
Phishing Analysis
Detailed analysis of captured phishing page
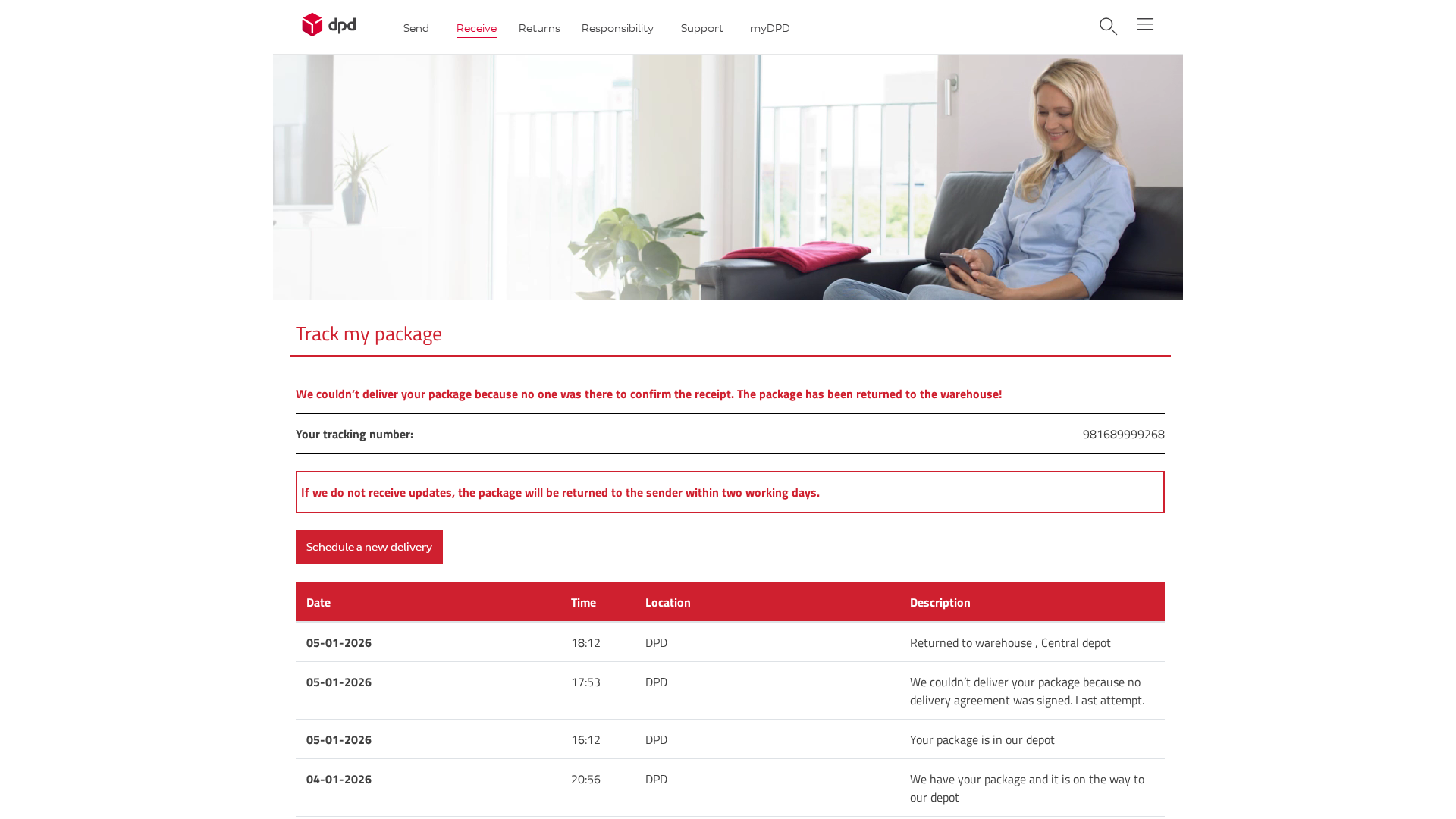
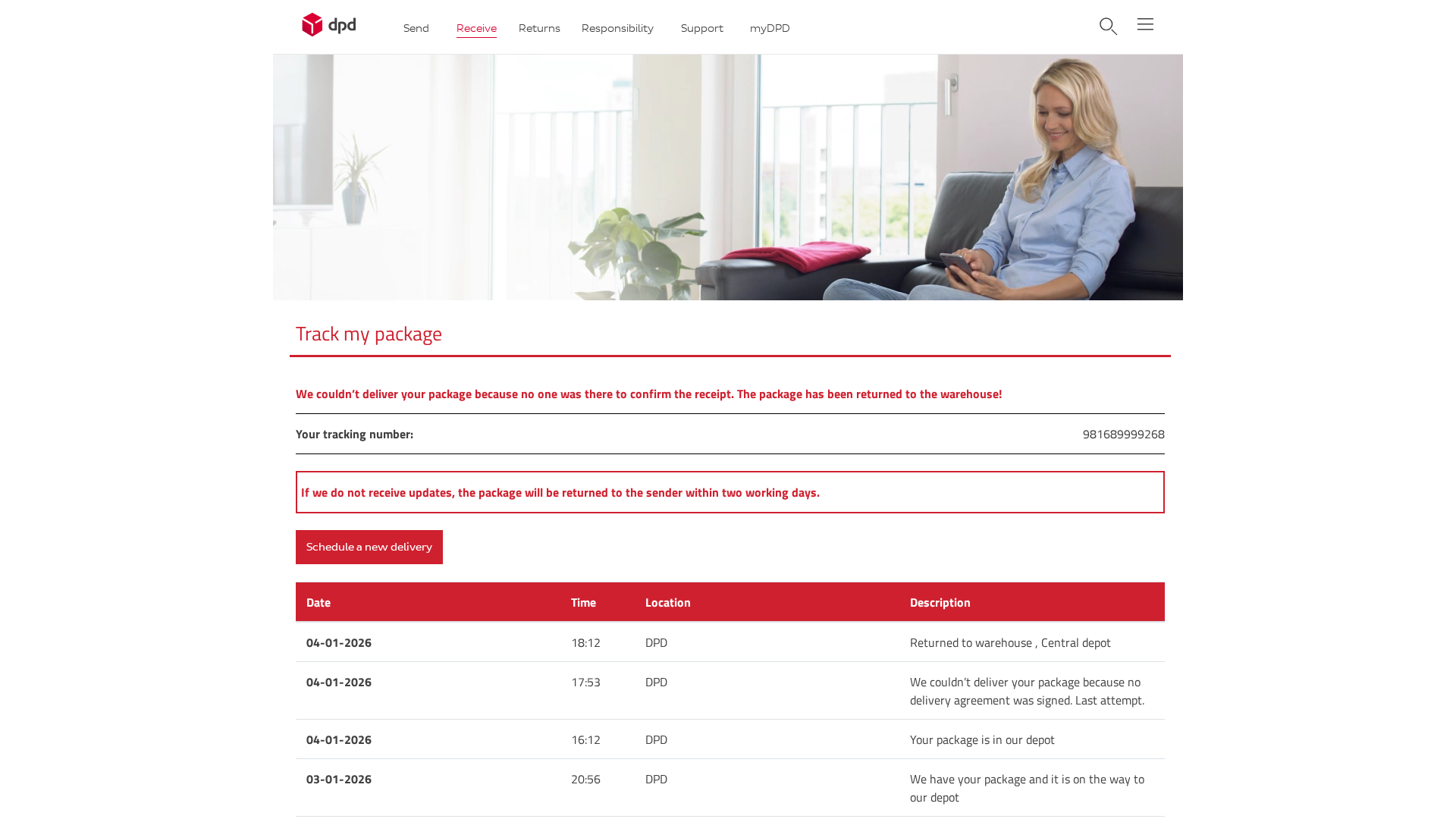
Visual Capture
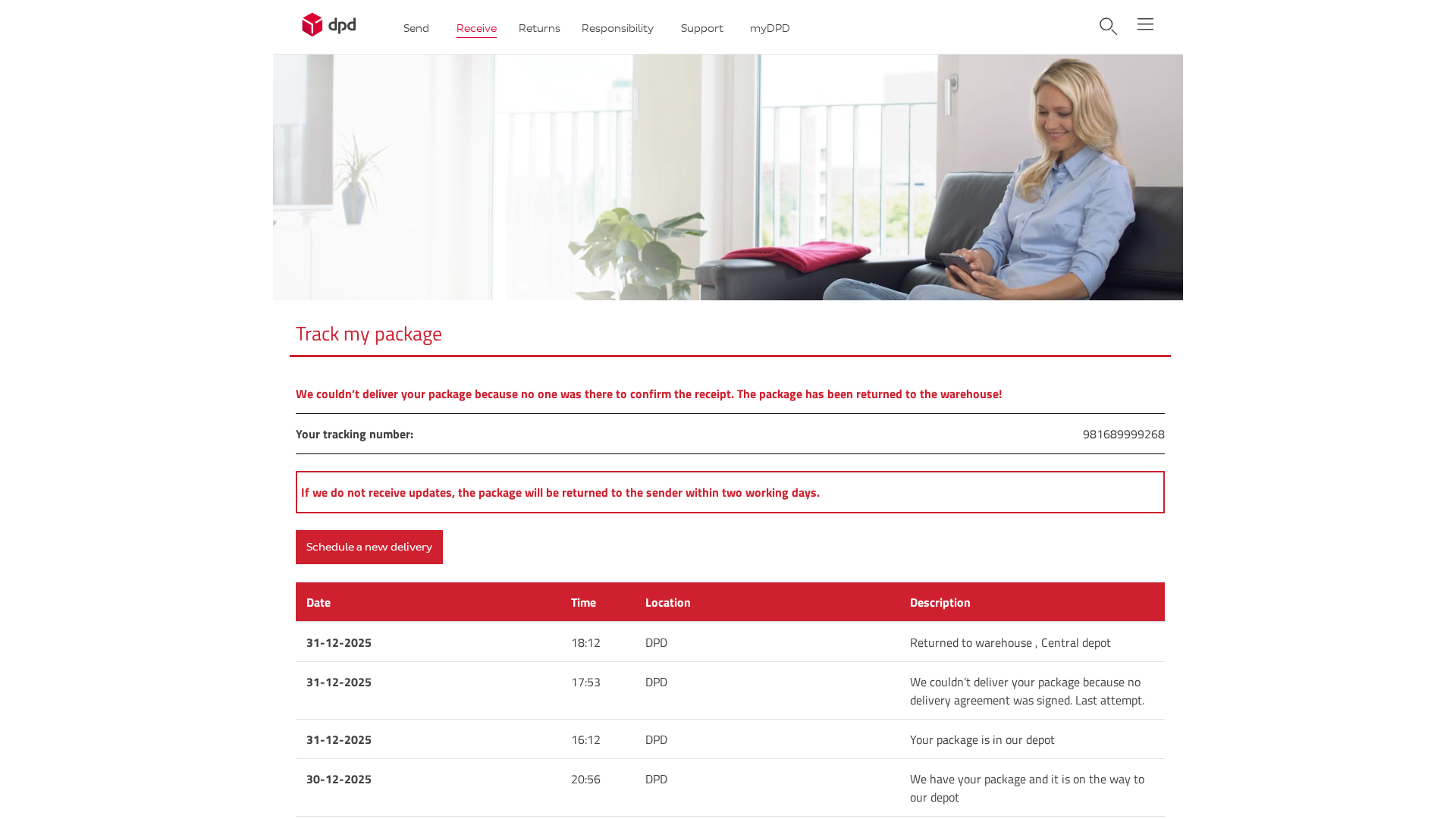
Detection Info
https://217-160-164-192.cprapid.com/de/update.php
Detected Brand
DPD
Country
International
Confidence
100%
HTTP Status
200
Report ID
e371e31b-3a0…
Analyzed
2026-01-02 17:10
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T176B2017094B5B63F009F7391A7386709A3D39383CB520BE567F8836D5B8AE84DC23169 |
|
CONTENT
ssdeep
|
192:bixLoxwz77qKHv/ySchJrVUmZGkoRXTCReWyRMOsUFf9kIT/JO:mx8xw7pvKpJrVUIGk0+TxFUH/JO |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e96bc99c962466c3 |
