
Phishing Analysis
Detailed analysis of captured phishing page
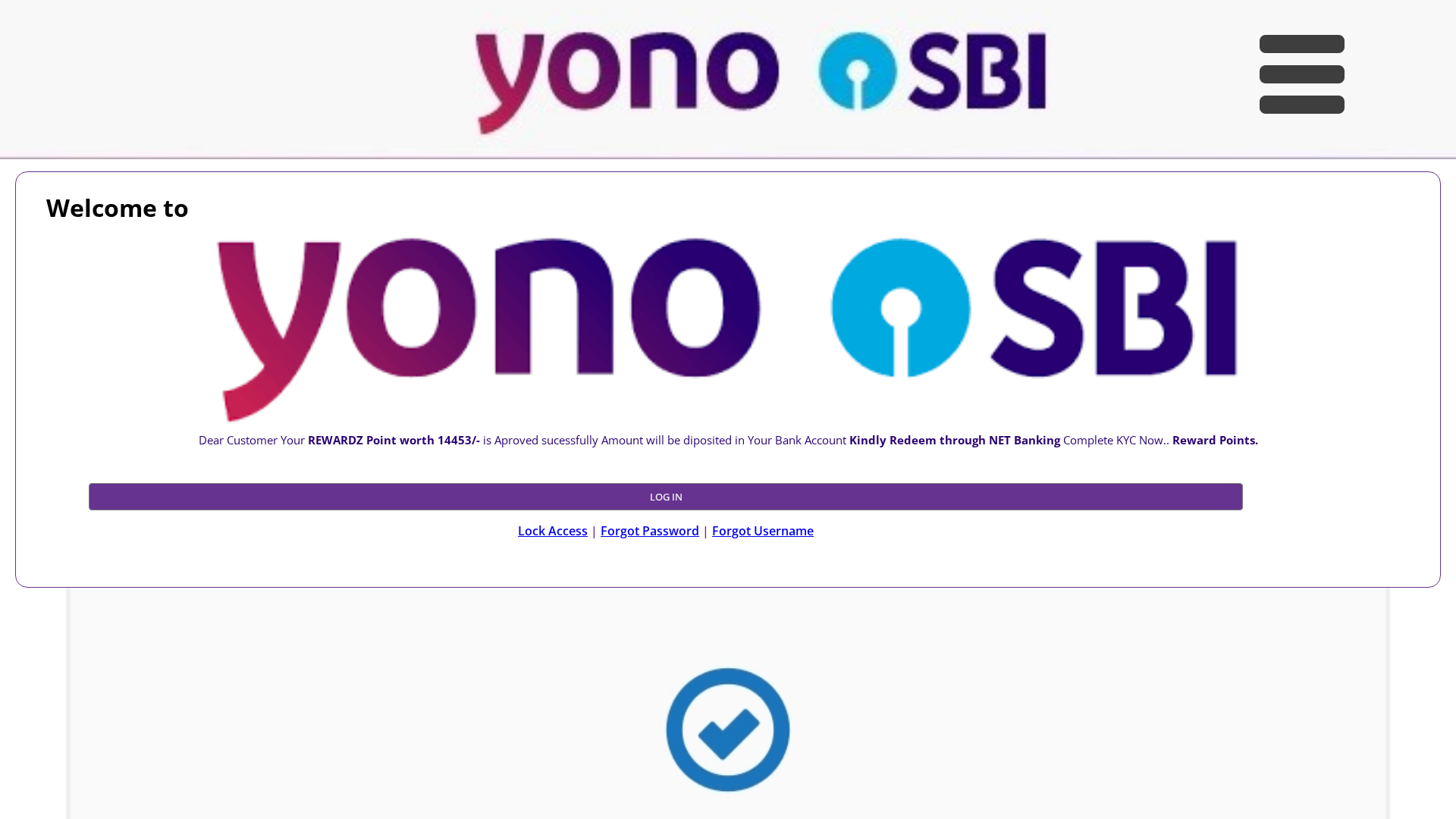
Visual Capture
Detection Info
https://www.sblvtr.vercel.app/
Detected Brand
YONO SBI
Country
International
Confidence
95%
HTTP Status
200
Report ID
e2a8c51f-144…
Analyzed
2026-02-25 17:10
Final URL (after redirects)
https://sblvtr.vercel.app/
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1055173314849E88F857380C1F653791DE243851A8B534F41B7A9C6E5F9D6D36D93138E |
|
CONTENT
ssdeep
|
48:AU6CCSEM/8pwWTNmTNMQk52SVT1kNNyybxafd+WhmkUq8GTxBaLN0:sSfk53VTuNrad/m2sLN0 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
fb79c484637a3906 |
|
VISUAL
aHash
|
c2ff818183ffffe7 |
|
VISUAL
dHash
|
16d61b3b671b0c4d |
|
VISUAL
wHash
|
c0da818101ffe7e7 |
|
VISUAL
colorHash
|
07000400049 |
|
VISUAL
cropResistant
|
16d61b3b671b0c4d,2d2d929292d27065,66aaca4a2a2aaa66,0f3371696971310f,0f71616969696969,0f3371696971310f,33f5c4653594b567,6969713313061d3a,0008101010100800 |
Code Analysis
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Phishing
• Target: YONO SBI customers
• Method: Impersonation with reward scam
• Exfil: Likely steals credentials
• Indicators: Free hosting, KYC request, reward claim
• Risk: High
🔐 Credential Harvesting Forms
🎯 Kit Endpoints
- https://retail.onlinesbi.com/retail/troubleloginhome.htm?bankCode=0
📤 Form Action Targets
- /
📊 Risk Score Breakdown
Total Risk Score
90/100
Contributing Factors
Free Hosting
The site is hosted on a free hosting platform (vercel.app), which is commonly used for phishing.
Brand Impersonation
The site displays the logo and branding of YONO SBI, attempting to mimic the legitimate site.
Urgency / Reward
Contains text like 'REWARDZ Point' and 'KYC', which is used to entice users into clicking/submitting details.
🔬 Comprehensive Threat Analysis
Threat Type
Credential Harvesting Kit
Target
YONO SBI users (International)
Attack Method
Brand impersonation + credential harvesting forms
Exfiltration Channel
HTTP POST to backend
Risk Assessment
MEDIUM - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Brand Impersonation Analysis
Impersonated Brand
YONO SBI
Official Website
null
Fake Service
Login Portal
Fraudulent Claims
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker aims to steal user credentials (username and password) by creating a fake login page that mimics the appearance of the YONO SBI login portal. Users are tricked into entering their credentials, which are then harvested by the attacker.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
www.sblvtr.vercel.app
Registered
Unknown
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

YONO SBI
http://www.rebrand.ly/Su7/
Feb 25, 2026
No screenshot
Yono SBI
http://online-jet.vercel.app
Dec 15, 2025
No screenshot
SBI
https://online-jet.vercel.app/
Dec 15, 2025
No screenshot
Yono SBI
https://online-jet.vercel.app/
Dec 15, 2025
No screenshot
YONO SBI
https://www.online-jet.vercel.app/
Dec 15, 2025

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.