
Phishing Analysis
Detailed analysis of captured phishing page
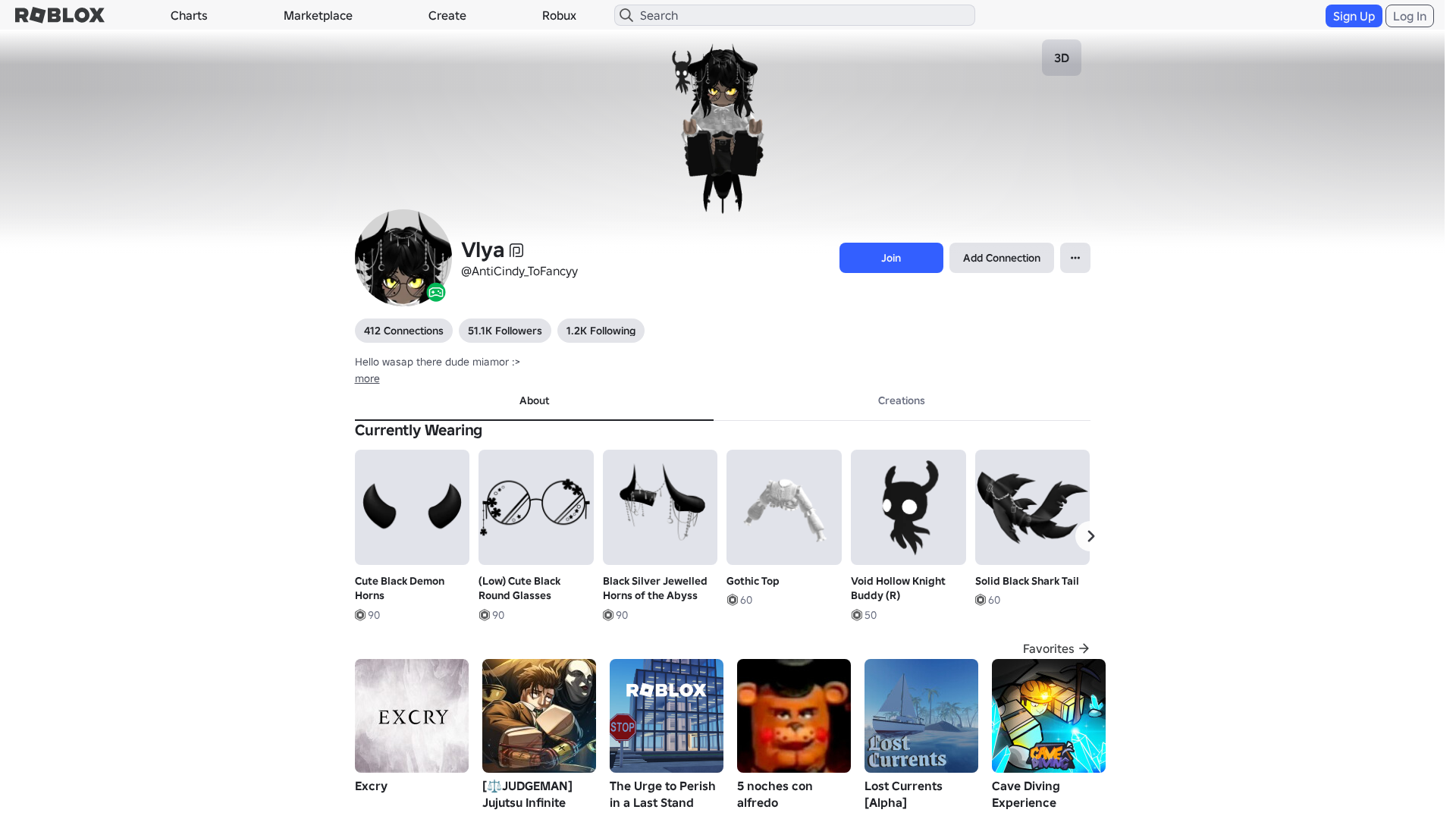
Visual Capture
Detection Info
https://roblx.me/s/roblox-com-users-9303833
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
c2e27eec-1d2…
Analyzed
2026-03-31 22:26
Final URL (after redirects)
https://www.robiox.com.py/users/375237184373/profile
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13073217292542837617B79DAF064672AE2D3D70FCA8346E1A2F8D39A0FD6CD1E85340D |
|
CONTENT
ssdeep
|
1536:VXB+jmXWnGrNXLeThsgXSggigu6gVtgw2gUpgg9g6CAAgPGgrcghSg8ngRBgQLgF:Vx+jmXWkXQ8iJhsv3CAdTnYK5pNratAY |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e4966343d1dc9c6c |
|
VISUAL
aHash
|
0020dfffc3fbc3c3 |
|
VISUAL
dHash
|
c8e8363016328f0e |
|
VISUAL
wHash
|
0000dfffc3d3c3c3 |
|
VISUAL
colorHash
|
07203008040 |
|
VISUAL
cropResistant
|
c8e8363016328f0e,71070c7179796959,0707373b33f78aa9,a63622b9d8c5edcc |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/376532000/ROBLOX-Boy-Torso
- https://www.roblox.com/catalog
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/619511648/Stylish-Idle
- https://api.injuries.lu/catalog/85361710130557/Caramelldansen
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F375237184373%2Fprofile
- https://api.injuries.lu/catalog/131005273065361/New-Woman-Left-Leg
- https://api.injuries.lu/catalog/78320358510723/New-Woman-Left-Arm
- https://api.injuries.lu/catalog/12518865418/Goth-Black-Dress
- https://api.injuries.lu/catalog/15134871898/Gothic-Top
- https://api.injuries.lu/catalog/95994802383292/New-Woman-Right-Arm
- https://api.injuries.lu/catalog/6803411196/emo
- https://api.injuries.lu/catalog/15416339423/Cute-Black-Demon-Horns
- https://api.injuries.lu/catalog/17519048492/Low-Cute-Black-Round-Glasses
