Phishing Analysis
Detailed analysis of captured phishing page
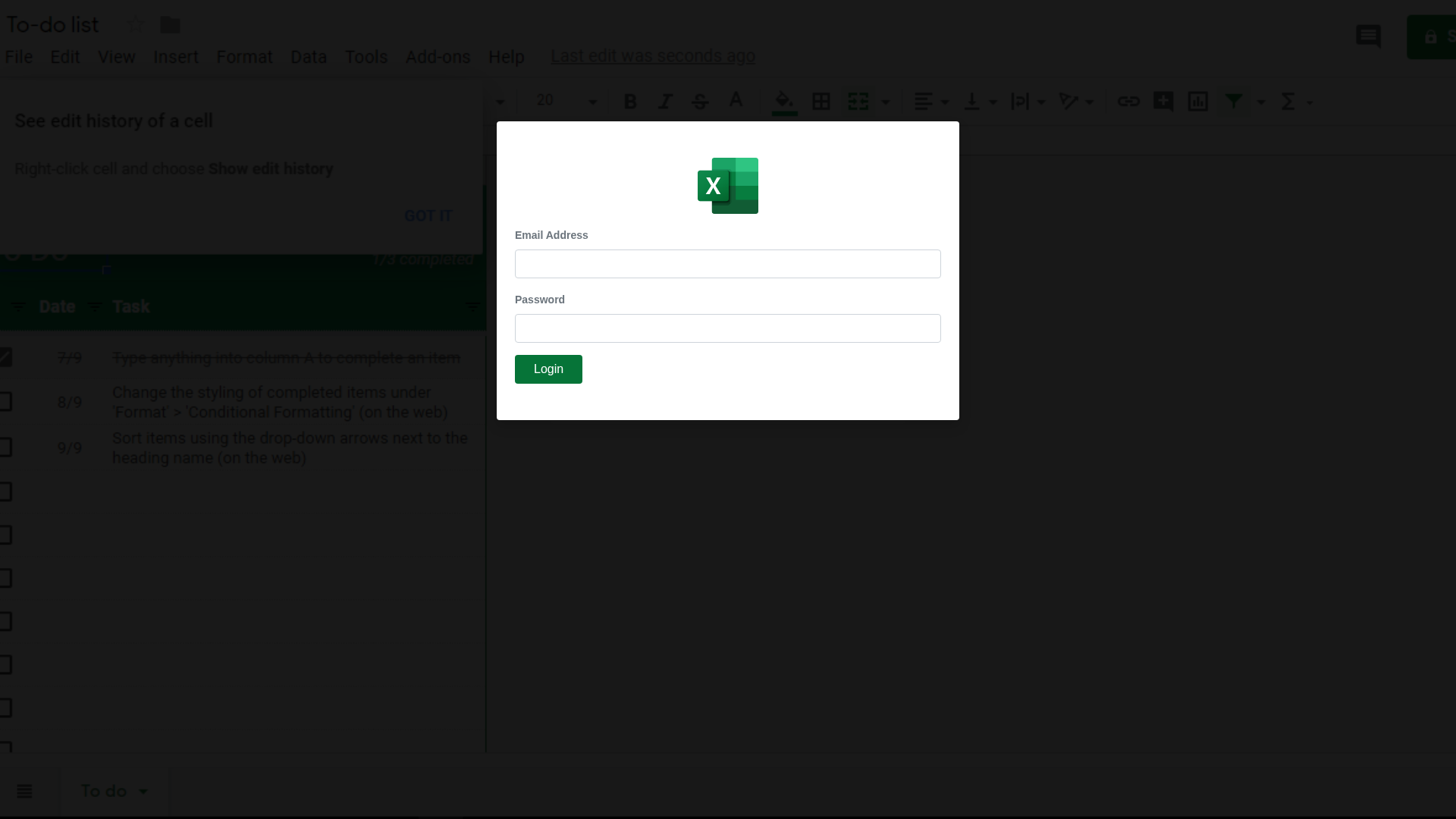
Visual Capture
Detection Info
http://cocorost-556.jp/conference/excel/excel
Detected Brand
Microsoft Excel
Country
International
Confidence
100%
HTTP Status
200
Report ID
e1c0697c-3b3…
Analyzed
2026-01-01 03:06
Final URL (after redirects)
http://cocorost-556.jp/conference/excel/excel/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T11F51EA3020549D2B6ADB95E567B8630AA1C0E2C2CB3357052BFC8BDD5ECAC4BCC93685 |
|
CONTENT
ssdeep
|
48:nZYlPwgTQ/vxhb2K+h8RVhEdl9sJguNPeHx:naQDiK+WilslNPYx |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
999d666731992666 |
|
VISUAL
aHash
|
003c3c3c18000000 |
|
VISUAL
dHash
|
9471717170042000 |
|
VISUAL
wHash
|
7e7f3c3cbce0e000 |
|
VISUAL
colorHash
|
38000000e00 |
|
VISUAL
cropResistant
|
e48ccce0c880d0c0,9471717170042000 |
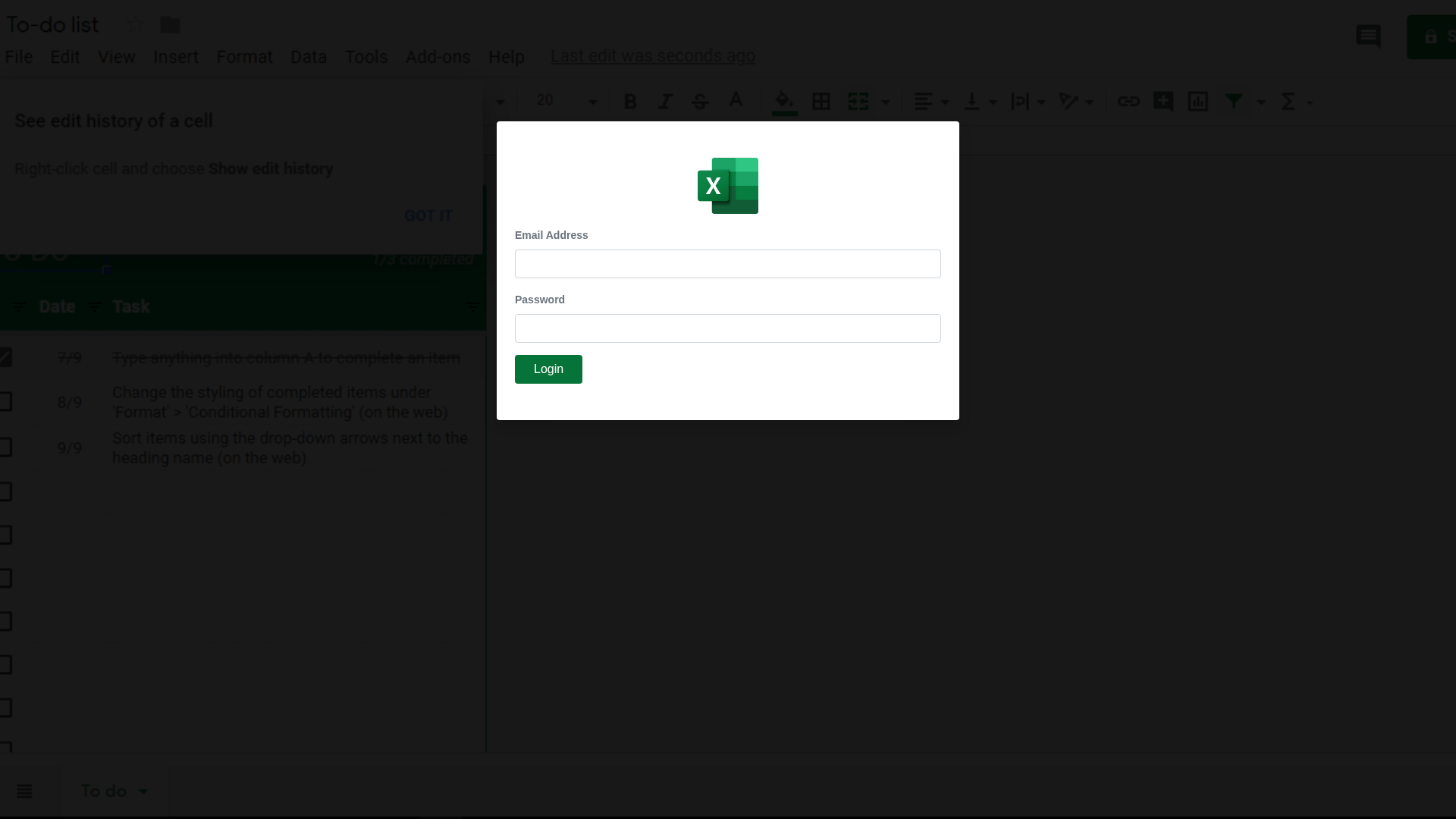
Code Analysis
Risk Score
73/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing attack
• Target: Users of Microsoft Excel (or those tricked into thinking they are using it)
• Method: Fake login form presented within a Google Sheets document
• Exfil: Unknown, likely to a third-party server
• Indicators: Domain mismatch, fake login form, impersonating Microsoft Excel
• Risk: HIGH - Real-time credential theft
🔒 Obfuscation Detected
- fromCharCode
📡 API Calls Detected
- POST
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for cocorost-556.jp
Found 10 other scans for this domain
-
https://cocorost-556.jp/
https://cocorost-556.jp/mail/GlobalSources/?email=...
https://cocorost-556.jp/jo/GlobalSources/?email=3m...
http://cocorost-556.jp/services/
https://cocorost-556.jp/gx/GlobalSources/
https://cocorost-556.jp/mail/GlobalSources/?email=...
https://cocorost-556.jp/conference/excel/excel
https://cocorost-556.jp/mail/GlobalSources/?email=...
https://cocorost-556.jp/gx/GlobalSources/?email=
https://cocorost-556.jp/in/GlobalSources/

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.