Phishing Analysis
Detailed analysis of captured phishing page
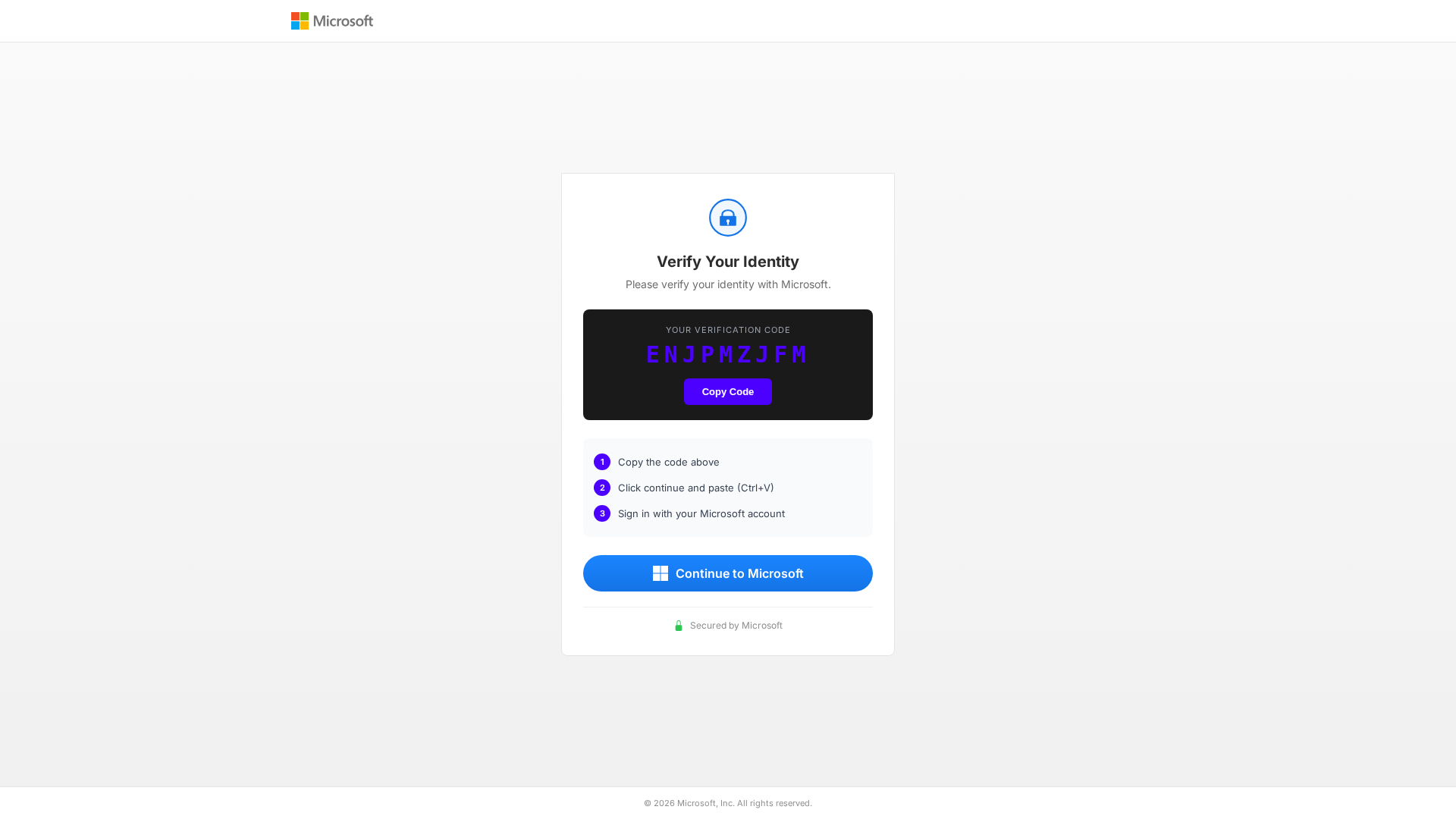
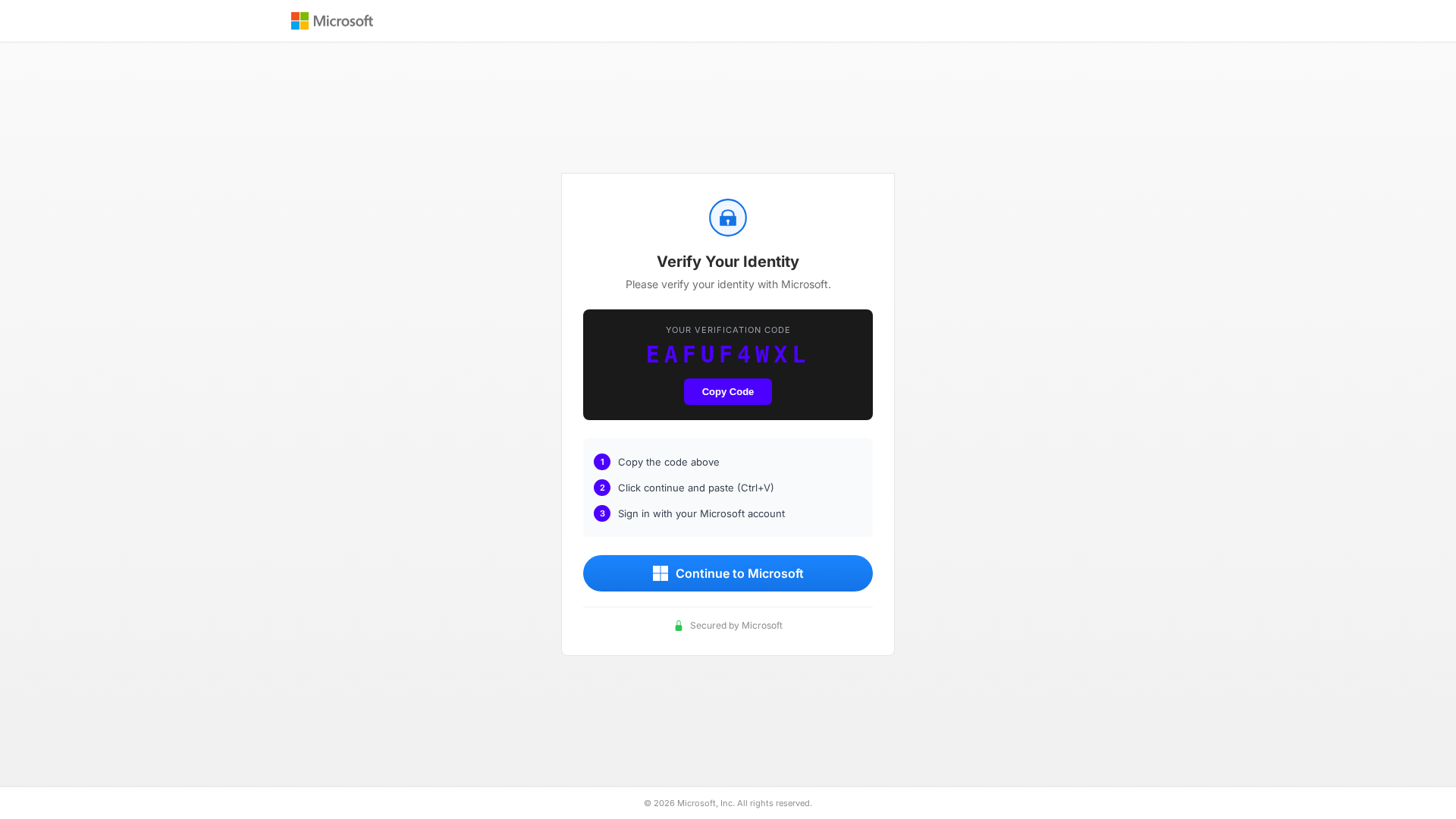
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T123E1843253188AEE96CD938C5B293B9E336592C4B27703406BD74264EC49EBBFC77950 |
|
CONTENT
ssdeep
|
96:T6jNt2NvO4DZ+Stb/jY+eo4hAryAes9mBYYQgWLDmy43oggGFlj6OIDi3auPq+:y2pToSBjlevudl9nN44PoED+6+ |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3a68c9933269d99 |
|
VISUAL
aHash
|
ffffe7e7e7e7ffff |
|
VISUAL
dHash
|
24320c4d4c4c2801 |
|
VISUAL
wHash
|
ffffffe700001800 |
|
VISUAL
colorHash
|
070000001d0 |
|
VISUAL
cropResistant
|
24320c4d4c4c2801,616941494d33334d |
Code Analysis
📡 API Calls Detected
- https://microsoft.com/devicelogin
📊 Risk Score Breakdown
🔬 Comprehensive Threat Analysis
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Brand Impersonation Redirect
Impersonates Microsoft to build victim trust through search engine manipulation or malicious advertisements. Often redirects to credential theft pages or serves malware disguised as legitimate software.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for secure-device-auth-office-com.dporozok.workers.dev
Found 1 other scan for this domain