
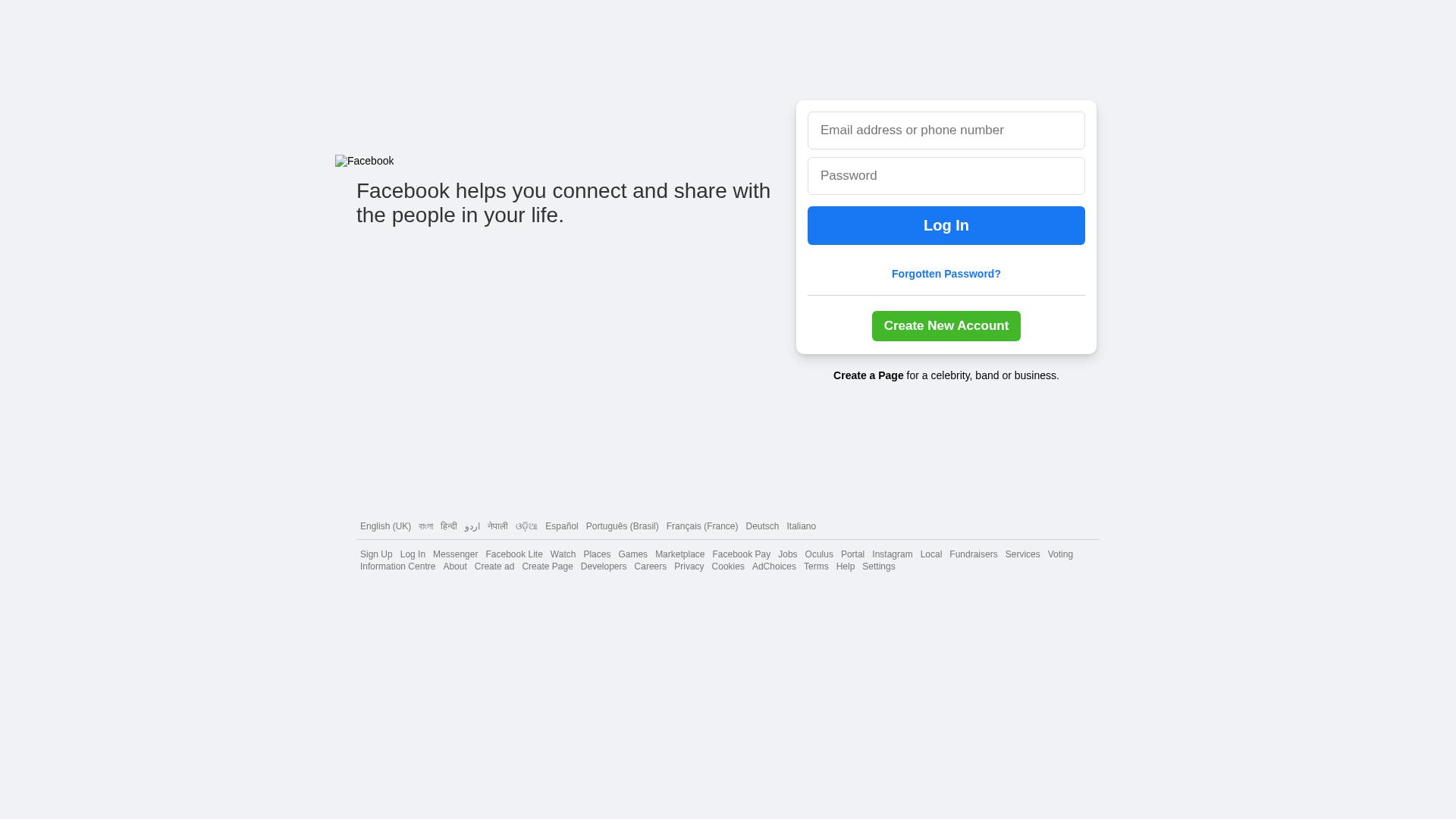
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
No screenshot available
Detection Info
http://dipeshjais.github.io/fb-page
Detected Brand
Facebook
Country
International
Confidence
99%
HTTP Status
200
Report ID
ca686cc0-47a…
Analyzed
2025-12-21 17:01
Final URL (after redirects)
https://dipeshjais.github.io/fb-page/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1308127227188641B0BA6735D6D21B37DE78345A78F6A1F4261A08E4FFDE2F52CC441AF |
|
CONTENT
ssdeep
|
48:npNmTNMQc6CDdAJsDu2C02we9m6NWxLatxvw+qh0dkH/rmnArRlrzK4Asau/QkVk:nI09Cc0iGBPp |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ec6c929293c56d6c |
|
VISUAL
aHash
|
0c00001000ffffff |
|
VISUAL
dHash
|
48161656090e0000 |
|
VISUAL
wHash
|
000c0000cfffffff |
|
VISUAL
colorHash
|
070000021c0 |
|
VISUAL
cropResistant
|
48161656090e0000 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing
• Target: Facebook users
• Method: Fake Facebook login page to steal credentials
• Exfil: Unknown
• Indicators: Free hosting on github.io, Facebook logo and login form, domain mismatch
• Risk: HIGH - Potential for immediate credential theft
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Facebook
https://facebook-login1.vercel.app/
Apr 01, 2026

facebook
http://itznick.github.io/facebook-login-page-clone
Mar 17, 2026
Facebook
http://www.facebook-login1.vercel.app/
Mar 11, 2026
Facebook
http://facebook-login1.vercel.app/
Feb 21, 2026
Facebook
https://www.facebook-login1.vercel.app/
Feb 07, 2026
Scan History for dipeshjais.github.io
Found 1 other scan for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.