
Phishing Analysis
Detailed analysis of captured phishing page
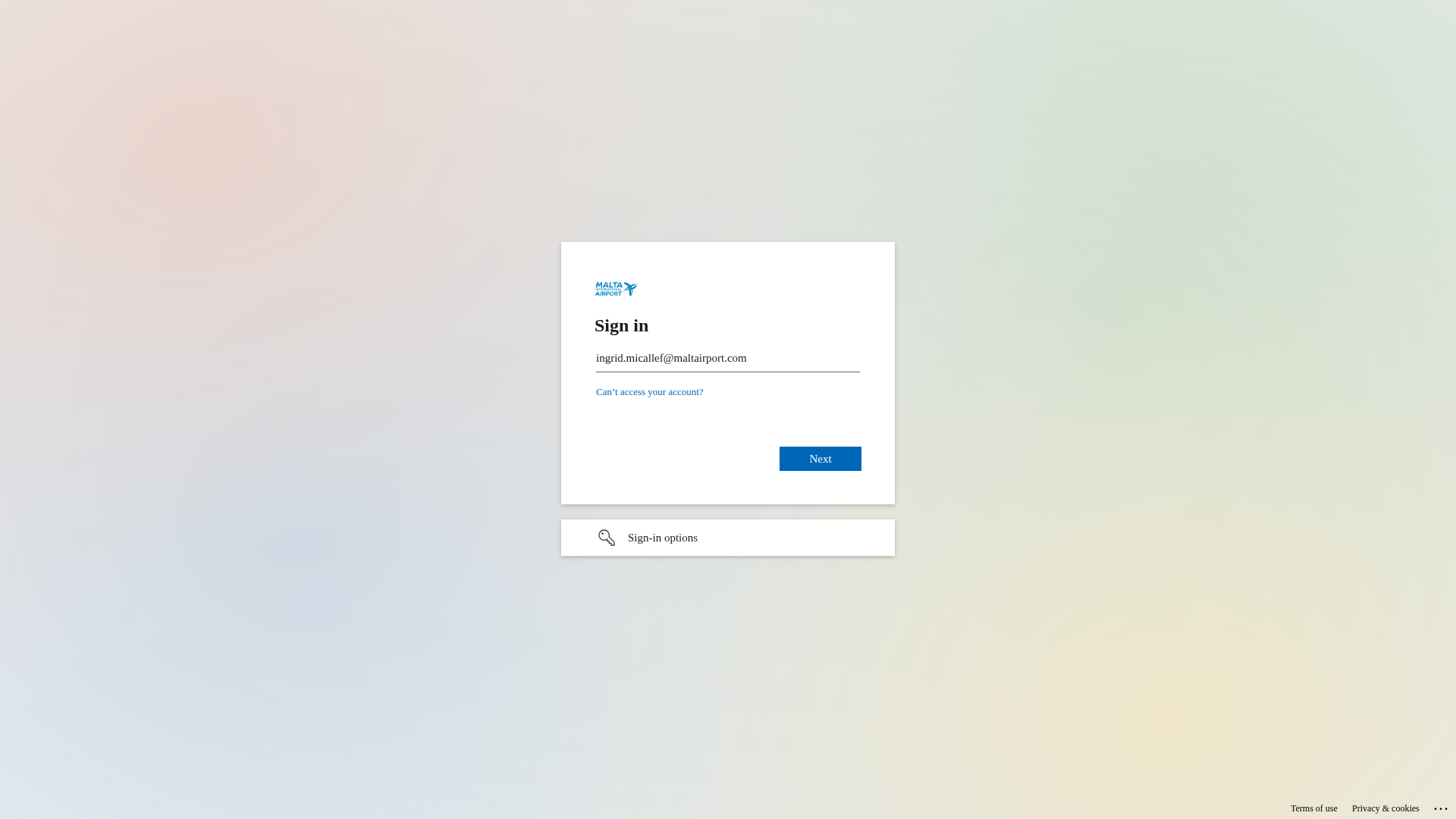
Visual Capture
Detection Info
https://auth-secure.me/W9fGQN9d7MBo
Detected Brand
Malta Airport
Country
International
Confidence
100%
HTTP Status
200
Report ID
e52316db-3a8…
Analyzed
2026-02-05 11:58
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12BD1EF7160509D3B52C3C6D4B2B96B5F3394C346EA87566A67F4C78C0EF3E16CC1A226 |
|
CONTENT
ssdeep
|
96:nIpkCGTHRPyCdM+krwkMzs39TbJG9KjsWsjOt0U2gs0sjOIOVJQ6Q6ynQjNsjOx:9Pdfk8+9TbJG9aToOVJQyyQjF |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c497326cc99d9e4 |
|
VISUAL
aHash
|
18001818191f0f9f |
|
VISUAL
dHash
|
7161313331727d38 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
7161313331727d38 |
Code Analysis
Risk Score
70/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Threat: Credential Phishing
• Target: Malta Airport Employees/Users
• Method: Domain Spoofing
• Exfil: Stolen Credentials
• Indicators: Mismatched Domain, Form Field
• Risk: High
🎯 Kit Endpoints
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-903832305169&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-2888-21bc5137cc6d&protectedtoken=true&domain_hint=maltairport.com&nonce=236479803447.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=aW5ncmlkLm1pY2FsbGVmQG1hbHRhaXJwb3J0LmNvbQ#
- https://login.microsoftonline.com/common/login#
