Phishing Analysis
Detailed analysis of captured phishing page
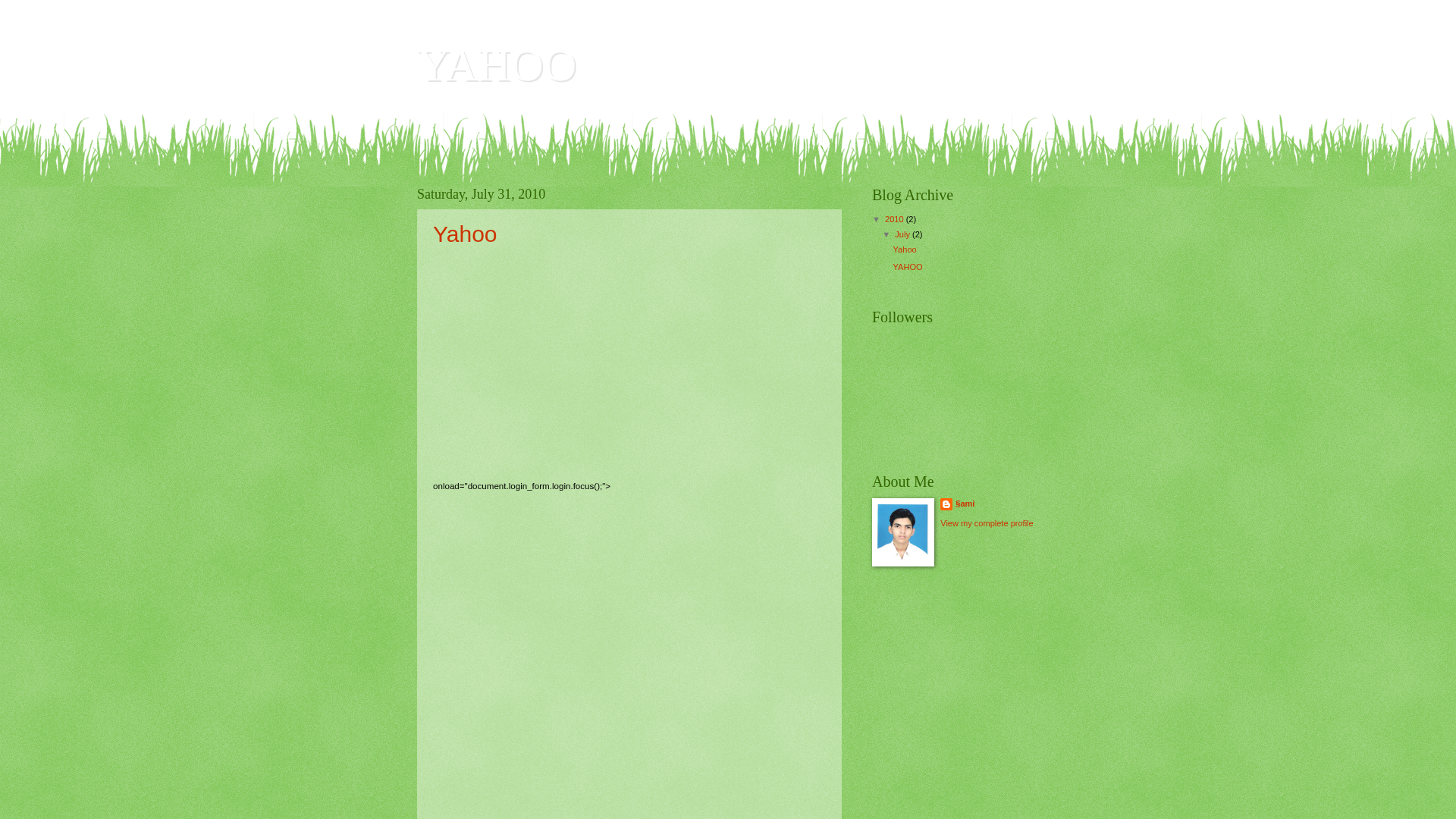
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D32371F19240A9AF8561D2CED3737FC8D7C2508AE7928C85E9A4971D09C9C93DD172BC |
|
CONTENT
ssdeep
|
768:z7HZ6DfXLnQVTwBa4AVYG1umlo8xa/CRz:zrZCfawRG1umloez |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cdb0b2b3c5ce4d0c |
|
VISUAL
aHash
|
ffff103010383030 |
|
VISUAL
dHash
|
0034726272626262 |
|
VISUAL
wHash
|
ffff303038383838 |
|
VISUAL
colorHash
|
031c0000000 |
|
VISUAL
cropResistant
|
0034726272626262 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
🎯 Kit Endpoints
- https://www.blogger.com/feeds/478254526604074400/posts/default
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=7270152012916715041&target=blog
- https://www.blogger.com
- https://www.blogger.com/post-edit.g?blogID=478254526604074400&postID=7270152012916715041&from=pencil
- http://us.rd.yahoo.com/reg/sihflib/*https://login.yahoo.com/config/login?.src=ph&.intl=us&.help=1&.v=0&.u=7flc8u916oq6u&.last=&.last=&promo=&.bypass=&.partner=&pkg=&stepid=&.done=http%3a//photos.yahoo.com/ph//my_photos
- http://www.blogger.com/java%20script:PBopenWindow%28%29
- http://yahoo302.blogspot.com/feeds/posts/default
- http://yahoo302.blogspot.com/2010/07/yahoo_31.html
- http://yahoo302.blogspot.com/
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=6897557750077868125&target=blog
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=7270152012916715041&target=facebook
- https://www.blogger.com/dyn-css/authorization.css?targetBlogID=478254526604074400&zx=bec942cc-9a17-4167-9d05-070fb5fccf8b
- http://yahoo302.blogspot.com/2010/07/yahoo_31.html#comment-form
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=6897557750077868125&target=twitter
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=7270152012916715041&target=pinterest
- https://www.blogger.com/followers/frame/478254526604074400?colors=Cgt0cmFuc3BhcmVudBILdHJhbnNwYXJlbnQaByMzMzMzMzMiByNjYzMzMDAqByM2NmJiMzMyByMzMzY2MDA6ByMzMzMzMzNCByNjYzMzMDBKByM3Nzc3NzdSByNjYzMzMDBaC3RyYW5zcGFyZW50&pageSize=21&hl=en&origin=http://yahoo302.blogspot.com&usegapi=1&jsh=m%3B%2F_%2Fscs%2Fabc-static%2F_%2Fjs%2Fk%3Dgapi.lb.en.PJsh2cctCQI.O%2Fd%3D1%2Frs%3DAHpOoo_QlMhY2cycn60Rs8eI1WInRwuahw%2Fm%3D__features__#id=I0_1775345382298&_gfid=I0_1775345382298&parent=http%3A%2F%2Fyahoo302.blogspot.com&pfname=&rpctoken=30145090
- http://yahoo302.blogspot.com/2010/07/
- http://us.rd.yahoo.com/reg/login0/signup_lhs/us/ph/*https://edit.yahoo.com/config/eval_register?.intl=us&new=1&.done=http%3a//photos.yahoo.com/ph//my_photos&.src=ph&.v=0&.u=7flc8u916oq6u&partner=&.p=&promo=&.last=
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=6897557750077868125&target=pinterest
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=6897557750077868125&target=email
- http://login.yahoo.com/config/login?.src=ph&.v=0&.u=7flc8u916oq6u&.last=&promo=&.intl=us&.bypass=&.partner=&pkg=&stepid=&.done=http%3a//photos.yahoo.com/ph//my_photos
- https://www.blogger.com/navbar/478254526604074400?origin=http://yahoo302.blogspot.com&usegapi=1&jsh=m%3B%2F_%2Fscs%2Fabc-static%2F_%2Fjs%2Fk%3Dgapi.lb.en.PJsh2cctCQI.O%2Fd%3D1%2Frs%3DAHpOoo_QlMhY2cycn60Rs8eI1WInRwuahw%2Fm%3D__features__#id=navbar-iframe&_gfid=navbar-iframe&parent=http%3A%2F%2Fyahoo302.blogspot.com&pfname=&rpctoken=42459664
- http://yahoo302.blogspot.com/2010/07/yahoo.html#comment-form
- http://yahoo302.blogspot.com/feeds/posts/default?alt=rss
- https://www.blogger.com/post-edit.g?blogID=478254526604074400&postID=6897557750077868125&from=pencil
- http://yahoo302.blogspot.com/2010/07/yahoo.html
- https://www.blogger.com/profile/10794590599370150709
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=6897557750077868125&target=facebook
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=7270152012916715041&target=email
- http://yahoo302.blogspot.com/2010/
- https://www.blogger.com/share-post.g?blogID=478254526604074400&postID=7270152012916715041&target=twitter
📡 API Calls Detected
- http://us.ard.yahoo.com/SIG=12fo28js7/M=294867.5495648.6574428.4664665/D=regst/S=150000869:PB/Y=YAHOO/EXP=1114408190/A=2167824/R=0/SIG=10tt88gbl/*http://poweredby.hpidea.com
- post
📤 Form Action Targets
- http://free.mailjol.net/allforms.php
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 28 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 28 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.yahoo302.blogspot.com
Found 1 other scan for this domain