
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
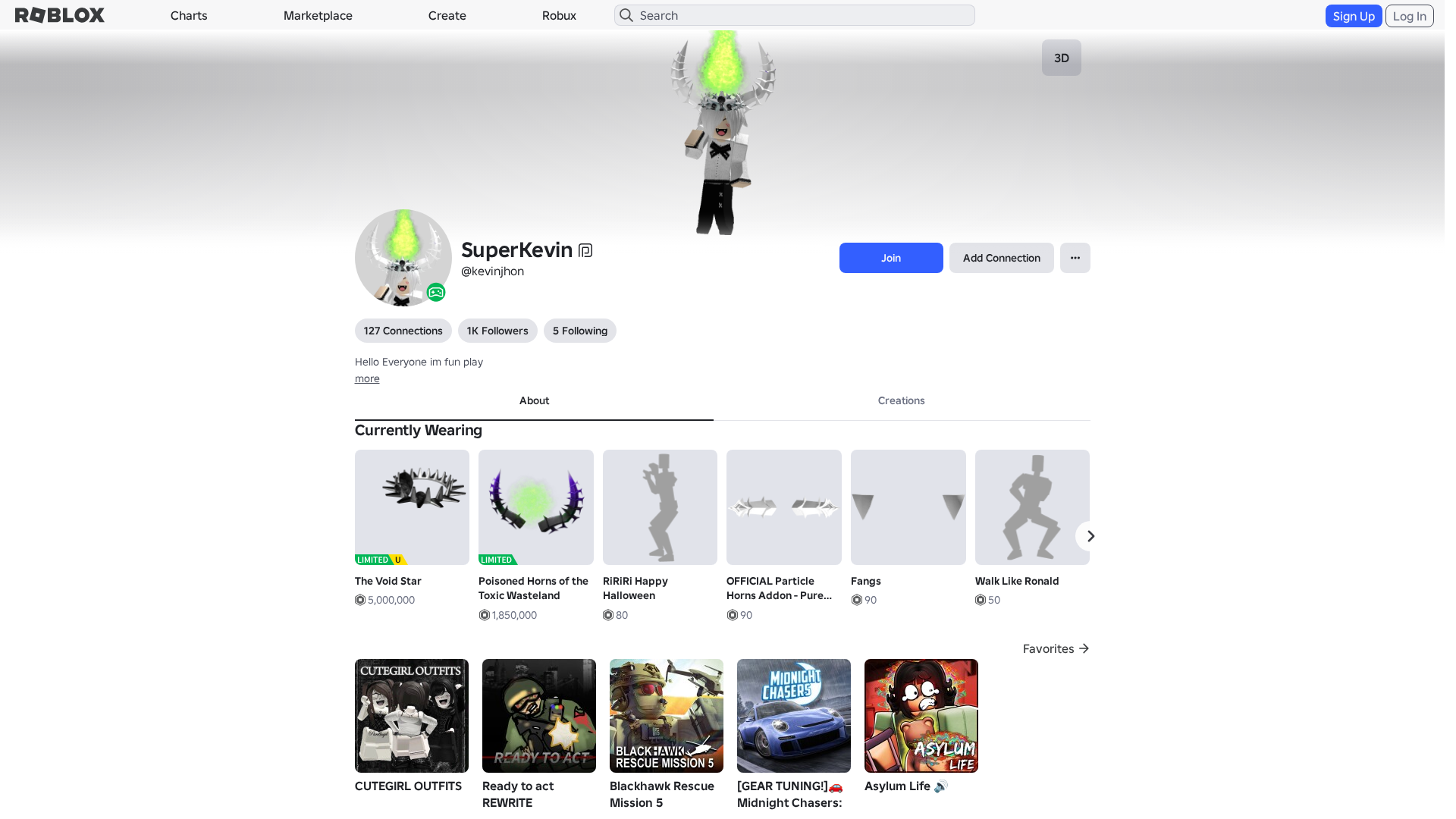
Detection Info
https://rblx.foo/s/users243671918813profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
d14ca21d-273…
Analyzed
2026-03-27 16:28
Final URL (after redirects)
https://www.robiox.com.py/users/243671918813/profile
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19883327292542837617B79DAF064672AD2D3C70FCA8346E1A2F8D39A0FD6CD1E96340D |
|
CONTENT
ssdeep
|
1536:GtzXWn4r656eOGsgJRghGglHgzwlg+T0gsygZVgHlgLbg/2glGg4Ggoig/2gmTgB:szXW1534NUwFelk6m9wgDuSEqBO7qjCU |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0c7304b92bccf3c |
|
VISUAL
aHash
|
0000d7ffcfffc3c3 |
|
VISUAL
dHash
|
e8e8a630b61a969e |
|
VISUAL
wHash
|
0000d7ffcbc7c3c3 |
|
VISUAL
colorHash
|
07440008040 |
|
VISUAL
cropResistant
|
e8e8a630b61a969e,35b5741696961535,469ab39b93b39bac |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/82472002425747/Walk-Like-Ronald
- https://api.injuries.lu/catalog/5319927054/Oldschool-Swim
- https://api.injuries.lu/catalog/5319931619/Oldschool-Climb
- https://api.injuries.lu/catalog/124343583684063/Fangs
- https://api.injuries.lu/catalog/101481154733615/all-black-pants-with-white-ribbons
- https://api.injuries.lu/catalog/126354114956642/adidas-Community-Animation-Pack
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/138043046957459/S15-Thin-Right-Leg
- https://api.injuries.lu/catalog/70377346830781/OFFICIAL-Particle-Horns-Addon-Pure-White
- https://api.injuries.lu/catalog/84573004630668/S15-Thin-Left-Leg
- https://api.injuries.lu/catalog/130433936882245/Super-Super-Happy-Face-Head
- https://api.injuries.lu/catalog/5319914476/Oldschool-Fall
- https://api.injuries.lu/catalog/85665834724929/intrusive-awkward-wave
- https://api.injuries.lu/catalog/5319917561/Oldschool-Jump
- https://api.injuries.lu/catalog/119944754814745/S15-Thin-Left-Arm
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/117201516459260/Wanna-See-Me-Dance
- https://api.injuries.lu/catalog/73680983308648/The-Void-Star
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F243671918813%2Fprofile