- https://passwordreset.microsoftonline.com/?ru=https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-588329030920&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-1107-21bc5137cc6d&protectedtoken=true&domain_hint=maltairport.com&nonce=977779769301.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=aW5ncmlkLm1pY2FsbGVmQG1hbHRhaXJwb3J0LmNvbQ#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-347724824671&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-3257-21bc5137cc6d&protectedtoken=true&domain_hint=maltairport.com&nonce=764369411043.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=aW5ncmlkLm1pY2FsbGVmQG1hbHRhaXJwb3J0LmNvbQ#
📊 Risk Score Breakdown
Total Risk Score
95/100
Contributing Factors
Domain Mismatch
The domain 'auth-secure.me' has no connection to the real brand.
Impersonation
The page tries to impersonate the design and functionality of the targeted brand.
Form with Credentials
Form is used to collect sensitive information, email address.
🔬 Comprehensive Threat Analysis
Threat Type
Two-Factor Authentication Stealer
Target
Malta Airport users (International)
Attack Method
Brand impersonation
Exfiltration Channel
Form submission (backend endpoint not detected - likely JavaScript-based)
Risk Assessment
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Brand Impersonation Analysis
Impersonated Brand
Malta Airport
Fake Service
Login Portal
⚔️ Attack Methodology
Primary Method: Credential Harvesting
The attacker attempts to steal user credentials by creating a fake login page that mimics the appearance of the targeted brand.
