Phishing Analysis
Detailed analysis of captured phishing page
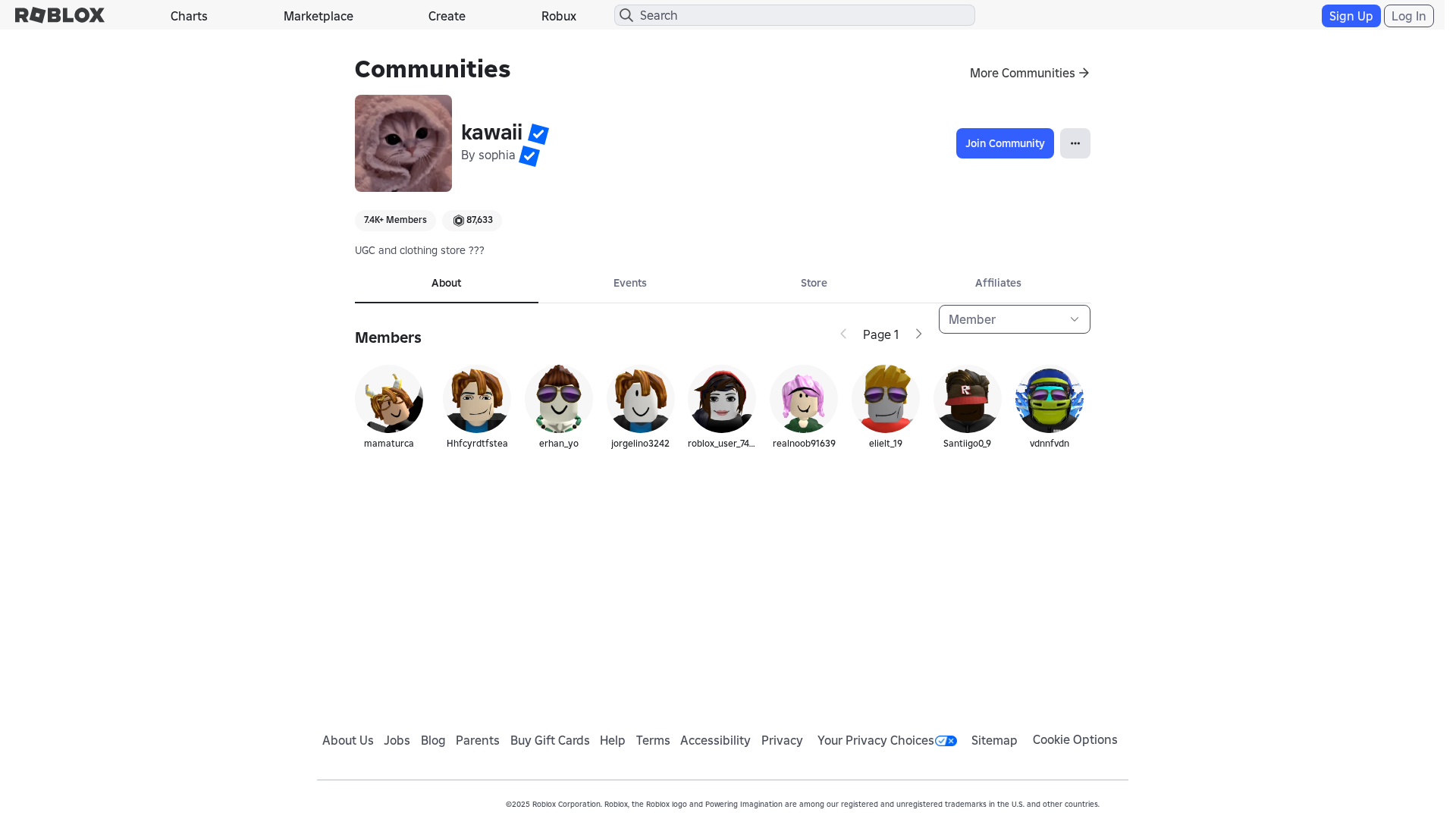
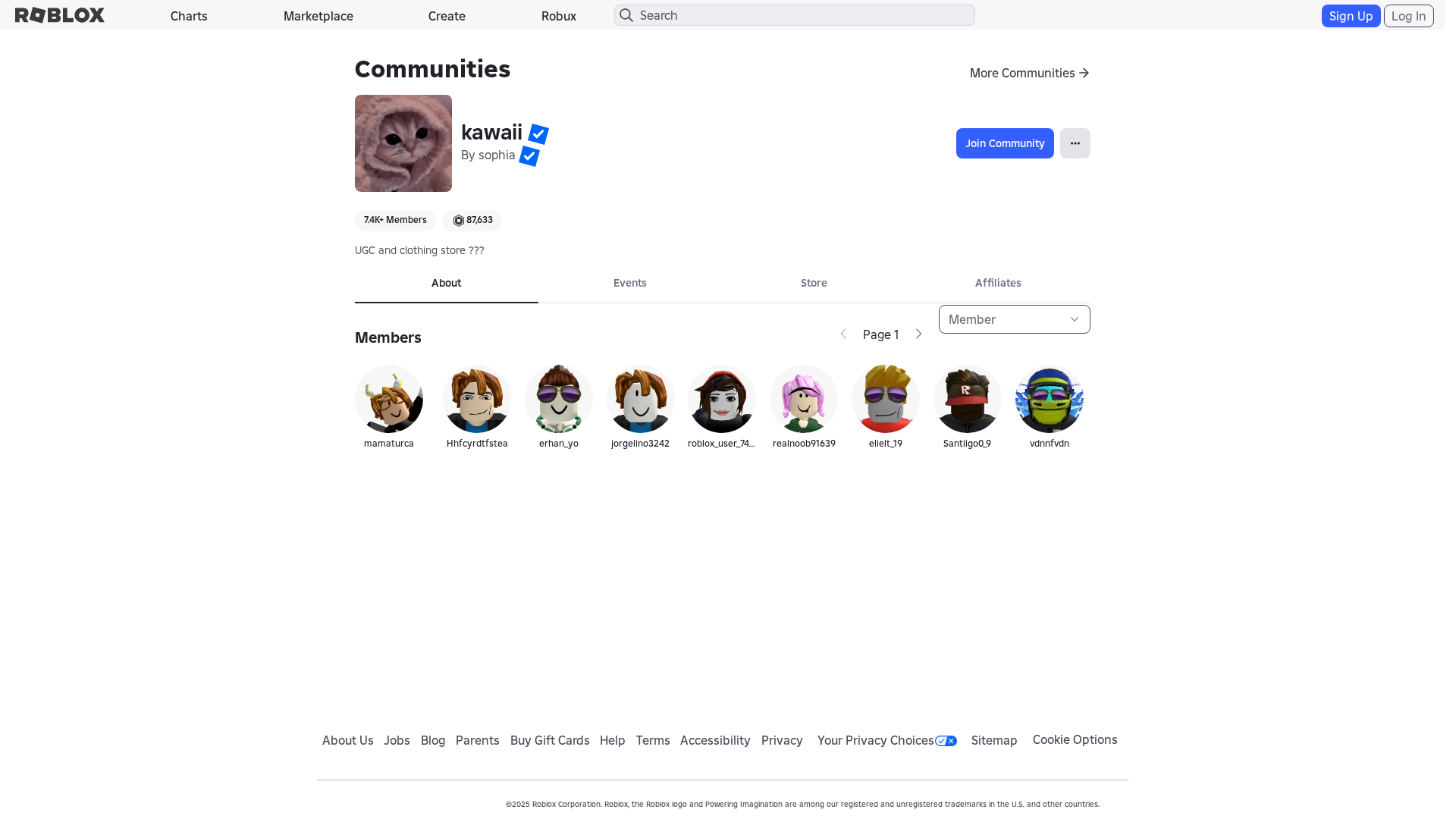
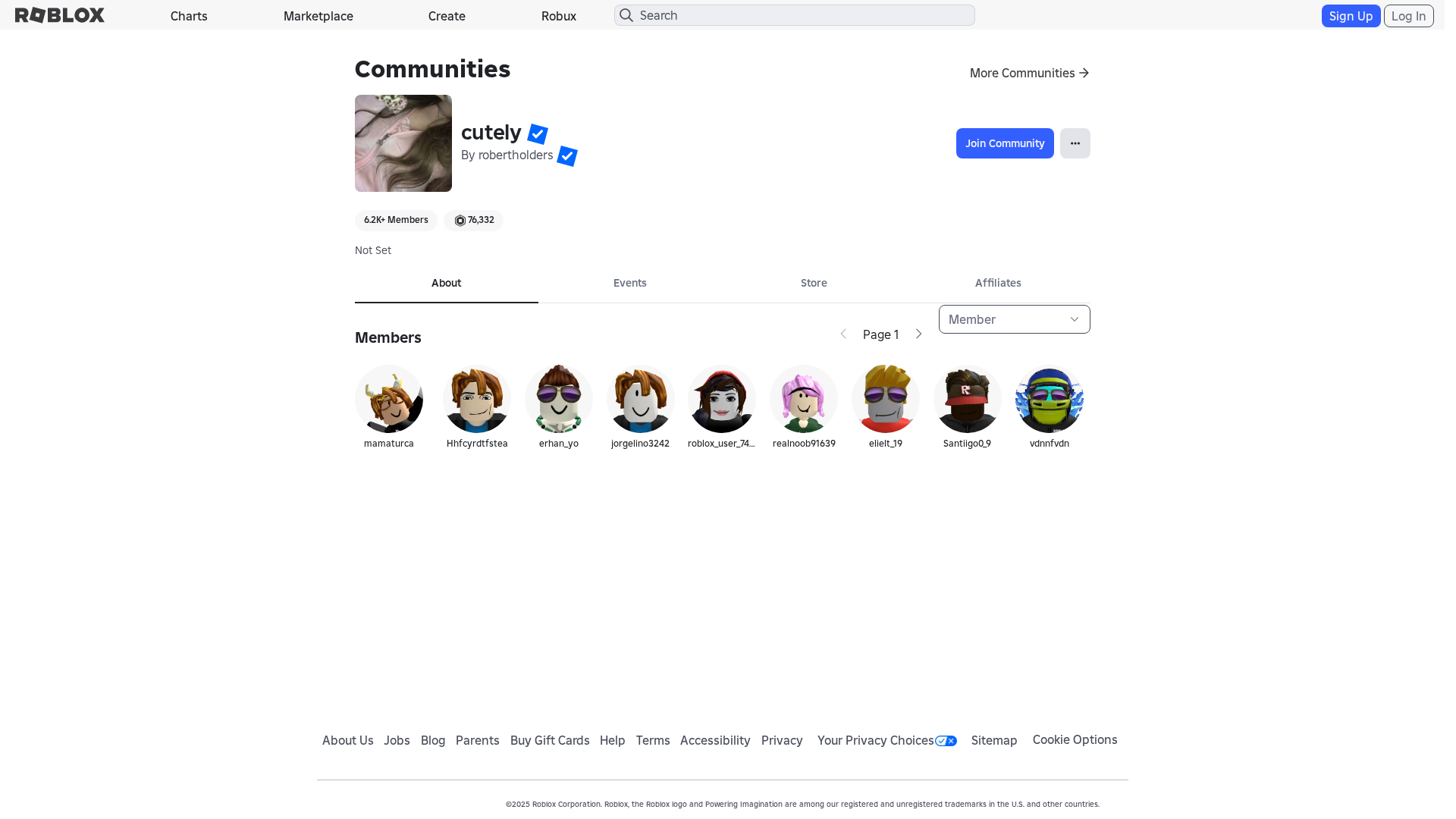
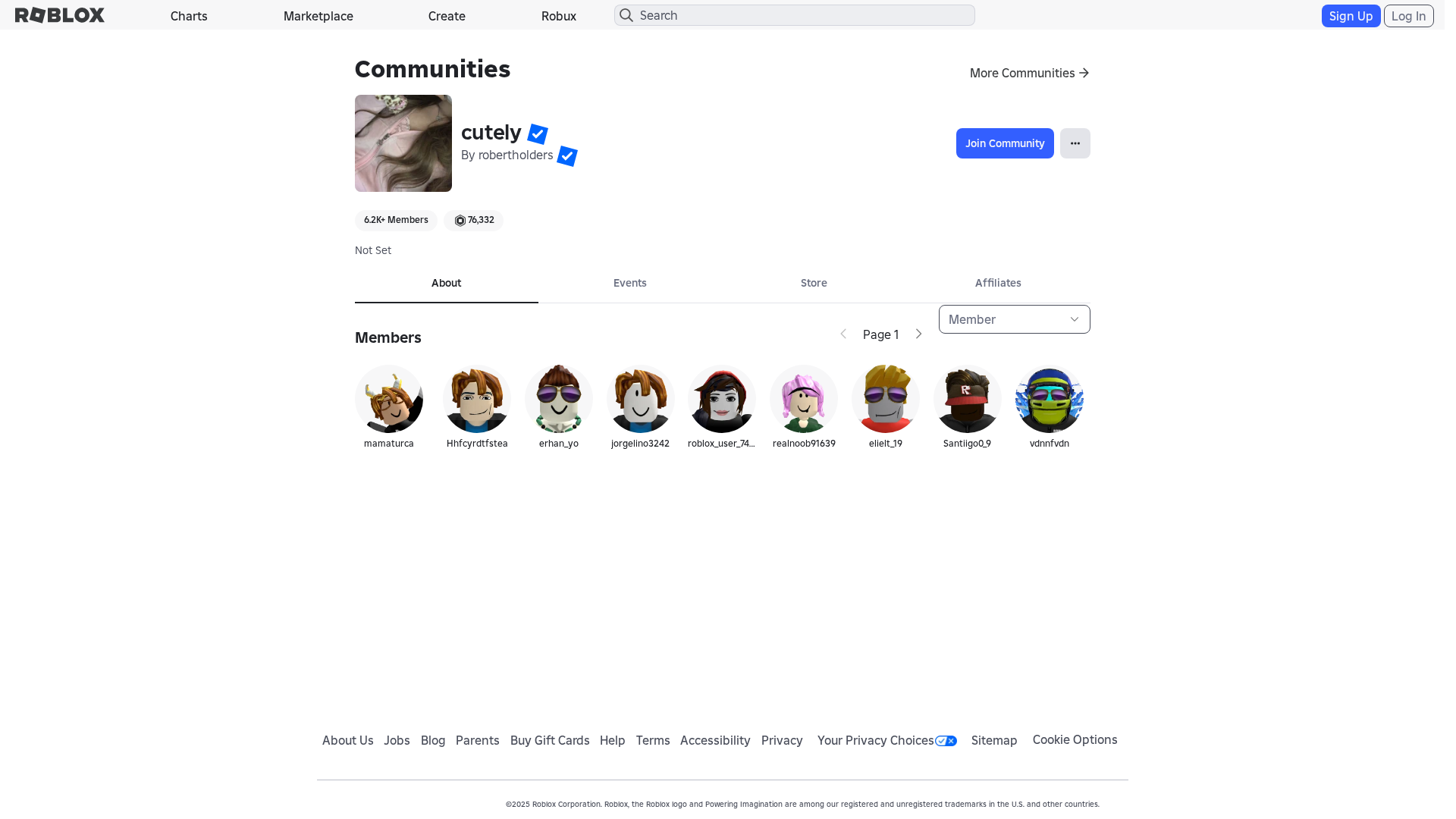
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11F53F9B193106837956F56C6F574BF0563E3DF4AC68286EAF1A8A32A0DD4C92FC07427 |
|
CONTENT
ssdeep
|
768:xAeXWZejLR+aXDzx2qf2uuOCuOx+sHMMSBmiEI:xAeXWZeXRPzxuOCuOx+tAiEI |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc3c9e9261c3c3c3 |
|
VISUAL
aHash
|
1a9bffc3c3ffffff |
|
VISUAL
dHash
|
b232201602000206 |
|
VISUAL
wHash
|
008b8383c3ffff81 |
|
VISUAL
colorHash
|
07200010080 |
|
VISUAL
cropResistant
|
b232201602000206 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Roblox users
• Method: Domain spoofing
• Exfil: Unknown, likely password and account information
