
Phishing Analysis
Detailed analysis of captured phishing page
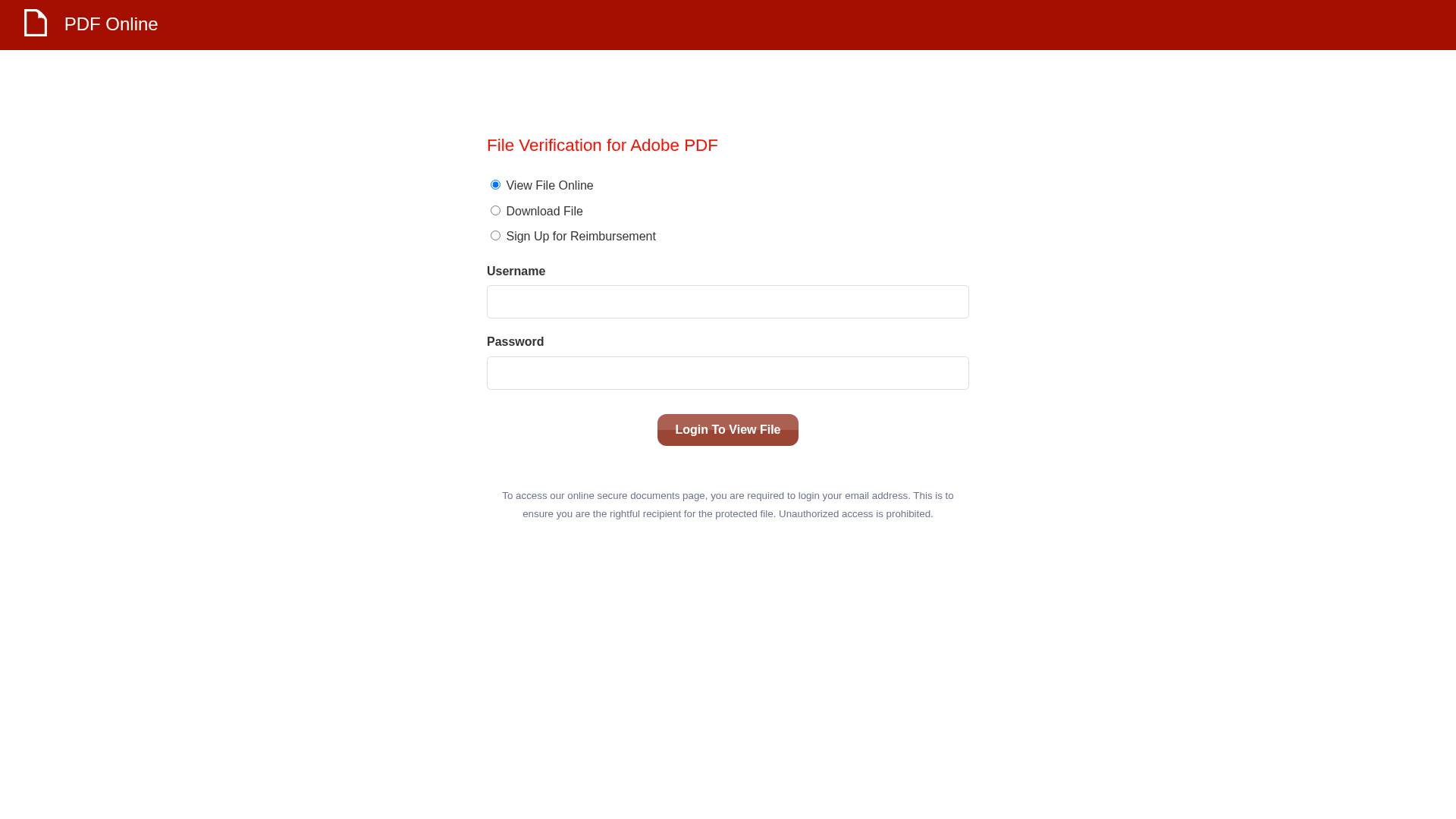
Visual Capture
Detection Info
http://currentnewsalerts.com/s/63bzgfsvbwsfcdx7y9/584dd8/90eab167-7429-489f-99f6-ce86e8d0d81a
Detected Brand
Adobe
Country
International
Confidence
95%
HTTP Status
200
Report ID
bd2a3a50-8d1…
Analyzed
2026-01-01 23:33
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17151623190449C7A2152D7ACB3D6FF0465CEC1A6CB0A6800A3F4E3CDEBE7D10CEA6599 |
|
CONTENT
ssdeep
|
48:nICYWVBcWzcYRlUxv8Tj1fRHgoMfc06pB+OTgl162phmzeVb8JoaTokg:n7JLREyRfRHgoMfX6KOTg2ywSNqomokg |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3395c66664c5c72 |
|
VISUAL
aHash
|
00ffffffe7ffffff |
|
VISUAL
dHash
|
2000140c0c140000 |
|
VISUAL
wHash
|
00cfc3c300003c3c |
|
VISUAL
colorHash
|
07000038000 |
|
VISUAL
cropResistant
|
1818100c0c140000,8040402020400000 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Adobe PDF phishing page for credential harvesting
• Target: Users expecting to view a PDF document, potentially widespread
• Method: Fake login form to steal username and password
• Exfil: Data likely sent to /site/submit based on form action
• Indicators: Domain mismatch (currentnewsalerts.com vs adobe.com), login form, 'Adobe PDF' branding
• Risk: HIGH - Credentials could be immediately used for account compromise.
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /site/submit
Scan History for currentnewsalerts.com
Found 9 other scans for this domain
-
https://currentnewsalerts.com/s/63bzgfsvbwsfcdx7y9...
http://test.currentnewsalerts.com/s/63BZGFSVBWSFCD...
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/...
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/...
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/...
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/...
http://currentnewsalerts.com/s/63bzgfsvbwsfcdx7y9/...
http://currentnewsalerts.com/s/63BZGFSVBWSFCDX7Y9/...
http://currentnewsalerts.com/s/63bzgfsvbwsfcdx7y9/...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.