
Phishing Analysis
Detailed analysis of captured phishing page
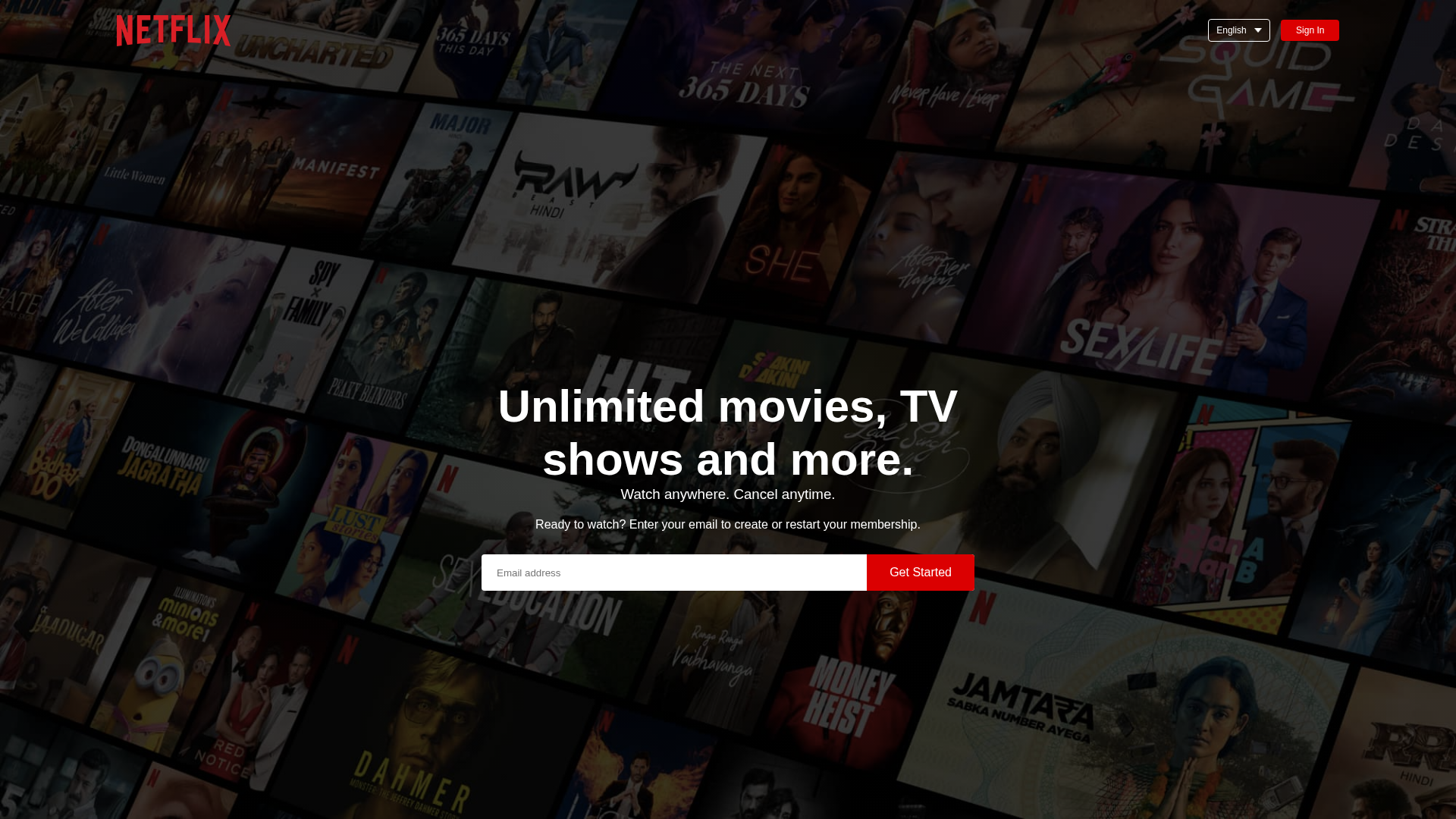
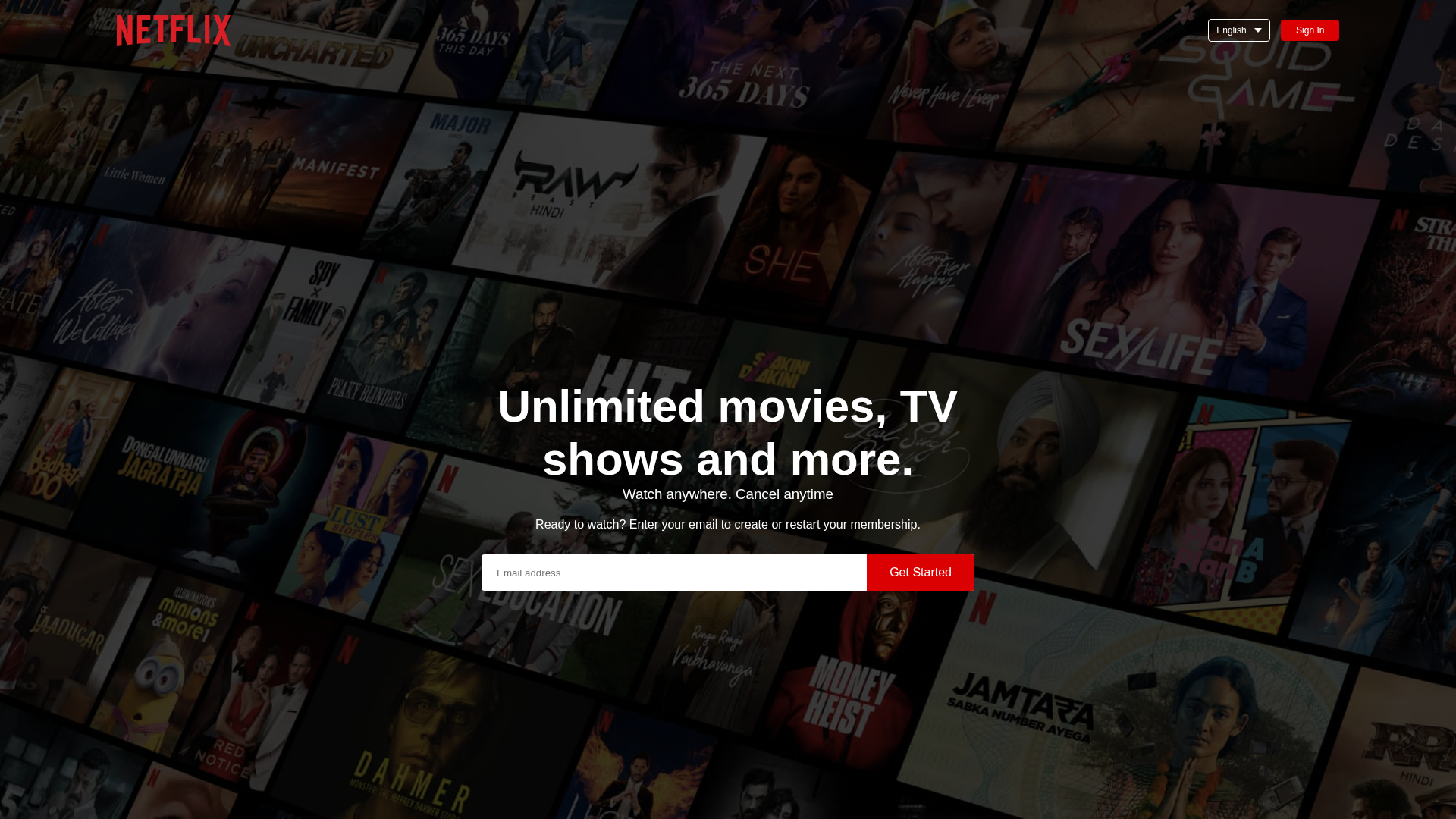
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1DEE1A77A5644116F02C343A13B799B2BB7994190E717272824D9834E6FEAF09CD7F3E8 |
|
CONTENT
ssdeep
|
96:TusSIQ7HSmnUAhciW8t9BmRFn8lDUwO4TShBi0fTECCzJ7+/LRg4RK8oAsIp:6v5ymn+wE8lD/9TqACC+Fg4RnoAvp |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc6532cd7131cd33 |
|
VISUAL
aHash
|
423060d83c3c0705 |
|
VISUAL
dHash
|
8664aeb272602c0d |
|
VISUAL
wHash
|
c63070fe3e3c8707 |
|
VISUAL
colorHash
|
39e00000000 |
|
VISUAL
cropResistant
|
80c0804040800098,8664aeb272602c0d |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Netflix users
• Method: Impersonation through a look-alike website on free hosting.
• Exfil: Email address.
• Indicators: Free hosting, Netflix logo, form.
