Phishing Analysis
Detailed analysis of captured phishing page
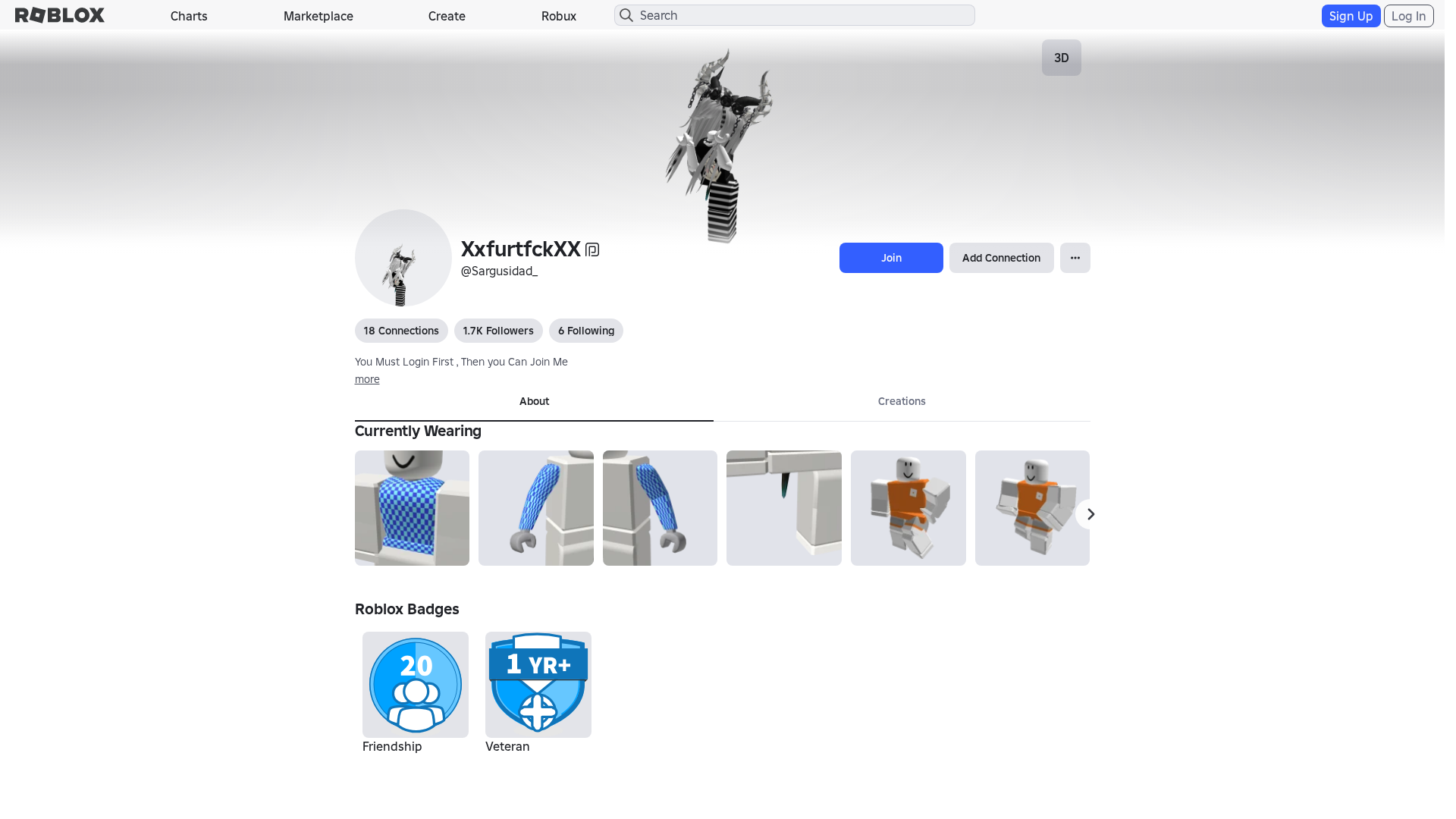
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FD73867292502437617B79D9F165771AA2D3D70FCA8246E1A2F8A39A0FD6CE1FC1340E |
|
CONTENT
ssdeep
|
1536:ekvXWn9rxCM+L5vEJE+YuOfegNZi7HZ7Hb7Hz7HJ7H37Hg7HC7HL7HT7Hy7Hv7H5:dvXWDCMccyruO275777T7p7X7A7i7r7E |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b8474331c798ecbc |
|
VISUAL
aHash
|
0000d3ffc3c3dfff |
|
VISUAL
dHash
|
e8c8b63016363032 |
|
VISUAL
wHash
|
0000c3dfc3c3cfdf |
|
VISUAL
colorHash
|
07002000180 |
|
VISUAL
cropResistant
|
e8c8b63016363032 |
Code Analysis
🔬 Threat Analysis Report
• Threat: Impersonation Phishing
• Target: Roblox users
• Method: Domain spoofing and JavaScript obfuscation to steal credentials.