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
auth-secure.me
Registered
2023-06-05
Registrar
Namecheap
Status
Active
🤖 AI-Extracted Threat Intelligence
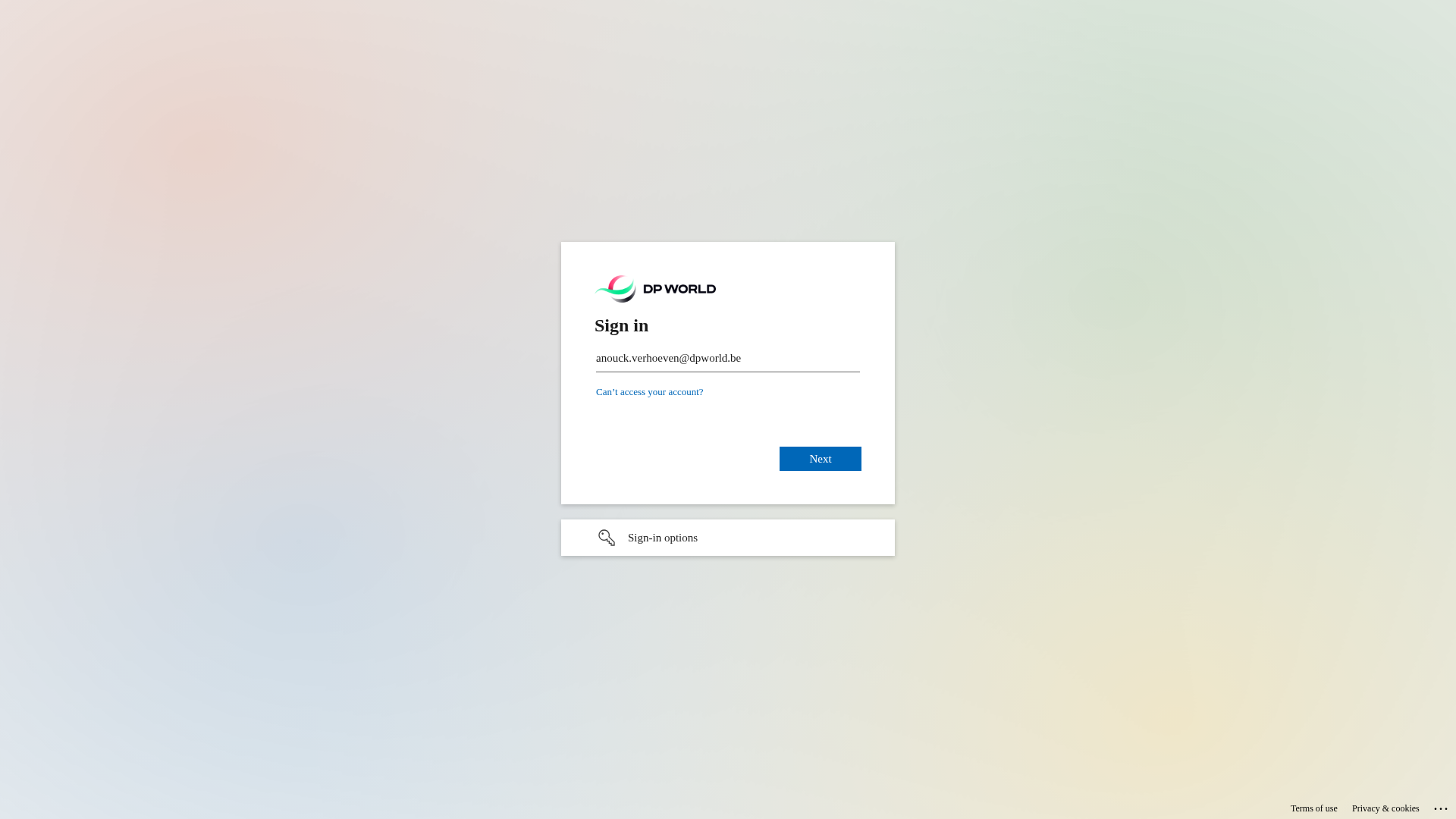
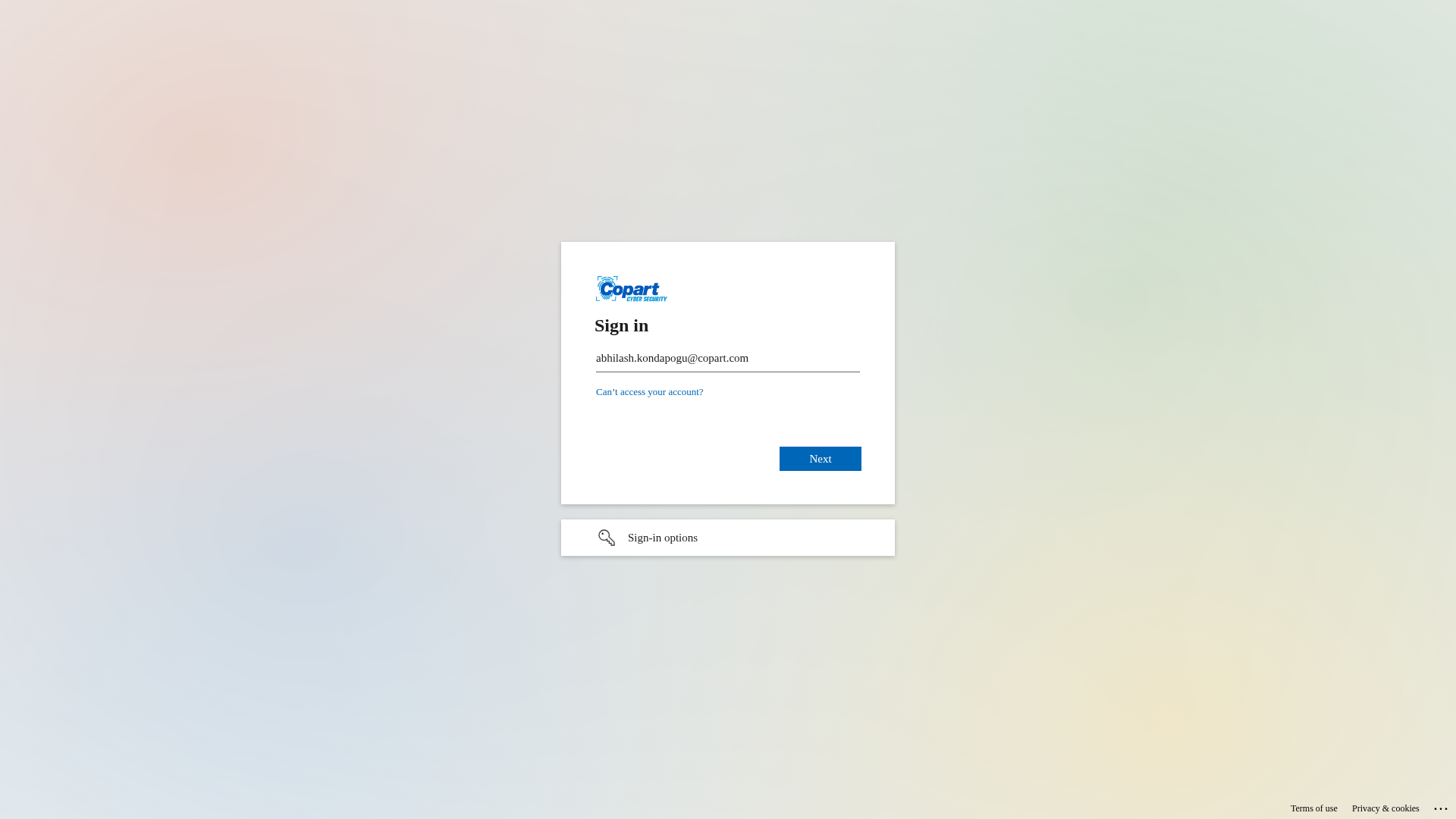