• Indicators: Misspelled domain, Form actions: /search
• Risk: HIGH
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /login?returlUrl=919887925
- {{ $ctrl.getCatalogPageUrl() }}
- https://auth.roblox.com
- https://www.roblox.com/info/blog?locale=en_us
- /catalog
- https://accountinformation.roblox.com
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- get
- POST
- https://help.roblox.com/hc/articles/30428367965460
- https://apis.
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 183 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Domain Spoofing
The attacker registered a domain name that is very similar to the legitimate domain of the targeted brand (Roblox). This is done to trick users into thinking they are on the real website and to steal their credentials.
Secondary Method: Javascript Obfuscation
The use of javascript obfuscation techniques (atob, eval, fromCharCode) to hide malicious code that could exfiltrate user data, inject keyloggers, or redirect the user to a more dangerous page.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Functions: authenticatedUser, apiSiteRequestValidator
🔌 External APIs Abused
- account: null
- purpose: User authentication and data retrieval
📊 Attack Flow Diagram
User fills <input name='username'> → authenticatedUser() → fetch('https://api.roblox.com') → credentials sent to endpoint
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : Light
- : Light
- : None
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → authenticatedUser() → fetch('https://api.roblox.com') → credentials sent to endpoint
🎯 Malicious Files Identified
0c2a7c793ed0761b93b214956992ffb44014abcb404fd8bd2f9a7eb32ea0a600.jsMalicious Functions
authenticatedUserapiSiteRequestValidator
🌐 External APIs Abused
-
Roblox
Purpose: User authentication and data retrieval
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for robiox.co
Found 10 other scans for this domain
-
https://www.robiox.com.py/users/262683709646/profi...
https://www.robiox.com.am/users/1310878322/profile
https://www.robiox.com.ua/communities/4183949668/I...
https://www.robiox.com.am/users/7347444177/profile
https://robiox.com.af/games/18552244424/Kuriko-Tes...
https://www.robiox.com.am/users/4848485136/profile
https://www.robiox.com.am/users/6260607824/profile
https://www.robiox.com.ua/users/1370831435/profile
https://www.robiox.com.am/communities/1717646415/g...
https://www.robiox.com.am/games/75007449985844/Ste...