Phishing Analysis
Detailed analysis of captured phishing page
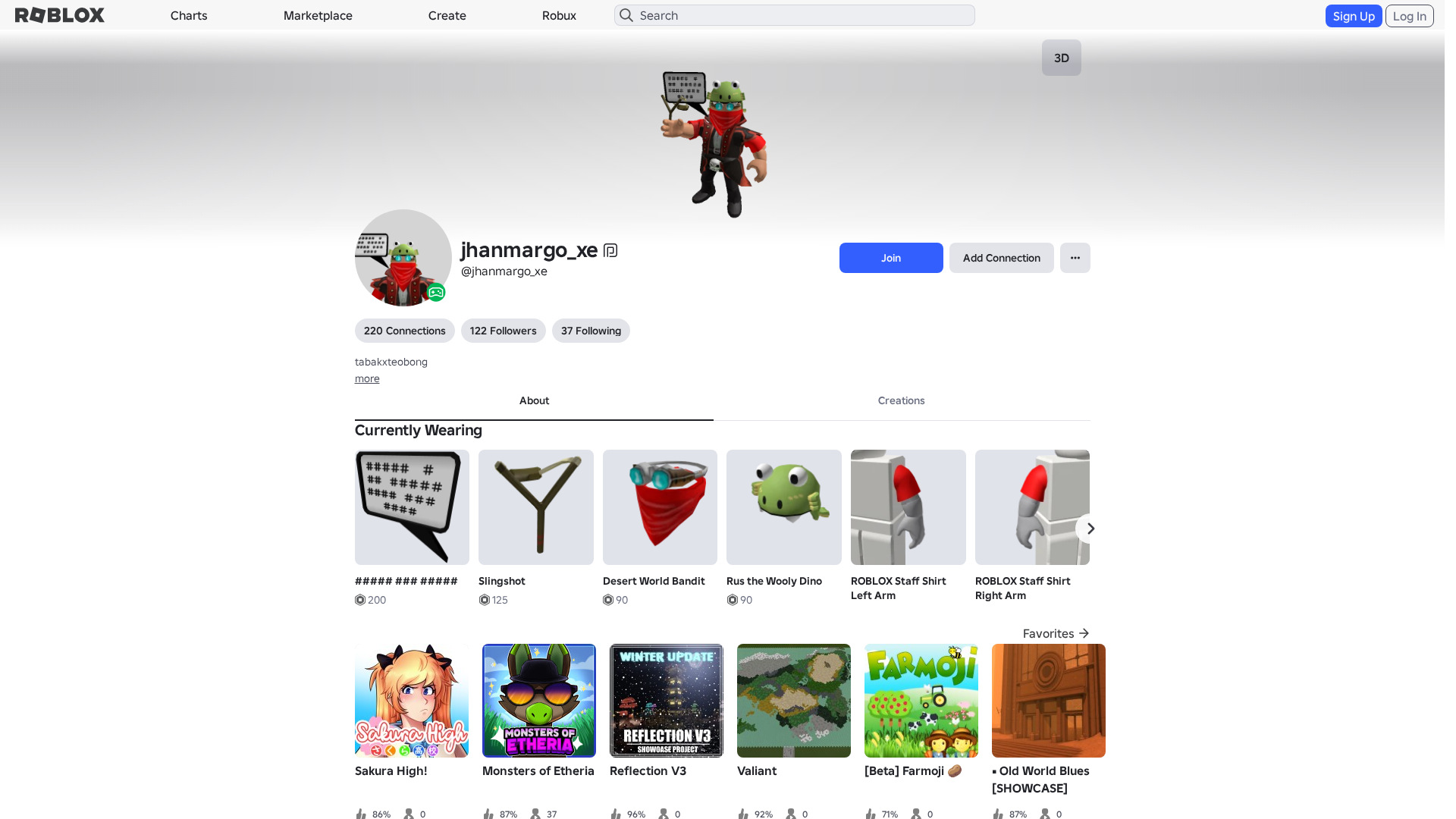
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A37351B292512837617B75DAF064671AD2D3D70FCA8347E1A2FCD39A0FD6CA1E853809 |
|
CONTENT
ssdeep
|
1536:ISlXWnarUUXeRXsg3fgdTgdkgY+gsZgVDgl9gn3gzHTgXLgkzgxTggpglpgkNg8h:flXWbUGoga8Skgu61QxqHf2bZkN |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b116634398f99c79 |
|
VISUAL
aHash
|
0020dfffc3d3c3c3 |
|
VISUAL
dHash
|
c8c836302e268b1b |
|
VISUAL
wHash
|
0000dfffc3d3c3c3 |
|
VISUAL
colorHash
|
07240010000 |
|
VISUAL
cropResistant
|
c8c836302e268b1b,330e074933940ab2,ae7e5898a8988aec,860e9671298cee35 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/17695667/Desert-World-Bandit
- https://www.roblox.com/games/145897181/Roll-Up-10-000-Stairs-for-Super-Admin-Obby-Dream
- https://api.injuries.lu/catalog/405995284/Captain-Rampage-Torso
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F423283805665%2Fprofile
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F423283805665%2Fprofile
- https://api.injuries.lu/catalog/130107808/ROBLOX-Staff-Shirt-Left-Arm
- https://api.injuries.lu/catalog/3916647982/Rus-the-Wooly-Dino
- https://api.injuries.lu/catalog/734326679/Knight-Fall
- https://api.injuries.lu/catalog/734329002/Knight-Climb
- https://api.injuries.lu/catalog/734326330/Knight-Walk
- https://api.injuries.lu/catalog/734327140/Knight-Idle
- https://api.injuries.lu/catalog/734325948/Knight-Run
- https://api.injuries.lu/catalog/734327363/Knight-Swim
- https://api.injuries.lu/catalog/88871634439416/Evil-Skeptic-Head
- https://api.injuries.lu/catalog/130107952/ROBLOX-Staff-Trouser-Left-Leg
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/130107879/ROBLOX-Staff-Shirt-Right-Arm
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/130108169/ROBLOX-Staff-Trouser-Right-Leg
- https://api.injuries.lu/catalog/109016325316032/Evil-Skeptic-Mood
- https://api.injuries.lu/catalog/3702659347/unnamed
- /login?returnUrl=
- https://api.injuries.lu/catalog/33382537/Slingshot
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/734326930/Knight-Jump
📡 API Calls Detected
- get
- https://kyxn.dev${e.endpoint}
- https://help.roblox.com/hc/articles/30428367965460
- /api/shorten
- /api/pageview
- https://ro.blox.com/Ebh5?
- GET
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev/api/shorten
- https://apis.
- POST
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for roblx.me
Found 8 other scans for this domain