• Exfil: Unknown
• Indicators: TLD mismatch, JavaScript obfuscation, form submissions.
• Risk: High
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog/86499666/null
- https://trades.
- /login?returnUrl=2011286467736318
- /catalog/2510242378
- https://en.help.roblox.com/hc/
- https://search.
- https://voice.
- /catalog
- https://feross.org
- https://www.roblox.com/catalog/77318417634476/null
- /catalog/86499716
- /catalog/86499666
- https://api.
- https://itemconfiguration.
- https://inventory.
- /catalog/4660621665
- https://tarobi-dev-test.com
- /catalog/5063543382
- https://js.rbxcdn.com/5c8a2ba3737908f693394045e81ebd71c77cde6f87550ea51f7833e8c98200ae.js
- https://www.roblox.com/catalog/86499698/null
- https://engagementpayouts.
- https://feross.org/opensource
- https://www.roblox.com/catalog/139607718/null
- https://roblox.com
- https://www.roblox.com.ml/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/catalog/5621576440/null
- https://followings.
- https://chat.
- https://www.roblox.com/catalog/12479835990/null
- https://www.roblox.com/catalog/11573370910/null
- https://sourcemaps.rbxcdn.com/internationalCore-db1cf6cdaa102b16.js.map
- /catalog/1018553897
- https://тест
- https://www.roblox.com/catalog/86499716/null
- /catalog/139607718
- https://js.rbxcdn.com/098e80c8e9f4dad5295663f4a79f9a64.js
- https://accountsettings.
- https://js.rbxcdn.com/a3fe79f1bfdd96b7f0ad20eab2de7a05.js
- https://a
- https://www.roblox.com/catalog/2510242378/null
- https://app.lightstep.com
- https://a/c%20d?a=1&c=3
- https://js.rbxcdn.com/df687479f6a19a6541dc4c819b900ac9b19bef72681f89040066b80bf8f82c15.js
- https://js.rbxcdn.com/964fdc5ae2518a2c9c9d73f67eee026b844e68c2d3791ac6c8e28c0f979a3854.js
- https://www.roblox.com/catalog/11600327265/null
- https://mui.com/production-error/?code=
- https://www.roblox.com/catalog/15093053680/null
- https://www.roblox.com/catalog/109307809085242/null
- https://www.roblox.com/catalog/4660621665/null
- http://www.roblox.com.ml/js/EnvironmentUrls.js
- https://premiumfeatures.
- /catalog/86499698
- https://www.rblx.org
- https://www.roblox.com/catalog/115477967934105/null
- http://getbootstrap.com)
- https://www.roblox.com.ml/info/blog?locale=en_us
- https://www.roblox.com/catalog/5063543382/null
- https://www.roblox.com/catalog/1018553897/null
- https://www.roblox.com/catalog/12178647739/null
📡 API Calls Detected
- get
- GET
- babylonjs
- https://help.roblox.com/hc/articles/30428367965460
- POST
- https://apis.
- https://ro.blox.com/Ebh5?
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 266 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker likely uses a fake login page that mirrors the Roblox login to steal the user's username and password.
Secondary Method: JavaScript Obfuscation
The obfuscated JavaScript is used to avoid detection by security scanners and potentially to redirect the user to malicious sites after credential capture.
