
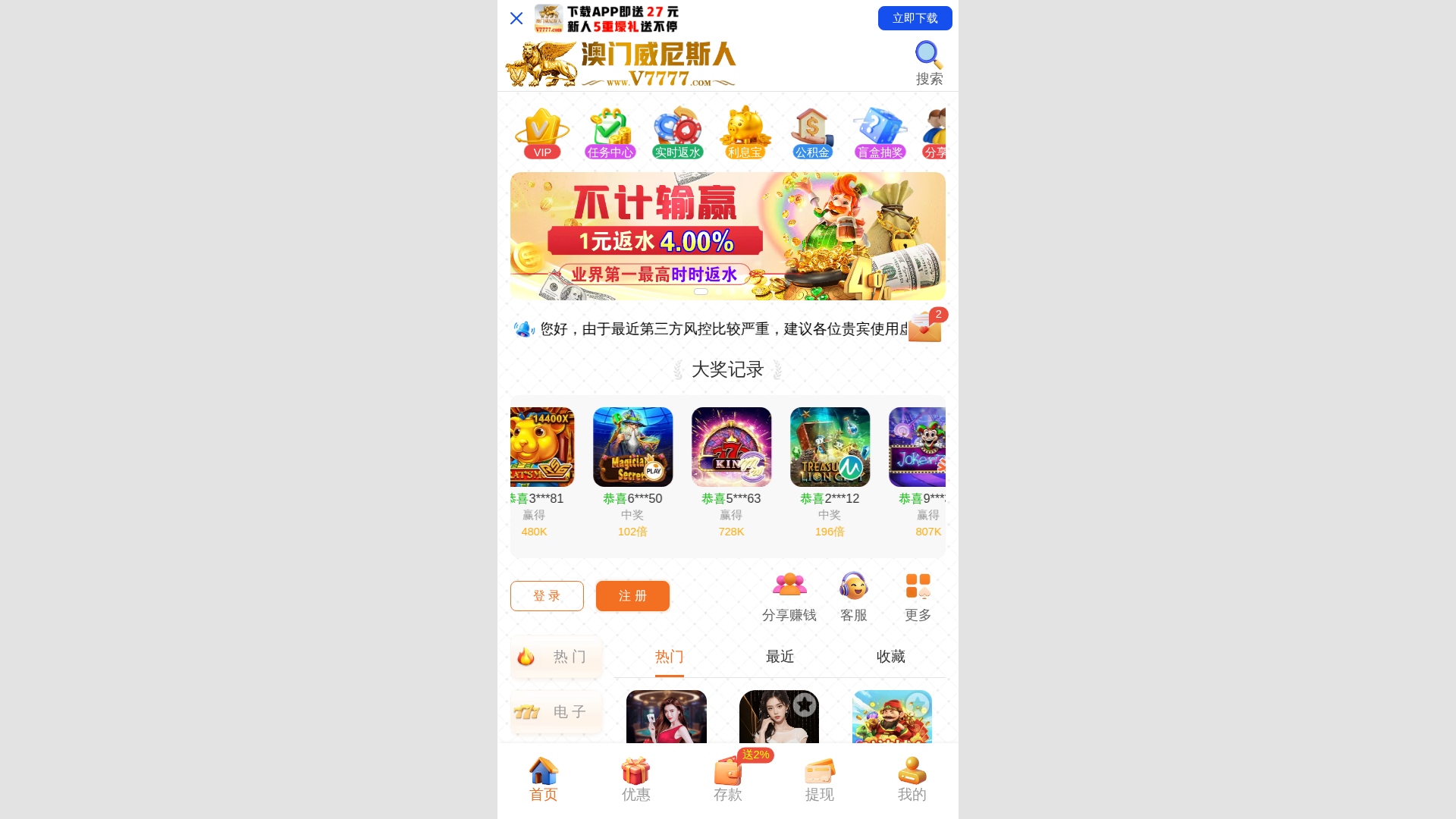
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
http://3222vv.cc
Detected Brand
Unknown
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
d55f056c-77e…
Analyzed
2026-04-04 11:12
Final URL (after redirects)
https://3222vv.cc/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T136C3C530A1A0743F010304EAB63B773812ACA3AFF70155D466BC1374EBEADF5A972199 |
|
CONTENT
ssdeep
|
1536:V7ztplRl9D7q/VRgRXxeM1xeqxeBIaLZg4e:V7zF9FXPLn |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e331999931cc9967 |
|
VISUAL
aHash
|
ebe7e3f7c3ffe7e7 |
|
VISUAL
dHash
|
524c4d6c4c70686c |
|
VISUAL
wHash
|
0b23233f033f3727 |
|
VISUAL
colorHash
|
07400010000 |
|
VISUAL
cropResistant
|
524c4d6c4c70686c |
Code Analysis
Risk Score
85/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://3222vv.cc/siteadmin/upload/icon_rwzx1.avif
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_cp_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/upload/icon_lxb1.avif
- https://3222vv.cc/siteadmin/upload/icon_ssfs1.avif
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_dianjing_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/upload/icon_vip1.avif
- https://3222vv.cc/siteadmin/upload/img/1956973204993884162.avif
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_sw_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_by_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_zr_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_qkl_1.avif?manualVersion=1&version=v7.1.184
- login
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_ty_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-11/common/_sprite/icon_dt_1gd.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_qp_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/upload/img/1956972989234855938.avif
- https://3222vv.cc/siteadmin/upload/icon_tgzq1.avif
- https://3222vv.cc/siteadmin/upload/icon_mh1.avif
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_rm_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/upload/icon_gjj1.avif
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_douji_1.avif?manualVersion=1&version=v7.1.184
- https://3222vv.cc/siteadmin/skin/lobby_asset/1-0-common/common/_sprite/icon_dtfl_dz_1.avif?manualVersion=1&version=v7.1.184
📡 API Calls Detected
- slashOnceReceive
- svipLottery
- downloadShortcutGuide
- devtools
- iframe
- moreInterception
- findUs
- iframeAccessRestrictedPopup
- slashOnceReceiveFirst
- switchCurrency
- recharge
- blindBox
- downloadMainDialog
- setRealNameDialog
- ageCompliance
- HEAD
- temporaryAccountGuide
- newCutOnce
- slashOnce
- forbiddenSelf
- afterRechargeActivity
- plazzaSetUserInfo
- distributedReward
- setPhone
- switchLang
- returningBonus
- discountCode
- bindRegister
- cutOnce
- interest
- setBirthdayDialog
- iframeMaintainPopup
- securityDialogBinding
- eventSign
- appDownloadPwaTips
- setAvatarDialog
- securityForceBinding
- setChatAccountDialog
- loginVerify
- GET
- realNameForceModify
- withdrawAccounts
- manifest
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Code Obfuscation
JavaScript code obfuscated using 52 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
General public
Attack Method
obfuscated JavaScript
Exfiltration Channel
Unknown
Risk Assessment
CRITICAL - Automated credential harvesting with Unknown
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 52 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Generic Phishing
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 52 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
3222vv.cc
Registered
2026-03-31 12:05:47+00:00
Registrar
Dynadot Inc
Status
Recently registered (4 days old)
Hosting Information
Provider
Dynadot Inc
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.