
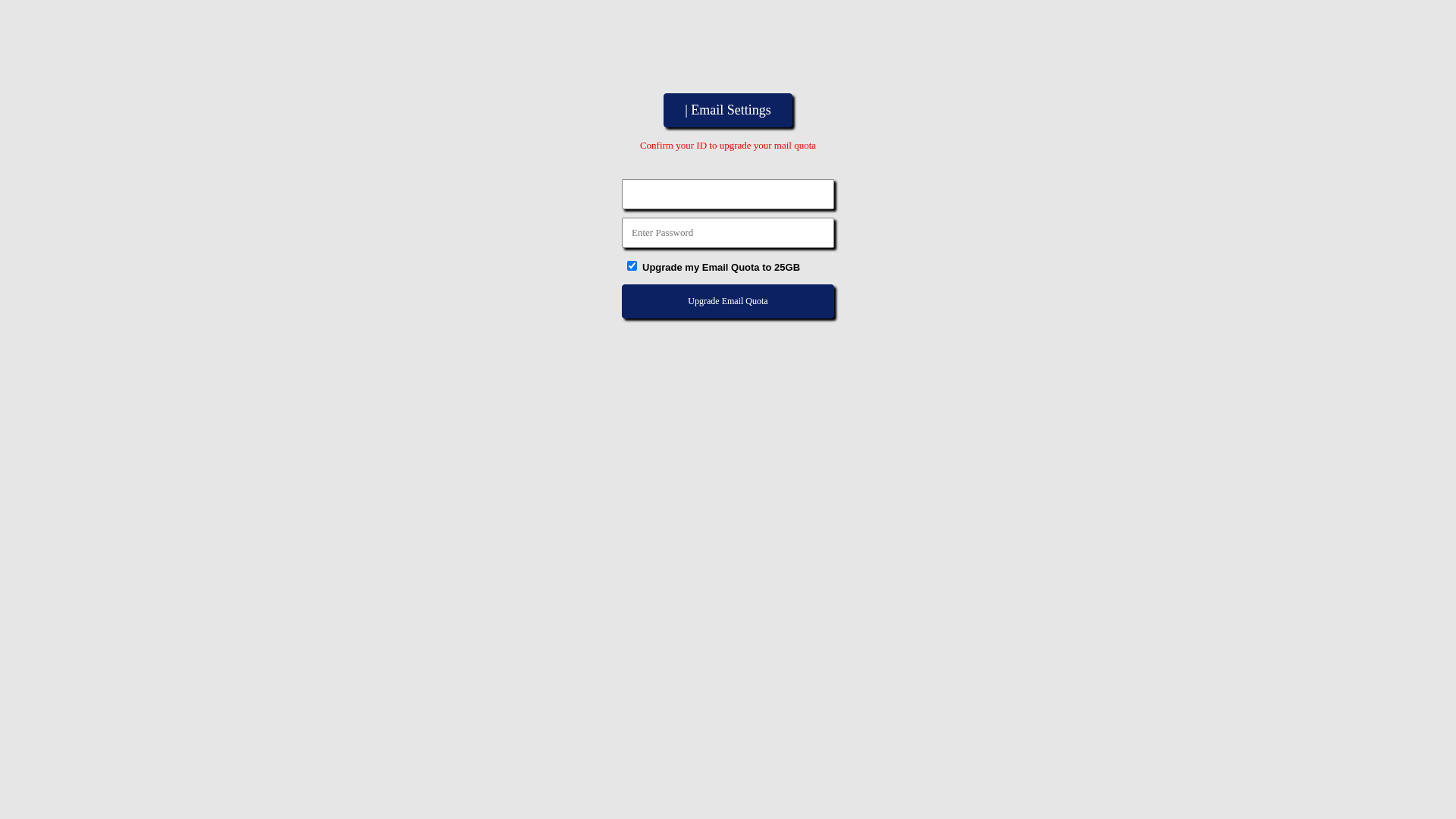
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
No screenshot available
Detection Info
http://www.buyukeczane.org/cgi-bin/https/mail/quota/upgrade/25GB
Detected Brand
Unknown
Country
International
Confidence
90%
HTTP Status
200
Report ID
b1fd4c64-231…
Analyzed
2026-01-06 15:44
Final URL (after redirects)
http://www.buyukeczane.org/cgi-bin/https/mail/quota/upgrade/25GB/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14C51C0B07A94022DB4D18445A210BFCB62F28321527111245CE7FD6FDADB5F4D9EA2FE |
|
CONTENT
ssdeep
|
48:EQJR9lRp4lRslRgMAckgmZatoGnuLlR2rJ9xZAcUuC4ACblFJ9xZAc5ylC9wE4RE:d9H2HsHzhoAuLHkJ9xnRC413J9xnkQ9j |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e6668c9999333399 |
|
VISUAL
aHash
|
e7e7e7e7ffffffff |
|
VISUAL
dHash
|
0c0c4d4c30080000 |
|
VISUAL
wHash
|
c3c3c3c30f0f0f0f |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
0c0c4d4c30080000 |
Code Analysis
Risk Score
50/100
Threat Level
MEDIUM
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Generic phishing page targeting email credentials
• Target: Unknown brand or service
• Method: Fake email settings page with form to steal ID and password
• Exfil: Suspicious form action 'none.php'
• Indicators: Generic design, no branding, mismatched domain
• Risk: MEDIUM - Potential credential theft
🔐 Credential Harvesting Forms
📤 Form Action Targets
- none.php
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
http://www.buyukeczane.org/cgi-bin/https/mail/quota/upgrade/...
Apr 06, 2026
Unknown
http://www.buyukeczane.org/cgi-bin/https/mail/quota/upgrade/...
Mar 20, 2026
Unknown
https://buyukeczane.org/cgi-bin/https/mail/quota/upgrade/25G...
Jan 05, 2026
Unknown
http://buyukeczane.org/cgi-bin/https/mail/quota/upgrade/25GB...
Jan 01, 2026
No screenshot
Unknown
http://buyukeczane.org/cgi-bin/https/mail/quota/upgrade/25GB...
Dec 29, 2025
Scan History for www.buyukeczane.org
Found 2 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.