Phishing Analysis
Detailed analysis of captured phishing page
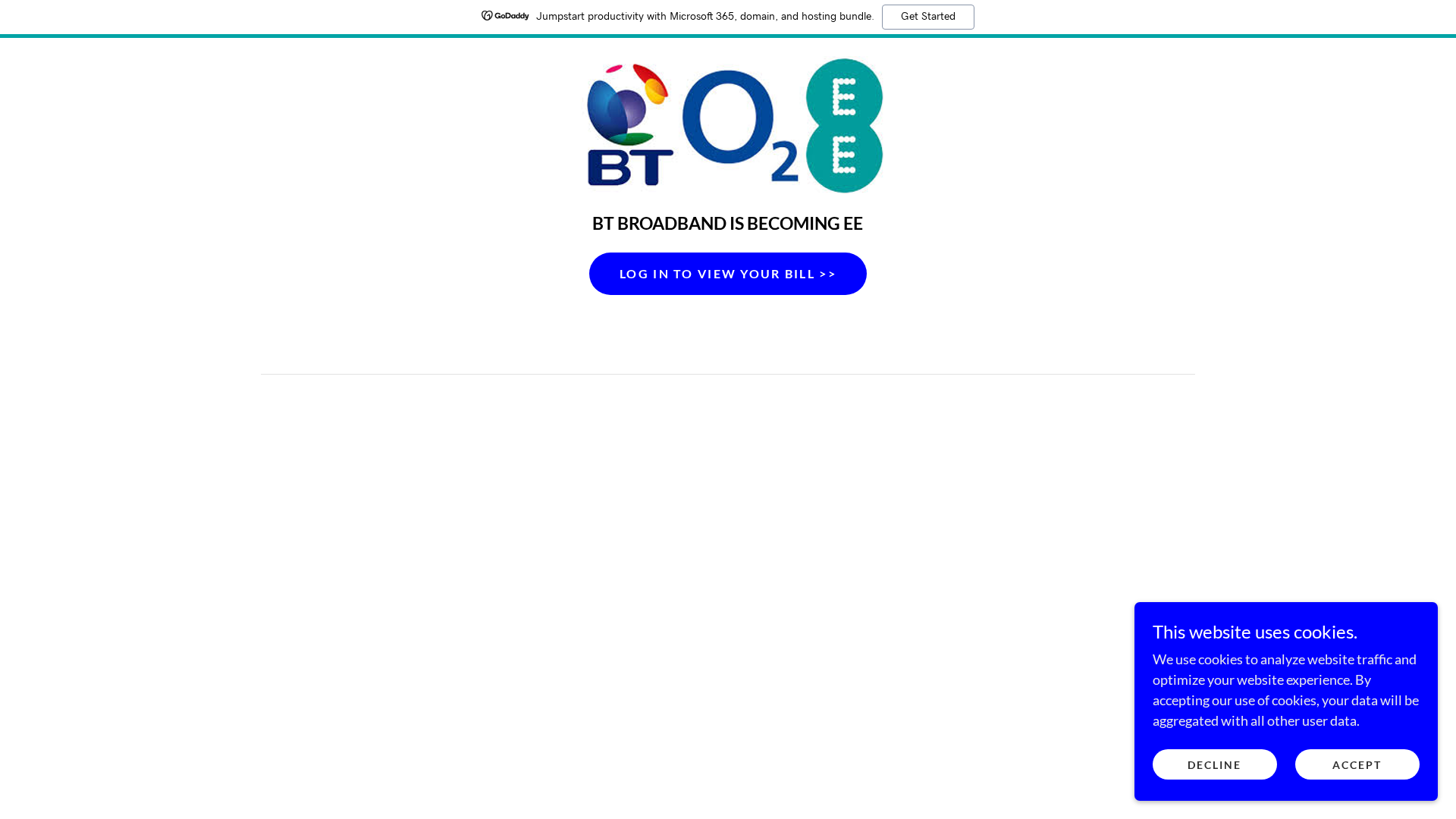
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T139523246260839A5C2B3489C94506684B387DB4FC921877086BC5E7F1FD2EA2A795F3F |
|
CONTENT
ssdeep
|
192:cQO0YOryHjbI1jaZPc4alDtPCZw7yBNQ6VyNU4JQMdBCWvoacsLjwpcBlb5h1oQg:2OryW4udiy3Bg6BR+FhoQ |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d2a5528dad52a75a |
|
VISUAL
aHash
|
e7e7e7fffffcfcfc |
|
VISUAL
dHash
|
0d4d4d0c00080808 |
|
VISUAL
wHash
|
00e7e381f3f0f0f0 |
|
VISUAL
colorHash
|
07000000580 |
|
VISUAL
cropResistant
|
0d4d4d0c00080808,451144f4b4064145,c9c8b0b09088aa8e |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: BT/EE customers
• Method: Impersonation through a fake login page
• Exfil: Likely credentials harvesting
• Indicators: Free hosting, brand logo
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
🎯 Kit Endpoints
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:120,h:120,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:72,h:72,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:60,h:60,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:180,h:180,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:57,h:57,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:144,h:144,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:152,h:152,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=w:114,h:114,m
- //img1.wsimg.com/isteam/ip/7a17d71d-8d60-4865-9278-d2e9a6eb3bfb/BT%20%26%20EE%20NEW%20LOGO.jpeg/:/rs=h:182,cg:true,m/qt=q:100/ll
