUwVjlwPr7tAHETkpLNhlPGKk/GKUtxkhOBXCPv1IGRUGmGzi0e8wTrZJ38lGZzBwK1ZX2O2JZQJ3wPvjjnijwJ3bJ7idl2tA3CBtoqd4IRShHHqchqGexeO0Op6UDjF/F6Pxi8aFjEXwhCiNj3UewoSO4wAFIHmD3PUj94jhSGUxNlgR5hqkHBskxLDJSxFlKH2JUKBoui5321yUhND1E3aQMt4AAHtjK9X1PGrKECeDJ2yG2IIMxAaaBu7tO0QYW4T0rmu6R8mjzJqAJs0z/3rqwOPgFtyllWmgSKbiFsHTlBtihHW8FWoDzJbYYZyG6Y0RN+VSuTJhBAdEVMzUNCPQAIc41OzkqAkWidOWSZMLizCJVhyVCfu4c+s6dsDHv48y6tIO4G4zuu+0uJ4qvKT2Wk/ZC5FQOP5PmCBDg4kdWP+//du//eZv/uaF2g8WYYUgwtMzvGOPJSeObD5oTCEeYZQMoJjfEYNgBzxVDJTQf6uAoRxhzuQLZe4MgkvgQ0gQL3m02rYCC9sY11hUAYC2e+F39pBlY1ZUDEBuCMCxvXx65C2TQHH/3RB2mGGXfjUTYQnzTSycTLBmBqTwZP7Fwxzp2fhIADB4lWxesx/GTwZed72gZ7jgXlYCVqZE2AdjmVAQGrJFc80L6BAZxzRbObtv3LdBzOgGfZw9E722nZomTiukrhi1IFhlGzfyKEzVQCHf6i0JASoKzRsByLLyMCC1duFaOWKK7Kkl9IB7N49Z2sRJkKopK5eHDOhippSHJliUC5OBXhkxXKbEvD8OuZxAE5WlHHDzJo8AoLh5F6GsMxdOTcCUFiwhS3aUvnB/lhIauf7jP/7jj/7oj96LFuyLdAFfmvjSl770a7/2a5/61KdKEBbN9I00hDAiHQbDsVhn8iVOEf6oYjBIZwHZFXqGWmfCX9LCnYlOATE80jwOx6n7UA48Tu4b/og/BBQdO7aa2RZxTUR9LUOcukaOFBJVrjNQIWQYIuWSIKWSGR/0xTJc+cvaSkjpmINFEahOYuADolWU42fOrkbktaQxMRebuhMXJNsicGZDeFleXxhYyoWCIKn0yQTWEujPZt51azsWwzWKoECyPqn49xTCjPJyVSlJntKy6pRaCmlGfuSRDnpChGwJyoiRJ6NQmkRtUJCJtCKuKEmt5FjBwKWYU45SDkePKwVuhVR5La5jjWB2ZDq79KVQxBAv/UXyxclgDKvtGBmao4Sg8BAaABe7ImFjHUah4G5E+MxnPhNlX/+nf/qnUoYFibEV7IAn7gBAyXl8GVIR2gADGKw///M/R9pnL1rRPB1yJM8w7zrFLK8GdJb6S+zfwnh+O8vjvgtkUMbOnoQwPKZkOSZqlJ9EgjX57/4qVcRooIE+fYkpAMGqD/P8gta56uOVnO6mqujp/HEqBewhoQa2eDolQiZPD+r7y/UyzAeeVEYczWONxQTXNictCDPRZQmJk5g6RmPV0QoBo7Q0vvoR9gDx9oih6HBHhgPWsIx4WeFiQheOd05pjJNWJdokT5FaSTiY21TemwUAkD18QCybWIXYw7sXfK/yOT3BRjE1AgcZVIKShxVepL30L7hQAKnHYlPIXlAGWUQcynlrKCXYK1M87glyJLRRQhgCnsx5PMFlSAUiABx/8id/khKY1u7Pw7pc5futa2PRtm0enseZLhjPxhT1Wrbe+Dr2VhCIco+CJR0aXmOtylhNHnYdGjY8viKisair+0PFFE29DYULBAKzSwOLoUS8jlcitjNEYaTgIvOmysIAm0kWmF67EjDvMNl3RQj5EgSkgJmZD3dOZyxmlUvBcossJK8z1WJGnD1WIU1LmsoJIDLLbhQrJjhkbR3V4QHL/qzNj1OHWtROSNhvk+UFRlyoJ6BO2KE7YUIhfMJrc2pt0+RSYKlN4W20NwN2V4bBtEIGbEskqGnCpP1C/UXFVR1xqp21NP/gGcIHuFAgrBCbCEPkq0aeFqSkAzeMjUJO//iP/5glrcIwUAKX8oVyv/5bBXFWsiAFgG7wDKWa677AVa8GnN84DUzzqoWqadjVEvXUllIzuCkXnDWDWY6QheMRXITcYJW+xzntaAm6FR1OuY1IoVEmXbncpBnB8hCLMEWWmAnZWCvvMKqnhsy8jrFYOH4TkOan4dWKQmOEkbxx1KAhvMgJWzY+TKMKmbccidpIIN14SXlQkhGpFHbwBjg/BgHxNkFxIZaTAocC2REZEdGTnkoyNA185kvZJXYBvP/tRaAypFqgplkoTHuTTNxjQoy/gyZnyJabxHBH4B3ZexCe61M6qP7fVqIK9ENqjzx40yECFr25naYNxeYWIaTqDDwzyM2+j33sY8wWf/7nf55IRPwKT59wPi9mIScwrGRxMxGy4BK8vvM7v/Of//mfH1zIpwy53KeG3TZTuEmqnS5ILzi/w0Tj/5R7j42rgl44NnUTHkTV1e7wPMqGDDQgYq2ZsOjR87rYLKdEdyZ5ZOATOuSND8MBRUq4GNTmpswgBZcKCSbKTGqEvJOxzMVaNEFBL6sYZEjtUxCp7GqAV7MZVUp8N0XsOfgYGbGQzC5hHNVFgGgS1KFra5MotimRzGN+KVB6QCLPJgQsrOJHWbIAJ4wGfMiSHy5Uim2/LIf6kp2HjQxDEmrgkhk4hIZUgMEov/BMT5dinBMMsCbRF+hvO4QGM2DBgFA+1kOaun/Qv12QAnr2sDYAHcopYerXaIWlEa2YAGJ1v/RLv0SGWlhz7EDsXVQPDKENIQlbnUt+7nOfexf4y1i1MeY98TbORTNJ9alGq/pd4MfVXYAEns7OOGWnkZMhvWkLE1I4To0fEhaY2jsce7qEoV8EzvITXQYANJnD1w5QfpNgsMsMvdSETCp1vwmWgXAdHHS6no5bsQJYCiVenXCM8WAzkCJBBxhk6JKq+4aNU4yrGcaz9ebaXTZh0Q4ALGfmCIlT3nX1teyrrCjhQFt8vID9npwiveJm4a0M7mYp5FaH6+wDAdM3VLG3IloDR4FsVAUl4wLWadb8IipUJS6ifYI8fLlNsAS3oYVIxG1IiDDogioHafKfY642VjF8OOA1fRlMMUFRdD7EeIAMLPoFy54DkCbb2XaPnF+chLroRJTAJO6RtNoOSYr61Sa6Vb2b1Msp0cfOyiWTknd/MBAJSwC7JTXf+4xYSL2IJkBnCbBheAmyGLM7BvpqduUhPxrVVRccxFnYrQyhbnPbgrkK75j00Zd6Mv5/wLNk6tMVq8ygIZG253ocorhZ1pvcBeRlOxEBvwCsO6QsN96p+eqKU1LOWEvxLVRQIiSRyJgyAACGkMOcn+ne8SuvIAb507ffxsukQ3WWeZyrgZhoJd14O9wtzBoca1oHLx255ZNNlTyoxIIAPZq4oeQEqeOxogoLX7uFmkhkZAPdPBBve2JqYeFNPUPDXAqVXw0xQcqWzFPKqd2mBgJn1PzSeGAgS5NsFccE1xLkFGGsSio1Yke1Rlkpw5HkxDqJhvFzlQoxKkkDdqnMY4lLvywQNUst0ByyTfGkQyG/q/RENECneL29du33fu/3mNwx1Hq4fVW8cCaGcYcNpYzU6Md3D3xPpHFnMYmhDnPlz0xngVpmo/LDJhsRiqHpzsTmRk4J+LgA7ua3Y4jkZBI40DCp7gNukchAGR8qNQpX1aS6+VufrfvEE/Gj+g5YEAdUd+ZHVOowJO6s788EwEiB8WKzbiwmSiIBInHV8ULEOleMIbI7eMp3rkOrLfers3P/+mThX3iAwxHJVApqos0VjhICIfn9VBUICfqcWRSMQkjtg4+zUe6tElmQZLQUEYXSHpKUK8aEKZiXEbQQrHEMbSiT2kzDXwVYxIM8KATy/haFzNXhsWiAfkHrBJdPfOIT7SbyDWEX4tf98WzRInIR+Mhw81GvuISpdsvxHF/YiqzdFn5bmqihj4QCMCRPk0aGP0nbWjRcdx40g1UwUMksJqswPuGhsYMMVfga0YWSjmQJfAtxmwF4cb+HIGBQlBRNaMBKW/hGNK8QYgUUyiyDvvXmmzffeotRWN7WwPgoY50VkqQSfDLlREZONCyfTbadQIS0jVstTElqRq3j2E2itOEHsiUC1dIuVE7DndIWKUm4hY8A4IaRx5EJaBhTQkP8yo5CchiiljWRzm39Yz6RdmaRj2uTZOdbK6DgVcL+2Eh/lX2cGuBKSXDpshQhBjMlf1GG3DSk79iiBeLyHzv9sqWd6WrDyEzCRL+KmALkN3wD87Zpw63iSfoNTlYAjL+/6U2MW4Cvl0kqwyJOXYcBsmgJHMJYIvGtVMVlMZ4M3URM4Y2pLHnyZAMapyUFphaqoufISemn3ANzVSg78siQajFyhyYBDgD4HjoZZOrK6FItORZhqSK0qIA98azrTVIEb4qerHKHU5SRoiraZodIZKrAHgXZacTYL3q6xxlsUTY0ASeQDbBJpkRE3CUUkS2mW76h1vD6Lga6T2dH8Sr3dDWA+WF7jI+IMn/5l3/J2EpLvXhiJvhTP/VT9DJjK8yAqMd6PFZ6cUpPEEMT3wsK9/MWoL/U0cA1kuiMLzR2MJwaAWl4jp5kIcTC8Co6dAp5j+cuAQrMKZAm3DM/0LnAU0CVMKFprnx7Su3WnQMmMAn04EIBkaSWRAYACpU8mwEJSsrOMQHKaWGbRKHsGdStCW0ollBQnGrJD1rl2liTxeshAShQSapGik7hOF0KasWko/RhByo1o1UD2dNVbtXEGmAtiVQtKXDBVkkL234JTzoI5qW4/RnKQFKori/hlXnq5Dn7SxcQYogvZD72sY8xtrJTLp7YkvrJT34Sq2ao1QEaa2HDTi5O7TFiYOexsa3rDrs9i6tVm984ne5dRJo5Wsp5HI6DZryf6omtgiZJhtOnyAwiFLZqydPTiKGDdIGl1xXez0dwyE1e40tSXYwsTgfNUdqIGe9rCZ3VWvlCFrbIzEMOjqt4ecJJ55vIyamXtUIjgQOT+C2EGjYi8wglzROf4ZhmqhIKQSeJmBOPqfav5ROdfFJxuw5nIDVQZp4YPECk1ggVBYEfgmte6LmUyqVKTNPdk0WxdbMDJlMKAOc/wrcDyVehJS9K2VW+AFt4lZ6IBrYhhuUnohVdioFxvBB/nlXk5iDoEKQni65hX/qk2b9LinFaL5gep3Pxi6Gy4ak1lpPH4fFNqtghJUCiQG545/uqlA0vaY5TEUt9iRHK8LK4aVV56uZ1QgZDHq74aLtK3lGeKCDRC7384H0Uw4v/iSQOktpHHMkjKNHNwMIflth9SYLbMuhTjloFm1jKgxPtgye58mVdqknKhdzzbtzdk1OePqZp5WE47OI3QhBE+WFekabSqiweMY92FsHSRB4SYXmQSikHT8t37VhDAihs9CbB/NCzQ0LM0Zt9BtBImxKeX5AOr7IYsvCHF10A4y3gdCcAsMvHdAjtRnR/Uai43GS5oLfsOF3lLqgBzI81cmaCHRbRjw93o5AxGnRIuBB5+pHMBWV5pOANA7XCbLD0czBymBMFV1QzCuBgKS43BViZFnBKVInRYrem7I/TF2LPvqekSTMufd01i7ZMD/M24PoIYAQDfa0IXQgzbA0KczsPwxp9CnIr4TKDube2fB1B1qEIDr7GjgCz7rxvEB006XtjuDe5QGA0EvJQRST6i8gwaBLCssO+gkH5kDcMJXQQbQxsFJ3yPUHky6eHkA0yhDGreEELCw1vv8kWHcjylgvUBJraOuWrgf18QFQW5m0k8vD6FlezyY3PrEIMHIaUsHGsSAjmf7d3sd/klhS9MvhuBkdzUKIoW3ujZV5rZRGdQqhiwc9J/IhBuezQSQmdAEXRHKSlKg55lxd64cJND7Cp4e7127x2hrib/RzywSTsZAUy3IXG1eGxawDzI77AhikAx24l5XhRxnQcvVxSMWxfrQUdZhIXJfXe4bUgTFOn5hlAr4XOJWJZmqxR7AZjCbJc1Q99+s97Wn76N5/UYpRx1y1WbMWae8lxBl3/1g1f2IAXOfrwkQ8urtlW7hiFsHWDT6TioL70inEKZnz7NOMSNn7qsHP3T6wbD0QMIg1/8UMGJ/E+r/d4N7QUG09zWGATvMSz2H3zJKPWO7dussuXbxXzBqvsgsxACRnVnk7kZjKOPJ9Fp7C30w0L2YBKw2CEM7bHuWLhkVB2Owu8OHFaa4DuKpYjKl7OpSRWRJuog4wN4OARHNI6VfJcr4i7EkQrqTNUb1NwoMBfGhMQm08m5GyG4BzM8icjUjK+gM8HDSqGvSsMQISgPIgDlo1IoXEKHY+3NpvPEA8qEIUd3UTnSX+xlpd3STQLTCWRTskqhpBUmixiiGe3t+Dq+Hg1gKViiSyQwwbTfOONN1599VUKL8pVX5qxCauOddXGLkrpUcFj/04W+KMpactJWjG/OA7je/ajE6QcFWTLOKGBHZuRXidwKpFWYKL8MkwZ8vkgdEkCTrSCgXyM0XDjGR0jFO9sYpjpKxb8NvuMfgqAJ/dFA74zMy4jXQnKNHfxcp5N87rP8D/maMaw3IvXvQhphI4EGr0mHuezRHEloqSdAnoCBWhEHECULVwYFQVSvyMRt+g7Mg6YJOXDDCqDaSL/AW2yLtGMDI0e/Q1c2Ufco5d8yJ5EaGwwohHhB11FWkkGJpvdxAkZ4oRVo3IXTeQyQueGCijpENqGPAYrccWi3CsCwyXUlBJfHsoLFe33XHkgM4AjRxbtDHArScNEW4jaKbbdZELe2gV7lXmsGug4CLWzI4Ej0YoLMpdi+v1CfIEHEXfCxnCSGiF2cyEiTxQ4JoqcGnHSMNoI0VhUa8SRLJvw5h0T6PkAaL5UOeCw3PEIPp+tA453Yt6QLxbwJGNPUDwWoG5ZMOmZCuzoJOUNuXSNWh2IodY8R84yzip8pzb0BWM9RksIgGxU6XVzeDVCbpZxKGynw5o8xE5v3WRsBVn2wY83OlKa5o9jTrPDID3NKSnCS0J+lJOb36eGt4ElyuBQ188pgtngHlvCqTAboFGbIjsug7ICi58rRrEQ2vIpLTToklUCMANaNJGSxETlzEDNYOhAkmvGdUbfZc+RHySNgw4tSWpIskGX0FV6QhrAptE9X0j90Ic+xIash96hzjANUms6aafWbJ5QO85gs4x9k2EshJ/GArVGpwKkXJh54oZzRvd6ftZKMGkAgNc2MdTuJOSKzXptG8iajcQdaeCkB7dPbxqPeNqlxowGNG3IjPklvDgTI2l/rdea1pIRMjFx+F08rgFR9wkAR8KMsROPk008vJkA0K7w0QetTaH5AW+IcFZbaRjWzPstZKyClEHmmmESGHIcrchDAGSOX959dokqYhOFK9mImUAhlcimmS22RQIiy2REftRt/ggSMYCja2h+dJEb21lK5KXOIDqmYlUrcZfQRgiGrEwzuXOoJTpRPJflNAcmEKeF7R9GvSgpMUzJIpwC2nxNQ1UkskWVk8JG0qvsY9EAy+T4AOMsjp///OdrToyVKL8QP1ZACFh0KJMAELFbSJXaheg8KmCsbg4f9khSvDvHHIelGWqu3fYbdGJpk1roNN4Nxgw3FNE6zB2CTPn822Rg4twRBlTIMmnjwLRNgrgJf8o0T9wCIR6sSCOfE/1Lj7BQeiRxffaWZDzVXfAfQlKHXYIMyqJQ7RAncsZnQ9Zyn9gdC1QEWhfQRyyTI92XmMO1Bw1yJ5AmAJ+X3SiQVGxVEu2hv0eeikSx/HXJy0xoJViIRga9BGDqqydtOfnSgoHNlhH/LV4AgUdfPABl2MjQkQhicQJWeYEjifCCJGTtIIva5Skh2KUd4hL7oBE9l69YTvqMWtf4cCIdTwgrfMKWDE00c6c+SV2lx6mBTgCxeFTP1gRY0eNrlPTgnNfmePxn2TA0H5zCI4cs7/uMqf4yuWnka0wwXQ9fv8vsiVPfHeq1vL+sr+OjvLyJ9W79IEab4ZW2DtH4o4EQRQJhAiorOdi7fmeBi0pkAxxC8ZzpTToCdRExMQ9QfpMeYBkPslasH9FfHUYBL6JOKa7CIjaInhg98F9vBfggb4KJFUkRaRQpMUk7uO43nTUMWDglTEUr6/sOYXxOWpayabCYRNs8C8EBoI0vkQETLKuchebeQTRKLX8bYUYD2gzLrGrirgmaDnqUmIukMkBQVXigNgDKOApBpjE0xyhlDJUa9AcLIam9nsV28B2+bhPwbcM8pvI+M9uiXOUfnQawSK6fDI6IOH1Ap85wUQ708r/8y7+AC2IsRFO5KJFHCo/dYtwZ8m/oKpVjfgx9rwq71XRz7HIH9iiBmL0EbA41WL1xrVVu6iGvJ8iNSMA6LuEikU0whhwJNLfzUQlDlO4WzVQ91VUgw6sc83I0ZIFwwKEdLKJY/Kvw+FUzQsY30T8Zx1Nxq8kIZxQSXiQJZaxje5fDIqqT2xEoAebePkiENsH8kGokcwBGJqEhtBQw7p8YmdgmeVaATscoTnmI1IhOyEDQNAAaNimJXFE840StzSKjzNmJ99vwgl73QNmkTAzpWbiIECrQSZs5p1izRni4ZwcHMiMUbVPJ9J0SpCe9YUHlkYM6KOe/3ZDuopHe44i6R8CT3S7YnS3rVemj0wDRipfD8B6+PgYIYeyrcedCTBip8VYs7JtURCaVD/EQ9YWYXgwYu9a6SF5Z/RsjHPHLbVoJPBQnTuiG7L4xn9US34SsDWPIpRNP9MoaWuqNHQ2MejTuRCyjlRiaO0srcqwzJuMaSVzJcpJVkW+KIf3ANNLIgFFPxzGuODMpck4UMKfi+mQCll0QRtaCgrsaat3Vqc/ChRFfvwhtgKKVWQWLFFAAELqS8mOBvHzGBt0gC4CbRdnzgsfyTcfeAUzUBCddb5Bu4kVcFPIAtRGKAOk2hOyPz71kFt4orJRIALOiG1CaEvsopIoCcJnISooEIr9u82OQyfaNNph8M2pS/Lu3TvnKEGIoCfKDri782hoNU03ZLxsFSVh5QGSrCfvFBo1wBIt+vwHP3C2F+9j4lnAOnZAKiRflgEo17WhptbkqXacPkkGlpQMweSZ32EMRu5pe86CEDJDAEK1ee+01SniqhiOSFP7MIwHO1Y3I2RhHD3NKeOqLACFYGyOELUnOJPUUCjG0jJGw+CxNHDJSor2VuU6kYzPJwohXd8SMM+8Du7uj1R6OZAPjn7TFvIZtolYA/uoBXtfpCLjs/DRY67BTRZQJEb9gSB91T7iup7dKj94BprOWSIiR9F4eHPHDW2+91ciAGMPZ4/tiVUqwEgR8u00+JWsP5mfcyO45aixMYicX/ji2NVBRKpLIOA0/htOCLg5HxLIQZpGyWIh4h4eoUTB755ltYkZID81GH4AKHBWmC0Y8XtJLITpHNYupsQTErmn1VVyZ50NPmNESYrzvnAhka2whMRU9s4PuLt+chI476pk4s0jPaNk4lf5jD5dXLeR2U+sNX1nH2O7o4PClwzvXjl86OH3p9skl/jYn4j7qRBeRoIqC6E+0Rr4lF2JViyrisK7QgSwzPqZ+rI53iQoWAJD4guGnP/1pDIyHColZwJCvrd/PGq+jkKETQvLINGSJX7rijRtf+MIXqCJPIRm2OBCz7qfwJEsaep2/bZPayQXeN9+/wuTHbaIEApeEnMEVVqjEBT8/wRSJkRgfyiOOOSFyM2ebycySEqzaSEikO8pM09lVrvH1F7S0VAHdXioS3E5OfBnZ9Kl0Vdy/U6GyMA5Kx9aAG/HkXkHRPJ7mM4BcKlA+PcfHwxCIL4sxBspdQk5BCBH/IKfjRMmZ+CMpUBgoJJbVQsCCFkcva7BRR/xmA6gwfLL4nZkXxzajYrFSVgbK56KexaASuE994anXZ5JLYNSZBDdF763l2FGnhUHnKCgN4C4JZVloJ+wINmDzgAUdKZyyudXeSGTHiCGnMHNnA5NKNkkn3lFNRRsJfSwBW8gVx1av5gvkdQ46wKoy3nOay0sIvKAHtEFHYy4cL6SCIsZItL91SmBiEMRAGJqEGKKJo/3El9dffx0DBZJTYtaDsNOQkohcBDiyRMNKC3GWwygnWi0uD0Lz0cJgUucuf2R0ya07rri09+2jw9s3McBsNMcysdRYdVuoWizkv8+Xae4WxVW9pMdPvOSLww/NFKRQo1E4S1zE01Tzt/fmCAWYPQ6to4SCrMhAOkTNK6reSFXHfXgetaLEi9F83/VSNycetgqYlkipXZaeM8DhaFKe1tVa4POOLV41Sj+6s58dW4yUfcJmkybRtCnyRdYNRLNzHCj7mYRUHarXfINxmmGJIWWk0uRca84iHFHXADFBBFikVZCawtDBd6zkHzIKwdhU0o4FbWiCt7WBRJX8ZTQ1yiGL+hgux4J6zRt9A8TiCJhD21s3fUoxFxPJvUhJLSWtIMVZLe9CaqBP/5+9N4vVLbnu+/b55jPdqdkjm0OTajYlNQeRkjiICklLkegYCaLYim3akSUBkgM7jkUDdhIgAQTlLREQIID0LMBAkCc95EEQHMBBEgliYkWDiUhWRFFkd7Pn7nvPfL45v99/7f3d0+zbVLdgsm9Lp+5399m7atWqVVVr/WtV7dp7263RAVTZhs0lCMIl52y5Ojg4AE0++9nP/vqv/zqUOFYkEQAa4KYG2NcqtLCPVIjT/03N/si1wS9SMcVKfS0+3+p4jVQTSOiU3FbJG70DQ+vJeGeqB2DYIFyuaPjcIsyqebQ0NLf9L+PMZei0umZCIo7P+aDzYUt/giFtKfCt+V27031Yy+Thg2hRAHNhAnVMAUrNJXnDrIyNq0qUPg4EnWtn99vaQvsK/QmAsP0fPXMWSSCnoCYmcEXhXDpdG47MiJNEPHcS2DlRjDjrclk2Q2onA1evDKlJHewFK2PgEUT2oYKAqBE8QRNCUi5kLzCmhFQbvSwa9Rg+vG4dMTYtZWNEqhrbyZKakN5BFIX0lzx5aD+laVo4s7l1TZ0SMiF0dksMzNHdpZ84NMAn6FpXNpm/BJKQDU3f6g8yznU0fwn+Une6gyNds6muuhcN2cT8mSe4UagBGaMDHkrTWMDCCeISDpzQI+UEQckaFqnE4HPV29nJclGMi4UWwyIgC4FzjnyDB9iqUqgFqAe3Gu0uZr8bzm0U4ADNXfqkNxel4K0WIiI7biRxAkQ78N9BWAyqjVre8qtWdaKFwRdgxe6dCTG1xAIILJktebbfoZuvM1TdoccGLKTGklrVhkhMs/fzjGGzmE0FkohW9B6xnRTcmaaXkBhH9sANRXZLOoLbNzQ4NJicalYVj/xUVWlDzBHtkUC/RKBAfI48GOkDzJylZURTDNvkIFZb9oXSSOLK2lZInT3dcK/2zZJn6WtLWX9IDbZwBb4WppnCeT4RPJ3f/rocFVAAsqRZJWuLpnxrmxscrZPIpd5WWlNH1bXImhLaGOSjNW3QiiWvvODb8qR8O4YIyFkXoLOr+03/yxVswy7QYrZ15xx10X/231oIB+bICxN4YpMACiBFZmJwr37/938ffAFNgBUiWYqCgIyAHZGcg2X1yuNXlwcHXDPmCyRBuYFUToihlFoIq/kgx1dzeHNjytNRBWlt8YhPwKByWd9wKL3dBchJG2a+wPoUtWtdhKKgYe0egcz/VSkmiOjzihUuOQ0sAM3P5yQ2NG31KagyMSB1DOAEvfy0SyEDx6mlTxQIBEtOi8Yk+RhkEmRh9ADzOLfkuo9npdp6wb8y0Ink4glKB5VwUNRwgCf9qwDxCoErkl6BfKRZcBe8jMRGcpGwgbbia1IwlSNitUNZGpHLCOChqiHjsOLo9opMNOTDWXBQbQMo+ZGFeHLmmEvjId4E+V8owlIutCBKrNtYspEEJZ8gmfOYu1yVpAtcbmJAq6qFkoR5R/WX6G96w3GymhrQYXmIfn9DAUUkI80Ik2o7lI+FdsDol3/5l2nwJ554ArZ4UvQUSc8++yxZoAShCubq/LXaHfFIghKVo5SCpF/5lV8p9wpRmV1yhIYYCn0tPm9iPJpo6dw9oDIxzmhitBEVTQWrmhxV0fqxRFumEWqbN4N3MYFfuWVtRvf4hKEJQg/xFSyaQCIc6gYlJpMWMxL45JdPvXFFlqKFuC5peSKT2/6VoH4yjZEInB4AAEAASURBVCxRl8pIDJSbIxcSJZR6QLahJLoUjxhuEXCsAQlzxueysTalQlpVKpm4hLpKCvP2YExikRB6a0PAJ/fOoP4asRs1bfF7A4NdrWoUnXNvjvrSjrqt4Kx3E6oYl92z9E47u+sjAZfJR9+dlVsmOV0yBIBxpgTvrpvrAUs9LMRzSVJf08+I9Nm3gI7QS+QB5RHegYgFAhattobL/oLb7/hsI0oZb/d7+8sT3g5+EdbTPRHmdquXeLevW2nfin82CoTwm64HVr7whS+80eqQHTfnve997wc/+MFHH320djMUfOA6kcQ36wvFOHnggQdq7la3/NBRiiOmUOzVRdOfMEGLiqDof+qnforsTC035lRVKDh7NZNvQ0ytuJdqoIZou75/VslxfFTwEVpKzICXwaCLxLHnCt30goD+Og3hpFVXVJqthpll0QYN6y+lfVxwQveJg04Q+lzUlkSMWE59pl/D89PzQhZzacAkYXG8igZftW5Nxj2LGeJYr9kJRDG0I0LV0g0X2IifkuRjzoHRzp+RSKsMebDAXAUjrA94LrwKK8gTbEEB7Kw0kIAaxEw6QNKfn7vc2R+4hI3wU1+cjQ3jSrgvtgZVbij64ihfqkAABTDpeDY0LhGL86n4ws3/BCVEPjjMV2BNvSOVSJpUuRkDcdfFCCe3ApAeu0toZ+cnngN0wwlSIgM8ksNeK4yw9NykoGRYsiAViUim6523yWrLvaDwoRmUqMVSSgA0E6EkWchCVLqHcwEQkXnN0GjJ3V9cZu4oTuodW3M2PewtVucHx4OHHlk8e9zMDlwLgIc9EUVqVuSAq1xkLUtLyizTqLdyKI2pGqAqdfLYY4/94i/+4r+VapWzU3NAGKKFhOIM9BT62MsJdVnnrz5CVpQgFwy/+tWvcllTUZTp1fRvTowmizDYC7u0vVisxmx8n/BWieXxardZ8QnQKaPn3mrOxjH2QnKzhxs+wAeDbC1kzPnQOwvPNApLvFFFlB2T9YODWwOs3V3PGoiGxnBMjHvDOUEpsW3ja50DVAquIYc7uRDL/hYu+KtwAmXaqfZDECMGYEg2tVAIKxBO7ztL1eQIPUCJbFRAA9MLoVAkFIOhh/NtI4EneZEUlAEcpudYoqUkuLtAu6aFwLfecGe8WM7Yc0kM7sx4NHavCqIIURnT6OnsBQHdVdbUIUeLoerWDHr+Em6nInahSSKJr6SW5naWbl8obHDwUhPWAVdM1NxqQdxgNndgaYQm/hhPXTPsM5qwTmZ78QI/2nc0GrIoPj1nzculxRIImTiBpDwFT5GbOCEUbjYkbUd/6irTBYV6qpRVo78mI94RdjzpDx/9wEf+8NYTzfEz9kmLh1TcWXTVHy3znrSjpIVehm9nC/BdaPwybjJyBK2YbD7yyCMg7F0EVdETlAOrwaOycUQDFAbLYuQmerWaLhg0m/sfevlktl5tC1DrZWUhgw5OdBc7SF6ucntKZTaEt6vRrwhtEsXDw7E8rDBz7mut1tNZvLMazTVhF7e8iu/jEeFu63NgABbK79hcPzyFdrKPNZlUWACf4KHwZ6RI1455K95HGhyQVbACwNF7Gg7JhRjEtwNkNm/jkCkVddS51PeCn/xTO+XjogJEm/V56BSWQIbkIaZCRSuWDedqAvFelvBE5gdP4iGu2a8iZtwmnqIhtlA8y9xbrMwebW0K1SeSjGeI3I3muw5JICaZeDv97cVUyCtb5fWcIJfEd1e0uhwJPrbO46M0Cj+mhDNUyZbmfZXz1Wzdf+d7398wCNljbV0gLnbIzY+++sZghS7Dt6MFwCkwi5V7po14WJ///OdxxzaO27dDgtdXBjoSk45meKY+gQjnzWl/yC7IUTO++p6Pfux8wB32Hm9+Kv8C3iIJNsLzHtK3ahzFFcUceRM4RaFV8vqZ08yVmtI9Nb+zv1ZlvepMGw4UVPQtpdQSbGg28RsyIKJyhVa2EQpTdkkR86wYIiv4Kqvs+iyepEJWU34AoZiQVChmwYBJDJ9jpcKHLIKckFFbJUsc4KX1D70mCVLy0NicFHc9PENr/BeFLh42XwVmevioXIqXjC6e66/i2hBZWOaylH3AhDYd2mYljjPpE0EdkIxLBielcmfWohnvyiekomoyULEQ5jXzYiUcKC6+m9rCHWLHhcIsJ3QIMwejWEFj1zWsm6Pp4mSx3czIFZ4qgU+TmilQZYR+V5fKYFJSKsFl+Ha0AItiLFexvgZg/dqv/RpF1jM9346y/xxluLTC8hU/9Atj4Jnc0aC/O5sPb7zr0a8d7KxP0dCZL2AAqlyGCSrFpULn8YPK5My6UTUTMjm4KE9r58ar9gZHXBHQ8VfHwgWxYAoMMJ/4Phoba8nSmKVMqj0mIgcyJGh0hk7piYypuqacExOLJKyYPZU5c4SWI0YKdyewxTBkRUMES86I2QqJodkYApG36gqDNhUo95VN3rozcKFiHUcKgIwrV767YPW7wvCIKloaIvkfQuXIj5P23Al2GzYCyFxEorsKpL1I9X2mSTyi3rZ4UI/62P7gF72pc8TCP8IwANmphSQFtV1B1lnha0Mbczn6ENSLw42gtPXW+mx6PtwaMrH++ssnzb0PN19/ii518teseAqT4AHI2/QGlx1aIWvXgVJehm9pC6AbtZBfe9xZHSO8ievrr1lZ1AcNwUqxDjcIoHLLWa+Z8Ujsgq+oNM+erg/X/a3Z2ZhxEx2NZer1o54ocwWWbNHq9hJtz+2/WPJrltsluPqh9QklGAjtBhpWKXXJ0clmF6SuoB3FmhQ+Jp0DhLhCugVOE7VwjvDd8Gkj213y8tUXwTpijzQDBBgyl3hkSFJJnMunrCyUReNydSoOf78xbcEpjEtOSMOxK5DikhPikY/AGcQEGzVB4rRvHYtvcTMvobyeOrlwjigSkBcB8oij0kQAc6VudQIZAaQy0umjgYIgRqSi6TrSK2VoRfKhcELRICHnNFSbJQOdq1aMUQAlIOYbtdGiJU8RznuTg2n/vu/8aNMfB+BYUxSi+DETFK1s9YBi0KqSOs6Xf7/lLUBvohXMKTiiBqzcA1Uoxre84D9fAYEeYUYVws654YP+cbdnv3nwOw7ng3kz5PmK5eI0OMWWmqpI8MLBm0uyYtja9sVA9dvL+GLehoJSg8Fb0pw3UEMklBuDLfgrg6140y4GcCRQIv8WKD0lQBVjLf6ypZiktIdi8w2YUGQklSVWKiZJTGVrEwIvPOJTZr5hS4mABju52ZDqEnVlI9YT4K08xwiHNMaLXcBZxoqU0RUUnnURGoiJavmQkWpTH5ovzyLIjcVR0FSPqZ2pVuk5RnqIElo+3k7y/oAv2UhAYILjjN5SO7UkJhxESXKnS3SpIg3dqBsanUFz6Hhe+M2QxSiQ50XZkDHcWs/Oe1d2eWM/D0PzUez7H370+cHOujfealgs08MiG/KhEdX9YJYOPAW+WpXSKpeHb1ELoGOMtQ8++CD8owvi12Zw+hYV+udgq7bwHyVV/4ATntQXjBjmRrt7s9E9j3zfZ17o7a+mW6PhYHF+HB8ry0NbPOAc+ALZgs5qcrlCnKGKsIvuRdXddemvw40yhO4KPSVCpeVem4aFADHSnMbiyNuFRLZL7JSofsffUfU9FVigCUdjOE8XECGFf4oblUwqxw0maKS4CFAEE4AZY0IPLBgd76/4xMOoSZdVgXLAKn1aIVPKrJ2zuM1K09INHsqE0+YHJ5R77YM/fN2MkqwyQYKc3OFgkvlbl5Jl+aokMSDliq8DjccMjFwifyXBBVDBCeKSEjmYypQ/riORbiahz8Abq+0WWs750heR5q2as0rADcctXneNyArmxpd6b5/CgG78oYO9BcsjPAAR27l4ZQ3PKS0Xy8lkdM7n1Vgi6+8u2b/Q22l6k3XDOxtuL/BHLSwxA5poRXNcYlYa5Nt3YG8Xn1xlPsgtQpwsBuSNFn37hPimJaF9miwBHc4wlz/onS8F2Zpcma13rr/j/V87WDeHPES5pRu/YH0V7XMTgzYmNJF9yWjPwIs5aHvtVi3Um1G/XRsiTW2U2lwp0cWyXLX38grmYlqO6ElyekgwS0rUyMKFExCABRjiJZBrhMllTE3MMbJCpjLDkY5Fi0GkdWExPadcrooV2WrWRtWKHhMGFijFbwaySWLk3UMuCeTiyCWhfVsDeejyyjBjY8NyOdnZI1mHLW/YIoMceb3/7LbX3ZadCiCLbvl8seIxiDxHxn6S3nhsTQd5TgpPj4vAlrvU8vAXLr0NjYMZWSmF7xI63WWeSoxvz8An8tuuwCaOP/cFEXzAxmvnZT1ePO83BfWQ3HGKhLl5QZY8LK1TjAOWLQ4uWKUjKUMgK/ecBgLZ/E8Dumw32T49vtUMtpvxaL7un/GU+IPvXf3RU6Odq8vTF3GRQbCt8eScjSHx25r13Gl80Or2GoBFXIY33ALoG6BTe69qfymXqCXxqGxtE6WLK7KUmDJAK45Ectwo5Bsu+1uWIYOi0BMkceWJMRa1Yy/g6eGyubH/0qK3NSVqfHJ8cwz4zLV2BtiAEpqN9bpvcXl+xpCYxVfSWBIhEqH76Divwvflcap04QfW4GOG6nu8FfQ2VkbzKAU2UkBWldaSjHXLN3Ji8mQqZMFZ2RrpVVTXkB0rA3K4BBvIBDvOIKabyovTBjug2XQHBGYM7kAgAiVA4MarYAtH0YYiuGT1yVmTrJAWvcCSKQLdsNKVmROTq7B414r+yiDHxMCXQJYKcLAVqj7sjxoOxb44ihsCynfvQ8IGnjoGr1A1uEmJgLQCfHSDnTNbYupRgnFJVznLs4MNcKNiVtSm8UYkNx4ltiJMAI2Jk207e+laPS/rkJaFAt6JA+DhNDerGY3HauD5vPfxz/y15vrbwVU21NZ+Udbc0lM2HT2mv9dV48JpF3X59/W1AIhDv212itYJCkC3MoChEmxZgACXikg15K0TwCw0JAc1BeVDgRbNdrNz3z2f/fcOGQTn6/0+b8bkU6OnkLLK4G0etBo3JrrNqoWDKpZe4CIXpx3cJooapy0utoluk4vZhLKLtrWgyY8GvBhMzXVMp/WYjOxeVUbvYGj8YkqRyuQyO02vCuJYa+Ikwa+4cU48l99AT6S2mUV3OGzkkV3H0EismZqHiUpCGheEIqqCKa0FhWq1FlNJ9ElxwARRKmyKIUuxIoYTjuVMURV/VUr4FOdqIMle2YIUgTB4PJtCkIxIiiOjxYFcNJ+S8IoIbz3Yu+5cIGP9rEuL6Gmm0JAvfhx9Xz9nha07Cj2AxV5aJr3cWvaz9bTjjBd8rQ4WgOaVZjXqD/eAN1QNNk3fp97C1s1YBVh4fDmtqzb98s/rbAGUSvXqNB69r5c6cMK9P5iQhD/+S7/0S6jABtdeJ/O7gAytaEEWF4I1ltXoejMbXX/4/Uez3i5PPh/dnPIKvSE3kbDtMkk9C3W1QCpmlRbS+MuGqZeWxTBcRpQ5F4ltfGfaAmBnb69uCjkkaAUJhQWckqmNKYrOVIvZhpWUHXiV44IM8Uw8YC+R1+MmbOiLibb5ykBNSYK++HBCKQBWu9O9rlvhwrkYeexaoaoFW4mTvKkMJ7hstmYScGagUQCeTbXRi9w8AI2XELANtANOASrnEIBKRR94Cp462PDstzM7/EIo2ZoGJTXhGW9koSg5E6p4Tp1IMh6R5IzPNf/qRV0pSd24pQIpDM63mxRoED5ZyEYYXS5eYgFmrea9rReOVvd84BMvnb88bm7Obh7ATDeKWnC3ERZdzaKMOpXUEGEuwxttgeogjqASHQ1IgUqccERNiQe/7r//ftcQasx4owW8efToBlO+3HEKark4MV5MbjTXv+PmydZiuh5tNSenbGyY9rZ5VIXndBx9VeZWn6OoS+aKqDjLvTLBCpjCOVBjXwShBMVLUUKeROomKsoU4KJKqroktYoLRzUW3c8MRssKUsgzZitBhfCEM6xjrSlls+oPh4QNORkh5diGi6cpnXgZF57EKWnLqT8XjsUZZSCL2wLanKFQnrZgC6rzykBrENPd3UNsLmP4nIUCjq5vhyER1Ko4yLhl0S0QhsbUIu6yEEO+ihW5AijUqcgoT1aETkhPLoYIbASMsjNDedK6xDCzp2943olkOZO3c4acs/OKIaCLp4RYYVjNV31W33h11mA1uvbw+z/y0v/1L06nLFc5g7eaLIyaF/fKKTdCwNH+AR2NuKggF+W7PP9mLcB0jyeia7c6a1j0W3UdusOj0S+//DItzzmPN+N2fTNGd2Ea6qViiCKoznIwaXp77/30X31uMW7mzezs5vZofTYaL86Oce3Lq+l8K6qcdTBVPfpfmBVWXpdR5H5criA20HRaExrfjqBcJXuIVNlNSLzDPyYTtKoVm+h5VojLmTBJUn4kdQ6GXIpzy9+RH4dBlyIY6t9QiEky2Ngd5/DJm40ti0vZI5pggTzJWVkTZQv43oK2GlIlOMnpipB7F6CUOMdiigdFIk1DvvnM5S3Wx1liiHMkLxfXZa9krOp7kkAWl5XqQrcso0PWvHrZUJpMIUaA3Na0CdIW1q1DZU5ctOP1CpAhm7NdvCVQI5U3rzEgUyS3VtCF1EKThUgHHKTNUMPdRFp8sF4x0DFjH9ycrm5c3Wmu3Ne8+Dxri4jAbi3W5n2KnQLl0v6yRx+lvH1Toup3eXw9LcBDy3yOkF4GjOhitAiV5YR+4Z1ZoBVMeBCHvez1ePPr4XmX0EQ38fdxydknyni4Ne+Nm53r+2//jq89sRquh4vp2dZqul6PHQFdJoYsHhbqWhbDPSUBCKt2IsDij7e5WcQwpqulhqlJocxd1GbgNE1tJ8Qo4E/DGqn6awjwr9QyGJIkIBKeEBByrjVVUvw9U7tAfnK19/3jDZUcWhZmGNJiWxu36VwIakWffteuEzDiZOnWkRRZAdICPg/cBqJQEUIrelUv1GS4HTZrS0ENK9CFtkUCwDC1dI5VW06Qj19W7zbCSfOqAL82V1c6JGRBNtgySQaVYe3e92Jex4t8KI72jWwV3fIkhlayKdJ/daSl2rYCrQCpGd8y43H5NQ+Js2o22jtZ9B/7xA+O73lgPNlBm2DY1g6Y3SylVjFB8IuCXJ6/zhbAb4ISJ6s0+Od+7ud4WpAep+OIBLM44VFnUiGr95G+Ts5vLllgAO+d6RtWJyr0dc8H48c/9MTNEzaK9nkYuc/tnSNfZDQYCkNlos40UDB01KVuVI4WIJCqq8KPlM6YxSgV2/hSzoIAQSFhY5vf0BoS56d7hXyxbiLJTikWl0I1c/5fMPZNxotihNZDaNtDRYosF6CjWG2EqSxmCw2Xm6QNq4q8PSVs8+DmFGomD5EVT/7ikVZCSMNF3Bn0R7RNPqS1Ws/mS9aaRhNqOxqzBmFzs0MTA+cvrDhmdcneDAAoKucc4UmJLWBFBrP4822q7A6jSyCwaNCE7wymKeXj9Ju5XbCHVDHdGeySh+MtzlsslECUszZ6F8fL0YhLHmCc8WYcpKSXWMNiMX/NY4RbvOVjuGp2nnnh6OPv+u4/+t/+l2aKiwU3npQ+cwNghGdQpEg9YHfY0esRgMvL8EZagA7Fe/rZn/3ZX/3VXwWPeEiQ3DVcY0tgFpflvHNSqW+E/b9F2kCQqtxaxDdhDWmWi9A9oYdBlrXVeY+PZVz9rg9/5l8/y9sK905ffnE0XHNrfTFlcog2crfU58DEJXLwz9tB2hbldXYcHdtas3eBN7W0ApSZeBEbwwRkwfGCF0aUpsEkszXD6D9Ix3qt3JmJYVyuZDE3wvqYQXEjEj6cc0uKKmNuMXNOlC0SkYWQFB1kRVAIqFtU5YIdn3QxIRAcP4lS3JHRSbLJZQQF+afljPEWQ3QAnwB3rNizlQrI0AcxJJKFHwy4PyRnrmmjgctYmZBbK94PkZec8hKfwUQyvjEGFvBII58MVCBghZVyPpFImyOiXdAj45q3xnsrjx0QTOjiOmU0ICotjQD2ThoijcgWLBimXFCIZzHWfV7QvhxOuGGXfgGV2AvhrrE+exnsbStBZ1NLdN29YMg22mHrFjvN8nSE+05IZm/XyZyo4Yjbf1nL1Csd9Be+Ve3sZLJz5d+8cPx9f+sf/Ktf+fnV6fHOaHU240lpew+0yteRlBWv/ht0QwHe7ECtGdmwfJarWR6iPTkpP+UNiUbrk4vNUGgIC+GsMdX2ghpp7siKgqBUcXMvBTEonUuOxNQJGgyH3/3d3/3IRz6yYbLBo432q+jdZqsN2Ztxwgon6qrGsdyJCmS5oRWkXUspxWX8IhoocNUFtexNF3xTarHmaeedhwYPfu/Nm+NJb/9sNu1P6JGF97sd+maDZrY1P9Ol4raPO2yyFZGNo671sCrClwqxSJ/OkHsC2WxkW9WGpWX58eoogD4AkZHbdOyj5ycQsHBI4Jy9VGakD9zvhl/lwjHLMlvcr8w9dG6O5WalDoC+jGM5jliN9uVY+MoXSqQsi2MCxF50nQQ5YUiavZsolSezm2wNZWcs1rrdvgsvwJXqIEwqQZbUSNQZDsAYXvbAKwPz1RzVyGp615D68iVVgIYvpRGjBEniHKEg8lEYMiQwsRZXo4VEkp1z6g5+FyuI6dlAcfKai1Qf1oGMC/jLOCLa1lZPSpsnoS49ujONybatn5ok2R0Otb/ZebiOLAOFPUurufOAFuNoWQrhPJHP4bC2rjpRPCMHleqhAfzhLgw5uT9IhWkCPCzv+m2NB+cvn11919vPei836/2t7Xtmp88inAOPLtXAdazM5/0cI0sQXEW0u+QASNHIAM1nP/tZgIAWYms4c6uagr1ayC996UuvjiQGtKrNnJzD53Of+xxeD4BSew5enYWVpvvuu+8XfuEXPv3pT0fbBmR3VtAtpr46y1sjpnQVQwg8YDkVoda8sutLDXgDHF7TGrQCfUaDex5+7KVnBh//0b/15ZsMhkABDw+eAmnYha/dc6EqWxlyRM1giw6S7ATCJxAtTcXlj+a5YAUHxU/puk2co+sk0jWcq+M8D+cOHqQzYAjdWcENcXg9ZKl0ASJlEaHgMjAD04/YUkqP6XT0YQtT9/wgaXbJwYOI2v2kPxR5REMxl3I1cOuVTXZmjUwFJsaK8ZnByCZmnfUfOLgHr3SIEzklJ0zDPTKZUDCkaEWQOIG5YogkBvCgyWHHeT0+jb/jqxOTq2gCZxo6hRJjvcBEIijCJW06xuqlEWkqu6dAEwBKagQwU5GBFdmhSxMEyhJvLog9VgdTDwpKlziUgUQ0Pr1uXBoRoASjfJgHSdAMNy5YhWZ+9fru0db5i88+10xmH/9P/vMv/vP/rlkdXN1tjk6PBT7ed5rg1j6Kq06sqLvjCFQhCLD1xS9+sSQCYmpzwBsSEH2oHqRhmLL91m/9FpBHJDB0Rz4Qf+UrX4Gg3DEK5Zyjbf7WDUwz4pWgLqVPnbKKLPzUQoPR6l/Crg8P3eJ6d//+l75+q3nHp16e9858vzBzwOPe8hSPH/cqxqBxMp7TStipE0NKJKDMDJCaCnptmhaevyHV88mlbeu6CEQCnPk0BC7lYgaC8WFgsnK2kl6glNYc/KVMi22Lq8jNsbjJowv43WgIwYiU3rItmY30TeURxMqWnDKALvIUpxYfMneFGEpSYSt3QKQC/gtpzN9wZ3SRqj5hxCFL3bw2Kmhd4B154QC72kAAsFGe4prBczhzlJBfJ1DylWBpGr0VHRV7p8ja7GkIYhJgW0NJCmizCz4J8OQxbjknrzLITA6ZFnK0BDs+u/Dt+E3fyyxN7JP0jEjk5FLtPHjqyWayc+1t10/Oprd2rjZ772r6i4ODP2XvDOKw3iC6KSGvMZLL3RbYKMDDK9XgKAHNAsTQYNU+r19aGhXUs5GjOmTEhyq2d2RCuaxJ1VhYBHC4I+VbKVJ/yqf86HA6ng7PL2rL1K/q55G1H/QMjVM3eqPB1lmzO9mbLsfN/sOP/9B/+OQB8wIfte+vzgAsHrHw7eguYzhksgzjEzk2rvZKu1kcy1UMit4fJKFTNQzCEdc4fwQvNSSsDyYYAbMzOHgJ9hSObLJfaPrOq+o4J4/puly3LdcSEi725W15OoaRWTohiRZwMd0dBTE+PBprKcIEKMwUaCs+xdnMkRPJqxHgCRMfviOQP389FCmDIWMjEwEKI4Z4CrCMBDLXCcfiS9n1MI2t0p2TZMUhtsxiTLMhqLPrNiM2X6DGNKsqIL3827xVEp5X1trsGOpdjhgUtHAGPeS0IHK1fWwHSayEiO8zWl5SFr632RKIUQ9Iyjs98hylveTmFyN3r+wD4KvpfL01eWGx/6G//Y+brWtsomEC6JxTNiplLWN2TIv1XXEENWiZ8oNoXtwiupWGIvKO4bWEhhi/jFBLVzhZdB/c7siESMqFFVi5mTYWh9fi/5aIR70Yzfx14gIIvDud3X18aN7tNe6wQcH4gRPcEeo34/7h8SH0/f7u4lb//Z/5j87G9y62r7ne2ZwNlid9PvccD0uVRrEDQKwWRf0cNdFetLHe1qkJtYYgMJWBMDehbTVsR8+c5GEAYgQGdFtTUmJMwBXqeGXaQn7y5ASfwykbqYihhULMT85gTcc2XCrHK44pQnGwtIvn8xmL2DpHlg7zbwiZ+oEblFIEFhoyxK6TTd66ZNG9XQrlGrgmGweIqp5FtCkFvlDQABAQugbznFLAP04EtRSZSLmaHGAR++VoKf41JCmtmau4Zi44tSFkbW3bc+vmdA4K5GEKqah84l4Id3WMBKRxRAoPCqCQKo4edVKe5lNiAcelUlP5AXy+Np9HJ1RIB9GtrZMXnt95232z6Rnf3pivdp7h3vPw/uF9y9Vzx8P1uRrhcoMIR6kWmIMnd02gBXCOmBtyLPyqzn2jAqJ5rH/xYmK8p9oMRbu9FisoIeNYpQBbBZTVEW+06LuHHm1B/1At+tkdf8CX6qS9XQilBFEKFq/nrAhfOZyNB498z869j/3O0wfNeL9ZnuNb9ZdnPV7A5io6EOUOK1QJTML+aKjbmolyoozO+zLo4tKVrqm0JQuFl4XDgX9w5BkPWECJXpYptAJqjGSswAnFYDLxgJISTCQ+NCy6a0FFBF2XEQ4yaS9lETJsyAkpQC0tsukAaajAgpeIS3I8LP5gtAVVaNGGGycmJcRSZeV2yxplGTA38GZKVzDQiJKho4RSShCBYGkXQnE3IrMMLuXWPTsNceUlkuAIQK/AIYAaNnYPJ0QSoOHcDkPoGAMMJWvbJXTyN4oOEiJIAtTZt4oPVdN+u8eOt3fdINf2DSAXKVw7xJ+sNqJQ+UMW2YJZDi/8uM3JcbQ75nXvtD/MZsut0/XOhz7/9+dno2lvB+4DJoWQRSHs+QtQG7Zv/oF3clY/Iko5yFSZyOrNVx9fS2IQqnoH1CMXDjhHHKhXc6gYkl588UVKrFz27is157UKusvjHRXzo7PL34ozlRFUQGH04sd+aX5ernmeeauZD681owe+9zN/42Cx09/BQ2ekY5ffed0KZAUKMOJHLLbM6nsaAd0Pw2gjN4uwRLW9NZMqkaHaH7M/4UCt14fiN+djE0v8IyEBbig8y1q+06YN8EkpdAo8gxH0FCDHT9esjDSzK+TYhE3vEFMZPSZ0nMWasvqWTy7t/fwq1ex6nf2NcrYEHf6UeUKDVCYRAmrudCetbYskm0a21LPOIS3AV/lEkjYQjxCV2B/kc2EBLGMAO5bDWPXgWeLgaBWUWjnH5IRjW1tO0g1EOkkXhdpWiAAXzyHsMio4QNO3qxDY2Z6cGffkAwfi67Yj9W05ciOQ3QqCXZsB113N4pF5ltyVI+gDhrIvA1echdHzGZ9fHY6b8R7dfjxbvdAfjR//gelvPzNbnw1Yg2jY2UAHe280CNq22V3yB+BAEhqKxkE5gCoeysPPemUL/9nCMvuDCVNCHCX4kL04qDl3CteuXeM2IsQopd0UnYNYFXrrB3RN94mfwx81cmjMOmZuOHcVVHFHDHWjebPf7Dx8uHXjdLW9nLOJjw06uAyLDNdoDa494yuXM/lloFUZBSwYq8nOBB0a/cBe/gUUtCN0jy6wVQE77Q9njcdip2fiwWbSA4f4Cq35KLxBTLRr6lV3GLd8qmdNLuvWvrR0YzZB8fJLfPpXowZe6GWEw2Wjr+lv2a1WvCEKNXDFDf75MpeWTF4ebICShfMggEUHHGRugCFGze1+TZvzdvGVE4u6IBNlQEFoc3JmgezDYOhwTYhzZCIXKWSUlHiG1Kxz8XIsd1StVhMnBe1LJySIfjM+u5KlX+MYUEzMW6/HUlAHDf0dfnF/qLi+EiPJ0i8v8jKOwZi1GGRZuKIQM4AnNHo5bFeB64CetU6CCS/107dVTuvK+2/YAeYgowvG2Xw2XbuLLX4ZVeDFNb6Rhp0j9KjIxSdNmukBA+PBavT2D326Gd/f7N1HH47bJThf5aV6vbJbrcqbGqrBq78QBLTiSCO8UaGKD91FRlY2cbg40hGvxaf2UtVKlnoTdSr72dxYTF+oP4TX4nO3xasx/hwfnacxbxNWdIUm/dX+hBfiNNv95trOkGQ+eomn1exeb3bf/uG//rO3mv1nb56gWs3pQTPlhLfcyoRF6FF/2edVWMvpEsVDRXVHxCmdfTR5xP8oeUyMvoieo2yOuxXSM0jhR99ttBgMlHw8GcUW1liu8b3DNRexwWFChzJUM8nqLAh0dMlJNNA3yUiDzeoZYKnpbvAIASDgkowtMOj0wD9ZVRJ6nCP7BNjhxQlD3eL0lEgIKjuDGRY/3tvjNVdUoRSMCR/xqBb85SycWB3iq3R5/RlBVGhJ4Lsh5pyyuWwjK4moRJa4JAmFcjAj58Qj2UZlN9zaEyjDgUPYBu8TI1AS2GIa0KRRi5Jj8rY4QS4glhiKsb/ZsEq5dqx4myGIU2oNjeMS+y9UOzWPOJjwGBc6xE1mkIv7QWyRdaecG2V5iy1v4+mtTgdXb25Nvv/v/Wf/9//03697T/NCFIaywd7uwg0E4aNK/0ULpS50RSkQQw5+VvXyHatqa7OJLfsY0DZoKoaTVu+7bJChoN3V3f73QteigRtp19tDXgDJzb75PVdHNw9mJ4v5zmhwNFv0dndWx80Dn/uRF5bbN+f496PJ1tn59FC/nBfb4sF7n4dHwfiYwLRZ4nyxw68Q0KFa9wrvixGXojhtVQtnoi2axuS8oAeDxPC5Q8jYrDeWDKXOmJ6mAQqEA8aQ5KoNzJ0KOqvQR9OiCWWzFoMJD1wEANr4crz7gggmmIQgAUMidOEKd4AbONDj8qHEeE94SS1P88fA12s+5pxIJYGaLPpgUZKcwEn0LuUh1ysXsLKP3FVo6ppmgMJz/dQuFAB1V/xtaYJfnBcqJb8HSiLoKOmdxkvkesEneVqsTEGIS8Wsu2OGTEU3WHJqQjUfRdviYE9as51pmuriok2QrBRKJiRPrxgfEeUDiuFrCWTpZD3NfI5Xd4/RkCzBr0C000r6oo/rruM18Ctf3s5ZD3YPm/4zc25Rv2t58sz21uE53tgJ25HWPeZNJ8dK/Bcu0GmqTvqXEx7044Hktq9fo7J0C7lwtVh9h7JUmRgCSQy5RBZ4FQi+Bpu7LhrVYa1BXVPddMkZ2NBJfG305OBgxosecf/P8Nf7e+vVfnP1PTfe/YE/OehNefUjk6TF2Wg9A5XcxqAioufoPwDDm3OcImRJy8aTXSFMa/lpComj59o3ZTtTQeVi7VnJ0jOL/lfLlbekqptLrmVNBSXE6E7Em/PcrtFaOxoxjijTExsz7xirDkhTgIUs8sf50tJTVjkNJNPTOCuwCk5xCYFM44Jx5Mq8CSTUOUdC6QvH0j1Ro6VLGSbHd5GWnFAZAs/KcHt4JLaKrGNBSUVWDMRcdotqNC6fZRM6FF1O1Q7GtPQIYA/QSeWnWH4FCbI1tiWOqJy3TKqGFtfSC0c2EPltKc7hkGbQq6JkM4aWaN7KYM72OyV4Uj5aFOFAK074sDjy8HA83h1v8MdzZ/F9ctDf/oEf/5nf/B/+YHWFp3aPmunp9o3rZzdfaCX4C/eHZqSt6E28Y+79sT4FADHqvqaznBZg5Qtoq8bAjSJLeVvEbJx8uyDj0FuizVq1uSgrA6Ig0/CdeR7sQ3f6w/HBOdo+uf7Q+24utt/zyR+7edbDD2dhgZuD8zPuL/MNAb8/yGAoRmzxRAbmrFloA5osOgmS+I/BGR/LvwElaEqXyzycScRpUiJXUcAq1oHNaGjvJwJD0egObm5ziPVpVvIJfVnR5lgnzCQDDJon9oBbFwQxBwQd83DojNALk1tzo2iXaSpWGCKjRpqBEHlEHphXfKQiUt5Js141XkKEGhFC7wVT63gi4hbEKVTmhLa0O/0pnZN7wiYXnM0YjWR2zSVJ8WOr61ljD5wXzxQBAxGn0qlynUcYxEuTUVsxP6MU2TMWOdD5o99Idb8crSMXBw0C9J3gm5Muwr9mbH/65A48rk2gBHl1Mk2LhnFngW/KiW6j608fj374H/+3J6fbzXrCkHr28kGfr7p2Yl9k/RY6b9XgVX9oQPqR9QV2YIE11Y/fBK0KmGrJnx0VtQ2i2gFWsN94VTDZnN/9DYUNqBgAQRuie0YanIcNRwf4VmxrB62eOX/w8R+5/9FPHvp1AG4687qr0/VytsQn5/Vq59OGt4xy+89tfqw8AF9qoLpKcBzltNWnOikbZN5XP4ixUkwv5qWflXEdzMyalWIyHmvz9mdrO/LeGJVVKbsGDgAUMaULzGAyidF4+YULx+TH5gyct8wxRpIYe7LO5bmyhGeGOhQGqy9BScVyyV44EE7hBsM4NCgPUpUc0BAQrIJTQrKTzDUmX0IUvrSSmZpapU9aAKq0C8euKWW14anQuXSAQBpKcgRo24grzmwCONc5GfS1OxwO/+IMU64YjIonkTA2fQNDQbQiTnRUKpEWnbagkkjg7K8LLcAx8zenP0twiAOe4C/MMTEXVI3lCWq2ULAla3R4tjzmEzu9K8P3f3L+x7/JCld/3F+esjbx1g6lUq+uQ90fBFloJ2CIl38y16sl/FcTE4MvhiNWi+44YhuAw+eCQ6kcZKVv9T3UO/K5OyMZB0WCjWvTNDvbo9OzGbeYDs6Yo+2M7nv30cuz5so7rz3ysT95dsbzxIuzg+b4iG1bWCNvMxmxiQHnwi05zgRx4V3tdumVEb3GYI3FJJw3tTEe0KY5OrW3JSsSneUnPnGtGbJDsE0iAvqYmEZXQcO0I1TyzESMLnshlvj6YRNJ9sidSgJixe3wdEMpl4Bf0YdP4QBMK1NEEphUAKJy0jGRM+ZJFp5yBovQNGVIRTY6SV7TkhCvJ3cxmZUVhcpUaVYEW4Yn0vodQ027IiM05wqSRiQvgXxc0vqpdYAJIuZY7K3Hf6LC7d6yJEHUMVRIJ9KZxBUk6TD7uIx82wYtjTemLME25xdh2h6rHo3M1Vs0B7qSr/5QXA1HqXsQufLSJxQtG5RGhPLdFest2s4Ncav+kFr1ec6iN16OdifX3v7Vg2c++sN/84tf+o2dvf3Tg+fuu+/+559/SjnesuFTn/rUHWWn6ZjTAVUcAZ1nnnkGlfgmU8Ii/vmf/3newg6u0VOsZMGZ/lKXojBkx/NCA5lg3rHQuzAS5YjVtvrTqh0AHSMeTHbHPFfQ7M0OWZre+ciP/+Qzy+vP3zye7K2as5vNii0mvEqEJZ6x3joLpuxsYP0LlpiwOglvn/HSxFRpzrRB55kXg/FJvRhNpEhHlNahNeRPgUNyUwrrH1kA0YLTDVZAuoAjF4HFKtRSKNqFJ7PXJSdxHfK3NUfS5JaFI6xeMy0EyHulEICYNBozE+YrvJhgwCU3NCFWHjlbLlzYBsF+M84rIBcnJSnEhK3hzrVyyNEwPCz2i5JRXAmQWQ2ROGvzweMlzxJSgQjYsc3fbj8Ub4JAuWHtXSTKpnRqSIv7BotgJ3dFeWKWd5Upi+K4SETduaCIqpmokWSihSn6gMceRkil1PQyMAK7wYi9rVZY2o4SXCTG14AQ5XPOxbM/Go3Hk9NT4CYvfiARSmh4SLI3cvAAH/m6hA9V8IwF4vD5iVFvuNOsfW0Ob59Z9Saw9T0Wkyuryb18a3z7nqs31i89NnrmX/7P/2Of79u/9BQP37OqDx6HOWKVFiqgIV1vfYOYXEX0SrsrjujWHeWg1Wu7PKk2/GBQj1XfkbgiN3AGT+jx0dKPrQqii6gcSkLSW2VKSH+x6EsDodTgbu1asrKgzXp579vuff7Fm80QXL7ePPDYD/wHP33Y3P/HNydbo93l6ROL2UuszS/PT5tTNnD2hmfHvfVssT6fr2eOjn6oKYvuS5UDdjQ476h0RYLFWBRaM85NQ2ybG4lxJtRfVvYHWIePzkGMrSIeeYGAYEHnfLg5wK0JbPYSHGNT8cacyhF4Y6UWFDTW2sqmtF2tD1HAFz0stwNpxbO8ewN6PYbsbneHBg7hnO97SqCZzpCfe5ZaKmSwWlB99mTtbMN/MeX1cm5igBJaYlr14Ipn5utTgWyjBYu4dZpHA0lhcuSeLfBJI/ebpLy7Z8BHaAsUlFsviXkc/2BLy9I9QCYfOoS03rCMOg5J5wus8MEVYaUK1llTWm+NgYBSYMyV4uzn2k+LrLz2D95pfQr3Bq1DRDm5iC8/2t/2c2rfIpJIHEsnmgy+VVa7B27agcjycKfsPGrmH+bAPrWjzXDFdeIowTHHCm3xWi+7k5xEUiZZaSd7EAqEYPndeF6DhUKpYbSYH40cnJ+e7+1fffcHPvDkl36vub67dfQia1p+RXq0I+mAzbMapHoEN48AIj/Y82pBBb+rgm16p4CQG1hRvzSAPyOoygnw25xfzAMfLut4Mf7be14d87r6gQ50b191o1Kqk64w9HqTvWu8tGdyZce3302u7bz7I9tv+/6nD0e8fG02u7WenXFnHIByWZ6P5vCxULa58wojPfq5D4QFYqIcuhsZ6YlEsd2d45J+EErwEM0wAaw1Z7x5T9N0FV93DJmAlcVisj1poYgMmEm0GrWHFlNqi4NBHuGBEz1KLWTNLU52FKL1xJALIGDFFp4ysUhrLaTgjoBiCObOx4oiVlvDZhiTbRny6F45Js185J5ZTqZWLD3JDeybnfAEhbCHbLJ2YYst297uJLL96X8pGOJgyT4KC2+CuA0nC0c+26YzYDwbb1WSMhxNuKBs6OXnI0JiDnnCIweRRekooVUEkSVlViWgj6naF2TkpwwOJG534JzC4JCCOIskCql8QXSLSRm6SwRoEJEXj5nXBJvXMsxl4QgYGUisDqxrycLfKkCrFJYtHyhsd9b/hMrIRN/wABTuG0g0ak6n6z7PqQzPprPhzuRktJ5/7Y93fAj/rBluc4OBWRAcHFWCsfBuWyO4lauufazDZXhTWkANud0z31QEe9D5W5shJxg5PzyLaTMZL9BGPoczevD7PvcTL5zfODijx095P+3Sl1niiWDeLldtAVVuS2YPdi61nQwAqNzs3G1ZIhQxKq7qF22MXsYso0cVj+mbilyqstqsEqPL2XFelhWNN5VI5mbQ564WfxOSl+yYG+qKgWBJtgjDLqEtK+oPC4NWqBmVnXAsHCUPnIFOSu+CRplALqySjKTWiftmQVieAh66MlMIQz78M2k6DhqzeNNGuGecpHQBeW8HCyceMok3dYCghJayIAB2AAuOFTmKjzWxAGvdywZzwCV8BBTiNXvb1saFj9AjNgkMtBO4ZKPX/4wHlppGlH/yO2lNHXQLQ+plYhCatLzZlcaWz21uRmR1jJ6hIPEj0uju5BwgdojIQEQSehPXKnXxdoAaZAwu1zirDWzL7S1nZ7zl9qGH7n/u+WfmLzzDm0udqNJ5dT9RT41FUwVFI8qjo2GYYzKtTWUt+zK8SS1gl77OotXXkGZ6xsg68dEbo3BGXJoYXHnH6uzKp/7uf/nS7OpXXzoc7Y+nZ0dsNI8mlCcFGPHDZ/F5Q+O94cOkLwpJPA8Vol84KV1oh0rjCZLlwF8BE4RA0ThJHQJtbXUEFrVLboooW0KMvHwxc8nGKCdScrcWAhy4gw5LUICYvJv6IwNEXWuQbxPImlxtk+JZC2+6GU769OMAuxivFMnYIlR8IGgwYv3xstDwLf4kEQSssnyLaZOtF1XwjzOyklXe5vD5p0oTlsDFCgAEfAjShE8JygxTPgmQ10lYhVtIK6NJFKGvSK1TXPhwDWlOESXQxhtnUz2KsM5kIZBLsTmXU9gQIzBXjCSy8o+IkzztuaVVjJpDnmgF5MzAsyMm/SPmqD5kzy7TyU5mo+vt7dHR8eHV/b3rN66/9PRTw/39JfeDeOcDj2esWZvgCb7d+Yx3oXp7kgI4wUnz/TSKEeWPNJeHt0YLoETYha49PcgFqz/r3vZ4PdhfHV/59M/8Ny/O7nni5enW9uh8dsxWbj0mnaZ8oLfQyiORicFEhRUUFndDtApCVUtoTGo/Ws28rO4UcZmJiaDD13RUb/VfSk4NdSmcRVfbaId+ILU0v6UskvCnCGzKyZe5tKwMuilFhkaj+xX0lUJZ8NcJoAycw4qzZClR5QY9+YkGNrqtDwAXRQEgEqQKWWqgwbrvy4SJtUigcLwjP6sbq071aqaFQCz+6W4oYFFbLRulRSjiSyYKAxHLE2sp8ydSOsGtSI6B8mITxwkpaXTYh4YEaIRufmwHEdwsvgUdiUNgh1A9us2DrWB76cboMmUeB79wE/ZswZamKuJlCqEAc7XVZttfnScDKigRfHq0HUUDPTQHxCkISkpn5Q4Xm/fEj8ZHxyc02LV77n3kg9/ztf/zN7fuu9GcHzWzI9YC9/a3j454ZB/xSgBZwMfPtRpcDc3J5eEt0AIuhnarkJmu8YoFtLA32L93tbj24c//s1u9t3/9eLLa3j0/v9Wsz91pVYAVl8o5IB/rXfO93mAWS91gRI+1ZPQ5i1DxubAd/SNmLXWiPav8LLKo9BoCOonmouEMruqPltImeRHLwoxQVKjDmb8sePOy9qihRhDTKs6gIRMTGWvh2qyl6BbEfDj3WhnKvXBhywiH88hT6RbhT+5dGPjxP2iYGhKZEqirvmTJCaDUEqeMmOEy02JJ68JWrMCA/ODKGtjtx7hKIGIJNBQUANZtaVIHIgE5CBDdpkikOBpB2np2SGwyzdK2pn+LW7Kn2WQncFQ8V2FpQ8pKjCq4YaLmihiRNkfbcN5pL+/KDIUnFmLdXHokVJVapLBelZraSxlXTrbwF1CQWKFDRTTyNtPk5kFpHuIxuwMZP+RZzAfcy+CB8wXO1BilPTpfnDSD7/7sDz31xd9oaNezWxMUc8qD06gM8jM5TylytL0CVbVUYaGX4a5vAWy8Bja6DxeDlytw5K7M7mp25fEf+4dne499/WR83pvMjg97/el6fsJTv5sJYNBqztfF81YZp4SoOIiCdgStsHa2bbP5NCoYbdPHLz0RGjSL+AmodfTHNJ0c2k3lRn85x6vAFuCMhRsRttWyQpA2KCCGMidxBRyImV9W9tgpBHo08rUALlvB5NUaVmIsuBUgZ1wEXLqCtESW8MuxCmXkdLlqAHJhrYhhMcnNDJFlsAtFQdzWkby8fqxe0MW5QlQ2jmQB+QqwrFsXyBs0AQRdbtfyhWFMjwblT6oayOAiGTXwmgxmKIjnQlQghiIQunJRKJfeiCTVxonQHr3I5gMGN3vMVIi5S9n3w1/2GtBKTwhltrLyRxropI8nxd/wicC5EOz4hYYCwta2ToxpSuA3l6gVr0QOZjlo6SG5MwxXfr1ADG6k9Md802x8Mmumw/3zxfoDH/7AU1/8P/hGybjhqbH1eDLkcZ7oOg0uKLNjcNAswLwMlMhwGe7+FkAx6PqxGqU3xAcR0Cx2Z+ysBw/sfNe/P3n7x59bXZ8Odxa3nm2WRxOe5Dq8ybPMzv6yuN7OAbmvt5pxoxBHIj93+cFQlwpfHs4Wo4qlRVr9L48pCOR6KE6Tq1dqbwjQKPVcKFJn0X+nkDoL3qRyjCdVhknyNpmRTgCLv3wY831YKEin5SoPeTiNnSR7RNLMcmIu/lOahecH/0ACJZMz+As4csGT3kolRsdHkVp7Xy48trcOoHN1WhhVZoPFd4CFOO1dQgUj5Mi5AcPFdGkhfZrbC286WFmoyvpZqsKBXwRNE9k4BOvJLwWT3F4amaSUBSuKEu7dPKFPZyPpdenECSKEcOZGMNWmioqW4HQ5NYFlyenUqoqL/GSsiaXgmGBx2bBKDuXpEEtEi1+t5EXKmUT0Ov/AQm7+Aaz8BCxEWM3OJrvbi6NbDT52j5kfO1WGw71rc5bcJ9uLk8MHH37w+a9+ZTY78RsE5+cshgU3c0TQLQDL0iyk6nN5vNtbgO7CItjBQ4/xARsWgHmPWm81eqAZvfOdn/g7091335z2VIkr6MfR4uDmkByiFT9Qg/V13wrJZ3rxsLBdBi0+3IIWilZoGpChRsdQ0U4txW2W+lwwIaiK+hoSQxa90Rpy7rKqKu1ytedkBF3hYarP56LX8BjlJpjn/CdOi9C5qu0/yABXrA9KTuTDF86r6JDHOIwwKGHBSkRpI1sDwtYQ1wRcEmZCtB24oXiYtTOq2jiKIBvAIi5QI8gqXcKmRK44x8PhTodVJdgiXdAhpVvYtZAXYFkryJxb+hYkqCDl7r47CWgWGiXccef4sX2VlR3sk02kSGBjVXPZBpp/ZstseOvz9bEUSMWZVY3c/CZSUnS+u0P1uOy7bRUTR4D0Tdc64By9AkcYqkoROZUyxruO1aepScYU8S3QSZIwDxBZ51BHsLYDoxelB87nWal0QueKVb6fSn15SxHFzxuGUfuM9BGqzK1qTs5vHV6/eo1Nqi+88AIfD5ueHrMLjibirUY2Mg1Gxt5qf5vnV8TYrj7W7zLcZS2AWqmN+fFH1dzb255PT1lz37tx42yx24ze8bG/+188N3vbS+cjXvfIQkBz/hyrAfhTvKydF8gJVS7ZuMoOQnECVBGJYpVLxWAOXzi7ko09oySUF4BQ5VQQxvJs2lPncaz0hrBInZG5m0V19DA0fgSUjELJuPHaIDDIc352Lj146S4qttoTDc8Fb89QFZFTsFAernywEPDyXK51dDsrT2ixIQ3NB0F8ZXHckSAdVdA74kddCLBHNOeD+CW+RQvwIlq/r1J5lUB5KrgsyB8LhIZz9hW77IU0MREEgKmL7sqcBrooWQFWkRYYWQCs81qYykwNklfPtPBPGqRJMk0WoKm4HDX4NtBXpLrSlNLJ4e7TahdJXJwzyR99FpHrUk4Vn+NmQa3rLWXRayuvsqpmh9k39pT5FaN4hrGS1FhEDZPMgMOuVSrL0Ei/4GUz/WULVtLpHhdKkVHvVQ5Iwlom8rMhZ7G3t39wdAxcP/7Bjz71pf+X993xYjP33aBGaN1qNtzbZsXs/Gy1vdPwud/LcBe2QBQEuWKst+Xb2t/ha0DHk8nuarh7etxrrjzyiZ/4Z3/ycv9ouTNlNWN23MwPevMjV6+8kc/HVnlBFYsnqBEzQSZcHrFg3xHi6hX27SyJElQqtOm2Gjvn0DWTUkEgiDbXTJBL7Qxj08wCMGq0fg22JWNzxYzUUEgds1ulr+vWvkxueCMmAQNBFO/dIVwk4YM+4kjMgjaxWUgUp1gTaVtHzgCQJufc8I5hw8RCU7xkWpijuNl7vfGEZzHZBL9iG30xUWi4AkZVtLJ1dwkjSssLOuBDGvyLkMakySjOVHnQcALqiAJCR9w8Yk2oJBP1jLpKiJ6CSfBYElw47VVOfj/DMQQI04MLTxte1nL2L2yN8MxQ8BcPrzikWOIznQwJTSJ1vDZmv0qSmWTLx6awRvwrjuEAheUTp7T46cKMf42r+vpgAMMFedEeuJAG2YDbOts8eDgzJ6+wAABAAElEQVSdnvNah9He4Xzr8R/8K0//9r9qJuzOZVw6cbBtVrt722cnpxQzRamqHVppL/+8GS1Qnf/KkqNoJFxMU0vwoUbD7flgspw80Eze/b2f/6dPne2f9K+esXF0cTQ6P5jMT4ZzlqhwVLjRwvd5uSHIcKVjhVuT/aKc82JI0AdnimHVnUpohapYa8+eZxxENxhniUf/FcVzrSB2ouMhBPHGI+3KSJGlNQs5aCoJ/omqu+GTQoRCEjMJMYnsPLygcWRzeWWDhnj3u3cho70ZtYSYDLgoZ3mEP/aWO4xtTDHSRyA1XMgsAhhTxoQMAgY2lsd0cKncjO670jA6uBpgUxWkoahru9MdVuTzmPyjIU9xap8eU7DNalrXCG3ZaQyzbJyacCE1oaU3H8xur0AxMnDtFF14UrisvtOaNhPEEUMWQY+2UOVrW4EYz0tmamR7VJLwUe1Cm1ii2FPJDkhpXJsw/xUsdUQ2GlEOFungRUDIbD7wBYHcyoGPDnLcVPpe3aBR0AxOca9cQ98d8DX74/7utemS1zOObx6dfOJH/92v/f7/wy4HvgXFHe4bN64c3DroTXgtLFqqFJfhTW6BTrkuihFNIOJiGophR69G+8vRjWZw72d++r/+05vDw+bKCQ/NrU+3ZrfG85PB/IyFdp9P430yvABr7le8BCxmWywF6IngNLknQGvXg4irVaqLfjnyqRooh2oFYHHaLiaTItboi0UyhVwuamHXnQGAi/qc3PHaSqWLd5IEqc3uzQ4sAljnZ8qheOVjpFiIA3yxCUuj7FY6T1v0NIH/GrJggWyS5cQkTI1jxSTSmARSeXCJWSdzQM953sfX2LqFlccRC3mIDwIJL0jutgYLLu6FmnUeCECiSoK4FcL2LcyDU9w5RCEgGElYoCXw30CRt03SiLYWJS2CktN3q2eaCWApk15t5KC8lpuA0A4YMgl7S7RpqiGskr1bsEWsw0taSopO7TxBPnMZmVOuiqVVlUPLPUNfhiygkz5kcwOY5Z0X93y6M1lCmDA1TDZm3T71vDg7unHjxpwXlNJgvcH2lb0nn3ziu773w899+f9rhj0G6Olsuru/Nz3hwX0erh6616brvwh2efi2t4A6kN+FklGKXNURhUTFeEH2cHjtwcX5sNl+8DN/75/8wddn0/71o9M570VfT2/25odbM9CKt6pjeryKgG8PuqPd+aBrWKCJw14Aq6Z+qI7+jlpURul1NLOmgUoQwHKnanQbtcTccMTUOXJ1y8doJ4okJlb2GGPOqYhZPDegtLV+5BquKTKkdOY3PB1sjDcTtOsyec2NYpxjbPQ0GguhbdSy5ZQLf1UM5AaFMYEQeg2TsxLGvwzhvqGUQHE8OK1soDYLZ0VTfIIHysMaOh5WFVHsN+cuF+IfJls4WzCMFJCzVIMTiwwNMebV4P1t+LSAVakVW5WCN5E0fYiRhkRHCVik8xJjGwRBbEhDQVJEIMkY+km04j/XlttCEvHKJgnk7R+BvgV7y225WYTFiVktZptH/tTQLl73WX6qx3Qogvt7QDVKankUYvFuuxqgkONh/2TuPcEtntbpbwFP+LqsDjz2wQ889Vu/tffAfdPjw9npKUvyw+F4MWWN1k4t8S6Pb04LtNrxisLT+8RUWtSa0Xews2yuNvvv+IG/8w+fvLk+bfZvHZxP9nbmRze3Vue8E835nZuq8EtYslzw8qP2jQuiVTkv6GRgSy+Bns9KszproDysDqyQRo3XKLx0Kle2hkW6QUbJYhyUJfRkflOjuuZAmjho7vBpjZRztT8qC02hVch4cwFsgCVTMUBzxo+x9K4ss4e3/DlHJoosVyZyAiiVN2RJL+4+UoND4vJ8RUiW+lIqMUKNUIULBIxSXZ2pLmtrIEoWPt4lbNPyR2ksPheCT7s4RTznhCLmkmZGXkW3GNsvex7InulhWDAcwEynNoEirb55MWqmhFnLJhJxKUjYul1KQYHd0zV4eUiUIwsYWjkZtsNQK3MQ0yjHRWkoXJLIUKRVEQAr8sCOsrpKyyXccySht1wPuC2SG3xiPy9NBq34mR3KrAbgYbGdl71V/R7vqzs/Wk+PJzyuwRL7ePLSweFgNPn+H/6RP/wXv97b3+2tZovpKe/fiUaqEJfhzWwBNekbQ+mXKhQ1wphRmeVgr7ny3o9+/h89e9Tn4/NHJ2e7O+Pp4cur8xOcEBAJPV6xfNXDq5oN5w038xfuZiAhGCQv4CYWEc0xXgsyIdYUUBMj1P0UzqkmBgRiO1hCRbt+iuZrwmpwzDCKhKDZ60mayh/WUfJUED0PplA7gaYFNaiIFiA4soJUdYeAEzhzpFDLSYFQe41JB7AS3+lw53+Qj8QiCwEeog1oScqbvBABQMETyiISyy/QFLyCA0QqZ9UddnqCw20ykkyaEiWQxO4FzT39ZFIBE+/x4Y7jhWBzx/iVrkM0q0aRJRrNquhBtMhKWVLmrTrkRgguKaLmsb7rOnLbM22PtY0V/GgF5I9c0gBGleA5Aldw4P6pB88hE1TQk656gpCJ5ksiyQqIFkDiyBOOFsBahJF8kFw2IFSft4PwRn/LV2VMVRKX4VCCxRav9VjOx3zcqLeeHh2O2KuBhzvcPZ6uzufL7/7kJ5/44y+vT45Yzuit5+M+WAgrJQEIPav6vfJIahtun3Uxl3+/sQXsmvy63s4F3bNp3ju0YkVVPp9IZ6nSTqGL1QpemtTfWfb3m+EDn/zp/+qrN3tH89HB0flkPJqeH8/PDpnru+HZEai2XPFEzqzPJ3PYUuzrrhKpZgk9LDuJO6hjLrupInpEKsWZpEI51KqcZHFgc0N1Uk2KBWrIZlFXNTnWK3y3iPrO/jDcGddbzZ8YublMmx0GWFj2W2TlBPrMQAEL14+0yUw4sjWy/DXV0kKcjaZE6hKLKSCLOdlQHZYpo2ZN6cnFfYUWNKgu+zzKyxAmiYeUoqkkRXPJXzKyo4FITlrACsZJyTZHLTR0FEEvUYhikM2K0ijUga0Zbvpg7Q9B+UYqJC48OQwICmwGQebwsI0KMKCBrT6e/BRc1bIWVt97I8HRiq+bC8rHfnKGAV/o5WyWbB5h4c42TuSNMNUUkVduMqEppSPFpqL2MrFlcHcNafSAUSTJCEXrm0np5OEcj7x2bApN6eHHNBA9BqrcMGjXsfrkJvjYQe4UspPXD+coGYuGizm70cZs1Fj1lovBfLm1c/2h5184bHavPvze973wzBPN6ry3OkZpVny8bmsbvhMX9FFWJRmNh/QT9U2NiY+Q9g2npF+G12oB2ohNc+VW25hc05m0GgsfdGG6y761EdsujlbXA4J+RxCSScObGl1fWk4GvBJ02YyuNKP7miuPfvQ//sITB+OT1V5tH+RrzLztig0KvJFyxedRmRVyr5AvmPLpKj7/x55LXpzNcyYMY0wJNz8UG55uy8o8UYVV+7JCuubtdEw0UFNGQ+Wvx2qz+RuVLl8D4gr8xQ6RU8Txw+8YiQbry6pmU6iFLGEgSJc8NIFbuTQWgMlG0IBhwpq3u1ijXaJSHDTaJpQsiiiMym0ezQwK0Ab7IoWDu6iUC53l2UEBltrjbpbdinJr3rLHK/148BaW0Cyn3DF3uQqBzRgoiUQphe/r+Tl3NnCJZ9XfAharMZFeXEByzRV6aoPEsIn8xBQKsoUToNd7CplgXIFtELwALxnbmPyxenH8qGTLy3j5d8SeE6owaFo/q2KTnaIJLg4YbucNB8DYyoR5YaoVp1RBJThunjQvNHRVaTMRENlX4ZfyOQvcdP5mG5n+lKciitF6QtxLsEjHRI4UwOiX+SHuFOMzK/FzFAO4gRSdWjbD6XS1/8DbX7x5OFssv/djH3ny936HF2XRS6PeZLma7QzHU1ZnmW2Ox/QQH5tWsPrBLicIENWwFS7Da7RAgXxpCVZqGwr6doTHXKnUKlOi4pHkXhgxNDTjN8MMltbMJ4Mhn8fYf9s7eDd7M3noY5//wtMnk5Pl7nTFGxl5fpRXXJ2DU37bnH1VS1xm38yH6+JOK30W7hI6AXQ3Q7scDkZEa3Sy0Ck7FlkgiCp55LYNqs5fFUxIwJzr9cs6PhmvsQbtkUvyM8TLIxWCW7Qyq1dgGXRGWF2ymurzjwSVOCe0SKWgtj7Zp/XVPgNz2V66mqEyW0KdBMhCEg5KZugsilMyRk7fQxEOubem9wQEcQQ1Wem3MtbCILvbwVykisKhLxo2J2FgbaA8zpAKCCvgUORO0BI3M6T4TbQXgKWMeqigNLmKJggoTy7DgBOaFQlKJo/k4lglFqmpGTFkAmd+aTSziXpSdRyMqWs4WZwFoY02BAUBTMUtZQo1BGXQ/2SgbUNLn7Zue7Blu2FO4zJiK0GqVvEZaUrZkJm4Fv5QIIe0qCmI49NevAgeUawJS+y8PZZ90pPJ+cnZRz756T/9vX+ztb07YJ/h6vSM6vZ3BvvXT89EMTS1SpKha/wc+QCGJtY2Q2p0efiGFkCBGIFtJZ8ZRpmCD15CyCd1eV6CIx3Dlt+0JknqLCM+L7/mE+XM9xejxclgNd3lLWcgxfDadLrbXH30g3/97z97Orw1Y3UKaJov2dG+OOMtv37G2b3sPHCDD7V0J7QbQbOPwSdvGNz0pyhDUaOBaAWyoUPoRdQlpgFBHA3nEFBmdFK3iCeX7rZKS9X8q+kQF8dEciAP5tAaPINB2FQUMWRqWZk1wqjq8jQCFnhk1h9Fh3NrUIydrpO3JDKDUtSDqOVhmhIZtKfcIZWgQAZnT1smVwKssAKA0dfIpHAPASxoCLmUJ5jNEbQiSNEF3jLAGlZ7beN0Ids4ocpsNgnFy8oATi74ixQc4WimyGSjmGnD0HllIsxNxiQlpipUbW9SlwUW1V6ySrxtyGnythwspILuYspEknbtvyRRIQg5FgeuBER6u6oC26QyBd1QVokZuYyjp+0vHapcceSKFozKSFyCyZLhJLWAK/2tUuKL2ur0nqMdktL9W6cnp3s7V56/efT4D/7Ik1/92vL8RW9RosA7+8uTk4b3Ro98nyyc0bIOrfDe2OjlLAUJIop8L8M3tADtk2m1E5V0TemV4MS1+1HsmzxCr4dCbqHM9uxvD9m8zvRhOePuCVN0Onze215uv6PZfeTxH/tPp9sPPHu8OOOdZgyGgNQCwMrPR23YGsr8zycEvSeIpyx4gWIsYzPwYLGxDwdRVULWWauK8Lo8IqZ/HNeyD0u4IQQqgh0sRojDEsQinfVlqwTPeBGfWsg2P9DQkOphSuJFARZ/LY4/KmoM0gtyEaiUlsfP/8bEQl32CkFLpqabFe4eW6iKuIl3JgQHSlQwQJj68qyHC9/FkveU88Qe345QRGWUIakdgayIRJbuxCSkIhAvYCU5QrcyaF1AYLWzHINK9WgPn9SGpUvKqZotEw/LSH5BxALFKo+8nHSh7JyyaLI6Vzgrf/tPaoDQIKvTVxTLIsIeNgorebWyGMw2TiezlpyFQHuDqJY/V5AXlHScw4FWCJdUHF0xSzhDb2dHSJELXc8IRsnwykomhdm+kJnLAqD3v5Eoe0g9GokwVJUKMCcfDtmQu/3iS0fjK/e9dNa8633fvXtl/PLX/rS5elWNWZz3hr352QlLjo7NrqeklfQGFAWWpXEWcBle1QK0tk2deOHehs+chhM/y0UDEpN4+w6t4IkOl1AAltUcb3jGOuW4z3ar5oAV86vvacaPfPBv/IOjwQN/8twJr0EZjrj/O4UsjhXfWAee2GyFY8V3BYUtQcpNoZtfHD0miaUTKm2UAwyLkQpSCGR8wEht4cIFrKTHPRF08jpQ4pOmHkAljc/WFXN1z+khaTRDGoEomVki6merUBy5DLZOTjglF68+Z6M4+maxppCe7LRX/iYXlMwiEsqqY5hQW65GZ7BIshcIkI3l83xpgvYzkj1qXHIMQe1kknnhUTFUhsAuPInfuGmQAQqu74aCUoSGCtqH16+YQMrXpjPNAnAMMsME3Tpx+WsoCcA0QKdiEump0qVSHjetRmSFMN+IEnq5IUk4KFVatCVvz2Vqy1q9NHABXEukahqoWgiJlqe1VoaE9FZUPO1erU9REVJIhIr/8vXMbCSFNvlRNHSISHodHaKjWbAkmaL9z0tS+Wgyi4h22nj7dLnlO8CvXOXx+fd8z4ef/Z3f27qy50aes2O48Qi5o5RMCCq9JTujKfk7mZN8edi0AK1UCxw0UADLKU6ase5ncJ6g4eVcLV6PRzyA4tyNF8eMhpMzNv+uJs1939XsveexH/3Jl5fXXzheL8/BIL5iwgvaz7d8CsddV6KVzwbm8cCsvuNPgVasF3tixzHUoROlaeJCFsjBJshyVBxcCWkKQVoR1buMTSQVpWqXXFJGnRkaBatuvhkW1qu0g/FY8GsvLIcgqxqbLacliC5zYwpc0CEivlsjgwg4jz2FT9CqMralcGEwtSPzvDgLERhDAIVVP/7a3NnKsCGmmsRDVsScd1Jh8u05DS/PXNbrmSyD5AKF4lW+0gZ0qUwF13QIyBffj80JWCBJcEhGBIpQuSCKVJK6QCxNJikC2Li2PYn+b0MbE25wEhapjdBgXkcjOvMCvSlCguWyRokkAbRQpBT40iC1Ir/FvTsriwTR2At8HI0JXUxLRkwAyqYDLMxLgQGqyC+uJ2PbKL5whEGFO+HcP8iiieMKGgBuc+9mPZ8ylvPyLB6TH+9fe+nlg/Pda3zi8Pv/ymf/9F/+r2974PoWJsESCfeVUi3l1BM01Ojm34iRuMvDK1qAhiptUwkcpeia+kFGIi0ZEMkToFFC4rx7NZgvuLO1w1fglv3F4Ebz8EfHj3324U/82NnwoVvTwfnR8d7V3a3ZyfL4li+HWfISUdCKORQLWHhYvuk4sOVyu0vsLEHqZLmI6SCGt6w6OXxZKHFaATFqjwDjAgIRmmVslHMNCtHNEjNxk4KUHDr3ogavWBsZdC4ySmsgMRxV1iwqLecXVtyJKLbqFGwQg6Wl4IIFWGKKJhc3AUJc2tcioMatFAQq257VNUZYvpXYF6Ch4ozTBPCljrYMiB4I46SlL3TLihXgBXZWfLHV1wiuxWGmm9uleJfPBabMB4N5ikhQ6AS+AaZtloeFaQ6HLGghBwtpHUmaJzS2E7E58LdlZZswWec1UiJ5CD1Wdm5UiCVFA5lFV7d259KJEcloNxnyvZzQ+hgSwnhuCFsY0nkG1alymqbCIEyO4dnSJ2d7cKYr4IS6xSzz0nwKHbYAprwdmVi7YPFRBCVDzUfiGs7nU19OK/rZydxhXxyfbF27seBDYVtDJhqf+uEf/r3f+N/nR0cIn5X6lA95aqDfrrjUSrW+DHdsgWotdcc3U9JBGLmqksAYAC7wMJovNa4flMzz6ESUHkRYjXbO5pPmgQ9951/9yfW9j99cXbvJ9t7pgkni2cvP9xenvB+I5XbfuqFvBU4xPXTRyhV3fGdMrqCKz6pmbghGeJtY9KHXMGwJlI4TcSIdqg+laSCkg5PnmQkaY18nO2ub2pfOgKUkA6xyUsdSRFRSVk5OKUKdDAeZwx2NtejbIbZQl2ivdpS3GMvBgjoIM5/KniB/frU8a41yybENfm4STqIHkRoFzDwnHmhhPojXxjmzQlWdfSiBjqDNbfByHZC8dcsS2RMouj/a5vN5BopDqsoGYRtDcQmpuxJz11XK8OIIPRjM3UmR1u0eznhwAr0Qm1d849BWgx31TwUshxMX1fzrHnfaV5vXsrnLYltwJNllLN0Tey7FmtfABT91EnTC2+QzSiK9iXQ57+rhTVvcrLHP2ICGAAgTnIAAvmqBnMQbLsJVaSzUVTNGMyW0TWhZpeFmB+oOSJm0wgnSc5TA4ZJDtQOl8HVDNAs2DpEkkQU0HaZJotO2BtNqKpgXazTo+Wh3OltPV1vf+YGPPPlHf7w8O9vZ217MzrixgcsYD4+a8grBFd9DKj2R92V4VQuUctArfCQz/cwwk77G32mW20CTj6w3437riLEbiG7ghhX6txztnzdsZH/kfX/tZxbXHn3mdHuK18ULjucnW/PDEXusZud0DRuvssrue9lxsphMupsB7ECHnQy6g4G3ylCSKwJghLaaL9Co5yqMSodW6FWpsByduIIzpfmqekw9Gk8VSYk26oXV+M6wy8mQnUQsBnF/BnbijDelQQTvQqrMvP5EcjTTuaSgyN88XtJOMykokaqrxVcunBUEiN0hJCiDhdmu8HH6grfIh1H5bmm3Q0qj5ocMcfDGLPPFoVJy2hqrDCzwYDamzcJIItmpxgqgt1QBC+ghLoThnIKQBNzgyCX8FSyBExfdiSIYY9GekKBxGgRsZS0CruO0ktDGk0YzpYbSbOjMase0TZIKp6eQmNFPCUjNGnbQm4usIlkuqSViyRC2LSU0lRSa1EQJI6/+mtJHioAXZQiCEKgNYV31MCOkOSIEJ2QmCw3iqp1fb0uAjuzqGQJDjQLAyqvAqNomnemWCimP3QBIgC7rC6iVcMOAsphLr36scqfKcyb0aGx/e59dDcv+mFWUk9PFBz/+qSf/9ZdgESVf7l69NudZ2+0RX9GVpc8ylWSXx9dsAXqDds3ssBSdJltd2Z9Mz6a86Hpnm21u9uFkOOAxA3Yu9Cc3uJG13r6n2X/3x3/in5wOH/ry02erHu9XBK0Om/lxf3HSW8y2cJuY8W2BShzdysCnmz0vnHIyCDwBffB2SkpfI0g3IKI77RhJTFYXSCW9DFINNQdw5ilnGe/QOGBLlZUsegYN8Ber8wA46sXUmKmSd2RkVHfJQwzcPLU4jaCUNjEhIVGwK5piaF51nXJThNpPKdoQ+TjXXDMtg954gyW02xpalKFoa0XgHQfaO41CCAzhzbHrkDtRxLeZwwdiWOo3JITz7UOfZ9zgkEJJt0wSYQGIhqrNRgzBJF0h/kOHKJExkuLHAMLKnlBMqBJzUc7bSPSIzBEPFKDGMWhLBTMEfPq49XkiBvE0U5vdbBhyMKItl4gqkRObj2jRhdrgW2XckjCAw98OBuEQ3anaSqBXZn8Y3ZamtnkRfEqtHG/S/PCsYcJaKY7/oedkPR8NUJTZCu1kLwRrovxKnSgGbfF9RGxbZifDlktcKNpsdu2eG2cv35pO19tve+hwur7vuz58k8c5jk5uvOPhw+e/7r6x5ZQiqBjnGY0s+DK8dgvUZNB+kkbjB/BnOyN7aTpfM7va2eF9e1vny97e/gPT/pXm6tub5ZVH//Y/ena29xKfj8BHPz/un9/qzV/uLw7dyO4rGPQy+OQI7zHjtmBBFVsZ3IdF53DfKTiFmkSVRC4NXq+E+4/6TSprq55ogOqU6QXap+oVxKibgBRaiK2pV6kD2alMzE4huHTzl8xFEL02MsE8nhSqrDa3T+RIXMoMDd6cbOVpAW1IQvwazwjx4LQLzs2rbxHzj2WZgGBJxDyUDYHNl/gqrt2HVUQkTLaZe4RAlvJkJkiYT89rUce8KQih4Gm1rPIFEbl2FMIrTv6kBBRi/OY2vCIbNGnZOphK6CpDE7VlSpbAicylqhiJ+U8iXpltbeu1wdxKYk8SlUyhLyBnTlaBVE5DA1E5zkXcpqcvWFmrSNlW1rpuS7S/pCeVEwiIr9JVtww4RnbCpP3IA2Utogesw1c+gmrYLUfcdGUmZz9zSNGmsXiisvL4BI97iVmsr+D39ra8e4JFDYbg+unJ7HQ92L1+770PvfP+937Hk7/92y7fn5/2R33WRClgNOYlvBl7q6qXxzu3AA3eWaUE2DNrSQ045UYr3ZXmGOeJXaH3PnJ42DT7DzbbD33wJ79wq3/PczeX8+PZ3vb26vjFIa+LWRw1fFPeKUS0wyUqnqma4ncw1NQrGXAqsusKZQgk6WGhdOJH4ZS6EHWNfQh72aJFNAvz6lqrO+ZCYRzggw4Z2dUuWKlB6i/nhts6QEVLr4uCY9nj7RItulPUtqRcdk1noV0oVpbZBXCjhCHCSkGctlCK1NO/F2i429gx8a+pEvg9ZzgUKw0mSAc48NeFs272BwFkxFflS4oU5SlkbmvgDDo8FGJIq+S8SQt2lcVjJVFlT2qgwLRj68WBaKrqilH3nixiqgVLdM3X/Jo9ogpYikd0WkhmeB1IIT+yEDgjh/6XnQSFGaQnyWTrLpVCoRbJYxeSXzhsxecvvlymhwWRZoE+JUltMeGc/jdeyS0JsuIGmUWUfrBeQGGuoUlLp5LBwvyco8MccGQTMbo6wLJIwSWxSOSqHGWpzTCkuXgdzYsvXLtxldVcH5QfTw74wPnu9cH2/v3ve/9LX/kyys0uZN5Qs+6PebhKwWyHy3DnFkhf0q70DD+6DrRyOQlPd8Yy7miLPSWz+ZDHA3u7953dWjbb9z3+ub9540P/zpdfmM57V+fL/pW9vYOvf2W8Pustec0xb4xxFcbFRHGDFcdz/Gg6BbTK88MunursONoJVREL5aGngB7UhFlhqSVSmUocesND/iQhrToROasghYYIrVP6qo0wwdgGPWXpAUTFUGh0HHWDKZSacGziYi6BVb0MH7kpD8eiUfIwVaoEMbfKhExKlpG1xMwNg1bKZjx1MFBkNkzV9JBoAEsxi0Y6KuiyFzGBpxSt+cNNiyYjoVKJLMHM1opsRoIRCUwJfad7CtcDdZUrzGLPilWpHCtPISjncCkUbOW3VkpD8S1g0bKk2apVZ5ug6spfey2uE6xKGHlSCBArvXgsmSEnLZUQYYd3MpMMf0hClLIsDWGsIQfzk2qceTlyJhND2yqeZQVNMjG+jZcztai8MorKwcETDvzPiFAMoxnMdLmTwb1UGoqpHz3DFgfKp28pA1HAPDdL075rtyrylbLB7uTs+JAXPAzHo9nB0fj6246Pj09n84ceeuc73vf+p//gD1EbRpyGF13DRGUV/C7DHVuAnsvPQ3UkfUCL0U/4uNwxWvZ3msn1Znht3dtvxtd/6Gf/6Vdenk7711jJOnzhoDk7m7KzxAX1M4DJFXSXXMAsesztC26/YqLHpnZiuAQRMiapY23wBEvioBppBV6iPhnmjZeQ7IgYiMGkK0hMsqE7ISORWVfBwhGFZG2zcnLk5lLO5VlcchTe5HZhfhP9backUhugrROsoiLQeeMVW6vJKYhQa21aAgbSmrTlyoE4skCkeLROMGTTHOWjmZpgiSkUNmBFW1xkLiYpARk2qGoaSRXPtio9rCqSBoUnFxoqMggcnAYA6iwX5IfM/GbzLxwIxReSVIPxyMTiBpGptiChmqatNfGkQCCNiWHp8ChHjy39K86hKo+JzAqVPk8dyW7bURcKME9XW8Ss08R13Ci1bbVIVaV7CkHkT57AIcKTQDxRVl/0qibQgbNwb06xWNvf3uIdDEy2fZ7GmjPGIK7+KohTz4fw6ndmjgwtq95wss3u9t393aPnn752z9XZ0c39XV4YMHz25tG8v/Pej/3gcy/dam4dTHaGfOOAzYuRAQkvwx1agB6iL6I9KCLGQq/RZXyJmb1v9EC/Ge81LFrxwtcb7/jEj//0k2fD6eDaycl8enyKIu1f2Z0eHzS8hmENXKFI7njwazdLHnJmsyg7sHSdXLrCQXBiGAQRm9AHNCNoos5gR1qAE0ZdsCh/zQGTqvoQVH7yepRG40+lyGK8YFdk0KMrNSaWjVhEJSePLMrRUzD1M6BTCy+xPj0aJ0AtR8WAk1ZMxZNdhlpTm1dnQ7Fk2Jnopiwh1UyE4uMJUEVkB3aR2dpBUEUUJfWqahJJTN0Z1NHxbr4OI2tbMOeSkBLkAAHx7RpWlZqipXaXRLmdtr+u8EYsH1PPjljFCsfUOi0C15IsbVKARsZQZTGrAyxiqAXtBH0ESk7O+Stb2bRRcG9b0OZWMbpQ/Lmy2qmYdSxcUKuUS5WpBpWGU5jAoZM2+/jL0UMJVSx+1ZbmUsTK3h1TdlJIsjUjqzmcEZLQa0Y7dAeThfWcu912DLH494gmSxSAmnnknh+QBqb1l+enk73d48NbN+65enhwky1l7Gs752vS453T+dbp+fzxD314+563vfD0s6vTE98BoKZai4u/GIylVayC3j6L2BZcUfrxBcactKFSbl938W/+3xLbeuF123itSBVfcUSR3tKkEnSHrUwHBQma6f/P3Lk0WXJc9/1232f37emZAQYcAAQggAIpvkSCb1CkRdFWWJLtsKWwLEXQkuWQNpQXDoUcdmjhj+Ctv4KXXvsLOLSwF7LCpiXRFElIIAgMMI9+3fe9/v3+J+t2E/aeyLlTnZV58rzy5KmTWVlVy9Xh6Phw+tRuM+mNP3T7C9985Uu//Gh7crY9Xu6GV08ubx3xybbN2Rt/fcCFgRv5PN7M+NdV8YQg72Vn3YrJIFNCByRuzLfBxK1oJzoXDmYyc3RCxzKG1gMHmkYZTboeu8F27IGUlzvQN9HIh3PTvzYXRsOxVVlQLN3xpA5CHROCgCXFTBFqAAZxmDe14Q2zcYpn2y5RpR3XWnPalhMBXrLOc0gwX0Sk68C/HvuW40pINAQOiILmlCrwVJRaL1OgMKB6g0qUYO2gxecA76aKGw5LcklFRYd1OOBrCI0hqDlbd9vo5vjo2LiFFjhdNaf/pgaKsuJT3M5x/EUYkIAOV8Yr/tZ8+4yHS/i2FXXhG3okTpQIQUQMVR0M5VmrJCZyMwvfIQW/UhN7sECNS1Wb3HNxYkU5aNgZQjPDQbaAjYfsC68lfKfKGcyoEDpAil17MbFhgYbgoZWorOYv8zMjSynmksXcEO5kBlrhxAJ+aiHdARkCOrA6JbRIWgGRlvsPnDWIhd3tqI2m7KOTICJjl7mvJA95f26eEmMTPFIzG4Fz5ozyt3bTymrObqzBxXx9ev/l+5/4yoPv/rB3OJ+eDlfz1fHdp3F2rKUomfcPeQDOO4pIES7pdvUdLiDNi3HIshMJbyV8ei46Rdga9YFXDR+gxEY7xHJxhp3ovoU6bgt+2T/FXoR8XQ3H79UI8RCSqkl/4PchB2On5wcHx9OjlV8D7Y9P7+0m97az8Rd/748HL7z2/cWtJwe3l5dLHw/cbWfzq9X8ws+kruZsauf1Mju+2TXnqZwZX/DG2DE3bgVO2B+UrQzYDhT1OZgKH6GgB/UF2rDxCmaw9H1BBmJOHr0MYyQOHQyLbmNklqvCr2lDufzTMC+rAcKetDMSLoHR/SzxKOwzqKiNesYPCw9cnv3CZTDgnTRa2i2pzUIHnkGu0hpz9yLqEI43oZCMlNiWwQhxIZu2hoTKu9vk06I019mBkIOWoxOkKdLZvBJNlI8ShfY5cP7iYIiLaOVOfaTRq+qpLMkzhsv5HFbcPABmh7aY3QQPe86TeP+cUSFV6HnFC8d5g1/Ri5sQJ0TL9RBJkcKnIACQur/lthS7EtxTi4jwB0MeKbn5IgcQebWh33JEWuVXBaUIj1THq5cuauwY4cEGtfaXiZYeoy+kzJ3jKrcUxXlsfNl5OjmJmMSmvqRVxK0m0c1UKR+EQoustDr2glsywZSMedgIWxxUKlp2pkA7b/41R0gng1tXUs7TYnc+0IK9i2ElwlitCuUfY8Eu2RoxGF7Olherg5N7L05fevnJj99YnT3pnd5dnV24OYuAgS5m+2J5W+ViXZ+XG8WlNk3BDXbkqA4tbU6t+Gs5xVFJDpwPUoJf3JQzE7agFYOoDZfMgrY9SLFJ5ZKrnW9HR9MFtyfS07w4l30MB5OT3tHd9XKynY3+yb//D995a748euaM9zLwhPNsdog/czsoT9tw5SOYYt43H/C0zYoVd16b4S5QF6HoWedcdIozQeeX3j2scEP+DDK8JhFZ03mUGwtjVjKXQ8wQm6jNU7CrheUgiALZkny6TS+MLXHq0NOhCFElYkwDNBBrBwziUYYY4ErdYMpdd4qHJvDTVrhDSNSQMM9aWHEJlLglSmCAgMjZ0UIgTvV3wNrKNh49ARTXyBZuqENXfkyWrlZHx8fyHz0ULL6FGooqUVv6qdOGvA1ORxnAHLPSUoRlxiLa4WjRTYdKbshzTKpTsrCV4RpcANCQIlkEb1wVeTWSKmrRAMmAJe7TBrE6gWooR6TwHZfR5JM2r1QurQVWDDap9rAHsykLz+Fc5CRLOecHUPEvjMYR2ipXziIuIJTG9u3p9L8ZxA9TZuguGmIlxaFYjbRAHfytVSyRklAGviEVjbr03EP2FWKDtFKfQS8G9q2c3GIrQyJZ3lnq5482q/X4+OTeRz4xvvczF2/8iB2QB5uL26PN4XKRDUa4SYI3P5XBJVuWKpBsRMCKIFgefGJMaqJjgseYCE0ILY5yhAkgPyCJu628GASNw24fT8C+8nq4xi7gThzzsrh+ImpMmct2f3J8Nrs6HnHze308OlguF7vDcW/8dO/Oz/ZufeRz//LffffB+sns4NGDx9Phoc8Grpa+tNe4mCgJT0QGRS6JgLJQ5XZQqBvFuFnFSaLeqlLCFkzHgT2f291uNPfKjYaxJecHRDQah71uImNHczSEN8Ogy7jLMVV0jANCsgJ4l60iLHtPY7LQvzHt4NSAnQZIIpfkw2wjyLllLSWGYJjr0UCVRJUuxuHczFzVOiYcvu6nQYTGTxiOf2AiJhv8bA9IJ2N4c89Ow+Agoo4xztTPWC9prxCdfI2tqsjRxklUho2M4oCx6Ty4c1JYCqIGFa1u4DF7zZl8yIpuDk8Zx1Q6qCZUkRInWwAqqHN0VJZU4SnAUum6VEhgU54rgCPbnbIpN1+1nJKzGWUUeYHz6uF5x7Y0u7xVVQuKCEm/pEStdE0kIie2klbHV+UtJ6C2tthtyLtawEWFvapV8IJDqbU0nAVCxdTk0SbSwrw41VyozRFwJvYYCu+Q7TPLZm/X8JgXPFwQaW0md57bHB5//hvffONP/2tvMlicP8Tki30NVYbBZuJvY5NsqROaxiqcAygA3MQBE7QT6I11c22NTDQ/9YTeqmPg03UD5PHX8WX/IZl3YVEZPgtVGpRuN0eT4dWCfSLb6d3nd7ee3x7c/cg3f/O5L//KO1ejJwtmzyMWFPrzGSGW3spFAfdh2loE+WwEb2XgwUOpMRapSrisCTlQo94omwm2syjuheSz3hke9SwLysUkfUQsqpbpdEp3WtaYwriPSEWn2C9lHlqFTXL7KJOMzuwCq5l45cmJTbSzdDlF2hoty60UOFXoqpzavtW+KlYnXapkzYRGfSgyCVrFlYZt3KQeqkraXeIxQiGDgFryBe8bk/XLKo0SkSfDHLCQhGDcXqqqobLLdkvk3YdFHYmyyhhe8ejBYklrCslXOfNEEmV1yhGlRH4hCq+XAtee6rXLco0Wy6OFRfoTSX0oqRbhqlXE8NIhaxCgVN0imzmw8xdWIlLpskZ5PAvw4VMYgOh79C2iwnctreUABBsMK6Y4CTekUFTTX0oNNu1fCoWBDKfVZ+GzlaeWclOAm6sSN6zTBOxiDKHYEYUBLzTWkepPHVPNssvh4Wgy2fCFy63rgwQL46Ppuz8+H956mpX4V7/y1be+99e9W6eM5CV34rFFF3V85LCI8cwcGyWcm1gSoiCuHwSxTOlop/FWLMD4zNiu57ep5egDkegAxMKM9prJmOWCnU6GYaqVIy4YF8N8jVXQS9b4nnpuyYL64VPb3r0v/Ys/mo3u/+jxmjdUcy+ET0ku332PGGpxcc74ymYFoyq8la9byI+Yi2kYDkGcOCmneKiF4BUT9lFnO1TjlDsm70ZTrKzGRlGod7t4rXtFLmWfqrwFMhkvnNPazoqxecL/GHOcI+Vl20iPIbqrSzkdU0Ztmi1HxpNgNUsNdfEgE+X1Cx2Au25Vkxi/uEhgcyINLpOWGiTi9MQHYZvqaxw6JIxQFKFcQMSgGT+IOELCF2hCwAPM4JjkPE62yuWc8qxwURKylGl75MHNEWdBqiqOVBFH654KBUfgOKaZ/JBu1lJFKzlKKkuxIzoV1AIWtxnBAIg8dbrgFDBSCdJnitdxWawUHmjbfwXXRO5OVX1cQwDIg1sQToufYogKtSMOOz1/O+pl3TYt0STdGBNFYEUY3DltzqiwlDa0KiD2wHFDYSG81KmYgQIHORxsGMl5GWWRtYAfS/a6Ts1XeGDZKYomvETbFoNcbed84nDMrUOWFs6v5lfr7Uc+/+UPvfLRB9/5y97Jre38iiFSkZL27Y/RxlxPc2+sli44kascJYcgXpuZvTCl8RMvHyCHlf7a94tiwDp+waMaV8cW+VNoxeJZgKdf/Oj5we3d5vTgE3/nE7/2rXeXR7zTar4e3L7zNGv1s/feferpu7Pzy+NjNpFe+cVTX3bsdtBMCckw72PpiuCCN8bQKXgQFp58zYOPN+O/LMRQoZpNdUwnYxrOHF1e07/EkhndmQSVCNW/YTXmAfcVQ0UwsMVIEsRZkpQBbK6MKRlOmn0Dm0jnBh6thwSHGpKjqRvFNLIE9q6NX2aiyCCUhUIOUMpHfF4ziXIKxIBEW174580xhA68kVE15AJJy4RZxgSA4ArwA7i3eJW2U9Sm/E/QIOakUA7zWZIPWcXvasnm1jp/UqdXI5FnyYRND/tTKFUKW3UV0RcivakubmGImTMekYtN3tcFpIwiVR2VmFTnxvIJoEEQaVMre9JtHSyzmoU9HbatUUc5sbJZtKUYLGBcXlAUnwIIWhtaEvjqDtpYGLb0+ntPQQmIixk0DXbqQg1UqUqAJRYx+CdHD4LpwRw0rtFh2KES5wVfWI+11USuOY3UoKQR0FbV0RLGy5pH2r3Ly5eNfN0DGyBYW19MuWW1mk1Obz+6Wj3Zjq4Opi9/5Zfe+8sf+PUE72ItuLjCTC6vysK+Lx0SGNtwlsXrpFjI5io2OytZEvKxbZn7wCQjKNhzJSjBFMIRHZDVOVf3IAIyIifScBOpN7pzuTjajZ/9wu/928Fzn3pncfwu29d6/Um/f/69/7PdzE9Pjh+98zaKXS7mu13ew+ejeWRYxuKY113hdxJw6aqyj0FtcvNL1bZgR6MDsVcU1KaDyL2/vAU0PYpFYQb0m5ZV/WsXGx8lZNvPqjRIypTNhXdwskNdH6jN0MQY2eRMQIvl6GKZfQmwUXJu/BZQEfKYa7/uScwMWFHFCgtQAw9dBGRCLbmE5zGR5h8VwH2zAiK7BxASFiWLLNSHn5TjPfKZvgxTpVRFJRtAMlDuTEdWCQsHpvJ7w6uSNDcYpLbhwZ7Z1lDnFDnlq+/FE4Z5l0XxKhUKGt8oi6x7nmTGt1Iw0pjuZQOE28QVJyhkmP85gyLtqqSUqGRJ6A0eyNIIHdhUPXK180oFKrGBpBBVUXrCAnuarg189XQRty9MBW5zTtDC/o4krYiYJKQbJaNO4rvDKu3S3IOdnBRLahxGoTZn5BTmWAvNQCOgDAe/TSloR6/PuQILodVW32l/683hmKXjEbdY3CDCloQBy+uz1eKKHSvnT84OpreGJ3dWvdF8ffjhT3/x0cOz3m7UW/r6H+J1UDF5YUsX5o85Ez0hmDFUNNgkkPnSMAUb9mCwjE03RroPxAHmmJDETxVbXg/4yZz9VeNcKSIYzyUPVv2ntgf3endf/tyv//6D9fThYnTBk+ODo93VjBsXp6fT+fnj+cUTpkQ+WHPA5I61qnxTvhawfOyGVS1uq2OvTjB1DRB3yYYxinLzCQsvgfQZ2kJpOBItTC1rgVxj0uN4t4zP2F30qRmku21R9kDn6Bowsy5lgT++hhKa8SoijUcyXjZNILHEIncEEKn4FUJ8jt2r5XmhrVEABC+ICx6aZCFM5sjHTrVnjN8gI2vEAlov/vxYg2smmhoODE9ea7OczStksZiUlXgDBV4EqBtzC5TzYmsinZYITh0W4LQlshFDpmKdVypMDcATR4SJXMH7ehmbRUKOlFKHx6FzCpQjGtm3OeJDobnCgMRW2QMBBu4f04n4YkrcCYYiQIUuUJY9DSx9qTLAL072j1AOfLgp7VDB+3eAjCBljopMuVNXF9dkHCnoI/6D1LgmZpzAJjPzdJss+8u9RVdVieQlbHNcSNjz7RwaARyyiyn70bA2uUwHo0r4rSGsJRAtEna6UR25+jzS5JUrPYxIJCUjcONVQe5lA4prg4QQHCq1ahBDxMb4OQyMQHVzUYtxFkn2Y3NcrPJ1aNsCDVHdqX6FPaU8Fb1dzhc83rPdDBbr/jM/8+mPfekbb/2P7/ZOn+G9prv+djpc7pZrtjdgj9Mxi1m8tEbBeK/myk1AbBfIvTXLuEpHAvvUzAck0Z1jGE6XMKIGx3wQkE+moQUeF8ecli66EGv1jza7Uf/4mc3BM73pqx/71d999cu/8qMn64sZj+PwYhhW+bjg6X0WfDSQud5ucbiZ86jgYHvFcrvRJQhrYsh2qt6GEe6XJni8GeURYHj9ZvcThoft+FgiL2/wi4T2iq8248LgwGbTkHYaz8FVA/vAYnwfr17PPsyQYTQLz5u20HVcD1aCPWD1zGx0iJARlHrmoXUFYbFZ91Tm4UiL4Tnay6nFcvSwsZx9L8IpiBzqMI8lgxcuUAe4RGbSRvmoNQ8bOe50JHAI69rArjeejIt2945MfERFISzwKSFQXHZpmmDL/UyWcH0djSoPCZWQSMrewuz6fVwejo+8b3tFamJ7XpjFC+N4fc9qxSWZEgAcQWGUI1UkF91hcn8OdvKmOCz+FhzHqvLeJPduk65hfR2E7gPPVE38k3Tz7h7ILEPQ1hxoc+VBlL7TfkFShWz6NpG7vkZKi2YVsmTX7qlGy6HSxIgTEAZcdnMWGGUgkGFHHdLxvOlUPIUq3dCJnOYlTXob/GosY4U8reoXkD0vVOinsT+vi8EMG6XWOMzOAt1epP+KKclRGihWHDyuxHb6vSw/ct9DATfswGZndvaVMQEfXa76B6M7L3zx9Qd/+d3e0ah3/t6StzhhB0qFyfIx6j6GhQtgnnl8dGtJhQ9sBrvuWMHBW/yXtD/1I/zxiZTp0dFi05tvMeVsx/Nzp+4tmB5xjwGl8Fnm04PbL24ux71nf/4zv/Ht3p1X3jlfnV9t3BS9Wq/YF6qvYRzyc+p3uFnwabXh7oqPc6NJCtFPXnnMgHfMs+mRgSM8EQGTLdUSS/NawiZSO4MfPYbpMIK1FF6eFSVyinkArzLJ5ClCrSQplmOtujUkAqop3WEIdTs95FLR1cbGLDeeSDeJrqttGAqZhXEKmnzQey4wFpfLoefXqUAQk7HWxhfX4SSYobz8Aw0kKZO2NQLocOSCK4ckRmbgDUQCbkhlniFmEgoAEm4UZwJ1jvgmCMIACaVwCoDQ8bZA0iqnTJk7h0UDiqgozmpIF1Adq7wkKQcZT6vbTtjiIIdrDrQliYiW0SJoxYz7J+5goYsoLI+V2sLRixheBtVoyQ2kqGye2bnlMCgtS51q0bOS4yQOV3+WR6bT0Jok4Uni4edWeHFKsbVmxAKKwzKyC35DrtABtvEgFviXPm6EpgnsPYUV0VvbJctyBzLXNO3PORlMglgdAwzrWciAMNe9iI3ugwX86JV1EGlfy5IR4ul4YvFm2eeDVAw8Lh6ssRAi8Exv//hvf/Tg537hq5/+3Gd/+L//58HJZMPL/6ZHLGy5w595Toxt3B8ul4xFQkWMg6ucYZudlqEi8g9MQrWob7Zez2B1MO71R2zmH/F6ntXiFgNpsT0ajw6Onl7v7vRGz33kN/9w9OrXlscvvPVo+ejJpdMR/ND8Aj83ZMEXh2IMxfrUbLe5OuS3nfFaK2Rl4Ph5LvMMEmYzfrALdVUfmbF3PXpjgvf2wZajNQ8zYNZ+35hy+pFVNgDjqjIqNXoHnj2ZCUdb/KKLdRBYLG3i3TI6pGgXu2ZXeSknLwatrmwwcZPAsU+NUD0FRrCYnA3sdI+pgWKSI79m2TQLAgzagIPkaVyD+TTLGO8w62lhDOGd44DHEJ2czxo4ECj3BLSg7pIWr80bteESRZEUsIiffeaUVQn+C0hOOSpM9ENVmhO/sJobUM7BS74gaiAWCukpiBhxgZwSswHvXVtLurVPTkioI7GMrUAY70hjf45ckt7UODnNgbaVAP6tyLMoxsnAkuVGYaZskoAVS9WQkLY1ADNgDKt1VG0aT5pRFHREx7S0OT9oQz2YYwlUFHRrs2+aTDujXdoa/rlPPdGfdQqudyV1lzZVihuVEdaW4AWribfS6emzVLd8UkXWKiv437q2DLEWayTMl+1ZXDco4LYC76zR4pn+eY3gM8Wb41vT2exqNrv41Je/zNuWe/PV5vROb7bAxLjtyIfCy5qY3jAJjMOSp/rFduXjWtifdg5WxkfjGRN31mGOT1RMXodNaImq6Ler7WS5udWbvviJ3/72w8H9J4d3Hp0xpeAD2kxI+svZBVM1p1+4LeZ3+D0W1NdX+CwzLA5ySVHlJEIbbIWrJt6HsNwrSsIZh7d0Vb6PNflYjErS8ulotynRHS4XanvGq44yk010Metm4UZ5+ClNIpGU1oIIDDcHAsCaAU3ieqoTQjR4OG9uyObpIzIkHoSIARe57ghzTbBEc4XN4djawue+bxPIy7IlIihoMrAWZjpQG1srAEGQ2BxMGXliNmnvpIwDM0mUE1Apb421zifiC4AGBZlyO0DisILH2dX74GlvhFUsiix9U6fQrMz+SIakEInWOBIl0YSZJk0NfivJYpSvCHQ6qy6uK5KVj8Y0earRd85L2gQgbSN8IbCS1moERoMsXRLEIMhCWErA4OQRXaLi0l340BkWLTImGAq1xk9xIW+YHZDWAU+zdC+n3pGlXeCp4dfww1P4sox/2KLCIGCpiUaeG2oBkcV1vUvhET64oFLGo7uqQjoBaSGCrVkCD+DwmihLYtPX4/8MC1kjRLc0Zj843yJenD/mo1Xs3no833zoY5//5Dd+9W/+9L8PXnh5O+ORCefyLEnMV8tbJ9MZGx01FYdXJEiUlaKUSOenn3gGmSs2CxluKOORPeZrxFr9yfjOpnc8P7yzPX7hC7/++/df/4dvraZn/VPeZsVNn97iigWm1Wq2XSx4HhPNrC6f9HeL/nrOhyR4oRXaw5WwlklX8vxATIJucLmKCyzqxJTQFXpAs/qv9K/61nyyHq8742rBuXuyMLVM77IA4ROMdJTAlAOmzQPv4PeCDcL0dbsEYy36NYHpZxqVYaj70KW22Ry1jZnWMcRuXuDlQgPeez2pgDP2osHAhbgKD/ZMQRlSu2thVUAEDljjgXxGAqzKixoAJG25UHPVY+ULywaMVEzhB0DOOKhUCPEVAIeoDgTgfS2bosmXw4K4qsqaF2COpth7AXNMFabQta8iaAiBiI17ObEgicmgtTk1lg6jYC/P2hgJAFUkPaJf1mnf11KVBuFoMwO7wwxkUcmtA/DZu00HYYOJJDCWypo/vYGOOVCENmFJPIarpWeAaXCNCL6wPpWib0vDtLKzK1FOakdQ2s8RVs9lE0k3GHBrCLJXzRUbpJpm2FIn1nIGQFiptgqRU3j16e4gVFy1HrdnJrZLBp8VccANIdZxHG+UMC6woLy1hmfEtqvJqM906fLy4snl7HzRW/Zvrw+nn/7aN3/43/6st9j1JkeHo8Hi8px3Qjx8cha0sA9y0TByEZVBG49fuvgAHBGcDkMXXE7WS+7rTKfT+QodTDa3X+yNn/3Kt/71W6tTnmF+8Hg+Pnlq/e47hFO7s3d3C95pRRPW6xa4mIPtYsCyN1NCbwJ6p4VOJUpgfPTmvGim3QfMZJBVFSrpUgIiaNuzGFW5G62LlXUvzwmLHEGUaBXAa7XE712rjLdAahbA2evRafKxK9trG23c2BFWCkvKlVLy5NWCyfI9MhHTBmMTSfA7LoQzdNmnahI8MaqCxbTELDb9sg3aaRyHQB1dMiEqnxlcOPuSqXG+J+UL3kzhijbK59W69m2BBlRgMAr7OgAAQABJREFUYOQCRBUkOVLC0jvABG4cqcVFSF6yET8qBNJ3uqei1CETIJInwVqSgQjDcTIRvpg2BIge2cpgaJqTKuEoqTgsV9SUwGFNQwq5fEGETFNDMnBAbXNATUFyIRaNwK9rwB/zSbBQIjlqYy40ZJzLT1yD/rHuP6aDNXoYiBQ0izAixhFAMrYApsBwPQcSTmW2WYcN8A56xhAVlViCAfYUy/blnbyrqAXLW8D5y5n/g097ct5PD/AvRIu0QDTs2jUj3wNAgEHSS5QBzyiBdSm9f3HCak09Cz0eT/vDk9v3XngyP7iYHT56OPvC1//+8z/3yTf/7M/ZBc8btXjWkABESzESwCyIwBmxG5bZIrkoPzDpYDA5IegeEBzttrcmfcLC1WbQu//RD3/zt+9/47e+O5s+7j+zOjjarLbrh++MD1fDHQ/kLPvDg/EQ37LYXZ359VPCDddMfZYNy7EnlTX9ybOB5SbsR4scYcxfzNWYoVRD9WdiPV4L1kKqy4jLvBVuarFSqU/LJIdNtjVj7AjkNMZcYws2isXWeg0o2ygtuygY2SsL1g7lQcacujZv1RjrxixIoAIBkbdkxtYkIr4uXTus1AZA9lojCcGY0FCMyIkFIERVIiZnaHE9lKS50givFwKVzkRsOybp3O+lVAFpUvcBGdGoGsgMfOmWwyJDCt2GBABKQKjD4g+JalLBmUn2+rRjCBrlC4Ghf6BNQh94DDF2YORN4I0AANOQs0YYFlkHJkGHIrQSpxvXpve1RB5yFI5Or2ua4DosFNN8m0O64HWJOixxXXcWjeOwAJJn2CglUp49X94kjgcMFm1TC1GUslGxi0FzjCdKQNT4t3fxZgThoAYS/NnyV+t6CByFIFFTaCSCPaUwDC9a6CgU7WhE5bjhlrC1laqWcvDx1j8/ETKUloLQVnaLAO8dwFHzodazt9/rT2/j0XhW+Gq54fOtn/zq1/72R+/0xserszO6zRttpIwpbAFEErlxrNOUcdiDUNxxVdDVcn9sDRgvcFQ/8lpba1iQIYTFUFG/nyCBHgBLE8aJj/sh58FwMTxdLvlu4Cc+95vffjT68Lvb0/l2Sui4efdd7pIfzs8OV74ihq2hvAh/zZtheI+V73vdEp055AyvGDJtk2f6F8xxPd4cRJ12cx67cZZXfiFgsStNWavQF2Bm9m06i4b0iOOWqvBNv1PLf+6GCExQvHO1k8ki0TGi0oWBhB0ZQBtQAx+QkuCUgxOxlKakaYQCMHfUgcvUluUIDQAK4GcNKC8gFLSNEUTTuknYP/lKNx2W9EzBX9mcZdDARgviwEJbEeflUZp9nSJJUhaoBXDODauh6zEPP2fzh1sf5ITpNBvUown8FygZJngAHAWUHTKGYM1p1Cnl3M0f07jOReFuCH0eU7/YELRMYd49v+PRZAXZ+XzMd0fmS1rC+uGI/Y26yUpaahjleHXlixxF0bQPL7KL16Okqhy68BtlIaLcZOYof4kbXYeraCIqKJ5ookZwT91L7B1+oQUzzERp3iUHjAxoPWBSLyVs6ZR5GRce+x5J2SQjP8DJSduhBJVgBg8eQXu1Wk45hVzw8LGV/o4+GI/RAHv9AWabG0c+Un84curNrQFOY4qwg4mBHykUAlyUwIEjwpspByM/EO3lmc1yAHjbSy9lYEURzta1lj5vKWfGzT0Q3rkIb6zwDA+GRzzEw5uat9xTG08Xi9XRyXg82J0MF6fD+Xf+y3/qvfm/etu3D5YPx9slDOkkYYoPYXBh5i5YhOXSVkNZrp2aITFA/C8XGbY5K4EcUw7t/BikbD3IPi9LHZNMZQnl8kodi2jnFwGTSaM+r+Pg0zQDRF7OaXIIAl9zpmsdHw1mh6e71SkfDfz8r//Be+tbi+HTjxe7Oduz6TKfqpn7YSF2+XM/dLUgfmRthbFLGOCUkD0KRJH4AnxWlv/srPSvvLEGL9MOVU8rqkr8Yjiwd0x0llXl7GInlsSRlRljEwC7NiI2lGaXEtEu3SxGSAxt7y2GruuxriHqY8SJHlilYDGgj2vl1RGOWO0BX4vHQXli3GhtPu7pigrldAkkJMoVC5vRI4vN/oK+Q6aZqJZmK79Thmuo0MFK76PSSh+qdFg4DOp/m78gz9Y1TgRQFVkdI8dekowgxr7Wzj6Q5XIwzmdfcm8WcHijOfjhmvDq8uIC/qvwZi394rj0xpRelapqZeySVCXqIak/moxwtKoliWqaQSONQaE9AtkasAjK06Mwwc5S5pO8pY9jfeiV13GQApx+lAC1JFXTjXawoX4KJVnAwtmUA5Qck134Vw1hhub0tSl9HN5yyqGWuhHX5jJvhYxgT0HoOcVJ6dYMPIWySVX6N/BCZQi2KnRTeIQHqDUi3wkFQSWhPYwDq6xgQB7MDiAYS9sIVUPD8Z8EOPshoQASL7kQB1p/NeCOBpiwDEcaFRLmHpZkADBqcAAwfrzjxz5VuiocSjErvq5qcR106I4HLHwte4PlbjI8vnty74WXPv7ZB3/xXfZh+gTjZnbKvUVfNtAn7sfbgQcrzuhsXjt80W8QQU2ZTUXNequwXeJ0RwXiUeomomMUZNx8ARvwFvsXFbbztpvdK/Jue3r3zmK+cD8z44jrwbC/Wg54M8zk1V/4+N/751fjlx6uTt59wJccJ37Odnl1sLo4ZLPCiht/vBlm46e3fVeMLwjD+RJxoATGNsdMexnZ+Dn0qP8i3rDHVKuiVayakkTK9hycy6hCkKenBQYyJg1aT+weQDR1iFZfIQrwNqWQBANSibrioYAzFQI9I9cmYIzDhAdQqiSZ5bRd9C2CkPDJ4FKEyWmDTwNGpWwB0027yIoofMp4iNsWW0KcWvQCBciLz0LHaQ1euS3PIAF4wM7RGh6Q8YkNAqULWfK0kxyLPglIAg5GcQ3kqqJWVri/YVQAJk8pxE9VQ06redyScRYlwPHshzu8E3kJADSlpGovyrhJdWQL8HJp77P2SYjErvT1ajn08RF7g5aND7uvJZqTo5wEWo4gEls45jS1QAgEgIMFVukOFB1+ChGTXWH4LyZTldtMBbcEhaKifYR0+qbrbZRIOSYZtn4CD0MMeJDdQK4HqhDCzlZEyShdHIyQ5XqoolSP5U0puS9+nLqaDdoUBYMGQZlthVf7GopcqeeMZeuzKoefcmFew3WtRKhYlX/yA4sl/BepzeWAf0xzWG8+O50SeVzwoByPU1xezIeDk/7o9BOvf/OHf/EGW/Y2B6PDk9P5gpkUQZCbBQgGCZmxTVBQQk+w84lLOds065WeTQZoufY/TjFlCuWPcIJrLm/sZIdYvvzA50p9viTN/Buu2aCxORive2PedMnaJE7tZDraLNmLTsiD4EP8yfjuy5vhh3vPfeFrv/GvtievzHr33n60vjhfnT51b3l+xntBDxbnvh2U1xnzBXlWbVe8O9SoClmiA2IKNlh5HzB+X3bVEHqDCcRjd4h7qfe9BWfRJgdiMRIa1WjjztRwyZgy+ifhvzFCZCO2yIIoJCAe74bL9YqFvePvOioF7YU7JZanNpZClJXREULyAlEtv41khw7eSt/efoW5Qy7PyoilaF2akwBxu6mwGmBC8bhATzFcZbQVVbFAqJsCa77GFEAFaXletIBzVTtujtV/uVMffBnmZrrQB56LfwrlPwlStKJxuqCFjTg1KsvB0TwwHkAejwdstnLV+KOouCy85OEQaJwcJZygBdhnAQVIHBaF1AIDo81Ppg0jh3JqC6COqfFQXVGnASnlRBkM0RDiEEU79A0garImzuh1r0pK/Fc93/AgG8mlioCFRMaKjWHNjrSq06YsdZiLn/0ReNaqtNb2o3foZ7Vkk+AnY56Ev/AxkT4zGQzCbmPs2j1sluEJGeslXKjMNU7swtJWO9qOEq49uiF4YA6oLXkD0f0M6lxUIKYOFqmwWixUxEAzj/BD0cuzAXcA12vuHvNoIpa/2h5eLLcPr9Yf+eLXf/bzX33zez9YPn7cv3Nnt7w6Ob214J1bhtvOL6EhtrBT3Qb2/HKQNTwYbw+EOnm46lRVBbShP/eBFY0YwHFcPrrsHD/8Ow9enxwPZpc81gcWyk+GvMRq/MxmdevFb/7Os5/55XcuJxfr6eMZq7XHk/HxOXcDV1eHbOVfnRNe8fSNm6oy3eMJpLylWmfNQKI8rgdpsu+vYseYFWMuPKO5XCpc8KCT4guUHV7UgB0Wo5N7zF9JLcTGbClaVZ+BYg9bTkVMgsI4LOHsoIbIWj3adaoqL7bBCXCUTxPxWOsqtWsPsrpHFU6Kw7DZDuINjfCKHcJE50Rgj9LO9dggSvDRomrmkR4PPLWSK2sLaDCHh0RDbAohscoIGC6JcWrAFadTTmN/Kp54K2W49lnXDsvtc0179Jh73xt1GWoywhU395wChCsAWgKi6AGZWokBTeJtskhL0I6g68WS2amGwuq7E3Y7WVXZGQ4xfnX3UAJdykhIAYX5tTo6GsvAYCFj1zIQ0oU07CQEbX7SqbaOWIdK/lgGgFKAOuahiwneNKEVNSChkpReoYmtMBFB9mDWU84KWbWoSloIQs01uK2T6Frgef7TsaEIAGt5OCzvSwQDB2YlxZWc0EaqFCA29wo8U9cOAwjjqaVEBMLYY7rBJIa1j7InMUZDtvbEtpHOC4ytuLrjLtiThHvYLOZjrGDEx9l3u9FkNji62PaXg6NXvvD6I556efCIhaPl1Xx0eosIJdfwldvBaG8kgpUP8vxerUzJX6It+GWtExeDULBgLKD7KinCVOTpclbgsoAnA6vwyZLZChXz8ijuP693/cmdF1bD+9vtnd70lS9/64+vpq/8+HK07POY93Tx+GJ0dHzx5g9O7xztZg8H2/NDPsbFvip9U2ZGUHZl3ahKDaA6HIpBHVpgQJb/YjWJjIpFbS5YBlJvxc/ONhErcW6JLqw6yumevRD5FAD3ZwfRKrN17UCcZTAW2oAW4Cnfp5a0tnS7tQYAoQtJGgJtffNuwHKqa7Sb6YWsZxkumYLbCK4yOTbmQUGTQIUfQUyUMOUsET0Xp7MtElFNSooNsxQSKXRMha8EDwF3rxlvEPEJRLWHFLLJ3E/xE3iiGbgpNnRR3RDWd4f7sLfjWUKiJpuEZxxc5WWpS0VRfliA4mPCyXkSPMCbOgIKebMcF0fCrbIqz/o8Dos8bDHaqmEBc0wh97MwaGUoeqAlY68HnirrkirD2g2cUpAqJRE+GvHYUlMjJczVAxz4YAZ+D6f6gyiHJot4sFJVa7GS7pXYpniNKyEZfiimUJYFyQ7/bUtFjteYGeLWwlOiURvmAoflB5oKgIW/RhB4/BVjp/FOiSmBFm7MewIqzStjpslOPRxpdBMt8Cj69jDJyMwQggYrDLI5gP8J7/+bXflIy3K2WMzxK0dPPTN78PD8YHQ2Wz3/3Auf/tLX3vhz3qt1F7/m8Na1EXuv/XaiygAProrlNu5dulYeGbRmTjnigWyFR1CyGwkeffkyq0b8wMBl0+tSNWfNXK+n29Xprfsnm810dfJCb/DcF//ZH97+2Nfenk8erYbz7Wjx3iM+MTs5nlw9eoet/svLB/0tm9fZBTrb8TrjeHc0wTU06+s6LDQVT+T+WOMWHBZD3Yurrl/Go2OEhF2UCET6pC5l1DIO49cAtoNyJK+ns38xHNrEcpA6Sw3ABxHdYXBXequOFx7dNFq0bbMZOxxa3c8mzQaYkscXaTDE0AQQghb1ggdjurj4b8euar+NQMeBlQQzQ1K+awzSACGVqHkcWKKeVKj0xaw9VUADTMBlFVTYNjdotHBX8b3QxixxWNKK66GQBDCck5Qi2G3eJcTGXSFVFRYAzTkl1WnBVglHB4MChJ99gyIAKMgBSsYm4BqMMDvjKRLwJXyQWl/w5AqVADhgjIOfrfOfarkXK3/TViqccPCLuElA08G5bne1aWClpY0WjKh0T8FubziWUWUIWmIy2qLUrBkgzGhA2qXFJlkBFgxdZFe6UzsRIWgkgd0wC9PoG08NHzgkopujNisaNMS0YxPNTUpVGH9ugw4PmBQSd/xooygP5YCQLtIJYqyUCFyXcS7g9ho2wzhRoAxI8lE4RV7/ORvthkc0xiFMeaXy7IybbqwoLdgK8NyHN1ezk7v3zy4WV4veZ3/x107vv/DgB9+XTR9xZ/V6QWdzwTmaTNgn73d5DrhFg8+CA+5SSZ7OiCBsFokIKVIyPJSrXqxwOQ8lEOMLaFExal4PdmvqOFdPbmcfrYe8Fubp3jOfeOnv/NP7X/jVq/Hz33v78mBy++LqnI3qx6dHiydvb5ZPDvmg4PoxL2Pfbc+2W95ZyFNH7OTwKi8bBE3OAZkhxjERZ6kcHCtPC/Kcc/pRSLRFTATltlv92hF4wdG+uHBG1cBGTGUu94SEDvKYj0oGIiFzug8Yo60GKRkN0hc8gFMILar0FsyMbtXWXEYpz3spMJaBQUlWiFwZgakYKEXOaTKscJSi8NTfdcLvua8b6hoVAlOQURiWYKNsPQA2rwGJRuRQliIabwIZcXutjAqGtTKsmtiKG4Oqr1ucMmpp6GUD5PgHjngSmyTcq5JisQSBczC6/pAl/IInTybG77HgyZB0OrIm976FilOqoU0oyGmQcjBRLhz3JNjqwy3MLLTjxWezWU1TaZV6ZSCRL0o8LU8eYpzaa+iNAw4lMFFmw2wJvDI8I2rIhu/OMRdCmUmd+DqSZKJN+cQJk/IqNXgQRtK2ivAYDieR30KTJfkr3sALYEnxV1Cy0dRneXQVxLYiBd4CcGPCOW1oUUob2IQ98lO1WtKYh5nTFux6CpOLDoDJCl7Cp2T9UiHRAUW6BfnV4GyQTHVOZ/dWsXrlIMT0x9NDniJ88hALOxr1L84end46nV3OdqPpZrHiCcP5kzNWtXaHo4cXi9HxrZ997XPr0eTyyVXvas7lzyeNWd7wqXpMpTblywTG6QCSF8ThlIUvjvyr/acYEiEVfirqdplNQ8+QWxpL2Se2ZNF90T/d9Z/p3Xq598qXXvsHv3cxfOZ8M33zPZzU0xfnj3tLvonN8tqjPrv1l5fb+eP+4XK9uuArgbxH3RlNG13xA4jse/jyIQlXlzjlaAhmvjyFGwgigp1roUbkwM5PWZTIElyX6tVoZdaOc/i1ZE/oDqjFYLVwXZunCpb/FPq2eACCxK6XokaC09HggdTdpCSWg2MKIe25MaYIXNgc9iRg46FsopVqWjdSkFBDpGyIRLKkrboyMMEgG2ndzJlTBRQf/AED70pBWdbO2nCmKGCMT4Y8PKg2FrJrAugHUxx34S4qxccS3OEWWDzNnb0gKAtHhBDyGsybZ1y9MlJz7052bIRJxQ9YZaq5G7tJR5NjFtGht5jPWdWiZdFAFvKkkoeMLtHAihhP10iY5c6+LhTknUVKwjpXv390xHsC2AHvjiff5lVKR3WlPnyib8wxIKQIdh2l3JauZ6MwBumoA3RI88nRGHIYEuqHBRQBA5PJ2AVp1Bz+jEpszlV2xQYkRLMGCF7WZYCtGfIfvIBDC8YgAR7HtmOqlCEFgCXDzqq82IwaLUPbggHCUjASIsC7Fx/6t1iFCHczkZbekMkYgMx5K0ocdYQZel26fA/HRQSAwSEzcJO43KaAc4p26VH6iDyQDAsHnsZO4EACEvtgZGpssGR3QsqdRD7jIHvLyywccdtwMxkdswcgr/YbCY5NM5/jNeaM7IOD2WZ3uR6MTu599qu/9MYbb7MB3nhXi9wYHfVW08lwsbqUEHoGMwEfH1Fk6IZd1mETExNPOL4cJfgmY63NUG7mg96KV0jwvb7TOydXq/5yd7odPt87/Vjv6JXXvvXH4w+/9s5icr4ezVZoZb0lGDxcHKye9Jb8LnerKz4RyKw2L6KCdsSPV9eNIL5DHT2gK2emcK1/qcWs8lx0ApyzuuwKI32LQ2JE0cSIKTakch2p9Kz3lGJYwOcWmMqmW5EMKuChp/hvM7oqr7KyD2M2gprc4kQ9pp9N9tVKrcC8JiNDAIkG68MgeaUEHMCcvQiymmLbz7zNGaZ48UZeLGGn2Db7qiQE/5ZpJOoC9th7xKIgalmt+yNkxWPzZk1WneivLCDgi8M7rWkIS0qbGzs1PiCnWrS6MOkp6oYM4uTNMMrAM/iMKrZl6aoYodm/qf6QzhgocQ9+gHwdFUwX78M3w/EIm+T5Vlpxyi1iBKEhtQVGHs+ggFCvUGRy5KM2kIaLOE5X+8lTyBGwalkNyNMOdCRwUZhydU95YeeIl8TrgQcmcJjip7Rr4naF+H4KqSoMwYye2erohrH0o8jhgYT2+cyXkCKiU2TDHK6zFg1RZDFqh+Fs7PNgtgXSkYcXokefaNEVSZgm/pIvN2o+qehqB2kbdaWi8KsceROJKV0fbu3jcC8/Wh9nmBFX2vh+3GsoWy5cTkCSXx3UukjkTRFgEzhk8kRlUguEQ4UCKijXj1cL6t1SKKQsYvHXkYItmBrqBvEh+CjHqiGAIxAcLlixqWHGDoHd8NXXvnT/1U/9+K++vx1M2R9PLa+mXS4vT6fHi5UPu5w8fXc5v1TNN4TQz9uvfBcR817fmh7jw1e8HUF34gLtnFfqjQ/OWX06er537+d6h8/94h/8Se/Fzz3Z3Hq06F8uuGOx3vKaPZzsmnctXHI3kOsPN7H0qI5/BUAhbn8vJ8UlfL3tc43k52thCAbjUJCOjEe6ybgp3U5L+U2/24Wqqn4oSrWrWz0FVOg2QcntTdX38KVTKLYLmIsYK+U6AWz6mwY0iRnQEDNQH1Xon4SZyVQhRA3lOmsRomo5SjwHHQcGDG9CgjFjR86pNxhPIkcqBxSnYLwGNH3QjN8RRyrAGBIYQiUotDmTfwRj0bFmWhlxRUXTCoYgEhVnBW/JvgoF4dgSFlALw+QdsEky4GDUeuMYSk96CYCpxMMAj48rDJRQTupPjvLGUTvLvRJgpLSAKCnVUEKD4gZbcc4GGIyjBa6yXFh9Q+M68Q1XV7vRBUNu3vAF1+xrv+ngUGj6T9zghEoEphQmuGzqa5q6Qh6u8NPgx37qql28dEBpbqtmL8VzbtPCswFL8SD/4kVy6Ef5OZRclGvWKj8W3JWCjRJkuW4AmMyGbhgKQmFaXEQt4qt5BXQ+gLa4klNioIH/ZVSoBMvNwE4sSRql52DKqc4IJP5kjBBSIcg7FpQorW1PLwmjBBmihhsMJ3wWlzsCHcIAIgr6rWRybPMiA1fWdQR2pbOcxeru3XtvPbx6d3YwefbVu59+/d6rr733/bd28+VqNB4f7pazx3wObDzYzi4u+9ywgTC/4jpsMiB5owtGlNG1YJcB127eUTyeDmfcoZyebLYnvXsf7w3uf+iL//ilr//Gm094r/HpxWzNBZb9n/0Vb7C63G3YOMaL9/wiI0z7Q9/YI/QqFPDdMEwpeUhww4VxuFqP2GDK/fVDFtuQiFcbMokGAqXps1BTebr0suwibNMtKhGMMlL+VE/ao2muAdBOi/cLxgmK481UajygvS0Oe5N1NG8a0oTubZ0V1GhG6pVABzBWhPL1oUk6LzijsSwVEpinxxgmdpN3V7z0I054s2GNWdsjMkzEVRH9hRvmOnEWeAekILTnHAh//M9Y0IRcCysOpBumc+oqgJBhStFsyZkMykTxiUHFb1h+Iy+HYY/hzyjmFLBCCxjyGJcJA3FTNQds79qoeB9CN44CiiMDTvp0YhL5tIeENCgnUVjl5AuMquKVuKkgKae2mhBeDXkoOmhhgkQzGsC+3R8SBQxaTcYTSTSiQY6opOVsJqXcjwh6KGA53n0w2c9hUpUBpyMP/tR28/ZCb0u7oB3MkEAq3upKsYCGQ9GSgqmOyYbOPi4DMzA4x5h2+skZR1lV2uXSSElsVMEaC7kGX9MFt60pgB+pqhZzzUa5WpRbTaFGk8AhTRSBDCzYBU6VXUYyA1sUCeQY5YcXW7EDgNFPPOLAdWizoW53sFxcXl72p6fLwfGjq93jDcvh0498/vWTZ59//Jd/VV92xXC59IGMPTdscsF0vS64aAUvLsarSh7PGfM+rt7w+GDETvrL1Wp01Ds47o3u945e7L3wmc/+2u8sj55/spw8eDRf4kl5wGs9O1xf9De+AYaoCp6MxLFM95XGYbHwbHiuJ/L9YoSZBFzY2HaFqxoJx0qBoIaWem0Y0Vvxc8biaTPOqEJ1oEAlr/51+EXz0SrwzrUrqb84vsIDFDpF7iQvPOo3blUq1cYRuB8OYaacgr2dCx6ZKtHYbEPbGyYmZ3sG8FZJjdViI5EIxR3/yRVPblRIQJoQydiCwILpVQ0wCUb0Qiq2UlfHYUeLhtGDImVAyJ8U2sA373hLXauKMhGcKlwViQxDmBLAwFZNUBjTMJggDlv5Ssm2ekVtUazmTPtoS57mpLZxlGtGFUGS0jAAKlgxQNlXkSGBDhiOezBakeCMI1V7MNoLG3DKu04qJKgGLdzon/RzyQiE3s3bB84gJWcACSuZLWqC0E+vlxYtBi7F0RdCAq7xwAE4oncZwDJsWZYR6hxooq2QS3lzInaGHdn5C+r98c/uwwOJ3LGRa35dcbzuFx8ASd7IxYzLWJh0lMAVMldk1w2CRfUJnB9MOuPDIsIPef1xMQdRYGpAdg2UPNXBEgliEyBgtxSvtygFwhX3bN24yQb0xZY1bDYEqFr4d/KUz1BsTtxbMx8eTVfcOGRmf+/+1dn8IV/4O33mo1/+2oOzy9V7Z+te/9ZTTx0fHZ2dX/DIIz3v5gRnvmqE/6gM2pNbU95KtVkNVqM7vcGd3vaWK+v9F77y+3+ymb50tjp+94xhNJiwlc8N608ON+yr4ollXgrqfZ8EUKhLzeiw8FOs5flNBH8Gj7w4AYdrkMg7qhicKxzzkllQp5h4K7pDDKoSTSZcjYpUJPxqlnHxsA0MPY4Ro+26AKbhATcedGVBAgC2yDkZi21uKzL0g96SHi+bsWs5g0+SVJKxNJaJn8ddojMGGf/DIA3FZcOcV1tODNmCQIsDj0ecHVcjg/R0YtyuXGkgvFwgs2bEyRduWGmihtGOF6MtYKSgobUXBjgIeyqFBIf0qNcfajV1mjT2izo1lABZ/ABf5ZzCDcPN8DZ+inLHMvFhtppTWQyQQWouwI2NOJBu2Bpkxdfp7AonR1ChKplDUVQXEBXl0qiG82pQ0IoRr5QqG5LIkwAgDwb4AIZTGao9B/aQ1Dmol5ui2y9dIksVdn9DeE6KDB0OJ4ByRPFk5J+T/x82akASnm1CXvK46jz5mZbVNsyj91AJskLYuCqpQ6LKQzA825kmO01cHZ8ZsulJW4Bf7MIUn5p3eiYqMoZHn1Gy4EkdToZNRlb6CfQOKMypZA/l8I0lZzRiU7nKx5YpgSuna+xSiwU5nADx5+Dxctp6okIxLwWwyJSHORXr4pvDydCXC5ydOYHlOz28qmZ069kXPvLzX/+7P/jeD+fz7dXFgmd6+Iir+ECmOWUYw4gBB8/9boZ3nt2OnurNp73hc73RC7/4rT+afPwX3nyyPRzxLdheIqsNr+jq7Xhr1RW381h2JnjDctQSB42enDsVeNUeX47wCecNS7O4Wpbe2KnAuhir4+xsIOJi2NFY6uli5A0ePQhKRAEOFTGrK1WEIW1XIIHxQJqLa4B/r5NMwUTiBYJM8Di3FpmIKN3/pCXOPR5xmQCk8+x/TYM/WCOJV9+USRQmACXBkNFmTPtyMFdbj0gR6kGltslUw2pgQ7himsz6OmtG2j3r4jo+iIITYFp1SUJh0VpyxSd5ALA4jikUPHDpY7DIQ5PUfBIZORGJ6iUD9VoyhxNKyi3yV3QxS++56UmlTtpHUhW/UwIS8qRqRUmciOGMC1jQq3V3hJSAVGWU8uTFC6FI1RxZVVGLU8UjFVghKX3ZxLGNO4NJzlyeJ3FSf3PsshTi0BUnJhVHw9N2isRtAcRG3TLtrUlohjvxpAUHaUCLxgwYU5BJ1fuHrmWxK0MrJMkQACCx1pIutctJMZhCIR2N+07dk5Siy3RGTD76JyS0S1RLMy7QJ0RlMGsCwaZuhecauccGRITgsomAgYBDUVAur35ILTSK61x/4CwRGWB6DXutE94MFuGNvEjIqa964AXpTCYMv3hpgj1KsfNE3M5yO+DR9t3iYrc6H6zPtotHt07GLNH3+uMn58v3Lrfr8VO3X/r4x7/0jTd//JhdUIliQs7eAGlmWezT4dp565n1ctrb3Ond/eQv/dYf3X7pa3/z7uE753ir6SVbv2ZXp0eT2cVjNyKgHqJpr5sIjhHpTBlwOHTmqL4JZzPrb2YDjnxCYse72JdEiLwbLHvracjtcR53xsGk45USkUDCeYYWR0rogjKucqiBYhTpa4Qn4tHp2NOVcaVfqdS9y0M2wATsyr15iR93EA1YaYphAQtxEIqhGViQ1ynjBWRBJUza21ZaJky0lRVSJ8LVXCD1JGhhoJxWnoS3tNcXx2FRzEqg9p+bYJymPsOnBGJotas7NRhX7n6WGuJcAn99oGsQkP4qVGo4KeKqSQgpL9WgiifBS+g3XbRyckcCIIXckfF2v/DxMxRWooSkBtF2LvG04rRzWCsfAqKujtQVHBIBDRyJ9lLN9kWylOD5DN7DMbW0BR6Yesmf2OAPzrRGIXUyAPtfFvNX7kkRWa+E7qnaEwUJFN2mMBy5/soaRTehjTHR0LZgoFUmWh22OEgR4wOdEXIDgCe1l4lbsDBvJKOo0OVTHxh7jb3CBhPWgjRMFndFp+H3quUAKHOUDHwS9XYmqEHRNs1twg0Ig1ge9IEndMBwog5JvXyXirXQtEgrS2UmZtp8FPQoEieWRLWxRHdqj1BPAfg5lr1TxOvlkIOn9uDX9Su/YMcb8XifEcmRkimMSyT1NBmDczPko6Ob+VEfH7JezxeLyxnvkuf2Hl+C4OUP8+3h46vVxz731Rc+/pm3vvdDfBmRXJaiuc3o+7q2g0nv9Lld76ne4f3Xf/ffTD/82uMrXpVzcjHndRCD5Xozf/xoOj2enfE8ENv0eIVovmYKM0z0yPt2UH6sVfFBRh0Tds2rRP0BHP+LXErPD5OJtTvIUYqLa27p8DJAiTrxp2nhWVCZPUvXCMz6Mxqhc+iVwKtTNIcj8epLFXMW9eXw48fbXbzvBp9oWOuxE/ynNfO3BS9eXRxdngZSVuy1Mhjb9PiisrVVDir6BDKgsUccoi1VeMVJFg2LDdunrRiwQ5oZp8f9yZiDwVXJOCyaYquMTVJFOhRQoifQIDAkGrgCI8WQRwcxDWdLFnYpiA0XYJU7eDYLG9Tvc6BVX/FH4kcLHHlNK9cw9/fzkFgoZpsFrRgAYAMDYMWehV2qPJseYB4YHA6iH/LMA6AUsQuU1zBAA4jz83OO5Bfcu+mx42lCY17uw0cAyk0Wl4nidJZs4yoqNKmkPdDH+dQ1AKQqJ4NivP4hbfzxnmP2L43HR3u+IVF5MhiFF0NSPBGo0v08MeIrmyHNkUrKixCeU/yVHN0YaPRIxxupco8ek1IF8qPN+XBpuZHrVkGADwY5UxV5xsVg2tvt0XRKU9izSro2UgP9MQhFCfWOVbiya2LIpQQoMoTYrss9f2672sfsIA/z4KEtLHNRJC+u8u90OHmpU1Azft6pwIWUcrZ9jFyfgZD7NkywAEIyDkCSIxWd1BIN2Nn4xuUky5kxIsjxGqreIdM33ueVFvTOaLw9GBF/91gyPxzhsBKq8m3Ag0lel84WwtuD+Xf+83/sLf+2d/G906enZyhqOe498+lX/9EfbCavvPn2FXs8D+eLKR/yO+hx/8/9CG7cI35ZcnR1EneJ0+HoMGPdnGiJxSn8C8ttfBuWdzDw5JoxNrcS8TuEtGUYWTGMVWQqp/t355jc2+Mc64dKkRHK+5Qegijhu6hwQ02trubwsInvsfLuKkrTQ6F5/jP02dPHpRe07r9xCPl5wdxEaovi4HElq8bwwcGKF0jYG/pUCNFVssQorfdJcRrT5qh5uwuBWi4hcYL7Vmyh4suSkUW76gQkD+blnJdV+NYqWKKkUptG4ZfDCcdKmKwkAtSV8VcZKSs+7XtNMRKFYSoY6cCQYArPgH7II45Fcc1FF0UpZvZDMK7rFFSMufVqMRxxJTyY8x69IMFp0Eo8nbr2PBQSTm8waRaXl6cNQRzaFAGKtD48nfFDOc2g3TUu/RsfUJJCw7EiQPOUlEIcoM2Tp2OotetM8M9iLfbVUmHDo/C2LYpKBgFCpVpAmB+FJErM85OFa6mqoSXGraaAqxFtloGYP2YiXekaXOg+lqTzEpT/5QP3vRgU2Fm7xCTYRG4weFmKLZLh1jH/g8oGkvSQbQ38VZLCKwOEnr5fJr4MBgwF0nkewy1Nq0RBZL6WabkWGHXj1VKrjScG46+AnT2KIuFFiQYj0QOOQHBaMdlMHnJuSa1BC8Os48gO2DC8BBwZaXCrsO51xc0STc12w4v1cDA5febFlz712ufffXJx8aOHvemHX/+tb2+efW07ffmNd9ebRf9gcoyxuk99w2I/bp41KdehdE++lIoNVr4ZxvfwrQmj+LANS1q+h4/roFU6LzRbMTqeDlvj1BIjMsNGhzpWSBluKXriUqxQ+SUj8wnHsvFGVVCL36aUqihEK6Dzqk+ptedyRMtREQUjPmuRbkQ1MmAPiSx/LAGSEuEFsB/3KZ2Y/qkLSSpSKHA6J+Q0bY2E5owFK+wsL1ecU1ipGjAwGTDmtaw2OgoADBDPIejD0ohP8HZjWQBTWI3DAo5zocGo9rSTOjWDUYQW+JtDTF3GotSBKUdBpk5T73yQ1vCpzSqUU9ThyPWDGhJ7KsV5HcNDKyifwNE3jlJGe7wdQZZF+fiqd0Bl2kSGwkq4WjIUhvVWzikTPsrBU62qCUcCd44kautYeHg3s24xW+Spo2GJ6js2w8MeVaHFRAGg6vr6VmFn+hkPVvhDKrQaJ7KKGJIGo00CEhE6fiz3FgYcwqPHJCaNWAnWckMoeOAdYlQzaIoTgRMKQYMlKr2Vc4USVgxYEiAGaNKxJA4tXNm2fdRDlSKL3KY5VSChg+U43pmGrgVIHUSOPwYXtRU3hW23xUbVOLaKcKu1bMQBG2c5GY5l27BY7fw+b+/jrh+f/5M0hUNCLB541q54henBMFWUM8FEEazKHxwfH+9W88FiMT3YHh/u7j99573Hj3xN+tH0cnf44PziYDiZDEez8wt2eBFD8WDNFh/UJuDxmPgsNi/M84UItyZUGMLIxx1wCsvYhLN6LAPE2fLKTSJEwLHqIHR8Jnu5ud3EOFRZW8k5L8kVFv7Qe/opBlj8n4Tsm0RbRBa0StdlLHMWjx9UPEaH/kELBrgy70hsN+zlGbBQl1X4idFSGPOTA6I5ZKFc3uIQUSjlIKE5qFV8kUgoRyVt2/RCBAjR/AhgXEAZudSSxzipDB4AIvj/owcclqZbyiybKe3pFU0h0NwibBNDFEJMDpTRZ6a6gTOKsQnFLdUg5aRQkYEj2soka0T54DMIreXLa8vleOQOfkpIhSKIXT6pDMcqD6rOdmt+S6SHJLqtvDS+IGoJrdBBmIdS9ij2GMnQ3YrUBG5ao1VFcHvuC2cw2JomcEYiQxXwbSxZabKkMqyN5MrgyKcwtMRWGkYt5NVO03u6y7NqTikkSKgFZqwNZvIUcgZtIdXj3mGlPDgb8sa9OGWsmog1sisLawdgVKKIHOpFOh0AFQl5SWfUm8KnficMFNcaLD+S58p4rVhcl+UYBOOCWhOXvuhNndSpYwYU4qHKuMzbwaUL//LDZK2lLHoLWMvDnoM20wRGchj2EknGe3Pqn02nOA5W/uYXj0B1NLnDV00vVyeXm9Pl9nS5Gb/z9nvb5WLMc87rq8XVGa+p8mFE1td77CRl4wLr6L7ECmwuS+F3+GhgeStO2a/g9BDOGf8+RqPIAmdeK9v4F9Qq93QFR8rUlzNp7b4kVRdU+Ofa4wiqUlWtQpGzH1FggaqONPGg8vdH63Phif5xOrS0o10cdASKE56rCa1COYVBUoiEya+opYfh3UqTF5qqoeG+WdVhqXsehSqKkLQ7Snzx2FB/YaPCzOmeK1ksb0VhASEvGkheSFHZ1pQNA1XIWdleR8FxpN2HK/Jp0KiTL/YcJgiV/QMWdUnc6SlXtX4yAQK8iv3JVIQwIqt9rVV2uuOwsizlECL8ARUtAahMVrXsnr0MlBfaInqznDyJsYwsGld0UUeA186QHUiFnPJCS7dDwOGo7M2tAEN9nr/jatviSOgCgZ5UFaDYSuKFJmbKKaWuBjxISK5xBMIm3UXJC064tCYiiVKHIOvkBa4kU1rDMM8qUgtOqp0bGgX48DY92DFlb8UrMNISWzkIg4qGoShirTzlwKZYBHgtr7y1CoutkIeyO90l40WdJWG1h2a8pLuBOSjlNgiD2ngkFAFzZMJ/I1fyZIBBvDiGbmqJXFz68lXo/PQa3rAjz5KNz8QwBXOrwW67OJ4MVssF37ngKetlf3L26Px8s72aLybYG+/Y46sQl4/Xy7MRz1MMWVw/1wcxGXQhK+9UwD3x8mKW3l0MosR5ot6qyMEAK1Z2Crwb+CBwfIyFlJVHL0mwDC2CrnQkoBEntgqr3iyLFDFdagUDXiyRURiaA0wZE3+BLQGq9ZemwDnL/6gZxMHAwCLeoS90eaISmI6LDYQv2LY37b/wIP70Wp7pKwoBtCFRcTo0CD2VIilzoIzh6j5dgMXQtXfCYYkT1gCCw5Cs1g1AdHISDlzcCHoq+UFIPJGiUIFFxxcthgQty9qtwF/jHDjvUjkKzTLDau83wF4lADLQmMrYB0rkQ9HM7iMfyBpfezzAyH1SGBXASQEeCiCqQVf0yFNXDSBDpvK0TSgAVAsLq7yA9zCc7hPMFUWOBVACMnpSovuDLlU0oYpCMpkDYRfGGrBXASAwHTZRkQCmifCV9pmOFs1T09ghr09Jk9IQglOI5Az+azyFzaPbCOBInuANbHsl5ulLLaZIVLkSIAKqi7BVGFYdL5wGj1YeDl1vdgB6IjUnJSayeHIzGl6qUkgePtGYq7OBB0YAwhCvVEBzGh/k+BCvFsgm9AyyGoQWFo3EJggfSBHipGCHAcwYZNYrAi9OuDxWmkAcV6WbcBKH7/dp/fkFXx+AJHvS2XXOfgnuGbIRdMzbs2e+YqF2SzHnXvO5rUN2SnGrFzy4pPJZCa/IE3C5oMZSmpvvmQKJElnoMB2C8y/40SXQ1shL5mIREA99T1k+NxBrPxTV8tWPsa3qr2RZPtQzFoyaBIO+gGkfWwHUcKXqkeRjO5xrEvnBW1SX1RnJZam+KZgmsN1d8osZqrA6JRLIvpaBpJyLULvSttuIoBfKaIUtoarfzXcW2ITTHoDhP+ilQJtqIjppaqMRI5TRmVqiNOwV3QzDsGQ4JoqYbwYpJxTg05ECh5VKeWYUk8yF+RCPcdI4vqXmahAiQyueuuJ4beGetOEMe0whrYxmbN+pqN1WyD0R32ECLqgCSqYN5q4NhRVzFUOgQPNB1dQdSYpP1VQpugMSRWhhKbzpYjQRMBVwaZO8WOh5VK3eXWCGGZeZdmvEpZ4uVImJG22fjgmJptugSMghVUBQaMC0J84pY9rPI7pRP0dKpJuuikCNqVyZtTGis7qWRiGsIocHL8oaU3qO5nCiQJhjpOAoMge5Mja55JahR5zCRijEiXIoBEyp5Sa7rXK7KQ6FcURjr1XexM8LlsDGYC6VEoc5jEXqEFAdXUAnSSaEokaZ6gp+ZQajRtgS1ZuPeOBsBlBKr/RsacBzWE8czF0tOOMWCm7dvQ551kXndsAXLtZ865C3A7Km/gAz3Dy6HNy+e/7kHMfU5217qIZpJXeylpdDPgXAF8fUj/pvSijf5HoQriqbsVQAPEAbXWePO1yQgSF2h1CGFmJRUVCWsawOTDvkrMosR2moxm0KqIbWKEIarNR7sfQluiBAIxYiG8tz9jLuPx4lK01yoi5w18wARBUMZTZsQMOqDOpCjYN9KjLgaFkXmGql5uVADIVZa4SS6szHlsx7FhT+dSmD12Q6zoX0iUJydIcMMTo4YVRCj0T3IYrntvNCQxvEgBqwfq3dADAXIJxynEtIAx5ZaBULksmQ07aV2osEWDkDJzGEmDk36ac4JYEZlUar5quw2GMII1XBsPdAMCAy4iiUVqQoya0pFVRFVEFWFQDNBiWebCWDn8J5UciRNiTytIS/Bpm7h+TrFEbJAEDDMJ2KHMBGSSEBoHjiSKKckqoClpFbeKiq9pXRdaIMrcidFrrL1pD3pnthcbktJTdbVR78lTwFrT/jdTwP5eLnf8hxWk0CKAOtJOUFGbPdQ9kU7SNDhr/NEclSBno3JwcJAnKsniQPq3SSWLTUEOVt7EYyLTW6cBWthj1HBeg95kcX4b3hkVoFKi+8f4UAg5/bjixIO3UOV4xHLxdhMtQ5xVRiPYHRedEHMERfE4o5Sk1KE53p56Guu9RVYfE7dmBwqofrLdkOgh3ttu896Z0cPfXs/YeP3tuuNge84o3LC/s+Ly+JWI7GY27w9y7ZsuDnISKUluMg4cqBufMViUz3o0c04O1lwLg+uWpJ4toKaxVA1QO8tJUx+wunA4g+mYMCRCi6wJYk7ky6OwdRGCFU2xHgJ8uUOd1kT0mRsNGZi0Yp2kIejSBzRmjiYhkTsb1jeGuPQqz1pYNdbBqnF5OAod1qYbyRprBDTetZS+gowk9MNCzZxWgAFLUGZOuklJDTeXD9yCAFstXWH4jK/3UhAgrJy318Pit0gUFTmIIRH7e7rhPAldRYmCEQbXE9Tdyu4S4CBAwJTaTAQEEJInMoDIWUfVGsO83nc/ZOUY5yiNFOTk5mPAFWTcJqsNmC8V4Nq7aO1DJeHFQEMHRSUQUvqRwWkpQ61H4Ypc2N4EvBGaLAUI77AANgPAPTxqMz/Nx5ieulNgzRBEvhTF1x5B096MTNNbzdgRd6oYtcHECFVOMRN5K5xVQBJM6VNyL5rV2aeJ+OLuef13GjMEs5gS13qdnXcI76oJKQkR6zkxkN2qsjHoPgnxskmXky1EtSZMlqapyCwsC48KLPylEbRZIO/bIMENbrKyDimha7alVRmmudGUfAl94O+7wRjM8LyqHDw7dk5aM7jBYdNWDwnSs0GGiOiHQVWqKKzVskxICl4Sibgxg0isK4AaUPiMkw40quKPBOv10NFnBKAk5iVTUTFEhNFrfkQUEXwIMcd9N2ahkp/ChCKdTRf9z6c0vXejs/O+fC6nudWH7yXhzDj92Wh6xTDbcnB2u6eMFdaLSoyOUXzLgwpE2oTH+oT20Zl0bzliMrEAw3PlrokwPsc8jbrGqrdJRMn3IrIK88DCo8ajh3fod24rchh1q4tPgSkPYWEKTUSRG5Vr8T38U4a+HROM7lM+d2LMKoIXVCipunEg0QxCY5x2S05qYHSMCJI0M6frYgwYCGjfcCTDvUInV4FgTCQ3reMl0JQuVuY+6uUkmMp3mAGQx2uQv/3LiANF1jAKWZ+3XRIR3H5kqko5DPiY6OJpuFW8OwNXAqyJaXzU1KUbRFJ5QR6PECHySDkbgzTci3wLl25NWOBE79vk08RXpKHJK0kaUK7hSSEmp4qJ5C8jgvIqThyBBnPl/w4jzaUlVREagoJzrRZiGR1HSby1bTI0XgAg4gScK1+rTnqmp/3ANQJad+xfOwHCcwpCIDJsodmsFcwBwLeaPa1VJoyssJMXbAbBuOaS4buTsZb2Nd1Kqf1vUESVG5kX8/8xWg4STgGPxoKASVTonCGCUaTbaZAKNXGlx7+obcXtQoOJQ4DjSa0zBIuourorcSNQCdnJr3DObZTOG3HPYNU2gteECdxBmqACZngHoDnrzoMNlCBv/oAe8hV3YfEBCjkq4HmL/lyVs7p8MMRrnCwgVQaFpw3eARCjmgiWhwEiGBTTojhGkqicV0OdCCDaZ4MmQbJ5P4AgTLjifKgHG8jRikuAtO2H6FPYIcKLBJuPk+ImkvCVZJO3TUU4kmf3IVg6SxwkU+8MogsgOgMHCT/tXroUa8jBv2rUW8DEFPSiqvag1Y/soSQBIpQyXdGgp6iMwYqnm0KmUTgidlnivT0QXMgLMguiPNoqtCIiRoa8KYPO7YQjQQSVuzNCHf2to7XSq6dRbkWAt/KcZipNINftvGrYglABwdZV44eEEp3/JwM1cKr98RyseSwQ02/gNoQx+icgBSXhg4ki8rpYJTUii3+Iva/WSIKk5J4ox/LIbJN51Yaa/lbzHbmgDAJd2wqLBUBkS4Sb1vkAJEhqrKFKOUcFqt0o+0UJg9sEji+LxQer0y/KlUrehjOMe2aAIwheouFmycZSRBSxmlnCNmxS8mJzPFACRUcOAsCjwISbRK6GQXQIVUTWrg1yXNYS3PdAaDPE4ncjlsShbCpWxwFXfZU0ejvIYkTVbLHUPSiynnYAVnFcoWLBWFArZKjDXsIBcMICtCoA0aTqvIo+EGoZHL8Rn6uI/mKtCgI1/CGdgIGXciepQvG+qjqMiKoaJaJYnYVoLJEJ81s8P575/UxwB0NjZUV0AonX5psN7y3CDXJT9vLFkwAQVA3IeGzqoTr1VY8JTy9tBvRvQJOkCRJXxWyVQFaInFYsE55QAu5IlctSqM5KozQY2qACScFJsylp9M0KeGqIQhDbnYEJMRUiIIqSyMUIhotnpPKu16EvDl7dQF4knNWvSs2nysikaC0FSHW9d1+InGjBXJpYno9v0bVcMJgjG5Ll+cNkKlpzHUYkhyYbiqRCmM4gNgYSUjSs/VeTBXrT1hv2eRjlx2fjkmcgkiw1gDP8FRjAfJnKNl9z4iiSrXEaYyFovHGLN4K2EFAx2owHqTNOc2B0GSeo5jag4hY9ORiy1Tl/2VTDDDjwFT4z+9UpxUifSY3oGrchxD2x4kL4t26k9ooU6rCcfKQBvI2tBIZk8PbIia6yM05F7Jomvxh10yplwNwEYtHBvwtKmNjpYEiPGRaDp2AY2yOFJLcaX35elFACpkhTrKYBrxfpjWPTDYDePwScMYb2wSGH6doVjVEb2JjeiGKjhphYGhxFP+pCp/9wbH5Y9VJ22QVje1R17Wb1gnQvIoEYOF91dLwvGpyweoOIeKY46x6YGUoRs7L5ZKTcW4LImwDnt+4IEpD66HztBkjRH0wsztGPyk2KI3l6HiArkRFai48DgHjOQSNzrxoT/HKricINWSF/EXTEvd4cos1akgVfoWBmXCQwOh4AKdExuW1UTAP5vJdUQMjCTtGpIex8jRIpL6UYflLdCGMD+ZgOJeFQoNP2Jm/AFCK96TaBeErWokTHrI06JYhGSJpOXHtXmxCf0yHxXRLCeAQAmey7kZmznsze9lSbmnlaRdgNc9RZnFna0K6Lk88jc21QyvJm4xEkBCDx4Ac+Ko/eAvGGWZkbmZE3gu8SiMgTgc8zCNA7A8k5jThKpim2PIXnNKlfARKrr1lEIYCA/6SnBWjyQ6YnA3PwWWwg8MrTiCh8KiwmlzWFbrca3YH8lUorASKPhOFIWcQpL1lw6Eeawa12a6voSwvtmRZbTly6Sz2bu4d+3GZKC9R0KGxTZiUKwYI7eJqT5Epjdxzg68iz06furqFkHANGM7gr/pNgsjVAi5TgwnXCQkyjAjaepaP0oCtDQokVJQ6Y5mAAVPM5lSUWyJYfS+lKtutACfGqomhClhGxCLqKGslqqnkVSrk1mW0C0mWShzjOT4OqlIkViE9ZL0It4EMXAV8mP/RUwGlVT5rw6xMv2BCdkpF0VSNC/GlHjlJINuonOVIyfyzJHpXI60pcdlNaGEoQUuC+8imOygYBv4UlAi99xiRIRlvvyMH3Rpki3Jh+hJ0wQAAEAASURBVHzV2W7Msrf+BS0mSJP1YhZyGXX8FbX6RCfU6easrJVsyq2yJPrij2apXnnVvM3gtSSpSxf+F/bz3Dk9oj60PwBlO/GCypGOF07+6L4tkYK0uD/QpiqWJOSDiNW6VErSw9FXsURHCBlLK0bxA1Ui5phhUeeM9gwUGpLNaUTOvg7uOdC8sJmz80UaMLUmzqToEHtw5KsIZsTscQOO+7CJg8MYUJnLg4m2OhQe6xOJ3o1+7buiyhDjUTmawhVqyi1j1NqcSKMXDHsGUL/AYYzm8OB7BxJtVBUlYCBPjAlmMiQKSWRkOGmP/GYGeEc+RfqTmGwRpqJIkqm0bwZ8lYAW9RV81ZInUcvpPm8nJMFlOkPYquVYDa/P0xxwqoDnP40LWN/XYS5UHAvV/lgA+2MBgBzC8Xw+38A6dyn0mnouBQ4ILx3XwxvmgipOBFbLiDoeajLbLLOJUfDdCX9p38HzV4qhCi2x5dSX6rEHvFQR25ZhbSKFobtHEjDdbqPRKQqArevcSVJUVxHHkMzaGLcUadLgQNZlHa7FPBwyYPBHxFD0bvdglRtIhlBlgDNIbUkCKeWDsQ/viYrOKgdBS/ZpiZNAizXdvLuKLSn82IvqnggHtg7LxYJOD4I7CKkCW3jzXJ9YHe047/KS34M1LxYZcDHglD0wwKHa8JTKqu8yVKCYOqj3tKhDXD9EOzbgRlCuZPxqvem6bwufjEnFKVvDZsWecPJVUk7NS0kgC+q6T+ORq6qhspmYOG34mh2lPNbcqqrT8bxtxqdzYeDAE86AYJLm6K0hCXUA6pQmVioC0PxvqWuVHlEyE3VCdvJVPjVlRU2ZVUItVLyLFVfDsQK6GF2t8UursCENeXimlaUhVMohD4wV8ApEDeOiUcdYfEMEGIk2tZK/x74XuPMCxEHtcg08tTzqKtkkBIxNg1gvG5TNkgqYBgjDehjdiWDGCNHO+/jhNqEP0GL9DOzaDxKI4lAS1PByJ/ogAmcAOUQcEkkOJYyvBkN5RZFdWxucoHuxeki+iZDOcCRk/OSyGuKtF7k2A4iqKCTCwT1o+ER2dfuviVstcpQKXCXvNZ4WsUdFp3EitjgZGLePmXy1y74kuHzlIpoF9ODgwLTL1roDVsrdTqUYJQ7ZaKAGTHAWXipKVuI9QSXl7dRwhjx0iG0dx4LaiN7kezi6NocxURV60uAxANS/MF4SFMUTMLIthvfzsr2UZzbz7jrdUHxguQZhy0fYBkL5o+7omChSMVo5fs3mpAZmNh3E6xwwQM4Swcmh4suqvtD5qHXyRbnih0fU5Wi2xgOWwHUZjMhNCfEH8Fotqwrs7wcmA7awWWt/B3PD0HGFIiWVRL7FX3YOvcPB+qROHAPjVgJF2U+4ZdTfPIttYyCyUSiKKKdAdeYTZWjTwvBOIR45TGRnq3JSBhxGKkib4ZZVrbx9yBYJL0pkRiKtMsEJ59qHCbBiVcm6EoKp/TiqiR6YCmE5LPIQLZcE/vhPFW4e3uI0AAAMlBRSRaKqmHHXFY0Llw06JiipBsVTtaHErTUdr3BCHkhSTc32pxVR04rdnkSWRQzkZIhLi2m4Q70O1tI8R06yfgGe4rUgwUOGhLuEW+52hCtjDWUrtsN58QYkux+4o1CKBFVaqwNlDHwgO09AaXTU5gkNuloDSCuvUlUsBjRY+qXX4g8a5mhG6pFIyHDFOTxw2g2ezn24hEOXabYi16DL9WRAWkgJgU4mYiiBhU8uLWSY2eABCHfSMei/404moYNaYJu3U/FwdcTQyKjS3Rgj4Bp9oRoZf/6jFjH5ow3BCd6KYtCVFN7sC5PlsMBGHJ/1qyyWu1oFLxkyMIWT9CZksHJUwJpd2t/0Hty4ymWVtBxXcFXaS59UXs3TLzJuAcxoyJVosodECGsDjoiAKh9wqAXarK8x0w0zyhi5FSsqAX8m5QnToKClQZZb+ECQfIEM3Q1pWG3agOHkJYQIzm3ZWiJfESGHcEOtQV4EoFIXUVC8OZXX13jKkQRQq9BCVQtJSbqEdgGwyj9dRpz2bMAbe8pHYJWNk3IebPshUKBaSVo5smKcGAzBApj5wB/AnlKVKTb40S0/SXc87IkWgzQhQy0BB/n9KSUYJ2OWnaJ5EMcXH5d0MEYT+YtQNKGKeWllaEiGI5wAADOc6qnqk6hVqt0nFTROp/wOpzSgBgAjF/+6fZGSwkVz8myvACl7uGazKzBnHsallm+oAO0PdXjrBtoufnN3Q47A4NxSg9OkRr6ASXJ4fni3ghdXG55YiDrUCM/cG2iwp2dBxIE+cGQgA4CNCJg4JNgGAZdVWOIYr9EfbAvqlEtB5AAfyjPgj0lhDg7pdJAPnzh5yRur4NWvS/EtY/Y9edUNmDaDQFbCogMPywGlvCeQxLhhfsE6wiGMwq0yAxmDUP9LpEB/LMiRORyNXbMDgiILRZcf+XJt6EIZHbxsqaIUVbstK4NWZdrRwQC8boc/+hZAqJBTdQ4Cdz+hJAQBwM7U2ozg3NGjO8DzETBqKFx4aEUJvc6PNlXPoibP5ADIjz6g32EaDBg8AnJJ8admGNV4tTWvYnPsu55SV2qVk1FN7zjy4wvg0UL2tRvYUS42ZrcxlSYC4WOUA2bw24f0PovE2cfHC0yiPTcT5UWSmKgYQRtfrLzaln2DKpRFB6rAyKgEbvfTlgBRo/YwNXmgFSgoZrylVEyolkKWANNX8m+eN6DwlC4XebTn1yr1X24LyFXcthpCPL2caU7RXoQNf8DQRjgBAImKBMMRoBuvggoKx1Y7SFCrD5xmAlhv6+XawkTHclejGPmsh5HXYPinF0ikw6wfa1QRDL54MQyb0cWbL9mvCyMaGF/xpgjC+BpdCVu9fLtesScqvpjE2M5WwbAN87oeqvBZOo4sPbMPK2gGRqyE33ywl9fyM21iV0qfWRNbtPCYrH7xtkc/RyIqu48VRKVwyJGaUmAZbrCzTCZxQDUN1B1kjMGBCoquK89plYAEy+AIy5SoQUwpjBdyqgIbn5dJhoaLXkIdHicTvq1iopCGlTjVJpPIV2EhpLsoFiDJqjSGcEEWWAHAP1d+jtfA4Y1GMeVgJlfGUWTieMAFFSSOl0m+uJAWvd5ktAV+ueMQFigARKiEmXAl9agRWyAZLkEuMAJjEXTa+3gI+vghIjWHaYe44777q3HTujAIpzlzjANQaIacUvBzSKkN5MIygEKLGj3g2lhysq80sE9bzyKaiKr3CTRRBkzTskot12IzGKRbPyn6o9rNjRm6HLPRMa4NVQirwRSzIqQJ7IVVh2XohycrXZYMXZVHKEVy2Nbcpbb+2xuMLZl3G0FrUAQ4UVy9YROrlYDE3rCuS1EMJxTDc2U4AW1BQDw6tB3J8qpicu72hQbWgNGmF34vq5QITBtdg8ySFTPkzZmKSqSzBEgK00Kz16SvmRWVdSzdtA8AS7ragoe+p3HqPVAggZDYhyaABRDuTESoeN59SWo9gJMj1CpDc4BBhR4qE8U3Vv8vW3ei7chtNIvaUk+S7PW//3NeH0s9aLhfRKCw2bLR7NqJRGbkgKFQxSLJln2GVsJaLRG7VML0dTdZ3nwd4HP9BHbCxc9CcaFo5tsaxmoAZNpbXaqgLxg2FAJWxwlE7ukG/CHgWG4Zs9XiBBrH2joQNEll1ev6kPFjQ9h5cDoLPDEFH7jwfBf73/xZa6dxRbsWTIck/Rh7KTCV7T42VqdGBGGIbRUI87GOPDuyJxVpoqAKalqENm/0V/C7oBCLZF45LUUjycy5IqOka0DXWSFLqybF2YekvVvWjo2l+hZpzf7n7AIpgBjCido8aXQna1FGxgNjZDJtr4trqWJOru5DWTK6dZ+Nrli9IVIQOMwZsmw+C19WnyyOuTLmDEtZhR1j1MB1Po9wbISTmVKXkp+ARSVNaVw+MSscXjoPP6/sgxB0ohYkG56YJh6kMgdYN+xjPMSXkC2azDrjo/Mp1Hqzu0KxkXK8BbL6OEWNO+E/XrFMJg64mEgPNIw6uWq3oqeXmwHgOcdKBRTy6cOenGTAkM7O/bE7/x/MbvHap8eTIxZvnRuuJ/whoPrqZ1gtVr86e5ZXvPhvFlfrVDvIXgH5THAI4edBTSMuC81U1lRae9YExcTtBnb+8DPEVYlcxkY+IaOQ1Opr1CTBJ3WW1KzWXQG3bo6OAy2qcb71t7feZgP02lQj0bshjpgMTOYolzm38PP4RguTqtyarm9vu1AU5/pFiIEWHGJsUM/YemY4/grrD5m/04pKywWZIv5GM0KZ/CRVCY92bPsBuUxcBlY9yarFcNJzwV4PxVVwx40MygzWWwqivwgcox28FmEiNxVMBM3ZbFtrF9E+I4lDHfZ3cwPW777X91ioQF168I87N+Q/fFox70Y/4cSNWg/Ck7211kPO7p5gL9B6oaVXnEmIF8PQMfjgCzPzuW+Hs2426jiTxHDMJyQrb+69yD9aN+cyUC+ECDxFVbkED5mefJhemfO5t2NHgj/JTIijlTRuSiS6O3q1Z+v6vwuQC/U/JY7ptXX6IanouOPAi+fhMJ05lug2QRCTzB8bUDJdwoC0KfNZUc09h3E1POqaNq3ak0GAM50X2eiRLCCRs9MpzPHW5t86Ps7ERtOyJ+iAzGpyCw56U6Ct8VChJc1Xd0bxJ7m0YCrTQlQvAlmsu35NfZ2FTwCtjKYyAcKYA6eb+z+3jahCDmcJisS2qXHRbuB3gVEeFuH5MZUtnzZWxBzJ02W3e93IghUC4SF0VYUQMMeAvcsmzpFf8wSIQsBewPSANtdnOorO/2GnK2Vs/uRYzEg/3pJCO0clvJ3wKx/zwckZO38C9fiUEdDmqLwtHxGqVzEyrUHntFYe/xJPkpmzdMzFbl/bXNSH3FnIz/m4ryG/7jVkHGZfYCeLyP3gvud1Qsw95HwW3HmymPMtLsTh+n/oeRumD2OzzlvW42pj7F9BpFXPsu5KCkYcTLaTg1a6xUDWYrmbh7njsyxxstk611ZZtJWkyzFQnbdrdaxjuYeV6PYabJ6rsaTFA/+ZhFpfLdn2cci31aoGDOIMyrPCRiORiChd4zvgjZj31jsWfRI7W+66ye2JOqZoja20xbQ/JJvJ9lbiYHfC1SU6ZnLb/X2WjkzssLOyB81L3/PkGfZpjIlaiqFkSSmzfvTg7mTeIk9D5CPlaApYgVBBwW8Tfkrn60jHyPM28HHjThNNcbZPReEXdWDHijsWGXItM+qoWOAcsTcN0aDQ6RHGn+VidBQC3lS8qITb2+fkFQuQ6zCrBNjzDajol0tCTQO0gCCIrWpxsDKcd0OwYu5xDm7Wjl2pdXLWVg4kJ4wmgIYImjzCPa8tWOhdypH5b8O0BkUs/dGSgWYqxL/AKtg7AgFLsOzwXzOY0Z1C6lAqhS27yaKzyjBDb0GplaN41NulAfOu6DYonS1RCX5Ma0syOrbKTCWPRxsoIZUCnFm7XVV8yHTqolCERSoYsPyLb/kX+NAcScLPxg2mQRXJE0uDrXXy+HMvxFMM2uKlHh+ejcbk22oZydmSoZw2+QYJ2rm506TFYTB7PQKmRGdLl/34LjFxLVswq9gbR/pb7fGAPGjHT9XTtc1AoSQyt2CTClL4+aOSkl0GTpRe+sK5i4yTLWmncqRzLDo5fOCPwfuna82thehiEv9axqkAr/a3zidj9S1uZMGisZ5d1xdgTvZsQZXMXuj2+DPM29TgIJgsEDLGADZwweLUdi0CudXuA96aojDXM6KaqYRhl5IJE8y4qkSw+BNTa/uZibfphFZhWpvIVhxTey4F/cFBbOdVXpwns3Do5s5mP+HMUN7DORdtcXIzhtY2U1aSCHdJoa4d1IrUZA0b65pRpQMdx1oo2lnqAnQ+9YOjkJxWV5NEi2DsVvkyGV5qRa9MC5OL1wESkep/fQk+6W9EEZOXMv3NHOtAhBZ1qWEpROdWDTERmeR6/50Sc2EffkHzVkcM9JyJpVQ+vLATYE7ghCJnooYTMQO0sWsImsngD5mUQqaeSIKjIQY7z+vi9hwkZZ/TcpCb3/VNOIarLY/lX3KoaeBlNkE2ROecHjMtOYsGvb6FMy96rDtJwVLiVAx8KaKCEBq/ErwYOZIbZ1mwYJLNXe10VcNaEhpG9lZblxoq75N5crytw/BCxHLCPvQ4OTPH8pqoLZ/iIxaHo5VJleUSnS/+ysVpuztWE+8Cy0eaCDCRxErSBktWqPIhOtnEZWj8L1XV+LRqARPkqZKsmGO6NYJ14zDD6OIr8uC2h/VyR0hlhFO4lw2pwJcgVhJdYInle3LqDfn422Q27Xnjn0B6Xz8qzMjbM3QxjFsScJLzwaqkcxsJf47bOfkHOQ+MQcmuNoAtNFbSxTqgay67ivY0NUYHnGXDmtALrHwMAJEcyQEfzp2vZGQrDpWB3+UGR5MjECqygFbyBvf79y7I0G4rJdIff/T9DZYdbsCPI/WHFgT9nAXsskhQYMZ7kCPShqoHFBQyDy+xzWkBgJ4lX60lpD3lsEtOWvGyisRmBYHvuETEhE2Zrx5up6/bKhx5BLdIKun3jAOPjOS+vqY42YJOMnqCPVpgOUmmcV3h4VPaqKeS1y1y9Cy1WUL0WRAodY/aBWuysbLFFJUAuyY2WE6mNZrubOdzSQIIwp5ibx6yMOV8lfeGZYM/BMw6vyoU3farY4ZFgkoM4NZ0Q042uvJc90d0NXuCyoDekD5SWQVAGZzcTg8/kyRDFo9i+EZhJkDWgwz7Kmt65rZp0EXEKvXGzCIS9e84rcphkOPwei1i9f90omw+8y0rl07IIPGqSjIZ3KwRHD6RFCsex70/zIm4nU7pg9RZiGPupTB6ykBOvOkswyElzc3AI9i/efQhAmyHyEMMWWx0SszpnLrEDa4AAW4Kb9wGz2JKjHrw3wxJVXISgzKTr6ikmx7vHsTyhB+otGaFYoWAauJaEqo+t5ME/A5UlgwnDw0oQYgNACnIlZHASBJzPK1xM28RTmwCRinHrCYZpV1BHCFcLVW08oCf9QGUfczyXhWM9KyvyYKMuMyri0nF6zogXi7meaXFE4yzOiU7aKLiVBDR7xqpqokBhZgjvrUDU5WklXJWv37xNVbZB+ITwCTpKGDEskMdx4UkGd9x0bdQnRAyY4LrO2p8gfr79z//9Is3TPNISN6ZqmssZycih89DWO3jnXp0VOKsf6Sz5iQc+XflnPtEXJ//LGk4T6x04saxBGm+OLdvNK2f49S6nM8F7NJpVqn3W9y8WzT36BrI/ZkQU7Rnungzo53PndI+CgBQpF4ssqmLgIIj6hWnKeYQW32QzVTsIpIbNKCyimVi5MSb13yNRx1V0iCavncW+wQ85yKz/SbXzIakKefkNDGgp2dXFro21lYCjwdxR8lojrc54su8V7yqAKdz8zjj+PbVFN1YIga/KvzP3gdIluFGmNtAFyRdJr72+AMUed+p5MQWr5+1TK4aZt72bCDtQ1MiP72Z2xRf84ZUz0HdgWXr2vUlzmwHl7TJpMG+oGo8kzabSkvwMhA347PQoCX/8VDXZRejKoGJTk6qb2oRWP+GA38LAtoUy3MhrCaDXniGs8ulfqIzJ8KNMZ9INlwj79crO7DNDMYAJp8cCIQ9sd8Jzki0APz8088C9zBo5kwAzxoqvF39xP/M1+xozE3MXBh13yd1XsH79u2Xn38xHVQrny9EZZpFDyI0wPrce0HkyTkqstBJl1DHyXzqMjLr+ITZ/ZofmsyISuKe61YEAcz06bM6rXoMzMaOGpTZhjI4nNnY4jq4MUXCGzYIx626Qh1dDvI9LTT5KzMVHIRjvjK12xb+DXbqo2H6vq1lCq1oTQrfvfvtc96dxFm0GTrrh3nesIFcHM+KJqKM+cNc08BHEwACNiOvdzUjehPRGeuXk7MK8iAjknhXcImuA8TxfRNMQPSfPm74AePSXlXb76eSUWKlTBN0iqqnYa0J53i+Uyu7QavamRWhk8OkWyDcgMWxBOUcm2t2DKWbqxwaZgxhZnLCa35STekCeM6Z6axjMVR150AqDWHHzStv3quOo6PF5SnKutZVgE6nOdMxEnURZQELGrrD7wE4OG378sUChNG326plSIjvm2eJa05HpFW/djzorOhNJTldsM/OpU1J5gRadYgzHQzzLGwLulJ1TbFVmRlN00qhqGdYTqz8OJlv7MqqQUXYmrfaEMZPzsl3jD1I2dAtnJpdx2aIKmTmYbQ62AKyy6553vk1KODmDS0q1aoLuPvIIXXrZvc75DMjKtbDd+uAUQ/E0ccAXicO0zM0r8AiCn+2XVTIK2Ne+aFpnaLqdBFDGFGx84AZ/nEPsebr7ThHuVskli4EQpkHiDWxjcD0kyqZLr+7Ik3asX/++ScPx2bv5JFfP6Wbc7Ds5B4NvpmiCgbUHAh6aDFntQWLD9mRYxSd3XaWnxZhMmZSNizndJbQCCub380DTtKhpDX9bfBtrBzTmPsVwoyXulVf4mEuBxbqWCd7ls5EjWeZFhk3nL41xta6k27P4Uth79EIxormeeJ6ORe2DWkeaGRNaQIRAUDf6HLmz+YoVoSgTLL8fOekOeYVo65QPIvfDUXFhE03r3jYhUIOio9ZOOZ4mpvWNRAZ6Y9K2hGJLrl5hfJE+Afnwoo5FlEo8VmsnEmgMaqlUNuaZZMSnL2ycDXpAqpccGIoB/dW9cEqHqIIcvzqNqfzJPGd3sx48WWys5XjNcGNQNdDCH2JS+gedTdzRZhWkT5OyQW5+BUDCQFHT+v0cE4Om8xVy30OBka0VbMUp7OEsDSi05SB+/iPYx4pZLNxlMmXQliTN9wYzSSKQN5q+GiOZKXPlcQwSSqNQkrhny5LXjqPtFJKMmG1jM8hKxB6ZWhGvSI5Ap+wavDrrcUIM/ZagtgyZhVdhHSx7mDvXjJGLwhx5mgjLsjFzNXy5SKozQDDqzriUIASXLnp7uZ1mSSj6Rog6QQy5z79lO/TsYEiQ0Uh5qi6QlFBE3Nx97vvnA5U0BBzXav5j7P9ThTaBOfEOc+7vyZMjmIcuKvbBkGtaB3CbARVodXX9SrMJxvkB4uHTlNPMuhE9ORN+tLE9gZfN54YkvbdWJv5iHYjBnCY9XyGRN72HGLRq55lHUG/OJaqrqlu+HWGrIzNTgDlootx4CaJMGGSqrcSqHp+WPUh97GcewzEOpDb9UqMzqs4RjFWhlyQ5qCSTZRWnNzoYaEChFcCZubnXskZewe/gWeR+58li0XWKI0y4hjnfepyUXfEZ3HpWVMytcaBjqvZxWmSMzei23KYgTqcsuMDMaZi9NgikD6KyjM8yJzAx3Wl0pvTMV1ARHG21bYkPyF3FGnr9ArzAUDG9NRTeSmRAdj5qI+e7+uIxP+Uf3PvewHChnHQnkLSfIx8vl36oGmc//gmuGNGRq3jQ1AI4++oCaEgXGONn+pzp4KW/nKETHcCCGZcoKw6jwoTnK0C32VnbaSnsKrjqvTRF+USE1iQnMPnyqvKcLjCIdGSVDDRhNGER0dSB9XIUkUgYdQ0MW7v5t8N0lnKdMnn1gydfGaul/TonsxzKqvu8eGhczLf/zZA3qLV86oZmHQ7U6WxS2H+0k135GamUeRvKrjmtnoTzVPLiiiFpcVlmNvsfmWhks8AfXzw5VZBY6urCheyx1CApJJHuu1JNjesb5gzGG/zFHWWx9jviF9jaJhuy90VE5Wpm60WvdBJ8VtaMJOiTLysELZGaZW3RKrGu+QmuguZazvB5jfBbHCSx+E5puxbnFbRHThS5FUyEXPQv+npNBzWq5pkelVXAsrboZOnpL1z/+ayPeDHavyu+xn0LsnjcK4Lc6+oiUw31ZjUhuGeX1UKli1u+g6K9R