
Phishing Analysis
Detailed analysis of captured phishing page
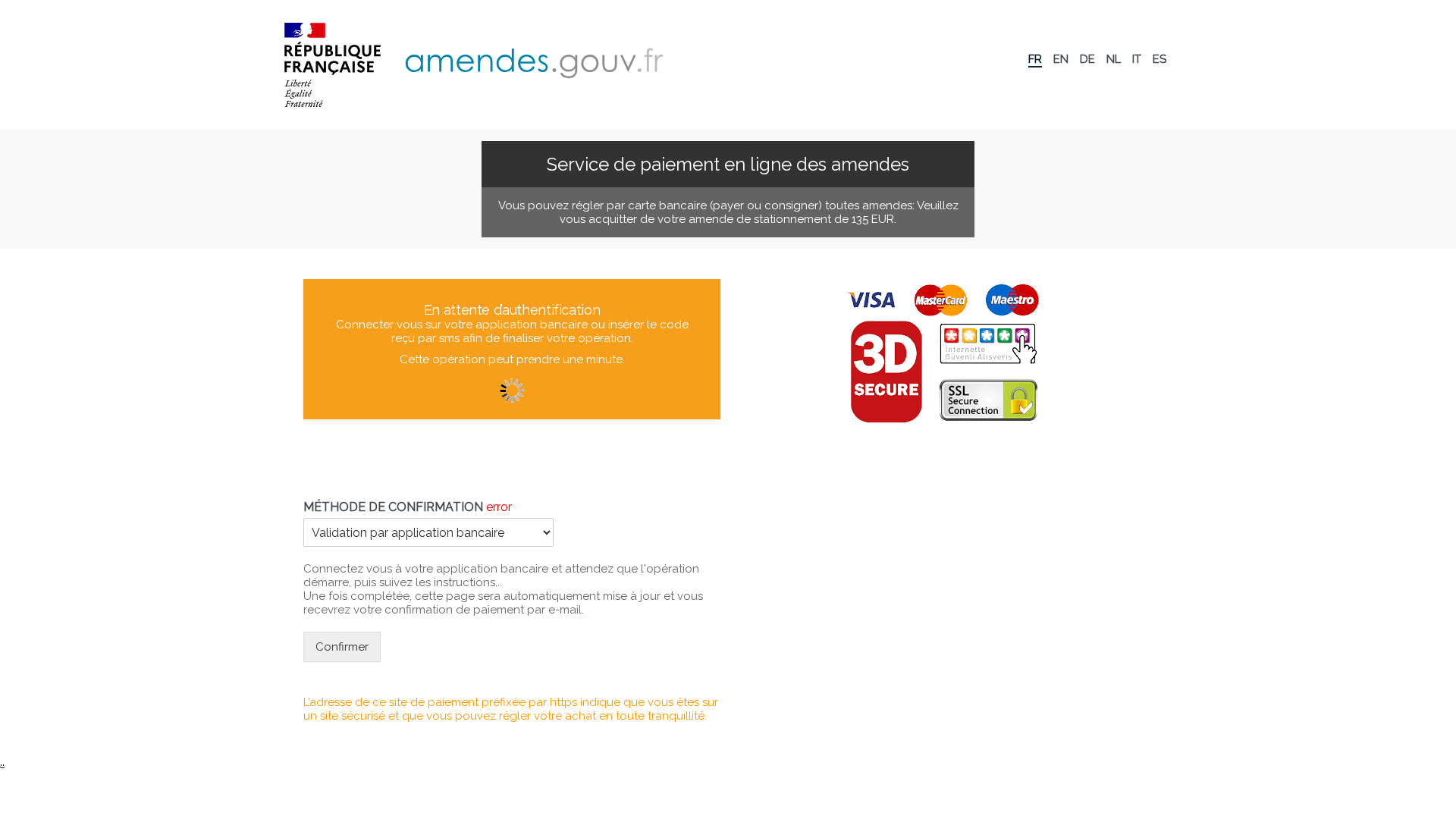
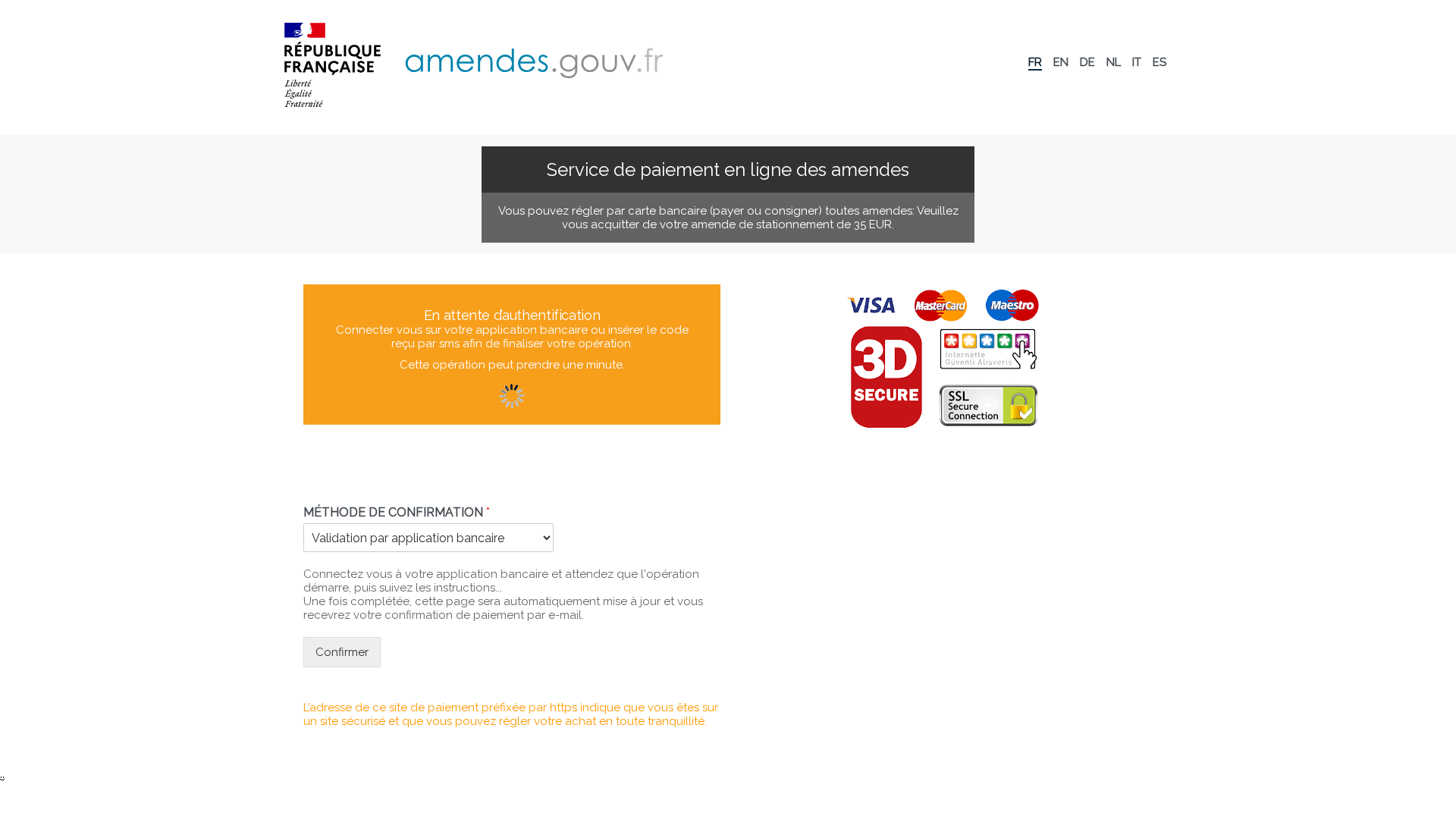
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A73285B238515D22606F51DE998F974F9282E396CF424FD1D2F4822A5FF1C90FE472A8 |
|
CONTENT
ssdeep
|
96:ngJWtJ5p5W4QkQC7JXntEGvEhl8jA2Fpqw+etOmqeMHSIIfII1IIoIIOI67DmBSj:gYJjbZS8pl6elvAY7Gpx2gtpV1A0iIu |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b435c3ce9c988bc3 |
|
VISUAL
aHash
|
bfc3c383dfffffff |
|
VISUAL
dHash
|
238e1e3636303c08 |
|
VISUAL
wHash
|
8f008083838f9fff |
|
VISUAL
colorHash
|
07000030000 |
|
VISUAL
cropResistant
|
238e1e3636303c08,13e4e81340a6d8d4 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAMAAABlApw1AAACylBMVEUAAADmAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH7mAH4QEgezAAAA7XRSTlMAAQIDBAUGBwgJCgsMDQ4PEBESExQVFhcYGRobHB0eHyAhIiMkJSYnKCkqKywtLi8wMTIzNTY4OTo7PD0+P0BBQkRFRkdISUpMTU5PUFFUVVZXWFlaXV5fYGFiY2RlZmdoaWprbG1ub3FydHV2d3h5ent8fX6AgYKDhYaHiImKjI2Oj5CRkpOVlpeYmZqbnJ2en6ChoqOkpqeqq6ytrq+wsbKztLW2t7i5uru8vb6/wMHCw8TFxsfJysvMzc7P0NHS09TV1tfY2drb3N3e3+Dh4uPk5ebn6Onq6+zt7u/w8fLz9PX29/j5+vv8/f5chY8ZAAAHJ0lEQVR42u2Y+VsUZRzAZ3ZnD1hBF7lBPDACFQGvzKNCUzPUvDY07yQSDMwkTUsgtTQtNdpqs0hT80jLPBIvRMxSEbkEPFA8EHaX3fkfmvm+szszyz7smvj4+Dzfzy/7vu+83/d9PzPzHrMUhSAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgiAIgjwLKEKiOMJ9HPkuUUCXJ9KZMrTjG+9cWMlxsXC0inSxtBJYqnwSAoH7Or5x/TEWqJqkAIE8ks17IgLBJR3fuEOALY17xgVa81SPIaAa+irH6KinKMBWDXwMAf0JM0fTgqcpYP9M+/8FAs7wUda0pynA1g5/xgXsxk7eCyi0XcM6q2jnAlkMAulKpVIhqUUrRGhRgNFHRIQHaN304RLwaALszeS2AurosYZUgWHOsfm8uHxXUfFh48wepKjT0ut8lO1AXl5eRidBMXT4mxmLRcaJAppVpaUlx3evGhUgHSQdNGT6IknAJGEMtH7wZL77EUpPAvZCPxcBZvDmK012x3WjShhaUsENUmgpTddL3g2gJBjW474rzzTaWAkFooDWSIruHnzDeQRQ9MouamiVBuxVw4WguYdvWvm8yceTANv4OiMT0C24YpdcFgSY10rFkTVt7uZOwCf1gmww7gVY9naOn7AOTzxpcQkAATpx+0Mh366AnXS3K1AqoM26I2uRCCjGXJUWWkwhbQV8shtY1hsB9l4ODEs1q65NAAgknXTerHYFzHubobnUfFFAYbjLuhHod1ZeasnVuAoo5jayXgqwt6dx84BOqWXdCoTvF1+BdgVa5h2C38NGUaD7acfcsNtFAc1G4ZZYLULixstU8BlSo9VisZwJpmL/cUS28thdBTTramrqHgpDOx5GUZHH3ARwAsrMFnEM37crMGHqPfitcQrQ80iwuWhD7hb+XbIu59+rAdegtPnXhdM+KYOe7F9rtVMrYPxGg8EwXqtYStSs5zZlZ2ZmLrvqKsBExscnTt5F2m+eQlOzSdJ2aev7XED2eYdAhHAP67bl5+ZOV7UnkNK5UPr4OAHfn8iV/FBal891YNsdxk+qRTA4c34At9IMIQMq6y3fyAKOkJGtJYus0EWB60YWuIFMvC0q7c/kZfw2Dq5otjsExjyA1NlXNJ72gZYUelSDXCD0HKSOhVHq9PvcfT6dALPNBKVFYbBCG5pg5oyVC8RVw4PZGSDroo0AFX2B9KAPExLdSLkosBgUH85QUJ4FKF+jXSYQVwmpfCWVUMb9VoyGVvxgrtjyyA7U8xI8jtlygeEwha3vUB4ElN9A9lxELJnCK5WuAqvhcZfHUN4IUEOqZQLxZDp8yO+z99gGg1JSvzVLOEGcFcYtE0iG6WRN9SRA5cMtK43oD/s4+57CVSAXKpyP9E5A82mrVCCmHFIbucVMt6QmR0vq+x6A12MTGUMfeEotqXKBobB9tObQHgS0ZJYVh8aQhWG9ylXgY3gCNf29E6D6XZQKBJ6C1KUB3Dh8Rjo+xJnNUHqxD2SyYPe885IgYM9l+OLYKqhz+rn2BZTjyI3frwshy87lwbSLQBqcIczZKu8EmCVWiYBmK1naTs0cGC8Qq6XoGVDHtjtRy3R5q54sEhGCAFs5f2D88yr9nyTy6Aw+MjLAVaAggW9s5IoKssJ/pNT+SFIlaYO4Cz19nQLDbkPq2vwwnY+P2qOAuHXBTZpC1jDWfL2GUG3i1pXe/5LRlRWs2Ut2attqhvI/6KxbFK78QNjizPVc1LogV4H70Fqj8MLWv0BRc4T9ynKDu2Dq6hQIPCScuIoLTaZ0tUcB+u1miUDQPpe9/dYE7hErl5ldii/Hcw8v37mEVUZRsRelB5A2AjJaN3CzK/IvSclvQU4Bxcz7rJdHiRTyyeQ4evAC9MgKWVe2z6GF0F9kp2S2cQ6/eLxULxFQzLrtrYDtj2j+zo2vcStA+X9pfSQBenSt5DSqnFYuPU3/HUtC+h2VGtxbroNPnFyLKED5Zlz3TsC6PxEmrspQZXcnQEX+YH4UAUqT9UCyUDDJv4vvS9N8YZmm++xocZZeyxAO9CGbH4gClGbiCYtnAVt1XpSw1jLJB5vdCVBhq2rt7Ql02dPAUztWyHd6t+QWl18hLNUhc3aW3YIaDSa9Myho4Yn7fKuWOtMI5wrnP30HVD0H2w4duWBPOUR+EUi6WM/FHWkQuXn54LIkteSD0rD9EgQUdv0OKmwjF9VD1p6s5fNfad3+3xqTxJPQ2VnQLZHLRzg+VmlddCLUSAyVftKHp+RsNK5JG6STftPqohO4in2FQdF+vSGyO0O64B4ME5skktDLX37EoXU9+fik3kwvqBDtGAMT0pfP91B06N+EtFrL4J/7CIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCIIgCNLB/Ad4GMDQOvb49wAAAABJRU5ErkJggg==
📤 Form Action Targets
- ./infoz/otpp.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Personal Info
- 2 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for antai-info-amende-non-payer.wasmer.app
Found 4 other scans for this domain
