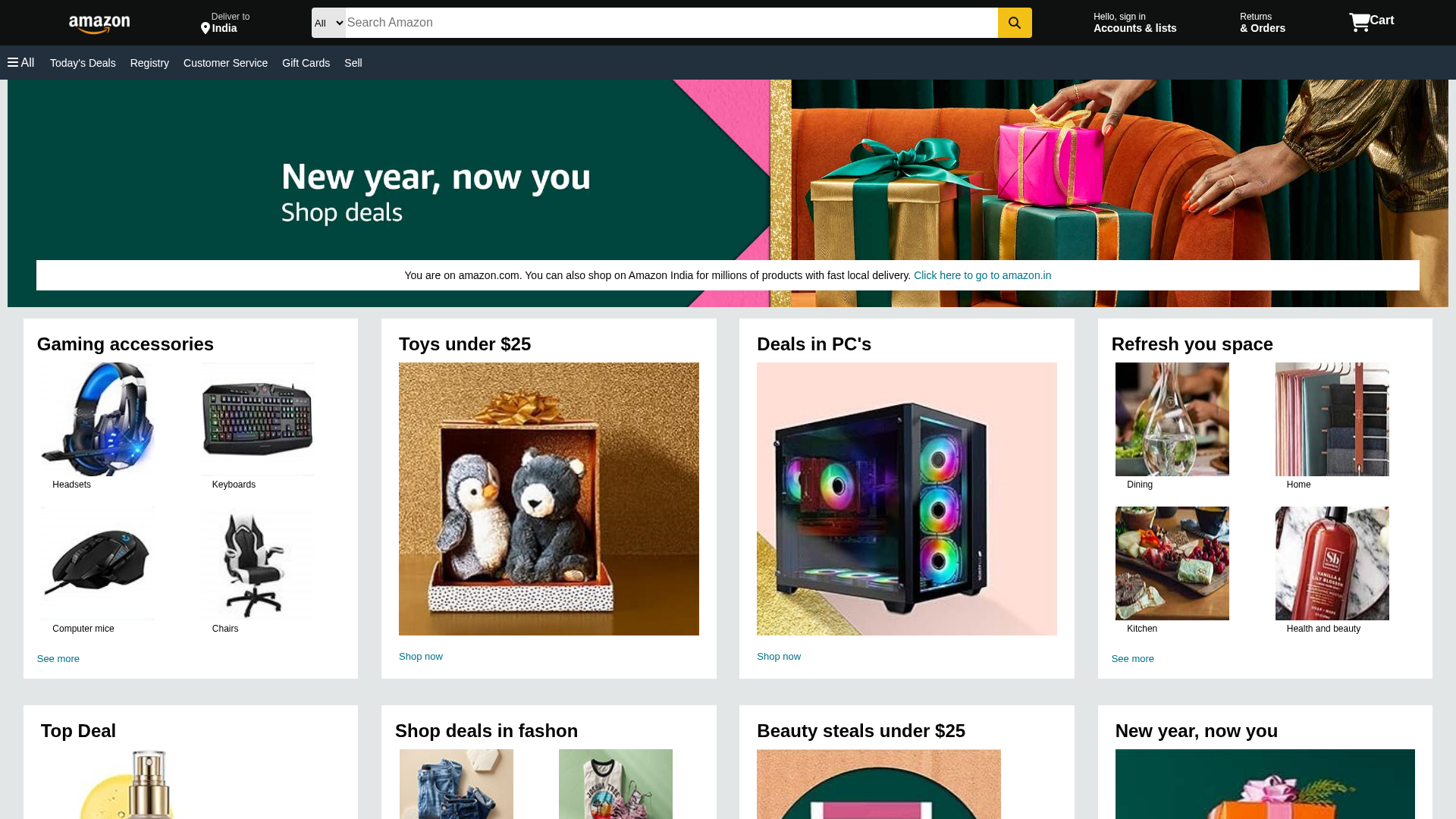
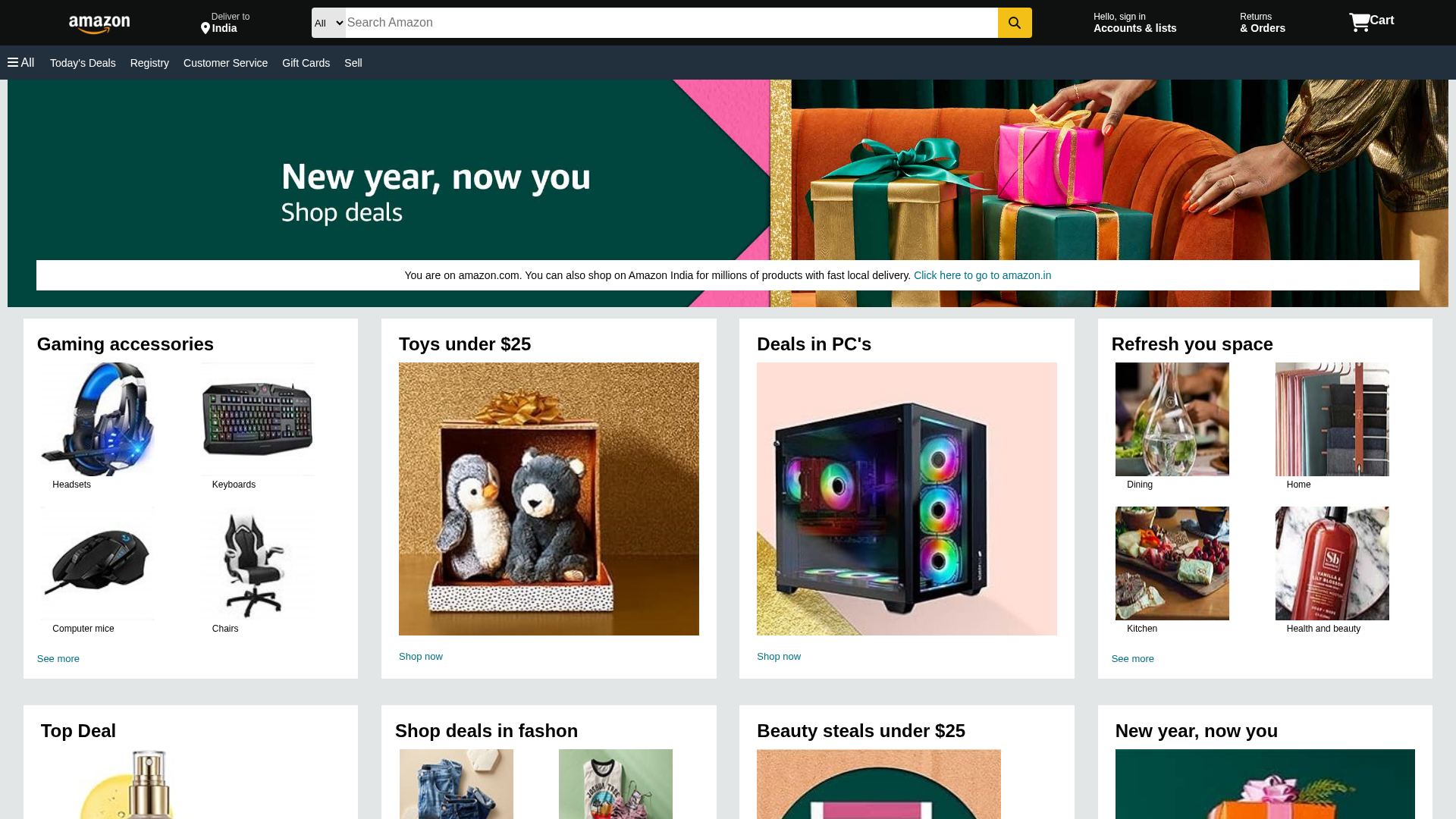
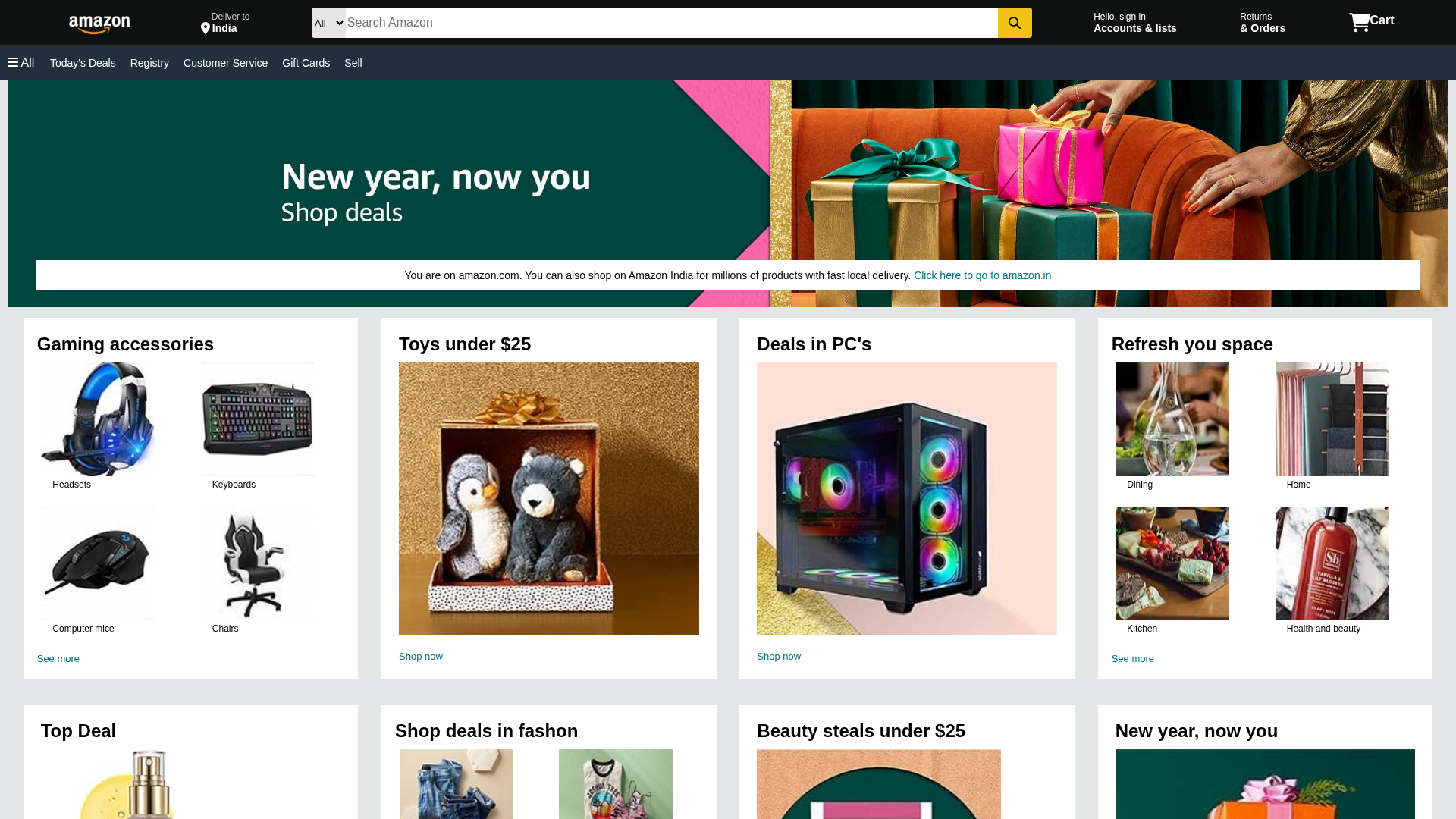
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
https://www.amazon-clone-umber-three.vercel.app/
Detected Brand
Amazon
Country
International
Confidence
95%
HTTP Status
200
Report ID
d68efdca-348…
Analyzed
2026-03-02 14:47
Final URL (after redirects)
https://amazon-clone-umber-three.vercel.app/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C202F630A081AB3B00C792E6DF355B9EB3E48299DB937B0853F58759CEC9E4BDD12190 |
|
CONTENT
ssdeep
|
96:TtxbJfWM2QtuJlYc5QoH3M6YFBeDaRhLOJ1+izAuaLdEynqqkj2u0:BTfWjlYcioX0FBeDcLOJ1+ikuaODqc2J |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f01f4e25ce8b6287 |
|
VISUAL
aHash
|
000000ffc3c7fffc |
|
VISUAL
dHash
|
f15cd89995959995 |
