Phishing Analysis
Detailed analysis of captured phishing page
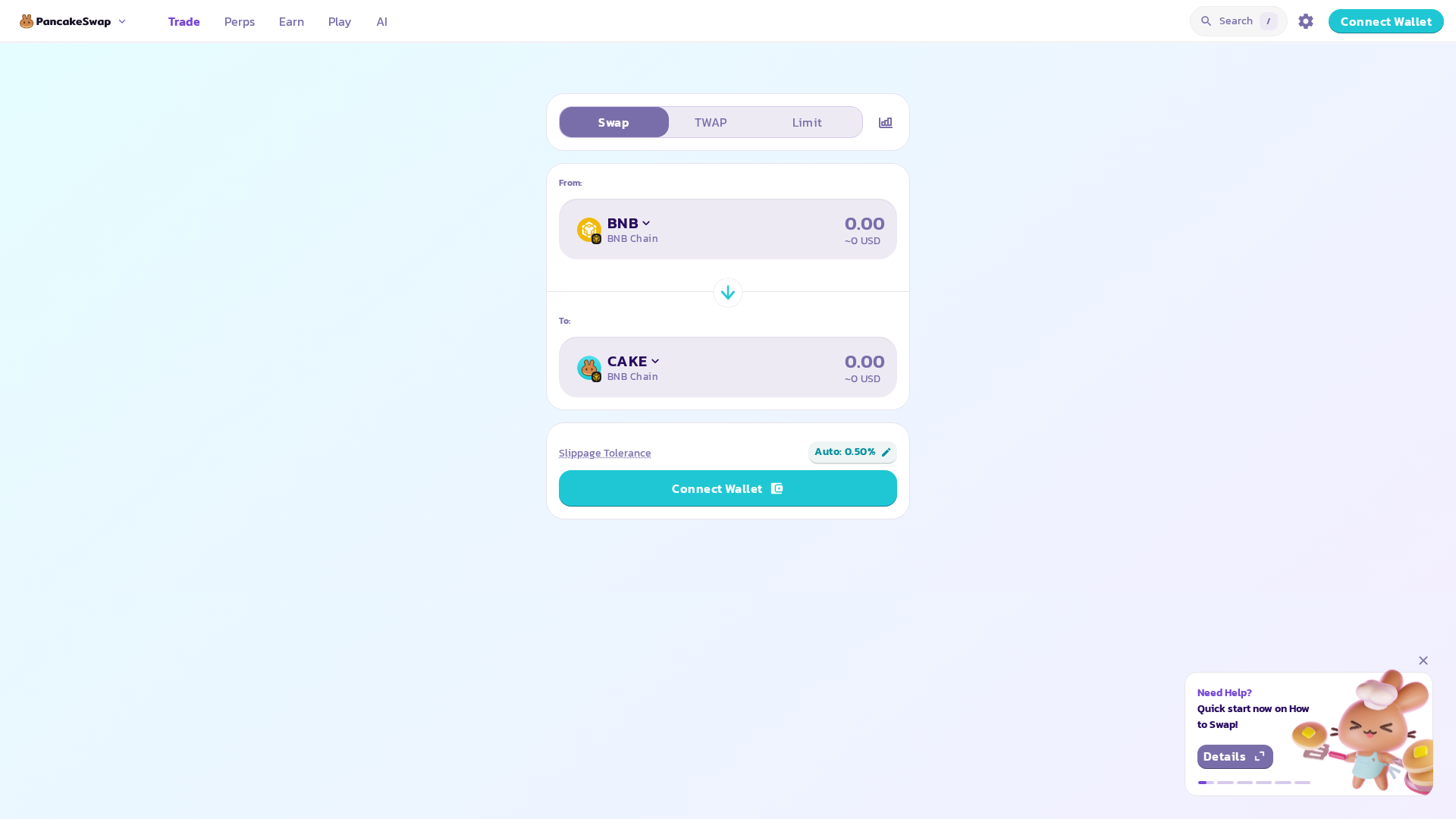
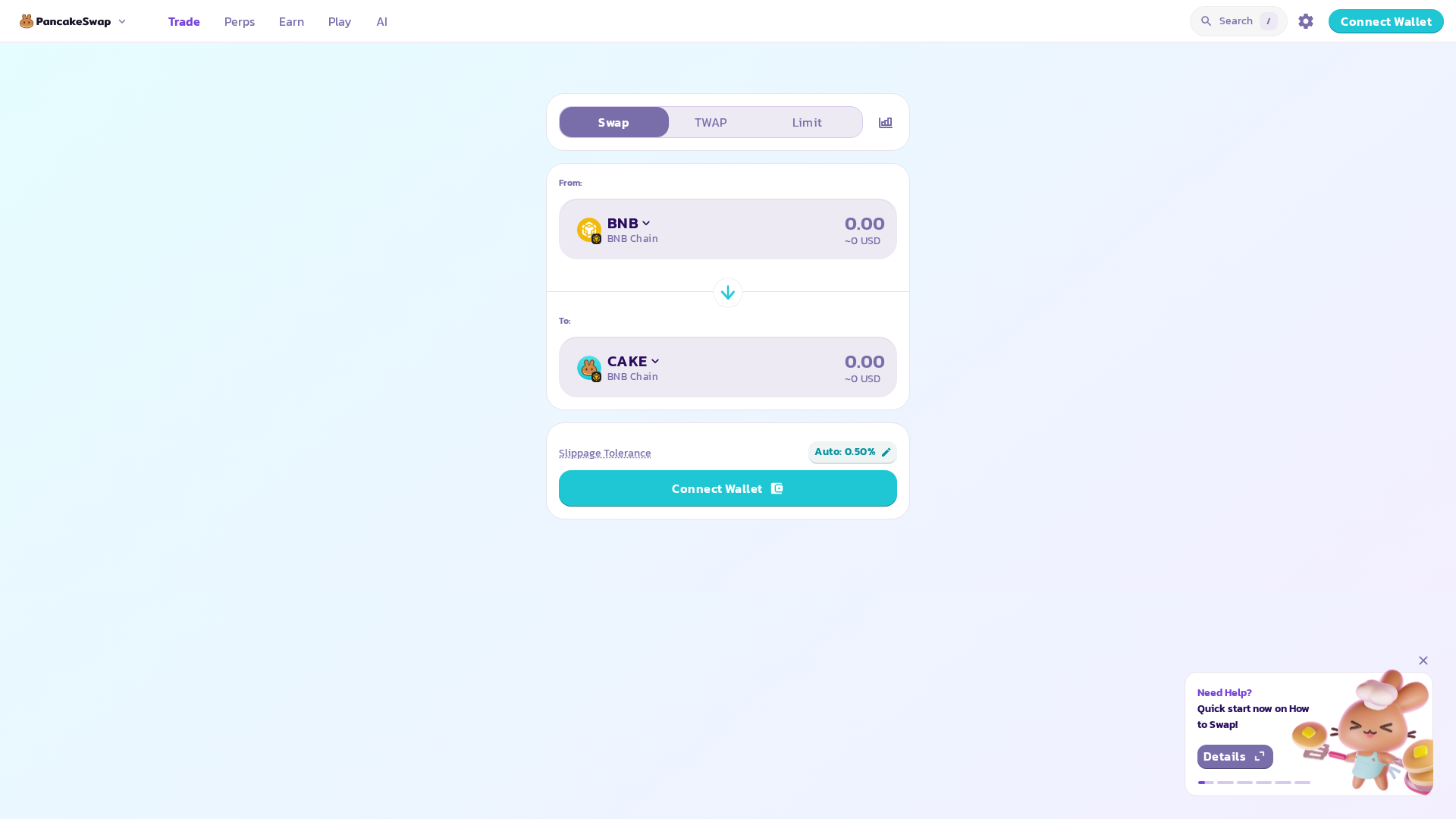
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T161D3E9E1829035EE4217AFC8DB326AAB741B307FFFA3CA8583B457A5A64BD54D844C44 |
|
CONTENT
ssdeep
|
1536:jXfbX0KQlQLfUUixZq/lQLfUUQlQLfUUzJ4CFf5l0RdyFm+9ftidZ5m9b:3QIj/IQIpF3i0 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f3a9d52654ccc456 |
|
VISUAL
aHash
|
eecfffffe2e7fcf4 |
|
VISUAL
dHash
|
d85900104c4d3004 |
|
VISUAL
wHash
|
feece0e0e0f8e0e0 |
|
VISUAL
colorHash
|
07200200180 |
|
VISUAL
cropResistant
|
d85900104c4d3004 |
Code Analysis
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAP8AAAD9BAMAAACB7rzyAAAAJHpUWHRDcmVhdG9yAAAImXNMyU9KVXBMK0ktUnBNS0tNLikGAEF6Bs5qehXFAAAACXBIWXMAAAABAAAAAQBPJcTWAAAAJ1BMVEVHcEzm4+okyNbn4+rg4urn4+ohyNX////m5Ot92eK14+ohyNRK0NubTAJrAAAABnRSTlMAgPk46bhEUCkdAAALNUlEQVR42u1dO2/cRhDW4SzApQw7wNUugthuZNgGVDoIAqhUkARQrYLWadgzNlLYkWSdBdenB1zrYbhKsZBM15Rk+EeF5PGxJPcxM7uUgiBbCD5Z0g7n8c2DuzNzc/8v9ho+eXwnW3fvPrmBze/8vjyR1s+/3L3W3X+bdNfWddEw+G6iW1t3F/vfXnr4jx8PDw4ODg8/ymzomfn3yp1OD75BHMf3799Pv8bh1cFJxYUe939cKN7ph2zzIIhFEASQfs0+hiUNPy72+/i7B0m2MWSbV0vkRFwd9smE2ePvfliDuLF3vSCG8LA3JjybMT/5PtCvlLBHV7kgtr1TkLN/d5pJ3rxikTNha8Gv+Ef544OAwLogPs+Z4FMRhqu59EEEmCUKJvzqef8kBo3cu+vRV58U5Pu/S3CPX2rCA48U5PsDaf90nXujYDRTPzPPFbqYqaIPW7iX79/+6xgp+KHgGYv/hTl6QKQBbn/Q8CD97TduBrBs2t8GSxCPUwp+clTA3STgr7UMDxzU4Gn661OBVnyVFPZTRVx0UYCjOHBZ8PcJXw0yBHwPep0Dg1eu1xc+HqUC2AUS+ChN4iFXCJkAEhE4L9hnCiEVwKfAw4IvqRqssARQIQDgwNeAiHQhDDMB4OHf+L9rl5PJJgOC/Agg+xKekOFoUFuACw6VVDwk6+HqDAKZPFdaAkkP51MNxISfWBlAqofbFAKW2xAAjkKIL0ksuJViMGcbYQCD1BQpDNjFYyDgJJHq4XMCA46EP/YXTukEz4KUAWvOiu/AgtQEjgL/aw3NgtXJLkXnBBYpHiINQc8AcDOJVAu2cV5AqQEe3MIPKI8wYGIAZqE8wlLLDTeZ6uaXUjhcRMQB7/nwLyyxESIuSEFo2gPzRekUt+w2+M6LA9ak7FZLHDRR2ItDlp3iiU0Nl7AgRGWNqMBo0ZINv/f4wN0VWrLleb0N+uFIGphsm1HwHVvPcUo6NqLh0OQHhRd7TH3iphEEEt+K30XDrV4kQIGCBZMEBFPnAMuw2CCDVAKAYLdwMon4TC+DUX+OuAkFCwwb8Lf0MpjvSEDHVCe/BOs6LCLYgEOxIK+jL2jSgSPRsw2WMniu8cSYfMydRrhU++QlPgoRdeJc7ZNXJ395iLowlK4p46IhPhh0Ds72VYaYGiEeS765cURpiAQVGO9ErxKXYsFYpQSrOBjM2H8cRdFLRzBccVCB9ShbR56VYB4fDu/kBLxyQYLPXSXAq8CMAR0WkIoFCiQYTd7izC7cKQh45QAScdcdoFXgMorULCAqweuOI0BCwE5FgIMWpC75TTsaQ6rARRT5YMG4HZctIaOxUNrfxgITJH1pa+EqMhaQGRBFb9luC1pQlMJQAghn02BAFP3hEhNsNnVwN6AzoM0CSqzyuamFSB0ct/ZXsABbLDhvaiFSB/faBETsRCJsauGocIVgfIYOA1IW2JJZ0DvEhUZAPGUxQMcCe7EA9uXQeIjCQQUDECzQEXAmmwHOCC5UBLDhcEM2A5wRHCsJ+JNdJ9iSjeAtwoaV+7diM3yxQMhmMMLEg6GaAIpPlAkD2QxQRuCBAK0ZNDyBTQQvi4hgRyUCQmR8WcckA+lFtV0Jp8XOXwslZOZJIHmDAc4T7BVPXBCQHBdmyCwWPKgJQLqijRkDSk4ks8/s0q4UFC3JEbHQe9ciIyoJyP/BL2tJdriELE6Fx3lOWIog+3zqkDufVASM0FlZIilj4lgsWNuvgGCZ9pqoSQC/WFADQadELYzPgOEAgiNQAcEQVx9sJacIAszFgtohz5yxYIjArVZTIdGAWB7rigCYQPCmLA3QCNiJ3BCojgi2SyB878gBjc5ZigVfSii8PaGkWKAigHeyYDJRILEfDuBWicVyPCSukYAqJhoR35crCBCsInaJxavuBNiZJ5RB2YpPAjgcWCl8UWLwqWAngAmIaVT4XO2LvHAAoROlNyKUyYkiAFup7DU+M7URwDCCYH3mDoe6zFRXLFAScPXxlMyRzxYCKBwYG+JTbbFgQ0EAcAgQxfemRCQsODBgcmDaqV1QM/UiIvFBwAtOngoVAe+cdaCoHil1Tl8sOG8TINgc4KAzlNkhlwNT87fwQaGCAKCKgEeAfw4kNL807kMElGLBA39W4EEHhMWnCu9WIHGACER7BCsARLG0fzMUZg4Uzkj4sAJacLaBc8edYoEzEAk/8cDUrBaIYoGBA+JaoPisJGAifFoBXg+KmJAcFe/5AqKzKiynAchF1/kbdUBbLCjzgmXKpbKgLNm+lH+2wQGsDKDMjKi5YdB9V8QTgTU51enmeif+YxEQlwSMyOfpD6NXU71hoIsF+1WB4sg10e5wAFMsqCok1BoRDpsINSKpSgaWOAbs2AQUAnh1Qhw42tU5LOuE8+7nqRHOqMuaqlIqRyTgRQdwRnBeF6sR/th8smCPoYRQvb4mu0MXAqRiwXr1Al/njYBDAPpZ6jcmdGeAwQGBAMIV8lszrzpQvzVzx2JUTNiWav3+PsNiYBQa659VEWD7A2v1m9MMCsW1i0B6d2yGQuiJgPP6XCm5VoohwHoNYV06x+N8v0rDAcDBAPnlsR8RyGdI2nZIKBYE35ImAVcfcEbUOEzmEBOlW3+SCAiP888YdZbPEd1iRwSXs30rAi6skhCVEWwZzpKhUWFnlqMUBBw1asYQIMojVDtsFQuKA3ZHJQf28EdN1xuHSrlm8KI4TVUQcBAhi1UQiMZ5QrM7EtY8tVzlqeupHT5bJyq5ZqA+YijljWBNCtzMQEMAQp6tU7UDxm1fSQfaK7HJUzSNYHayWilvwJQKOgvxB1onq8srLtS0IEQcslSv9jUX+8lmYfJCZBXonK7namFoY4CmWNC5XzDgxiQXCAYIFQ6+4d4xUXoD8jnfzh0T1S0bXLFgw2SDOqWG7i0b/m3DY+p5e6G8bDbPhKL2kXPcpQvFTSvVXTMkKuyZj5oLpQpscm/bKYoFIfmYMyhu27lcOb2knrVX3je03bgEjB6+xIUSZ6obl0OHBiQbNhAWdhXIlIBfr9yj3TVQdyO57VCtG5NeXG6UFcruzWudvK1h+kWNQcImA93N6+zuOaM4UZjiMeEEh+buOer2vdYWwsNTbIatvX0/71wmMNEt1we3b6QDA9QwuPkv7UGRdeFAB4OCksiKZjC0xeoE422ZesHcdCcWkgyYKmjuRUOUgWBQB8ZuPNcgA3M/IkRHJuHC/lwC2y49qZz1wNaTitWVi7JsXbnyvmT9goCtPZ7cmY1YLLD/LIztPRKl3nTgnwGI3nRDVHtCJjaFmCbiSz56o2nrMvb+hJkafuqLAFzP3lFvlriO61qs7tLJPVkg14WQXTrxfUqp+RO2YW9/nVqxLYuXVSwADwzAtuu9RWIBoDUA37B4uQcs+EroV2zv2EyXB61jc9a0O/EOgpS23ciu3fhF7dqd9y336waJ/fOzzu3sYkH3Zz/TJwjUves9pAWM3vXd7v0utsDp3p/PL/CXC3CGSPia4BAwJzjMZlh4sgDeIJGnk65TYhQLNtijVPI5Jj4KIuy5SvkkF/cowGGgTz7Lxi0gd5plQ5rmoywWgOM0n9k8I7coyG2e0WyiEztBGjtPdCpmWvER0MOUvXyqFy8G8DRXbMSkYHziqICyU0gpoBYLxv4m/BWz7WjPf+V9up4eD4Q6CPc/X/ADHv89zzesJjxS1G/iedRnMeMSs38fMy7n6imflmIB9DXls55zipB+T8Ne60mvuii530mvc/KsW9XD9z7rdq417Vfe/Jqm/c615x2fzuYdn1zbvOOchJud+JwL4mZnXhc03OTU75KIm5x7/h9a/wAp+oEsluND5QAAAABJRU5ErkJggg==
- https://blog.pancakeswap.finance/
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAP8AAAD9BAMAAACB7rzyAAAAJHpUWHRDcmVhdG9yAAAImXNMyU9KVXBMK0ktUnBNS0tNLikGAEF6Bs5qehXFAAAACXBIWXMAAAABAAAAAQBPJcTWAAAAIVBMVEVHcEza4+rm4+rm4+uT4+rm4+qQ5OqQ4+r////m5Ou15+3yR3cwAAAABnRSTlMA94lC+sLsxIFoAAAT0klEQVR42uxbPXMbyRE9kaVA2cku6wqKZF1dwEx3Kgf8A76yI9lXDhiyStUjMlMyU8IP4IGMjvZJ5DJTApD8lZ5+r3d3ZrHY3QEhOTFEgQWAwPT0x+vXbwfffPP/29a3/devX+rt+9ev/geL//TDP6qqurT/1b9evv6aq7/Uxbu3y39+/3WWf/1Dten28SuYsP/ndr2nTz/f399//vw0ccMXNmG/2f3z+5WT4FzwQSSE+/vZ1/DCT7bK85UPIYgXF+/iT7Qj+Le1DX949WW9f3kfF/fBxaW9j14IEnz0RXzK//3zl4zD3syW997rqkFc6oJoknf+9I5O+ALr/4XOd079HTT+MQRwQfzx+mw0KL4yh50fdx4GuP9yGb2t67h47xAF3Xb0CBwS7dJgIA6XL3Yb/gNsPy6ve/Xq7+h0XT7eeSyLsKgNwdMJu0yE/SNsX3PdYav6T1MR1qhRgpwULUx1DZzwy47XX8Xt6wqeqae/FAE8jUFOqCGsD7Vg9ssu17/xukWtP3gfDzTqXjNRsHVEIJoFf8x35wPE/7nHSsj1uEvPPAACaTJ4btx5mCD6Wy24fLOr/H+Ohbi0hlv4AIsh+aNhAS8IklNjglTcQS38yP2rX6Obox8U8jQQCgP6WOB1z3SkCQG+UAsuX+0Cf24C6s0j9kg6ZEBg7gfNAAQCVarJgPp0br4DRNrT9bEgthnvBD0AVYAt0//6HJ7UitBiUVz0asG/H5aAM11fyx3xtYTX/aEetA/pSpp/xCJNzWBYHe9OowV/fIgBsQAu9YOQVbp7IQADf7UFCN2t2SHqBOKiIEk0IMcPS0RNwJVuGy5gtoGFCAzSH8KRpiDywWkxqDGKj5opdw9JRE2AZ95KTbfriHnqdwYBuQYEUEQUsYbgnHXraMnsAWlwpAAIsIMLfO0ChllBH4URMhdoUmiiCNqmBE2DN1sH4BJxFZe7wDPaahqRCSCIYvBkR46dEaVwvG0QNAArx4TSUNMOshDUPlFIrcBWgUa6PruEvSO+eLdlEGIAnoV6fxoHZDtQUAEI9YZs1z7giMX4A2c1qg5Ra/1sqyD8qAjYJDbKH9DDCtAHwENbKCAFwFeCBh8FSad4f7pNEBSCVkQTABA+zdxbszIQElQnIQk9gIawPggH3t9tAUcHGgBmMirbo7YFeWg9GC+ABqqVhCl2Zv1LQLOmgYZlVgxHe1oBwm2SezjGgzkRUOKgIGiCRlS4cYuSlqJlpntfnIcxA5cSbAIBqjDV0YuNktM6NUKENgiA2DNjrHQ1j73cFebhY/RAwd4EFKteF5AfHImpCyQooOkoWBJ1S1pmLHhj7IsfCx3wM6wnvKHEXAh1JqpNcDrHAk5GIEPYOO0FPHCAiy+VuSA64Erjqf1GEAU+ANx73HEwAQHFlul/xyRB9QRYxAk6vqnIBTNtwsh67EGs8YMVaa6zL2M6CRwWtBYEvMCTDhAjQFBgsnwocEF0wHfNsAdno/SAOjULJ0PGhjGnAw49QNgZLgK6gRsAkLirEgd4G/ZcDXeAHBtHUO0+kIQHIkQ2KaMY0BGsVAVN6c10B2BFpcKW7vC6AbwQ88DGSco7YoFjQzAay0kivjKbmgVH1SWwF4uE1gUGybUL2Ao2iwVg6ByafJEL1AE+1C5wiQt87gKL9maxwLMzkrNEUya64KC6JPdGdrGYak4CpoPoEwpGxQJ7BxAtHE/qCLELfLJ+y5w2SxhihzG0mVDHxQK4itZ6mdQRDqvqr86gHFult5nYmLsAPX66WECn6LMnVfVqAg+44fgDUEc/IJoYM+X040rEAmZl/IP5BF7wSNsghlCETtB4BTIcPgrwKoViQRCGJXaEj+M1eIOBh+MPspnbJPfwFo8ysYBBiBbMRysxpuAzbMVxImU+B/O1N/ZXLhZgUoq7mo2l4WGsQbZebA4Tn2O39Ry+sW65WICEFTkeS8NYg5xEAAEINIqPcrAjBm0lFgBJxVXVtyMouERT5U4F7RWZiHKyB9uJBRjm/EgaHlQ3rDp8GoEFyyHcbPxbiwXaGFQxGEDDfSUCJOHMIl8Pe3A229LWYoGgLGbVfwZBAPAF7ol5y4Y938Ddg8QCNftkKAYagZrOCbkVmK5n5MFHHiQWOEDBi4EIPMO65gJhu5Ukmg8UC9QFAzGIEbDwrbnAty54iFig5pxs5oYHUOSItIg8BjKshSd2IRYMxUBrwDvOk/Sst+YrBKRdiAVhIAYRhZyVEbbBpWALKmg3YoH4jXVwqIoEBzxhlxcSew8CsiuxQFnBqw3jwDMOckYjMRYJQuC4792IBRGLvt3QiZ1RCU50wqIXXhjcnVgQY9Dbk58oF2NxiSe+sZiZxn1iwfxOVYRiseC0vxCPqivj9eBzyDJuToC062LB/HqxWHwqFgvkbS8vikW45AjojNEKqDiK1/WKBbcLvS2LxQK56yvEWISkruLZfX2zU3G9YsEp1l9clIsFH6o/9RehsykYs44Y4BqwrIsF72jAolwsOO0rxKNIBTxaQE0AA3uOY09aEwvk1gxYFosFsRDf9KTASkx+ImwY9ySM9YkFtv7irFws6EmCx9AF8WZHDg46h+TpFwsaAy7KxYL360lwqJcGCCh8GzubDQN9YsFpbcDiU7FY0IPGB9UVc5fEjuHruiATC+aNAYtVsViw3pIjCjDwyF9OA/B52CQWJAacFYsFd9Vva42API6mcy7lgL5JLGhDsDgvFgs+dNvBI708Lt6YW2AZ4XNkk1iQeGBRLBastYNDTQEbRMUmH2C43ygWJB5YLIvFgm4WHkU+TIQj7DjTQtCR+8WC1AO/FosFXSiKMATOS+5iVEIIMBvEgtQDZ8ViQScL93Qqt6meV+pQ+UJ86xcLMg8UiwXHeRY+UjrIqRD/QbYdOfcmsSD1wK/FYsE8z8LD6nd0H7EhomF9A2JBZkC5WJBn4UHko3ZFwIZdTkYyIBZkBhSLBTELX2SEeMnnSffoAsFovVEsyHOgWCy4S6lx7MUsFIMiMTh2Q2JBbkDxyYIPaUeORdAgIEHMM9hDYkGOA8Viwfu0DB5BFxASLlYsU2BILEgNOCsXCzIwViBm3sBlzDm+bbNYMO8mYaFYkJaBFkHjAuYuid2QWNABolKxQNIyOKpW9eBjgWf+DooFHSAqFgvukm6gZMBR+2Odm+mDYkGOA8ViQSyD35IqbAkUpoLAKwKDYkEHB4rFgvdtHe7pTAK8QqhtEHUjYkHmgS3Egnlbh6BDViHCnVOGGBQLcgPKxYKkDp9gLraTyo6QIsyeAbEgb0ZbiAVV1cLAd66pFJvqYcmgWLAegsKTBbMGCA4iJbcO4CwRhFPwkFiQJeE2JwvuGiA4igaQ9ZsEJDZEDIoF3TIsPlnQAkHshfQT9ixi/XRELMiBaIuTBX+rgUCbsbcKYcrx2tCIWJD3gi1OFjQNeT82Y44vYoVCKBoRCzpVUH6yoEGiPZXH7KJUjYAGYkNiwWnHA8UnC05rJHqsbADtAjiEbYauWOClKxZkc8E2JwvmtWT7qPodn4km4hhp3xEL4mrnq1wsOO1wwuZkwf29TBIL3tZQ+KT65OgCgrm0uVuLBVjsPHdBPhk1LpBrnZYniQU1FEY+BHz3RLhg9ZuKBbe1oxOxIKuC9mTBLaW7KWJBzYkiEiNaxvh46iYTC+q1XCoWdHsBTxbYny4niAW+xuID1cd4UbAlUJlYUCuCZ6lY0BlM7GTBbS1cTRALaiyOrcDbCMQL9KjdRCxoFMFFKhZ0KBlrtYnLBLHA1QbEViDs545tGzamYsF1Qr8bsSDPAWsbrakTxIK6GSglBfci2bJmmooFiR7WigWdEOBkQWvUclwsaAyoqp8JGhhjWSm5WJDWWyMWdOYC5FrjgMXVBLGgpqVVRcj2bQfoiAXJUqtGLMg9gKUSSz9NEAvMADZDqbuWs6MSqVhwnQ5htViQExLA8LtEtpogFlg71GYI1sj0wCjQEQtuUxfUYkFeBeACqW42QSw4bgwI3rBfnKsv8qZiwbsUdWuxYN4NgT/JDBgXC963HgAhBNcxwMrFgnSzsRAI73kZqo+vUwMmiAWtB3jiMHDTTMJcLEg/+sLEgtyA+ObUARqqUbHAPMC5CF0A+INKyMUCyT57SW7VJSRZplA/HhELjJGoRigcG6nj8ncuFnRcoNnRpWTzRX5bjYoFjQE3duLQXGC/U7GgzwVdD9x2DLgYFQvmjQF24pAszrELdcSC/KMVVDoiVdcBi8WoWNAaUJ84BP0h4+uKBR3vdnuBk9s1A9yYWNAaUJ84NO7YJxZ0vOs6SBjWHRDNHBEL2hxoThwSKnrEAsk/W0/85Um47gD9o2GxIPFAfeKQNKxPLOgkWHc8l0WfB0bEgiQHmhOHdoVgXSxY313Git/1GLAcEwvmLQ40Jw49S3ddLOi4+CKfDc961l9QZh8QC9ocSE4cBuo8a2JBd4urrEGc96x/PioWnPIL0vvqgebEoXWtNbGgm+UXWQj6bhejYkHbjJITh5SSe8SCbpovxwxYjYoFCR9IThyCE/WIBSfdDY4YcD4uFjR8oEpPHPLCSI9YcN1Z4X7YgLNxscA8oEJtcuLQhX6xwK+5YNiACWJBy4qzE4euXywQWZTcLiaIBSdmwKzKThy6DWKBvCsxYDXhawgf7LLRkV6xSk4cbhQLCtY/n/I1hGQ0S08cuo1iwe10A66mfA2hNuBAZ8PkxOFGsWA+3YBJX0NIxvP8xOFGsWCyC84mfQ2hNuBQv1qbnjjcJBbI6eQUnPI1hEYhOayu8hOHm8QCcdcTa3Da1xBqjehJddU5cfjf7s4euW0YiMKyPDpDxqnSqkypo6h0I4rq3EgTHsAzdh9rmC4NbfmU0QLiH7hvsQtS1kx0AXFIEAAf3vseFAty3QW86WIItUp2Vx77jkNBLNDdAmUModYJFy7f33UcYrFgqxyCmhjCrlZK5xdDd+s4xGLBXjcEVTGE5tSKjq4DxyEWC7aaIaiLITQuDlqPw3giFAsUb+JRGUNoD/BpPQ7iiVgsiE5GL9oYQt4cnfrVqB9PhGJBdD5+1sYQ2jOj81w8iCdiseAj/g7qYgjtqdmK8n1BPBGLBUVsCGpjCO25IfkXBvFELBbIk1GljiG0DoY7kijCeCIWC/LIEFTGEDpWprlHnQTxRCwWiENQHUPonJ7fO09zGE/EYoE0GWXqGELHP0ATARNP1IoF/SGojiF0HBTu8HgYT8RiAX4TK30MoeshWZbfuHgiFAt2wgepOobQddGsyjcungjFggzdgjcDs6DrIyInFRdPRGIB3BwamAU9Q+GcstZMPBGJBQcwGT0bmAU9Lxm9h1w8EYoFYHNYGZgFec/f/lBWbDwRiQX8LXi1MAt6fkJ6Ddh4IhQL2C/Vo4VZ0HdUrihqysQTkVhw4Objl42FWdD3lJKrlo0nZtBZsOV2InpmQeCqdZZKLp6YQWfBjv0aUDMLngJ3e3n+QmbjidhZMDgfMDELQn//eTVg44lYLBhMRpWJWRB6y8+bIj6eiJ0F4RmRiVlwCN31bhSy8UTsLMjDnYiBWTDIF7iEBRtPxM6C/mRkYxYMEhbe38/FEwVnQd7fiViYBadB5HBJUxEbT8TOgk24E1EzCw7DlA3ljNh4ouQs2PbP6PTMAiZntCDNnI0nSs6CzhA0MQseh7lXFzdk44mSs6B5Ew82ZgEXOFx7XycTTxScBbuOrcHALODSdjQIEMtIcBZ81OdTJmYBG/xdXL5OGJZR1FnwamQW/OKiz/duPeJZRoKzgG7By7uRWcBmTmkmQCwjwVmw+Sz/VFZmAR9//0mn6DzLSHIWuJ+NWVC0lmZmOWBZRlgs8KYAG7PgBGgoDy79z7KMJGfB3swsANlzn74HLCPBWZBZmQUwfe9fRJ5lJDgLzMwCyB8gAgNkGUGxIBZDGIgFAolk6Z4BzzLCYoGVWSCwWC4cFJ5lBMUCK7NAoHA4CgZiGWGxwMYsEFkw/hkAlhEUC0zMgr1EYqFngFlGUCwwMQukJ+CfAWQZYbHAwCw4bEQaDz0DzDKCYoGBWSA/AU9kgiwjKBbomQW0DvyOoAmPkGUkiAVqZsE+wqQiMBxmGWXxGEKEWXCIUrnmNAwRyyiLxhBizIJNlEtGZDbMMorFEOLMgjgj8Y62hoBllMViCFFmwSkOynR0PsQyisQQosyCnYbau6LZcG8WC1TMAg2f0BEaIctIjCHEmQU6Zu+SnNaZWSxQMAtyHbV4QYTAvVksiDML1KDS9fkWZHaxIMosUKNaHag0QSyIMQvUpFaParWLBRFmgZ5V62G1drFAZhYYbgCtiWWWIBaIzAILr9gRmxPEApFZYINWr9PEAoFZYMR2O2q3WSwQmAU7I7Xbc8vtYgFkFli55Y7cniIWAGbBo71BgNj104kFCVUaRO+vphILUuj9rr9gIrGgSCuRWJNcMIlYkNbgUHdYjBcLUjssfIvHeLHgKb1KhXpMRosFRXqPiW9yGSsWjGlyqbtsxogFp3GlStTmM0osGNnm4/uMRogFxdg+I9/olCwWjG90qjut0sSCYpKWPdfqlSQWTNPq5Qbi+QrsYoH7/x/j///S7GYWC6hIKXkGCq5g7bvFTGJBMWW/n7+Cd4tYcKV+QbVYMPH/1wWf35ViwfQNj7Om41IjFlyj43LWtHxGxYJrtXzWPaflpygWXLHntNP0CsWC3d8rN+62XbecWHD1rttZv+236ogFX9X2O7t53zH9btz47O7CbTuv/TX41u/m97Wt3/VF3LL3/D/6/QPedr6MKcxRzgAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAP8AAAD9BAMAAACB7rzyAAAAJHpUWHRDcmVhdG9yAAAImXNMyU9KVXBMK0ktUnBNS0tNLikGAEF6Bs5qehXFAAAACXBIWXMAAAABAAAAAQBPJcTWAAAAJ1BMVEVHcEzm4+rm4+rm4+rn4+rm4+r///8hyNXn5Ovx8/aD4ei/8PNQ1N41QEQMAAAABnRSTlMAjC3hWr0VTO2ZAAAIRElEQVR42u1dzW4bNxCWZBvoUW4cQEc3TQEfkwAFfLRTF/DRdS9+AtYr+ZxFHB9qyzKkF5CloGcLSXq2gDxAhL5Vvf/cXVLkzJA7QFGeAsMxv5355uMuOZxptf4f6NF5eXS4vb29s3P0ovnJXxw+3x9L4+ftt00++uHv4/oY/tYQhpfPx7ox2tn1P/0zecbZfDKbzWQzeIbQyaefzOdCGvN5DuF7j/MfpsSbTEV9BBmG1weeH38udCOY+TTCD/uG6SUIrz0w4dfE+MI0giQenLshMf9UWIyYC8OuW/f37B5fNoJLInTOrB8/GTETTvnmT91w6nL+iYCNwB2C2P/Q+VMETniAmz9F4CAWfkHOnyAYkvXgJ/T8CYIRURPbhPkTBNc0Au5T5k8QvKEScEoAIM5pRPyROn+sicNdCgHuhCAjuCYo4IQ6f0yDU7wCCPo4x6pBm04AmhPOHBAgGU9PcoKKgImb+SMawCNh05UDUifcQgEcO3NA6oQDOAPdzR9FwjWYgVOHACIngHi45Y6BOQ9HEAD7jg0QOwFggg2nDMxDEfQWIFyPJxO8AjDgzjkAATCBDwNATODHAJEJRtYa4GN+60DwZQBrE/Q8GSA2QddqGfRkgMgEt1bLoK/5oxXBuCh2XK8CFTm8sVDhqfBogqE5Bv0ZIDbBifFF5M4jAGF8MfFJwTQSDwzroFcDRCZ4Y1DBqV8As/Vq2PNKwZSG3bUi4NkDkQ9u1oqA7/mfaDjk9MB6HzThgYiGN5weWOuDJjywzgcd7yJg8MFWIx6IfDDSrQOTRgAEuvUAsw4MPn/BaNErzUoM/lMfwzC8nMJ9oFyT9+AABmE0PiDW5F1lEII9sIwBhI9wH3SdBGGQzB++dxKIiCDspwAunQTiHjwI/0gBhIhA3FW8DmMpgCLBiQsdXmQAHhyQAKPDeAAKEiAoQACgIAFCBQgAFEqAWYoJAGbjP+kLAQVAbTnYwCzFBABB9b3sGPM6SgAgqu8EZ80DOKnIkGgWQEWK2o0DqLAQxUESgAoL91CfRBQAoqyFPQ4A3dIL8bRpADP51XgT90lCAnAu75q2GQAEchjggoAKYEgNAhqAUhj0eAB0iUFABCCFQQf5XU4DcF6sBptMAG6LKJwwAJDicIMJwJAYhUQAUhwecwE4yGVgygFglgvBGReAk/yjRHAAOM8+TjpsAG5oOkQHcEvTISqAXIm22ACMMiG8YwEgMin8jg3AmKbEDgDs2ipx8PXLow8AB5ZKPFiF4dUjAEDw9bPF1l2mxUYAQTzTlT2A+D98sgZgXAoukmm+WQNY2m1fZouB8ZV0odkS1gFIdvHN2/jZa6lJiQPdg+oA3Kc/NlErW41MALJN8ZoJNACClWVwpACMi+FFqNmU1gDIf/+d3XJoBJDvyle9qgGw0Py6DsCmPYCKV9UABmFoeZCRrscQAO8tANzDAUxsORBeTY0AcgqaAQSWAPoFgLIYKQFIcD/YAWhb60D1oZQAFsUvvzMCuLZ7I5P+pnquBxUFzTpgDUCyasmsKgDLUBczBAASr0pipAAg/6pxLbAGIP5Sm0AB4ALgAQAAmYaSYRUAFqF1EEIAlDz7zxoAA13EUgHIf/hqDQAIBXMAVl9mC9Wj1QCAKGivhFU1vNQCAFHQfjHSitFC+wO7I32IBZRiVAUAoyDQAioxqgKAUTAHYLk/cV83QQVAEIIoaP9KphWjCoALtWCbt0gsN0jqYlQBAKSg/Wu5VozKAKAULADYbtbXxKgMAErB4svIdpuwJkYlAGAKFt+G1hulq4oYlQCAKQj4PNeJ0UKJxj6xKQNgvVddFSMZQB9MwWKHxH6PqCJGMoCl7uPBYo/IfpesIkYSAAQFCwCAA5OyGEkAEBQs9gkBO6VlMZIArOAULHZKIXvFJTEqAGAoWOwVQ3bLS2JUAMBQsNgtB50XyJGY//sThoLSySUEgMy2fPyNoWBxYgI6MyqJUc0UoPTO4swIdGp2H64d3yAAuphzw8Ha+a8Aj1KcG8L265frAECSnIuTU9jZ8VoT2FNQPjsGnlot9PNDMoyl03PguV3fCQXl/AHoyeXKBQXlDAro4fGFDgAoyVxOpeqBwkAtRuAMazmLBhaHWjGCJbnLeUTQHA5NJD6AzChnUoFzyZRidCUELgoR5+cDMgXL2XTwVKoFlYLlfEJ4MlmfSsFKRiU0DFRi9CDQQYBJZbqgUbCaVQtPqayJEfCqTSWvGHHB455EwdolD3gq0YBEQemFEJ3NtaRQsJZdj0ioGxAoWL9f0KZcskHc9qpfuEPcMenjKVi/Y4JKrF2hXoYVOoi9Z3SPpqDinhHmplWApaDqphXqzu/S5YXDMwQJ+g5v26FIkJoATEHlfUPUtecow0mV4gSnAPbi9xOCS/D8msvfGCVADvX1972Gbn5rKIC+54EYM001lP2mfKArTsV++569/kBTFRj0lUi4a1DwV+Fgr0PCXomFvxYNezUe9npE/BWZ2GtSsVflitbkqV8PmAqmcldm469Nx16dzysNz22K9rJXaGSvUclfpZO9Til/pdbOGXOtWh/ligWoWm+Lu16xFxNADOC+aDe4bDd71W72uuXRi8nELQOhHQS4a9fzV+9n71/A38GBv4eFqy4eAbqnD3sfEzdOmFEa+nD3skm6+VAlkNRWir2fEXtHJ/6eVvxdvfj7mvF3dmPvbZchACnSnLm/oOP+hvwdHltpj0s7N/jocdni7/LJ3+eUv9Nry9DrVnjvddsqd/stgcg77Y5HPrv9Rh8sz0rtjqMxabDfcTSYOz7HjuDteR0P3q7fmSHSvudHbxn6nv+Hxr8LH0hHvlR9zAAAAABJRU5ErkJggg==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAP8AAAD9BAMAAACB7rzyAAAAJHpUWHRDcmVhdG9yAAAImXNMyU9KVXBMK0ktUnBNS0tNLikGAEF6Bs5qehXFAAAACXBIWXMAAAABAAAAAQBPJcTWAAAAJFBMVEVHcEzm4+rm4+rm4+rm4+r///8hyNXm5Ovx8vaJ4uk7z9pg2OFY7LqLAAAABXRSTlMAjMktWlAOQPgAAAgJSURBVHja7Z1Nb9tGEIb1BfQqpwZ8VeqDrm4SwFe7CeBfwJKyz6Fr+RLJluX2GICW6rvVuPcKAXK2D/11NUVS3F0uyZ2ZXU5RdE+BYmgfzbw7S+7HTKv1f0O37rsPxzs7O7u7H9423/nb41fDudB+2Hnf5E8/ljrP2uuGGN69mpe16e5Bs93f3i6Xy8WiQYTutvvbZeQJbblMP55Pv3fY/3HWu9R52oKUYT45cvXz95IOll5ZC1JvuDHCj8Oa7gWE1w6U8FNifK+uBYkYrbshUV/kGbSNFqZ9B+5femYtsC6E7tD45ydto4R9u/3fAvpP3bBvtX8P1gJ7BBv/Q/tPCazoANd/SmBhLJwg+08JyPHgDbr/hGBKjIltQv8JwYQ8APD9JwT7VAFGBADPn88XfZoASP1vYiJeBrEAZp5HJpgwCYAsgxMb/ScER1gHRBYA0E4YWhBA0l5+yQA1Am7t9B87AT4SerYckDrhGqHAmWetwXXYtueA1AkTsAIjiwCxE0A67Ng1QKJDTgNATfDGqgIzHU5BBrDdfzwxDzgNEJvgM6cBICboODEAQAVuDGBuAlcGMDbBniMDbEzQN5oGHRkgNsG10TToqv/YBLWTYtf2LKDMCFcGEoycAbzMCNP6MejOABsTDGofRGYOAV5MMOGToIkMu44NEI/EKz4JGshwz6kEUxn2OT1Q44OOYwkmMpxyeqDaB13nEkxkeMXpgdgHnzk9UOWDZjxQ4YNmPFAxDk4a8cDGB/r5ABOF/Mc/MLHoU8lMDP6q38MwvIjgPtDOyYdwD/jrF4DwHOGDA+0gBHvgJty0GdwHfSuDMFgnAL9YGYiIQThK+g8vrAxEhAR+TgFCKyIYoiWAEsHARhxeZQAPFkSAicN4AI0IEBIgAGhEgIgCBABNJMBMxQSAhTodYCYCCkBhOuhgpmICQKCq8ATzQkAA8NRngmHzAAMlDHnNAvhyKGozAEzIGiQBKCo8RL2UUgA8ORbucQD0iXGQCCDFwh7ulYQE4Iurpm3cKwkJIBCHwXcsAHPqIKABSMNgjwegL8wEUfMAi3w26CLfy2kAwmzQYwK4Jo5CIoAwDjtMAFPiKCQCCOPwhAvgaBsGIg6AxTYQDLkABtvJ2OMA8LMJucsGcEWLQ3SAa1ocogJsI1GHDWCaPY7MWAC87JGEHeCQD+DANBIHj48zFwBHhpF4tA7D8QMAIPj10cCqWSyuB3iOe/lmDhDE//PFGKB2KjhLunkyBvgt/nA8qwcYpABmYrs0BfCTT8/rQ+HAaC4Kyn5oGcBd+nFUC/DJCCBbFC+sipcBrA0HRwpQOxmehSWL0iUA27//aDYd1gJsV+VVr5YArEr+vAygZw6geFUP4Ieh4UZGOh/36iZDAeCrAcCdMUCQARhrIBxHtQDZRpJFC4xyADkYaQEE3HMzC9Q+EAUCwGUtwCr/44+1ABOzJzLhO/V9PejN9WALQLCq5FcdwF2ZYCgA3logmFUCCBKsnwvMAe5D7ddqAM4AHgAAiDIUgpEGYFWiVyJAvkUpBaMigCjBv2wCiF88rgC4C8vCdgVAz+S9ZKULRgUAkASFUGwAMNKNxAIASILmc0H+XKp896r0AxMJms8FpcFIBYBJEGiBQBOMVIAbQBQULGC4PqEJRgoAUILmj2Tqg8729ykAQAnmSySGCyTFYKQAPIfGjyKwx3LNSLzUAJQ+t9QCmK7SFYKRDACVoPhqFoFNcFEAAEswBzBeKFWDkQRwCpUg5PW8JBhJAGAJ5gDGa9VqMBIB4BLMV0jM14iUYCQCwCWYrxGZAyjBSABASBC1TCcHIwEAIcEcALBSKgcjAQAhwXylFLJWLAWjHAAjwXytGLJaLgWjHAAjwXy1HLRfIAaj7b+/CBI0P16Z71xCAMRgtG1/YiSY75iA9oykYJS1NUKC4p4RaNfsPqxsTxCAPmbf0K/sfwz4Kfm+IWy9/qYKAHLCN985he3ZjKoAAAv3wt4xcNdqVd4/5ISxsHsO3LcbWZGgeH4AunP5bEOC0nk64ObxqQ0JimdIoKdotMEIfMJaPEUDG4elwQh2yF08RwQ9SeXTJSifpALvHmtH4tjzcKMQsX8+IktQPk0HP0+4okpQOVsNHAbaxwLgPQv5RCV0GOiC0ZOHHgSYIwSnNAmqp2rh54oLweirB9TghHjB454kwcIlD/hRIp8kQWkmQJ7mWmGfRJTnMfRBlhFBgsX7BW3KJRu4BDUX7hBnq8/wEizeMUEdrH1GS1BzywZzz+geLUHNPSPMTSsfsjavSGBq5c7vCilB7YXDIUIEI4u37VAiSE1g59Ip6trzZkoazyxIAHvxe/R3+O3BsyEB9BF7TNNffz9s6OZ36b3jdkN338uzocyb8sFCf/ec//Y9e/4B9gwM7DkoGsvCMa3IhxU14YHrf20mFv5cNOzZeNjzEfFnZGLPScWelSuekyO3HqhLmMqdmY0/Nx17dj72/IT8GRrZc1TyZ+lkz1PKn6mVPVets2y95gmLufMV82dsZs9ZzZ+120XeclglCfbM7ey56/mz97PXL+Cv4MBfw4K9igd/HRM7TlhQCvpw17JJqvlQJ2FSWSn2ekbsFZ34a1rxV/Xir2vGX9mNvbYdqrqf76C+IGN9Q/4Kj+lYMHSDixqXLf4qn/x1TvkrvbZqat16zmvdtuRqv/JvX24LDrus9ttS6h0vlkul4HHjJZebr/i8cQRvzetN4636nRkiq3v+nqHu+X+o/QOS/QWj6GL1SAAAAABJRU5ErkJggg==
- https://blog.pancakeswap.finance
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAP8AAAD9BAMAAACB7rzyAAAAJHpUWHRDcmVhdG9yAAAImXNMyU9KVXBMK0ktUnBNS0tNLikGAEF6Bs5qehXFAAAACXBIWXMAAAABAAAAAQBPJcTWAAAAIVBMVEVHcEzm4+rm4+rm4+r///8hyNXn5euE4ejB8PRR1N4gyNX17X7tAAAABHRSTlMAiULK5IlAvAAAB+JJREFUeNrtnc9u2zgQxmMv0LPbAj67KeCztwv4CVhZvpebRKc4Vv0E8bZ7t9EXiC97F9rmKTeSZYmSKGn+kJpisToFqdD55ePHoUSRw6ur/y/yNb6+fp1eb65nAsHfvV3ujOuP19dDRn9dCX65fn8zTPjrt7u2azsAwrg9/BAIRvhAmVcQDILw7hJF2a7LP258dYrxtCu8yeBHhNHZ+rHqvPIO4SH++76/voKwdd4Mb4HhCxEmPppfAS/nRhgvAa3vkeAcX2GuLC18kIvvlODc/kpRCJw4kRY/N4IDgjnOfnUNZk7yjyJeDjLSiBM/02DD7wBKsQg+cA2oFJNgwjNAzALg2WDEj58RkG2wdBA/I1jQMwA/fmaDGbUBlHJDsJFrAHojvHclQCYBvieM3cXPCB4IKSh2BqDw6WjkUgCKD5dOBcD78DfH8VOCLVIA5RoAI4F7AZASuBcg8+FCUgCUBD4EwEjgRwCEBH4EgEvgSwCwBFNPAmQSTECjgCcBUgk2oAcxX/FTCWaA5wBvAqQSPMhZEGjDpccWgPTEkVcBADacexUAYEPPAqQS3PdY0G/8Fwm2MlkQlg3H3lugJxX4b4GeNpj6F6CzDYZogc42GKIFOttgiBbIJJhItkBHGwzTAh1tMB8MoGU8oLRA+OWrs/FgRBBgpbW+IUhgHZNf4QHC6AUguiW0gaNOeNTZdXDSESmd8Bxff3LSEQmdcJUDfHfSEed4AT7mAAmhH8wsj8NUC+iIYIKFCwvscwD9iG+DBxdZgAOwcWABFkDDBNNBASyZYDcsQFAfDigW4AFsHDwL7HVEB9jyPVgoEOEBGqloyQHQJIBFzYNqWICaC0cCABv+8ygPYMv2IAug5sKpBMCE60EeQMWFYxGAB24n4AJszCfyeHAAZT6bz2UAZtz3cs5YUO0GS9pbKVeBBbMXMhUw+uF4J6GA0Q9HQgCbciiKBQBUORzNmQAREWDnCoCqQJEIplIAE14a4AIERSLYSQHc89IAH+DhFwEYiQFseHmImweKTPSKC6CpALtfBGAuBzCDAoTfvh78AfRn4vCU6LsDBuDblwMEYJID9GqdvFj9DgGwB8kS5AC9cwPrKEnDPIEBjun9yaFfgQVsLNq3TAm3AYTn3972K7AAjUVBHub5EQjwOf81dDTqA7hMiic3QIATMEHmAL1j0foSp/5logVgHQG/I+SjUS/AxwLgFgSwb7ndAYCOAQBhcfeNe4BPAIDPzgFKD+g7AMAJCzCC9oLU2E+9zwMGbr8HNrAHonMUndT/KKsC+7YGs6XCHCCGZcJGMrIBhIZcj64UMFStSGADOBr3KlcAhq8qycgGcIJbAAGQ9qyk+d/uz94wAdZRcSNgPIZ6oBiOaskoA0gqoUq7RP3fU+EKVFr2qaMJQut9DgBMb//sADjqtrTd2QSAFyND2uendoB/EBY0FACwrgyA762ZsBiIYU/KOQDs3fRkSUYNBfYaPA5gBqN6Mnr+0QIQtg0aLgAqEhzsAMcEZUEkQDnM6+TW7gGNsmA5QQADCJvJqKaAOWQ8wgDuMVNEx0YL1xQwLAhbVYIEOEuQRGUyqiqwijBZ0ASAztIZySh5agIgs6DxZrTcwe5f1R8LKgAB1oLlu+EUOkd1qrmsArBudlPo2zF4pnatdWT+kXsrDXx522V+AD5FU0tGJsBKYy2ImqJpJqNUAhPAsOBdjASAz5KZyehnbOYBggVJ03TG3/nyWGAosLY/tsIAEIsHQuOx4KcJcMJmQWUsIcDMFZdef35+KgEoFrw8keEAjCej5KYEwLyONCerUdP1htZR8fNfFAsaHw4xAKbbCpK/jZ8PCIB7yjejkwXglKCzoDI/Hk/h/bCajC5+TCgWNL6aoabLw3KyoOySLVMosESIna8/6o7rlgSA+2YTdgEcMABb4tfzfXt8zDpz4+s58rvdSlccoElZsLqOB/nd7tQS3nhxRqUB9GrCdVsL/KkUJQ3gP5+fHFiwsopmjgQ48i1YXUf0CgkQ8i1YXUmF/npsleBOKVovJHw/D9kWrK1vR38/33MtWFvViu0GldcAkgVrKyqx3cDWEx8VuRNQVtWuWVmwsaoWv4giOF0mC0gWbKxux6/i+MyyYGN9/xJtgpBlwcbacrwLq8no+VFxPEjaaLbSETULWvYXsDbZ4C1o2WZD3OtHtGBzjwlpRV2RjKIfSnHyIHW/50dqFrRtNqPsMAipFrTttCKtaDtSNxxa9pqRtrmsiBa07bajrac6ot/HcgEs+w1J20zCtCPcHRQ3DdE3fr8Q3KDjWy0w2NZ3exYYcud3677j0YAAG5kaJF2dkLWwkZ+Hf5H6A+IVGMRrUMhX4RCvQzJMG3RVwxGvRSNejUe8HpF8RSbxmlTyVbnE65KJV2bzbMOgvzadeHU+8fqE8hUaxWtUylfpFK9TKl+pVbxWrXy1XvF6xfIVmz1IEODKdjuXIEBW7XZetzzAlm4Xr9wuXrtevnq/+PkF8ic4yJ9hIX6Kh/w5JvInubjoCQHvSCPp03zkzzMSP9GJeaSRk1P26Kd6KSenep2NGFPjT/jx5U92Ez/bTv50P/nzDS8+iMXiX6HOuMzk306uHF/Sp3zKn3NanvQa94XfeTvutvus28D3WbdXldN+Y3v0IQ8cTil2QTz4kcvCJz5nKsieeX1mED31+wIhee75f+j6F+xDrtlaTTKUAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAP8AAAD9BAMAAACB7rzyAAAAJHpUWHRDcmVhdG9yAAAImXNMyU9KVXBMK0ktUnBNS0tNLikGAEF6Bs5qehXFAAAACXBIWXMAAAABAAAAAQBPJcTWAAAAJ1BMVEVHcEzm4+rn4+rm4+rn4+ohyNX////m5OshyNXD5Otu1uCZ3uZCztpJ1eAlAAAABXRSTlMAk9EvXeYTAtgAAAgZSURBVHja7V1LU9tIELaxq3I12VRxdTYHX9mwVVxhQxW/YELZ1llbhD0QO4vLgb8RUxCuhsrjiqkke5WpkPyolaWRLEsj09PdUu8jc8sh9OevXzOjnu5K5cdCr9rGzvbq6uqjnWcb5Qvf2H7YGiTWz6vPyvzp2wvCo/W4JAy/Phzkrd6j9VLFn739Eqyz09Ig1CLxw7fvv6v5cu4+nEUQfipQ/rYW8vajyi7ngybi5VZRP38t/PGfPZWz7j6FEIoh4ZdWKF4tW50QwuMCLOG34C+fe+qedRcooseuhsD6jscKsD4ECBoFqP9cwVbnlNsQAvnDjwq6nHe8CAL5x56yWIEansjJV+obHweB/HNluwJDYEGAk68RNHj8HyNfIyDHg6do+SGCHjEmVn35rxV2dWapiWaALXv7T/vCE6IBDgnylfpKM8SZAYwVaV1RzGBmAH/R5CvnBm8GMwN4rahr5gpIM9j1DVDR1zdsNKjSDSA2A5QSfAVccMhXjq+EJsoDjhXP6mI8oc6lAK2EVwgLvOCSHyhhy9oCjxXf6lrboR+DrxkBqBvLiLzCEYJSebFn6YIeKwB1a+WKTzktMLbDng0BQ2YCgsTcFCTAjgKfAMW/2mAKfBd4UwAABaagGALgFFQLImBGwUtYEOR3gdgRGqA0eFGM/JkjvAKlwYIICMLhvUmxNhicFCVfOYNBH+CD48IA+DuT3v0+eFyc/Nm+oHmvD14XCMDfF7y8zwSHRcqfBaMtMROEmGGxJggww7VCTVCbYWOpBt4UDMBPCP2lGvCKBnC7TAdrzHvhnP1xY4kGrgsH4IeC/hINFC/fT8o9SQ0s00E5Gliig3I0sMQPdkvRQKADcz4oIQpFsaiZk4k9VZIOjDl5s/A8kMgH60YnPCkJgDI6Yq3wTJzMyX2TCcD3Qs53mrW0TUawCXfCzpG7PyY64rphOwx2wpHrugfcjmhhAm13tq6ZjQBuAs4oAHDAbARwE7h1w/WG1wjWoCbgHGkA+zQjaGQSwdiOABoFV4PDTCKwJIBGwV7aCFagiWDquhwUdNN7gl1gInAS8ikUOOk9QQu4G0sSQKLgZjEU1YB7gQUCXPd3yp6gjwlDl4sA3AuuULQCC0OdlHx338OHot5iHDzBEOC6JwQrXLeOgxkCfCvweGIhLA5mCSBQsBAL66A4aCCAQMFe8ta0CoqDUxMAdCzoJt3gAcgJRkYAf+AzctIJ/gT8F6N8/MYk6QYgJ3CYASTdoAVxghwA+3g3aFpmgugn6x3BiMhAIhvUYZlASxxrAF9pRuhng1d2Xqjj0IsIiDeipeSEHwJTUXgeGMcAwn9zpCOYF4Y6eBGrwlMTSihO+uEucEveGbkHXgKAf0Q5x8v3/XArDgPQc5aXMEbydcpNHAhadjcDXADmgcDycogLwG2UkGuW94NcAPaiSFS3/E7EBSCORFXL6zEuAHEkWrG8IeUCEEeiB5b3c1wAnGhL8gAYCLkBqAjApuUdMRuAUx2Ld+UAbFlG4sV9ARlAFIvXLO9o2Ri40gBaOABjBgBNDcCTYeBWAxjgAIwZABxqAEqGgb0QQA0JYMwAoB8CGDIwcHf2GZEOcQAmBga64X4VBaDOwcAIoxS9Iajbfi0zMNBFHZK6SAAGI3yOOqdqAFUGBvTtUUkADAxMUKFB78k4GMCFBiyAfAbGPxj4nzAwYWagLsgAWyie/MsBDIUA6GxYEwTQ/4cAGAgBiK5IbAFcZlMfFsAh6lwwzSZ/HIDoXGB7Mmpnb8mxAJqos6E6ylxS4wBEZ0Pb07H6mtn/YQE0UPcDSr1L1xHhAET3A7v0Mj4cgOiGZFMOwDrqlowNwPya7kQEQHxPuEKvJUUBiG9Kq/RSSg3Azpviu+I6/VUFioH4trxGrydGMRB/L6jQy2lRDMRfTOyTAQ8D829Ga+SachQD869m9FiMYmD+3XCTHApRDMy/nNIjEYaBxLdjeiTCMJD4ek6PRJcIBhL1AzVyIMAwkKynIwcCDAOJGhJ4Sa1h3XmLRvj+I9gLG5UK3Q8nQVFhzMCs6vnC1guhlVRGRYaqjxmYgk1hoZIK74dH4RklYqCj61zsvBBaTWf6K7qgLWLgEl5qulBNV8G+rniuq6k0gC8u/Mp2sbYa6wapCr+o3u7a0gnANaV5/p9eAACpmlJsOpqiAaSqaqvIbPDcDABgUKm6Ymw2aBvlQ7wgVVkNri1Pa9IIABIHUrXl4Op6kBXCbHAL974gbUvIIs/M+4IqNhZOUSaYfWGBjoWJJx8WFpB9Y4LfEmQcAeRO2Vc2m+iMPEEUmxveGVXRG9Mu4sWB4aUV4bnhpX2puenBIX5f6NiXOZ8anlzijSDx+Aq4Lza+N6wSTicjy0LztunpM+XNadsmBuWYAO3V7cQiBgWJoMH87rhj9fk+590x6eX11ObBS87La5tnr1lWRxYVHDlvz2mv751PX6D85b6+F+8/IN6BQbwHRUk6aOd34RDvQyLeiUW+F414Nx7xfkTyHZnEe1KJd+WS70sm3plNvjedeHc+8f6E8h0axXtUynfpFO9TKt+pVbxX7YwC2W69Nel+xUVQYNexWbxntXzXbvG+5fKd28V718t37xefXyA/wUF+hoX4FA+uOSaEcTbSk1zkZ9nIT/ORn2ckPtFJfqYVdaoXx5Q/6blm8pPdxGfb4af7Mc8XFJxvKD/hsSI+47IiP+VTfs6p/KTXivis24r8tN+K+LzjNASBic+BImRnXmsMklO/IxAbOztic8//Q+tvuM0gsihA9V0AAAAASUVORK5CYII=
- solana_signAndSendTransaction
- solana:signAndSendTransaction
- https://blog.pancakeswap.finance/articles/solana-crosschain-swaps
- https://blog.pancakeswap.finance/articles/tokenized-rwas
- https://blog.pancakeswap.finance/articles/monad
📡 API Calls Detected
- https://proofs.pancakeswap.com/cms-config/tokens-routing-config.json
- /__cookies__
- https://api.blocto.app/networks/evm
- https://www.google.com/ccm/geo
- 0x3b3b57de
- account
- POST
- https://aptos.pancakeswap.finance
- stats
- /mev
- /api/paymaster
- proxy
- https://obj-cache.pancakeswap.com
- https://raw-api.pancakeswap.com/ondo/market-status
- GET
- https://raw.githubusercontent.com/pancakeswap/airdrop-v3-users/master/forFE.json
- logs
- https://raw-api.pancakeswap.com/ondo/status
- https://api-v3.raydium.io/main/auto-fee
- https://proofs.pancakeswap.com/cms-config/routing-base-config.json
- /api/auth/telegram-callback
☁️ Cloud Backend
- Firebase: pancakeswap-prod-firebase.firebaseapp.com
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- Kit signatures: angler
- 3018 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 3018 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)