Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
No screenshot available
Detection Info
http://gauravsingh1281.github.io/instagram-Clone
Detected Brand
Instagram
Country
International
Confidence
100%
HTTP Status
200
Report ID
dece0d03-e30…
Analyzed
2025-12-22 05:45
Final URL (after redirects)
https://gauravsingh1281.github.io/instagram-Clone/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T15241BD263089246B0B92679D6F21A36CA39391A38F590F0161E04B5FAFD3F17CE1109F |
|
CONTENT
ssdeep
|
48:nv1P84kwaFKuqiPNpUA4vxKW7rbOA4zitnbrA:n9iw+P |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b131cecc9e9364cc |
|
VISUAL
aHash
|
ffc7c7c7c3e3ffff |
|
VISUAL
dHash
|
189c9e989606280e |
|
VISUAL
wHash
|
0f030303c3c3cfc3 |
|
VISUAL
colorHash
|
07602008000 |
|
VISUAL
cropResistant
|
189c9e989606280e,6a9292183ce4a822 |
Code Analysis
Risk Score
70/100
Threat Level
ALTO
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: Instagram users
• Method: Fake login page to steal username/phone and password
• Exfil: Likely to a custom API or a Telegram bot
• Indicators: Free hosting, domain mismatch
• Risk: HIGH - Immediate credential theft
🔐 Credential Harvesting Forms
📡 API Calls Detected
- GET
📤 Form Action Targets
- /
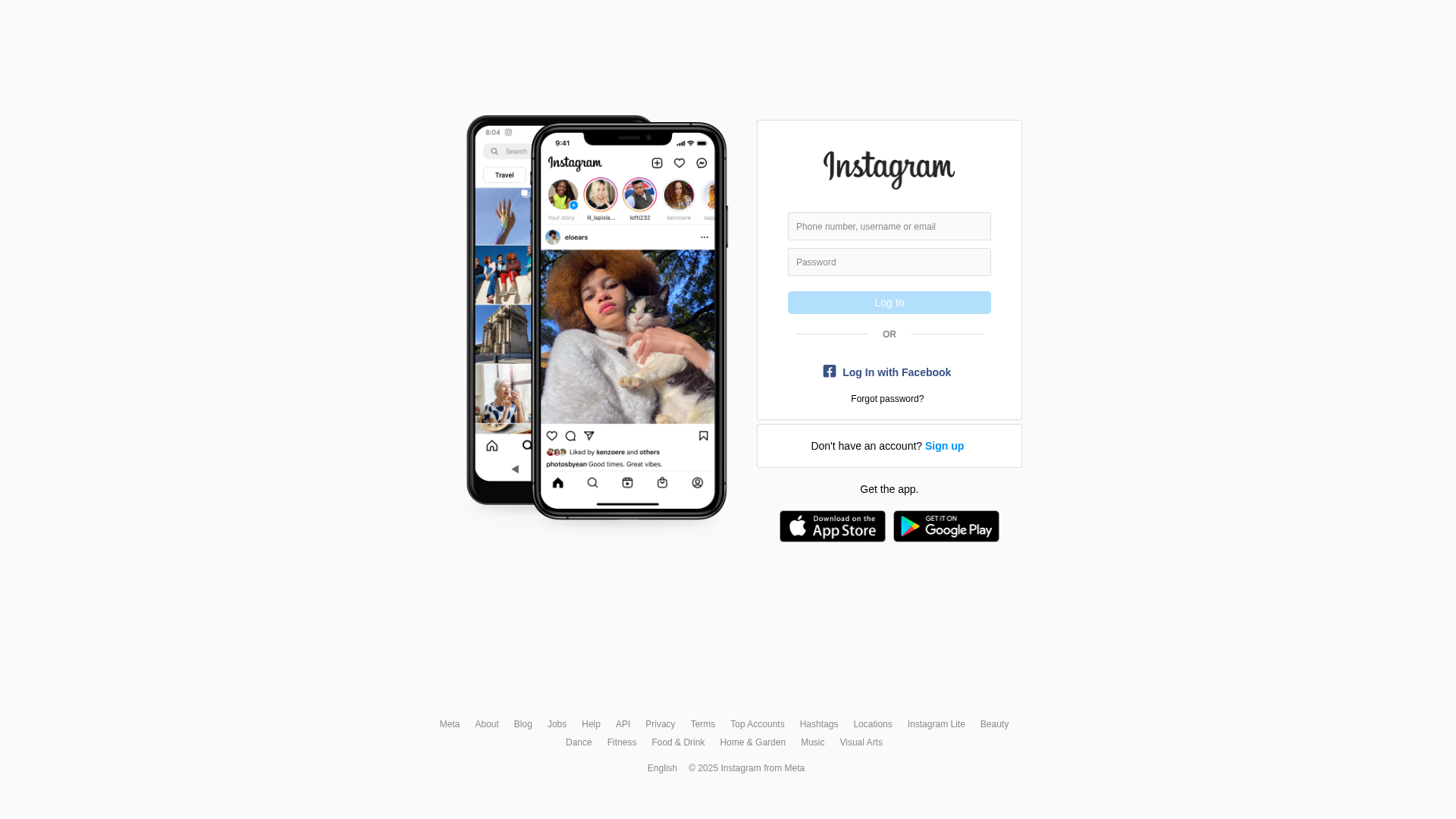
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for gauravsingh1281.github.io
Found 1 other scan for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.