Phishing Analysis
Detailed analysis of captured phishing page
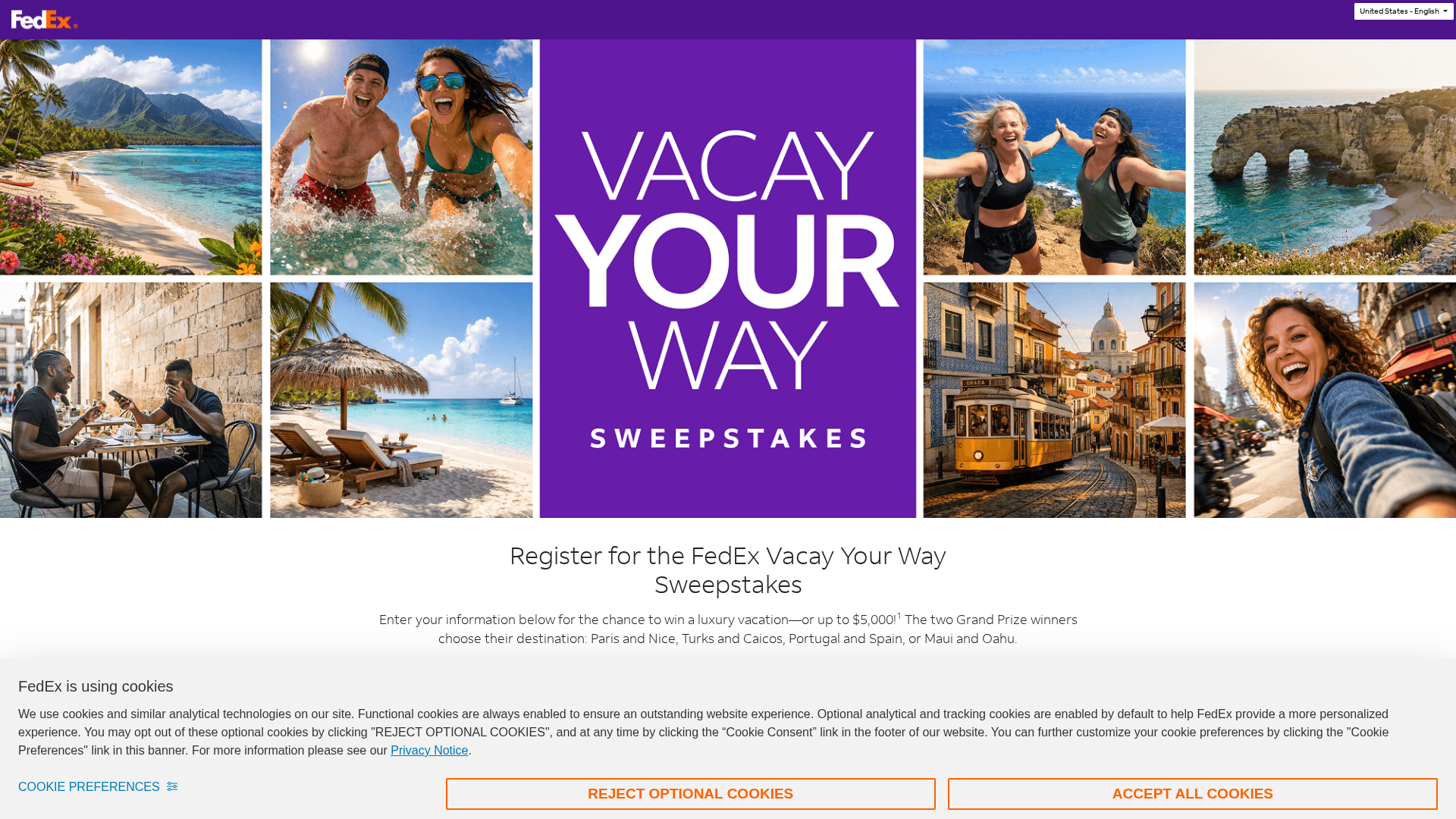
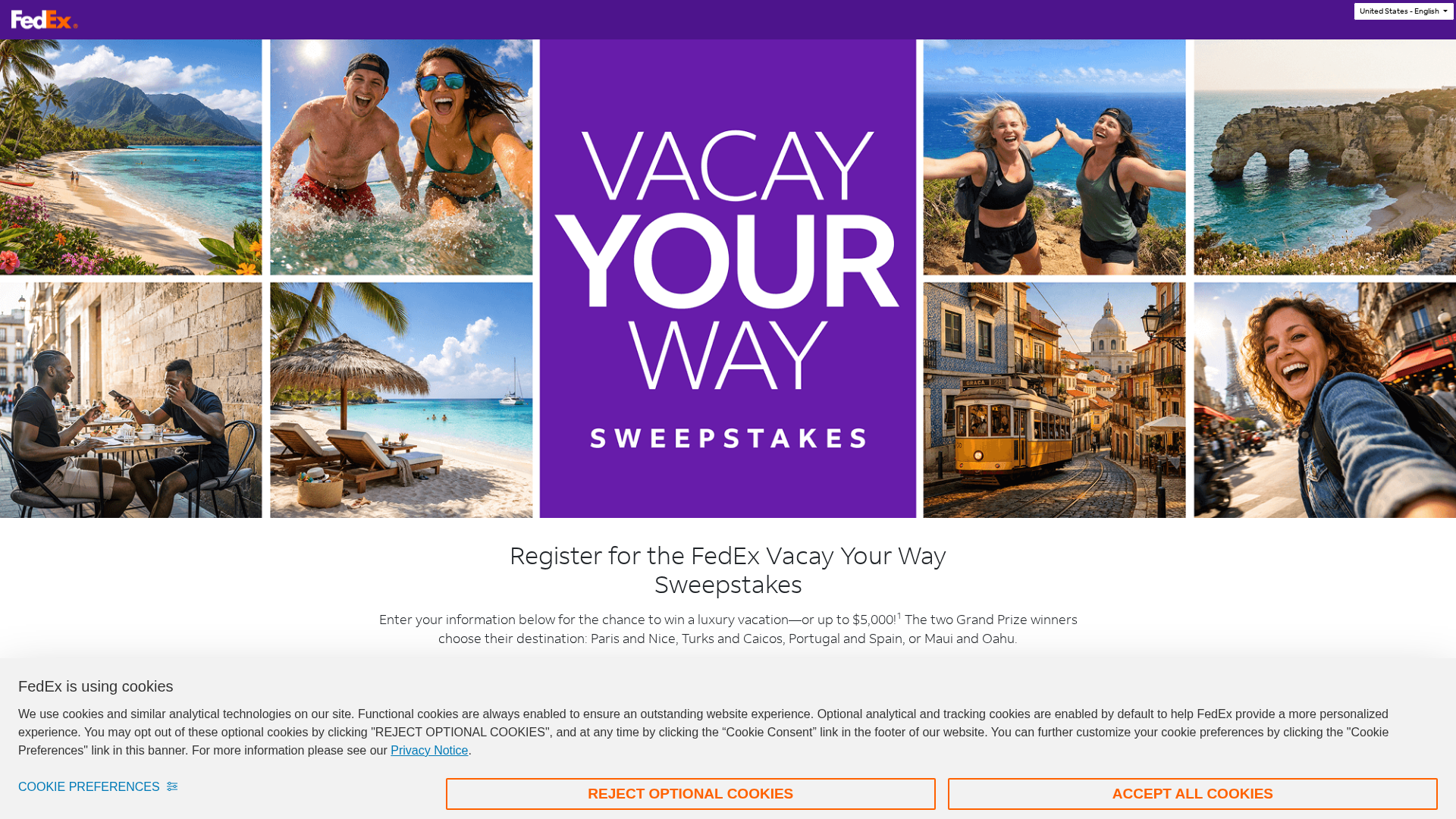
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14EA283307008DC2B40D7A5D962F59E1FA7E1C361CD525281EAE987EC0FE6EA4CE2B610 |
|
CONTENT
ssdeep
|
384:Rz655QPYoEiaY4Zxp7KQdnlOHmYnDDslkSzSfJ+xGrmZFbX9SbGr:5whfJ5 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e770b82227bcba0b |
|
VISUAL
aHash
|
010080a020ffffff |
|
VISUAL
dHash
|
8f8e124ecacf95c9 |
|
VISUAL
wHash
|
0100e0a220ffffff |
|
VISUAL
colorHash
|
06201000018 |
|
VISUAL
cropResistant
|
8e82164ecb8e97c9,6646959796d6e9e9,0f8e0c931646cecb,dacfc7a578c8c1a0,211d6b4b7579f1e2,21918c1931b01c18,f331796ebff96cae,7272637371534754 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- https://www.google.com/ccm/geo
- GET
- POST
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 51 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 51 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for vacayyourwayadventureawaits.com
Found 2 other scans for this domain