🌐 Infrastructure Indicators of Compromise
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : Heavy
- : Heavy
- : Light
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
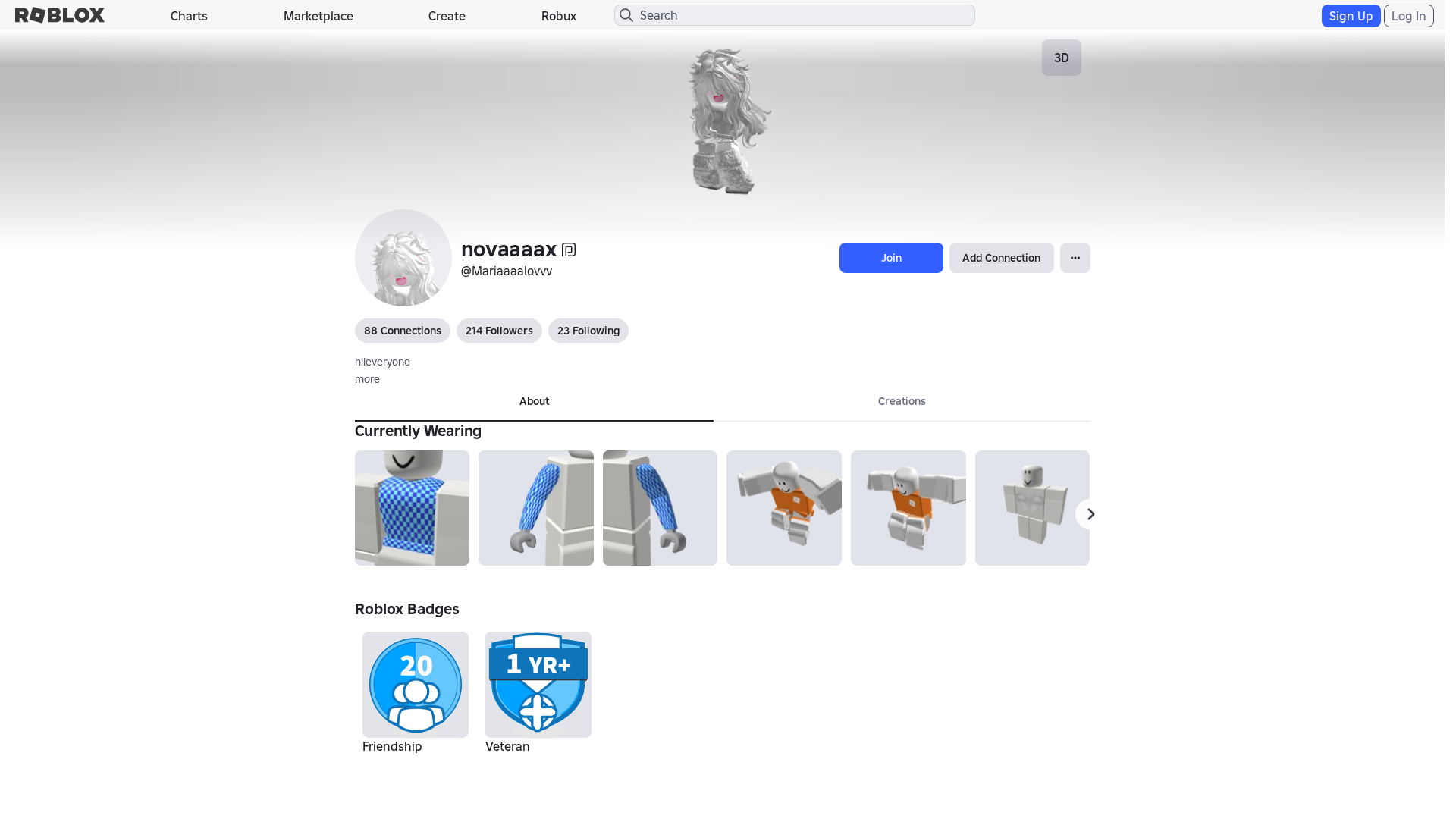
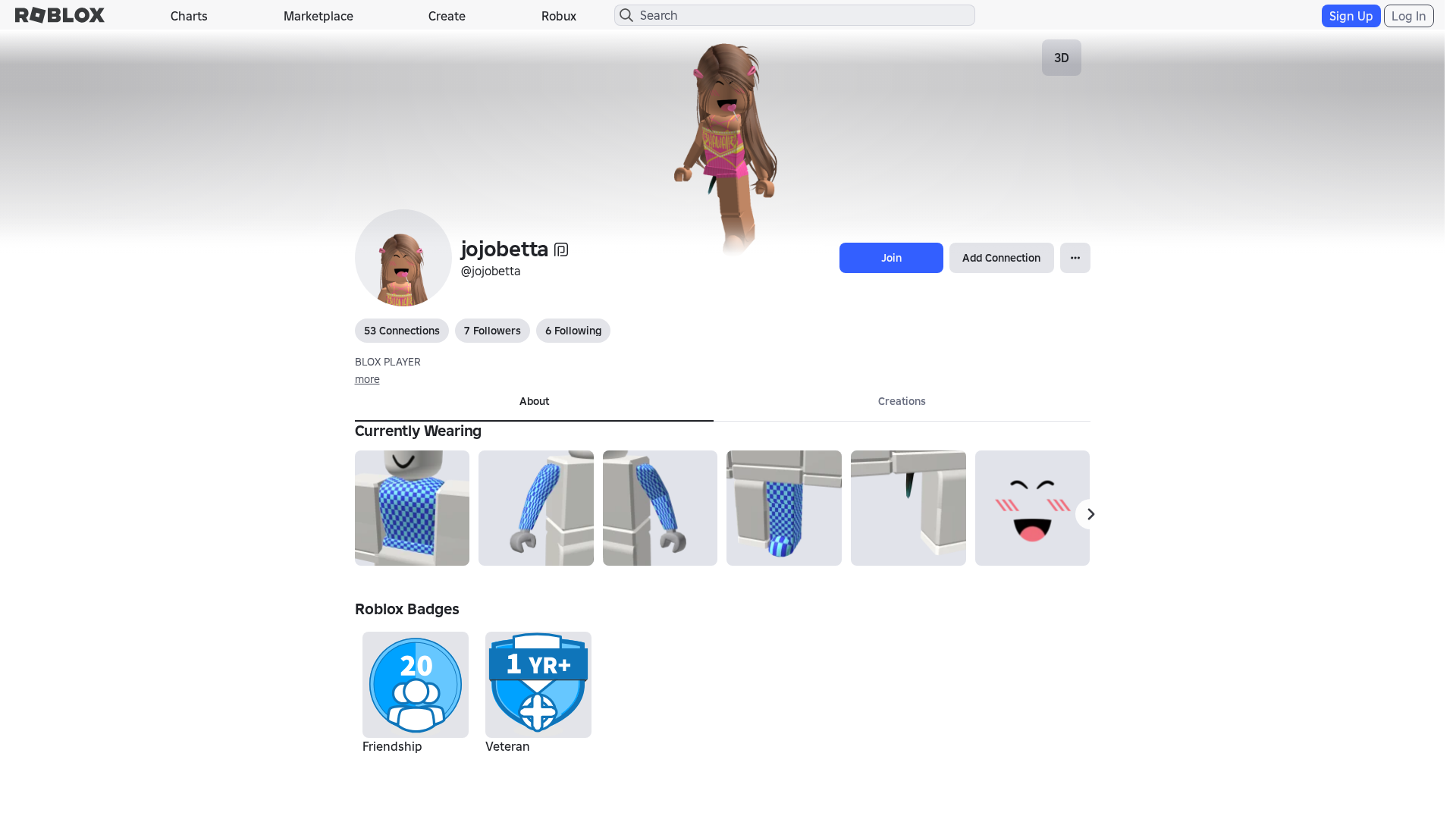
