
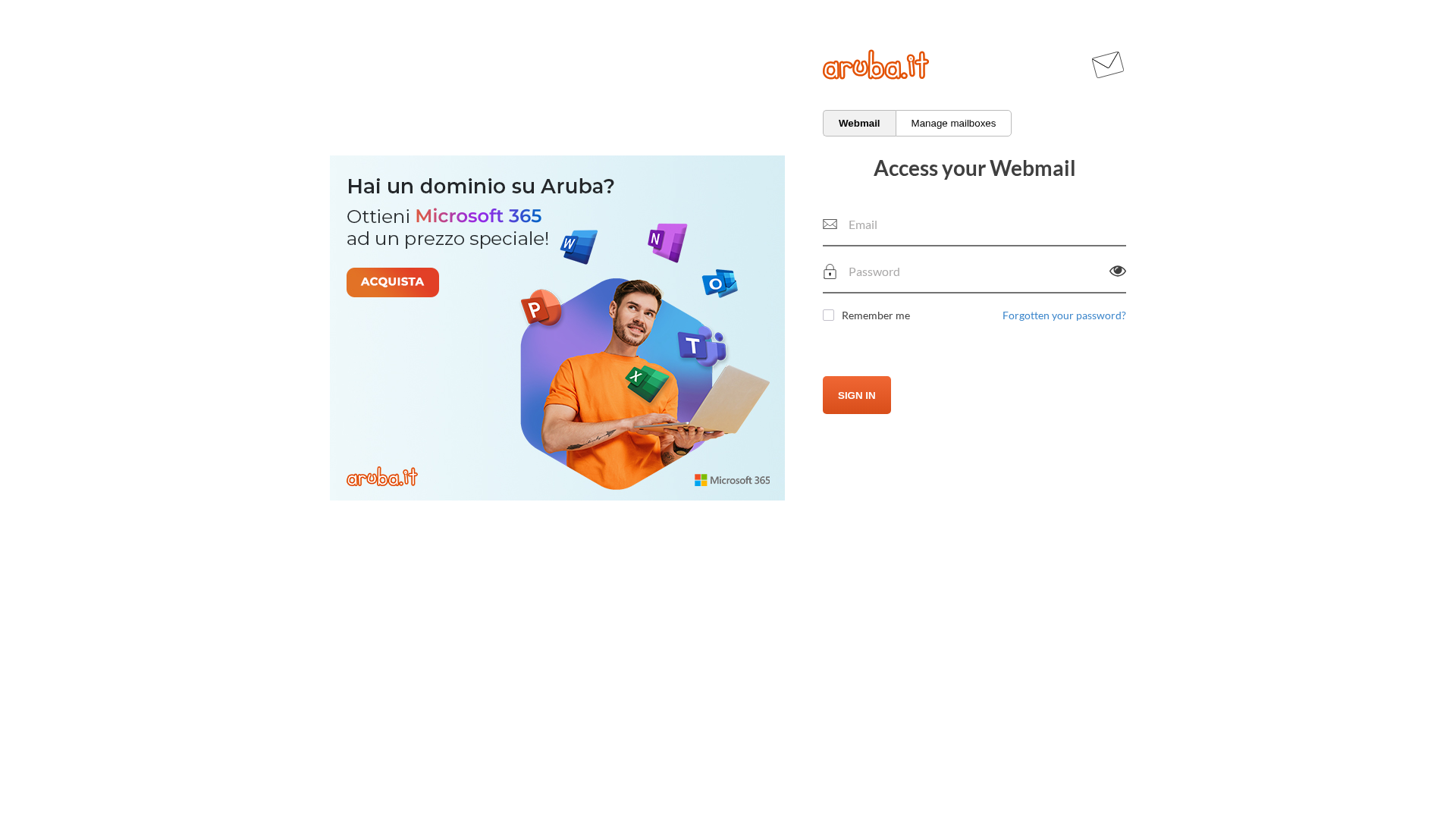
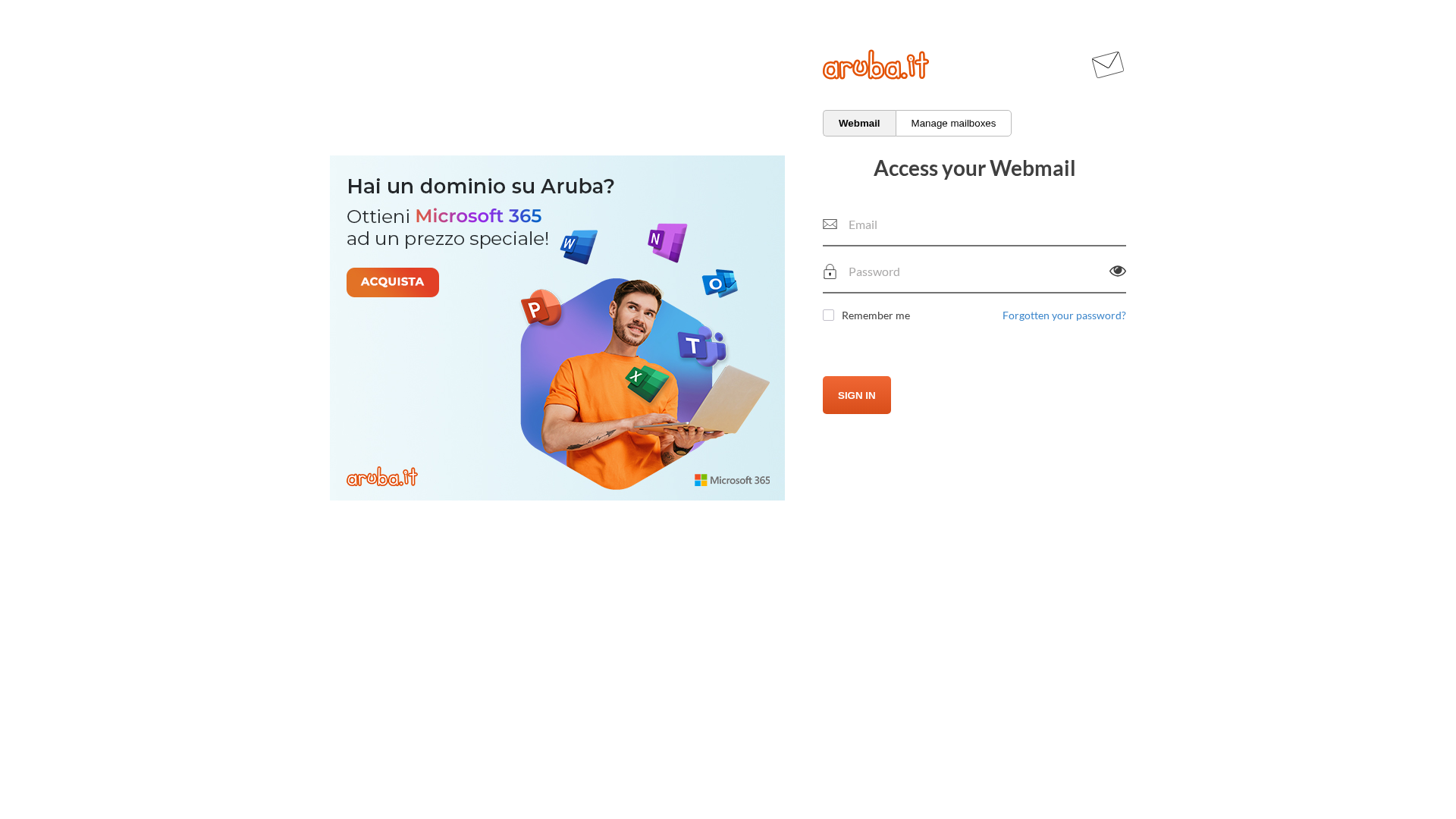
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17751D07180299CA78282C6D06BF1B71F7241C385CF875A4447F0D7AEAAEFD81EC55297 |
|
CONTENT
ssdeep
|
48:GpNCuso+8SeV9x/Q3MtUU8Hx8DQjZIpVPY5APu:JHQ/QctvW2FYUu |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b331ccce33339c38 |
|
VISUAL
aHash
|
ffc387c7c7ffffff |
|
VISUAL
dHash
|
04161b1f1c200800 |
|
VISUAL
wHash
|
d183818184fcfcfc |
|
VISUAL
colorHash
|
07201218000 |
|
VISUAL
cropResistant
|
04161b1f1c200800 |
Code Analysis
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- https://webmail.aruba.it/web_imgs/login/css/login.css?_v_=v4r2b65pl4.20210517_1745
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for bafkreid3q57qjuhurnmaqalp5lni7jbijkys2kbirtsnuu4pt7xbi3gbhy.ipfs.dweb.link
Found 1 other scan for this domain
