Phishing Analysis
Detailed analysis of captured phishing page
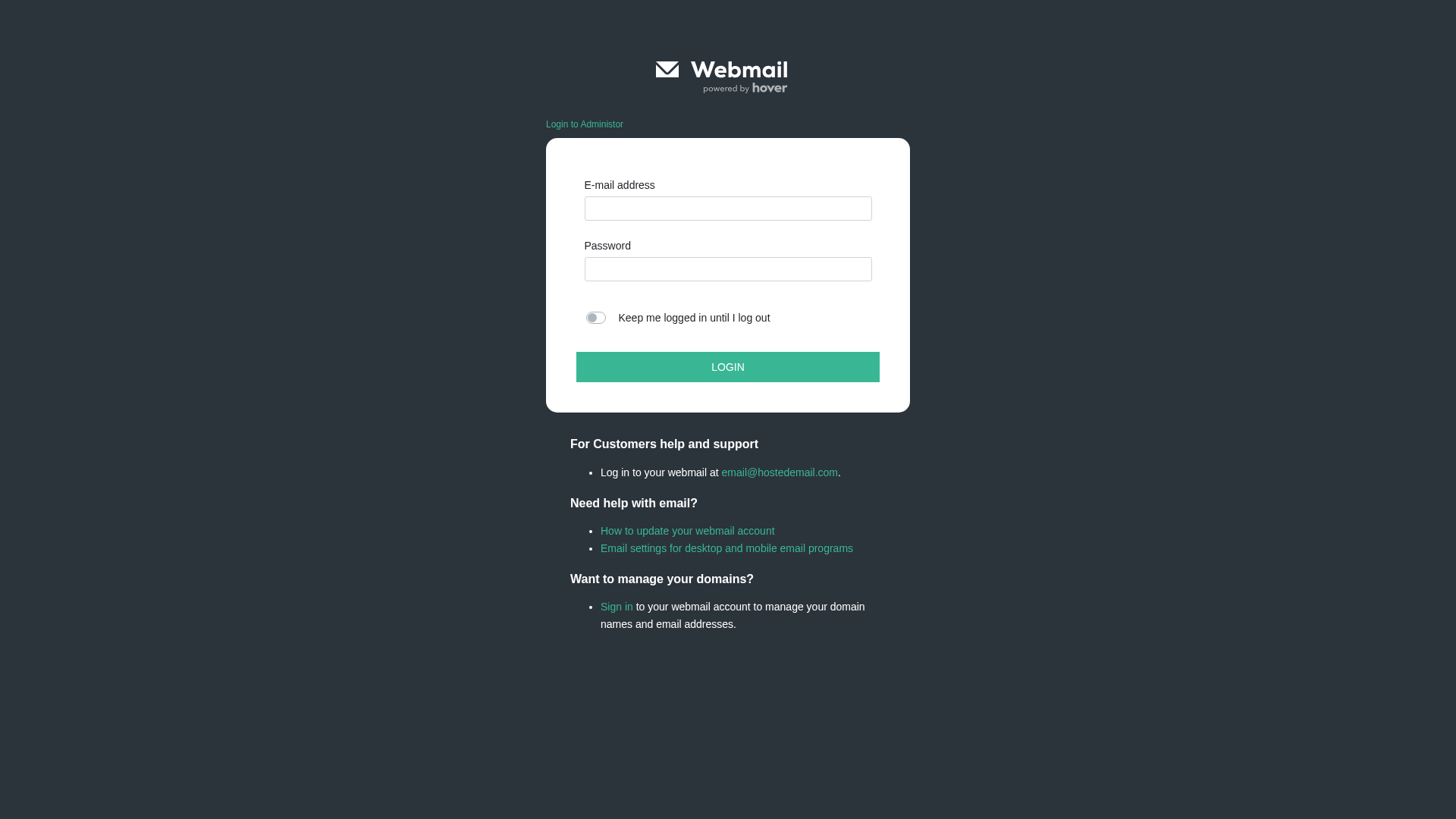
Visual Capture
Detection Info
https://ipfs.io/ipfs/bafkreidsosmqqhzprlnzylh6kl2a6gmgnmv4gyajxqgam45x5mn4lpjrta
Detected Brand
Unknown
Country
International
Confidence
100%
HTTP Status
200
Report ID
c6a6081a-75e…
Analyzed
2025-12-30 04:30
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12152B8E112246BAD84D795DEAF72D694638F80B6FAA2C5C45AFECB5858C3C80F717810 |
|
CONTENT
ssdeep
|
384:yw/O+rMimrrRMAciBMABrczvtVqpM6KK3:fkrriPdI+vtV0X3 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc9933666699cc36 |
|
VISUAL
aHash
|
0018181818000000 |
|
VISUAL
dHash
|
14b2b2b232343008 |
|
VISUAL
wHash
|
383c3c3c18181800 |
|
VISUAL
colorHash
|
07008000c00 |
|
VISUAL
cropResistant
|
e060e8608c9c3111,14b2b2b232343008 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
Telegram Exfiltration
🔬 Threat Analysis Report
• Threat: Webmail credential phishing
• Target: Hover customers
• Method: Fake webmail login page to steal email and password
• Exfil: Unknown data exfiltration point
• Indicators: Domain mismatch, login form, Hover brand impersonation
• Risk: HIGH - Potential credential theft
🔑 Telegram Bot Tokens (1)
- 8159384639:AAFn...NMHM_LSQ
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for ipfs.io
Found 10 other scans for this domain
-
https://bafybeifucnntp2tzvo2smmgd2nrz2anlih4bapzou...
https://bafybeidainj73npe2kepzldqmuwzes5stwbgtu2pb...
https://bafybeidzv5orafwm4qq7m5wdptagbyyaksssolxhe...
https://bafybeiby3jwvxj44lno5pu2qjn5ezh5mlm4fkoy4q...
https://bafybeiaz6xbudbilnb4a52kkl2ffapf7oim253s7i...
https://bafybeieqilhn5yjrdt2cs46bglcamzimrcgbfuvq3...
https://bafkreidpy5pr2m6yvnk6v7ry7tu5lydi2rkd5reft...
https://bafybeih4lunv4ykv3qnx3n4c2c3d3gl5vlonz34ui...
http://ipfs.io/ipfs/bafybeibo7ht7ythkoucqnhcd4lzr5...
https://bafybeicfvmv4fni2inofzgesr4hc754scsn2zsohf...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.