
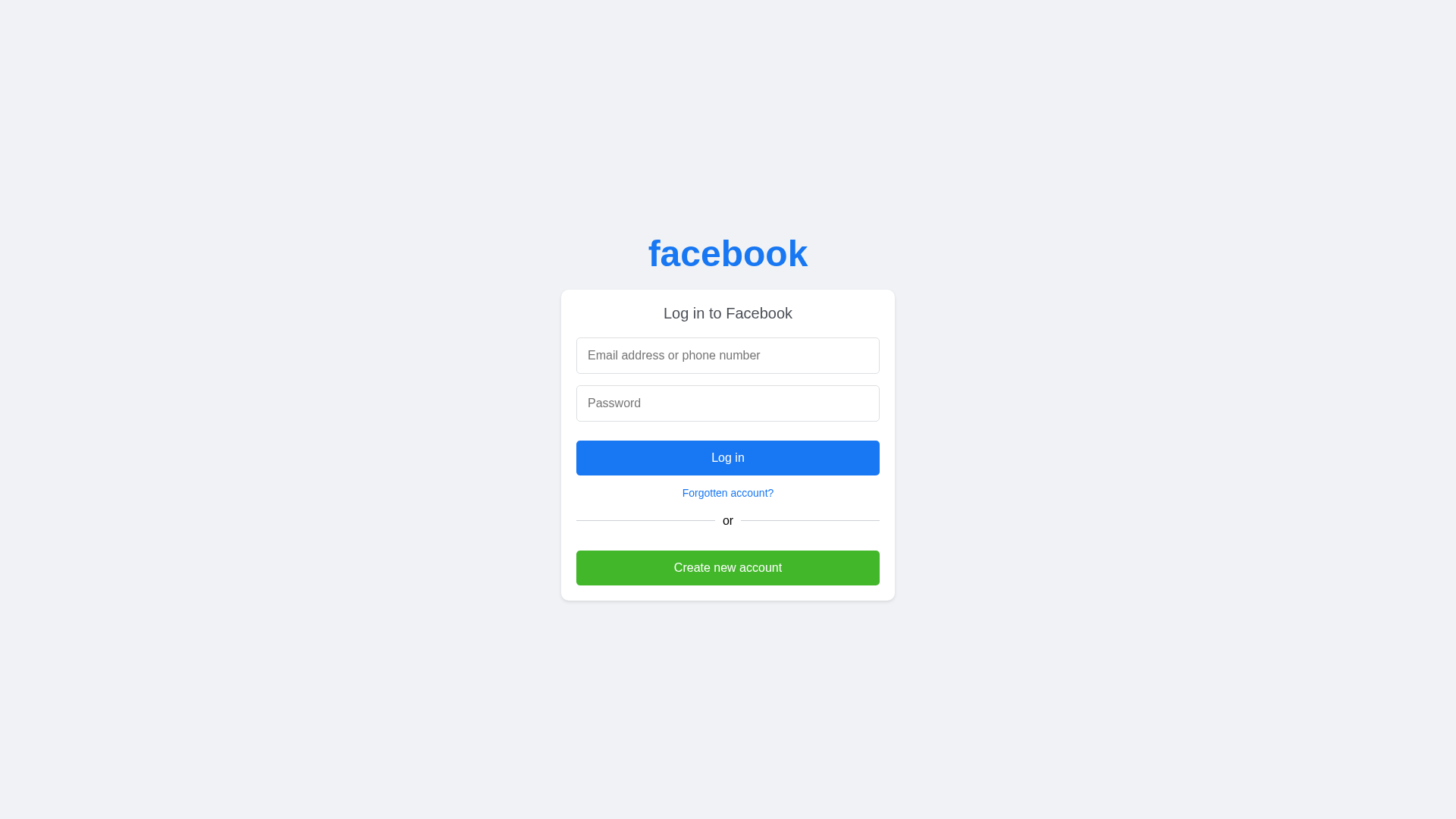
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
http://abdo02564.github.io/facebook
Detected Brand
Facebook
Country
International
Confidence
100%
HTTP Status
200
Report ID
df06dc10-182…
Analyzed
2025-12-20 16:47
Final URL (after redirects)
https://abdo02564.github.io/facebook/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14F1112A8000488BB179286F41693F72BB582CD42CF8735044BE093FF6AD3E50CE591D5 |
|
CONTENT
ssdeep
|
12:nYpH0fE9Tp+amGy7FUOYkDBzPaskzzuj6uoJD9kDVgOtWycWlVX9MtdWJ+pES:nkl9TQVGChPaJ/N9uuOHNlVX9MTaS |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b399cc6699992666 |
|
VISUAL
aHash
|
ffffe7ffe7e7e7ff |
|
VISUAL
dHash
|
000008324d4d0c10 |
|
VISUAL
wHash
|
f0f0e0f827270f0f |
|
VISUAL
colorHash
|
07000003180 |
|
VISUAL
cropResistant
|
000008324d4d0c10 |
Code Analysis
Risk Score
75/100
Threat Level
ALTO
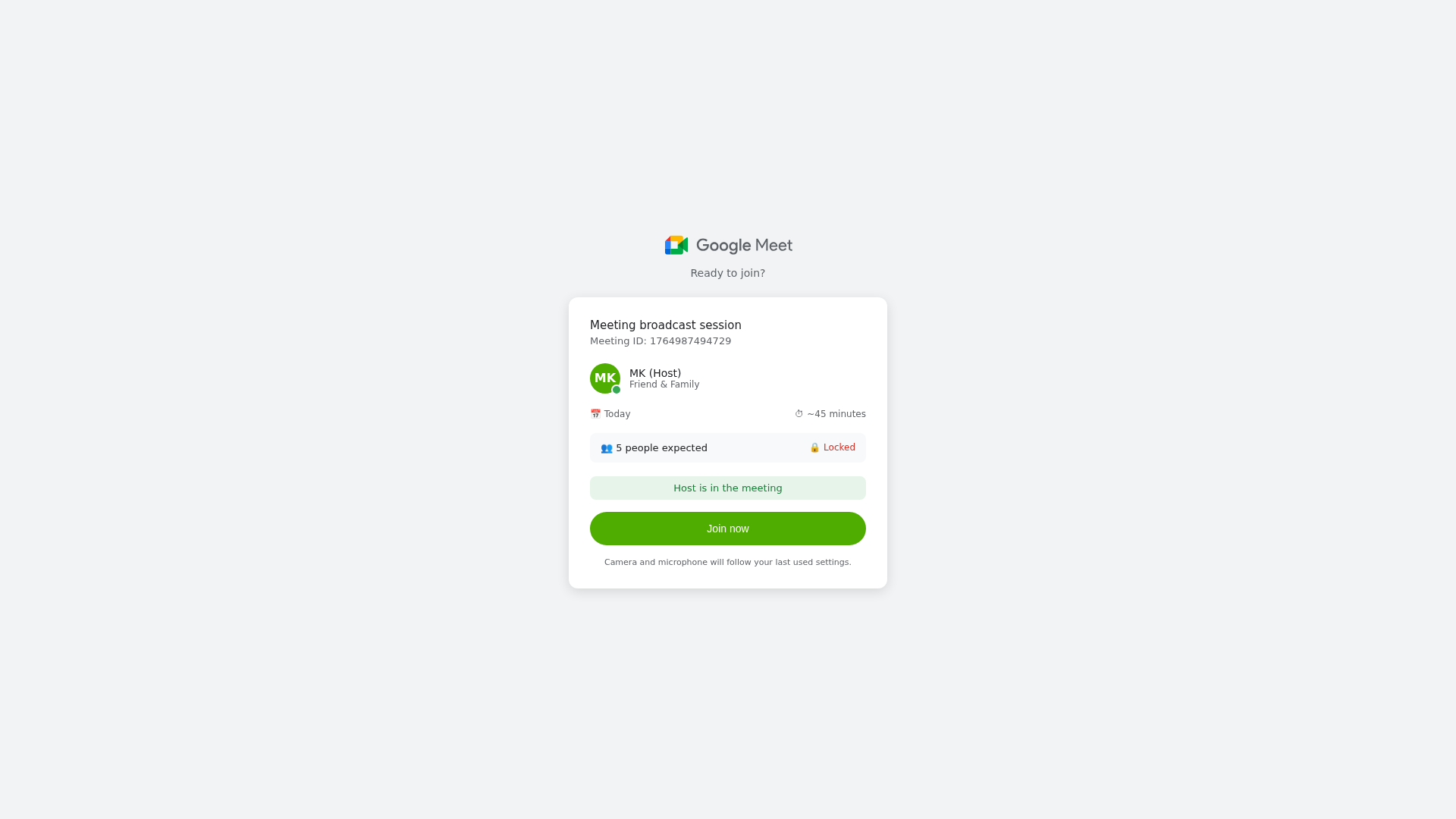
🎣 Credential Harvester
Telegram Exfiltration
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing
• Target: Facebook users
• Method: Fake Facebook login page on a free hosting platform designed to steal login credentials.
• Exfil: Unknown, likely sent to a server controlled by the attacker.
• Indicators: Free hosting (GitHub Pages), Facebook logo on unofficial domain, login form.
• Risk: HIGH - Immediate credential theft
🔑 Telegram Bot Tokens (1)
- 7388658900:AAGS...K7efaPOU
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/507b5d1d1e84.png
Apr 07, 2026
No screenshot
Unknown
http://merkfinances.com
Jan 12, 2026
No screenshot
Unknown
https://merkfinances.com/
Jan 12, 2026
No screenshot
Unknown
https://interpreteri.firebaseapp.com/
Jan 09, 2026
No screenshot
Unknown
https://interpreteri.web.app/
Jan 09, 2026
Scan History for abdo02564.github.io
Found 3 other scans for this domain

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.