|
VISUAL
aHash
|
f9e9e1f7ff81c3ff |
|
VISUAL
dHash
|
2b030327382b1342 |
|
VISUAL
wHash
|
a9a1e1c7c78181fb |
|
VISUAL
colorHash
|
07000000006 |
|
VISUAL
cropResistant
|
2b030327382b1342,696969c9692b3734,337367e7cdcd8d1d,0000db6464649b24 |
Code Analysis
Risk Score
95/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Package delivery redirection phishing
• Target: DPD customers
• Method: Fake tracking page prompts for delivery address update
• Exfil: Unknown, likely to a database or email
• Indicators: Non-DPD domain, generic error, prompts for address
• Risk: HIGH - Data theft and potential identity theft
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- log.php?cmd=_update_information&account_wall
📡 API Calls Detected
- POST
- https://whos.amung.us/stats/
- GET
📤 Form Action Targets
- #
- date.php
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
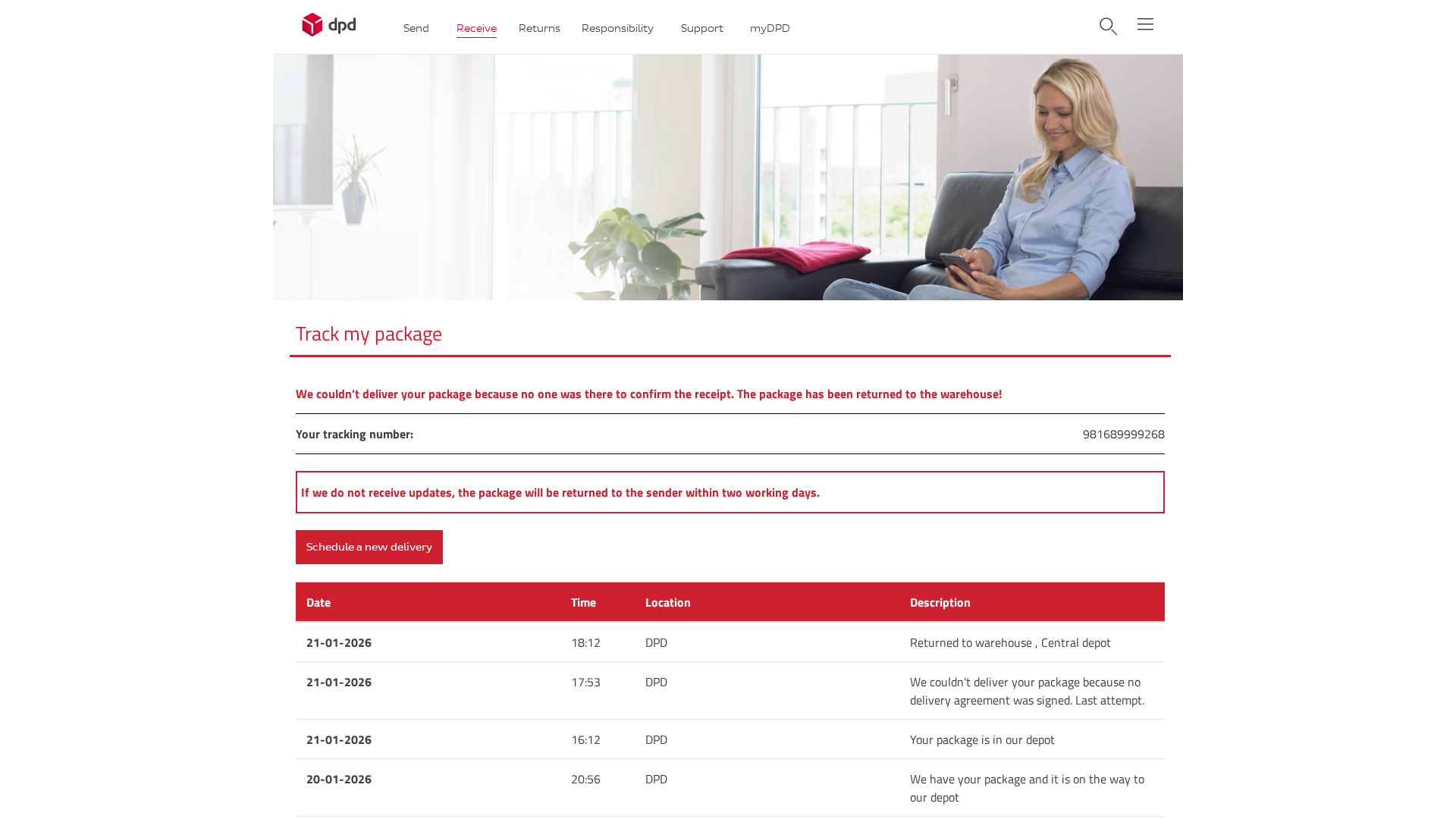
DPD
https://217-154-235-190.cprapid.com/de/update.php?l17wsw8dbi...
Jan 23, 2026
DPD
https://217-154-235-190.cprapid.com/de/update.php?g2e1r8w2pu...
Jan 23, 2026
DPD
https://217-154-235-190.cprapid.com/de/update.php?n10kik39uu...
Jan 23, 2026
DPD
https://138-68-183-9.cprapid.com/de/update.php
Jan 15, 2026
DPD
https://217-160-164-192.cprapid.com/de/update.php?g1hdiel1pc...
Jan 15, 2026
Scan History for 217-160-164-192.cprapid.com
Found 10 other scans for this domain
-
https://217-160-164-192.cprapid.com/
https://217-160-164-192.cprapid.com/de/date.php
https://217-160-164-192.cprapid.com/de/shippingdat...
https://217-160-164-192.cprapid.com/de/kasse.php
https://217-160-164-192.cprapid.com/de/kasse.php
https://217-160-164-192.cprapid.com/de/shippingdat...
https://217-160-164-192.cprapid.com/de/date.php
https://217-160-164-192.cprapid.com/de/update.php
https://217-160-164-192.cprapid.com/de/update.php?...
https://217-160-164-192.cprapid.com/de/update.php?...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.