
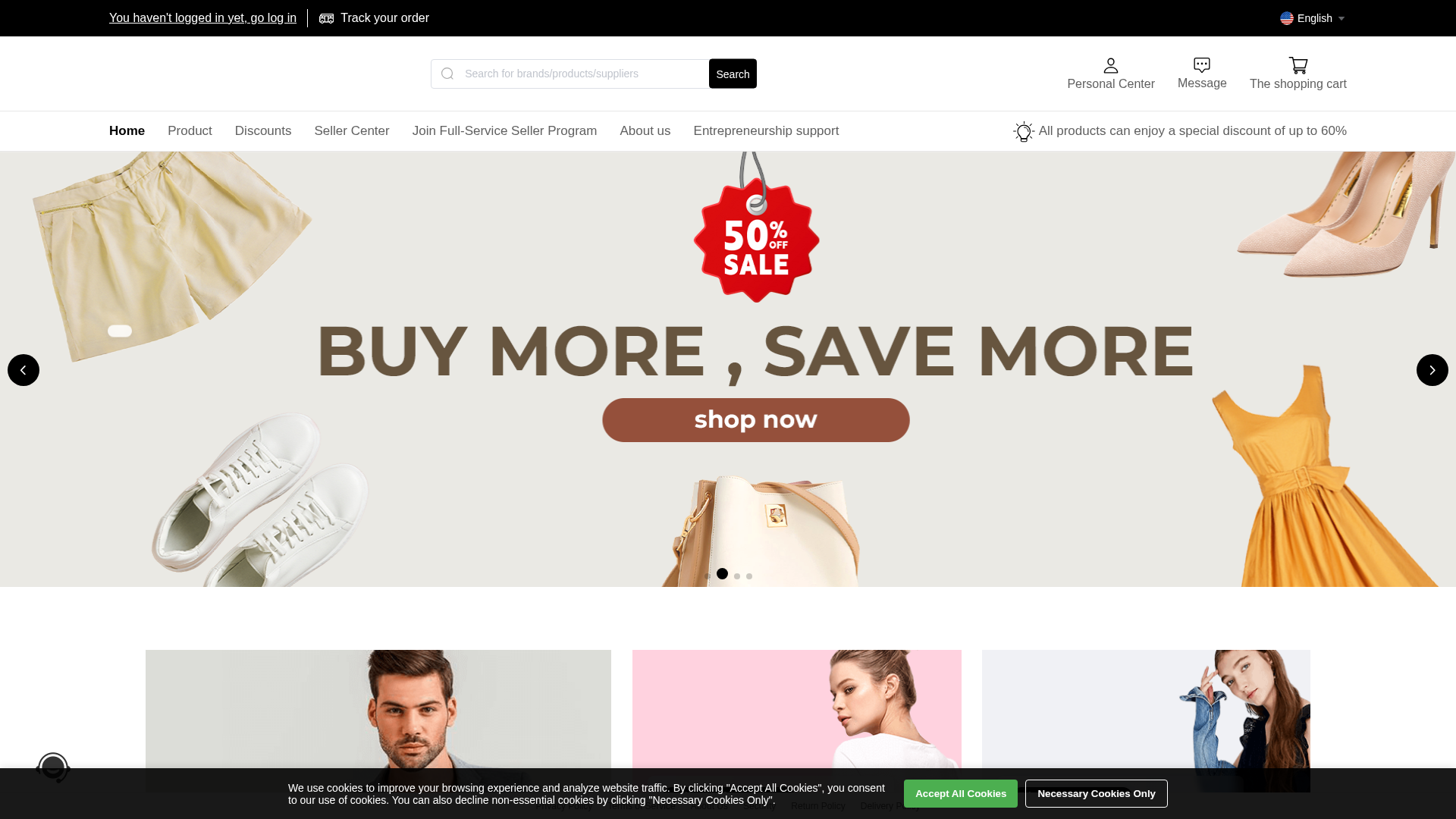
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T162834070C695613B06234ED9B5716F0BB2D3930ECE67890467FC478EABEBCD5EA01486 |
|
CONTENT
ssdeep
|
1536:2W4AwcAxa2ay1apJGDfLTlzHWOCFkmiQ2oOh14FDB92:2eh592 |
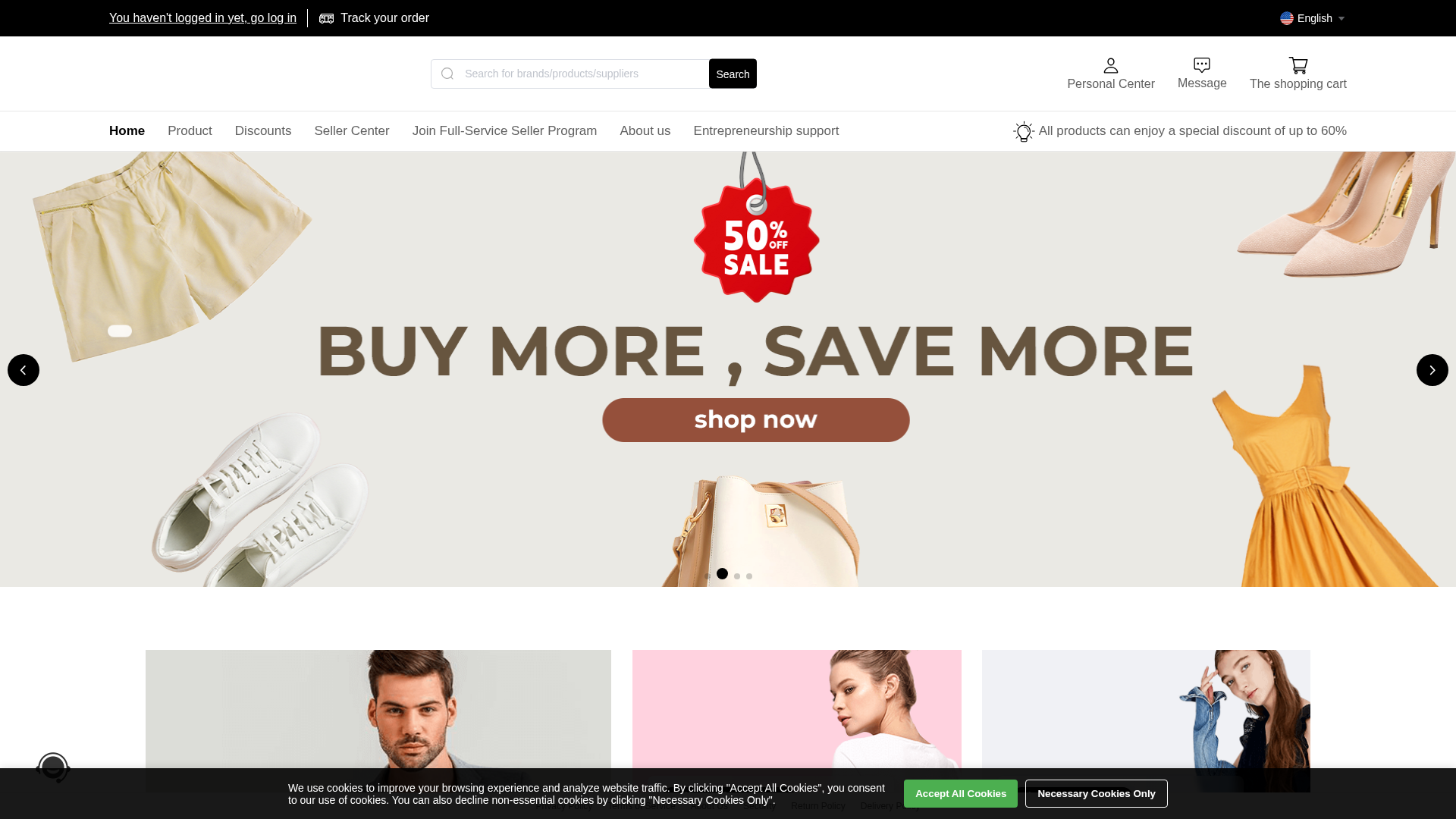
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f6a51add62a80376 |
|
VISUAL
aHash
|
00ff66c3e6feff00 |
|
VISUAL
dHash
|
896cec8f4c48352d |
|
VISUAL
wHash
|
00ff6641e6fed700 |
|
VISUAL
colorHash
|
06e00008000 |
|
VISUAL
cropResistant
|
