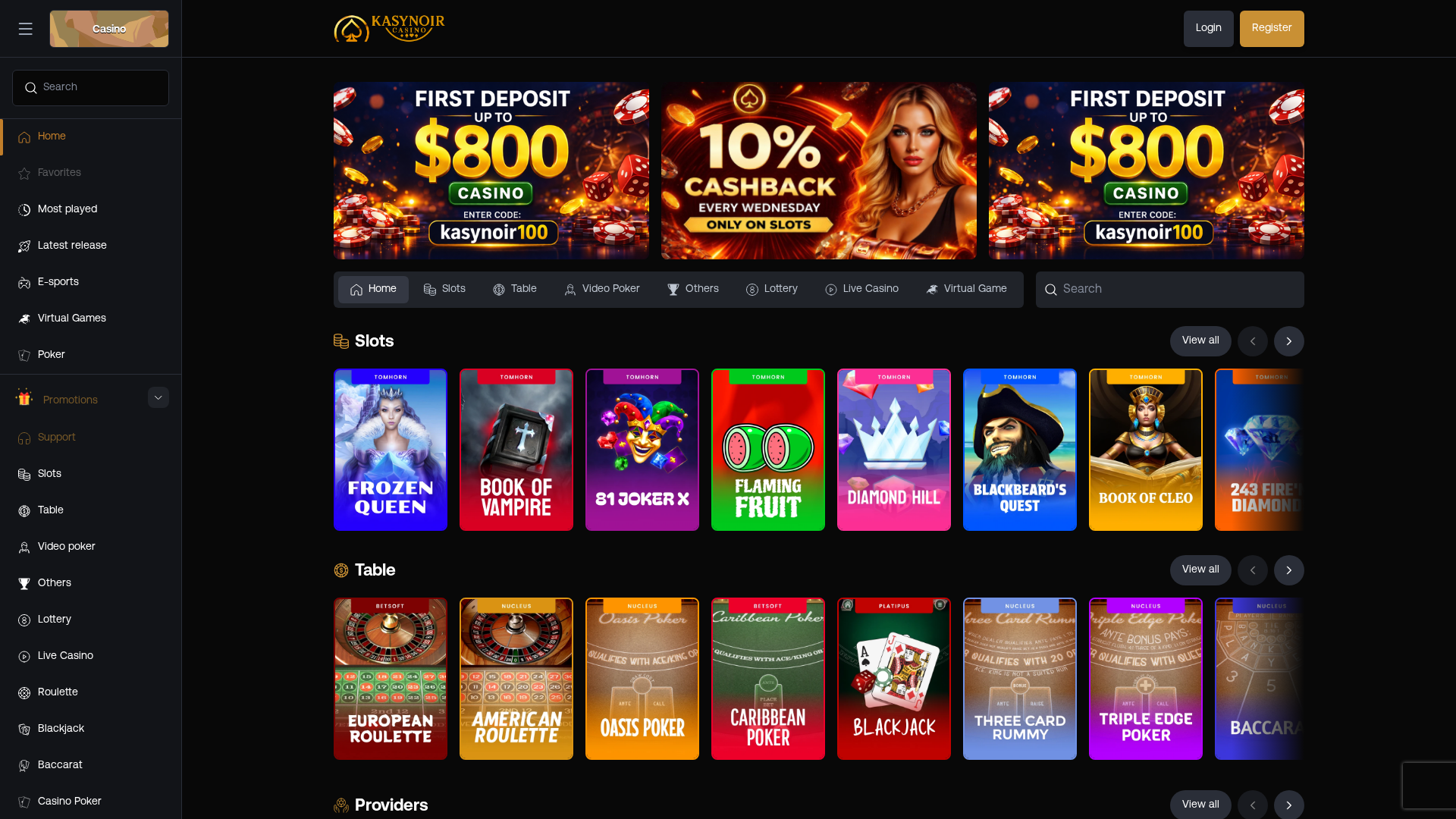
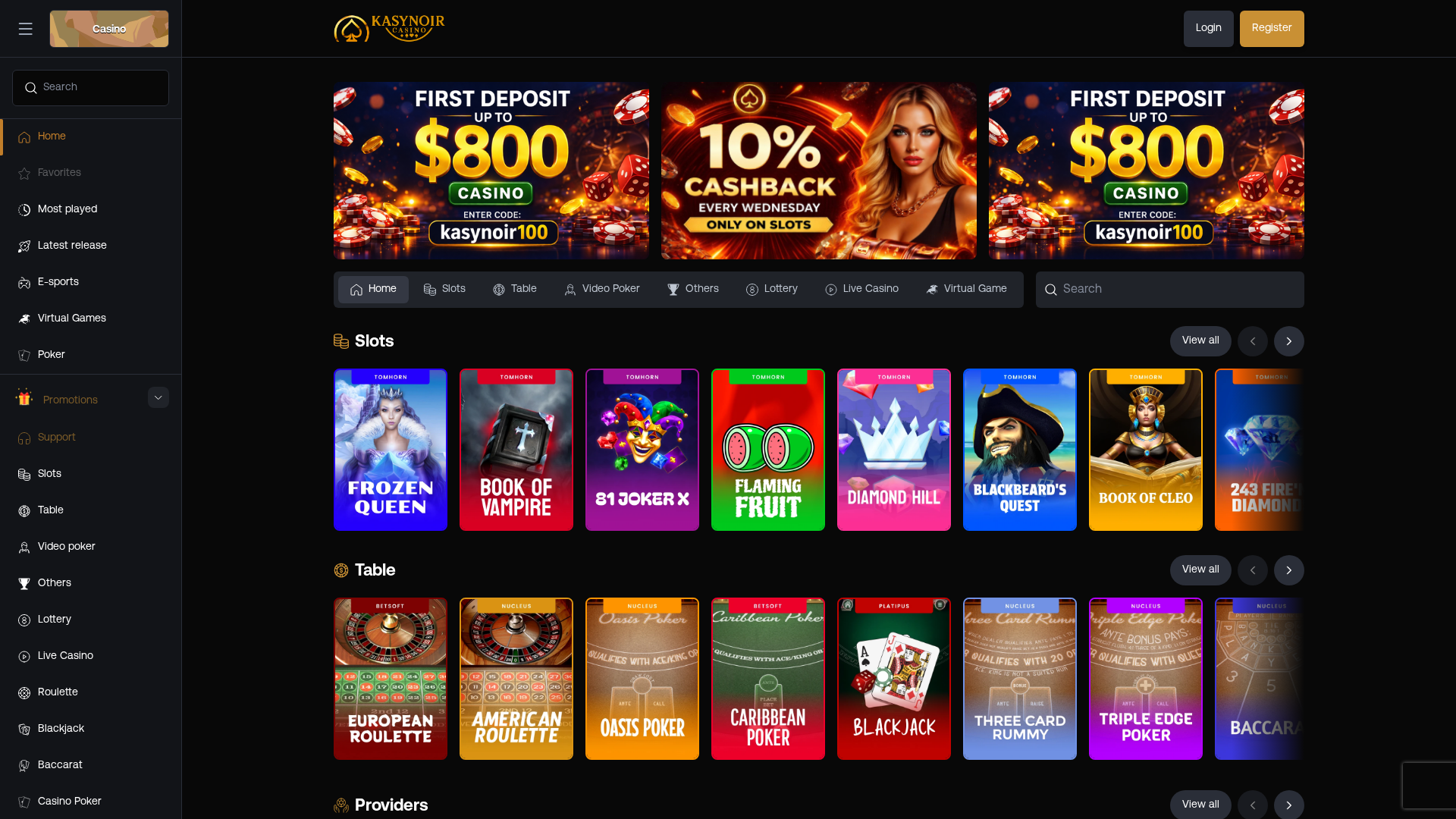
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17944C55B330C562DA83747C0EA123666519BF3DBC241D1DCB7FA8C31AA43CB9A516EE4 |
|
CONTENT
ssdeep
|
1536:g7oQov6/TmNjiYSVZEr3Kg/QbFSNdpgFMH2v/BwZErK8ReWZg/QbxBHoApSHb9Ze:koQ66/TdYSwbfN/gFx3Bi8Rx6IF9n |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
97696cb1616c6897 |
|
VISUAL
aHash
|
003e0c203e023e36 |
|
VISUAL
dHash
|
4a6a584858766464 |
|
VISUAL
wHash
|
803e3e2e3e0a3e3e |
|
VISUAL
colorHash
|
38200018000 |
|
VISUAL
cropResistant
|
85b62bcc3369ccca,3675f0dcc83032b6,f8f0f0f0f0c88c86,e8f0e8f0f0ccc4d0,f0dcf0a0d2caa252,4a6a584858766464 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
📡 API Calls Detected
- /api/footer
- /api/ranking/list-auth
- /api/reactions/unfavorites
- /api/promotions/cms/
- /api/promotions/cms/get-all
- /api/ranking/list
- https://signup.srp.tools/signup/customers/
- /api/favourites
- /api/providers
- /api/session-ping/gamesession
- https://signup.srp.tools/signup/customers/459/registration-flows/userSelfRegistration/password-rules
- /api/search
- /api/reactions/unlike
- /api/categories-live/
- /api/ranking/all
- POST
- /api/most-played-games
- /api/reactions/count
- /api/wallet
- /api/gameurl/
- /api/ranking/last-champion
- /api/reactions/favourite
- https://ip2c.org/s
- https://www.google.com/ccm/geo
- /api/get-provider-info
- /api/ranking/details
- /api/categories/
- /api/policy-page/
- /api/games
- /api/banners
- /api/reactions/like
- /api/verify-recaptcha
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 279 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 279 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)