
Phishing Analysis
Detailed analysis of captured phishing page
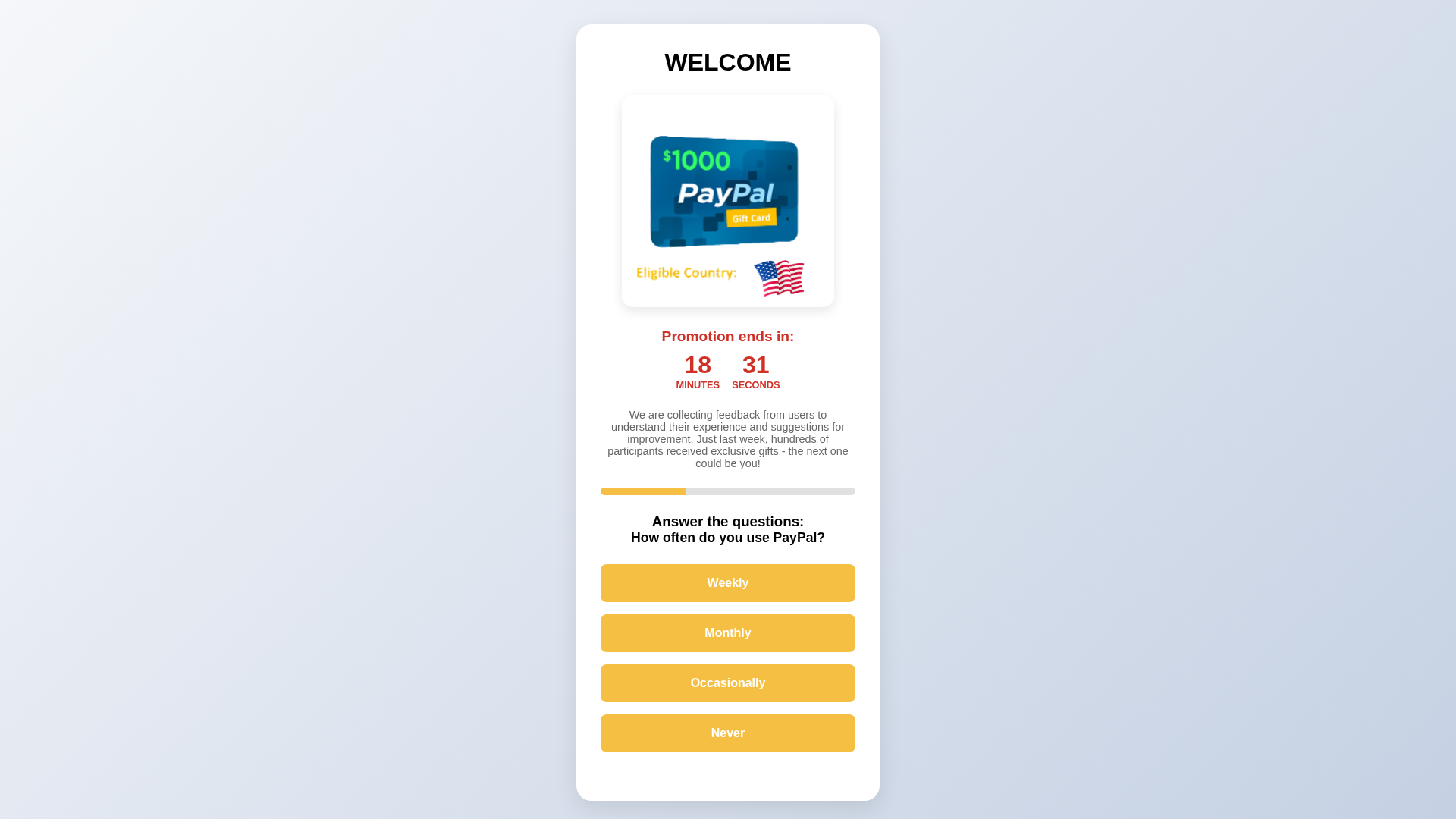
Visual Capture
Detection Info
https://im.nbpublic.com/loading_page/paypal/paypal_cf_9/index.html?lptoken=178b679293c5996d23ca&cep=N4Igdgpg7g+gFgSwC4wQExALhGgjAIwGYJdDCBaAMwDZbyAWAVkoAZz8AmXADnYjXpoOjAJz5ulfCAA0IAG4IAzslQZsLfNUqUA7N3rlCAQ3ocGRwge4jT7EZZaFcEVjogz5SlUgQBbCIpIRr4ADlggHCwc1OQsuLEiACosjJiMqRyEAHTUhNwAWh4KykgA9gBOquGM9PRGuBwiEOQ6HDqUDDRo5BaM3RyUZPg6RpIsAMaEHuPBIUYIAOZgVdjU3EZaLGh9znHjLHHREOMQ9JQeYKVoECsgLDC4F1c3SACeIe7YADJGYGgIYAWT2uMHGcHmYCwAG07g8QABdWQhcoBCAAG2OSH4MEu1ywoDeH3CPz+AKBsiC5QWEBQ6HCa20hBoOiGtREBwaNQ4aGoj1kuJudPUcP5EAAHkh8SBCZ8QAB5bQQcoeSnU2lqEBrDbHfCMFLXfBoDltXAiRim4GCjX3G0AH3uuBgLHtMA4TpdhCdF3FkswYAArmi0QBfYOyMEQmAhUolBClSGYUDjf3lFFgJAAOWeAEk/uKsCxZPhyr8wbn/idFND4WGQEoYCj/ijxr6kOV/RBZABHRRhRMgIxoOSg2bzJa3YCDkehVTBjyD4elRWVIUgSdDhWUJXZtBz2SjSgINEIIxYicAAQBlFKWUU/vwoPBYEgaPPe4Hf3KpXQE+uch376/GgX4/j+vjbOEwB/juACy2zvuMx7jAA1heV43ohCAoegb7TCip4IHIVqQeM+E+ERAF4RABFETiwSysApHUeREAZvR74LPMGrAJx6AcVxMDgYwkG8WgcGMO+6CUEYkFSUYkloNJgkQdgwByeJkn+AgslaZpEAIMpwmqX4+kaR4vhGOMkEWeM742YZ1mWWZsilFxkGuXxHgeWgDmqd5zkgEuW6VGA9GQZeYDXlkMyhGOYBZEFSp0f4uGyP6Mmqel77+v6q7ABFUUxXMizxaFKVzrW9aQFAWDSWiigQMGQA=
Detected Brand
PayPal
Country
USA
Confidence
95%
HTTP Status
200
Report ID
e81336e2-2c7…
Analyzed
2026-01-09 13:17
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E38131BA80D5273307D391C07B93AB4B76E1C244E7491B402EF6829C1BDBF59992E253 |
