
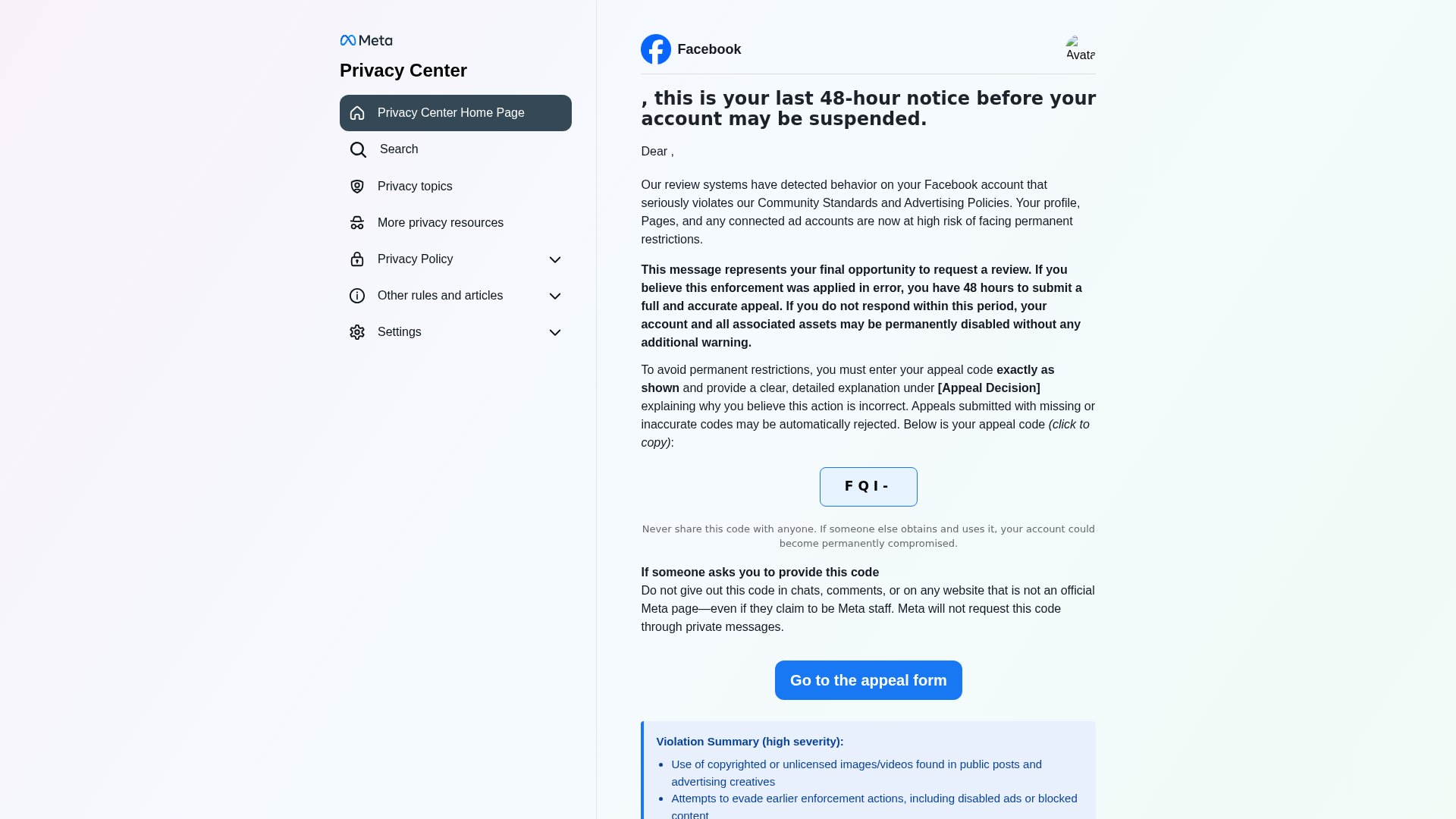
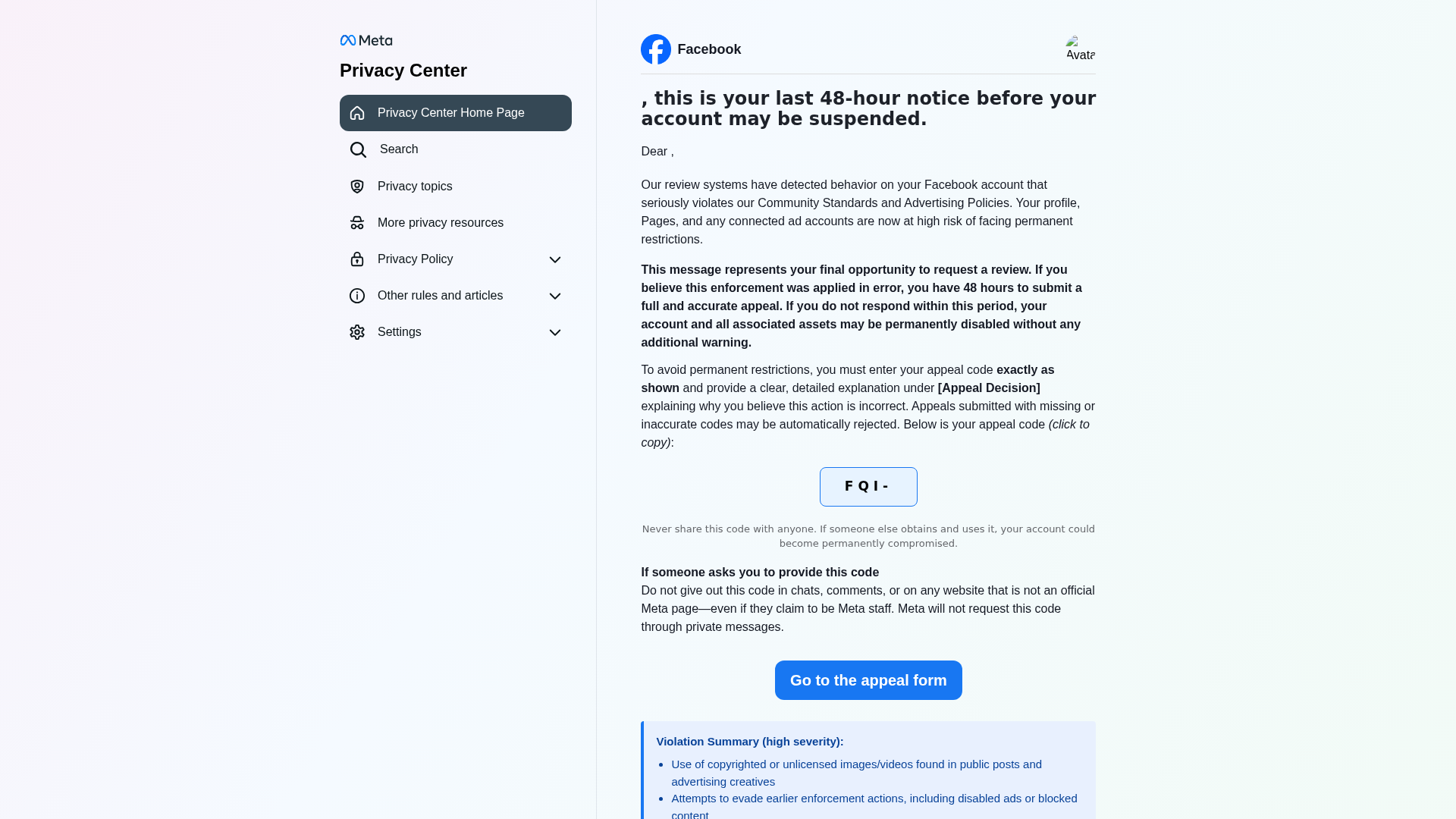
Phishing Analysis
Detailed analysis of captured phishing page
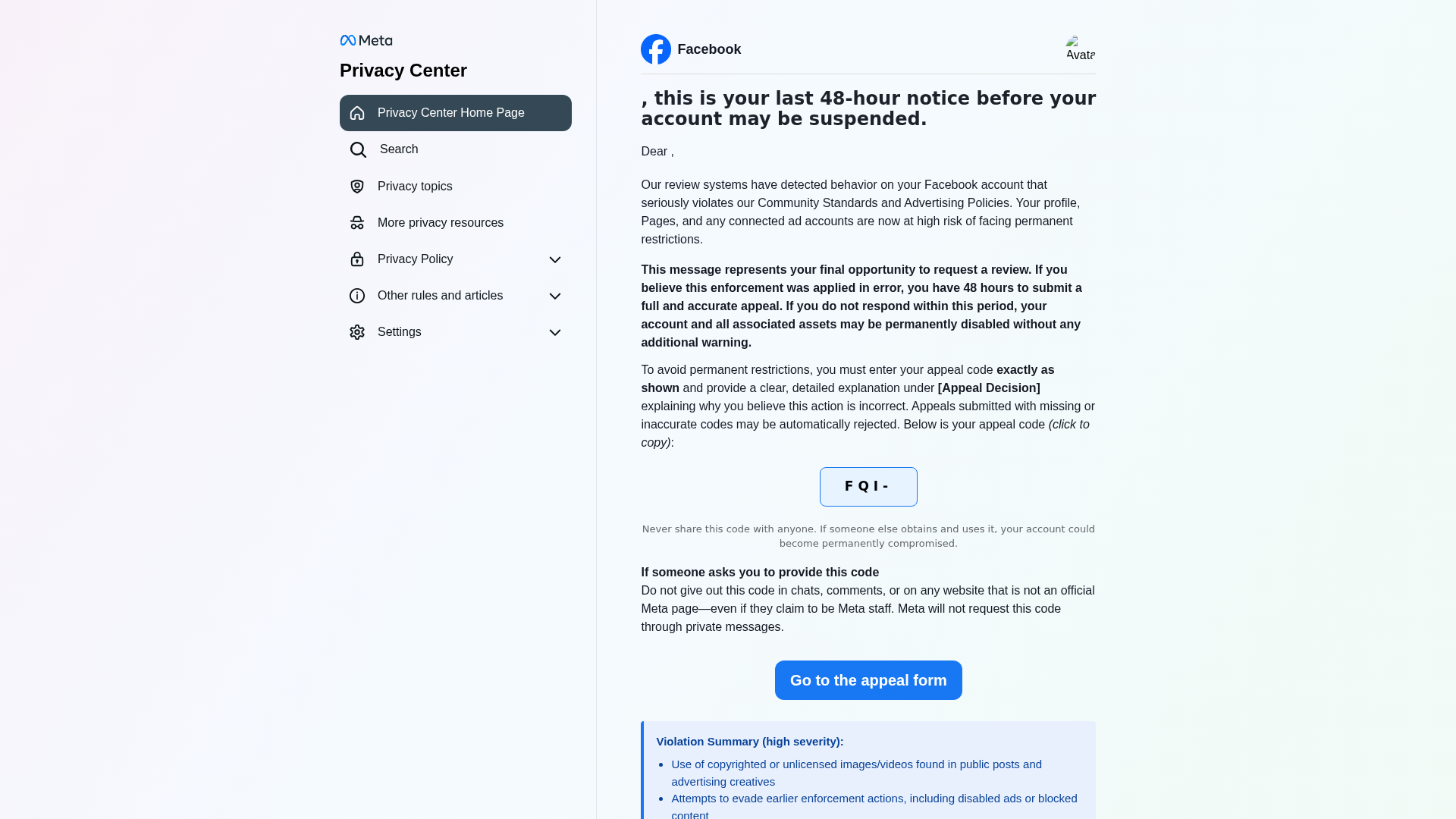
Visual Capture
Detection Info
http://lkk-msd-biz-ukx-jfk-sp2ct2.pages.dev/form_submit_appeal/
Detected Brand
Facebook/Meta
Country
International
Confidence
100%
HTTP Status
200
Report ID
d8172b7d-1bc…
Analyzed
2026-03-14 10:19
Final URL (after redirects)
https://lkk-msd-biz-ukx-jfk-sp2ct2.pages.dev/form_submit_appeal/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1AA72F9F10668237E828F83B8B5167799E2AEF57EF2774010D6AD07D91AC3C42ED67640 |
|
CONTENT
ssdeep
|
384:MC8r1KKD1DJ0VzpuqmALrwXJDnS7/Jwl2ffI3:MCwDdEq1M/Jwz3 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e4383898d367c3c7 |
|
VISUAL
aHash
|
8783e3e3f3e7f3e3 |
|
VISUAL
dHash
|
3e362606c6cee646 |
|
VISUAL
wHash
|
030303e3e3e3f3e3 |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
3e362606c6cee646 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Phishing
