
Phishing Analysis
Detailed analysis of captured phishing page
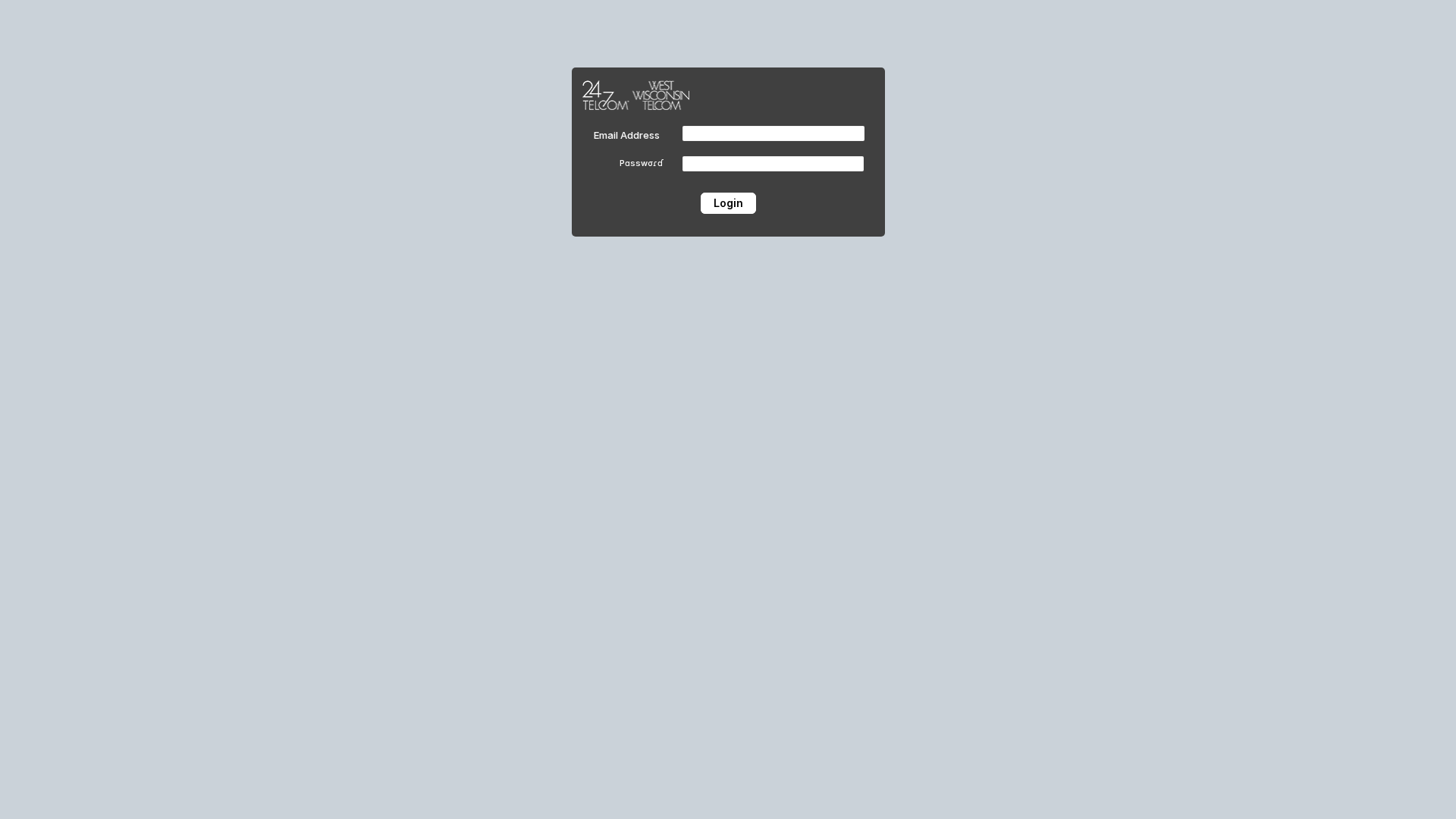
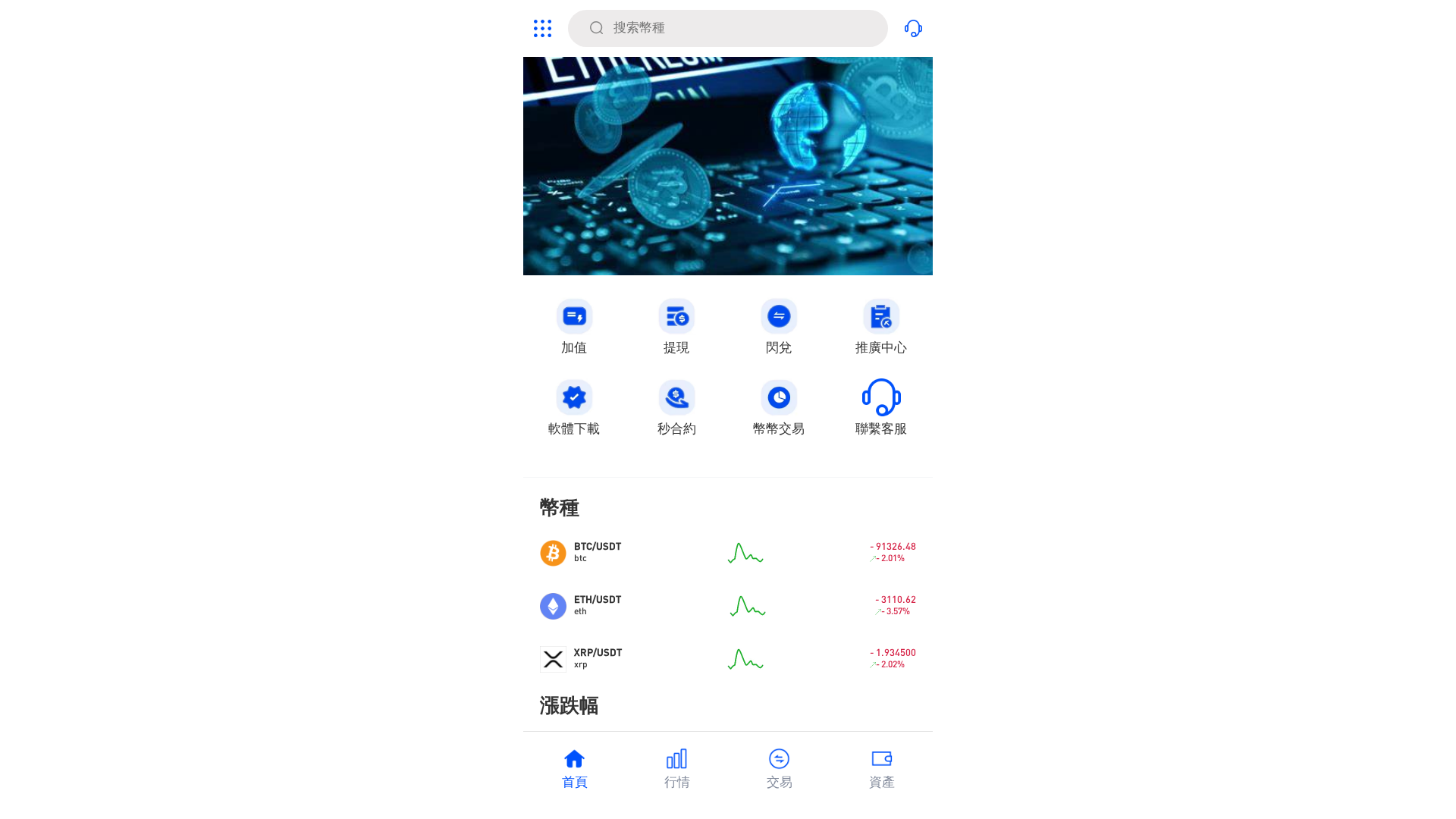
Visual Capture
Detection Info
https://grateful-aspects-830309.framer.app/
Detected Brand
24/7 Telecom / West Wisconsin Telecom
Country
USA
Confidence
100%
HTTP Status
200
Report ID
c36e9031-d1a…
Analyzed
2026-02-11 04:11
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E0225233B200DD294A9B56CCF1C49688415EC346FB3108CAB1A491FF7BC4DF0699A7AD |
|
CONTENT
ssdeep
|
192:skf7I0cqcechzz4vy9AKeMcnthWeNWbZfMmUU8VCosIW:ncqcechH4vuffMmUFCosD |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b333338ccccccccc |
|
VISUAL
aHash
|
e7e7e7ffffffffff |
|
VISUAL
dHash
|
4d4d4d320c000000 |
|
VISUAL
wHash
|
0707273f0f0f0f0f |
|
VISUAL
colorHash
|
07000000000 |
|
VISUAL
cropResistant
|
4d4d4d320c000000,4049b2b2beb2b232 |
Code Analysis
Risk Score
76/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: 24/7 Telecom / West Wisconsin Telecom users
• Method: Credential harvesting via login form
• Exfil: Obfuscated script likely sending credentials
• Indicators: Framer.app, obfuscation, login form
• Risk: High
🔒 Obfuscation Detected
- fromCharCode
- base64_strings
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Domain mismatch
The domain is not a legitimate domain for 24/7 Telecom / West Wisconsin Telecom.
Hosting on Framer.app
Free hosting service often used for phishing.
JavaScript Obfuscation
Obfuscation is often used to hide malicious code
Impersonation
The site attempts to impersonate 24/7 Telecom / West Wisconsin Telecom.