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
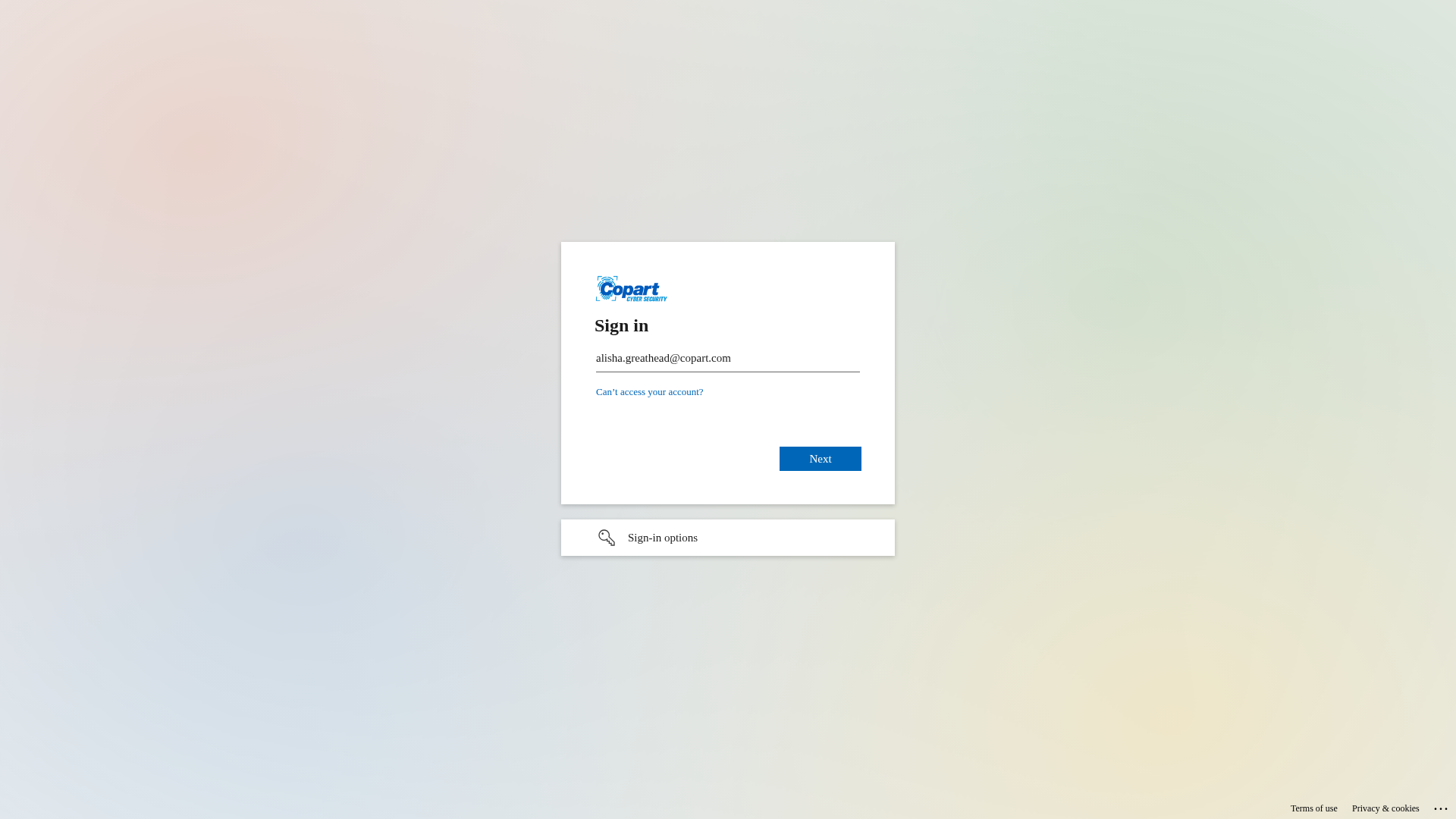
Copart
https://auth-secure.me/8t0G40Uc4yzL
Apr 04, 2026
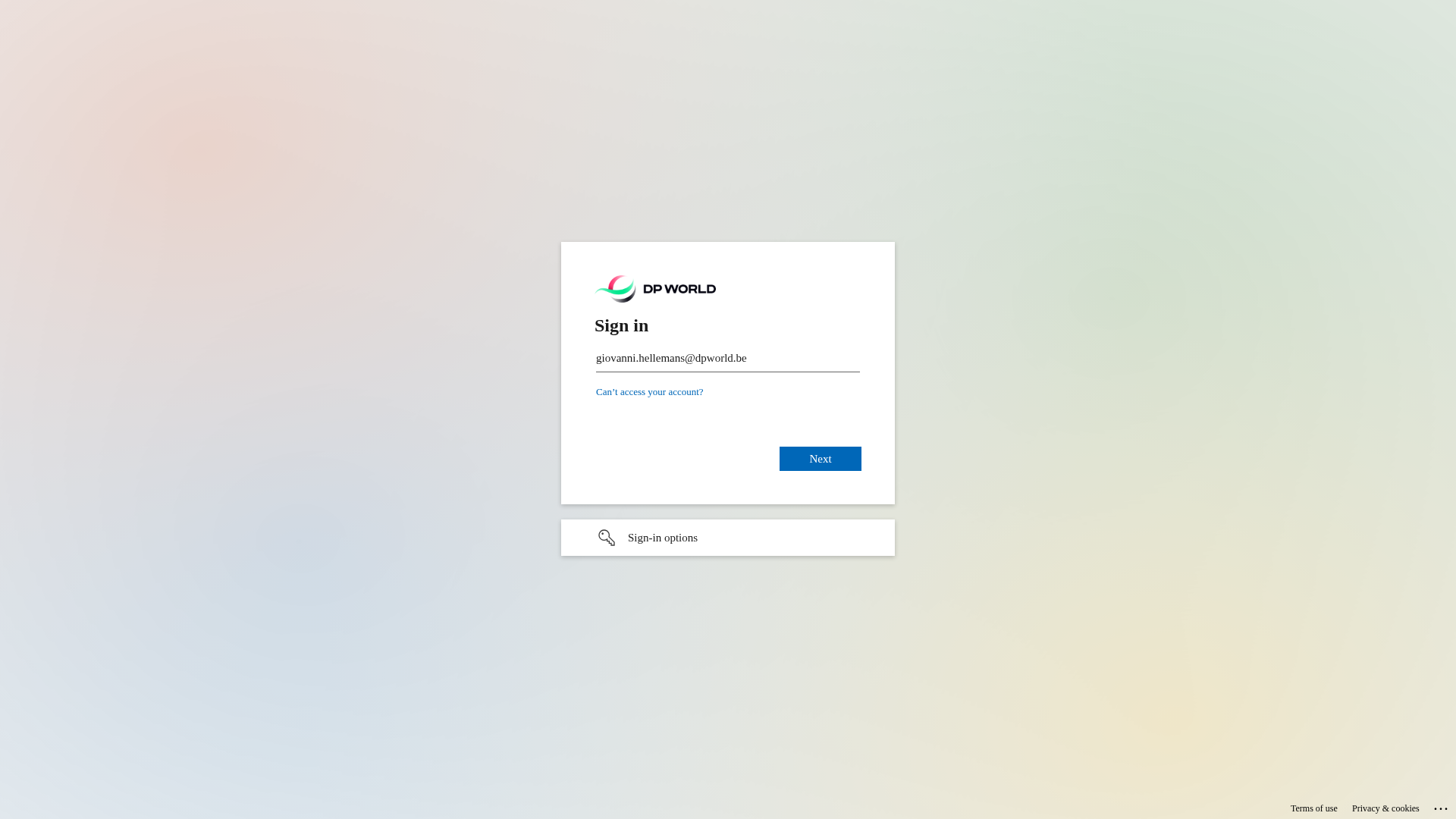
DP World
https://auth-secure.me/FcJF1VCMe7t3p6dU
Apr 04, 2026