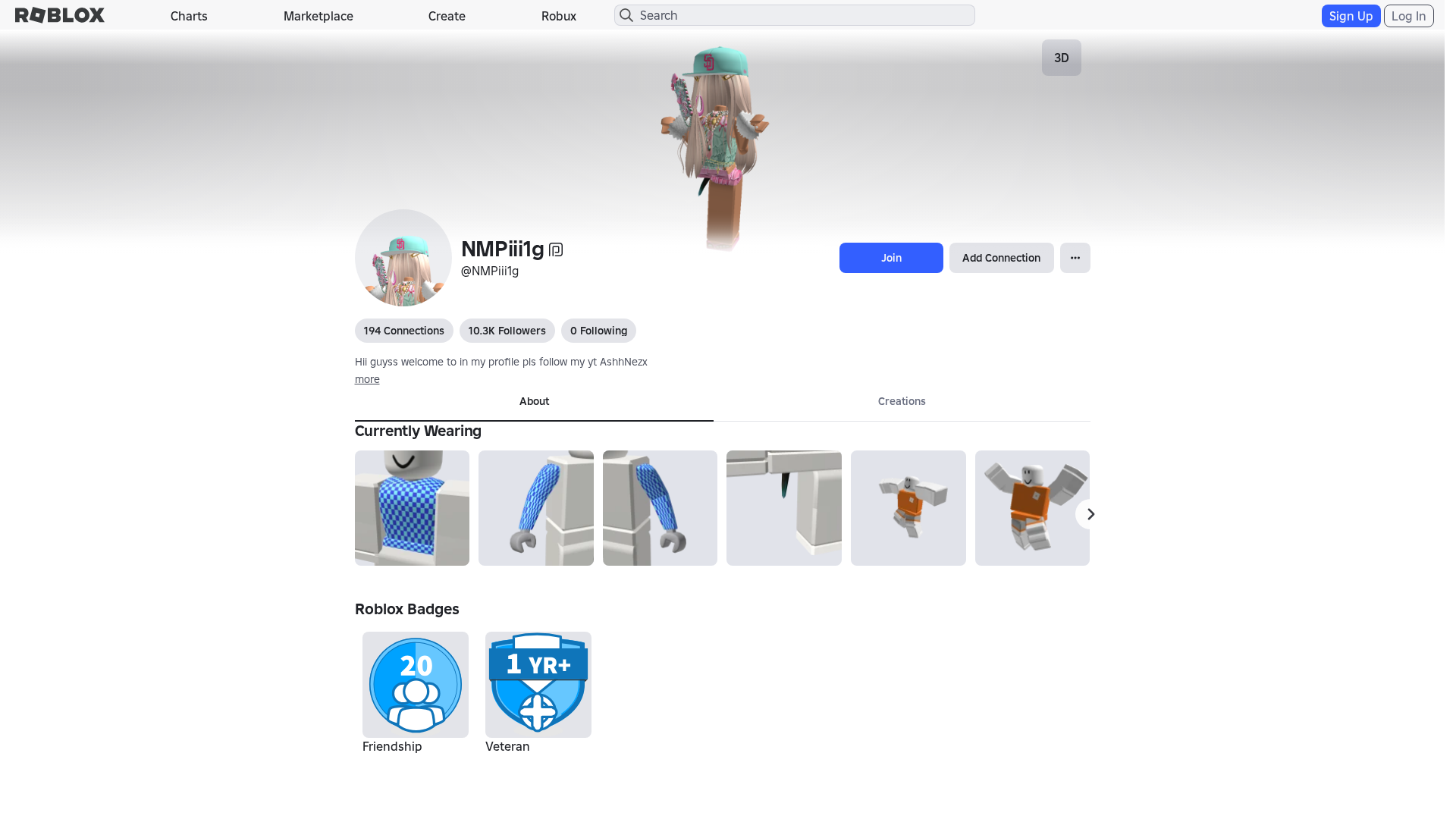
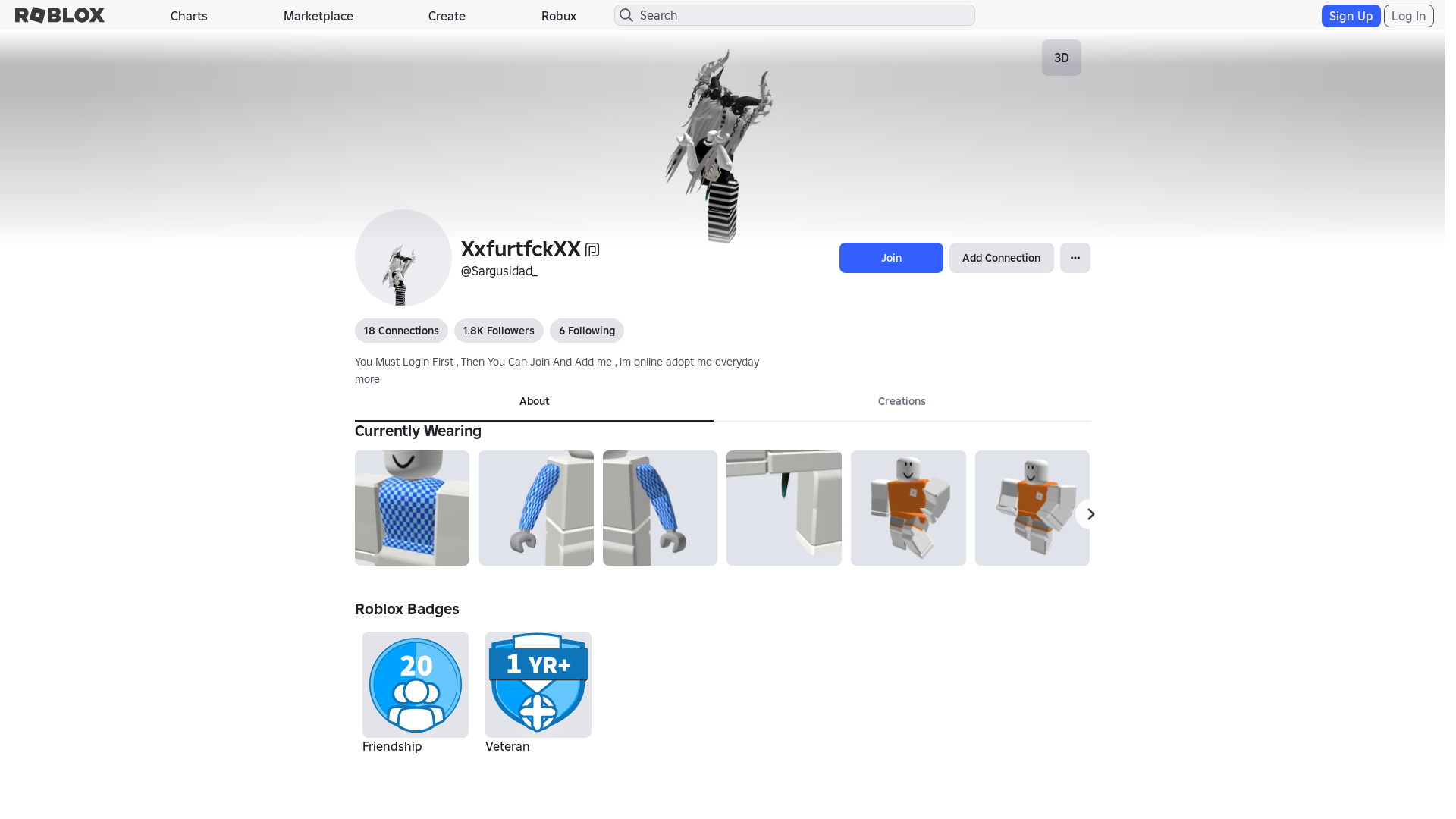
EnvironmentUrls.jsSimilar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.roblox.com.ml
Found 10 other scans for this domain
-
https://www.roblox.com.ml/games/123573053194279/EV...
https://www.roblox.com.ml/users/4359662752/profile
https://www.roblox.com.ml/games/102438880728881/Te...
https://www.roblox.com.ml/games/920587237/Adopt-Me...
https://www.roblox.com.ml/games/83789872591767/Swo...
https://www.roblox.com.ml/communities/7111087128/R...
http://www.roblox.com.ml/communities/8359925132/FA...
https://www.roblox.com.ml/users/8640321039/profile
https://www.roblox.com.ml/users/5222656123/profile
https://www.roblox.com.ml/users/23215749/profile