
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
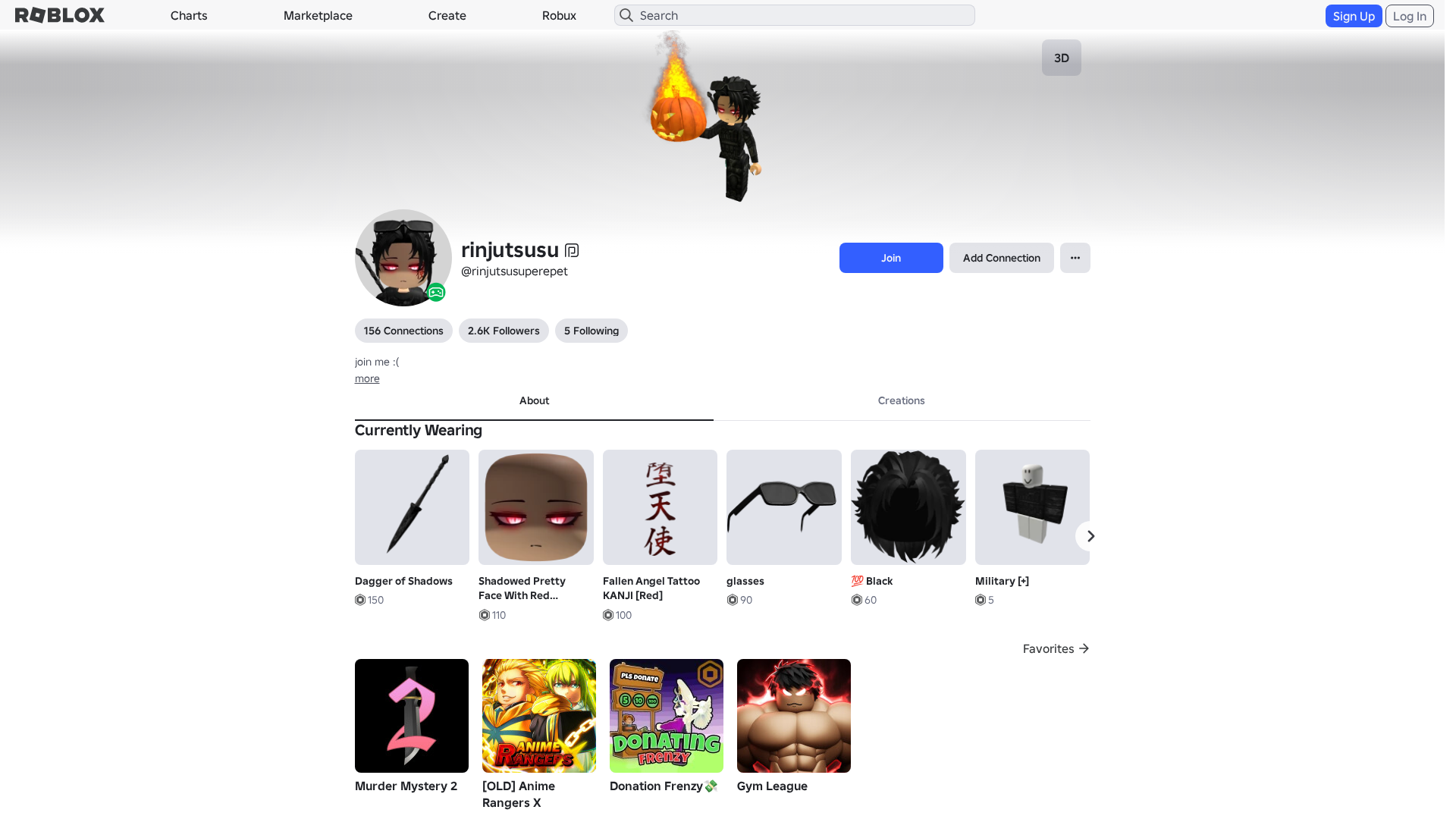
Detection Info
https://rblx.foo/s/www-roblox-coms
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
ddf6bb94-068…
Analyzed
2026-03-27 23:33
Final URL (after redirects)
https://www.robiox.com.py/users/373784747861/profile
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18563447292142837617B79DAF064671AD2D3D74FCA4346E1A2F8939A0FD6CE1EC5380E |
|
CONTENT
ssdeep
|
1536:i3TXWn4raRCeNHsgr5gTFg3cg3ig69giUgOcgxHdgjDg4XgdrgNDgXxgCHgUHg51:OTXWFR1Q+1GfsLs5QsYxXCZuvgQF0 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc471265d19acd3c |
|
VISUAL
aHash
|
0000dfffc3c3c7c7 |
|
VISUAL
dHash
|
c8e8363096162d3d |
|
VISUAL
wHash
|
0000d7ffc3c3c7c7 |
|
VISUAL
colorHash
|
07600010000 |
|
VISUAL
cropResistant
|
c8e8363096162d3d,1f2b6d4d5d57230f,7f87013331d46108,5531697931617135 |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/18199811960/Fallen-Angel-Tattoo-KANJI-Red
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/15093053680/Headless-Head
- https://api.injuries.lu/catalog/124765145869332/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/93993406355955/adidas-Community-Animation-Pack
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/126354114956642/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/796453758/Military
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/114917584866792/glasses
- https://api.injuries.lu/catalog/16468073901/Black
- https://api.injuries.lu/catalog/130373407996664/Popular-Jump
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://api.injuries.lu/catalog/106537993816942/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/123695349157584/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F373784747861%2Fprofile
- https://api.injuries.lu/catalog/106810508343012/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/18582264925/Dagger-of-Shadows
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F373784747861%2Fprofile
- /login?returnUrl=
- https://api.injuries.lu/catalog/131592085/Headless-Horsemans-New-Head
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/107913107504439/Shadowed-Pretty-Face-With-Red-Glowing-Eyes-Light
- https://api.injuries.lu/catalog/111083785120111/Black
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
📡 API Calls Detected
- POST
- get
- GET
- https://kyxn.dev/api/shorten
- https://help.roblox.com/hc/articles/30428367965460
- https://apis.
- /api/pageview
- /api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- https://ro.blox.com/Ebh5?
- https://kyxn.dev${e.endpoint}
📤 Form Action Targets
- /search
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Roblox users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
HTTP POST to backend
Risk Assessment
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
rblx.foo
Registered
Unknown
Registrar
None
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for rblx.foo
Found 10 other scans for this domain
-
https://rblx.foo/s/cyFAoF
https://rblx.foo/s/J3h4AL
https://rblx.foo/s/myroblox
https://rblx.foo/s/1p8tkN
https://rblx.foo/s/roblox-com-users-3324118
https://rblx.foo/s/users243671918813profile
https://rblx.foo/s/roblox-com-users-3110201
https://rblx.foo/s/robIox-profiIe
https://rblx.foo/s/LX0Gyi
https://rblx.foo/s/rxgKLr

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.