• Target: Facebook users
• Method: Impersonation via email and fake website
• Exfil: Potentially user account information, appeal code
• Indicators: Free hosting, urgency, brand impersonation
• Risk: HIGH
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
- base64_strings
📡 API Calls Detected
- https://get.geojs.io/v1/ip/geo.json
- POST
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting
The domain is hosted on a free hosting platform (pages.dev), a common tactic for phishing.
Brand Impersonation
The page attempts to impersonate Facebook using their logo and branding.
Urgency and Fear Tactics
The message creates a sense of urgency by threatening account suspension, driving the user to act quickly.
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Facebook/Meta users (International)
Attack Method
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 52 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Facebook
Official Website
https://www.facebook.com
Fake Service
Facebook Account Security and Appeal Process
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker aims to steal Facebook account credentials by tricking users into entering them on a fake login page, which is then sent directly to the attacker.
Secondary Method: Malware distribution
Redirecting the user to download a file containing malware, which is executed when the user interacts with the 'appeal form'.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
lkk-msd-biz-ukx-jfk-sp2ct2.pages.dev
Registered
Unknown
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Facebook
https://lkr-mvx-biz-vqx-jfr-sp2ct2.pages.dev/form_submit_app...
Apr 07, 2026
Facebook
https://lkg-mqd-biz-ukx-jfg-sp2ct2.pages.dev/form_submit_app...
Apr 07, 2026
Facebook
https://lkl-msx-biz-skx-jfl-sp2ct2.pages.dev/form_submit_app...
Apr 07, 2026
Facebook
http://lmp-nhx-biz-vqx-jgp-sp2ct2.pages.dev/form_submit_appe...
Mar 14, 2026
Facebook
http://lkt-mwx-biz-skx-jft-sp2ct2.pages.dev/form_submit_appe...
Mar 14, 2026

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.