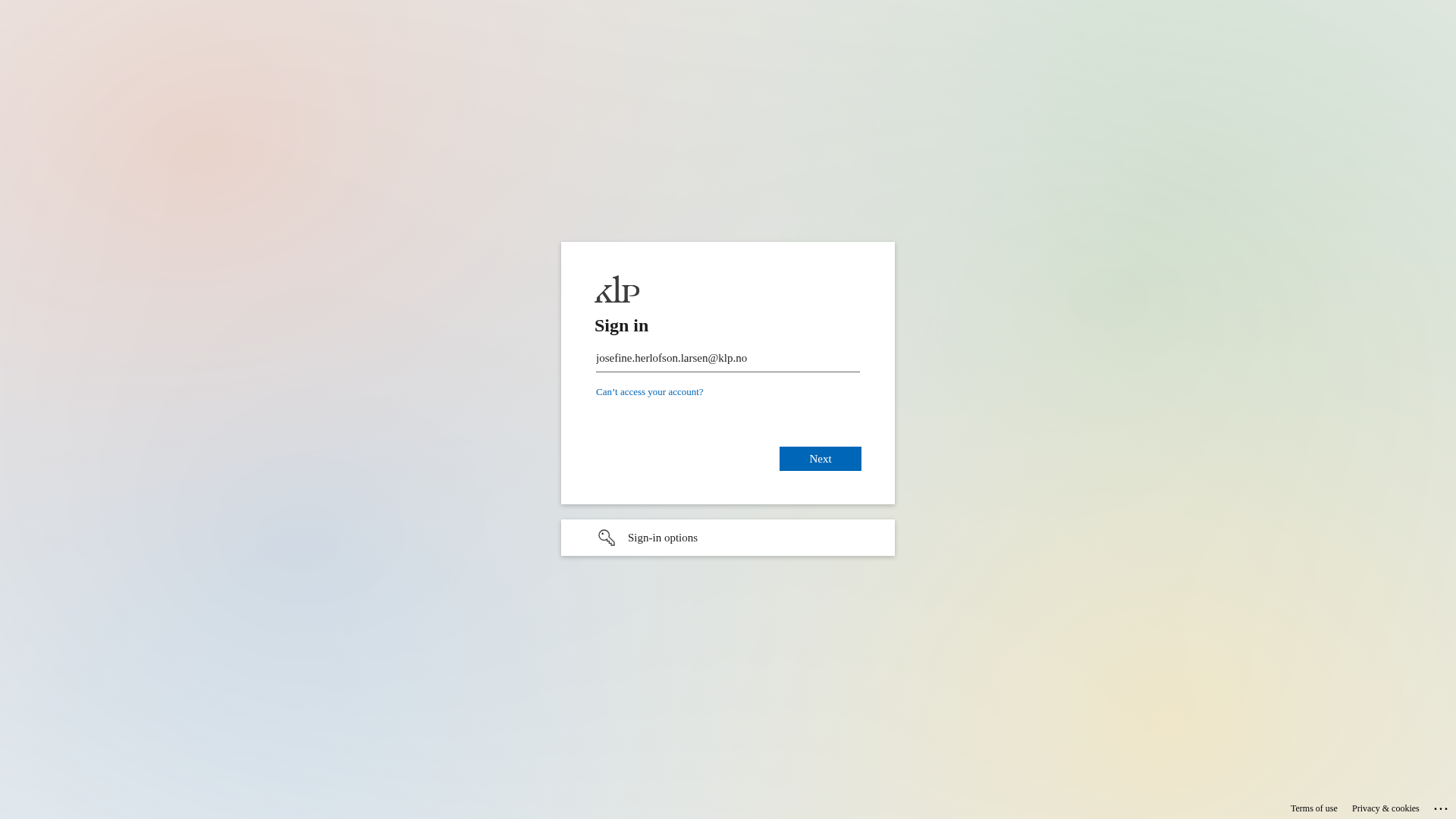
Microsoft
https://authentication.ms/FQXXJbjMQUwdPlw
Apr 04, 2026
DP World
https://signin.broker/yEXpO8mh47e1zQ
Apr 01, 2026
Copart
https://sso-security.com/hmoR7AjmD5_J9_rblw
Mar 31, 2026
Scan History for auth-secure.me
Found 10 other scans for this domain
-
https://auth-secure.me/8t0G40Uc4yzL
https://auth-secure.me/FcJF1VCMe7t3p6dU
https://auth-secure.me/aHS0lPwJXIgH
https://auth-secure.me/FD6ykZKir2E
https://auth-secure.me/VUdcJNnhD7bqnLCWgw
https://auth-secure.me/qU3AmxUILiqopQ
https://auth-secure.me/QGzrBLQ5YfdCUg
https://auth-secure.me/ehtRFxyFoletQQ
https://auth-secure.me/PnAdVDt9w961P1KJfQ
https://auth-secure.me/THrkG16Tmw5DXxA

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.