
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
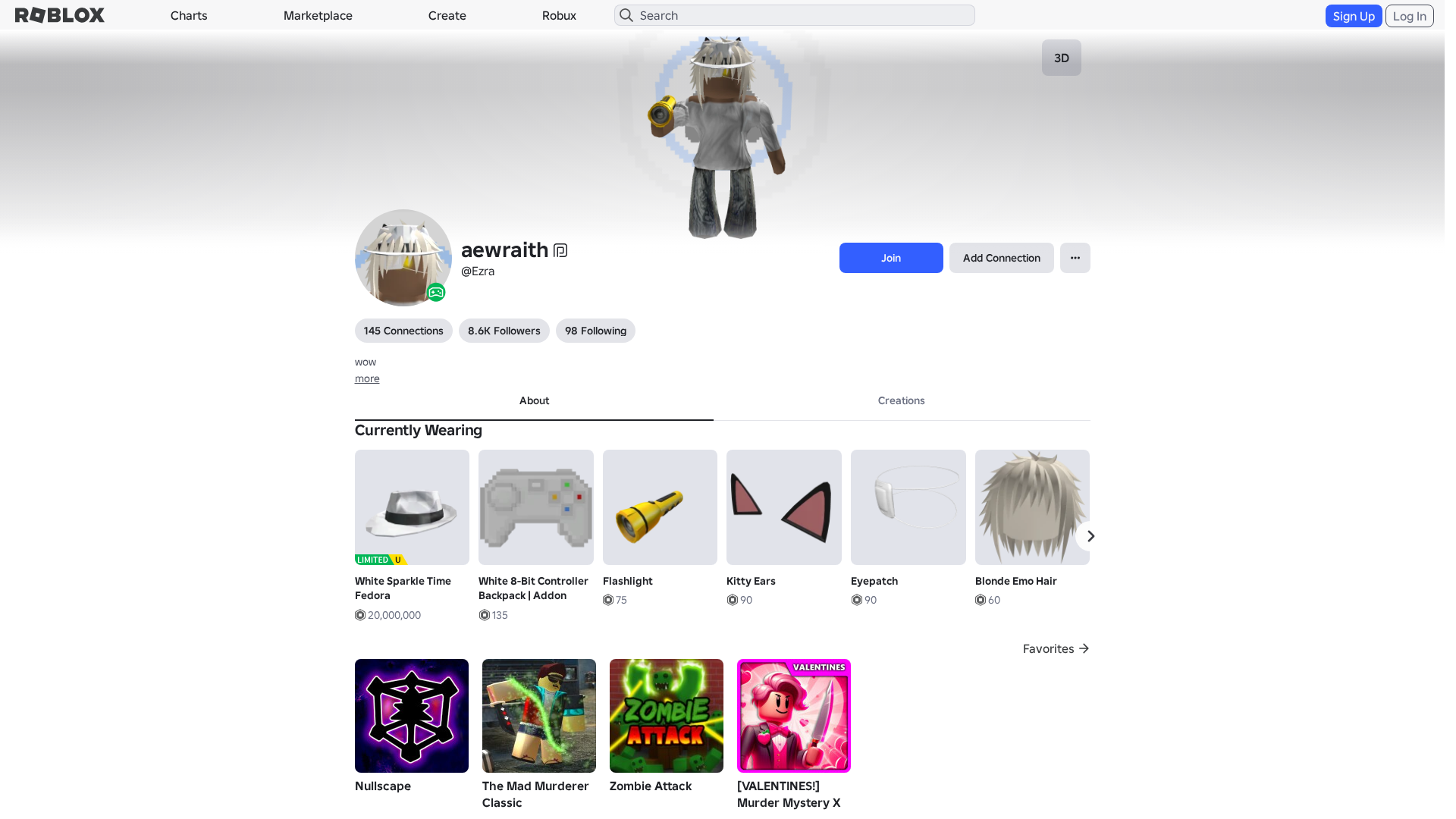
Detection Info
https://rblx.foo/s/T8Huil
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
c22db86a-be6…
Analyzed
2026-04-04 21:25
Final URL (after redirects)
https://www.robiox.com.py/users/384259844172/profile
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A1832F7292542837617B79DAF064672AD2D7C30FCA8346E1A2F8D39A0FD6CD1E96340D |
|
CONTENT
ssdeep
|
1536:I0wXWnermKTeYMsgN2g0ago3g/Kglig6PggugRKgoigcGgw+gMGgD6gmGgjcgYpM:zwXW9KG8MgRW7R044cbybqP9FbT15QSS |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b047324ddb9ccd38 |
|
VISUAL
aHash
|
0000d7ffc3fbc7c7 |
|
VISUAL
dHash
|
c8c826301a123d1d |
|
VISUAL
wHash
|
0000d7ffc3c3c7c7 |
|
VISUAL
colorHash
|
07200001001 |
|
VISUAL
cropResistant
|
c8c826301a123d1d,31a969ccc9e96971,77dba95b7a6a6858 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/93675237485386/Dougie
- https://api.injuries.lu/catalog/93101275362874/White-8-Bit-Controller-Backpack-Addon
- https://api.injuries.lu/catalog/73946479113094/Macarena
- https://api.injuries.lu/catalog/27493683/Tentacled-Alien-Left-Leg
- https://api.injuries.lu/catalog/105722319548703/Confess-to-Me
- https://api.injuries.lu/catalog/122281742555667/Glow-Motion-Animation-Pack
- https://api.injuries.lu/catalog/72213510878866/Glow-Motion-Animation-Pack
- https://api.injuries.lu/catalog/140499299581464/ORIGINAL-Electro-Shuffle
- https://api.injuries.lu/catalog/16983926843/white-long-sleeve
- https://api.injuries.lu/catalog/27493604/Tentacled-Alien-Torso
- https://api.injuries.lu/catalog/27493718/Tentacled-Alien-Right-Leg
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/2510233257/Rthro-Fall
- https://api.injuries.lu/catalog/116040770/Flashlight
- https://api.injuries.lu/catalog/85092320680319/Nonchalant-Sit
- https://api.injuries.lu/catalog/117205934652021/Yellow-Glowing-Eyes-Mood
- https://api.injuries.lu/catalog/78813763153341/Glow-Motion-Animation-Pack
- https://api.injuries.lu/catalog/147180077/Teal-Sparkle-Time-Fedora
- https://api.injuries.lu/catalog/140095450346434/Yellow-Glowing-Eyes-Head