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
24/7 Telecom / West Wisconsin Telecom users (USA)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 10 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
24/7 Telecom / West Wisconsin Telecom
Fake Service
Login Portal
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The site mimics a login page for 24/7 Telecom / West Wisconsin Telecom, prompting users to enter their email and password. These credentials are then harvested by the attacker.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
grateful-aspects-830309.framer.app
Registered
None
Registrar
None
Status
Active
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Total Code Size
26.1 KB
🔗 API Endpoints Detected
Other
4
🔐 Obfuscation Detected
- : Light
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/e937158b39e7.png
Apr 08, 2026
Unknown
https://gfhfsw.weebly.com/
Mar 18, 2026
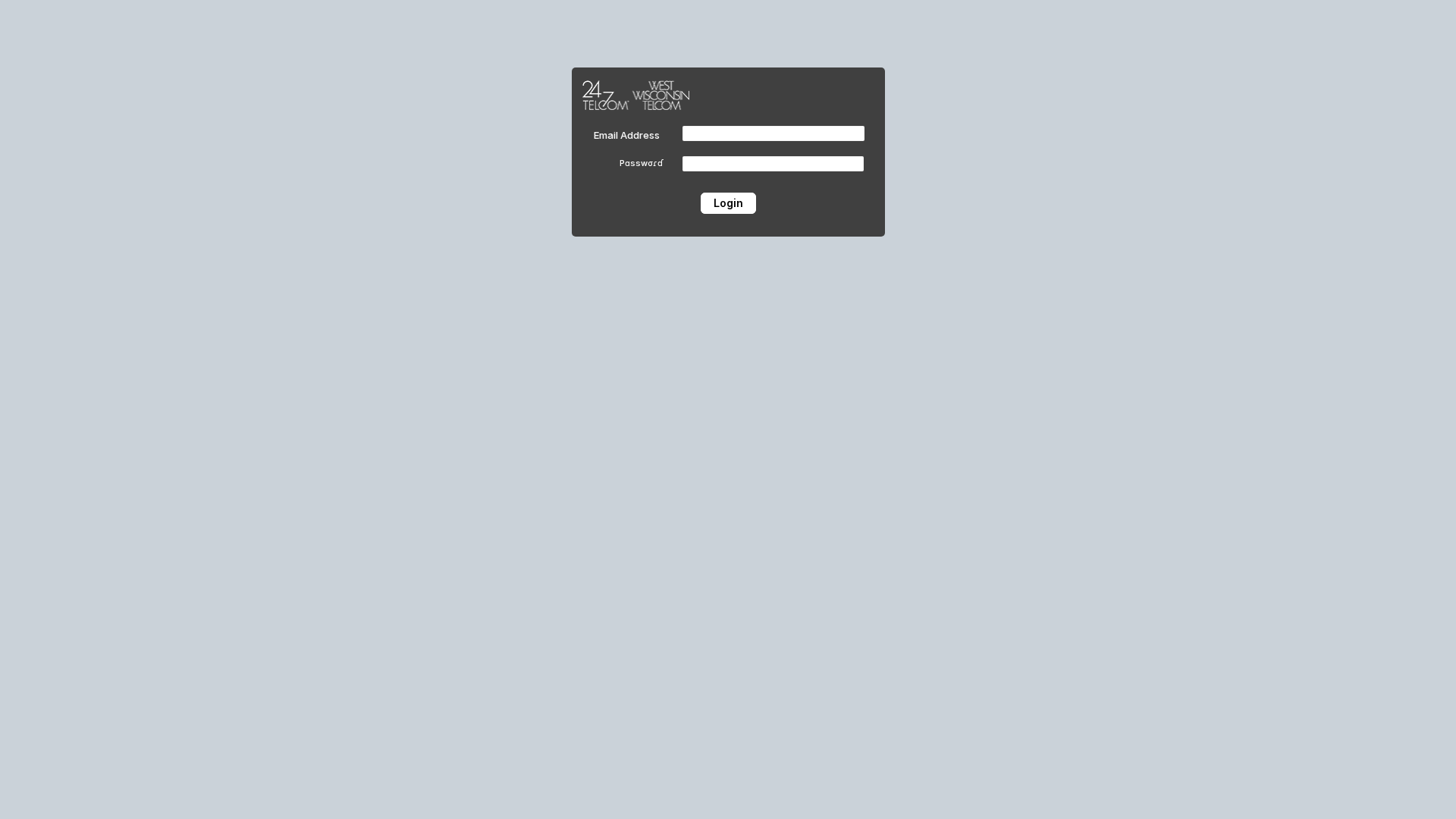
24/7 Telecom
https://grateful-aspects-830309.framer.app/
Feb 11, 2026
Geminis Pro
http://gxh5.geminis-pro.com
Jan 20, 2026
No screenshot
PancakeSwap
https://pancakeswap.finance-beta-service-alpha-online.pro/
Jan 01, 2026
Scan History for grateful-aspects-830309.framer.app
Found 1 other scan for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.