
Phishing Analysis
Detailed analysis of captured phishing page
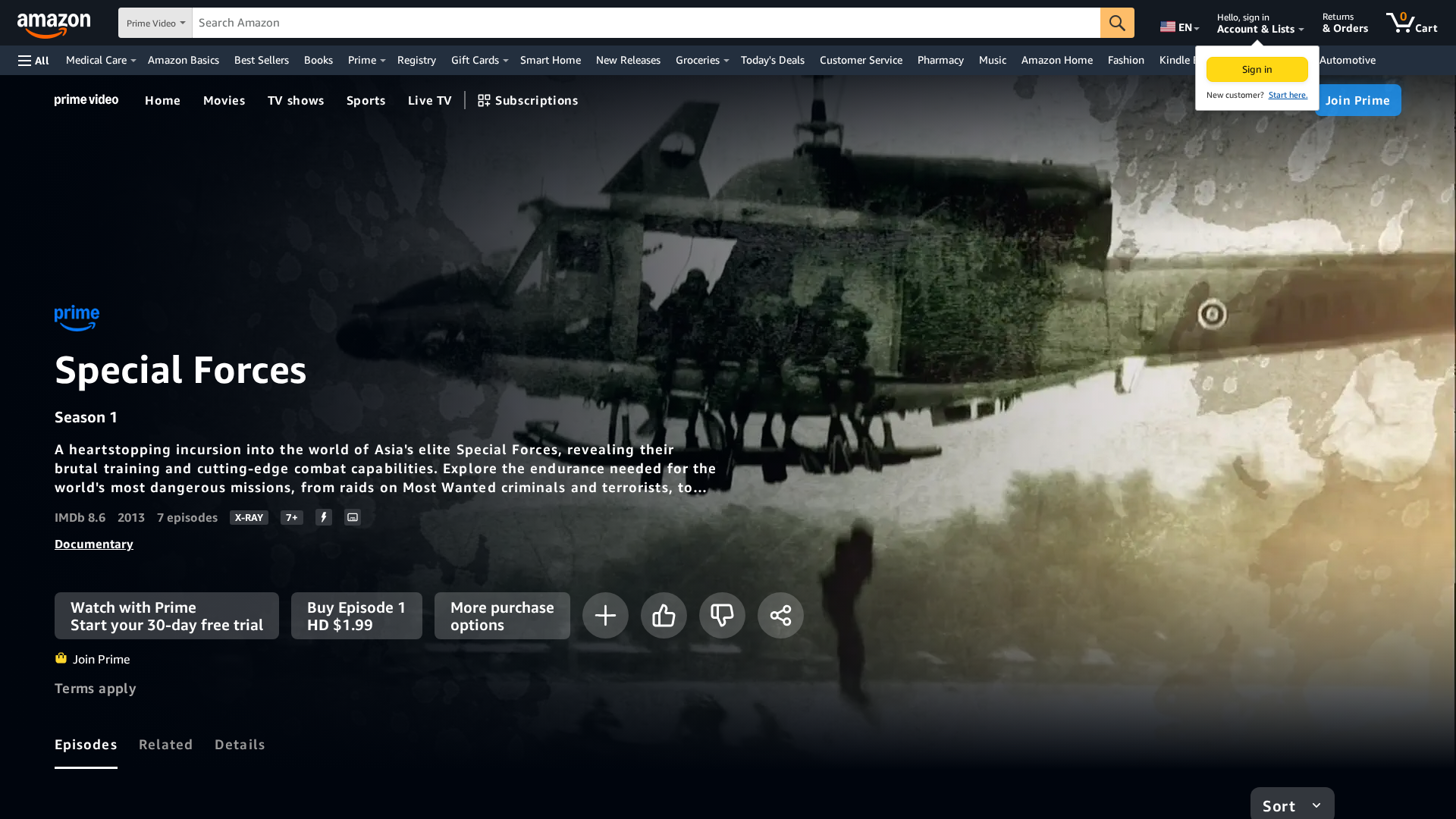
Visual Capture
Detection Info
https://dfgdh1.pages.dev/-/zh/gp/video/detail/B0CTXRFD44/ref=atv_dp_amz_c_TS8274d9_1_2?jic=16%7CCgNhbGwSA2FsbA==/
Detected Brand
Amazon
Country
USA
Confidence
100%
HTTP Status
200
Report ID
cf313439-2fc…
Analyzed
2026-02-13 23:40
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14554E7F3929400B71227CBDAF57A674D21E3F14DEF0A85809AE807689FF6D46A137835 |
|
CONTENT
ssdeep
|
3072:OVgTaOHhnSCADgCWDJo2xDaDv7hiTwYwE0m3dThToXX6URv:agTa6hnSCkgCWDJo2xDaDv7himX6URv |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a5c55992d2d0d997 |
|
VISUAL
aHash
|
7f0303070f0f0300 |
|
VISUAL
dHash
|
ea77f6afeeff7f3f |
|
VISUAL
wHash
|
ff071b073f1f0700 |
|
VISUAL
colorHash
|
1b602000000 |
|
VISUAL
cropResistant
|
808082d2d2c28080,e1b0b891b1b0ab91,7ad6a692d0818707,b7f3e3d899dbfbff,ea77f6afeeff7f3f |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Amazon users
• Method: Impersonation via free hosting
• Exfil: Likely user credentials via forms
• Indicators: Free hosting, brand logo.