- https://api.injuries.lu/catalog/619509955/Stylish-Climb
- https://api.injuries.lu/catalog/89442954912298/Solid-Black-Shark-Tail
- https://api.injuries.lu/catalog/71287495602943/Animated-Cute-Chibi-Eyes-Yellow-Dynamic-Head
- https://api.injuries.lu/catalog/619511417/Stylish-Fall
- https://api.injuries.lu/catalog/103040723950430/Gojo-Floating-Pose-The-Honored-One
- https://api.injuries.lu/catalog/93050802813054/New-Woman-Right-Leg
- https://api.injuries.lu/catalog/619512153/Stylish-Run
- https://api.injuries.lu/catalog/139435106875573/L-Lawliet
- /login?returnUrl=
- https://api.injuries.lu/catalog/76687759281618/Void-Hollow-Knight-Buddy-R
- https://api.injuries.lu/catalog/74638912161168/Black-Silver-Jewelled-Horns-of-the-Abyss
- https://api.injuries.lu/catalog/104982678489677/Gothic-Layered-Ruffle-Mini-Skirt-with-Belt
- https://api.injuries.lu/catalog/619511974/Stylish-Jump
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://api.injuries.lu/catalog/619512767/Stylish-Walk
- https://api.injuries.lu/catalog/619512450/Stylish-Swim
- https://api.injuries.lu/catalog/99564395067504/New-Woman-Hair
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F375237184373%2Fprofile
📡 API Calls Detected
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev/api/shorten
- https://help.roblox.com/hc/articles/30428367965460
- GET
- https://ro.blox.com/Ebh5?
- https://apis.
- get
- POST
- /api/shorten
- https://kyxn.dev${e.endpoint}
- /api/pageview
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
roblx.me
Registered
2026-03-28 03:56:41+00:00
Registrar
NameCheap, Inc.
Status
Recently registered (3 days old)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for roblx.me
Found 9 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.