Phishing Analysis
Detailed analysis of captured phishing page
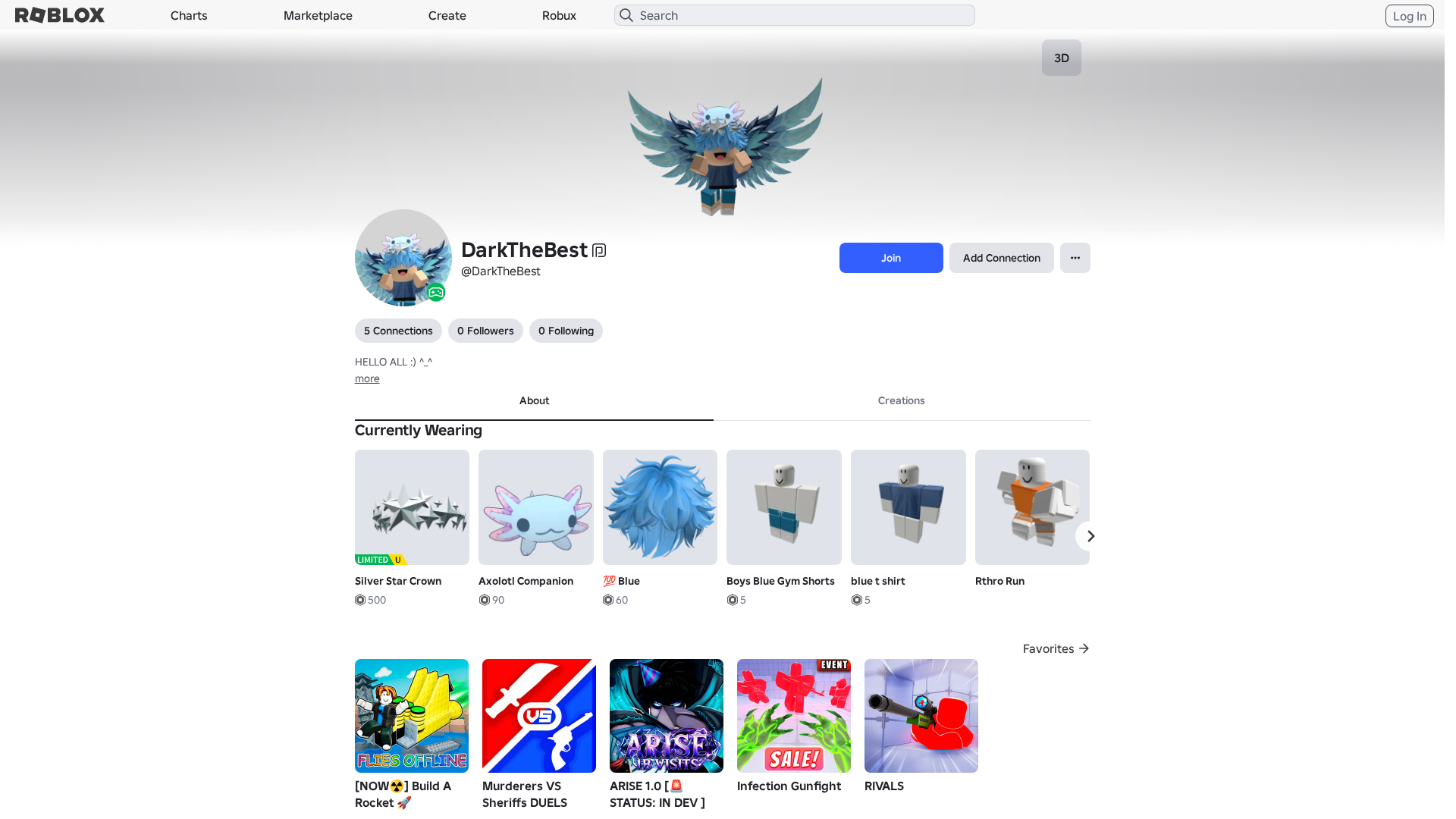
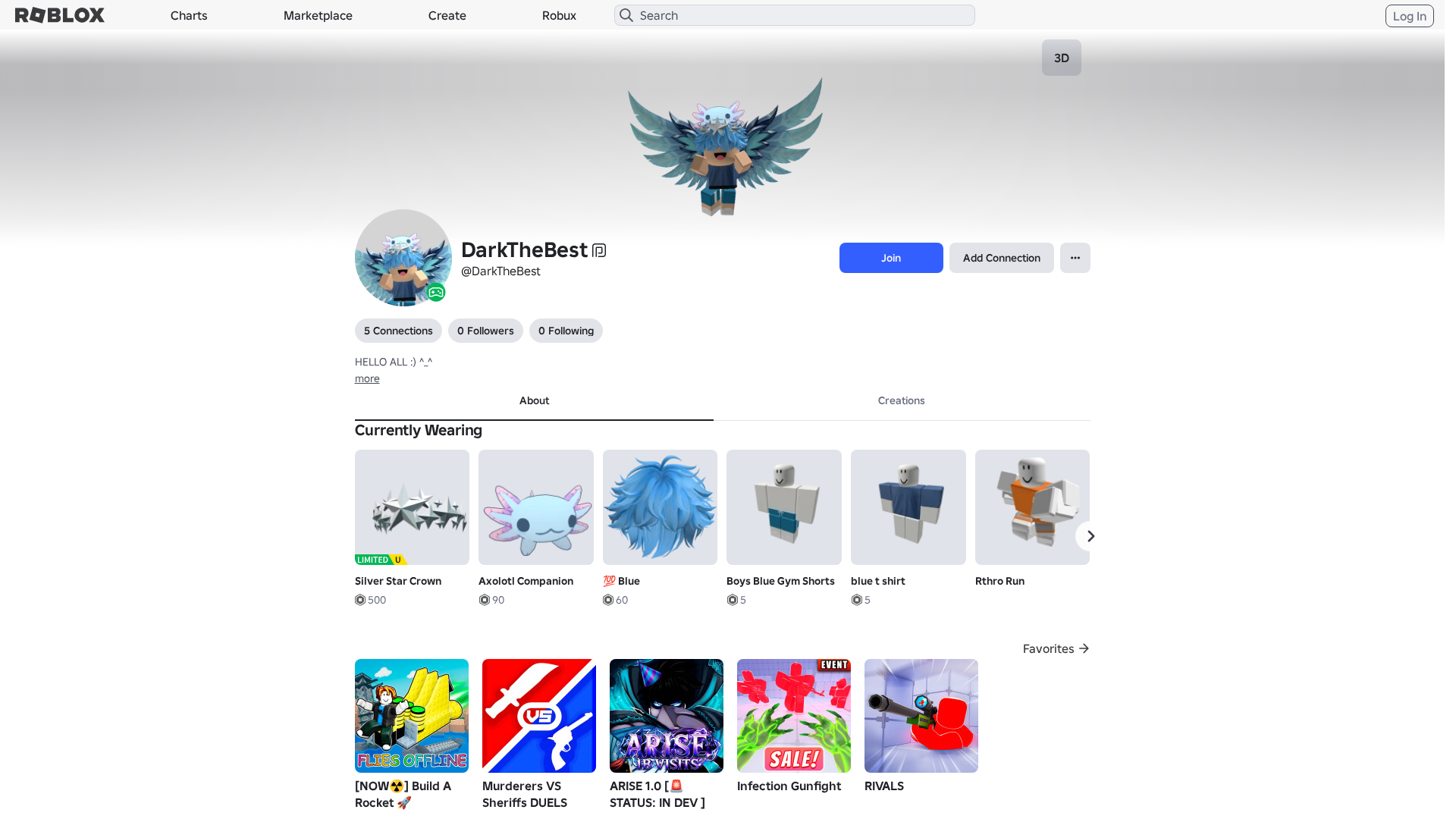
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1A763327292142837617B79DAF064671AD2D3D70FCA8346E1A2F8D39A0FD6CE1E85340E |
|
CONTENT
ssdeep
|
1536:IXnXWnurPU5eHPsgbPgHgg2xgJIgykguvg8zgX/ge/ghNgUbgWTgSzgwDg97gezg:EnXW+U6K8GkkRa3ePnPfC/MooncdyJb |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b04e3343d99ccc3d |
|
VISUAL
aHash
|
0000dfffc3efc7c3 |
|
VISUAL
dHash
|
e8cc36300e0e0e1e |
|
VISUAL
wHash
|
0000dfffc3c3c7c3 |
|
VISUAL
colorHash
|
07002008080 |
|
VISUAL
cropResistant
|
e8cc36300e0e0e1e,c973596b2b0f0f8c,cb2b032bb0a4a9e2 |
Code Analysis
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/15838376033/Mini-R6-Right-Arm
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/84743465463737/Silver-Star-Crown
- https://api.injuries.lu/catalog/80518181743320/Wings-of-Winters-Radiance
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/5319909330/Oldschool-Walk
- https://api.injuries.lu/catalog/18538164337/adidas-Sports-Fall
- https://api.injuries.lu/catalog/3360686498/Stadium
- https://api.injuries.lu/catalog/15838375985/Mini-R6-Right-Leg
- https://api.injuries.lu/catalog/15838372284/Mini-R6-Left-Arm
- https://api.injuries.lu/catalog/136368549551911/Super-Happy-Face
- https://api.injuries.lu/catalog/15838375824/Mini-R6-Torso
- https://api.injuries.lu/catalog/72284174896381/Axolotl-Companion
- https://api.injuries.lu/catalog/4915986211/Boys-Blue-Gym-Shorts