096cec8f4c482535,0000009393820080,010c686969697434,3535253d3db9edec |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
📡 API Calls Detected
- /api/category!tree.action
- post
- /api/credit!pay.action
- /api/activity/lottery!getCurrentActivity.action
- /public/userOnlineChatController!unread.action
- /api/credit!beforereapply.action
- /api/localuser!registerNoVerifcode.action
- api/syspara!getSyspara.action
- /api/credit!histroy.action
- /api/category!sellerTree.action
- /api/jscode!execute.action
- /api/credit!apply.action
- /api/credit!beforepay.action
- /api/credit!config.action
- /api/localuser!registerWithVerifcode.action
- /api/credit!check.action
- GET
- /api/localuser!get.action
- /api/credit!bill.action
- api/newOnlinechat!unread.action
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 23 obfuscation techniques
🏢 Brand Impersonation Analysis
Fraudulent Claims
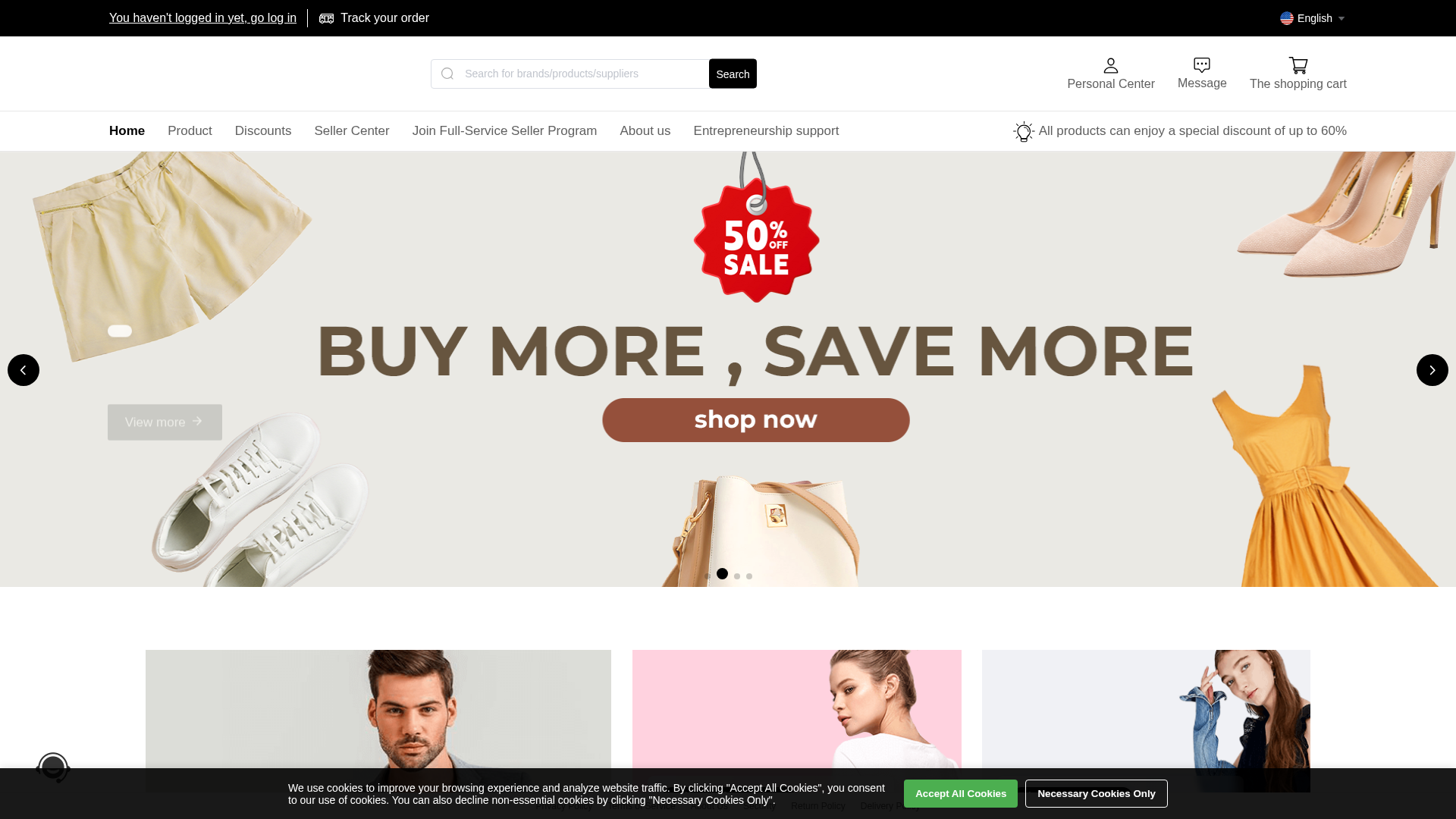
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 23 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for tiktok.1d2by.com
Found 1 other scan for this domain