- https://ms.godaddy.com/r?e=eyJ2IjoiMS4xNCIsImF2Ijo1ODgwNjU5LCJhdCI6MjQ0NywiYnQiOjAsImNtIjo1OTI1Mjg3NDMsImNoIjo1NDQ0NSwiY2siOnt9LCJjciI6NjU3MDk3NTQxLCJkaSI6ImZkNWJlOGNmNzJjZTRlNjU4ZWZjYTgyZmU4OGYyYWMwIiwiZGoiOjAsImlpIjoiZjU0NjdmOTg5OWVmNDU3ZjhjMDlkNTJiNzYyZDc2NDgiLCJsZSI6WzJdLCJkbSI6MywiZmMiOjgzMTM0NjQxOSwiZmwiOjc5NTIyNjg3OCwiaXAiOiI2NC4yMDIuMTYwLjAiLCJudyI6MTA2NjMsInBjIjoxLCJvcCI6MSwibXAiOjEsImRwIjoxLCJkbiI6MSwiZGciOjEsImVjIjoxLCJnbSI6MCwiZXAiOm51bGwsInByIjoyNTA4MDQsInJ0IjoyLCJycyI6NTAwLCJzYSI6Ijg2Iiwic2IiOiJpLTBiYzI4ZmJlZWUyN2Q2MjU1Iiwic3AiOjE1MDU0NzAsInN0IjoxMjc2MjY0LCJ1ayI6InVlMS0xZjBmMDUyYmI2MWI0OWZkYWYyMDZlMDRjZDdkOWE0OCIsInpuIjozMDc0OTUsInptIjpbMzA3NDk1XSwidHMiOjE3Njk5NTA0MTI2MjgsInBuIjoiZ2Qtd2FtLXBvczEiLCJnYyI6dHJ1ZSwiZ0MiOnRydWUsImdzIjoibm9uZSIsImRjIjoxLCJ0eiI6IkFtZXJpY2EvVG9yb250byIsInVyIjoiaHR0cHM6Ly93d3cuZ29kYWRkeS5jb20vb25saW5lLW1hcmtldGluZy9zZW8tc2VydmljZXM_dXRtX3NvdXJjZT1ob3VzZS1rZXZlbC1hZCZ1dG1fY2FtcGFpZ249aG91c2Uta2V2ZWwtYWQifQ&s=Ax9mrZPksd_4lhQEEg-G2R0ZYU8&omsId=baseline&psName=WAM_BANNER_V1&uawVersion=2.0.7&property:publisher_website_key=wam.md5.9afcec0e98878df3aba237b7a0f42504&impressionId=f5467f9899ef457f8c09d52b762d7648
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 16 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site likely attempts to steal login credentials through a fake login form that redirects to the actual BT/EE website. Users enter their credentials and are redirected to the real site, unaware their information has been stolen.
Secondary Method: Malicious Redirection
Redirecting users to a phishing page after successful login is another common tactic.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.site-1enk6s1fm.godaddysites.com
Found 1 other scan for this domain