- /login?returnUrl=
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F370729095675%2Fprofile
- https://api.injuries.lu/catalog/15838372567/Mini-R6-Left-Leg
- https://api.injuries.lu/catalog/71362591627877/Blue
- https://api.injuries.lu/catalog/11085891878/blue-t-shirt
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F370729095675%2Fprofile
- https://api.injuries.lu/catalog/3576968026/Shrug
- https://api.injuries.lu/catalog/18538150608/adidas-Sports-Idle
- https://api.injuries.lu/catalog/2510238627/Rthro-Run
- https://api.injuries.lu/catalog/18538170170/adidas-Sports-Climb
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/18538158932/adidas-Sports-Swim
- https://api.injuries.lu/catalog/3576823880/Point2
- https://api.injuries.lu/catalog/18538153691/adidas-Sports-Jump
- https://api.injuries.lu/catalog/3576686446/Hello
📡 API Calls Detected
- https://help.roblox.com/hc/articles/30428367965460
- get
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- POST
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 207 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 207 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for s4w.in
Found 8 other scans for this domain
-
https://s4w.in/www-roblox-com-gl-users-21623285688...
https://s4w.in/www-roblox-com-users-13342902-profi...
https://s4w.in/dTCDF
https://s4w.in/roblox-com-user-293628-profile
https://s4w.in/toBsT
https://s4w.in/roblox-com-users-1029920-profile
https://s4w.in/www-roblox-com-gl-users-21623285688...
https://s4w.in/WzXCr