- https://api.injuries.lu/catalog/85092320680319/Nonchalant-Sit
- https://api.injuries.lu/catalog/98464793617142/RiRiRi-Happy-Halloween
- https://api.injuries.lu/catalog/133757109397390/S15-Thin-Right-Arm
- https://api.injuries.lu/catalog/91773089278851/Street-Flow-Bounce
- /login?returnUrl=
- https://api.injuries.lu/catalog/2510238627/Rthro-Run
- https://www.roblox.com/catalog
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F243671918813%2Fprofile
- https://api.injuries.lu/catalog/101631968712095/Sword-Guard-Stance-Pose-1-1
- https://api.injuries.lu/catalog/92485119590117/S15-Thin-Torso
- https://api.injuries.lu/catalog/73931432971519/vkei
- https://api.injuries.lu/catalog/439945661/Silver-King-of-the-Night
- https://api.injuries.lu/catalog/1744060292/Poisoned-Horns-of-the-Toxic-Wasteland
- https://api.injuries.lu/catalog/125290815319101/tuft-hair-white
- https://api.injuries.lu/catalog/139371349828009/xaviersobased
- https://api.injuries.lu/catalog/124102129879581/Super-Super-Happy-Face-Mood
- https://api.injuries.lu/catalog/2510242378/Rthro-Walk
📡 API Calls Detected
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev${e.endpoint}
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- https://kyxn.dev/api/shorten
- GET
- /api/shorten
- get
- POST
- /api/pageview
- https://apis.
- https://www.google.com/ccm/geo
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 226 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 226 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 226 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
rblx.foo
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for rblx.foo
Found 10 other scans for this domain
-
https://rblx.foo/s/cyFAoF
https://rblx.foo/s/J3h4AL
https://rblx.foo/s/myroblox
https://rblx.foo/s/1p8tkN
https://rblx.foo/s/roblox-com-users-3324118
https://rblx.foo/s/www-roblox-coms
https://rblx.foo/s/roblox-com-users-3110201
https://rblx.foo/s/robIox-profiIe
https://rblx.foo/s/LX0Gyi
https://rblx.foo/s/rxgKLr

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.