Phishing Analysis
Detailed analysis of captured phishing page
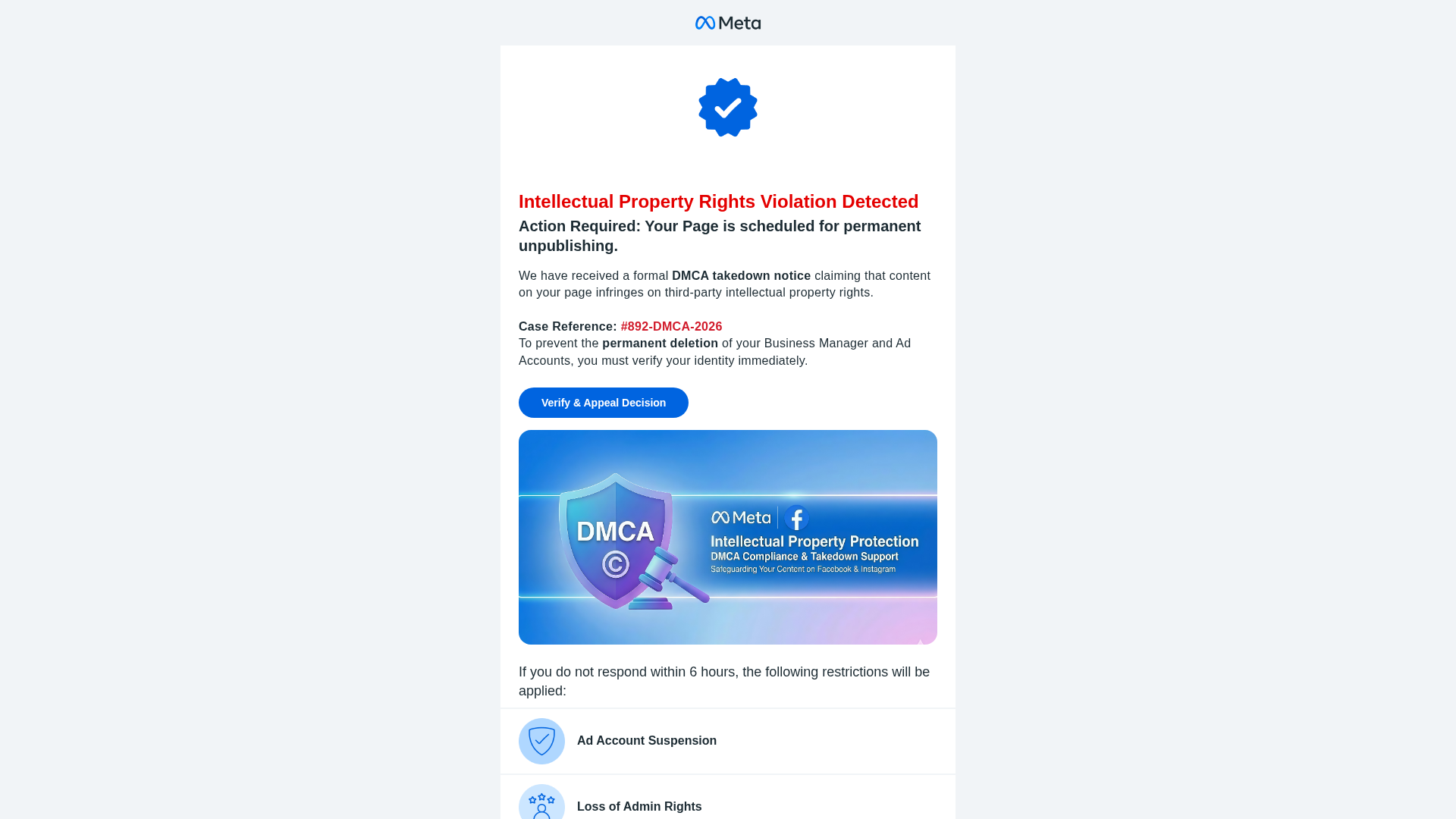
Visual Capture
Detection Info
https://sw.run/MexteaDMCA
Detected Brand
Meta
Country
International
Confidence
100%
HTTP Status
200
Report ID
cdc778d7-598…
Analyzed
2026-01-22 11:35
Final URL (after redirects)
http://15.235.156.55/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1CF724310D904891D01DF8EC5E1736A5812F803AEC71304D8FE60ABFAA6EF878C777669 |
|
CONTENT
ssdeep
|
192:Qp+XBSw+0LrVS3dNMAAzvE2v7ar7lrCmr0s9QOvqHKxrZWmWkEcGMkRY/zO2Yzoc:uaO8TAwRm92U1ROEXUac7d |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3cecc6699996618 |
|
VISUAL
aHash
|
ffffe7efc3c3efff |
|
VISUAL
dHash
|
28280c584d4d1c38 |
|
VISUAL
wHash
|
fce4c4ccc0c0c4cc |
|
VISUAL
colorHash
|
070030000c0 |
|
VISUAL
cropResistant
|
28280c584d4d1c38,24a42936165c2c08 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: Meta users internationally
• Method: Fake intellectual property violation notice
• Exfil: Data sent to unknown server
• Indicators: Domain mismatch, obfuscated JavaScript, urgency tactics
• Risk: HIGH - Immediate credential theft
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
📡 API Calls Detected
- https://ipinfo.io/json?token=0916643fd922ec
📤 Form Action Targets
- //translate.googleapis.com/translate_voting?client=te
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for sw.run
Found 10 other scans for this domain
-
https://||sw.run/verifybluetick^$all/
https://||sw.run/mszhm^$all/
https://||sw.run/mexteadmca^$all/
https://sw.run/
https://sw.run/Verifybluetick
https://sw.run/Verifybluetick
https://financeroutine.com/money-management-tools-...
https://financeroutine.com/simple-investment-plan-...
https://sw.run/MexteaDMCA
https://financeroutine.com/daily-financial-literac...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.