• Risk: HIGH
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://{deviceType}.{region}.prod.service.minerva.devices.a2z.com:443/metric-batch
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/oflc/r13.png
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/adjctq/a12.png
- https://m.media-amazon.com/images/I/41rP+7jmm4L.js?DVWebNode_apex-conditional-site-wide
- https://unagi
- https://m.media-amazon.com/images/S/sash/Ew2RCbkJJWYLRzR.woff2
- /gp/video/collection/newandupcoming?jic=8%7CEgNhbGw%3D
- https://m.media-amazon.com/images/G/01/digital/video/web/Default_Background_Art_RTL.jpg
- https://www.aboutamazon.com/?utm_source=gateway&utm_medium=footer&token=about
- /gp/video/collection/valentinesday?jic=8%7CEgNhbGw%3D
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/fpb/13.png
- https://m.media-amazon.com/images/I/81BXdoJ-FBL.js?AUIClients/FWCIMAssets
- https://cloudfront.xp-assets.aiv-cdn.net/family/web/ATVWebPlayerSDK-1.0/
- /?ref_=footer_logo
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/djctq/18.png
- https://logistics.amazon.com/marketing?utm_source=amzn&utm_medium=footer&utm_campaign=home
- https://tracker.marinsm.com/tp?act=2&cid=
- http://tiny/c1mr5h0u
- https://app.primevideo.com/detail?gti=${e}&r=app`:`https://watch${(0,i.Kr)()}/detail?asin=${e}&r=app`,(0,r.V)(r.p.DETAIL_PAGE).URL({url:t})}},
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/adjctq/a18.png
- /gp/video/collection/inspire-and-uplift?jic=8%7CEgNhbGw%3D
- https://email.aboutamazon.com/l/637851/2020-10-29/pd87g?utm_source=gateway&utm_medium=amazonfooters&utm_campaign=newslettersubscribers&utm_content=amazonnewssignup
- /gp/video/collection/BHM?jic=8%7CEgNhbGw%3D
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/fpb/18.png
- https://m.media-amazon.com/images/S/sash/pDxWAF1pBB0dzGB.woff2
- https://m.media-amazon.com/images/G/01/digital/video/web/Default_Background_Art_8x3_RTL.png
- https://${e}.xp-assets.aiv-cdn.net/family/${r?
- /gp/video/collection/Musicvideosandconcerts?jic=8%7CEgNhbGw%3D
- /ref=nav_logo
- /gp/video/collection/AccessibleCollection?jic=8%7CEgNhbGw%3D
- /gp/video/collection/Awards?jic=8%7CEgNhbGw%3D
- https://sourcemaps.web.pv.amazon.dev/61af9ac254906f0f384787f374af2730d1d9a9817fb9ea4b72bb70ea8fe54efc30651fb3b9917188c16d0f0586f31f79b4bd0e02ea195ad6b65c6e6048384a7fac9dff0988e910ca788764bfce08178e21a5742a92ffaecb63ae08689cd89ce8181612264b095a6e43b6d44d3dc61d5fe1405fa06ff322a75efa1b46077e6b335dfb78dcd87a8f61d4a999342c2206e357227dc0def62446b499b420ec5cbccb94755b1b3b6c6225f20be7f80d0c179aa8cb598dfbb2e11f6b19be65ae56843c016bdcf6094a746c5443ffb5ab0539f9bb8d7a47b4a8af854edaa8c6d2ae0717bef629d712846b98a360d7c46b3fe83c9f0e0d044eee1852a80f4373405587d4
- https://${e}`)))((0,Ee.jS)()))).then((e=
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/cvod/18.png
- http://a
- /gp/video/collection/primerolatino?jic=8%7CEgNhbGw%3D
- https://m.media-amazon.com/images/G/01/shopbylook/shoppable-images/next_tab_control._CB416468320_.svg
- https://sourcemaps.web.pv.amazon.dev/08f085c9bdd2376c47b5179c917eeef2c460a8228d7d757ab619bd638932139d1be47bffc6a7a37870fab56b6c683e3c167a52fda69282c4bd95d64cd7989749e7cf5ef874372f4aabcfb810a6a9db0966d5192750193825b028a4e5ed24898378e72d23d4ceed147b7148a3c4def4452be8d9c5374366b31961d6df645bab785e12afdd64aa557df562a745c44b742727b562025deeb5ba5e36c3750214a144648e2677901037b7007897224d16670550694e0578cdc6fc1d44881d3d0cb532defe2c1dce52e7281646d31fa349d31bf8ec1d0f2ff8994ef083f0c9955f495ba03fd619aea4899c45657fa3eb0fd0801a71db41fb8b91bdedefb4e87ad959cc
