
Phishing Analysis
Detailed analysis of captured phishing page
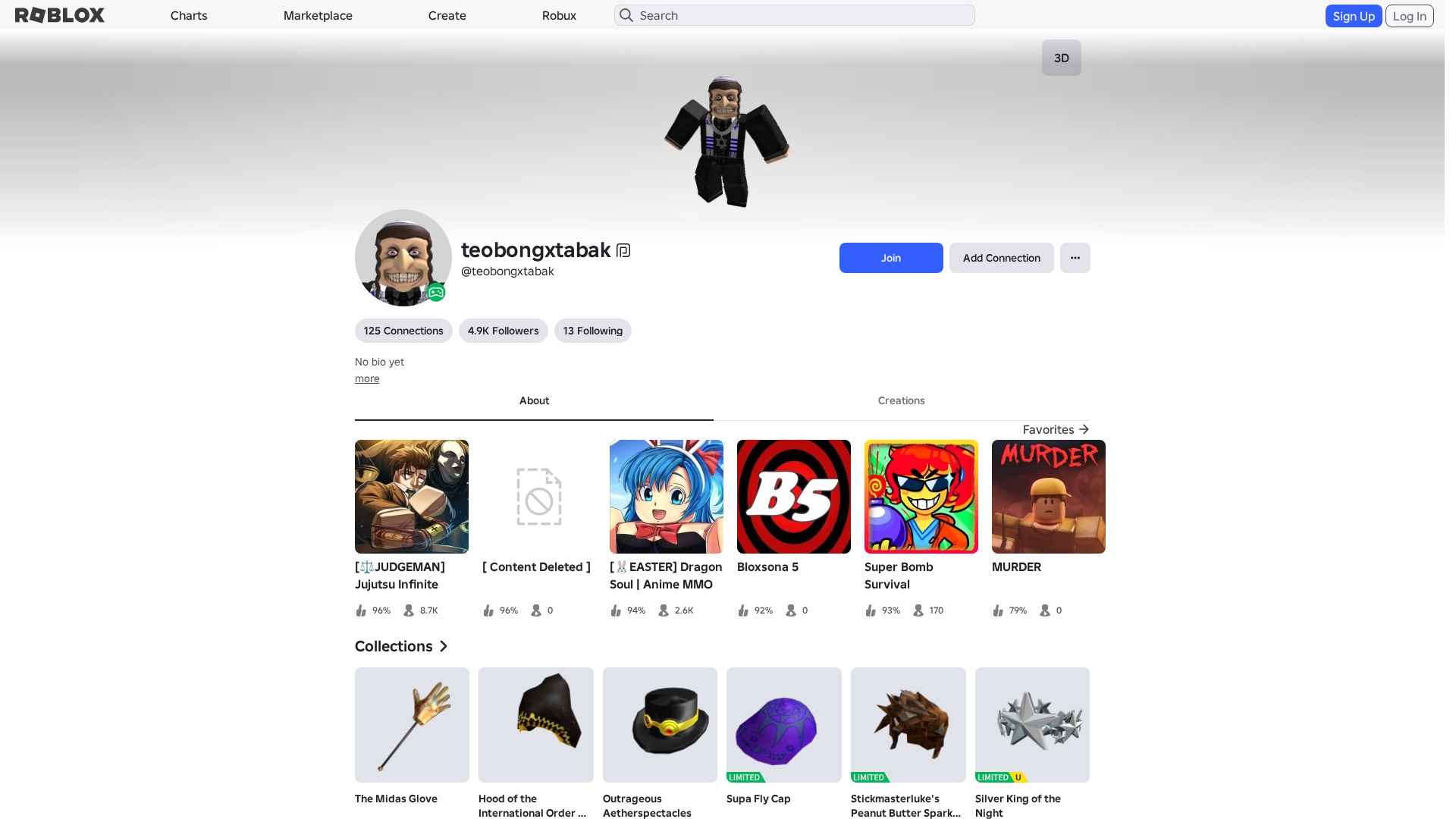
Visual Capture
Detection Info
https://www.robiox.com.py/users/398635291445/profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
d0c45572-6b1…
Analyzed
2026-04-07 22:45
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19253867292212837617FB5D9F164771991D3D70FCA8247E1A2F8936A0FDACA1FC5380A |
|
CONTENT
ssdeep
|
1536:l3aXWn+r/cVelefglkgbUg+8glrgUYgL+iXYa2HyEH4nGOuglZQmTF3kiEq:1aXWwcqVcj19aa2SEKGNglZ7 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e412136ded99ac6c |
|
VISUAL
aHash
|
0020dfffc3c3efc3 |
|
VISUAL
dHash
|
e8e8363027261e0e |
|
VISUAL
wHash
|
0000dfffc3c3c7c3 |
|
VISUAL
colorHash
|
07400008040 |
|
VISUAL
cropResistant
|
e8e8363027261e0e,8c4d73d99d0d0e96,6955c6c4acb85769,b28c7331386b3f1f,a3b2b2b8d8e4e46c,31145a707133b334 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/439945661/Silver-King-of-the-Night
- https://api.injuries.lu/catalog/17408016/Hood-of-the-International-Order-of-Buildmasters
- https://www.roblox.com/catalog
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F398635291445%2Fprofile
- /login?returnUrl=
- https://api.injuries.lu/catalog/169444294/Stickmasterlukes-Peanut-Butter-Sparkle-Time
- https://api.injuries.lu/catalog/17407931/The-Midas-Glove
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F398635291445%2Fprofile
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/17408011/Outrageous-Aetherspectacles
- https://api.injuries.lu/catalog/7636350/Supa-Fly-Cap
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- get
- POST
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.robiox.com.py
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for www.robiox.com.py
Found 10 other scans for this domain
-
https://www.robiox.com.py/users/262683709646/profi...
https://www.robiox.com.py/users/387072077925/profi...
https://www.robiox.com.py/users/217025834840/profi...
https://www.robiox.com.py/users/335157511751/profi...
https://www.robiox.com.py/users/239884675658/profi...
https://www.robiox.com.py/users/377777277866/profi...
https://www.robiox.com.py/users/255445160301/profi...
https://www.robiox.com.py/users/378472335145/profi...
https://www.robiox.com.py/users/411240076850/profi...
https://www.robiox.com.py/games/90118298734859/EMO...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.