- https://api.injuries.lu/catalog/104142334418357/BEST-Its-Gangnam-Style
- https://api.injuries.lu/catalog/130655908439646/Beat-Da-Koto-Nai
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F384259844172%2Fprofile
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/27402580/Action-Figure-Right-Arm
- https://api.injuries.lu/catalog/250395631/Dominus-Rex
- https://api.injuries.lu/catalog/892267099/Elder-Walk
- https://api.injuries.lu/catalog/1180419124/Disgraced-Baron-of-the-Federation
- https://api.injuries.lu/catalog/18676517458/Blonde-Emo-Hair
- https://api.injuries.lu/catalog/315549204/WC-Ultimates-Pink-Diamond-Distraction
- https://api.injuries.lu/catalog/1374269/Kitty-Ears
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F384259844172%2Fprofile
- https://api.injuries.lu/catalog/10321918782/eye-of-the-tiger
- https://api.injuries.lu/catalog/10369943613/8-Bit-Controller-Backpack
- /login?returnUrl=
- https://api.injuries.lu/catalog/138932314/Dominus-Aureus
- https://api.injuries.lu/catalog/27402641/Action-Figure-Left-Arm
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/138030172409402/Get-Jiggy
- https://api.injuries.lu/catalog/1016143686/White-Sparkle-Time-Fedora
- https://api.injuries.lu/catalog/4301204617/Eyepatch
📡 API Calls Detected
- https://apis.
- https://ro.blox.com/Ebh5?
- https://kyxn.dev/api/shorten
- /api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- POST
- /api/pageview
- https://help.roblox.com/hc/articles/30428367965460
- get
- https://kyxn.dev${e.endpoint}
- GET
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
rblx.foo
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for rblx.foo
Found 10 other scans for this domain
-
https://rblx.foo/s/Gccp6u
https://rblx.foo/s/cyFAoF
https://rblx.foo/s/J3h4AL
https://rblx.foo/s/myroblox
https://rblx.foo/s/1p8tkN
https://rblx.foo/s/roblox-com-users-3324118
https://rblx.foo/s/www-roblox-coms
https://rblx.foo/s/users243671918813profile
https://rblx.foo/s/roblox-com-users-3110201
https://rblx.foo/s/robIox-profiIe

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.