|
CONTENT
ssdeep
|
48:CEHPw5RE7U1ooAn8aVk1I8X/4NBILwHi1OSR9OtBrjk7pZ6gjXhBTZZR2NiPwfIg:lIRoU1Sk1I8v5P1OsstBrFgjjZZ/qh3 |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f3f36288cccc8c33 |
|
VISUAL
aHash
|
fce4e4f8f8e0e0d8 |
|
VISUAL
dHash
|
3008083030080820 |
|
VISUAL
wHash
|
fce0e0f8f8e0e0d8 |
|
VISUAL
colorHash
|
07000038040 |
|
VISUAL
cropResistant
|
3008083030080820 |
Code Analysis
Risk Score
8/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: PayPal users in the USA
• Method: Fake feedback form stealing user input
• Exfil: Data sent to unknown server
• Indicators: Domain mismatch, countdown timer, obfuscated JavaScript
• Risk: HIGH - Immediate credential theft
🔒 Obfuscation Detected
- fromCharCode
📡 API Calls Detected
- POST
Scan History for im.nbpublic.com
Found 10 other scans for this domain
-
https://im.nbpublic.com/loading_page/paypal/paypal...
http://im.nbpublic.com/loading_page/snack_box/snac...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://||im.nbpublic.com/loading_page_cpl/amazon/...
https://||im.nbpublic.com/loading_page/amazon/amaz...
http://im.nbpublic.com/loading_page/amazon/AmazonG...
https://im.nbpublic.com/loading_page/amazon/Amazon...
https://im.nbpublic.com/loading_page/snack_box/sna...
http://im.nbpublic.com/loading_page/snack_box/snac...
http://im.nbpublic.com/loading_page/snack_box/snac...

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.