
Phishing Analysis
Detailed analysis of captured phishing page
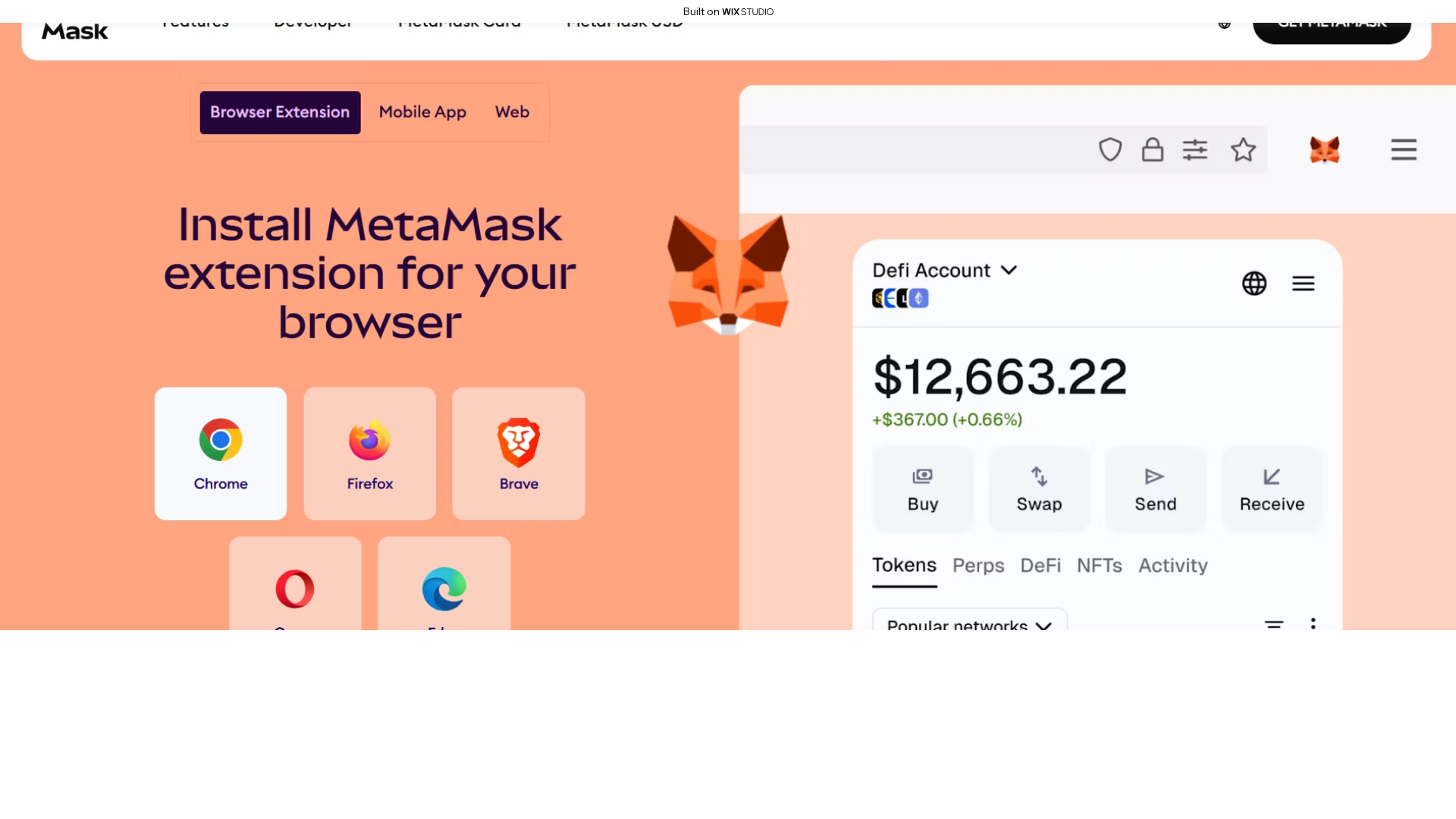
Visual Capture
Detection Info
https://metamaskcdn.wixstudio.com/en-us
Detected Brand
MetaMask
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
b7c59761-319…
Analyzed
2026-04-07 10:29
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T114335C726731B4A882DB92EEE7382D59B2C6549DFCCB4540F5C9968D23C7CD02287BB4 |
|
CONTENT
ssdeep
|
1536:al+EsZ/8UDDVR9MjBVRlMjB6DrpRXPZlQaQD9OehM+BrUgq4z:aazRAR5DrpR/PkEeDz |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b31fcec1c0c476f0 |
|
VISUAL
aHash
|
1e0f07074f0fffff |
|
VISUAL
dHash
|
7c792c3e9edede00 |
|
VISUAL
wHash
|
0e0f06030607ffff |
|
VISUAL
colorHash
|
07e00000000 |
|
VISUAL
cropResistant
|
7c792c3e9edede00,554d3588c8354d45 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://siteassets.parastorage.com/pages/pages/thunderbolt?beckyExperiments=.DatePickerPortal%2C.DisableDocumentScrollWhenLightBoxOpen%2C.EnableCustomCSSVarsForLoginSocialBar%2C.FreemiumBannerOdeditor%2C.LoginBarEnableLoggingInStateInSSR%2C.TextInputAutoFillFix%2C.UseLoginSocialBarCustomMenu%2C.UseNewLoginBarDropdownMenuAlignment%2C.UseNewLoginSocialBarCustomMenuPositioning%2C.UseNewLoginSocialBarElementStructure%2C.UseNewLoginSocialBarMemberInitialsAvatar%2C.WixFreeSiteBannerDesktop%2C.WixFreeSiteBannerMobile%2C.addIdAsClassName%2C.buttonUdp%2C.calculateCollapsibleTextLineHeightByFont%2C.disableBuilderWixComponents%2C.dom_store%2C.dontApplyDacOverridesOnBoBApps%2C.dynamicSlots%2C.fiveGridLineStudioSkins%2C.imageEncodingAVIF%2C.isClassNameToRootEnabled%2C.migrateRepeaterUiTypeMapper%2C.motionTimeAnimationsCSS%2C.overrideFloatInDistance%2C.shouldUseResponsiveImages%2C.svgResolver_2%2C.uiTypeNativeMappers%2C.updateRichTextSemanticClassNamesOnCorvid%2C.useClassnameInResponsiveAppWidget%2C.useImageAvifFormatInNativeProGallery%2C.useResponsiveImgClassicFixed%2C.useSvgLoaderFeature%2C.useSvgLoaderFeatureOnBuilderComps%2C.useWowImageInFastGallery&blocksBuilderManifestGeneratorVersion=1.129.0&contentType=application%2Fjson&deviceType=Desktop&dfCk=6&dfVersion=1.5326.0&disableStaticPagesUrlHierarchy=false&editorName=Studio&experiments=dm_bgScrubToMotionFixer%2Cdm_masterPageVariablesQueryFixer%2Cdm_migrateOldHoverBoxToNewFixer&externalBaseUrl=https%3A%2F%2Fmetamaskcdn.wixstudio.com%2Fen-us&fileId=6ac295b9.bundle.min&formFactor=desktop&freemiumBanner=true&hasTPAWorkerOnSite=false&hasUserDomainMedia=false&isBuilderComponentModel=false&isHttps=true&isInSeo=false&isMultilingualEnabled=false&isResponsive=true&isTrackClicksAnalyticsEnabled=false&isUrlMigrated=true&isWixCodeOnPage=false&isWixCodeOnSite=false&language=en&languageResolutionMethod=QueryParam&metaSiteId=603dd906-63c5-478e-9bae-01d6eb291a4f&module=thunderbolt-features&originalLanguage=en&pageId=26e79b_b35807badeefaf060c4c235a58832470_3.json&pilerExperiments=specs.piler.useEditorReactComponents&quickActionsMenuEnabled=false&registryLibrariesTopology=%5B%7B%22artifactId%22%3A%22editor-elements%22%2C%22namespace%22%3A%22wixui%22%2C%22url%22%3A%22https%3A%2F%2Fstatic.parastorage.com%2Fservices%2Feditor-elements%2F1.15034.0%22%7D%2C%7B%22artifactId%22%3A%22editor-elements%22%2C%22namespace%22%3A%22dsgnsys%22%2C%22url%22%3A%22https%3A%2F%2Fstatic.parastorage.com%2Fservices%2Feditor-elements%2F1.15034.0%22%7D%5D&remoteWidgetStructureBuilderVersion=1.251.0&siteId=7121356a-a8d8-4a04-a183-dc9766f116dc&siteRevision=3&staticHTMLComponentUrl=https%3A%2F%2Fmetamaskcdn-wixstudio-com.filesusr.com%2F&useSandboxInHTMLComp=true&viewMode=desktop
- https://siteassets.parastorage.com/pages/pages/thunderbolt?beckyExperiments=.DatePickerPortal%2C.DisableDocumentScrollWhenLightBoxOpen%2C.EnableCustomCSSVarsForLoginSocialBar%2C.FreemiumBannerOdeditor%2C.LoginBarEnableLoggingInStateInSSR%2C.TextInputAutoFillFix%2C.UseLoginSocialBarCustomMenu%2C.UseNewLoginBarDropdownMenuAlignment%2C.UseNewLoginSocialBarCustomMenuPositioning%2C.UseNewLoginSocialBarElementStructure%2C.UseNewLoginSocialBarMemberInitialsAvatar%2C.WixFreeSiteBannerDesktop%2C.WixFreeSiteBannerMobile%2C.addIdAsClassName%2C.buttonUdp%2C.calculateCollapsibleTextLineHeightByFont%2C.disableBuilderWixComponents%2C.dom_store%2C.dontApplyDacOverridesOnBoBApps%2C.dynamicSlots%2C.fiveGridLineStudioSkins%2C.imageEncodingAVIF%2C.isClassNameToRootEnabled%2C.migrateRepeaterUiTypeMapper%2C.motionTimeAnimationsCSS%2C.overrideFloatInDistance%2C.shouldUseResponsiveImages%2C.svgResolver_2%2C.uiTypeNativeMappers%2C.updateRichTextSemanticClassNamesOnCorvid%2C.useClassnameInResponsiveAppWidget%2C.useImageAvifFormatInNativeProGallery%2C.useResponsiveImgClassicFixed%2C.useSvgLoaderFeature%2C.useSvgLoaderFeatureOnBuilderComps%2C.useWowImageInFastGallery&blocksBuilderManifestGeneratorVersion=1.129.0&contentType=application%2Fjson&deviceType=Desktop&dfCk=6&dfVersion=1.5326.0&disableStaticPagesUrlHierarchy=false&editorName=Studio&experiments=dm_bgScrubToMotionFixer%2Cdm_masterPageVariablesQueryFixer%2Cdm_migrateOldHoverBoxToNewFixer&externalBaseUrl=https%3A%2F%2Fmetamaskcdn.wixstudio.com%2Fen-us&fileId=6ac295b9.bundle.min&formFactor=desktop&freemiumBanner=true&hasTPAWorkerOnSite=false&hasUserDomainMedia=false&isBuilderComponentModel=false&isHttps=true&isInSeo=false&isMultilingualEnabled=false&isResponsive=true&isTrackClicksAnalyticsEnabled=false&isUrlMigrated=true&isWixCodeOnPage=false&isWixCodeOnSite=false&language=en&languageResolutionMethod=QueryParam&metaSiteId=603dd906-63c5-478e-9bae-01d6eb291a4f&module=thunderbolt-features&originalLanguage=en&pageId=26e79b_a8d1652cdfce9b084f3f270e7d7ac06e_3.json&pilerExperiments=specs.piler.useEditorReactComponents&quickActionsMenuEnabled=false&registryLibrariesTopology=%5B%7B%22artifactId%22%3A%22editor-elements%22%2C%22namespace%22%3A%22wixui%22%2C%22url%22%3A%22https%3A%2F%2Fstatic.parastorage.com%2Fservices%2Feditor-elements%2F1.15034.0%22%7D%2C%7B%22artifactId%22%3A%22editor-elements%22%2C%22namespace%22%3A%22dsgnsys%22%2C%22url%22%3A%22https%3A%2F%2Fstatic.parastorage.com%2Fservices%2Feditor-elements%2F1.15034.0%22%7D%5D&remoteWidgetStructureBuilderVersion=1.251.0&siteId=7121356a-a8d8-4a04-a183-dc9766f116dc&siteRevision=3&staticHTMLComponentUrl=https%3A%2F%2Fmetamaskcdn-wixstudio-com.filesusr.com%2F&useSandboxInHTMLComp=true&viewMode=desktop
📡 API Calls Detected
- POST
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 18 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
MetaMask users
Attack Method
obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 18 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
MetaMask
Official Website
https://metamask.io
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 18 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
metamaskcdn.wixstudio.com
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.