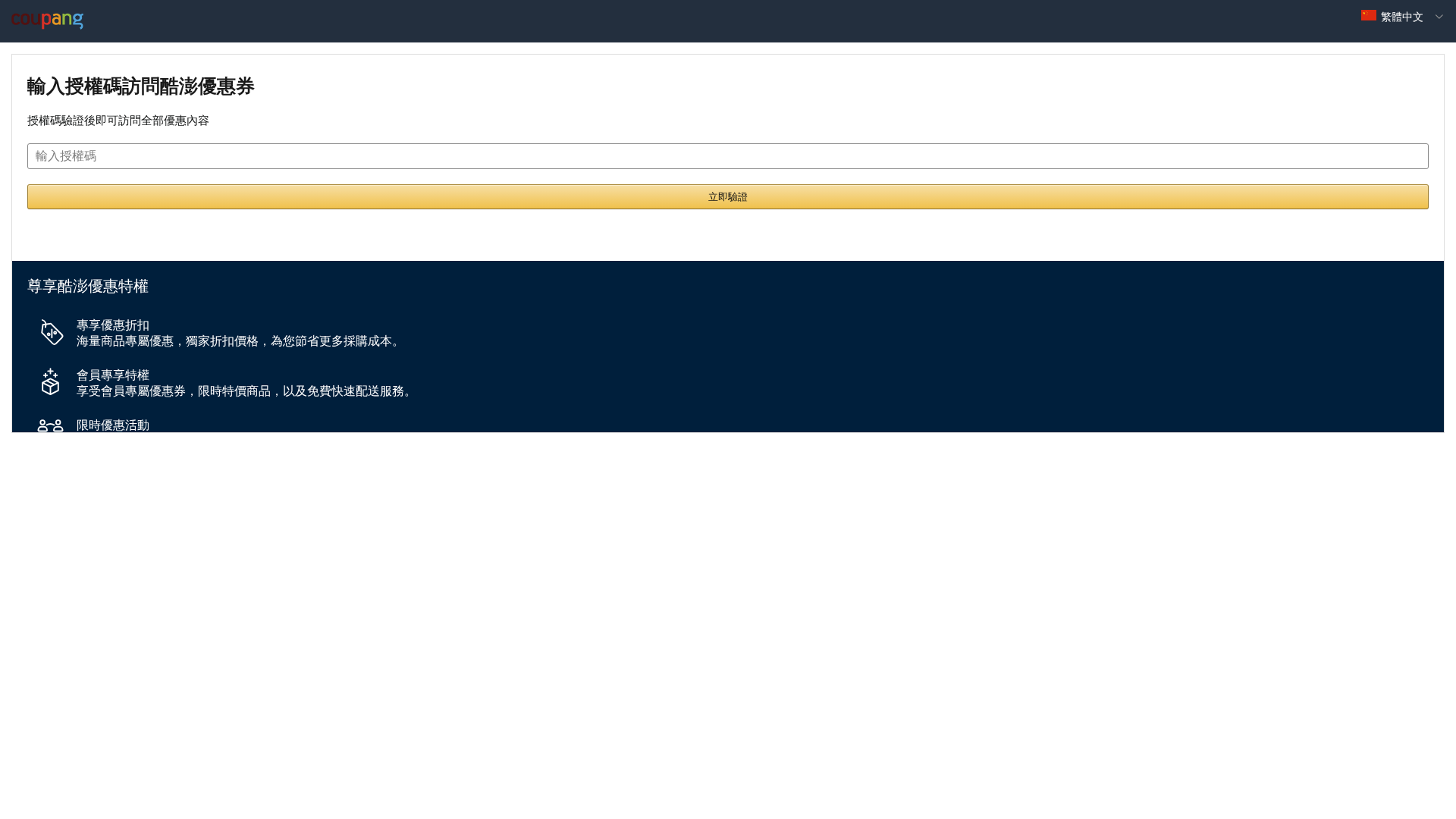
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
No screenshot available
Detection Info
http://coupangs.azureedge.net
Detected Brand
Coupang
Country
International
Confidence
100%
HTTP Status
200
Report ID
c1cdc2f9-a41…
Analyzed
2026-03-13 18:50
Final URL (after redirects)
https://192.252.182.34/#/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T186224534740238AB963B4AC1F4A15F1D3507E33AC6851D99B7A516627FCACE88D3B378 |
|
CONTENT
ssdeep
|
192:t+M9bUgSf54XJtPqDLbsoSsDWRvErEn45LfBaMcfYNqyTzhBeC3D:cMu54XLPeLbyEWTn45LfBarCtTzhBeCz |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
eb0b81807a7a7e9c |
|
VISUAL
aHash
|
00ff0000ffffffff |
|
VISUAL
dHash
|
d100011101000100 |
|
VISUAL
wHash
|
00ff000000ffffff |
|
VISUAL
colorHash
|
0f407000000 |
|
VISUAL
cropResistant
|
d0c9011121000000,0080014141000000,0000601080109060 |
Code Analysis
Risk Score
100/100
Threat Level
BAJO
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Legitimate Website
• Target: Coupang customers
• Method: Coupon Access
• Exfil: None
• Indicators: Authorization code request, branded content
• Risk: Low
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- GET
- POST
📊 Risk Score Breakdown
Total Risk Score
10/100
Contributing Factors
CDN Hosting
Legitimate CDN usage by Coupang.
Brand Match
Coupang Logo and branding present.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Coupang users (International)
Attack Method
Brand impersonation + obfuscated JavaScript
Exfiltration Channel
Unknown
Risk Assessment
CRITICAL - Automated credential harvesting with Unknown
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 55 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Coupang
⚔️ Attack Methodology
Primary Method: Coupon Verification
The site likely facilitates access to coupons, but without further information on the verification code process, it is difficult to determine malicious intent. The content is on a CDN for the brand.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
coupangs.azureedge.net
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.