Phishing Analysis
Detailed analysis of captured phishing page
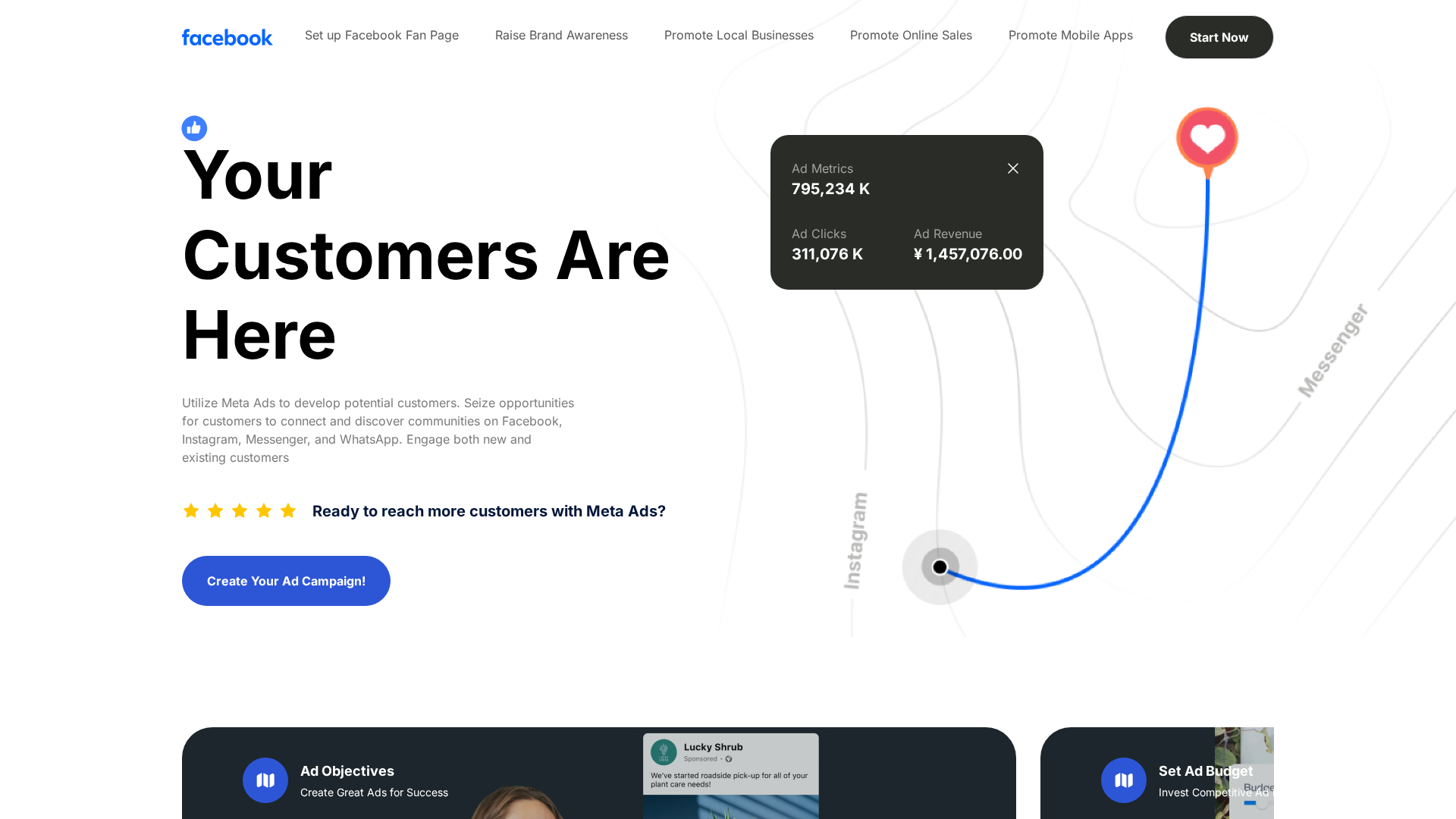
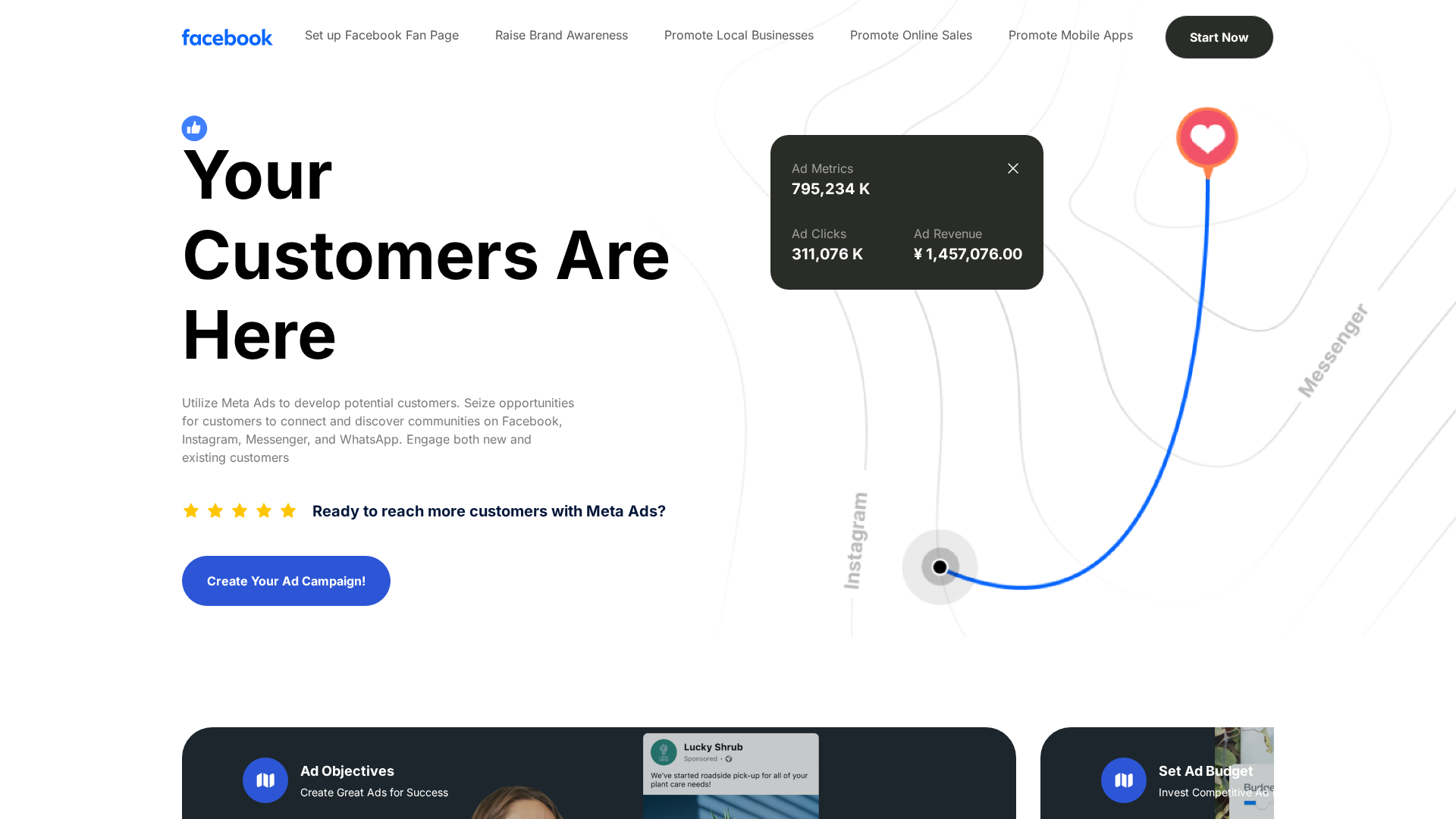
Visual Capture
No screenshot available
Detection Info
https://www.2025baofu026.shop/
Detected Brand
Facebook
Country
International
Confidence
100%
HTTP Status
200
Report ID
e12e562c-a1d…
Analyzed
2026-01-03 01:07
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FB934BB83549B1271B7343B720AE1503B368121F580E4D60B354FDDAB6B8C9A6877BDE |
|
CONTENT
ssdeep
|
1536:Iv39gITXjo9rquNULx4TESLwsGSMBDLw1j90+1Lmjzl:Iv39jupTTwsiW16+1i |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
aec46a921b933fe0 |
|
VISUAL
aHash
|
fdf393bfffbfff81 |
|
VISUAL
dHash
|
1167667131727533 |
|
VISUAL
wHash
|
81b1819d8d9bff81 |
|
VISUAL
colorHash
|
07006000040 |
|
VISUAL
cropResistant
|
1167667131727533,45928b82399c9e61,41843b9a9c0e8045,59dd7c989898ad2d,435b236f67672d13 |
Code Analysis
Risk Score
58/100
Threat Level
BAJO
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Potential brand impersonation if the listed domain is serving this content.
• Target: Facebook users interested in Meta Ads.
• Method: The screenshot showcases a legitimate advertisement for Facebook Meta Ads, the domain provided is irrelevant until proven to host this.
• Exfil: No data exfiltration is happening on the screenshot.
• Indicators: The indicators provided are the domain name and the obfuscated JavaScript mentioned in the prompt, if the domain is found to host the content, then this is a phishing attempt.
• Risk: LOW - Potential brand impersonation depending on the actual domain.
🔒 Obfuscation Detected
- fromCharCode
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.