Phishing Analysis
Detailed analysis of captured phishing page
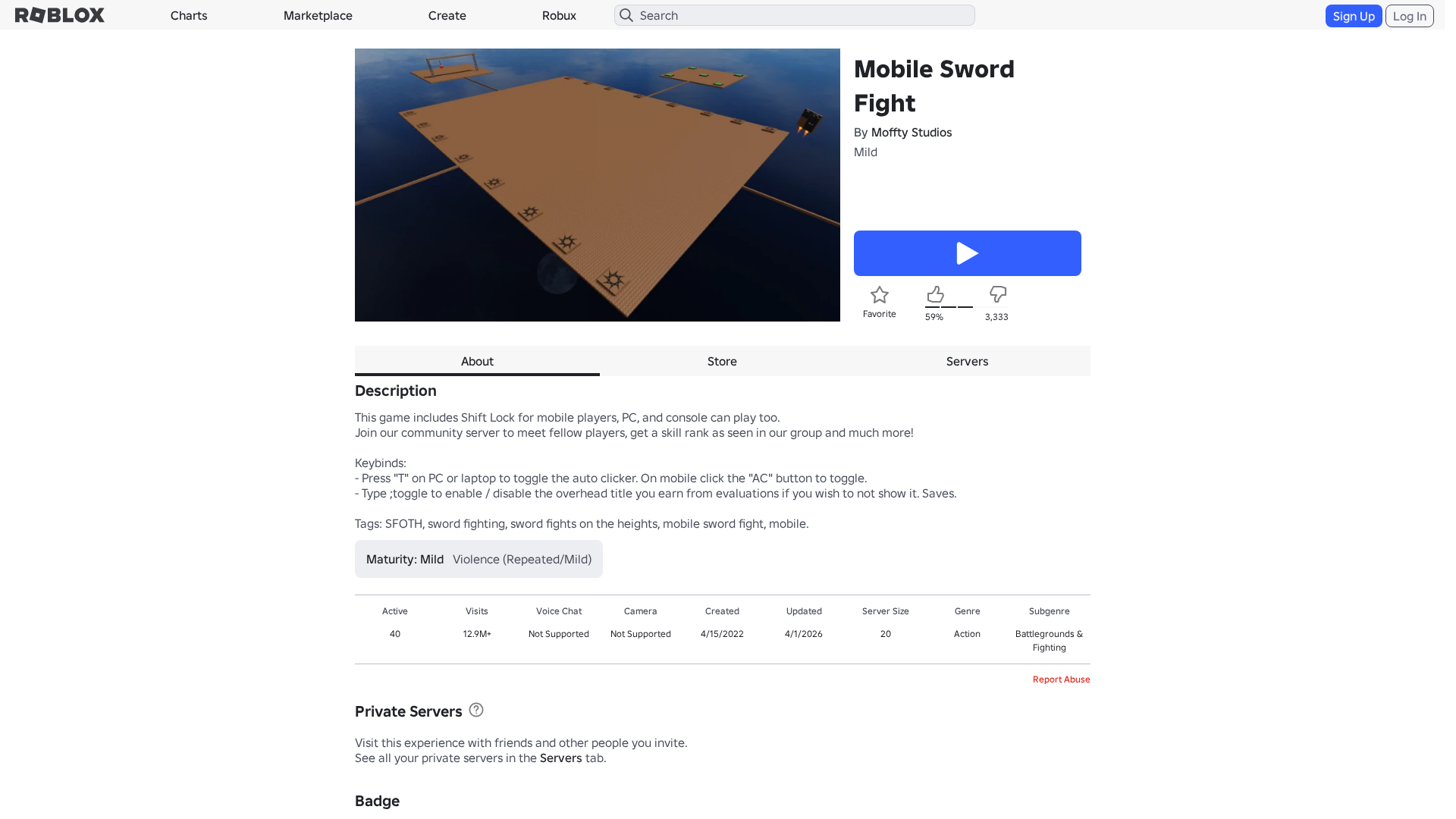
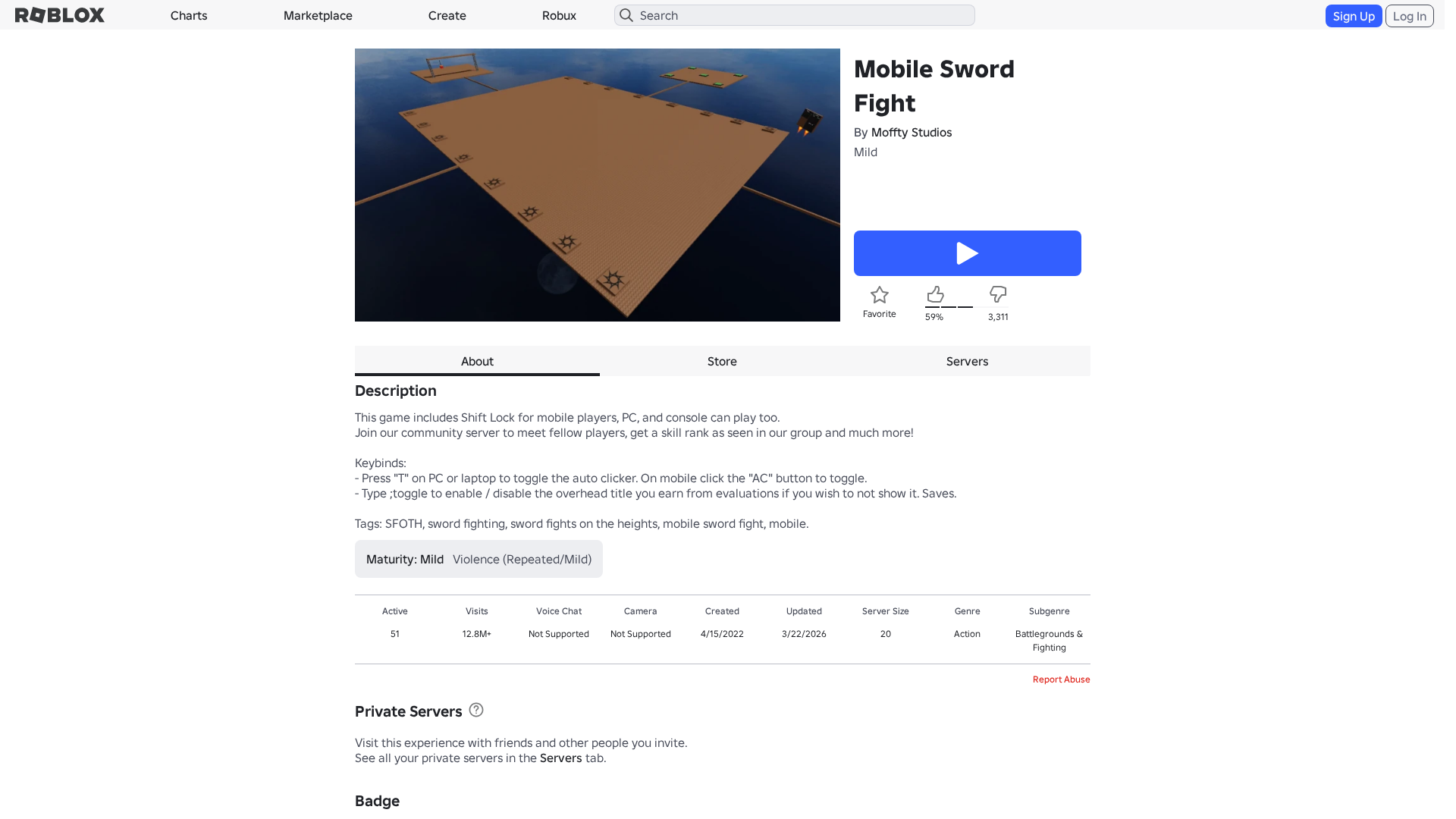
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D2139672A1211837A17FA6D9F159F315A1D3EB0FC68357E1A1E8A3760ADAC31FC1341A |
|
CONTENT
ssdeep
|
768:02GXW18rIW6Q9byqfQRk+rvrvEo3RpO9vBRIkFtdv0kTdiEK:02GXW18rv6Q9ujMq2XIaiEK |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b03016cfcfc9696c |
|
VISUAL
aHash
|
c7c7c3c7ffffffff |
|
VISUAL
dHash
|
8e2f8e1e341e1a38 |
|
VISUAL
wHash
|
02878383c7c7cbcf |
|
VISUAL
colorHash
|
07c02000040 |
|
VISUAL
cropResistant
|
8e2f8e1e341e1a38,04e1d8e46939335a |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- /info/blog?locale=en_us
- https://www.roblox.com.gl/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fgames%2F123549329464%2FMobile-Sword-Fight
- /login?returnUrl=
- https://www.roblox.com/catalog
📡 API Calls Detected
- https://help.roblox.com/hc/articles/30428367965460
- get
- https://ro.blox.com/Ebh5?
- GET
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
- https://apis.
- POST
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 208 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 208 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.roblox.com.gl
Found 10 other scans for this domain
-
https://www.roblox.com.gl/games/100705474040845/Ec...
https://www.roblox.com.gl/games/102168567330694/Ch...
https://www.roblox.com.gl/users/228584547867/profi...
https://www.roblox.com.gl/users/128263726413/profi...
https://www.roblox.com.gl/users/192423221447/profi...
https://www.roblox.com.gl/users/260017480254/profi...
https://www.roblox.com.gl/users/248629734179/profi...
https://www.roblox.com.gl/users/166267438083/profi...
https://www.roblox.com.gl/users/204843820165/profi...
https://www.roblox.com.gl/users/121056444703/profi...