- https://akamai.xp-assets.aiv-cdn.net/family/web/ATVWebPlayerSDK-1.0/
- https://cloudfront.xp-assets.aiv-cdn.net/family/
- /gp/video/collection/mgForYou?jic=8%7CEgNhbGw%3D
- https://m.media-amazon.com/images/I/31hknpW-QwL.js?AUIClients/BotDetectionJSSignalCollectionAsset
- https://sustainability.aboutamazon.com/?utm_source=gateway&utm_medium=footer&ref_=susty_footer
- https://m.media-amazon.com/images/G/01/digital/video/web/Default_Background_Art_2x3.png
- https://m.media-amazon.com/images/G/01/vcc/maturity-ratings-logos/png/oflc/rp18.png
- http://jquery.com/
📡 API Calls Detected
- GET
- /gp/video/acquisition/utilities/monitoring
- POST
- https://
📤 Form Action Targets
- get
- /gp/video/search/ref=atv_nb_sug
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUTERON0ZKL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /gp/video/auth-redirect/ref=atv_wl_tog_sign_in
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUWFJDNzNXL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUWFRIMUpOL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUVkpaWUtCL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /s/ref=nb_sb_noss
- /gp/video/auth-redirect/ref=atv_dp_react_sign_in?signin=1&returnUrl=%2Fgp%2Fvideo%2Fdetail%2FB0CTMD8L3H%2Fref%3Datv_dp_react_sign_in_return
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUTEpOU0s2L3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUWFNUMUxCL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
- /gp/video/acquisition/workflow/ref=atv_dp_non_js_pur?workflowType=Core-TVOD&return_url=L2dwL3ZpZGVvL2RldGFpbC9CMENUTUQ4TDNIL3JlZj1hdHZfZHBfbm9uX2pzX3B1cl9yZXQ%3D
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting
The domain uses free hosting, which is a common indicator of phishing.
Brand Impersonation
The site visually impersonates Amazon Prime Video.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Amazon users (USA)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 7803 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Amazon Prime Video
Official Website
https://www.amazon.com/gp/video/getstarted/
Fake Service
Amazon Prime Video streaming service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attackers are likely trying to steal user login credentials by creating a fake login page that mimics the Amazon Prime Video interface. User credentials are then sent to the attackers.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
Main File
21fYSeFelaL.js
File Size
🔬 JavaScript Deep Analysis
Operator Language
English (0%)
Sophistication Level
Basic
Total Code Size
4.6 MB
🔗 API Endpoints Detected
Other
92
🔐 Obfuscation Detected
- : None
- : Heavy
- : Moderate
- : Moderate
- : Light
- : Light
- : Moderate
- : Moderate
- : Light
- : Moderate
- : None
- : Moderate
- : Moderate
- : Light
- : Light
- : Moderate
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Main Drainer
21fYSeFelaL.jsFile Size
4709KB
Scan History for dfgdh1.pages.dev
Found 7 other scans for this domain
-
https://dfgdh1.pages.dev/dp/B09PD246FV/ref=sbl_dpx...
https://dfgdh1.pages.dev/gp/new-releases/books/120...
https://dfgdh1.pages.dev/gp/most-wished-for/electr...
https://dfgdh1.pages.dev/Crash-Freida-McFadden-ebo...
https://dfgdh1.pages.dev/-/zh/gp/customer-reviews/...
https://dfgdh1.pages.dev/-/zh/-Audible-Books-Origi...
https://dfgdh1.pages.dev/gp/most-wished-for/sports...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.