|
VISUAL
wHash
|
000000ffc7e5fffc |
|
VISUAL
colorHash
|
06201008600 |
|
VISUAL
cropResistant
|
8282c2d2d2c28282,54d8995595959895,e9d0151cc8d89892,d1d1515151515119,f8e4e3e2eae87476,981e3ba185c4b909,1b0d0d0d0d2d3535,070e4cce0416c6e7,c9f199ac3e8fc38b,0000023030317169 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Banking
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Amazon customers
• Method: Impersonation
• Exfil: Not applicable
• Indicators: Free hosting, brand logo
• Risk: HIGH
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting + Brand Logo
The site uses free hosting (vercel.app) and displays the Amazon logo and branding, a classic phishing indicator.
Domain Mismatch
The domain is not an official Amazon domain, but a clone on a free hosting platform.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Amazon users (International)
Attack Method
Brand impersonation
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Banking
🏢 Brand Impersonation Analysis
Impersonated Brand
Amazon
Official Website
https://www.amazon.com/
Fake Service
Amazon's ecommerce platform
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker aims to steal user credentials by creating a fake login page that mimics the look of the legitimate Amazon website.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.amazon-clone-umber-three.vercel.app
Registered
None
Registrar
None
Status
Inactive
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for www.amazon-clone-umber-three.vercel.app
Found 1 other scan for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.