Phishing Analysis
Detailed analysis of captured phishing page
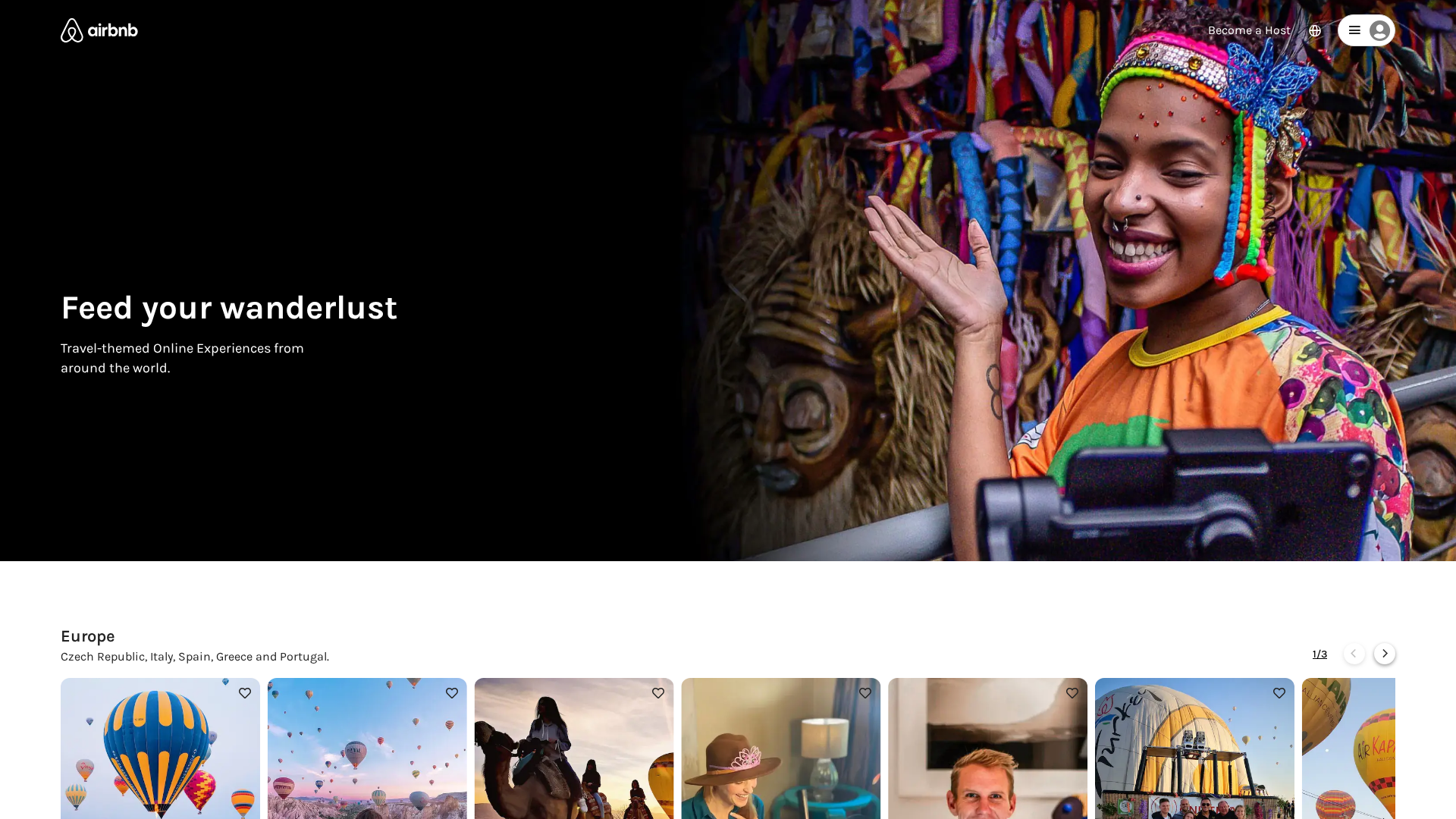
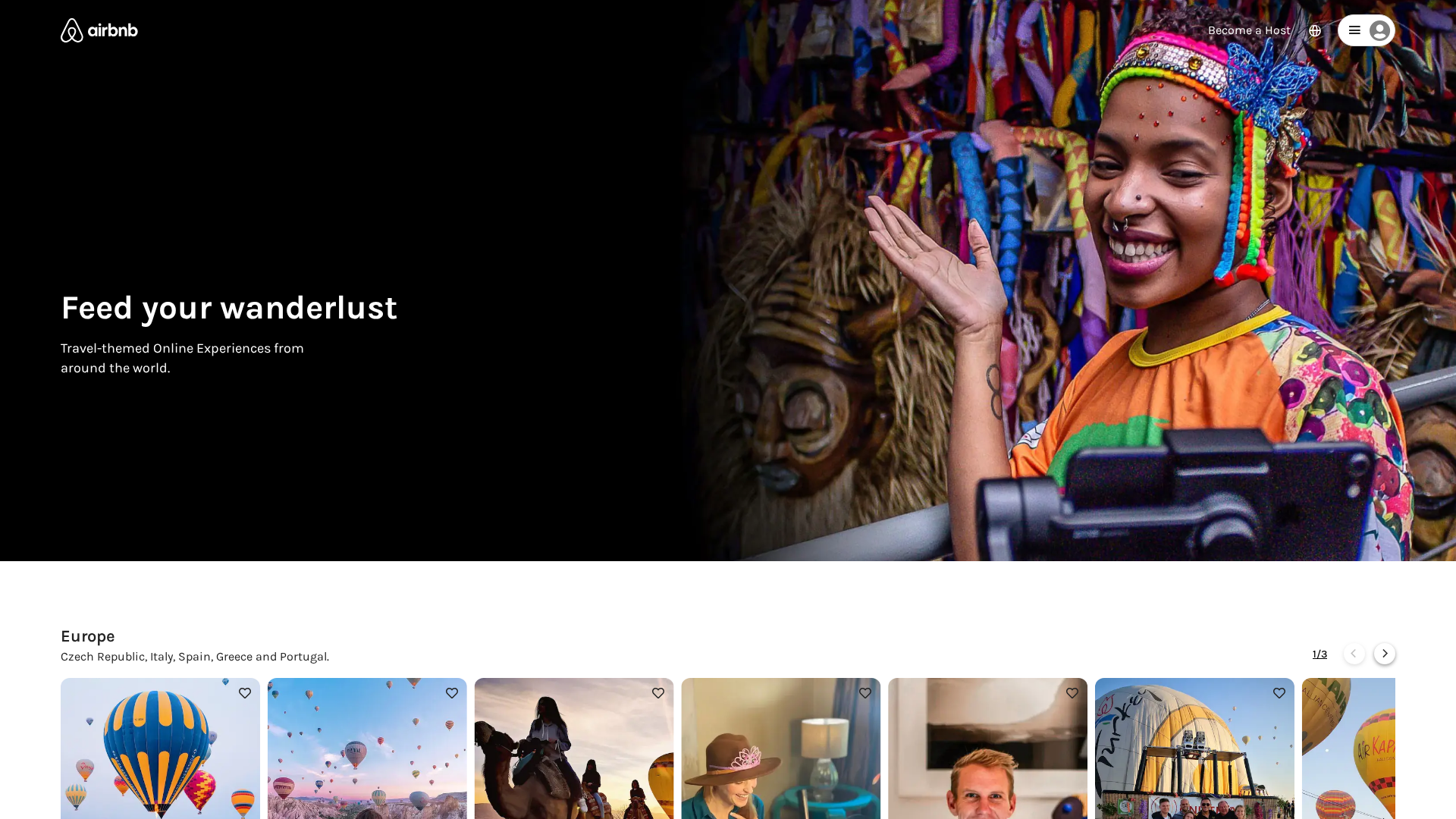
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1015332305160D5BF061BC3C4EB71976F32B48289EA8B056253FDC3568EEAC5ADF0AD64 |
|
CONTENT
ssdeep
|
1536:ccxQ80828g8u8L8p858R8B8v80828g8u8L8p858R8B8o80828g8u8L8p858R8B8C:b2H |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b315ed962acc5b0a |
|
VISUAL
aHash
|
0002040704ffffff |
|
VISUAL
dHash
|
1e1e989e0dd96753 |
|
VISUAL
wHash
|
0202060704ffffff |
|
VISUAL
colorHash
|
1a600008000 |
|
VISUAL
cropResistant
|
19c8f03a9a98fbfa,3cb836fefad9d9c8,195900d02563531d,1e1e1e9a9a1e1d19,65050c24646545ce,cccecef3b7e5454c,da98d85b1e365636 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Airbnb users
• Method: Impersonation via free hosting.
• Exfil: Unknown
• Indicators: Free hosting + brand logo.
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker likely aims to steal user credentials (username and password) by creating a fake login page that mimics the Airbnb website.
Secondary Method: Malicious Redirect
The site could redirect the user to a more sophisticated phishing attack, or a malware download, or to a site designed to steal financial information.
🌐 Infrastructure Indicators of Compromise
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for airbnb-clone-farukipekcom.vercel.app
Found 10 other scans for this domain
-
http://airbnb-clone-farukipekcom.vercel.app/stay.h...
http://www.airbnb-clone-farukipekcom.vercel.app
https://airbnb-clone-farukipekcom.vercel.app/onlin...
https://airbnb-clone-farukipekcom.vercel.app/index...
https://www.airbnb-clone-farukipekcom.vercel.app
https://airbnb-clone-farukipekcom.vercel.app/wande...
https://airbnb-clone-farukipekcom.vercel.app/index...
https://airbnb-clone-farukipekcom.vercel.app/flexi...
https://airbnb-clone-farukipekcom.vercel.app/exper...
https://airbnb-clone-farukipekcom.vercel.app/stay....