Phishing Analysis
Detailed analysis of captured phishing page
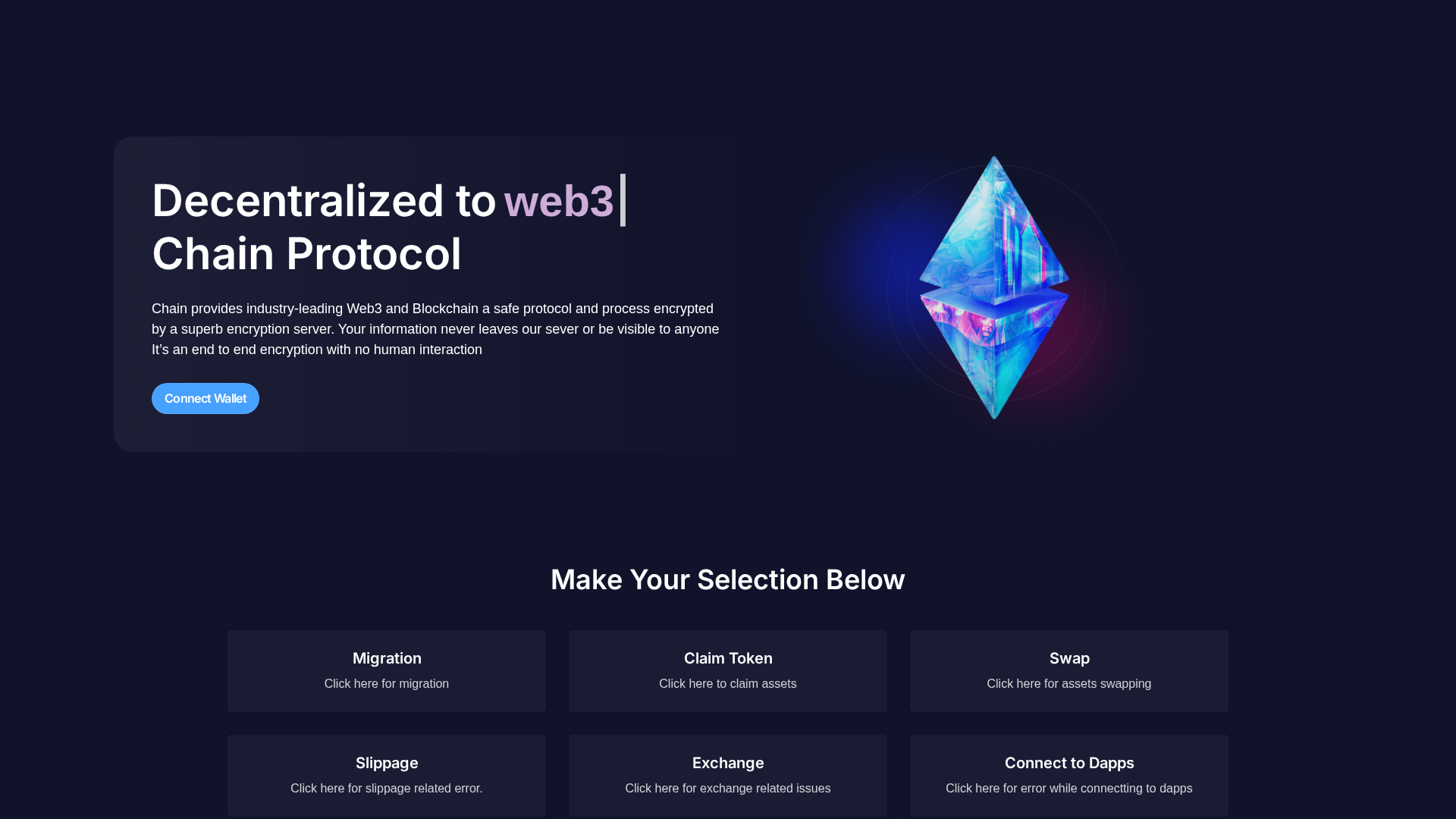
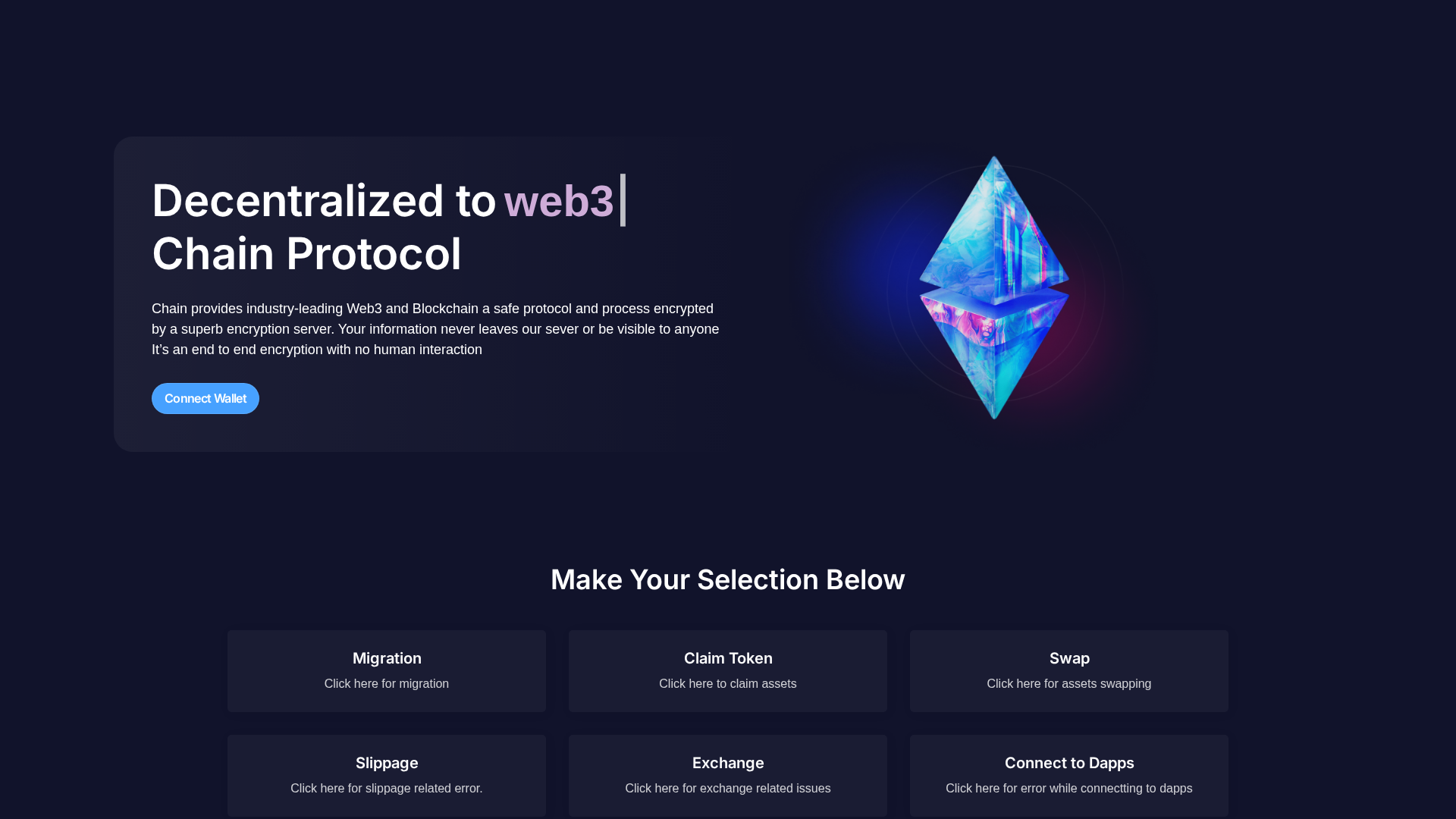
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13D42537A411C113693B35EABB520639EF6BBF66DCF3B04052BFC87944BE8E9A9C44500 |
|
CONTENT
ssdeep
|
192:xS6+TQTpQNiCq8M51dFIpByRcRsw2x0lLnCfJCVxw4dJMocfk7y7:xv2QTqQJCDdJM9cU |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d2f20d2d3d9292e3 |
|
VISUAL
aHash
|
0064ecf440183c7e |
|
VISUAL
dHash
|
328d8d8d8472d4d4 |
|
VISUAL
wHash
|
00f4fcf4c0187e7e |
|
VISUAL
colorHash
|
38006000080 |
|
VISUAL
cropResistant
|
328d8d8d8472d4d4 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://verify.walletconnect.com/293298e758398a25951f3ead4037ef37
📡 API Calls Detected
- stats
- https://
- https://api.telegram.org/bot
- 0x3b3b57de
- https://min-api.cryptocompare.com/data/pricemulti?fsyms=ETH,BNB,MATIC,AVAX,ARB,FTM,OP&tsyms=USD
- https://rpc.ankr.com/multichain/
- account
- logs
- https://api.wallet.coinbase.com/rpc/v2/desktop/chrome
- proxy
🔑 Telegram Bot Tokens (1)
- 8487102028:AAEK...GuJ6VIE4
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 118 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 118 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer checks balances of popular ERC-20 tokens (USDT, USDC, DAI, etc.) and only proceeds if total value exceeds minimum threshold.
📡 Telegram Command & Control Infrastructure
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for novelaevm.netlify.app
Found 1 other scan for this domain