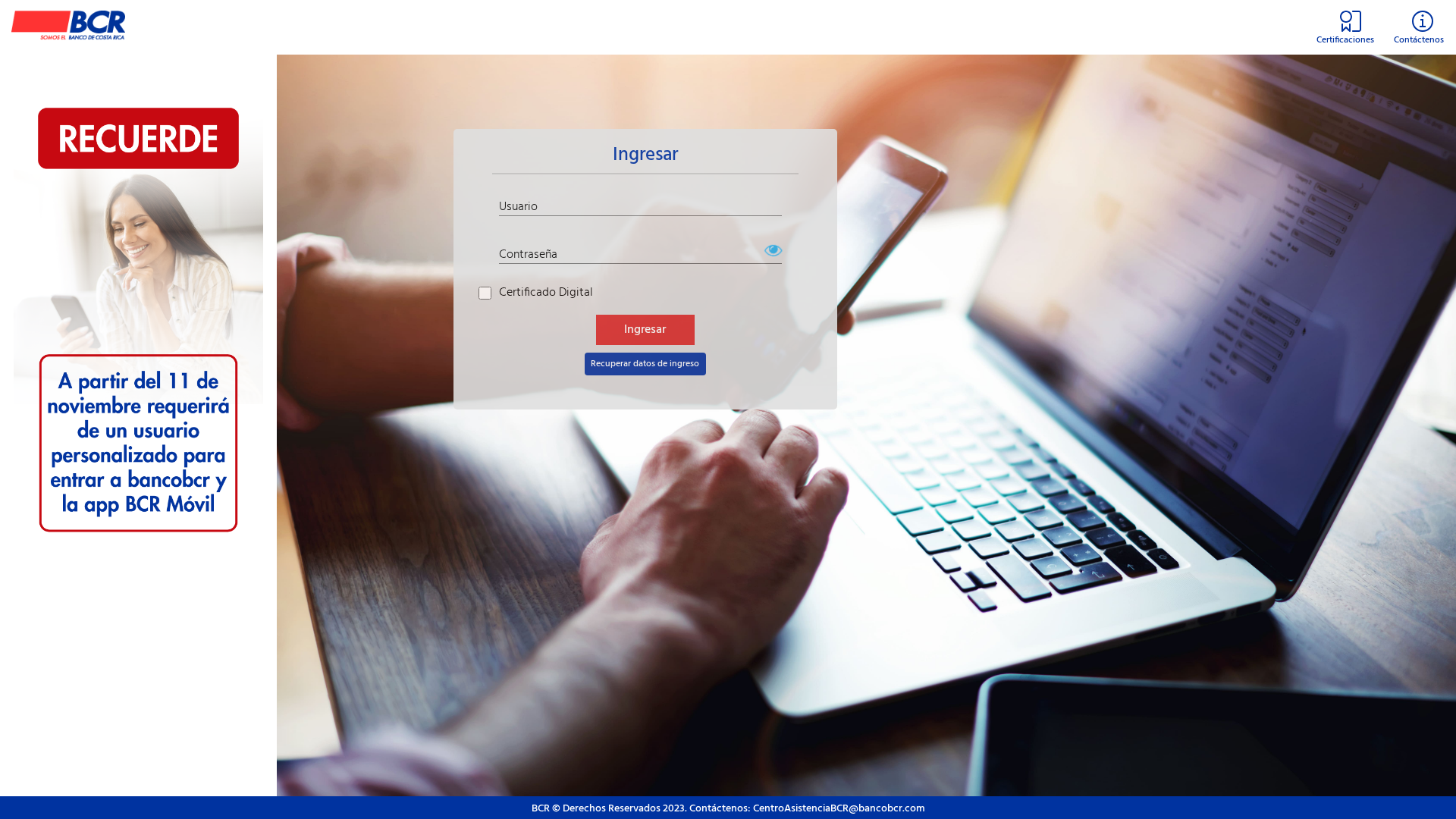
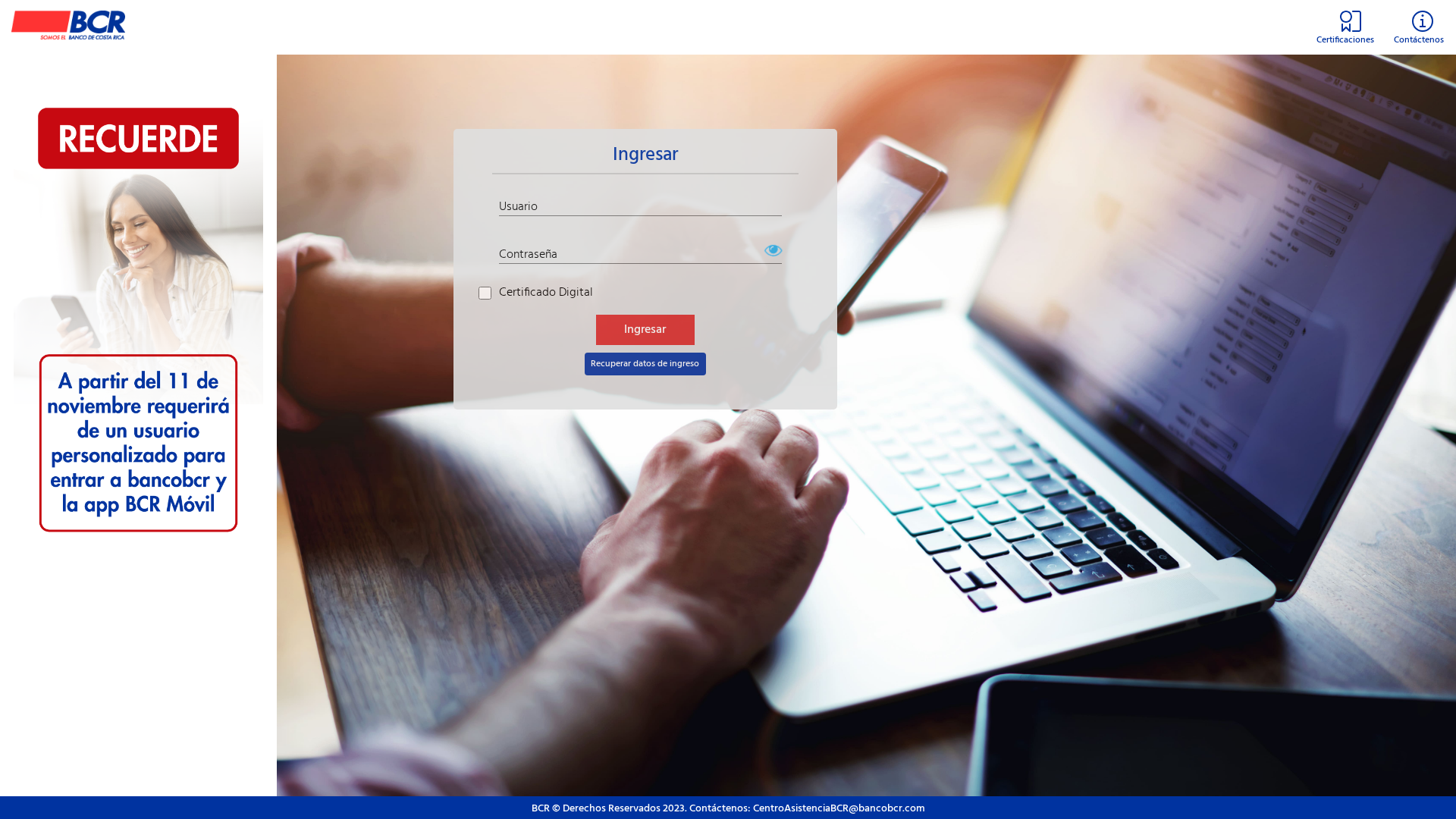
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C341046468C99D77E143A0E4C793BF1A32C2C245D79B090A93F997EA1FC7D25CD13190 |
|
CONTENT
ssdeep
|
48:glRIEP5PXtJmCWSUk+HFgT4lCb8sMhBvlr:cvtPWLus7sMhpF |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
da8561ba4af9b4c2 |
|
VISUAL
aHash
|
fefefe9c9cc4c0c0 |
|
VISUAL
dHash
|
b4642c2829290908 |
|
VISUAL
wHash
|
febefe8c9c84c080 |
|
VISUAL
colorHash
|
07601000040 |
|
VISUAL
cropResistant
|
b4642c2829290909,cba76c9830e0c0a0,7464282929290908,844ba89a9aa4c304,f9dc7c7e5f494326 |
Code Analysis
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- base64_strings
🔑 Telegram Bot Tokens (1)
- 6935178892:AAEW...-ywFnwIw
☁️ Cloud Backend
- Firebase: basedtos-84767.firebaseapp.com
📊 Risk Score Breakdown
Contributing Factors
🔬 Comprehensive Threat Analysis
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester
- 17 obfuscation techniques
🏢 Brand Impersonation Analysis
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 17 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
📡 Telegram Command & Control Infrastructure
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Infrastructure Indicators of Compromise
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for bcrsline.vercel.app
Found 1 other scan for this domain