
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
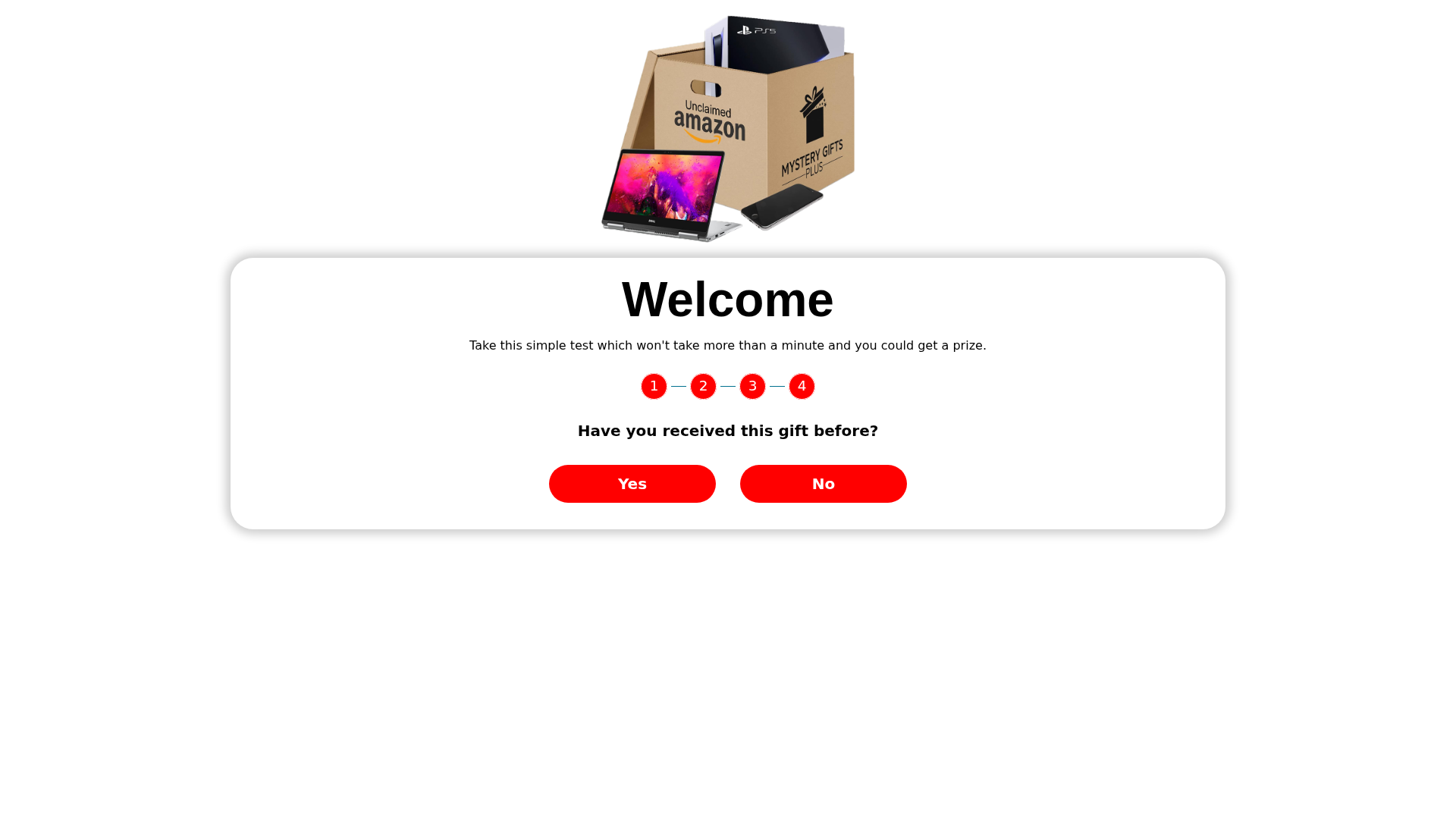
Detection Info
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3/
Detected Brand
Amazon
Country
International
Confidence
95%
HTTP Status
200
Report ID
df104f38-00c…
Analyzed
2025-12-31 01:54
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T150D2F7DAB691713603E36071813F230F3377669B78068458716ED7C11F6AD8EA613BAD |
|
CONTENT
ssdeep
|
384:R5cs8amBodiSinmAAmKriNpnjyMkg8XMtExRN1w29JIOzahXtO2nJ6P:R+iM7nmBmDijgSWuanfJ6P |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e666c666cccc9833 |
|
VISUAL
aHash
|
e7e7e7e7e7e7ffff |
|
VISUAL
dHash
|
2d4d0f0d4d0d0008 |
|
VISUAL
wHash
|
27278080a581ffff |
|
VISUAL
colorHash
|
07400018000 |
|
VISUAL
cropResistant
|
2d4d0f0d4d0d0008 |
Code Analysis
Threat Level
MEDIO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Threat: Phishing campaign impersonating Amazon.
• Target: Amazon customers.
• Method: Offering a free gift or prize for completing a simple test.
• Exfil: Unknown, likely data harvesting through further interaction or data entry on subsequent pages.
• Indicators: Non-matching domain, prize offer, request to answer questions.
• Risk: MEDIUM - Potential for data harvesting or further phishing attempts.
📡 API Calls Detected
- POST
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Amazon
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3
Mar 16, 2026
Amazon
https://im.nbpublic.com/loading_page/amazon/AmazonGiftCard_5...
Mar 07, 2026
Amazon
https://im.nbpublic.com/loading_page/snack_box/snack_box_cf_...
Dec 31, 2025
No screenshot
Amazon
http://im.nbpublic.com/loading_page/snack_box/snack_box_cf_3
Dec 22, 2025
Scan History for im.nbpublic.com
Found 10 other scans for this domain
-
https://im.nbpublic.com/loading_page/paypal/paypal...
http://im.nbpublic.com/loading_page/snack_box/snac...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://||im.nbpublic.com/loading_page_cpl/amazon/...
https://||im.nbpublic.com/loading_page/amazon/amaz...
http://im.nbpublic.com/loading_page/amazon/AmazonG...
https://im.nbpublic.com/loading_page/paypal/paypal...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://im.nbpublic.com/loading_page/snack_box/sna...
http://im.nbpublic.com/loading_page/snack_box/snac...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.