• Risk: HIGH
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
🏢 Brand Impersonation Analysis
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers are using a phishing website hosted on free hosting to mimic the Netflix website. They display the Netflix logo and offer a 'Get Started' button to lure users into providing their email address. This is a common tactic to collect email addresses for spam or other malicious activities.
Secondary Method: Brand Impersonation
The website closely mirrors the visual design of Netflix. This creates a sense of familiarity and trust, making users more likely to enter their credentials.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
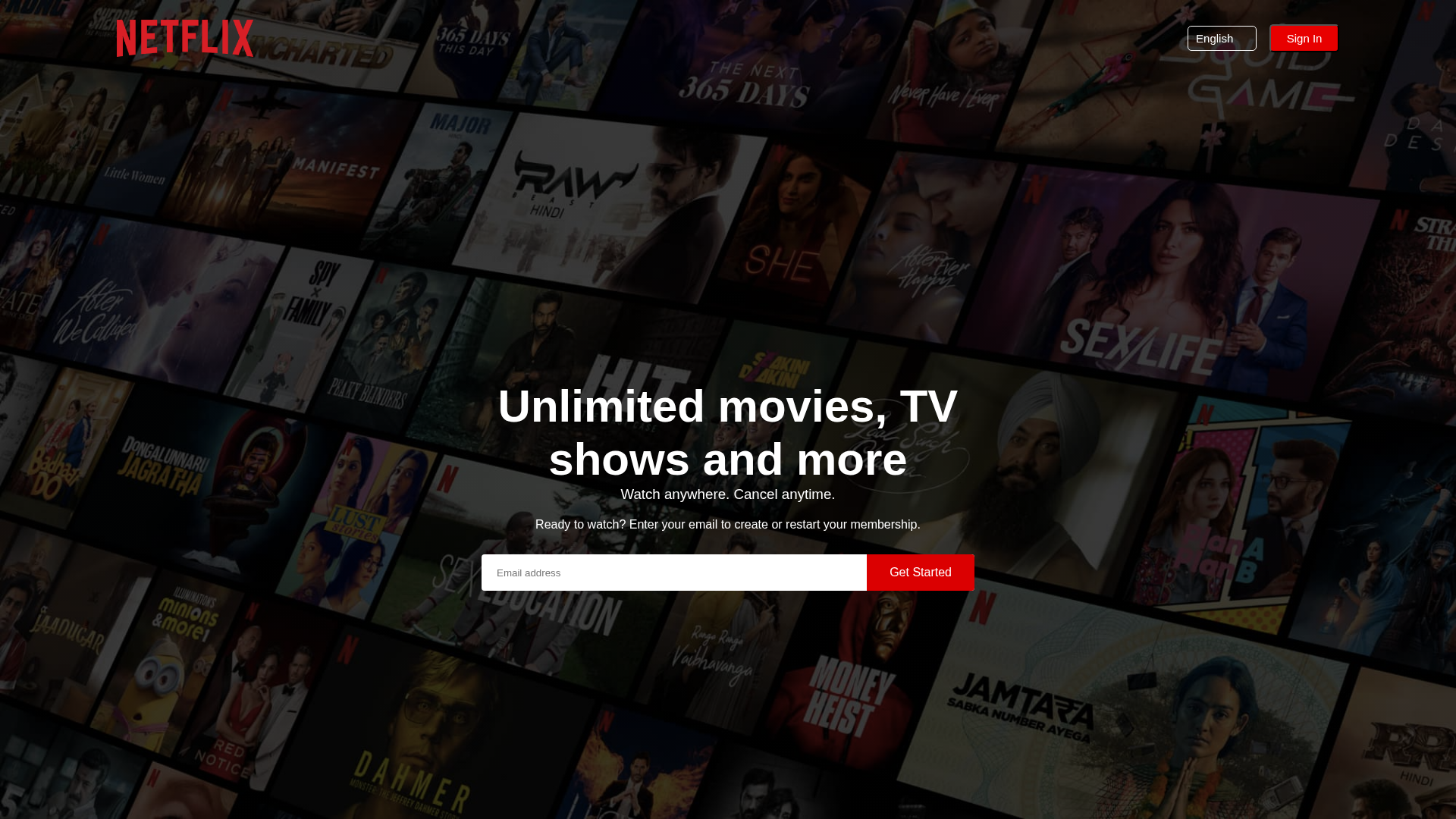
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for sekhariam.github.io
Found 2 other scans for this domain