4r+edi3J0b/emmhEBXMuu1cVstaa1gEhWXWtKRcWmvsAwFaO4uoXVE3HGFVI03tepyQ+fqj+xJk54oKgkwi3y2kyY//koXfZ8addEd+yQPvxbVcAzOIqT1tdydDpUZ18o9HysdgTk0uxGOaFLGTEjpbyMhG6XDrPygKF4+YpN94/b9h2xON7sZIq9V0gcyDhox+rx3Ptx7ZICa40CnMDO72XSbmL9YmMo4iPHdR8+CavnsrfHeIs898rvWAK/eubeyrySec3F7KA2AJH/qTJYkLRQtizhlko7Dm1jzfDimxivOFNcUujOQhzpqTRlcZ5CFU/CYq51zczWbhZwN03OHzzc7Pm9c9qQhQPNkTSiIoyHOGVWY900QleUhywPhLpfjxKtaN/pdFGPe6DRxIJwSo2Muq1jW+K4R2JXpQhCox+cagpHCHzg7ZsQ/Dj/mrI9iP91ayTPV0a0e9UEZLaCydPKEXRY1ZPuzE4DGlKu7rLxxHuuV+h+Hx+HTJAs4yj7rx9agcSYxD8eXmjAdr5USiVqpboiW19DCyK49PV6QLFgzcb436nHj2u29jgK1uwMwl2QGkZ6RxjhLBU0+Y7iDIcN9Q8f0+W6cZ6gM1Pi3P1BUc5kM5LltgnNwmmfWZmJ89MpwrGkjHAd+xxivSGKOv+PeQ7PDyCh/BiTd13WjGucwhFncSqJhJgY4u0lHH33Yt7/MJZwRJDPbpwALvSOOAm6I+HRwrsCapjsZiWNDAJOZPBWPOPBPEw7JPDBmJtlh+QKA7iq1rgl/1iEMxMrtHKcLxieGkCCFcEq7Fiy+0pN3zlKTBHKaOshscnHoBr2RTqtbitxBEvyacuYU7Nn79Ey7FaP7rCTP7+NlRTgZv2h8ZXHVrGjxiXg+1967LPCzPBqnM11zW8s6B6ob01LxofebegFmru/GLMfefchty/QZ6x0foK4DI6RURgj04zJuXohNbuJJYnzyz4z8xlwRCmk2NgTMlCbknP1jM+uYvxbTCCyTkVzUValareuFNAFfXODiawZSQLKg9iqgmVwUD5TUxRLmuQLVEIuNtK7RjqWW6aYtMtEyAjI2sq/qI2d52C39kkxGIn3Xfm+wmoZGkTJddu+nkYo55KjmkYnGJVO5Y8VshoEmZf3Kt4Q3xTWstZ4vqQzlFZdPQUPLUKHYC47EHlMpmhSibIkNdTlYmnml80iSkVhiBPJGpmnx43Z5Z9G5s2PCUqLERstgkSar48d3efcfEaHGZYcEYfivimSuJHplHDTJ27o5CEGxZlyZK4YTa1XZ+oBDmOJmYxxS1hMIzVuzEQuP8szQJ1C0BIkA5L+nru6CNT75LUyqZEAh7LZczQFZK0se3WLCxg1U3uZ8diWEV/AR5GcanU6tt1v1Bq51zhgQhC2g+ApJpmcdnd5tkb8TbyfGEaqTR6CKeRAR8yC4BNuVSC4Jg+aWJ2c8V9U3fjGtyI7x2euYsP+v0TGXvdlwj6PPczxOxc7i5Vv2Rx1Icx4/TdpdEUTBspovkzytbjbg5Rmds+WWBMFKUb7kTx/Fmdz4ydzMWMxODZUonF3TssmByW74FNJac+8/5rmTU1jXmQQdo8cf7wDaYFop7HB9e9efv3/+/R8fzO78//ObRcoPPueaXbzplOxP+o83IfPE1MCzDsaxc9bxuAd6nBCX7MrzcIKQdDUcboPqEiVmLcVntKuAmFwGSJpEKX4oL+CJ6PQyJtizOw5mTT6Ee9m5IiKc9IZKIowB4AU84okxl5Z23OUEJxehXIytfFwUrXBPT/kNDlen3sqNM43dMd9qpPzwY+7UNqj0Y1Voled3l/IUiIeTPvqeIl8Fkxss8JLD3rXI8NgsoHLL7DpqbabS3Ss4s6WRIhr/VZGAufbrf/7jkZ0J9yNQuW1NksqENa0MViuoTWEyCj4B0gvkWpk8kFhtZT6Mb2rlIllWuvKIE4IF4fcPPruHznChJ/URwxTOdka7FuPBCB4w74EXz15tHcmS0Uf4F8n1niREijZfCnqLI3me2dFmpjUMKrz0UAix/AxRI8TkD8d0XQS45UzHvz6hlI1tp7Q356DBTI4aEhWvjz/Z8f2YaeCdI794mB837AxpBjx5ErFMVeM6CZh6blhwqUN6+LPJfk7UWbxiwwbSk1frjEwAkdpRWjXcee1y0rMTyPz1zVKWiN4RqANZIzIas25Ab3R5a8stDv9MxU5R77dqFVg+hpIRkG+oE3vMVT1uNBX9SGbuW+XtsbamH/OuliTDV9KtsZRXbocJpatWlsWike8rDyTIgfcxDbuGa3nariQjhGzlgzPA3ExNcmolHXL2lDnjS0jsGzB2KJ2cwvzzy+d8iXie8s9VJA+5mbh843Get4VmY2FyirQ5P3v5dUo8IA3V90+BBn5C7gx3kcTzdKfMxGjAMlGT2G61RJUUNZDMADLxLYWsV/rMOySe6U28pDVkq+GVOFMkNovFt6/6ug+85Iaj98mT5w0muJb2vFdOPRkjLqsAbJzBJkB9kFzFnSxfeaPivA+YbKT74k8dS5Z+//L5vbWqD9YFSq/wMJ9ryW+7RqwROOz18d2HYSZFOVPFiheH62O+uNHS6/vm5oIB8OXzbwIXhV6wLzFbM4K7+sdRC2t/frOPAOZUnSnTgjAX7vTPWMg4SbZ2JGBBWSawkudU00tiMhw6UiVhgyrnmdwXv+UVa9Cb8wS2ymTljq2c/RzJ4Ex9nDTV3TmtD7WKEx9BHg5JxXYMfZkElAhkKCWqlanESs8wcWABB82IgxBPUubHkwvV6Wq5gETmcBWivtap5mzZgcs9/tNS0GQy4k7xzXad7jWkqbo55ZL1h1TADQUOV3eejDmLhCOS5aEl1cCsFgSvyQztachf376WEivSb85lcu3eWT2cbNyNMYtZVsonobWby1v6OR+Cq6GDVmsZMQdkLsWcKZAv3tSUnYOlpqmL15kYmUMxnmvyDFZsX1X8N5DxjZiAMEH+SKRmh7WahGcdaeeG04nBZMS96hL86EYtEcU/x46QfHVc/YxkX55+TW/2Ee24Hfed7Si9JJz+CmaM9N2xIZSf6LLufFewBoJIOIHM9sO2wd8oJEuFK1RzhK3XeukHTAR00wlZYfLJk6cEM41JBMK0D+1/Sjxs41+//PNfmjyliOvaRcnkak4q8+bwqiYjgZxuHn8nYRkK7lMIS1oEe2GoqbEYaJxPITiCJDFHMloD3o64aJeggl4ZAvqDn09uQQ9qCAOZypzCQZwFC0V6x2mqjjMmabDoWbqSiEuTkTtxOkocSTStQYFdhORn+xWqMIknE1B/PjGHYwXvbzGRn29gyQcte7Hj9qwMx1GVsDKaxdGU0Lc1zMrgZ2SUzhjJSArCK+BDdxTea0NYzGUDPz6QJEqx7ukEICLaQh981Q3fbAJcJaU4xzn01gTj9fn9TD/LMbjYifZKDLRKTTJemdinOzMhWk4g4QMinGDRcZB4k1Pf7sYiajEYqcpESc3kynrT/a08suwsEIMajxW0Wsb0gntAYkmPqZZzZFbVpwyYHjonKx+5TGIlvumd5HBqjDJkydpfNjhD6JTHDVOuueeFliRZOVeg8SyRjxl+vVoU8bzQevAE8KQ3Ynkl/o28Gh1ynMoWweCNLS2BrVm9iJ+ureLT1LYon0Im43DCdJ1rVPUvXbPPeMo20wK382hvJGWZy28+51zbSQFkT67HylMuDZQbY2NevksRzHGS7eo2lpy9V3W8i8BcVU0PtaApdi+s8bvQKOIMZAHOBD2+o1e9WtGv/Jo4No7jOa09cb39hcWAwg8FkcHjUzV9TFqVMpkBwZ0mScnapnEqFi9MrReQMI7A5uWa4JBXuJZXUx/McvBn6AqPcMzgeinFSD8tYarsKkQWvA3HqhC11vMEYjtN61rXZGQ6LnYt6GOnw9F0iMxT0JlRDs9oKFg0FiYbAZn8AdqfAxFP3GWN3TfY09Y/pP11eo7dDYge8QWZAb2C+do1L2jNS4wGp2JH5Soi2np8aLfSimL9P6mbk0EyW7bkPt3X7iBuqAz1Hrk90zgPsV5iLRZkQCgUtYbjVRD0Xa3mXnJVf6a1niqIzvXscdS5mmStU+SnxIlLExvLQ02/OZmQe8Z4ZOrMxLut2+JYwwzBj11aNRpz0tWRE/6TZHSqCbRxSUXDzBoWlfCV0PoR1HoBFuI8wJEZlLNFYJPzGvrL3sp0ylVMt6h74NF2IWItc2nyGKorsffI4OeZ7adKAD2V3vLJ7cUYr6OIi4a4NBmFLs4QxqF1ZdDK5aOtD44ELuzcu2LXGQLKudNJ4RVl0kPBN2mpTUGeV9WaBax5Z1WVlkIM8xHOqL1rlpzOiiMZTaCi88QQKx+y6SMwZkJp4QIO2MOvSlrO1DtJvPgRzIl+jkTrKOb0HZ2onpIxmmt4mOWtqVJYcQHsYUYd2bH7+DBkqnN6qPWk74KpGwE1F5BjNyH6z79KdhzbpWnd+bn3SiRvaPhDSFQxkx6Ou5QDadfTTNpV1I2gt+i9/k0G5Ch0dmR50yAy/mXCnEXH/qBpjtRbGVSPOqi2sjRn7AewmHHojUDfnh3Obd1qQBo/UHBMvziVnbQYE2Z8rpOks8MIrazzmWU6fau0H5qPQdqD2G/1PleS3qxuTVkegD9nWarNQMBLNGNTseDmdzaxh3GSqbOW5oTfl/7rrs0Cmluli84t9PjGu3RlYtyF1ZhtyH2idH0VhjQf7CqlZeV5d6+5daL112BpNgif0ir5O5Dw/5b8N7ulSPr76Dd5/QJOzMdynYuDSYKpeid4ZmhHLOG2Z96BIrCmDoqzOdBUgzkMmeToIuesljtuT+vkyUx4VcdhUiH/v3dYdCZEYsocwpQIyxQDMzyPVyWvPDJ5k3H0PJv8oICojj/defbqNwEFZ0w08Ik5osff8apXqYql8Nf0xg9eu+pM+ghoLfvtMPlJvn+Xd3NwFh2K95w3j9DRafcHqFByMI5WKg2z3Ub4v23BLfP4oIP3islYfVaD2ElhY992UFI7G1nBHi3tEbsBoCMQ9ml6GvX+BE8UU8TqGT5uKA0txMriZToz7SkCFsJVf9jBUWrYsYEGc5GeeCOQRL6VjLE+YVvAm/MIZG3KTIvD08+Sk7hWNqKob3jcAZYooHXMXGkAvf9O/zFP5glwBJmUKcYBUSSZ8eGWR4UPE08LEfy6hRnOjtOtIU5qf+3fVC2m1ZvzlC6mjxYlrjxvFwc2H9F7d96dbb8+5uLG21Pml3LDf6BOmPNnIJdeNX62rMqcsiHAnF2bxnJyKYqGTBIIcxdKE6YjzgpJnJXRjiMwbWIIT34yF/bo9M9UHM9WCHOsCaXhuU90OY/5s+BNYIrsIRwxiTluwbp8zOHMM/jcwpzR16MEOC31/UK9mTsm6TTI2R5kA+TlnT8vRLJylCNkXPSVWBa24Zi3WXqjcEwnA+cwoxWabzYNeEf93oLJCEq97CKnT4IX08dYI+k4zuDSNokIBSyfecyZNXuD4ZTpDdYARL5/i6K/e8rmrZLOCFbvExm5PRFGw/nYItGXQT2Y6iMT9c7kQa7vOcZ6X70BDLafNkt4yVgOcU61DlUzDUp85MRxpTQmdUfyl5+qesZu0Wa0MrXSWKseLcSaBJU1wmuKtYljKubLIbTEj0ZEpKteYwxfLDUasZjz8nfvsaYJiK7O2tSrOkNSfjhZ52uo/d7MRDivGDs5sFqE3KviNbfW+ZzFegtgMi+oZ3wYU9Biq1NqA7MD4wmzHZgeJpjmCCtmROMKmAj8SrN2TfAjptWm948/P3zyAzNZi00usHne+K9/9CeIgp+NaD9R2FtRRnzeeXx9aa252G5k9SEGTlyDXVNXIRea+XGIJWfPJ7Fr5bLEmFGTdKyPcVVrUvNMbZxVR8B/wAlmmcuf+IQ8LqkmP3WUocmnuWXVt3cJL5xWOhZU18PWHRALBlNT73OfGw3zezZ262p3+yzzu4215YkiBGLXsKp3Ca9DI64D5G/ZYuPocS0xWHrmjyMmQDvRt2cLC0FXlnNcNiVXelXrg/zMK7oZOxN60gc2jA3RtOVNtguVenO67Cecx4qWjC2pL4eKxkybnaF6Aog8l4kF5vSN57Y4pnpTJMbo7hVcTnYmzbcMThcgcZEWFESy8fU+m5qGuaEp86C2yCDEnpMf9+ZGmclCzSE8MBGlJ674HAe050zqj7usWsNcw3MJQ2ZFq4Je+znWHJavFMGJE5XIslX5mO4I8WiIlt1djZP9RQmKmZVxO3mTq/Q+XQLgFEDLvFNm/QhzrXO+DpNP6/JT+SCXw4u8if64zcNyzlBI2opGZH7yg4UTaRJyuvWODfLxYXafLoDfU2Ns3sLPAC2rXQsy19uzrOhAIDPK2/Hpkrd2/Pr//j8pNePqYO4OazrCTz/OUH3J+FyJYw22yTj3eXA2DtdEGOyrRfyrfgCxHkPzcwJln8P4jpqwriLCUjh5dhE4C8RxwjterSxMwsadHOcmYcV5NXnVLPeD3nqBPxXyaGVuIQJoa1o/2pL8IihardjVTnjpwNREABO+KkJTMSKjS+aPJitXWwn6hYW0Im6oiITnh4ifZ/PWis/ob31Q0NM6ZOBYYd/9+OHXf//7x5/S5fNTj/M85vpk2SxmZDfY7hwyJmJl5Yzqk7rxtSU1lhKKeRPnPfVgGvfMSEun4p+f81uEP7zLN+VzIAK14kvSPH7mgUBOOtPFOotByJmKsGMizQv9l28U4+eM5l0/NHekpZ/1IxRdS3QVHVfyiEY8ensPTjWxPdERa+1Hj9fN8329XGx1ArvZcwjI1UpVJpt86stQ/Ky8S9qYaNHqbzzxPJEU7ZMl/fLJPEXRyZN1SWlmsqjbyeTRpX0balTd1ml79ilZNW6ilpzgJ6ATY3G6/keVouMNP6sD5rY2HVeqSXJ36MjgZO9Tl4LfzV1PNn/4wsv8jkE2IDwRDkKW4tIzp7KTItznCjxX6OkyZ8z8tqZHB/o0NeT/+7//+/e///3Hb7/R+vgpP/SZ77TqTHGEgCMJCxm+eUFLmQy+wsqsp5uW4QZCxkPbmkSpSZWk43BI9owatGk5EpZ0AvtMniqmyW7iUETzhzyBGb2KOJKgKZ3WRSC4Rd6RovLt62fVeUIMB4IiLqvEViHTFp8MwMzzKTCAILoAqvXdgUPqwhwxYQEoLKkiNCEURNw8fXZWTerx8WV9wRnaCE1z3XHCjpwaPljVFVpT9OFEWpg1exJdG3FsYqprTZWJ4sDED8f9UgslCUZrY3ZIkpGWObNqQH1zSuOK7spgnjPhkAU2/JiTkPs1Pk8U7OXdaBM+IIE4Li2cqpPlgOAkjlhitzyVmOVwsuiYBnlDQy1G80GcZNad3U31qMSNIjy5Sk7qc/8+m7KCUw8zEuk7KRBMEDpzAo5myD4fUVvHvVSeUvUjMF7ceFoPJ+s/wUwAHFH3bQMc3HScLdGc3yVk6bSmZDmokVTFJidhN4EhlCOZ3wwXgnFZochP8agQW0KDULRBVWwb8fFppV9PdxwtTGdHo0KqAlijORd6clLSH6ieNYKfMm9LZL9cGTW/fOVovdnDxp2xmVmxKLI6OU8yLJu3hNnyZuh7DkDCgc3vFWacOAX6Bj5MsMAVGvgEEcTwd8yJ5DSlO0gKak3DjE7Bp6i6VtUVVYSjplfOmJuCkFeIKZpgOmKy6DgrmMfRKRO9bVPDX9MIxzMbW4dyl7k5qlVL59gJe/zZmzxkhHIxEZjK5aAJlJdhprO+5peT4x4TYlhTZPJrHy5UHVIGRayOOXukGzBVRUuLuh1OvuS1G65emX7NtzmfOyHZ/pjFdcjJwX4w5HUMDnvwnZXizfK9HnXDha0sLClU+DWG3AuhDiKZ6JcuaPvTg3P9kr98X+hGY0/4+YXh/EC02xbZKx3ENDkjnnGf9SdDhx3LXR6wFq1v40q8C8Yfn09oJjP9eRTdU/Kk/Als4XUlJNz2Dhd2j7BqA1CNL/2TQ9aMM8S5gXO6wMX2eTsNLzo9FO0YmGTWr8SRjwx6W8622Gm0HvQz0sWmnQdThR4LRPzx6815wyyh9WNGMbLhkr9VS9NeXZRzbyjCeUdSBLIdHRnxLlVGGrLLOaEWj8Pmb+6apRCotmD/sB32CLYB9VjMji+fWbYWfPmqIzN+XEa0xy08hclOJ/6C6Zj0KLnzgAnkvGkfk+G6nH/9Zqf2qZ96+faPL0btlin7yqD2Mc71ANhgtmx6X36ubJ6i6Q5+vOzWW3amxwGQnUsfWlvTjkOjOwLzEmhzkKJWNJCpjCY2r1TRyqxMRtOYqnzrWt1+bFXTdKlMcWKXmcm/Ns0ms0Ligl7oEY7zgQBjVwyhzzaBL1qY3bXhgB3CFCWIXYYKeKLSpGASHkFRVUH88ss/t06Nw7o1x3LjcwlovuT/kwuwS3R5SRAtrfMNfhJt7Fq8EDaukUjPZQpmwEUejzyEaeEknBkjem7CvA2aOZZhR7N5n0uNKXARWCX56E097GfMpfGhG0hiD/pTpgr5YWTioseJ3Ui8tV6xEfHpKSKK/0+YCXxA4by9ocbNE7twJIpYzxbrIKk7zCYKdnC8NkCv+Rfw2L/8h6CHlKtc6FV9V3kbTuD40OUJmcVxxWMojeZEcbhVf0SSmkuDT4oy/5uypykD4BE8IVTHRBJOIjriT3TulRnMGwwdUem0wppLLLqf5IfbmJElQTnxFCWHOlycLG652Hf5uQyTjKHMlJyMVxWiVooZrkmtUrECJS2dIIQ11OscomsheGbc+DQQjues2GvGTSjgPJHigbweqWid7nC04ih0Z1drRvNzT33EZBZFG/t7o4PokRYoAsvzS0vCVB0OAVDDifPy8+rN1AY0vuPKRfQd7QSUgdppcx1QrhqaFE1TQcRYzkRv5aJxaPJwLkHeySvv6eQ0pC+7eiYqvlqDbDgA5hmc86rdhpTrJlLXz8SWJGI6G5wPmmJy6tMnn0eNw0YYGe41lpwYXeTkU1TPQonv7HOGasZKzCpw6nYOi20hBN8DqKnkrrYx9og5UedleuE4CAe2V57QYXfXQbnEyYmUB4LVKojZembaW64KE8zlymBPjlKSnZLJnpVmppPUZmOYVvhIioO9bSPqXKQiGM8D5w+61VrMO25krC7ZQ3nNnOPx5NwnU51y0AoYTunxX46ANejBvJmQDrgLJX4usrTqpa3IyWzSlh3cGWl5h67ITQUyzstCgktJa9KYcOoCNL2TBbef3UsICzSK1vIJxauThyDEAVDtfaNIBmLu0SVgMMmUHqOYqdi1BjBjw4kvStNp+OdjoRkkKQR0OoQPH4G4WfNN60YmKIPQTy/E+xbIt3TPlR7qUiTggK3nMtlz6REnvVT57Lvek7sWBGkOyfeQ44rixLCUduh/19TQkr0Rzc8EBktbLCvjO96qVmI4/B9tWF6xEQsNPUC6408+yzmJY+H5g6lZwRjhOObryj1oMqB3869rRxzaepSR9zy+oWm2aOG/Ig98xq+5vxE2U84DzXA8sUoG5Id+GbwewqrPjvNnZw8ggx2z1ZxPiC1qYh7yzbnuBPgSeLpaYz5t7wQnxpsMaAvhDLfqzgGekK9wFgBWjktOkpkz506QcUSMcw4ElGi9VuuxiwgIV5IoP26w4a+PKGp6bGEOEMZMVPCx9CQqMk3XUAKV/WXNPWkMQhryNUHNfza2FMfXDfFnPjzwkS99ZB5hVWWOEUBX8ByGM/6y5yiPODNwA4kivuUGMm8TdWAP4AusPi7gsRWBObBOplL8GXW8JoZ2PbxEE5SJZMGKPI14maTlRKrY9W8raq3otDLsJ7njoCKP347YWEmHtRAwtAjLs3Ury54An7ePBlKbJ6ie6uIAba3U0dfWzB3opsm987k0FQId5m+XNQF5xs/FGcKqV/GVqWkOcJuAkplVf3jLBg6BmsthwgTusjDwHbUabBMrWCIiqbi1ly97uVgIhZC2i46gsKob1ORnfkzQbuG5JKZIJt3WcVCkfH/D+IRprTMIvGISuPxOojP4iM+EVo81OLY144p7X799ZdcuSfTEgMiJNcI/4LO+KIbjtNIhkit2blLKZVE7h5j8xqtMjt7pachAfv7pp7BUuVxDrZ0OyGktHXGGiKY87yQPUThn46gD6C79XNrIT/HxZSStLYvOKhdO/FOOizgK5DyV42+2UzE0fo57Mj5+doIHM8+OT2CSpL3iW875aYl+KCpcKhrRlrQUKnK26Cc/TZA6rfYarNZynEu04/gM4K6seo8j6n8uACWMrVajme+0tFp1B7dnm8l79dGU4F11S5VKyzGkLwabKHiVtshLpBf5pO1kLxKDoswBFvfcRN/8wXOdBOwO12parJJVCYGyFBmZesNUkp2c0fHd3u59qIy6dhxdBHP+oPMrB3QsLnGvW6LuKQR+JZfhXnJsxw3gFC51lPyVXVnnI+T5SV1HkEPcsir+voKcijMxqV4O5sNzmiAoMZC8RT30RsWDFk47mjwQ9DU6W23P4ag/dfI48MkjtpxlemannLKm48AS1UAorlVTFCt8FDa9+aEB7prQU1j1z34OGfOW2bCycoKuqhVhUFR+/fXXqZPXyjxkrZg4t2lu4VC/RasyQ/s8umoi75UsvkmG0yS8eSvnw7m6AgLjp7DF7rNmn//zH9JWUr9+FLc/ZqktjmyuwwJKFH+xLByXK0sOYZxo+R+fMdJztN5/zD2L0F7PfYE1keH8aaXLm6onG822BAUt1yu+N+qjH+bJ/TVMVxn1MGYYq72qnhEQdp0JJqi2HWZ0aCxR6fJIKlmgHrpp7IVAr7e8y5HvqaMkQNdH+diSPLgykcZ8W8Q/XEe7JEzIAZxLhV0VxwVXfJ6t2HvzPIbcZM/RL1FHm1Y8vzL02lUSgSh+GnXI8m89y5toNLO0pSwnkemzwF0WsnqcVvns1/5QqJGng+SqG4GgP88oIBeFDHAk4GmNlyGU0jxB2varkv/2OT/7ZGTnDEqgz+7I2u1lMto1wUz2jZ92t43Zej/qMvxnUr1w9vW83hawLaosjOPD8YoH6cPDD8BMPPdwNWBuuhl7fHbi32BOh+Y5gVxtWGpjtCUe9tNnwW7BUVQdoY1/N1C589jBD5yAdRA+NEfamArTq5JcaAMhwIZWpS3HEPoyWZxROFthcgdaGUQ0WqZPbfYGQSEnsJwVZMGPTWef0j41OsWEaVjbrbz79JMfb8yGyP2jIVxYXoJV9d4cWmyzwgdMXkF0tJXTvYtc005c5NHZCOmn7jB0EG845byWxBgNHCEAykmPE95gcvNLxzRCK5RBzUDOtpmo2WzcnGZL4hSXb/vJPR+KeVclYyIJ1fXdg0XLjTDVswFqtpn3vUR/+EI1DjTIdAe13ED5wZsGettPxGFa99pgXeCxxgQrrfU6XcUfwrmvnPkXH6WSEUM7eFzrEOHAiLgdNVCMiz13YUSQei3FyjMmpE1aXMJ4PEOY0BX+pivPcExK891MNRV236yUSwMg91ZMS2uHTkwGchuoESVdHvvMqICabYg8CCtupLPEkK9eEELz0+tlDhaKS/lpRd9HFueT/pxkCNILp0HVq/QsJh8SW5bViCVMdjICmgTDIt+pn8wHgRVfgtY3yNK+W87dEAlOU4YJgxnDlPSyrVYW3PiQnMuPBBs1VQ5E3ibOl+eBFvDvf9hPUUUbEoBOx8X5fAWb0RIs62+mYnrdH/V1Vu0mafodbAZmoiFrFORd0cSVV4aNlcCgzMrHXgZ/rGfU/ekmWroIvAg+ffxk9ARJDk8ndDeXc603Co15XvAhA0e3/utf/3JMuM2qcP1NX1WAzBYOBCclRjUutFU8kYviD56rEqmw9aak+p1UcfhNNsniuIDc9PZBazJZK0R3xl4AFfi7LY6ePzi7SjNzzX3Wc6Jg6RYSaGqOoxFwFZJno5t1IvklRkaTY1yWiYohmJRZfl4O5rWSH2KsjCPP8MkPB5FVqZNHq4I/7xETu775zWT0xNa0I8lbLifn9B8/ZKq1ROCJgqclAbqxAAAxPklEQVRAckb4/hqZYHzOTj9N3PAXg4e0LayqGXeqWUkzl+LMDk8CgQgua2W1EifL/Z/v53wpsdViVPKtgllNIDDULVvGiIa8YijFMcjf49AV+FypVCUrg+LDxllkBjX1gGWqZPEyYK9S1hFdPMx1d1Yoz5fxjSpzkV26DBisOfZEcWLJ5FdmLLw3XVxQD9occ94L9OJ1rCZ9Y+vGq7r8mIR8KmCnWvkXP4AxncHsiK8TE2k8jFbXhAwONElEFo3H/1BHJQSEGdUxXsnLM4fTfEuemzhzgQw26+ncPJ/RAufZiXR0ZQweH6poaMXzp4RuHhIC9/pcJFpJmppP6rtXtaomHAVRmHXB6DAmlnXwCeGq4KAd+Ry7DXw4tDYLJuyIY9BdQzi3aEBrggBNGUdV1FOZ8ATaNekgXpFEUCEgOcnOxVUdfReIiwKIptMyZUVF0zzQdEHQ36m0X27rmuBkwjQR5BltCAmV3bS2h1Tn3kyTHzETjhU7azMtAkMAEg9fytHlp6+FSRwpUe9FByvyMnXHtV4rk2V812Z5e3z911FNzBlOaiPv6eQP/Urc7vt6ook2Z7gWc5tybDyFR9fNZUmVSqbBM8JUx2Q6Y7TrQ1YT7IYMjA2xLfcUlWhlm5b7LKgLBn4v4uKXhsuRUXu9oFU3jp0hPrKZEUWNkoGsw8QV6w1tuuEbSJv5dT36LfwZERNKUFJyg7k9CGFsRwjxcQ53Wa6Cba6br0Z5ZL1uCHBUDkLQMywd8ePY00er4lsLsguxWp29TxC1VoDKzjvBWbkgrCrA+zcHM4sWSyRVr3ydzzKP061V+kXVjQjqiWGiz3GbjkAVh8yKJF9YBjZPyWQT3nJbERjkKa4JQRJHaWvcvtXRdSqLCMkdZ1fr1Mc0sxSw+DgK4pWTYVnPr0CcrD84CrumwzwZMuagHGedABWtc/KKZfNloqorsz0FcjhXGuJcxLFNmCRsRKdi/Jgx6hRTb5/RyvXQM2i04g/WNo8KescxRa565QmjNSH4ubxMhhjTLQlyyIQX5+TJIG4JMot5vZ2jGMMX1AyxkjF3dRoFBzAtSP1xzVxurVA88gCp8KyzN7FsAmcznvmUl+2RWKo7+INiyShXKz4mbXnxrpxq6PYifogsFpJY2AgXbkDdpY5DERq2cbG4AvowZ2WGYvnBHwwrBBSZ0YTAj+lnVKm2/fS4hSaKFYtkZ+YUr+dXILDpgdNlMX3pJllbhJUSzLsMmLmMpSc5Tg/5daLKiKziatGV7vmMVsZM20Uut/kgq1cDW15GFCI5T56DkzsMT7yDvdNxKmAjD3z4Tx7efPDtGhbc+fa00l0HSQfJOPcUDwAnmbjtrzsq5tubYqFc+pnXJOfMdQnYJuyaxuencSk+6yTO3DZib+ssjg8BoWlpvziq42jFXBmCo6pWTco8R4yvCaEKefSOV1cTztIyFbRC3hFHORMMhasg1iY7iKEPCNaK3YQmSx3ha56XW8gwiQ0NQdJNOGImtqPqWqc44YlNBZ9paLM+MU2YxJRrFKHgEB5/nKwgT3nljxd5A8i5UPC9mhu4e1NykbnkPTgrTx1YkzM5Yuq50yx9+XHMD193RnUHR+tuoBnjnopxu0cnZcSbD7nz4CRIy2KTOZCHnTMW0mlNFP/dGg5+Hn6ZZG6guClBADvLa/qlO18Po/2ejZU85taoyQm2mDjEEkJs5UWCZO1wLA4EqEmTXimV3jKgkzwxxvktnR0lc1KrvjzCx1DtYOWqUDmrCdCZyM2sYTomkjqScKp4mwZqqOyzadQfTxpEbsCIifZgdnuHN97togprAdq8DCk3aJ6lX/OJsQkP4BPF9c2HCdwnFB2OnEQGIoSc1fqvGUsEj6uHqPXgk2zU4Z/kWBfyaQY3CBDphVd8Xfajr5D++oZ5TJiZ+vMZb6wbTnvzNyjJXf/UwTNUWE4/nnDq2a0uM69W9HtTkj66KhNTnSSZtY5vQo1/BWQJvYm2ptdJ99OnD5aCZPJZTAivyjGFyuYsWtMeG0KT18S6owIEZ0xiCppYdnfTHyhaw5qniR7c+FFtuYFpRVMcnxYOevLolc1S/MGeD3+2MqMcEDkBwx/g0IAQcbRGDDkyLNJpqZ0jw9DVQkx3xMWxDqNXnRV2rxZY1rccSxlAwQzhxBvTuW61YIVTP3UB35JAH3H49GGzophLRcxxNuaadCvJQatQmluuG+KZ0bDblzud8WdrEPUFq31aR17UViJdkL2t0X+cBzhJx+XTMSoAnzmsKWJuxGlrmXDEaiMC6EId65FP9tLU0AKICdyZo5JrmkRhghbmjo9MQkt0xRdevbLQZsEWRQcHVzOiHXsan91h8jdV69lgZ/XlOGFihzdDqfD/TJKAdJrprN2znxahWXmtYjZJADMFs9N8AYcTKGeNBdKmDV2rlfHj/ekhDLl0yGGOeZoWUQMcZ8lBJ2nZ1KaXKXLbUSsO4rqNUMZBVKusxoWiskUnuS3ClZf4a04TQ5o2ZSasCnCYBBRuYCoEFMIK4jqPJjb/ESSj1nVj9JoC8ZTpspK75tJHGstxMaNJBuNJ0+gw+1b9FZgW/hxyVFTHh+wUQXfMi4ljK7V1gRMDp6IUIAjjX9/wiQ2Zcxdzp6DpalWEkAHRHF1n1qSqb52UIHkhvCmAgXb0YmR2euIylF0zeT/IJHxWnGRGorw1k9tDpCETxswLQhemeYufe8DJJY+bz2TPe16574+hKYOt4VSogosNxJPJccVI2nC3Ys752qzdAHl3Se84rydLVXHIOZlbeo1fGhJm/Fc4W7f1zgaiZiI5N2ZvptXxeDn8Bl48K0je8Sl+B58w+prl+Fcby0ONZSkhIwF18Bxja4kAmLc2osHoeRnlYLOLTBc0wEh7dU/3xJ7ArHd7OsR7rtKb+BIQ2XYZgn0T2muhNcZ8HDNpakFwNVfCLxM+cQg/WexrEVbl8MtJJ7rWqufph9SSGa5MIzDZI/3lbGybsOGNU6QE2AF4Fpp5QgXIStW/87Pp/NPsJWDMK5PfUfVRPQ7MDWym6RJTLj3Otatp+NNynADMyyEzE7M1FbnFHD0BR5Pxao2ANmJNRzeJPwUHLJkriTavM7EnffdgGiy3V2G4qvPVDwrdh2Xn6CKhPgITMXrIOApDYLmzeD799JPdYL5B4ms+lYomQ54ASccM7i49c5oub+la5rRiTtJbd7RWvUZVoRFWiM0NNObnr3lQG02YoQxNA8jP53rXspnFpE5mYppIGvuzPq3mqr3CjW6s8i4x9yzQv/6axzq6H4TQs0y2sV9/Cx9uFp2//GxDTCQQHVdnVIEzHad97UZvq6lGrp5jErDbRmBHONcIWRpwjEFWZANmYFv8iXvt+6mniea9L/CMm1iPK8H1ihahJlZTWik6biyiW8XxrnENnjnACmEwO9aLIE3GRY4L7st8JdIHvZtL0qjIBo0nia5YHRtxY74ZHhsG9V/8XnzTmkvUbniTE05+X169WouUxbd2esxl+5Bf+jPOog4QUFce4IqxGUV8nixjBXKSJLeHwGY3evoRdDeh6GqcVLgZDDl3CVqYzo3J3gidIahw0LWWzkVfTm1W4WVimyOTZ0sOhxwnXlYZ5Is/AQRFAP4wd4QTv10x3DfBsJ5lruQJhOKmBiixOruzC5DMlpELO3/wAc8osflpUmudYxccUcizQFHByTK2eLTNkiManz0Qc4i0KZRqv3N9ERJTNJHRNHVamO6pC8PS9v5dfpPiun7lERmhTUeQ80tqvtMp3/znqJUuZJjDX5z4TNNyXDxqBPBVJ7+IWFwVwkAm45GhxYUJh/BwVAko08JM6aLpL0l8j9ZzyPs7OByIifxQ5kfbMG5zItuYPoWvVR+Y9Hn404CIoTybZ5jrXkYZirrV5/25eRwvz4TJe46eRJYTXVTdyMPpxsOTUIfPSvp4Td6NVS84QR6epjj1zjv2Q1i86ccF/iSNaSoUJZ9j8a3JD9OrjoEfciyWmYHZ35Fc0yahANliPp0XgWiFUy0eGtdT10RkTVlxZmuGaxFJQvINBsJ//vbbu19+2cWUbzRLzuun8XfUY8IZ6OzTB55YDM6OmYUpfA7NPX6m17KtygmAM2RWcOyh2EXgx5l2ula0EpVmKTJ5wi7hSiyCPCtKnsAtM2GWE9iUOunOZSXhGDDKl6+fI/ksDfip9rRKB5TjTJNRjLeAPS7dpkkySIZL8aQ/Wvz5868TxodMPso/eE7wF894Y/r0yD//lZ8O0+S+TUy2aAKCCU25hoAoWoFgOidppYGcdXxVAkoEnnE1js6N+Q6/VwEg+hfyrNOafGyTXr2KpzPmxNDX6qhIL+9GzwxEIGKzLwI6RRx8YTsN9ZiNDHlMLiqIonUe8qZhjENXqMr1Z8KOIya28Grz+IM/l9a0CDHn1TB3icoBklyNb119tE5+Tl7Ty8+O4sY3IR3J152ud+stSZffapJnwnjfTWgJcu7JHBZos8105kx82/8zbhaCmQGGP6m+0sl/V5AnFcExkbL6JPiCJY7xo15gJ77M7XIh45+ImrGIvYwBoc03/PqXZksy0OsSi271AZkwJysbh+MGrwp4RlkDCSfP96Xrm6Qz6iLcE0N0lSmOZp+Bpjo3ifpWj8wyc0aCP9boZzhZckylhS/WhhtJ7iUpz+CM9fpwzWl5i67OzX5WsuRA4zmdC3lNxcjIn0Dkmkb8kjlE8fevydpMS2Azw6Ws2uRFW/mhhRNn30qam7e4F8iU4p2DCgFuGG+O6DVwGApa9l7lOQIhmC2IW6gknP5KGJVM0gIO9srP1sBvhqPY4mIcrbzFUErjK2cCTGM6MkcAMRBH1kcTIDzJ0akoa76EOHEGN6Zjqo8nqszwWEFoUubHqtQtB/sRh/YLjViZcyQzEl+srEkrMXxnqOULf7aiX4RZxGfRAjQVtFa0QgD+FB1fCW3xsy+upL/h88qIBChG3V+sNUkktNm1RWZfCgjzMD3q7R5vS/mAR28s9c6rAeHdwcwI7811O7BFytFw1JPGRJMQLBv0c6qfiXl7Y5nnC8pRNQOuT4cHo/fIhGKoasktlUw8Vt3sTVDJiD9timLDa56ktFBV2YNduVWUWP09G6gI1WSOXO3svV3Jn3Qfr3L+j6GsyJmCDIbjz1pV8dlNupw27xS6hurTWwYaaYwq7rv77Tjb1W/fPDEuwx4lzSP1+qL3pHKXrT7gSGZvQT0hUE8GUgpV/url6EdPY3NS2uIq8ccTaaQzRUkRo2b9oqw7NG0iuR3Lq9GxonjDV87JdTyG0RcGRFmM8TwQX9nrT4Tz9e0TdvQuIQ85FjrfBB69vNq5OfZtT1xeE0kYFLIUctZFszmfoar1CjzWyCe6W3z0zc6d3E7h9h8g9K9462bQlauF1qogyMBBdKZEUnVaI3BuGcJaHeVtTejvcboICL/lypxlbNzX45RvPLfJTb4M6vp0UXDMXtVrfo46TvL6DQdHnPCjDqqxrbrWsjuN2xSx5kLrhUVTuZwpjkNYdU5OgJayVk/Ga9IrqnzG54xqRc5haMfoywDFv00IOFNgEI2TwZiPKyXqwj4z//GWTa2u4uYkH/LjTf40luvzqiRn7hzpsJT7ycFfmcw8ucJS3LGNccYcMRuiTIXmf4aCcAbEGV5R3CrDNJ0aio4zXu/pLEzVEH259F0PAqtg9DJgX5wPvz2YuGyUHBvv/CSJP+SA7PVgfXh/fi/PUj8TEkvF5afRNit0o14HDvH4D4a8JjuQriIn0iOmB/MBsjLrxugZCmi7+ITWPsVRHQedyJaKJhYfQs4cW1b+St4u5oil5/mYYyb5uptu6HRdyqozoUqm7Bxi9JmATppoMZIcM6ar7jhkhImJT2bqV4YKWtmOxjVpfGjvaFKmQmtlHEdVx+mOwGHlj99z7wwHyHAgKJPccVUyE2v7cYzuZExJQRG4JjQpTJwOW9u4hBgLXhXQ+OhYyvtIb0CaIIjWzTPzfvKO49P6+uV8IzWm6uUzcTnoxTDrZIazRVATzpsD9Y3RabGvCT1dxwnPSbqgVkb3ByMxu75sO0C5ZyQwGxV1LcNbg/AclyU49Z97eRpgPtec86Jrfh8DiDPXW+uYc+w+0WM+wdlgyyeo8kWXHVjHqBr4GuVVT5jZttim4UeUcvyUa38SVgcBW5iWXJ7X4aYCr2/GMZcnsFpiPZoWy8QebwK8pS3Jm3NtibmkQnPuN6XTnahH42rKW46a8+ZpPvJJnRFCUGUsaC0vsKnz+f2nD30A7qBjzXL2R3GKS1L1lgebRzEaXbrAGyPA9SwOCUclsEyvSjhhBifHBVjA5jIZTZr4WRPN85u6xrQnQxlyFUt+YkS41cqTespEm5NYbzVp7u8qbwcUMYL1MEQsL9hIJ/4O+6on4Ruf2Zq3VD4Iqw5hzNdjo+dpSqQrT8BklDHMpWu0qjkFkIASh59iqUJOjAxJYo6TnA9TJMYKvurQajZzJIq5CjkxINbkqGn8e1wTNFauoalgAidwhRGjsy1CTbnMHFTn1o6DK6wNwdnCXcXJczfXkMvf48T1YzhtT8dIopu7q1IfR3UZGeGoaYr4ytag696D8/Yu1VQcFQmiS2ZV9IqhDyqZfZ7aRyu7rUtm8qzMkPlOUqG1plXdykqOmlmc5UsS3CksOwfyAyGwuXHBNeSlFH9iOfrfEpUJVOfQbQqyF6OPSwN5BN9GCU52FpY3/59U2KNtXL6GKrpdouSjb7XisBBWhRD8x6Ub3ZFZZz0Cr8zhhFMExC2vgInoUQ+h1I1tfv/yvqHv+XGXXbfqi5dty9Am7mrb5s35lNbMBUSWuo8Wo1LoYed0nTv3LyVZ6v6XpC5nqwAZonBebVFatQKBTTVrZf8vIb2HTQDTUUbzv5G+dtJwyEzM8ch05pedw5irXnrjmbdWHOAT03q9xdR6jxcZcQstk0tBSN2gqChkNnKAoGf9cghci7OiepkTpjXO0C5zxI4TQM+E6goOYvxxcjJcGe61mh76Pl+rOj2SnDAOYiZ9bQVi6iKfAJDuwHKSvJJpdY/p5aYanIEMcFVHZUmUwSuAwL/VnOGfzfB1ni1j8UqOX7w4fInr0kUjicZXJpb3GODX6PqJgBU3+wxl77UZ5d2sYtwFi1glBJ41epKDZSFn7Awk8+v0B/lXxxjVikPlQsV0HcvEyMYhNshMM05nKeufpy+0u9ufDVeuw0jmWxzcuOk+i35eB6OY2UFAqSuDQy+ZC2cuJeeZ23/lS2L0Zn0lLxgv+ckikSitIH3DHpE1mzN588ErCwqs2W7Om4/oxYEnHdk+dveaG231P/cH81373nK1hsb/N8L5I9o8epbXBuIQwKeMt1qieFpdWgWw0Sf25jB9FIcDiHZ7sooxnWCrm8BLMH46Y9WejGeoRqfKv3gYrYY7f3Ix2LjxlWnt+FqdodsKa/3SHjhhkh/T9CHvfEyexZ2oXnTfDG2KTXJPn+9Joyz9LRF9vIK5DDsql18rsZhEtRe0vlYD8YCMvs4jqK+VyqVrPM6PuZF24sQS0hqEilZmmxpCPJ5Q2Iqjr7TiOIqWJbHBJTl0fFD5KEkLgYs/t4LTzE5Sq7IUj75Q8HcmvHxN/KEofCCKJhxH1hWcS8yBHangz8qcV91ZhboyxSCmZET6w5ImCLMS/DwJ5Od4c4WiCkpBKBNjaEwg5eZOA586w4rdMekex3UPODpTqOe6TeY48cycRGcA+UOSGDBRP30UyaJnCjcbfE7e6tKSzJP4UIHYLXgdOWkMpgL/WSu5QdclBk7stgxBUx+YshwbBjJPF7jz9bfsQLOgyJ5VgJ4pJIe5pxPkmRhUXTKYkv2XURuRrOcJ2S+e6TPP7nlMRFpZv3muU+cQ/vlWmTg9QEzS+gJgwn8Wl9Dmc0dp4orf8avhvvNTdPycP/lemjyS0i/tS5jPZ91rNvgmS/GzYD3jMJhCOF7ElyWvG7gOhgQYE0cyxjOqHefkbVq11t6m6qp713Uqi+5mBmFwDhOhAHScOXzlIre9Oyzvinjc73ksUd7mEmGKaINBqXbUEZiK1qLl2lAVf56gceBPZW5fH4Z/1SczzCt/iUDNJNZcnyXoqrdMQZUH/PKWzT9/+ee3r9/yzQSe+fzw0Vs/EumoVX8Q8HU8edDh9z8++qhK3u5we8samSGoaqQICgft5Y22frVsvkrJ7ZGFdL1U5c9W+sXJDYU/lTFEpEwq8xogDg0mfA/RvoooJ+Q+yO6DNzdZM7QucIlqd82K5HZw57xk2/ibx8E60B5zTx/vTJtTepq9EO4Q+8Yrigo2FZ5nfIt0bxya4VlodlbX7Iu6PC6gLy0xscNnv0b36eefhacvjlH7GOtM76vmwUgNShy1Zn6gl6Y+WNtvr49dePxx9LZ6PhuZ57BydZssZSlh8HiO5LyqGyxbYSwsqXt3qQ+UQ/ELwAlSvzUWnGxk0PHcD1UmkfnyOUHky/9+fPchnvfDjngZqbKFQ6ZdlF1ZANPo2i3vLQ4wy01vZiUVgHr6yaJX+Xw3GQz3Ct+/64eE0+9BpSW6fscTyKUnOl2p9YXNwtfffstwmdUtW1KYey4uCZP8HDugtusxgmXMS+rihvn2o++J/vD1y+c5jJ8PieR3/pzJfUVyBpheSz8my/kCH4ju2AU4XnfzFUt59V1lzq8pSjHu6xf7bTQAYrfRzQ0hx8O+Tuqa0a0Fxi1rFATriEY4avWtc2ipWFp0CvXFyGagYvkvX2CHFsKHj97x5l7X5R/++pQTarw81pNUkzFf63a70obdLCPw9esXtsShdFrkOIInc3ICJjx//vnPf7oVg69qpsx/umjyhckBTUshkKyscqHjkTeS+3uWWqcmeGVNOARmA0cx1U14TE3MIwg7wmRqyKF7NpvKHMJkwpEiCjM9/n2ZAxkxDx845hSHM5kd1+qYHVC3GFyaMNOMTGxgV1FV69UN7SM05sHT0xAGMhXtVB56MSVvnTlhXydHmxxXfSsO9YTxfHQjOj0pyd+6E0KKwHOHPs/46ilzfXa1GEiXJsb7eE2+SQxa6Nzquq4ipHyGYu/xswIJx0it1bimJLAC6ptxitD+mv+rd5iwX90c5aaYwTl0Hs9K04bH9DRnWLyAx0r7d2502Q9I098rqEgkvVkX1gWV3/DQYW2PQHBYrHDG4TOYI/nQSeKjcOxG9e1sET/BZHyeAZx4nkJSOAZYxJ6iMRAtWYlaHo2kVCK6HmXq5ZzTJ9qq9efHvmtJo4nPOWqKsBGOJw81oRWH8Jomozrm8qxpUAjmdP7GIZmVVWdxUCTf+mhjoG48GvlLZuX6Q4UhsUwM1AqxS3BgC8t08RfCfMC8yDhX6zIJ5OTYAZPhOIkdGf4bBx/HwqQg2MZhHgJ0IGwjHLXOXpgdxIOaYQLcJICpjOmoVCuclVd/0FqVp/H8xQEyyREaRvCQLYupVuGQlFMGZ5QYPpq2V/qyDgw3sB1pZlj6OCf7t04qQtYBa8jkH6i1GOFvPYHFjXzJ6TmvvQWoye7HUclpjwm+mGK9AMmUT2ga878n3fzuxkvIUVRivX5U0gVs9lQY4VuwwDzBTqqhnDxAI+woHKsVtK1QOiMIG6n3uqn9VZBI0nFUdVRqLq6itsAFoQGMQKdazuNw/nIA/+IEQamkpMwHgHGxgPEQ1XIkq1Em0xNcV2fLA4u2R/ss501Ich0/+tlPWscloiKSMctQ11b3lUq5HD6rwMYJxFkPhBQlqhTM/j108nNajrwG2KdTKjoVIPZojnZsQ7gJuZizuJyTITyzOIrWOTNFxxGTNPIJyHPsv5TZcrzgoMbECd0ABzWZq4KJXkLgv5i4IoegSBhaHXhLnYV+/BkdIJ3rw+VgopXvLgnHOo42IzcpY25ggbMFwNk7FOgpJt1dF+ZZ0Ltgzdh81zTvHceZLnp8H8lDjNYEU/Fn43XqU3RUdSQ29R1XHawkIuYPTALAVJVrYlqSeZmaRjOde70xcaykUlcnQJDw5HHEq6gaSlcsnhgu3dnlWqjjjAwBLeRH4FQ72/HsT8zJvvUTAVWv+rAP604dd7qzRfJ6dWm5y1L5snA8dHTRU0GvGm97n9WWBIgaAaeoZVL1StJVkqKnjPN61HJVQli4n0sGsGudwBWj/uD1rxoTBX2Tr8wkj2JThGPIVDaHyD9Y8XPO47f30/LckA5IU9FshO+cEaMWqpzkzvDbnFwPvjocK987SRWUBGZt/T7P9SvG4WjN9UiLnuLhgqdO11pQf8JbOFFrYX1FbYYQAWx3TGs+oCeJUFw/k3y033oTc/KOaz3VsE8ho2h1TGjd322QWHowOTzdKzajjiBivRsI4aLJXG8nT5fY6BHoEY5DTkauJkLRNuh5Ns6Yjowx44jWhFYmjxjo69EWbGJToaVY1wjjr8kR85hbj704ClyTozKxGUKPmLoqgWta7qykmu7eShMZnMm8EvhbgjHn2KDQ754flQg/b22f1A/ElXGJwAJRLA4s2J5la/YUY6q3b9zY6L2NnNHPWEEkCq/6D18QyHxd+FPAIE13Su/6lco4GxzVbUQdPfgF9Oybq+DcTchC3FV1cWf7FgdZ7eWScCyYTybZzp0J5urM7AIZ7Hx2XPV4p97ZjnlLvH0pFwGXg16JJuFYgzMMQjylIDhRCkbetWybqZb9UVYWk8Rw6nK9aOLh/HZ5Zjg6D2AcWB1XLWoJ8PEtGrGRl/5Caywvy7Tva3cvJw9f1aBsE5DtzMzH2yTiWunAuNV43kKlUsEHMJub7eon7G7f9gZjxXJ4hVLNsNhQeYYxgTGvygh8hPxonelJju8Ih8CtjhAXeYXDyqAQT2ZiHdNx8hO+LiFwxAXnmvibPD6vSK4MZ8I4bKEVWnMesSpihVguKYeytmFpZn6045VGm/8kdyWoF7k41xFbIIY2lcUwGn+JoA7HccRa/1a9TLCaVKfiCERZFT56uhO7wnybJ0OwGbTK5kZG7+BQn4kdVVdUh7bqQrsmNE7AESyZeTIw1VcfhuO4JJCcLZy99a1K5aSrEKNn2oJEYLvXM0OKqHU4YAOVeuxyBR+R1i5/1tfOwKhN5eoi+OX/VYl75WYOPciJLhP2H7I3hCuPIK4wGfdCZczEWGHpjkhr/RxClXKoYGbqMJcfzNs09XwhX0WjDoqfHRJrLS9Qaa1L8efBxE8Ia61vPIQvz8FRfJNtv5RxRsm+hXB8Pn4OnBiB6sWny8Q3Hla9x5hWGKrR8l/GQBL2ZCyQWQ0V97QcebjZdK3s/AQvok9Hx4m6QUUTev4TAFHBJA+Br8Sd5xbNWl8BJ4mPWNHKE4pjTuU2rXpN488HhCa0goCAA8Rxs+YqIiY8zis9XUdMJVhFyw4Logoueua33EKZ0OuRMBmSErrjTj4zOUn0oBBbcQerFTHzM4ejEFNV0BQdJ3/5a1WNdAua5EYJWsEesaMqgfHRQTh5Vwu8JgnEngworsJAzHlNYb52fGUXwsCLeqzwaNCa9E5M9K2r3AO7JRsvH7/IlzqcD8p4yIhrvsMpnhwEg9eVMUO52avUzMWYA5Vv1P3c/96rOzJn4RBnc5Idjf2MWZqkoPlp6TaiWRajahT9UfJxvBRkHGixbcGcRccR06BOjKgqguK0qE8gAOjmOfR/lb8Baqc7EznWX2cK20RPvBo+cewvnzM9g5gIRrUCbaEf4BD4Y3CTQGhNF3O1nEjH5yyIiPGAuy9d3Qx0/KFljtjrefWm9RI8rSYZQpaMxQ6vCDKQdwaUDu0IKAN0TCVatnHhQStg2bW76o5J8pOWyLXgmH2auIdRQ4sln4iYibmkKbjp3nNtdC1egckMZ6NisDgTHkItn3mNpq6VPHprwgSu8NW9hjSNXhO7VNBTQeBM4PIv5olWMyGiCvoiTuFKI3Y1xz99P9oR/7OHGJ7v5JsHcASw51DAjjkr8HcvnGIGUH0lo0pgvjoqcai69nS01joQPmytXJw7BtAQeMndkn4lNeFM5hkkeLFbhNM3M42Z53GeUYvAz8XURMsnMwHDCYH3wknHdOsShWEi6mO9dKD2vBvNi/lmUE8v07StcHG06qRZlxpMaMvPYRJ6plkI4zjvT8dD+tk91Xyqh4xX4VU4iRNeN9ETtJ4hCLFSpSRqxBFodYsC9WR7QU2xUU5+x3TnAxWEoGe9wVw16uhHJ3wetoOY5q2BJxG+hyuKc55wofzdzjSgNZ0k9GUAZLWae4CeW2l/+g71F+sM8Un7AtdkmM03TfrCmM7zly01G09n7tjaSeDRSmCJV2PzTLrFrOFP9o/4JB5Mz/dUIwwELSmd7iJa67W4nBAYX3VNnmbArImM9hWWCUzSURV/R8IIR4WMoin0Iz0EHGJ4GYotqgoSRyE2DcyZ0IQYGmYMNBX4OoVKYfKha2VQOKNVBzjrjmcfS0KC1MlBXzZ3+4mOe66YzOBYmHAmM/TY6d1+VYqalKGpmt+Tx4Rfb8PZCkLAg1IT4AMB3511ZZib6ZkgoMkzG8yP7yPmYLXqVYmHpkDDcaRuxVzHWx9Z3Pf7sDIPZaPPZ2VQKlTWm/h68zDztAmzcX1+WkN6aRgZ/+atvNOi7l2ePKbSp+84rHQH8MdPn37SbxmzGSLR1RCk2k1Xp7Njpu1//fzLL7HqoaQfxJVvN4xAvuPl9/2eYJ6fsK1yh57Ub7/BMrazC6BfK7DNnb1pEM95Yu/ojlZ3ENDS/Dzpk4g8MYTz/kdPF3378sVQ8KNy2H98/ULD7waKi9HpS7jHcWIo727lk4weSgIvS1iixhe4F5kGm8frFQwaHr3jdt6W3MRu3EmnyWsc+/SCQMBKTiBOD/i7UrPnjUJZyrqsMKNIivvurPLEPa+tUGn668+vvmHNL7D6WtB/+Lo1AkYRcHlop1jb7dty+1Em891eUpIMUQ5a0it87wvHJ5ww45wFNnb/0S//THck5HgTMQOMonYwChQ9SA2uDEqIL/YSZm69edq2txsD1kIYrVDkqi7L4G/Rjmm0b85P5k7Djf/YqhgZeWYrDuQiLyugMq3ZIjCCDD6alucQv37JR9kwL39ivj8rvfmsgBtO/EFgmnqbiUCUOTYfZhSNwBcXgjNgESszB5/urMyoI8WOI+yan+iOmpl31DR3wami18Tef4c921ToAvdk5HSprGnHgQx5QeKk6bwjdLKGE2aNTlhlUWEqQppXWhWcqeCzvpsvmMCzxj0rt9YJBKJ4hOE4juCS818ekOsTjxtv8LXWTgyFgNi8XZfOWHsGKD7TZM7vJ+YdqhTMlQzsZnXHehOOR7plP+pxrHNINW8C5FuoiLnJkeuJojiSLHC3AypPLBJ6DD3TYAva9eFRxEhonYjgs81REEv4jF7hCDS0pKvWVRV8WjdLADFx1qRrIqRgaWseqCh6R4/Ir6Phnqb+gsl2HPhzhuS0WZrdrBpl5ZiylMTiKXyoS5ugcZgQF2rLGIaszJs2RTCXVFl2M5x6Vmt3PwNgKhF+RjX1VRNMk+AIfOaGj0Mm63G/4VYTYlqxBczOsQ82D3/5IbACjQhJrbHRYqAqk8egIntDPhJnjLQrs3s6mbkqE9sso053+JtHsdjCh0mOYHTTf62O0yUzmjoBVfLoV+QJTPFiEhuHA4pT/gyN+daEguU4/xAzIOw5pBUHBOKmBueWi4BDbB4QBphqN9hTH7ijcsXQJFUR8JuxzZyzwIHVNCdH4EwFcwv5ZBxv/Cyqpo9fErEYaa1MXsReEqsV57XEt3MbiXvEkgplVrQ+u60zCPCdyKXTxkdOE9XTfxvbWY7p9wytSbxOkThh1gNHhrIry71aA/oDHJ4F1qbPBzlrKuEntD7PnifKo54cZc+Witf2L2Zbpn5eQI9G6u6XmY3dgMwB6c626Ok4CeQeLKCLYvkRNOZrSZBx6PRX0vL0b5pWtHfBtWnh4RxqHrIhEZ3xb8eR3we2u7HZ8PvSXqL63a9M57kyUvG2k7M3s3oPMEnLysXJuKSabjplTqpoNb1S1SnOwXAq0jTme68y4MTVO4z8Jfjpw8dwck7IqNCubFBRDVTLhE+M/UPMmNyqgV7Tkc5bkoGCY2QSQ2cz/mc+laHwJ5E+5dUQ3umOil7YyQBEbMJqIokDTVG9OGh7yJXHyJlKY843TVOMLo87g678qpZaKpNHXPmbIhxuaMKJ3XVQuijpVZ3F1xk6QE1KTDfPCFArAPPcxDTXMHuap6OqkNOa00IfudKESQvzlgWATxfzhkd4+PPS8VVgkleeJHkylzOc6+FMY9o6oXeCmhaVaTnizMrQpk6F/0ZSBXP2G0FGyZrwXBHDxwHu+PlbLoGVCjc00XlZXssC/pzU07V99FJjMn50mhD+FKbRlQqnY2vuOd6sofuJogASU6ClJ5x5fDSkKXVy0MrDguVAhuSq8Sqz7VyMTCwmnu7m8/VQIGmim8/c/YRPXnEBokHGwG4MsHEXdWLK7MZoaZGPTz7MZ2jGMa7WK7YUTZN01OusYzI3nNHDL8zbYVoXIbluwRfIhtsFf1PjT1a9fIN1mN3aiIoqRYMB0TdO4z/+zvAE5dwxzJbovhRaqy0/vCJv5DhS0bQpg19DZ2qoutmBQyuZKTYVTB/NoTjdG6PqRiOCWKGiQ8CqB2SceNJYHPP94i1khqY2wFf+bdolJ8zNCzIw2fJzatPaEXPqmi6HFpwE8jyKhdCqkFcI3/FwLU5gaJdG4JARr6My2Ik5fveWylXTMAMszdhNylAcLwSCIrdAIyaAXnHCnMB1JcjyXoc0DWqmd6Q461OZDCaClcmMOaN/cwZzrfhXAAGTbj7alpx03ezV0gMVYBozzRz1GSUwozh4auo6odUctMLPxgiRgJSoW/AcDUCYOqA4ccmoRs83UwNhefR/nsyWmygI+yQI+AqQ+NMeTf3pWi3Zf73L588JHGfaETTAIhN3Uh29yWRnmr46Zz9aNL1irnIhmGsI1a1yBYYQrBYjxF/ycbi5Qot3YmtFY2Ys5asXTo64u8xyUmzUlUUbotU5sE4Js1n6mwP4EOCXX5/uAXc02+2CDceE3w24T8KYohlwvsuvvRCNPJf3pfaDTHLgjttkr8lR0znmHcwM0WwErTpeLW3PvTHrDO3YqdhzBWNvJefRhYP59ds5j4J6Le3HDtxyCY9DESbHVAWFr1gl7Sg9IbFRN0/wyRB/hUWP7/gWY+MivEJG07SIrer2MYLATCAm8CqJ+Qr72sTtqUzmwk5m1WvxVSZDTSH3WnCmM3uvTTODs0wt0cQUedlxzB0XKPnaeTtsHA9tkqM/9EcZ4BBQ5qvj7rWvSn62iM234aoql9YEwXDEMRQ0OX758hnIcLbE3FgIOBk4zi4tVro6paenkj8+FdgvqLi2SIZuiP9/Wfe248gNQ1H0IUiQ///cDhDMIrekKSTEQE1Rh4fUpWRV2WP7I71yyKWeB1YSFAPYTFtAbOzxpHh30iXu5vINwuTpFvLveWWmz27i315dGN08MhKt1lAYmdyFNPuUkMqRfZ7tL2/IZBPbr53ZyZrW7Yj80daqpH/zBGMkzwjAaKhDIqfMSO4o6ajqyJLLnC/MPOSGZHT5FWX3uJjzmDAbSBUbL2XCnnHbz3qewSHrpXh4ilHNZb5pZwMBvnkffROjvNB5tR74avqPvKy0/ubcJ4N75DoRtRJgKxONgRIXnrCX80Im4bGs0I0hr5d54ZT2pnTAXCBbolYChsi1jn4P3dGycCEw8bMkOIm7b1Vg+lPo8IXjm71qtCUZIbCbG5aawjOqFqiS5Ymm/+siMp7+8EGk/vIQgNiqWXS7poK9/KKIWgzVLGVQfnyf8eXKpdaUGMoBptAR6nN2ndNEcoThVevXXWvVSrDnIo1eV19oWZRq4LWbBrmdUze7DxbCPABFDSelWB82V/j5FA+XbZ0hdmawf3h7IjzLqpOnlKKyhWi1VRZrOMvsrpXhMQIuM5S8HIPm0dXOeg+y/vWO777LxHM+BuAo6VdgPXLnurAdwBITu1ueCTc77ARMgJ1EDCxM91BG2RZYAkP16fhUHRk22WG5q4g+zHc5UZBIgvEcQTdkMyqucXCPZnYoPcUEpEx5P3YAtpFfmqozJoKUBX17vZ0NPeqce93s6ZFB5sIi7rxNSffJm72AzQJ30de4U/bnrNtkWKyJ7d3P7rxZKuOEpGwOpxEnmZGsg1vCBPvnZ36Qxow/R3aT8tcf51aI15ftwRizL9MsxR3WWW9iMVrzAJ22smgCC49nXD7kyzd9Z8wOULhl+70thFQWRUn/MgeIp3CBow2fhV6IkgmshGQhjZvqt4l+PukO0a7UeURvWVDbGvEaAp5GM0VJtCKFJ/W2eOwvKtgbTUailUA+l29CANhYRFfSz7PS+8YHwlohMTySoV5Bnr3rp+2yaesSZYl8jPsTWPXFPTw7IxiGuj/885p3RMi5aM61tIt7qxEOyIU6jy9GolLunM5gapfjlqMgp4PDeHWbhkHN6BHfMYbWtjP5OCRaHHtJ/+zX3WjSkTob7aR6VyFCxiM2r9bi7t31S06BJ4SU5qx21+v+LvHkdj91LbruSAMh8IwAre7QUUSyTdMB4xPydHacRhbpFf7Ealz22hjLzVdc0w+eYZLfpfgs+DHNiF0Zl43LwE69LbPeNmwb1kSZTf/tTS5yv9+35x8uM25mcBdp6/DksJPVMPpfV0lRXiwKsCZ9OROqx/e5AfsBwNBkaI3tLer8nN2+SMhzzkq7sZwYnz8NGkdzMcg7xSyqrWpwuiMbBWAunx0lxgl5M9RKf9zSVsUAX5Q6Mg77IL9BoMef0npIZ+cYTHqqj0HoZ8lY3MCFy1KJkPCy86RXVQb4BaGZw1eQV2MJAAAAAElFTkSuQmCC
📡 API Calls Detected
- mixpanelBrowserDb
- POST
- https://assets.leapwallet.io/cosmos-registry/v1/gas/gas-prices.json
- GET
- https://twitter.com/yield_xyz
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 4694 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 4694 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
