
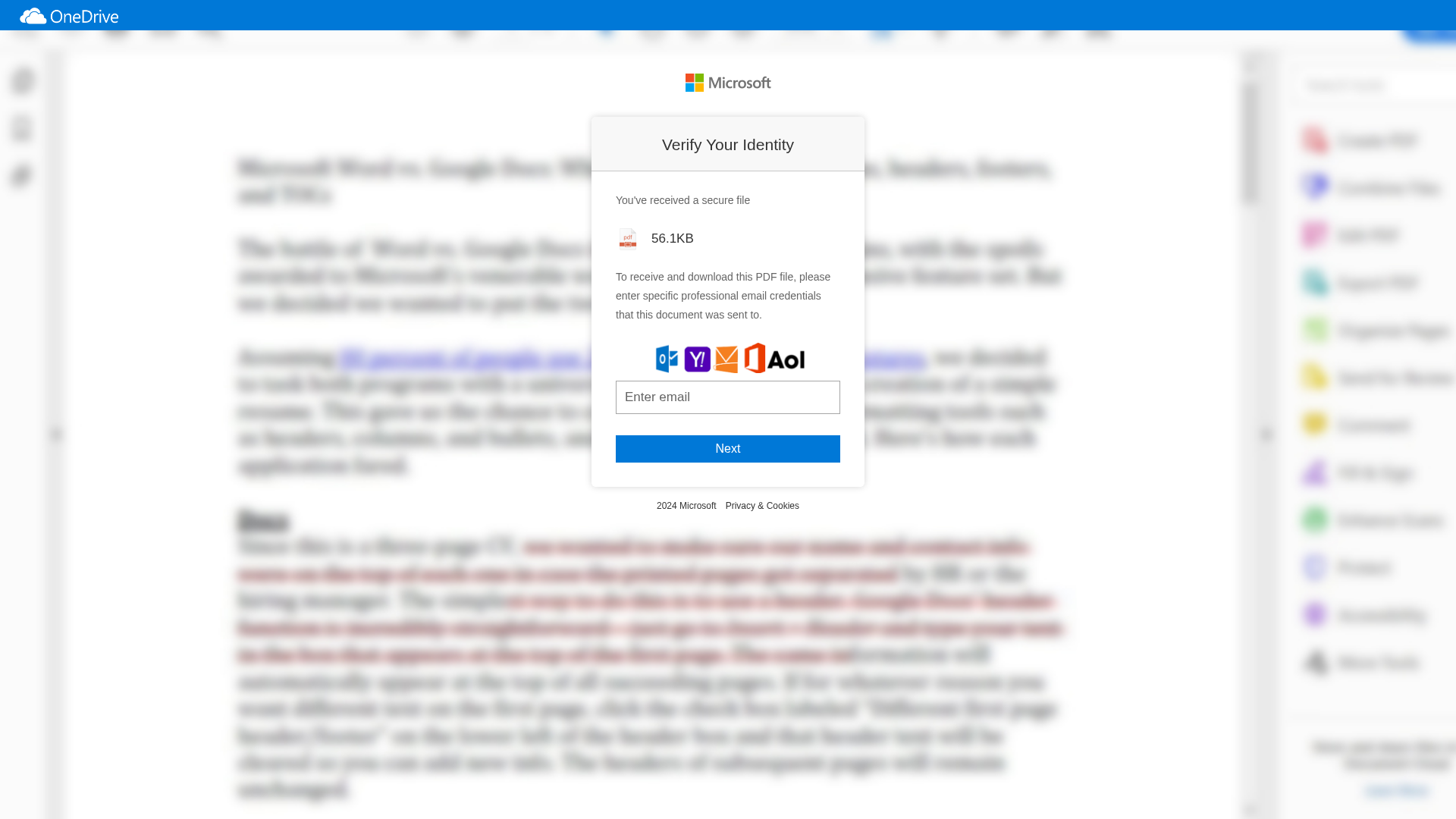
Phishing Analysis
Detailed analysis of captured phishing page
Visual Capture
Detection Info
https://harlequin-tandie-40.tiiny.site/
Detected Brand
Microsoft
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
e86fae25-c21…
Analyzed
2026-04-07 13:14
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B891B52292009D6384A3C5E8F6E7B61BB280C304D2434905B7F9B36D5FDBD85DEA1662 |
|
CONTENT
ssdeep
|
48:Gu6PpOjHgRwOzjH9NkaEfvN1+J2RGOTVNn0KpWK6YnNQOVBSo5MeYoRnND2e6kFg:GusMjHsnjHAOwVxx6mBS3eYltxvo8D |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b44b4163433d4d77 |
|
VISUAL
aHash
|
00ffdf87a7838387 |
|
VISUAL
dHash
|
882c362e2e262626 |
|
VISUAL
wHash
|
00ff9f8b87838387 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
882c362e2c262626,00004040404085ca |
Code Analysis
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Personal Info
Telegram Exfiltration
🔒 Obfuscation Detected
- fromCharCode
- base64_strings
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAABpgAAAFTCAYAAAAtLw+hAAAAAXNSR0IB2cksfwAAAAlwSFlzAAAk6QAAJOkBUCTn+AAECbtJREFUeJzsnQdUE2kXhgMkhGLvrnXVVVdXV0VRUARBUbEXLKuuHSv2gj3q2tvaRexdLKgo2LHQxYKVZJKAogiZ9I76+/3zTSYhoKJbg+59znnPJCGByUwyxnly72WxAAAAAAAAiiBCodjuT0WUbomtnwPw98DsV3uRKN1BJM5gU7FnAvsY+K9jx+Px7GNiYthPnjxxjI+Pd3748GGx+/fvF4uJETqnpNzlbt68xUEkFNsLCZGdJcIvC/U4S2z9RAEA+PPE8HzY6bxhTpKt44vJeINKKHg9S2XzelVQLx1cT7N6tLd6/YShmtVjllLXw1Vze91VzegkUc3uIlfzBsq164NJ/f5liYZzYWHGK8cmGi4f8lOf3lJXHcorh39fFi/IBf/ulNAgTnh4oAP15+B4AQAAAAAAAAAAYEvE4nS7L08GHVuvMwB8Cfi1KhJZJ/2TEeITon8monTr5P+9+O8zgfdN0QbvI6H16wDLJVE6m1pyhKalA97Htl5PALAxtGAKDw93IAiCm5KS4vL06dPijx49LpGQkO567949p7Nnz3JEQrGDkBDZWyL8smAxZYlIbPfp5D/WwmcUACg68Hgse+W2kNLyUF51zdZZPyrWjW2q+u1Xd/mCAV7qxQO7qZf9Okq1fPhiFW/QQVVI90TlFL9s5cS2SDm5HVLN7oY0y4Yi3daZmYZDqy8Zz2xfT2WM7vi6AP0unrtmy+yGqq0hdWR7fqumOb2mgvxKeMnM+HBnfEyy9fMGAAAAAAAAAAD4z5H/pEy6/Zclw958AkcEFRv/CuL053Y46Rkv6CWcPPs8WCblvU4z7POS/skI8QlRoZj9h2OSD2YB4ZDv9+ZVvljeN7D/ihZWEtD0OsD70bRfHakll1o60ZdNoskeKtWA/zj49W+HT+aaKpgynR89ekQLpuTk9OKpD1Jdrl69xhUJxRwhIWLTEX55qMeZQx1L6dh/PPmP3x/7jCKG9yoA2AT5yqCSmu1zf9Lu5XXShi34Vbt56mT1iuFzVIsCF6vm9lqvnN1tj2pWwHnlJN8UeZB7lmJoo//JBzdA1BIpx7REqmn+SMMb+EazdoJQu2P2Vd2ueXu1O+cu124PmarePnOEJnReoPbAyo76c9ta5V4Nb6BPvlRNcT+mFBEVxbX1cwcAAAAAAAAAAPjPYP4G8JeLpXwnb+iYvjlsahNm6+fzLYK3K72P0p/b46RnvKCX5m1PwHb/AIIQMd9ut36dfpFgwlKBQ8XxD8ckH8wCgi2ylkz5BVO+9w68b2yPVZUZ3kd5FUvUfqXeX07U68mZWuJwqXCoOMD7DgBMVUwpKSmcmJh0J9we7+7du8XjCGGxO8kpzjExN5yEhMjREuGXR0S995hwqGM5+9OSqVDBZAr+GW53Sf27YOsNBgD/FbKCurlo1o5poNke0ke7a/4cTeicHZoNwRGq3wZfVc3uHqeY4ndXPrb1E/mIZhnyX+qT0t7VjbLulZC0W3kk61EJyQNrIsWvPyHlWE+knNpRo57X96V66eBH6uXDb6lXjzmt3jBpt3bb7DXag8tm605vGZF75XAPQ2J0m9x7txroU2OqKmIiSqWEhnJsvR0AAAAAAAAAAAC+ScwyyCQu6BM0DmJxOpuKw5cnwxLTiXRzqzDrOQrmv5H+zVY50YIAb0/rWM3lIQqGEFkiyIs9HYHww9AthcTWM2DY4vTnbPNlfDv1e6n7feSxdETm2OFY//3C5gkVlf1lFjCfSr7tKRDSIahtQV1nvvVObS8xHXzZKumfzN8smByYfWcJ876h14v5e/bWz8P69VJU98u3BiOYzO8xjsi0Dx2tBZPAFC4VDhUHAZysBgCMHZ7DhNvkxcaKXRITxcXS0tJck5Pv/BOC6SPJf/z+yGcUthgfj02t+hwI6t9Fgv53wjwTCo6rAPB3ktXtO5esILdy8tk9GqlXjOil2TBxgeb3yUfUa8cnqH8bmq4M6SlXTGinkw93y5X/Uv+NrHe1d9KAsu/JDq6IbMel4ohIXyck7VgSybpVRPI+NZFiUAOkGNH8f/JxbQ3KqR1lyjm9RaolQ1I0a8Zd0m4POaQ/uHydIWLbHMPlI6Ny4871MCRd9MqNO/+T/lp4FXl4aEkiahMXWucBAAAAAAAAAAD8DZjb4DFtwKxbgeETOPRJHLFYbD5BU1gFE30fkekkOid/qzCRQ17o32/dKoyRTXmzcKzbhX1xmFZxOIU+X6v7icXmfPnfKWxOj1XshViuiajnao4wL0TB4BNcTASEiJ0vAuGHoW6n7suxFhgicUaezMAnwOkT3h95LB2RdfL9fev1LJh8+0ucP39qn/2V7VvIeubbnsxzJggc84lKanuJ6LAZufQlFUxsRjL9sZikhHlOz6cqmMzvG3q9zPvP+nlYv14KPN9876P874m8/FvHk28FZns6CM1SidkvzBJXK+F9xGXkkiPzfrUHwQQANLRgwm3yCIJwukkQLo8ePXK+efMmlzoWY7HEsUT45aHFkinsP1HBZP0ZhRZVWHARAiEOm46pbZ/l3ztoWwoAf510H5YT2b9WXekYLz9lSPcg9aL+K9S8ASeU8wNTlLO6ZSsndXirGOWJ5IMaI2nvWkjapSIiO5RApA8XSdrYIdKTZUprKl5sJG3njKTtSyBpp3JI2q0qkvWpg+S/NEbyES1zlRN9pcqZ3YXqxYPvaNdOuKgNnXNUd2jNVsPZ7Txj1P5g/aVD/Q0XD7fTXDrwk/7S0Wp0RVMKVDQBAAAAAAAAAAD8aaznK+U/iU6fiOfS3xg2SSb6JI7VTKaPxZ45eW5V6UH/HqsTRJYT72xRwZPtVq3KxOI/EaZVHA5ua/WxWSgik4jKu6/YnC//O4XN6cknJER4TgsdDh0r6UAUjEkm4DgK8mI6eS0QfjTMyW0nupLCOtRtAlM++ViBQGSOIw7+u+Z1KESWFJAj+fOn9tlf2b6FCJ9821MgNAc/d1NbM2r7CPH8HCF+reLnlGElOP+40Co0zOwlJnkyKG+2j53QLDJwqzW8T03hWvZLgdeL9T4puF/yvyfygiWgLY4xXyPmfS7Km7WE31tcpnKJ3u4ETp4IdgC5BAD5sMxhwoKJinNiYqJjVFQ0dVwW0lVDlgi/PPTsJXPyhJLdh8k7fn/wGcU0/4lL4H8PBEJnZsmlRRP9JQT68wvHVPlkOZ7CexsA/iSyzmWqkoN+6KoY12a+ckbnw8qZna4rgts9Voxyz5EPbvRGFlgfSbt/j6SdKiPSrzSSeLsiSRsOkniykKQVlZYsRLYyXcZL0hNLJzYiW3ORpC2ucCqFSP+KSNqtOpIF1nknG9xIoxzjma2c3kmoXtDvoXpVUJx2+6xI3f7f9umPrVulP719kj5yT1/D1aNeufGR9bWPrlbMjI93tvV2AgAAAAAAAAAA+Oqwkkt0KzwsfMxtwEwnt4Wmbxrjbw2L6NZihVcG0VVQ9El1DnNinP49+VvciK1P3uRvF2bVqsy61d4XJ/25JbgqBJ/MN5/wFTAtxkQmEZV3X7E5X/53PtVCrWCs5JIjHau2aUTBWG0vQZ4gMrXfEgg/GT5e5rXpstyfX8hjTBGZ44RFk5XMKKzdGyffcxTnz5/aZ39l+xbSsi7f9hQInZjg5+7CxNn0nPHvSLf/3HtF9JmWfIWGbpeYF9FHxCd+rTKikWu1rnmSqcDrxXqfWAkmphWU9XsiL1gCCj/zHgas5JLpeOhIMNJPkLcvTO0LmVaMVi0tYdsCQB60YMJzmLBkevr0KTc2No6zZ89eB+pzhakNnaUd3ZcHz0yyhJFJX7pCls8oWNrjLxzwCWcqLjgW0WT58oGYrnAVM61UmS8/wHscAAqBx2LZp7ixOERnFpeoY8rzNqzSkoBSbeX964bIg9zPKSZ4iRRB7qRs0I8aaffv3pAdSiGJd3Ekae2CJB5OSNKKg3Ja2ZvEkgcLkR6MVDIvW5oicafSgoVy3O2psKn7OyJJG2dEtnNFUv/S72U9q7yRDairl49srlZO9iVV8/qINctH3NP+Pvmidtei3brDa3i6c2FBxmvHu+kTLrQ0psbW06Xd+06Rfr9UZma8Mz5u4Vly1NOC9z0AAAAAAAAAAMDHYL7Vy8gl3AIvncNUHnHyTtALHRnBxBaJRPZfKJjshaZv9nPyhMVnBdPfVcFEz1XAs1JwKzJ8wt6quoCuOKBblOFZKqaZRWbB9E9WMP1RwZRXuWQWTXmC5IPwC0lhj2PEkpO5isn673+BYCoqFUxfIpjMlUvW4sYsb6if4wqgzwumfxpGMLGt1teJqVJz/AOCqWAFE/N+oN7bYtzmja52ciCEIjzbiY6QMM9IE1u1qkz/z7WEshKA9kw1mUUuCZiKMkFeNRneXv+p7QMAfwI7fHIWt8kzSya8xNetTtr+q+8jy2cU/HkAV7XyCSdGMuVVMdFfijEdX/FnIquwmS/QwPsfAD5COIvlkNO9QkVZj+oNpD2qtszpVMYjx9vZQ9rOyU/asfREaZ8aB2VDGvLlQ39+Lx9YF0m7VUCkjxMtknLcqDRjgi+3MFUt0YLJ0ypWkgnLJUnzDx+LxRNd4eTDRdJOpZGsZxUkH1AXKUa45Son+EpVs3oK1EuH3tZsmBSu2Tl3k+7g6rm6iNAg3DrPGHsm4O3dq15vHsQ3NabdqacnUqsqH94uTURFcW29fQEAAAAAAAAAAIoU5m/om2YR0DMMzLOWzG3sGEFkmltDt6URib7oJDwjmMxzY5g5QSJ2XixzmRzyyYq/QzDh6hcsj0QZeMYOF7eLs5qPQksbus2VKJ3LSCaHvBZ5Xy6ZvlCAWM9fYjMn9y0hCsa0rdimuUmWmFrl5bV4+yD8QlLY48yt8ahwcBghaJo/IRR/Kvn3l20Fk/WssA+Sb3sKhObk2wamn+PfYftvpWO5wcziYluta95+KfB6sd4n1vvlw/cDfWIUC04u3X5PiGXVR/d1vvej2GqOk623zT+NpQWiWSyZWuJxGbmUb8YSMwvrm98mAPA3QAsk6yomc/B1fDsjmv5VGMHkgOctCfiEozlMezxmJpTlsxD+XOTIVDSZxZP5uAvHAQCw4nmXkqVzenznKQ2sOUzas8Z8smsFHtm+GE/q7bic9HU9TAaUSyF7VtVIe1VD0q7lEenrTAskCRZETZk0M12XFBRMrZlYSSZzBZPELJgKPh7fz8uB/jvSjqWRrPt3SNan9nvZ4MZq+ajWLxRT/B8oQ3rGqJcMiVCvn7BPsyNkq/7gitWGk1vnGaMPjc+NvzDQeO92+9xHtxrrbl2sTGzaBJIJAAAAAAAAAABAlG+mDD2/gM3MRnIUiSwnVUztnwhzlYPQnm5LI/qy9k+4ykloah2VVyUhtM7HKyZMyZuDY32C+0sjssyxScetz+h2cXymXRzfqp0cFk/0SWTLfIXndqZ88d/5ouB2ZEJ8Msscq+dOFIzV9mIqrvIiEH4y/EJS2OMEApF17PPvL/Enk+85ivPnz+yzv7R9C1nPfNvzE9vA9POic5KQabmG19e8znnPo8DrpcDzzVd5ZLUd7ZnZX+a5TtTr31y59UG1Wr6KwgLCz+5bPZlq9Xqijx1MhZgTIaTbTdJVZHws/ExyyR7kEgD8IT6oYoqJSXeKiiK45mom1r9cxUR/RsEtc/Fxlk84mEOY/k1gZkLh46rlCzK4VTB9/KQuOzGV2ByQTACQB65eyg4o3YjsWTVI1rdGmLx3tZuyrhXipX7F4sm27CTSi5Mm8XYhSd9i70m/4ohs54TINkwbvBZWcWfEkrklnrVcspZMjGgyz2eiH2cd5nfQM5xa2yGJFweRPs6I9C2BpB3K/I/sUlkv611dJhvwwyv5sMYi+bg2TxUzOqWqFg1I0qwZd0W/c/4R48nNvxuvHp+eGxfZV3/7ZEvDqS01stcMcbX1tgYAAAAAAAAAALApVrNFLJVLppMlQusqI5u3C/uzMG3TcFUKbvuGhZILk3yX6ZZX+ASRSTDBCSLgm4Sp8mJ/cq7TpwWTeYYT23wbfcKVwCdmxd+UbLI6JtKVS3TVo1DswshpJ6YaELfZ/GqPiwBgYyxVTARBcOPj451xsGTCwgn/jJXXLq/IHFuEplaiuIrbUSAgnExz+4Qu1O3OTDUTSCbgP0eMjw87e0hj18zAqmVwO7xMX+cqr9o6V5P6F68v61ImUNqj0iZZr6rJsp7faaQB5Yxkexcj6eWQS3qy3kpasd5LPO2RxNMOSQqIIsvlgjKpzSdS8H4F5RMtlhjB5MEEC6dWdqZ4OFC/x+E96c35H+lf7J20W8W3sgF13shHNNOpJrfPUS/q/0S7cep13aFV+wxnQxdpz20fpt23wl+xbmxT5czOtWWjfKqSU7wqv54TWF6xYUqp7ANrXJ+EhzvaoioTAAAAAAAAAADgX8P8LX1mhoClcsm0NLXBY6qMvtqTJea2aQQhxm3fuJ+YTUS3u2LmMdmDYAK+VZjKIwemTaB5tpO5eolDWFpBWeY4WQQTc9l6nhVHSFjmj3wzw+6t5nk5Mi01nfmEyIUvENHHCly9xMeVDsTXe1wEAFtjrmIyVzClpKS4YMlE3eZkui2GbauWeZ8CfxZiqrip4yfB5eNZTQLCBUsmXM2Eq0KtJVNRaLUKAP8kKUFunOwZ/hVkY7waSAY38CK7Vewq6ViyH+nvOojsWHy0LKD0arJr2avSrhUksi7lkLRTSST1dUakl72ppV3L/BVGtFgyiyGvAvmUWCqYgo+zemw+wWQ1s0nSjIkbcx1XS7V1QKR/cSTrXgnJB9ZDijGtNKqZXTLUK4YnaDZPPanZOmOzZv24hSpe4ETF1I7DVcHeAxXTO/dULhvWQR/Ga6U5s6eBPj6yiiwxqkRROo4BAAAAAAAAAAD8bVhmjOTNW3Fk5JKjSS4Jv3q5hDG3TcNzdQQCEZs5OVwwbIFppg2eufJVP18AKIy89wPdZpFtDjMfzdQOKm+Gk2X+EnMbh6l0crKueiowi+urrmayku5YnnHpFoJ05SNdvURXLjHtJr/a5wgARQS6VZ65igkLJnPM1UzmuUysIlTFROBWegRuV0qw+XwBV8AXuAj4hCt1THQlBEIXIl8lE3yeAL5deCyWffaMXhUU0zo3lY5v3Vv2y49Tpd0rrSI7lw4lOxY/QHZ0PU52Kn5D2rFEutS/+FupfzEk9XNGpA8HkW3sTO3sPiWYPiOK/pBc+pRgamUlmNysJFMzq3lNbe0RSa2zNKAskvetjmS//qSTj2udpZjW8YliVkCcclrHi8rJ7U4px7c5opzovUc1q9tGzcqRC3Vhi8fpz4b11iecbW1MvPyDKj68THh4oIOt9xkAAAAAAAAAAMDfhnkWC/MtfXpwtakiAVcy4NZ4WC4Jv3q5ZMY0/0lsJxCI7HDlwUdih6sRYJYK8F+AmYdGvR+ElphOmppi+ua9+IPZVkzVE91az/TNfZNkMlc8WbfOI77CY0e+1ni4eklAizRnPh8/XyGXCtt8vLD1ugLANwLdKs+6iik1NdUVB18u0C6vyEB9TqKOm4Q9ny/g8NMETlRc+VgyUTHNZTJLpnSQTMA3AY/Fsg8PZDngiqUngQ0dyRGti8snt6+umtXVXT7Vf4BilPsi+YB6h2XdK92Sdiz5VNreNUPa3uUlFanEl2sgfbkmseTNNlUvmVvXeRRIYS3w/q5Yt85rxaQlI7iY0BVMnsz9cSWTrxOSdiyOpAFl3kt7Vskl+36vkQ2oI5f98kOOfFD9LPnQnzOVYzyFqhldUtTLh13QbA8JM5zYvMhwNXyk8fbZTm+uHWuG5zUpNvBKEcHB3BieDzs8MNBcoQnHCAAAAAAAAAAAvi6wXKJimbnECCam5ZWQQwVXL9nh2HpdAQAoGjCCCVc7OfL5dGsoLF+4lplNhGVuk7nVHl0VJcBVUXhuSRGvDrRUdJrlkmlmGyPT8HMWcqiAXAKAvxc761Z5uHLpE4KpyCEQEHZ8vsCBnyZwpOJMHRPpSia6iskimdItkulbaSEK/LfA85Xks9uXlMwMqKSc2r6WbEzLBorRLZrIx7ZqrZjYtrsy2Hu0fKznMtmQRuHSXtXvkp3K5pB+xd6Svi60lCHbYbHENlUCedl9fl7SPy2XvnRuE70udnnxckASbzYVDpL4cJGknTOinieSdiyFZN0qInlgLaQY9jNSBrdVqeb1EqrXjLmt27UwXH9q0wZ95K5ZhjM7huuOruquDp3dRrFhfBPNhvE/KjfP+F53cENl5fnDpbMiI13wcdDW+xsAAAAAAAAAAOCzmOWSWJwnl6wrl3DbFxyQSwAAWMNUPdFt9fh8gkMFz2/iCOjjhrkCUuRECETO1G3m6iZHgZCebcYRiuj5ZkXy2/wfyCUhI5dMVUuOdOUSX+hApcitOwB8A+RrlYclk7lNXlEWTBg+X2DPTxOwGcmEK5mcBXw8k0nkQh8PrSSTSJQB8x2Br46s6T7lpLN6/Sif08NLMd2/p2Jim+GK0e7B8lHN5ilGNF2nGPbzXtkvP0bJelVLJTuVl5Dtir0nvZ0R2ZaLSC8OtWTniSVby6Q/I52YKiuJR97cphx3U+iKp9YOiGzngmQB5ZCsbw2kGNoIKSa00Sln98hULxuaqtk49boudO5J7c55u7RbZ67VbZwyT7M+eKJq07Rf1WELexhObPLSXjnUyBB7pbry4e3SRFQU19b7HAAAAAAAAAAA4KMwYomJWS5Z2uJxrOQSni0AJ0AAAPgApq2ePZ9P2FNLLJvs6RD0HCdHUzs5wpUvoONCiyYhc5JVJHYUikwnWgmmZaWtnw9GxLQLNc+ho+dLmWZMcZmqJTZduQRyCQD+SehWeWbJhNvlMS3zOEVZMAn4dBUTlky4kolDiyZTdaczHULsjKshsWQSiTIczJ/DbL3eAPA5eHi+0ljPCoopHZooZnXvrpzdZZxyaodlinEeuxTDfj6pGFTvqqzf98nSXtWeSrtWfC7tUFJOtnV+Q7Z2RBIPNhUHJPG0R5LWdvllTVGXSwUlE9O6j57X1NI0mymnORU3ZnaTO35eDkjq44SknUoiWc/KSP7LD0g+3M2gmOAlV87o8lI1r49QvWjAI9XiwYmaZUMva1aNDtdsCN6hCZu/RHds/Xh91KG+hvhz3rmpMT/pk29WU94+XzolNJRj69cAAAAAAAAAAABAPqwEE65eYtMD7IX55BKbir2t1xMAgK8PWjbRMoZwTksTuKTx6XkkZsHkTAjFzkKR2EkoSqdPtFLXHQhCbG+a9WS7iiZaLpnaheZVLhEiJ35eWzxaLtlq/QDgP4ZFMuHKJRwrwWRnlSIJP82qmsksmehKJurYJ0x3FIkyOKbPYCCYgKJLlhvL5XXnSuUlv/z4gzyoZRv5BJ8B8sntQ5QT/bbKx7U5pxje7I58YF2RvHdVqbRreb3Uv/hbsp3TO7K1w3uJhz2StLRDEnc7k4xpZar6+arEUkHB5GmKxFoyuZtEEx1LJZMdPV9K2t4FSbuUQbKeVZEssNZ7+eAG/1OMcHurCPLIpbalRjWtS7ZqbiBfvWxYgmbjlDO6PUu3GU5uW2i8fGRM7u3IXobkS21zb55ppI86VFURsbdUZvh6ZyybmFlNAAAAAAAAAAAAtsNqeL0DFQ4jmMxiCVcu2UPlEgAAfwa6iomWMQQ3LU3glMan55E4CQihE65gEhBYMolcsGjCJ1sFBD3jiC0U0sckKv/+t/rNckmYXy5x+SbBxLXMXILKJQD4N8knmfASB88mwbcX5ZOs/DSBnUUymVqI0pKJmcfkRB3rHKnjHBtLJluvKwB8jEwPljPZqVw9aZ/q7aWD6g+VD2syUzbMbZ1sSLOj8kFNYqQDf3om7/sDKeteJVfauQyS+rkisi0HkZ52iDTLl5Z50uWbEkzWkukjzxU/f/q+eF6TjyMifYshskNJRG1PJO36HZL2rIlk/eoj+a/NkGJMa71qasds9aL+TzRrxsbgFnq6I2t26CLDluijD0zSRx8cqI0+5Ke9sLeJ8fyeWtoL4ZXkV8JLQvs8AAAAAAAAAABsxqflkgjkEgAAfxmBQGgnoGUMwU5LE3DS+PQ3+Dl4RhOfEDrSlUyE0JUvELoKBCIXWjgRYkehEFdTWmaT/Gvf7M8nl0TpWC45Ma3xuNQ6OvIFMHMJAGwEPY8JCyWzZMIt8z5SzVQksUgm6liIJROflkz08c6ZOt5xxeJ0XMXkAFVMQFEkq41zdbJzuW7S3jXmy/vX2S/v/0OkrHetm2TXGqnSTlUyyA6VFdIO5d5J/Uoi0scZkV5sk1RpZYrEOuaZRdZy6WsSTNaSyUo0mVvmFXy+5m1AMs9Z4umAJK3ZVByRxMsFSbxLINKvLJJ2/g7JetVC8sE/vVGM8ZQrZgQ8Vy/55bFm/fh4bejc89oDS/frj65Zoz25ZZo2YsdAbdQ+f93VYy2Mty/U1aXcqiwjEksU5bahAAAAAAAAAAB8o5jaUIktM0ZMsQgmkEsAAPxlBHyhHZ9P2KXx6ZOr9nwBPafJnk8I2dRlLp7JlIbnM/GxaKLbRjFzSejZJGzmpOs/LpksbfHEGVguccxt8ZjWeCa5hNdbAMdFALAR+aqYzPOYzJKpKFcxYfhpeC4TYZZMXFzJ9LEqJpBMwL+EXXhgoEMMz4edEuTGeRLY0JHozOISdfInsyGrzGsfJx9JQNk50p5VI6V9qhNkt++ypR3KysjWxdQ5rZwMkpbcd2QrR0TiGUue9tTSLk+4eFhJmIJS6WsTS5+TTQWlk7V8Mksnd1Ny8MymFnZUHKjrHCTxcEKktyuSdiyDZL2qvZMNaWiQj/PUqKb7S1UL+qVrlg+/r1kffEW7c/5+7YGVK/QnN081nN8z2Hj9eIA+Iap17oPYhnoisary+cPS6ekxTiCbAAAAAAAAAAD4VyhEMDmAXAIA4J+ET2BZQ3CoOKXxCRc+X+jCF1gqmDgiKnmiKZ0+8YqrLv+JdcGt+Bi5hKumOEz1Et0ajwqWSxyQSwBgcyxVTNaCCVcymdvl4Z/jmNvmMdKpyLxvsWxnJBOu5HSkPm9xqc9eXEYw0VVMuLLc1usJfNPYZR+Y4ao5vb2C4fDaGurNE+vLZ3RvTA5t5ibtUbVljp+zR44nyyOnqSnZLVh+Em/uJNK/1CFplwoCKu+l/mUQ6eWMJM3tUE4TFh2JGzN7yNwWzroFnq0lkK0FFCOZLIIJy6XmVKhtltOMSlPTEt9OtnZApJ8rknatgGSBNZF8cAOkGOmeqwz2lSlndhOpFg1KUK8ef0a9edYu7a4lq7TH1ofozu8Zp792cqAx8bK/7v6NFsa0O/V0T1Mqy1NSSj4JD3e09QsOAAAAAAAAAIBvGCyYCKHIniBoqcRl4giCCQCAfxo+dYzhCwgHLJnScMsovpDLF4gcBdTxiDo2cUzCO91y8hVLpr/7xCstlkzB857YOIxcwuthDq5ccgC5BABFgnySydwmz3ouk/WcJrN0YhU9yeQgEAjZuF0o/tyFj3dmmc60LS4y6wt8W5CrRhRXHl5RS38qrJXu6IYu2o3Thyjn9BknG+U2XdqnyjyyfbFFOW3seTnuLF5OMxYvuwVrRU4bzhFJO5e7ZIeSWmmHEqY2eB72tFQqVDAVlEteRUD42FAyWWY0MZKJ3mZmwdSUuY5/hu/vw0Ukta2lncshWfeqSNa3DpINbKSVj2j1Sj7B94lyercE1fwBl9Qrg05pt8w4oNu/fLPh9LaFxstHx+YmXuzzNjXWK/dRwo+auEsViE2bYEYTAAAAAAAAAAD/DEIRLZgcCPokKj10GofLnPSAkxsAAPyj8AUElkz2aXwsmoQOAoHIQUDQ0ttBSItv0wwkcwspkUjswMyO+8vHJ9PvscglByFTMYXlEq6iwqKLCr0+fBDuAFCUoFvlmecxWUslnCiC4OLKpqgok3wqivOZsGTCrUKpOJjaEosYqU5XlDvg6nJbryPw7UGOaF1cvWpcPe3+Fe11JzeN0B1avVCzYfI25ezuR+XDm16Q9qp6Q9qhWJzEyyE+pwUrPqc5K17SgpUsaWXPz2nNlpLeXER6OyKyjYNJmJhFCSOWJNaVS1C9lF8wWVUyWdrltcxrmUdvQ3erOVWt7RC1HxDZltre3i6I9C2BpL6l35P+lQzSbtWU0t61c2S/NHqhCPIUqqZ3eaZaPChZu3FStHbfkr26szuWG2+cGm9MiO6uiz3b3HBqS43sNTNcbf36AwAAAAAAABiuC1UOp1JljqFxOS6rrmaVmHc+s/TY8PQKgfsE33UMfVatU+jTqgMP8ivPuZBRdldydrErfIVj0gsN/CcRKJIIRWJ7Qkif2OAKCKGzQEAHBBMAADaFwJJJIOIIBCLznBInUyWTmMN8u9+eafFp92eEE/MYWiwxYQuF6bhiCsslLLbMcgmOgwBQNLEzt8IziyZruRQfH+9MSyb6egzbSjJ9LDYDf9YyVY1bBBOHkUzwfwfgL5ESFMTJnjHEVRnSpXT2WM8KsuEtqimC2zdVLx3aXbNlxiTtbt463dbZJ9TLhsYqJ3d4Jh/cMEvavaKK9HMxSLzsjTmtWMacFnRyJa1YbyUtWe9JTztEtrb7cN7QtzZX6d+QTZ+a20RdlngyksncVo+WUXZI0oKKuz113QFJWju+J/2Kv5N2r/xOPrD+W/mYVirlrC7PVcuGJWu3zT6nP7Z2qyEyLMRwdsdg7cFlHRTrxjZVhXSvIwv2qUpO6VhZzRtYTh46u2RWaKhLTAyPbevXKwAAAAAAwH+C2+lqu5SXOufYdHWZc4/kVfYkSn5Yd/11k4VRL1tPPJnRccB+om/nnc8GB4Q9/WXQYUHPuVHP2+5Ozq5/RaAol5ypcbr7SgMnqYAiA65cYuJACOmWeM4CAs8/IXCcmLko8JoFAMAmUMckOwJXM9GSSWiWTFyhkJ5XYn0S1sEkitLtxeIMu88n3S5PLtGiim2uXGIEE5ZLbCp05ZKttwMAAIViZz1zqaBkMgsmc6s8s4wyxzyniWVjyQSCCfi7SQly42jWjK2gXjuxvnrJQA/VpI6dZEEegfJxbSYoZ3T+Tbmw/x7Nb79eVC/s/0A1tWOWfKSbTh74PZIGlEFSXydEetnnyY2Wect8s5WwLPEqEFvLm68pBbed1fazCKaC7fRwK8KfmWUzZp94OyJp59JI1qc6kg/96Y1yQpscVUjPp5oVI2M0Gycf1Wye+rtmTdACFa//RMWMgOGqKR0GKmb17KldNsZPt3dJC2Pk3h80t6LKp8fEONn6dQsAAAAAAPBNc+SelHNLrC59J1NbjVo2PPtI3np3giRg7fXXQxZceBk84UT6kv77Bds673x2sHPY032DDgnWz416Pml3cnanKwLFD8mZmpJ3X0IVE1A0sJJL9lQ4hFDkJCCErnwB4crn03HCw6dx+xZbrysAAP9dCIHInm6ZJxCy8XwmUzUTdbyiQhBiLjO3xDKzRCzOsP+SmOWSUGiRS9aVS1gu2eNA9RIAfBXQVUhmyWQtmqxnM1lfj2LmNuHbi0L7PIKwzMK0HNNAMAF/AbucuQMrKldPaKZeP6mHaumQCYqp/kvlI1tsUwz9OVwxrOlVxSj3FGWQh1Axyo2UD/7RKOtTA0m7lkPSDq6I9OEg0ssur6LGwxSJR97lTwomkEx/Xi5ZC6bWrPyCDwum5lSaMnKpCXO5ObNfqH0m9S+OpN0rIlm/79/Ih/wklwe1zFAEe6eqJre/rZzc7qJyYttTygneR5WT2+9Rzem1UbN23HzdniWjjGd3dXkTH9VU/yC+SlZKioutX7wAAAAAAABfFTvis+3W3siyX3L5pUPI+efsSafT2cOOCjm99qQ5+u946tgx9Cn3l0MC13nRL8rvTpLUikpTNLkuVHlHPVP0PHyXHLn51utZSy+9XDvz7PP9I4+KL/fczX/ou+3pC7/tT9L77efHzYrM2LkzKTvoEl/hnvRCUzHlpYZj6+cMABgrucSm4kgI6eolWjCl8QUuVJyocKjAyVUAAGwGrmISCET0nBI+X8ih4kjFiYozdbsz0zbP0UowfVGYyiVGMNFSyZEJXblExQ7H1s8fAIA/hKXlnXXrPOv2eYRVZROOeT4TU8UEAF8zduGBLIf0YTWdpGN9q6gW9GmpXTFqoGb1mPlq3qDdykl+V+S/Nk6V9f3+uax7ZVLWrYJS2rWCXhpQ5q20Uykk7VAMkX5OJrnU1t4kOj7Vyg3a4P3zKdg2zyz2cMWSeWYTFbqiDP+8rZ1p3/k5I2nH4kjaueQ7MqCcgexWUS3rWUUm610jRz6wbpZ8eJNM5QQvoSqkR4p2ZdA53Y55W/XHN83OvXq0/9vE6DbG+zd/UCddLUtERXFZRaCFKAAAAAAAQJEkIUPDvpimcDr+QFpiV2JOud9vvf5u+dVXNeZHvagz7UzGj6PDxY367Rc07RKW1iIg7FmrAQcFXlPPZvivicnqvSdZMuzgPTJ4V5JkwfobWRsWRmfunxKRETXymCipz15Bhs/WJ4YW6x8i998foi5hT7MmnRaf3xr3ek7UM7lvfIa6etILtVNcugo+pAE2p4Bg4jKCiW6Pl8YXOFNxpMIGwQQAQFEAzyjh84UOjGTiYslkqmIytcv7axVMpnlLTBxALAHAN8EHoqmgZDJXMYFgAr52eDyWvXx2+5Lyye2rK8a0+Vk1yaeTMqR7kHpRv2Ua3oAjqpld4xVBHs9l/WrrpF3KI9LXFZFebHqWksQii+xMVUs4tpYrkM+Lp4KSz7zvcGtDHGp/0m326EozeyRt54xkAWWRvF9tpBjphpST26vUi/rzNevGXdeHzjugO7bmN2Nk2ITcq8d76uLOtTCkXKkuS4wqIYmJKWbr1zcAAAAAAECR4lm23inpuabMZb6y6slUWb09yZLmm2KzvVdezwpYGJ0ZOOPs81/HnhCPGXSImNJzD392111pC3rv4y8Zdky4anJE+sa5US/C5l/MPDzz/POzE06Jrw89QiT33c/nB4Q9e91602Njg1X3Ua2ld1GdZfdQm02P1COOCWPW3Xy19OxjeZdbYlWd+Ax1sVsiFfwHFrA55tlLuD2eSTDhk7X03CWulVxyAMEEAEBRgc+nq5jMkslRIKBnx9GzSpiKpC+SS1aCyV4oxJKJlkrm2INgAoBvinwzmqxFEw6+bv65rVcUAP4smVMDndXzA+uppnfqqBzXJkg51vM31cS2+5ST/aKVk3zvKUa3fKUYWD9X1q0ikvq6IomnXd5MHzdT+zVLJUxBeQFt74p+rKqdLHObqH2a05QK00oPVz2RPlwk61IeyfrXQYqRzZAyuJ1GNbt7upo34I529cgL2q3TDur3L11pOBM6ynDzVFtDQnRNfWJMVVu/vgEAAAAAAGzOmUdy+/gMjcujLF2Z1Fe66rFidaPzTxVtjtyTdg1NyBmy7ubr4KVXXs2fc+HF6skRGTtGHxcdGnhQcKbH7rQrnUKf3e6481lCQNizO9T1+7338R/32stP67orTdxhx9OXXlseke4bH6p/Xvsgt/aye6js/GRUcnYiKj03Cf208r6i/37+9eVXM5edTJX1iBGqfrydrioZI1TCf2ABmyMUiuyoOFDhUOESBJ5tQjjyBYRZLNmDXAIAoCjB59NVTHZm0YRnMxEEPo6JsSyywxGLM74o5vsLhTimeUvQFg8Avmk+mNOE5ZLV/CV47wNfLeSywZWVcwM7KKe0nyELarVPPrzJDfmvjZ7Kf/3pueKXH2XyvjWNsq7lkdTPFZFt2CYBgcVSswKCyaOQChlI0Y1VKz3LzKbmVoKpCTOrydOeeg24IGmXckjWtzpSDKr/nnqt6JSj3EjFOI8M1fSOaZqlv1zT7ZyzSXtu5zBdXHQLbWJ0Y1u/vgEAAAAAAP4xrgpUdtHPlPaRj+UOJ1OlnIN3JdxtCa+dV8W8LLb0SmaJ5Vdfltoa97p8+ANptasCZf24dLXbLZHa98JTRd+j96WjQhNyZq69kbWSd+ll6MzIF8cnnEq/OPyoKGHAAeJxj91pz/23P5W23fxY5/H7I2OL9am5bmtTc5usTX3TePWDtw1W3X9Xd8W9/9ValvK+2tIUVJl3B5Wam4QcpsUh++BY5DA1Hn2/OOV1j7BnFxdffLH0+H1pz2sCZcNbIlVpal0cbL3tAKCAYHIkCCFHICDYfAEBAhQAAAAAAAAAiiA8Fss+xofFTgly4zwJDHTM4nVzkc3u01AxI2C4fHybnfIhje/K+/9AyntVfyvrUfmdLKDce6l/CST15dLt00irChc6uLKlJSOXClYwgWD6OmK1v+gKplYF9nFzZon3sZcDIn3xnKYSCEtHWfdKSNal4ntZ10rv5H1qv1UEeWaqfxt2XndkzTzj7dOdDPHnvG39mgcAAAAAAPjbuZuptU9I1zjeFKldrwlUJS8+U5Q5+1he6fgDabXdyTm1N97OarAq5lXTVddftaIu++xOyul67L50wMmH0tFH70tnhiXmrFh/M2vb4ksvD884l3F+7EnxrSFHhLg6Sdh557PsdtueqD03Pvqf29pU1GjFfVTvt3tYFqGqC+6givOTUbl5yajMnCRUikrJOQmoWEgCcpmdgNjT4hBrwi3EGnMTsSbG4vtndg19emFR1Islx+5Je10VKH+i1hkEE1Ak+IhgYgsEuCJACN/gBQAAAAAAAIAiRjiL5ZDV7TsXxbAmpbKCfMqRUzpWVk5tX0s5wbuDYlTLBbKBDaOlPWvlSAMqIWn70oj0LYZIHyeTVGjNSKRWVgKipemyRS6BYPo6Yy2YzG3yPKz2sfW+pmcy2SHSm43IdtRrw9uZuq8jkrTgULcXQ9KetfXKqd0T1DsXrdNfOtpfd+1kN1u/7gEAAAAAAP42hKSB8zhL55qSqS0Tl66pfEOornmFr6ob/VTR6MwjWYtj90mvPck5HTfHZvVZdf3V0GVXX45bdu3ljFXXXy5ZE5O1YU3Mq12/XX15Ys6FF1cmRaQnjDguetDvAF8QEPbshc+2JxL3jY/UjdY8eFNvhWmOUrWFd1DlecmofEgSKjUzAblOi0dOU+OR49Q4xJkSh9jUkj0t1lS1hOVS8G2TXBp9A7HG30ZVFiSbBdNiuoKJwBVM6tLXQDABRQCCENnh1lJ4fgkVPMeETRBCBwEBggkAAAAAAAAAihrZ/hVdJYE1K+UEudWWTWjdUDres4V0aFM/Wf+6o2S9au6Qdq50h2xXVk96FUekpxOSeLKRxMMuTyKZBZNHXkAsfQMpuO/M+5TZ55JWebG8DmgZRb023O1QTiMWyqlH5Sc7RPpUeqMY5XdPtXH2Nu2FvcP0lw71t/XrHgAAAAAA4E9xKlVudylNyU7M0Dg9fq0v/ixbX/5hlq568nNN/VsiddMrfKXn+ScK34iH8oDw+9LeB1Ikg8MSs4M23s6atvLaS97Ciy82zI7M2DXtbPqxSafFUeNPim8FhQvvDT1CEIH7+Vlddz2T+21/om618aGu8ZoHxjrL772tsiTlfdkFd1DJuUnIdVYCcp4ej5ymxCHHyXGIHRyL7CfGIjsqtEjCmcRkcqwpE60E04TbqPrCOy967HwWueRi5qITD6Td8AymWLGm1HVCBYIJsDkfEUwck2QSQYs8AAAAAAC+JezwrKUnT544ZqWkuIhEopKZT56UefksqWz6/ZhSabFni2dFhroQUZu4RFQwl9j0x/IkPNAxhufD5vFY8BkK+Mcg6rC42f4VK0h7/fCjbHgTT9mwZp1kg+r2l/auNl7asfRK0rvYWYknl0+6c3IlzdlI0tze1BaNqV4ptEoJhNK3lY/t34LiyTyvyY2FsutTqUnlBxbK8SivlQ3xvqNaPXW77vTO0Ybz+wfb+rUPAAAAAADwh4hP1zhGP1MUP/NIXibqqfK7GEJVh7qtcXy6ujV1uVPUU3m/U6myYYdSyLG7EiVTt8Zmh6y/kbVo+dWXqxZefL5p1vn0PZNOi0+MPia8+OshQWz/fWn3e+56RnTe8fSV37bHcq9NjwzuGx6in9c8QPVX3Ec1l95FlRaa5ic5hyQihxkJiDUt3iSMgmNpUfRBJjKxSKYCgomKHXXb94tTXvTe9ezcskuZ80+lSgNuClV1qedS4oZQBf/5BGxOAcHEzatiAsEEAAAAAIDt4PF49jExMeyUlFAOERXFzYwPd8bJSol0MV/Gtz8JD3fE98H3Nd/f/Jj0mL1OWSmhLtmXDriSsWeLP394u3TOo8SKzwUPa73kP/75Vdrj1tlPknyz717yJW+Fe8svb28ti97gIYtcXiBLPGSncRZ4yMLnUJnhoS4Q+ckZjRWnpteQh88uGR4eCF8kA/4yKW4sTpYby0XiwyqW3Zjlii8/b8MqndO+ZK2cHjU8pYF1e8kDawdJe1SeJ/UvsUnq5XCSbMlKkjRjvaLyRtKUhahlnmAyt0YDmfTfTgHR9IFgqsNCOa3KyWSDvBNUq6ds053ePtpwdg8IJgAAAAAAvh6evta7pLzQVrySpqwT8VDe9FSqvO3pVHl3KkOO35dN3pcsWbwtNnvj2pisXUsuvTwQEvni2JSIjFNjwsXnhhwhLgXuT7vRfffTxE47nqS22/yIaLP+4Uv3NQ+kP6+4p/1x2b03dZbeRTV5KajqQtMspbJzk1CJkETkPDMBsafHI9bUOMSaEmcSRmaJVJhcwgJqUqyVYKIy9hYde+r31F6a8rzv3rQzK668nBvxUNbxtkhdJzFDU+yWSA0n8AGbIyBE9lTYVBypODGSiQOCCQAAAACAfwssk0zVReGO6ekxTtmpl1xlRGIJ1ZOLZajLFciUi5VliVFV5SmR1RX3LtTAS3wd357z6GrF1/dulc9KiSn38tnVsnhp/RjFvVM1lEnh3+ekRNSWplyqTz687pbzKLZDzqO4ITmpMTOo25ZKE08sl93ct1R2dctiRfQ6niJ6FU92gUr0GmpJJXIFT3Z2GU8RsZinOLWQpzgxl6c6EUJlliXKk7PGKk/M9Fcem1kbVzTZepsCXzcxPiz2687Fyr/uVKlmjm/J2tltnb5/3YpVM7Ml64fXXs7uUr+yPaUBlSZIO5VfLm1ffL/Uy+GKpCXrgaQ564XEjaWWNGW9p+VScyrujEQwVy+BXPpvxsvqsvW8Jg+TYMphBFNOHfx6KSuVD26boFo1davuVOgow3kQTAAAAAAAfAUcvy91ik9Xl7uXqa0dJ1a3OPdY3unAHXLgzvicCZtvZS9cf+P178uvvDoy78KLy1Mi0u+MCRc/HnSIeNZrN1/QMfSp0Gvz43S3DakvGq6+/+qH5Xdzvl98R15tQbLmu7lJhoohSW/LzkpEpWYmouJ4jtL0BORCxWlaPHKkgucoYRlkaXNnzqRCQt8nzpQpcXmX8c/G3aLnL2FhRa1LRr99/IhV116FnH0o70A9t1rJGRrXWJEaZtwANkdACO2pcKhwqTgxS3wdBBMAAAAAAH8VS1s6LI6yslJcyLTY4lgeKZ8/LK1+llRWI4yroBUnVtSlxX4nE96spngWU1P1JKaO+mFMffmj6MbKu+fdVHfPtZKnnG6jSD7trbhzwgcv5SmRbWTU7ar70S2UqRebKe5fbqJ4fPFnxYMrTZV3L7lJUy60pB+TcMJHGX/UTxZ7pIM87mgXefzxgbL4E1PI+OMb5HGHI2S39sUqroclya9sSVReWpegjF4dr4xaES8/v9yUSCrnlsbLI3jxylPz45XhIfGq8BnxquPTqSXOzATVqVlUQg6oTs0OVoXPcs8KDXKx9YYHvl6eNGQ5Zvo6VyG7lHOj0i6ncxn/HB/X9q9bs9vltGC1l7R06Cvx5AZL2jqvzPF2OiJpy74l8WQRZCuWTOLO0lJ5S7fDM8dcuQRyCfKx4NeEO569xLTH+5GFJF7lpfJhbeM0a6dt0p4JG66/sG+grd8XAAAAAAD8xzj3RG53MU3Bjngod9qdKHFddS2rxPwLmaUnnc4o9+thYcUuO9Mqt938pIr3lsdVe+8T1Jh+NqPOtrjsRhGPZJ4XnsgDTqZKh+xMyJm66tqrpQujMrdNP/v8+IRT6VeHHxWl9t8veNlt1zNN++1P33huevS2yZrUt/VW3H9Xbcndd2UXJL8rNjfxf04z499zpsW9Z0+ORQ54bpJ5dlIw0/Iu+FPCiMqUWJMwMmdq/B8Llkx0lVMs4sxMQHVX3svof4B/evX1V7POPZL7xYvVNe8818B/OoEiQQHB5MxIJhBMAAAAAPDvgb90ZGeu4sGJieGxcXCrtyfhPEc8FygzfL1z9qU1rpJwXjHy7KzisiheCRx8Gd+Gf4bvY52sSJ5L3mNW0Y/BLdwUEbxSyvMhpVXhU8uo908oqwkfXl6zh8qBIRXM0YYNrEhnb2AlHF1o78q63d2/w9Fv71pFv6lzVf0mn6qydW2r0dnqX81w4Nfqhgu/1TAkhX9vJOJqG0X3f8hNT6mvIZIbap/dbKR9EtNE9/RaM92jy831Ty611D+M9lA/iG6jTr3opbkf6aN9eL699u6ZjqqUU13UKSd7KhOO9FPFHRqsvr1vuPLW7tFUxipv7RxLL2/sHq2gblfcPjBEFXvgF1XcgQHK2EP9VfEHB8rj9g9W3No9TBmza5TyWug41bWtExWXfp+kvLRhhuLimiXyqFU7lRdWXlaeX04oIn/TqM4uyVWeW2xUnl1IZYFReWa+URkx16g8PceoPDnbqAyfYVQenWJUHphgVO4NMqr2jDSq947IVR8Y+1Z9dNJ79clZSB0x76HqzPz1yoj5/uTuWcVt/aICiiR2ksCGxbLHelaQjafeM8NbVJMNqF3tlX+Zaq/asqq9amHK69ashlJfJ1+yc+lB0i5lx0s6lpks8S4WnOPJGS9pzpogcWfNzmnOWpfTknVE4sHCcklIerBUVN5/cu6OrSUGpOjFi5VX1YQr3H5m5FJj6rpvBVIR1O625vcZGwyRu3/VRx8OtPWbBwAAAACA/xBhSTn20WmKYtcJVfkLT5Q19ieT9dfFvG66KPql57Qzz/1GHBUF9NrD7+W37Wl/n61PBnUJSxsy9Ihw+MzI5+OWXXk5Y8W1l4sXXXyxccqZ9P0jjgnP9D/Aj+m2K+1+hx3PRG23PJG5b3j4rvGaB6jeivuoBp6dtOgOKjUvCTnPTkR2uMUdFkTBTCu7cbcs7eroy+Nu05VFeW3urGSTtWDCbfLMwbOYcKZbZdpH8nnBNPPcI7lvvFhdAwQTUFQAwQQAAAAA/zp2eFYQ3Q4uxtQOjkw7W1yWGFVCcT+ilOpJeBl10umymnvh5bWJRyrq7h39Tp+8p5rx9p5axuvb6uVeX9/wzfWVP+uurGiKo726prGGug3/zBi/qw59P5y40NrG2zvr5t7c+qMmZuNP2uvrTI+5tMJNF72khf4cr5UhcnYbw6lp7YzHg9sbj433Nx4Z00l3bHRn3SEqh0cF6A4N76o7MKybbv+vPXR7B/bU7+7XR78nsK8mrHd/7Y5uA7VbOw/SbvIbpN3sN1i7rctgw95fhhhOTR9iuLp2qCFxz3DDnaMjDclHRxvj948xxoWNM94Mm6C/tSNYf3PHZP2NrVO1MZuma6//PlN7bdNs7dUNc3RX1s/XXV67UHNx1RJN1Mpl2gtLV2vO8TZozvK2qM4u2K4+Oy9UfWbeTnXE3FDVmbnbqWxRnZmzkVquV0XMW6eMCFmrOj17nerU7A2qk7M2q07O3KY8Pi1MeXzKbuWxiXtUR8YdVB8ac1p9cNQt1f6RQs3+YQb1/uFIvX8EUh0YacrBUabgy9TPVHt/Rapdg5BqRz+k3twdqdZ3Quq1/ki9IQCpt1G37Q9CqhMzkPLsQrkqcuk+xbnFPbDEs/WLDCh6YLkkG92ioWySXyf5ZL/B8jEtB0sH1hss7VJ2cI6f4+AcL5YpPvZjJX6Oc0l/1w1kx5Jh0g7F90m8XfZIPB3CJO6sXTktWIckbqxIahmf05JFkC1ZCotcshYHXgUkAgRiHevXB26T19RUxYRbK5IdKpKKsb631JtmrcPt8fQXj/Sx9fsHAAAAAID/CDPPP7ffmZhTJuqZotY1gbJp5GOFz74kssfamNdDFkW9nDg1ImPeyGPiFX33CTb573gW5r3lyX6frU8P+Yc+Pdp9d9qJvvv553rvTbscsOtprM+2x/dabXz4rMnaB88brLovqbPivqbmb3f/V4V3B1VYmIzKzE9CJeYmIufZCYg9E0ueArOTsOQZbyWVzGJpQmyeWMo3P8m6aqkQufQpyVSYYDoIggkomoBgAgAAAIA/jB1u+ZaZGe+cnZrqikMQUVxceVTYg1JSUjj4vor0mFIa4lZ53dNblfVETFXDs5iaxkdRtY1PL/+Q+zCyfu6Dcw1zH55p9OZ+RJM39042f5t0xONt8r62xrjd/sab27rn3vg9MPfKml8Ml1cNwdFfXj0wN2ZTX/wzY+zOzsbEvR3oxO/saLy9s2vujS299NfX9zPgx1xZ/avh4vLhhqjFo43nF4w3npszRX962mzDieD5hvAJiw1Hxy01HAn6zXBk9HLDoRErjIeGrzLuH7rGeGDIev2+QRv1ewdsMezuu10X1itMF9pjj25bwH79lo4H9Fv9D+q3BRzUh/U+pD8w9JA+fMJhw+npRwxnZh3TR8w6rj81LVwXPumELnziKd3xCad1x8ZH6I6OPaM7HHROe2h0JJXz2oMjL2gPjoimckl7YOgV7f5fr2n2Dr6h2fPLbc3ugfHa3QMStbv6JWnD+iWrw/omqUP7JKp39IxXb+8eq97W/ZZ6e5eb6q0BN9XbAm6pt3S+TV2OU2/tlKDa0ilZvbnTHc2mDimaje3vq3/3farZ4P1CvaGtWrvBG9H5vR3SbPSl4oc0mztQ8TctN7VHGvyztV5IvaIl0iz+GannN0DqeVR4bki11h+pdv2KVOEzkPL8UrkqesU+xYWVIJiAj5I9pN73sjGefRWTfZcqJvkdlAe1PCgfUPcg2aXCQdLX6SDpbX+QbM06KPG2OyHxdoiStOPeJv2ckiW+zndJL04K2doumfRgJee4s+5LWrDSqLyQuLMUZCvW23zt70AwQb4kHxNMjUzzmMhOFUnFeN+btGCK3DdIf+Vwb1u/fwAAAAAA+IrZmZBjt+Fmlv1vl186zDn/nD3xlJjz6xHCsceeNMe2Wx9zm//+kNtq0yNu9z1ppSafyai+8fbrpuEPpB3OPJL1P3pXOn5rbPb8JZdfrpt17vnecSfEZ4ccFt7otYd/r/32p3zPjY8z3NY/etF4TWpmg1UPXtVdef/198vuSaosTpFXWJisKrMgSVtybqKh+JzEt65zEt+7hCQi51kJyHFmPOJQwWLJbkYcYk23kkIF5yFNijNlcoFMKRBL1dInKpQ+F7NgmpQnmNgzEtAPK+5l9DvAP73q2qtZZx/J/eLE6prJIJiAIkJRF0wrgm/b/z4jgbN1dhJ384xE7roJcdzlw25yFwVe587teoU7q/0l7vS2F7lTWkVzJzWP4gY3NWVCkwvUkkozUyY1i8pL08Jy4ZOZWCCF3bfwfG4dPr8un1u3fGnyL+dLt5H1PimQyf9CCvv7f/p18cH2OG/JBKuMx/n5n804q4ylE8kd2ziSOwankenyOOq28W7nuZM8LnCnt4vmhnS5yF3Q5zJ3Qf+r3Dl9rnEmd74GswKBP4JdIfng57gd3McSHh7o8KnE8HzYBZMS6saxzhNeoGP+NCw0xKbO3LzUsUpnbub6QGfcWg5XFdGzgrJTK+hepH2nf5VczSi4Xcsojq2Xy4+vj2MUxtcxiONqaNOTK6lfJpVVpN8vJRellMRLDXGvvD4zvorx+e1aufyY+rlpVxu/Sbvc/O2zS55vn15o+zb1nO/bB2c6vrsX0fnd3ePdclOO98y9c6RPbvLBfrlJB355k7B72JvY0DFvbmydmnt9/dzcKyuX5l5autoYzVtH5+LSlYbLK5bkXl071xizcYYxZssUOtc3Tsu9tj4k9/LahYaLy34zRi9ebbzAW2+MXLTReHbu9tyI2btzT007ZDwx8ZTx6NhIw+FRFw2HR1wxHBx21XBg6HXD/iE3DPsG3TLsHRRn2DMgUb+nX4p+V58Hhp29HutDu/P127sI9Vs7Z+i3dHyu3+r/wpSOdHQ7OmfS2d75pW5bp5e6ze1f4Wg3tsvSbvTJ0v7ujfNa+7vXa+2G1tl01ntma9d65GjXeUq06zwk2rUtSe0ad6l2TUuZdnVLuXZNCwWd1W4KzcomCs3yxgrNsoZyzdL6cg3vB5lmUS2ZZmFNqWZRDepyTXxZrln0vUKzsJZSw2OyqI5Ku7iWVsurbdTyav1Pt7gOMqUu0i6hsrQ+0v72I5UGpuDrvDpIu6Am0oRUQdrp5ZFmclmkmVoZqUPqIdUKb6TaOQQpT8xCigsrHiourV0vi1rtj9sW2uJNCNgOfDzCxxxiUzCXCO5sSuc6TFjc14GVykt/+bG9LKjFEuV47yuK8W1fyEc0fyHrV/uFNKDsC9LP6QXZ1v4F6cV6QbZhvZK0YeWQXnYy0tteSXrZq6goqduVpCcVD5ZK4sHSSjxZBur6O5itBPnLaWUlmJpT1ztjweR3U71l1lqTYDoGggkAAAAAgD9GYrqGfYWvdD6ZKi2xJ0lSdvPt15VXXn1VfUHUizqTI9IbjDgmbNJnH7+5346nLT02P/Lw3PzYI2DXs3Yjw0U9Flx8MWzj7dfTt8a9/m3djaxtC6Mzj0yKyIgeeUyUOOCAIK3Hbn5Whx1PNZ6bHv+vydpUVHf5fVSFdxeVnpeMXEKSaCljEUVTYvNiEUCxeZlmThyTPymH/o6AYAK+QgoIJidmWSQE08LR19krJ8dW2jQ7seGOecmttoUkefw+Od5j5chbHosHXPeY1+OKx+yOlzxmtLvoMdUz2mOye5THJDdTgptdoJZUmpsyuXlUXtwKy4VPZlKBFHbfwvO5dfj8unxu3fKl2b+cL91G1vukQKb8Cyns7//p18UH2+O8JcFWmYjT9J/NBKuMoxPpMa5JpMdYnJ9Nl8dTt01scd5jcusLHjPaR3vM6X7RY1G/yx4Lf7naam7gtQZTAq5VGOV51ebHAsA2YNmDZwARUVHczPhw5+zUA66SmPBiZOzu4jiyxEMlcORXQksqYvaWUt7eVloVv6uMdfBt+Gfm4Ovqq1vKam5tKq+9+ntF3cUNlXWXV32nv/ZbFX3Uqqp0Lv1WzRDJM83xiebVNJyb/73xfEgtY8T82nTOhtQxnp5W1xg+uV7usfE/ao6N/Em7f1Rj7cHBP2v3/tIER7d/QFPdnv7NdGGBbrrdfZrT2dm7hXX0u3q650toj5b60ICW+i3+LfWb2rfSb+vWSn9wuKfh/BIvQ+zudm8fnm//9tn1ju8E17u8exLd/V1qRJ/cB2f656aeHmDKqb7vHkb0fPfwXGf6vo/Pt3v7KNLn7RMsjyL9390/1eXd3RO9c+8dG/DmzuFf3yTtH/UmYe/YN/G7Jr6JDZ369lbozLe3t83OvbVlbu6NzQtyYzbycmPWL829tn7Fm8ur1r25vHyz8cLiXbkX5h82np1zyhgxM9Jwalq04dTUaGPE9HPU9ZO55+Yczj0/b68xckGYMXJeWO65eXuo2w7kRsw6Zjw1LcJ4YnKkITw42nB84hXD0bExhqOj44yHR6QY9g95bNg7UGDY0z9dvyfwuX5X30wqrww7e2UZQnvlGEJ7kMYd3eSG7V1Uhu0BOsO2jrn6zR3+p9/cHuk3+SL9xnZUfJD+97ZIv7410q11R7rVTZFuZSOkW94A6ZbVR7ql9ajURbolOD+YpA4Pi51a1PJ7Uxbh1MzLQryswVy3+tnCGki7oCrSzquEtHPKIe2s0kg7owTSTnel4kLFmVlS12cUo1IcaWeWpO5XCmlnl0HakLJMyiHdnPJMKiLdXJxKSDcPp7Lpcgj1M+qxumnU75pE/d6JzkgTXBJpplVF6gU/I9WaTrnKPaNeKk7Oe6iIXnVAcWlDsPTienc8+8rW72Hg30O+MqikclNwbeWOec3VW2Z4qJeP8JDN6eohG+PuIRtY3yMnsI6HrO/3/tTlabJhP5+Uj2z+QjGyOZIPboBkvaohacdSiGzHRaSXfd4Jf5idBPk3A4IJAAAAAIC/ixuEyu7uc43znQxN2esCZbXTD2X19t0hm22Ny/ZafS2r86LozMCpZzKGjzouCu63XzCr085n87y2Pl7UevNjnt+Op8t67eNvGH5MuGtihPj4pAjxhTEnRLcGHybuUbcLOu98ltVu22O156bH79zWP0QNVj1A3/92D1ValIKKz0lCDtMTTJVFuH3deKa93QQmE2+Z5iqZM4mJZWaSWTh9RPx8rrUdCCbgPwwjmNhUHLFgIggRlwqHis1PKi8Mul5m1ZTYNptDEkeEzk9euH1uEm/jlHjeqtG3eEsGxvDm97zCC+l0iTfT9yJvWuto3uSWUbxJzU0JdrtALam0MGVyi6i8NC8sFz6ZSQVS2H0Lz+fW4fPr8rl1yxe3fzlfuo2s90mBTPkXUtjf/9Oviw+2x3lLgq0yEafZP5sJVhlPJ5I3vmkkbxxOE9PlCdRtE93P8ya3ucCb2SGaN7fHRd6i/pd5iwZdXTCv37VhU7tcazXK8yq0efpKMAmhGDZuw/a5Vm2f+x2Z8fHOMiKqhJofWU775EIl/aMz1Qz3I2oaUyJqG++G1zE+OFbXeCe8Xm7Kkfq5iYca5Cbva5gbv7fRm6TdP7+J29uETtLBn3MT9zfOvXPgp9zkIw3pJXX9TcKeZm/idrZ4e2OLh+HGJi/DlQ0+hmsbfA2X1/kZr65pb7y82t94cUUn48VlXYyXlnY1Ri/tnhvF65l7ntf7/+ydB1QTWRuGQwcbFuxid+29gYh0FGmKgKjYFSuCIAgqGCwI2Bv2igVDlyaoYMWOXRcSitjJTCjpuHr/uTMTCBFc3d8VV+97znMmTEISJrmznnn2+z5pcuAEadJKJ1HCchdxnJerOMZzhjhywRzJ6bnzJSdmLZJETFssOj51ieiYq4fo+BRP0dFJ3qJDE31Ehx19RQedl4sOOpKID03wEx908BcfclhRyYHxK8X7bFeKw8euEu+xChDvtw8UH5vGFEd5rpGmrFkvzdwWIr0SHlZxefemiswdWysubt5RcWHj7orzYeEUoTsrLoRsk54P2Si9EBoiTQ9ZL00PJlgfLD23LrQidc3milTm9oqUwHBJ0qr90kQof/yOS88uPymN94kkYEnilkVL4rziJDFeCZLYpYmSaI9kSbT7OQlr0QVJ5PzL0tPzbkhOzrkniZj5WBIx9U/JsSm5kqOTcyXHJj+XHHN9LDk+5Z742NRbBFniY1OyxEem3JQcmXRXcsj5gfjAhCfigxP+FB9wYBN/a55ov32haK/NK1H42GJx+OhS8U4LgXinmVi8w0wq3mFSId5u8oHgL/F2o0/ibUZADOXRVkNSIIm26APRZj0g2jQciDbKGAZEYYOBcEM/IFzXHQiZHYEwoA0QrmxJ0AIIVzSXkzk0pOAh8GtGsVwOcp8O/Rj4ePgcNPDn5U0p8bOsARB6aQKhpzoQeqgQKBMo0bcJPNWo+5YSj/HSAkLv+tTvQHwaUc/h25igCfWclTQGIuJ+EfE7IuJ5RIsZQLBIGQiW1AN8nzaAv3oAKN80BpTtm/qm5LTXhdIEZjgvOXQ+Tnx/36eEdWGnuGt87zWO8nOG5eSkggfP7MXf6TNBcGCVD3+3L7Ms1I1ZtmIcs2ThSCY+rR8Td+nKxJw7h+IuXc4Qtx/zJnWX8ly6AdxBF+BjdQBmWh9wR6kBroEyJZVGyKEomlDbO8S/QU2CaREtmFKQYEJBQUFBQUH5ioRcfKUUcYerdf7P0uY38ss7Xc8r73/uecmoyPuYzYGbxZO3XXm7cP351ytWJBeFuccUHJx+ihM94WjOudH7n18y3P3kut72x1l6Ox7fGrnrSbZJ+NMn5vue5prvfVpotPvJW70dj/BBWx6W9934QNI9JPtTl/XZoP2au6D16rug2arboKHfLaAuq1qSzU+qnJdEQ4oluXlJlXOTvkIwoQomFJRaw2bnKRGo0FIJyiV1AtW6Fkz+s9KVA+dm9NvgfnX+dp8bh8P9bl/b5XMra8vi61kbZl7OWu2ckbXC9nyWr0ValrfRuSxP/dSsJUNSstwHUiwekExsCQZRLBmUUsXAL5FcK+4KfOmxX+bv3sPfv5e/e2/VGPCD+dpjJP+ZKODxA/jS6//j78VnxyOpksVyLIL0/3dZKMcCksSsBf0Ss+ZD+lK3FxL7Fg1OyloyIjnL2zQ1y8/mXFaAY3pWgMuFK/6OFw94Wl2cNXvEhd7OPc6hVnk/cWCVEawsKn9+oZng/eOWguKCVrCVW8n9zMYvs7ZoQWmk8CtKUEIVFBRovnv3sD7OvtkItnGDLeAE+TdbinKy2sL2b9Lc8z0rniYPqHiYPPzDw3jDD/dYph/usyw+3Ds1RnLn5FjJ3dPWklsnbKQ3j9lLs46Nl14/7Ci9cchZev2gCwm8fRPuO+4gvUXcf+OIgzTriJP02r7JFZfDp1dc2jFXkrFloeTCxiWS82FLJekhXpLzIcuk6cG+0nPrVkhT1gZIk4NWi5MC14jPrlwvTlwRLDnrFyI567NRErdsqyTac5ckavF+8Wm3o+ITM0+JI6adkRxzjZIcmxIjOTo5TnLUJUF8yDlJfMjpnPjghDTxAYd0gvMkB8ddEO8ff1G83z5DfMA+EyLaZ3tJtM/mkmjv2MuivVZXRXusr4kOOFwXH5l8Q3xy1i1x5PzbYtaiO9IzC+5KIufdk5yae5/goeTU7IeSk7MeSk7MfCA5PjWbeP27xO/cFh+ZdIt4fQInAsc7kkMT7kkOOt6XHHB4KDk4/rF4/7inxOs/F++z/1O83y5XvN+WLd5nxxHvs8kj3ku+aK9tAfF+oAR6Qbynl6I9Vm9E4WPei3aPxkS7LEvEOy3KxLvMysU7TMvFO01LRduNeMJtozDh1pHFws3674WbCDbqEQzjEuDCsCElwo1Dy0ShQ8pFG4cIRKGDhQRiUeigCtGGgR9FIQOBaMMAIAqB9Cdu9wfiDXDbjyIYViNB+hD0BsL1ivSiqpSCugBBoC4QrGwJBP6wSqgJKWuEy5t8jm8NP/s2pSAlj5xokkkmf1owwf3k4xvRkqkeJZq8NGhooQT3V0qlRpRUIoWSvFRqRlUq+dHSC+7zpeXVUuK5ligBobsSEHhoAf7y1oC/bhAo32EHSg+7Ccsi/W6WxK3ZzEta78JLXd+vJHldBx4rRBu2dKyTEwLKDw+X6dKmJHj2uPIdS0MEe/zPle/0zioLnpVV5muTVTpvRBZvap8s3KVLFubY/g7m0C4Xt2/Dw+xbAcymOcBGawPMtF6VXBqhVF0u6TMAan+H+CEgwYSCgoKCgoJSU9JzSpUSn/JUoh9haiezueqHb7/X3HXtbf2wjNcNA1KLtL0SCpu4xxU0W3a2sGXwhVcdDt583zvuEa5/7lnJ6OSnJc5n7mPzDtx477Pl8tv1a8+/CvdLKjrtHltwbsZpzh3Hozl5Vvufvzfa/bRs2LZH4gGbHkp6h92X9thwX/pHcHZFt+B7H7qsu/dXh7V3P7YLuvOpNfMOaBF4GzQLuAUar7wFGvnfBPWX3wSavjeA2rIbQJkUNHRLPA9FkfQ385OWyoEEEwrKN0VBMKnT2x8qmLauyqy/jXmx+aZVF3TX+6TrBi5K11059/wfAXMynNctuLJz45Kse1s8boo2LbohCZ51TcKceEnib3tR4mOeLlk6Mk2yZNg5yaKBqZIFfVMk83vT9EomtsmSBZWkVLLwiyTXygIFvvTYL/N37+Hv38vfvbdq9PrBfPUx+trj8DPwlcf+s+ORVMl8OeZBev67uMkxlyRRMrdHomQOpDt1243YN69PkmThoGTJEv1UibfZOYmfdbrEb9wFgY/txdtLLC9unq1/wWFiz7RO1m0TG5tox6r9qPPCbx7ivJyiAef3kMKHndlOfPd4e9g+TsBa2Ip/fGoL/mGn5uWn3HQECStais9vby+5E9G94mn6gIq820MrXt3TI7dPkwdIM3f2EMf5dRSx5rcVsHxawXZ0ZCVS3s1u0hfZvaQv7/Wr4NwcXJFzZdiH55f0Pzy9YPjhaZrpX49SrGC7N2l2lEvF3VPTK+5EuFXcPLqo4uYRj4obB5d+yNq/7MO1Az4fru/xlV4J95de3rlSemlXoPTStiBpxtY1JJd2BBH7V3+4vGvVB+L+D5k7VpFt3zK2rJeeDw2rOLd+myQlKFySxNwvTVp9SJoUcESauOqo9OyKCGmC3ylpwnK5ih7PswRJkmj3FEnU4jTJmQUZktNuV6UnZ92SHHd9IDk68ZnkkHOO+OAEjvigQ554/7gC8T77ItEe29ei8LHvReFjikXhVlxSzkDCLXHRbssS0W6LEnG4Rak43LxUvMuiTLzbvFy8y4wv3mUuFO80g4jIqp6dFlKSXZbSytvkz+YV4p2mFeIdxhXi7YYVos36UtHGoVJR6CCpaEN/gr4SUXAfaRV9iX39Kij6V4iC+38g2VCFMKT/X8KQAZWIIBv6fyQJHfCJ+PkTuQ0dCIgtEIVAAdQHiNZ1/yRc0/WTkNnpkzCw/UdhQLuPwpVtP1Wyqh0QBuhSBLaXowPVik6GXIs6kQLV2tetlrW060zTiXou2LpuVWsg8G8OBH5NKcFE0lSOZlX461RBVizRokcmkyrb1rWuDtwnL5tIUSQvrGqQVJXP21LheWGlVVt625p6HBRQpGCiq6Nguz3/VoC/rj/g77QWlx2bj5fGBT4qSwo7UpK6eQaWGNzjKYupnslkqtYgdVF+gcCZSqXhfk24O33b4Lu9dPHNC3XxdS66JUwX49LgGSvKNy1I4W9Z/L48zE1StspZUupuJimZOVDCc+kuwRw6SnD7NlJsbPMPmKX2J65FA8A11QJcIzXANVQBXAMlSibJU1sFE+LLGNRCXb+vnx0kmFBQUFBQUFDk8/C1UPVGIV8zg13WIPV5SZOEp3gL1kOsbcS94k77brzrsfXy237rzr8a4p9cZOB1ttDEJ7FwDDPtpcPmS29m7Mt6t+TwzferiG3Ylkuv9wWlvzzpm/giYXFsfubM05zsicdyOdYHnnONdj+RDtv2GPTf9BD02JANOq+9B3SZd0DLVbdBU/9bQNvvJmi4/Aao75sF6hFoEWgSqPtkAbVlWUDV+zoplZS8rivMVlKQR/ISqSahhAQTCsr/lS8Iph9SsRDqlam1PfBSzx1rMyy3Bl2YErrivOsaz/OuAfPOz1kxKyMsYOali6unX8WZU6+BAJerwM/+MvC2zAAehhfAoiFpYH7fc8CtRyqY3SUFzOqUDGZ2oJjRPqnyNmRWh5SvJPkH8IPfS/sfzHc4DrN/AF//OXzDZ/HZ8UiqZKYc8Ps5Q/ffZXotTIO0o26Tj+2YBGZ3SwZuvVPBgsHngLtBGlhikg7cTS8ULzC6eG7WsIshLr3SJtrqJg0zbRLX4kecF373wIvT5bdim0kfJ/X88OiskST7tJ302i5naQrTURi91FZyZu5oycm55mLWYlNx4gozycVNVtJrex2kt0+5VjxOmFXxNMmt4lHs3IrbR2aIz2+cLI33d5RGLbGXxPrYSFKD7aTXDzhKs6MnVTxKnFnx6Oy8iuwY94p7kZ6Su6e8pbdOLpfeOrZCev0Qk3jO4IoruzZXZGzfUZGxea/kQuhBafqGI9K0DcekaesjpKnrTkjPrT0pTVlzmnhvLElyYLQkMSBWkrgqjiSJuJ0cEC1NCmRRrGRJzvrHSOJ9EiSx3imSqCXpYtaiTPGZhVfFpxdcF5+elyU+7XZTfHrubbINHKwIOjHjkeT4tCeSY1OfS45P+RO2gxMfdeGID08sFB+e8Eq8f9x70T7rEvHu0QLxLgsog6TinbC9m/EH8XbDT6KtI+XaudEt3TbTwNubhtEMlYPet3Eo2fKNrOiBlTuySp11vejbfYj9BMRt0boeQATnCkHxEtC2anbPcjnxAcWKv9zMH8V5P6vakAgC2lDzhWigsBEG0lJIJnaYcG5RF2p+ETmTqD35HHCmEDlnCM4cgjODvOpRW3I2UQNqTpFPI+ox5DyiJgSwyqg5hX8LIFgBaUkC36OIeI+ilRB5wQPfK/F3QmlVjTbk30M+B5xxtFwmmJrWIJRkx0G+9R0tf0gB1JqClD41vV7bqvvgMYTHUvGYKr7nyueRPRct3ALaU8j+BiijYKUTrHzyrke20RMQvytY3xfwd1h8Kj8yq7A8euXl0pSN+8vO71iMp27Vf3d8Y/26Pneg/LvBQ+e0K9/jb8A/vNaxbG+Aa9k2D9ey9TNdS4Mm+ZcyXSLLgiblljNdQJn/OFDibgJ4MwYCnlM3gNvpAtyqJcBGNwVcs0aAa6wJikepguKRSqBY1g7vS2IJCZKvQ3ac5Ku/kKj7epBgQkFBQUFBQYF58lao9uyduMGDV0KdrAJ+u4u5ZV1Snpf0inuCDz7zADM4frfYfG/WO/stl99OWnf+1ewVKUXuXmcLly9NKAhalli4xS/pxcGVyUVnVqYUJfmeLcxcHJN/a1Yk58GkiNw/7Q8/f2Gx99n7kTsflw/c/OivHiH3Qcd12aAt8y4plZr53QLavjdAPe8soO55Hah4XgPKHteAEsTzKgGUR1epCiVZlZJMGMkqkmRt7irFUda3gwQTCso3hcPJVyJQIVAjIAVTbi5HleCH/N+3oV6Z7bcFXhq/Y00Gc2vQxeNhK89HrFl6PmLl3PRIH9cLl7wmXCzwtM38uMQyEywyzgDz9S+CuQPTwaxeaWBG51QwrV0qcG2ZAibrpIBJTZPBpCYykiiaUkwm7qukCeKnoGntTPkBfOn1/+2/fdIPwOUzkoBL4yQwsTG1hVBrhHhPLVKAa5sUMK1TKpjZ4xyY1T8NzB58/sOsoec50wZeyJjYM223rW6Sm1nTuMGG9VjqP+Lc8DsHVkCIU7d2lGRuGSPJ2LxEeiEkVJLCDJfELdstiVq0SXxm/hpx1KJV4hhPf3H8cj9pSlCAOD14fUXGxs0Vmdt3STJ37JVkbNknObdujyjBb6ckymOr5MyCjZIzS0Il8b5hFSlB2+DMIOnFTYelFzeflJwPiZakbYiXpK07K0ldlyRJDkqRJAekSc76X5TEL78sjfO6Lo32uCmNcr8jZS26J41cmC09s/C+NHLBA2nk/IeSyHmPJKfdHktOzXkiOTH7meTkzOckJ2Y9k5yY+ZTgiSRi+mPJsWlPJEenPJUcnvSn+KATW3xgQr5o37gXov3jXor22r0S7bN7TfBGtMf6LVl1tIeuOILVRjstSsS7zEvFO83LxLtM+KIdRkLR9lFi0dYRFaItwz5VyiBY1QOFENnSrQ8QrusJhGv/AEIof0i6yt2W/SwPvV/2O0FdaGmkWykmBDJJQVYC6VICCO6DUgUKFZ+GlNhZqgEEHmoEqkDgCVGj9i3Vou6vlD4NaemjTbFcJn6aUM9HCiAdqiJoRcsq6SITJWQ1T0tSZFFiiXh+D3UgWEK85hIVagvfhyexb6kmdb83/frLZNIJCifi9Xyb0lVHzUiqWtPJz0BSrChqIwf1XqjqJR36uZpWF0srFKTSipYK0GJphYIQCpCrwCI/D93qskkemZirhtzvBtRQuRVICyYop6AUhMcGfj6kXCI+d+L7xN9uBsoPTSkpj1yaWZawZjMvdbMrnrZ9BDchtE1dnzdQ/t0ULzRuwAueb1C2Z+US/sG14eUHVkeUb18aUb5+ZkTZqgnJJcutH5UstSwrdTcCJXOHAd6kngCz1wXY6OYAM20CuMYNAXdUPcAdqQGKR6gQMECxPsVncglV4Hw78nJJ8ZgqHtu6fq8/K0gwoaCgoKCg/J45eqtY6dQ9rkrSU57WlbyyJndfCtpmvxR2yyrgD7yQW2aY+LTEMuohZn/iXvGkQ7fezw6//nbJpszXq9akvwpZkVy0yyu+8NiC6PyYOSzOuZmR7OvTTrIfTo7IZU88lvNq3KE/uVb7npWYhD8pH7HjkWDQlgfiXqH3P3Red+9TG+Zd0HTVbdDA/xbQ8r0BNGippOpxDSjDOUmL6TlK7jRLaDyuUmLJQ0EwKVYhLb3+80gjJJhQfvHUlWBa5nhehTkno3Ho0kzjLSsyAzevupga5n++cN2y9KJVC9KKlrmee7XIPg2bY3pOPF0vDUzpnwZcep4DEzufA866qcC5ZSpwapICHBskA0etZDBBHZIEHNQUUJeRXMkENcRPgfpPTF0fm++Awxf47HPQJNZSfYLGKcCpRQqxxlKAS9dzYFLPNJFLr3RsQrfUe2Pbnd1r2jR20sh6rC4GmpEaRg0iNcyasjTMm0epm+iw0KyR75inLCd1wakF/SSsJW4S1uKDYtbCq5JIt8dwzo/45PQs8ckZ6ZLTcxIlkQviJFGLYyTRHrCFXJI4eskFcZT7FTFrUZbozPxbolNzb4oiZtwQH5uaRXBVfHzqFfHx6VfFJ2bekJ6cc1dycvZT8anZHHHEjFcEb0XHpxNMfSc67vpedHRSseioC1d0yAkXHZjAEx0YVyLeN65UvNe2TLzXhsa2nNiSiMKt+aJwK75o9xiBaPdogWiXJYEFgTlftNOMwIQv2m7EF201FIg2GxDoCUWbhotEYcPEorAhElHoEKkwdDBF2OAKYeigCmHIwA/CDQOolnEbCIL7fiTZ0OeTMLgXBAjX96BkUFBXSgYxO9FCqAMpCwQrWlNVOf6yCh26SqeS5lWskKvegVU4ZCUOlCUt6QofnSrI36GFCNySc3uaUKLIm5ZLUCh5qBAoU1somZbSkslLk3gcLXqW0aIHiimIr0w20VVGvrRogtKHFD0KgodsFdecev1ltNzy1KQkEym4iK3nF8QWFCi+8jKrmdzfKj/3SK6t3GeVRW3lKoqIY048hjxu9DGu3upOsbqojQJtaWh5VGNbv/ZVVUc1QcqjWlgtawXYqaq1H7lPl6pegtKLbI/XkDr+8Du0rhfgbx31kX/QWco/vfhBWdzK3WVJ612KE8O6lSZtaAJb49X1eQPl3wmTwVC+O3iwGu5t1at0/cw55du9j/PD/R/zdy0rKtu4oKgs0KWozNvqHW+BQTlv1oCPvMl/ANxBF2BjmgGuSX0AhRJXTw1wh6uCYj0VUDxcmYBB3KaRr7BBAuSfoyiY9ORAgunrQIIJBQUFBQXl98mVvHKVlGclGlH3sQan7nGbRmZjreMf413P/Vky4GJu2ajzOaW2iU94rsT+hYdvFS/bfe1twOZLr4PXXXi1dVVq0X6v+IJTC6Lyz846zbnoGpF7y+lIzhP7g88LrPY9fW+66wl/5PZHFcO3PAIDNz4AfUKyQfdg2P7uLmgHZygF3AaNV9wC9ZbfJOcmkVLFk56TBIWSIt8qmLzk+QmEERJMKL9B5ASTKpRMtGAiJVNODluZ5ru2y1swOq3RcpcLnde4ZY7c4JG5JMQrI3LdkvP5gfPTwPKZqcBjYgqYZ50Epo5KAk4DEoF9t0Qwtl0isGpB0DQRWDdKBDb1koCtehKwU04C9oxkmiQwTgH7SpIrGYdA/AbY1wK8bzxN1WNTgJ1SMrBVI6iXDGy0ibXVktivmwzsOiQDa93EMvOWcZdHaUcFj9CKdDTQOq1v1ChS30yHpW/eMmqQSXNWJ8OmZxp8z/PE75wCprGm6JCTvviwU6DooNNl8QGHUvF+u0/ivdYVor1jcdE+m0Lx/vG54kNOz8SHXR6Lj7o8ER9y/hPOHhLtsy8S7h37Rrh79Dvhbov3wp2WxSKKd6IdFu9E280JTDHRVuMS8TYjsWir4UfRNkNAslWGARBtGUG3ltOn28nJt42TY+OQqn3wdtgQIAwbDIShA4EwZAAQbuhHt5XrCYRraBHElL+oLz/Lp1PVfhKZFFAQC4G6VZCVKTLB0QZUm80DRQkUBFCiQFkgw6dRDcgLnca0bGlaJV1kVBNMcm3dyHZ4TenXa0hLnHpUtZCXQtVQNbkjJ5NkVUtyFURUmznFCqZWCmKGrmCCjyEllzZVleRNV+B4y/5ubbm/U05a0eKqSrBVtcgTKFYqrZK18mtbS2UQ9XkIYKs/2FIOyqaVrWuoRPoS8lVG7SlZGPAFYfRZJZLirKhaZkfJ2gwyO8u1NmxJVVtBwUTKpVZAENQNCDbpSfh77V7yI2Y/KI9adrQ0LmhBSdz6AbDasK7PFyj/Xu4OZqhxHTq05s0Y3Lds6djJZYGTtpWtnXm7bP0sSVnQNFDq7wRKPUaDkrl6gDelN8AdOgDMWgdg5g0A11CVEkjDqIv1JEPpn4dXyaVixYqlupYMPxO1VXLVhGJbPCSYvh0kmFBQUFBQUH6PPHgt1LxRwG98Pqe0dcIjvMuZbKz/qXtcAwLrk/e4U0/c5XocvlUctOvq250hF18fC0x9yVp2tjB+YUx+6sxIdobL8ZzrtgefZ1vsefbcaOeTgpFbH70dvulh6aCwB+I+G7I//bH2HujIvAPaBd4BrVbdBs1X3AJN/W+Cxn43QAPfG0CTnJ2UBZRkLeygJILiyF1RMF2j9i1RgBRLNcxW+hnmJyHBhPKbJi+vQIlAmUCVgKxiys3lkOTksNUIVL+nZHLVS1JaNDatu//ki+PWzMtcsW5B5qnVcy488J18TrTYLhnMsUgEriMTgNOgOGDbIxZYtIsBJjoxwLBhLBilFQuMNeKAmVoCsFQ5C6wYiWAsIwnYENgxapJHNQsmBOJ3RH5tjGekkIwjgHLJlsCG2G9FrJUxyonAUv0ssKyfACwaxwPzZvHApFksMNSOKtKvdyZVT+P0zhFap5lG2pFM8+YspkXLKE+T5iw7w6ZnunyPcwQKg/Fyi76WeIeFkWiXxSbxLoun4h0mlPSB8gZKm5D+EmHYYIFw8/Ay4VbDEtHWUSXCrQZlok16AlHoELEoZECFMLjPX8K1PT8K1/X8JFzbi6D3J2EQ8XNg90/CwK5AGNCJvnAvkzaKVR4dPr8wD6uDmPIiqDN5cV5EVg51oSuIulQJJFnLscoKm6ZA6NsECH0a0xfw6ZZspLzRqYKUOM2qVwxVih0duiKmljZrsmqbyooibUquyGRLZaXQ/yGY/JsrCKaWla9JCaEm9PNoK2wbK7S9U6gWqqykUpA9/lWyR1BN9rSpVjUEjzP1eLraqvJ9V1UjVavgWiH/vASrWlNiqBryredomVdTu7lKZNVG8sJJ4fGfCcPaqKHy6GuRfVeZCvKSKRNLnan5VWQLRPq7CiuroFyC87Ig8NgwuwJB6GAg2Gnxmn/I5UJZ5MLd5TF+c3jxawzfJDJ16vpcgfLv5p1lgxbFzp1G8eYMdyv1sNhT4jU2o9Rz9LuSxaagxM0Q8GYMB7xJ/QDu0AVg1q0BZqENuMYagDuSrlKqSS7JBBMtl4qRWKrO3wmkb0KJ+F05Rsr4Cf7OnxEkmFBQUFBQUH7NvCmrUC7AJRrP3osa3n8tbHGjkN8xg13WO+lpyXDWfczy2O1i531Z79y2X3njH5bxevPa9FfHViS/SPKILciaE8l5Atvd2R/6M99i77MXBjsfvxq4+eG77hvu4x3X3ittt/qOoO2q29LWK259bOF/CzRbfhNo+9wADZZlgXpeWUBz6XWgQaBGcg2oeF4HSjKpJKs+8pCTRtVuy+FZA//lNnhIMKH8gsnPL1AiUCFQzcsj2+Rp5OZyNHNy2Bq0ZFL5XoJpql5Si0Vj06yXT7qwLnBmxrlV0y7meDmk4W6myWDyoAQwvkcssO4YAyzbRAETHRYwaHAG6GucAXqqLKCvHAUMlWKACSMOWDASwBjGWTCWkQhsaYEEKzIcKkkht4qVGvLVGwjE7whcFxOI9TGBXCOUaIKCFopaKG0tiXVlphQPTFRjgZF6DBipGQ1GaLKAnkakaLja6Rd66qfvG2hFZhlrn8kybx6VZdEiKoFYq0GGTc5Yjmgc2ex7nCd+9xQwO2ryt40aJdphGiLcZnQfVhGRlUCrO1PtuvygIGgFBcNHYWCnv0RBXQm6fRQGdf1EXjgPbE/JASgRljcHAl8dIPAh8G4GBEubEDQiaEBQHwi8aCora+SraxQrXZpXkysySUHJjaqKGoGsRRp8PBRIZDVNfWr+D9mqTYOeBSSr6GlIPYZEm8JHoUVcpYyioGb6NK+SS5Vt11rRLdxa0lKrGSW16IoUSh40laMZjQ5VheRXm7xqVUW19m4KlUTy7+GzVnCKckgRWYWPApVzhtrJSRtd8FnlkEwA1TSTqFIQ1TKTqFpVmII0qiZ8viCAqsmg9rSk7CBXiVZLddFnlUey3/kGoVRblZIi8oJJJqDge4PHRyZB4XcECkPieQQbBgDBtlFC/t5xWeXHpm0uPb1wIi9yWZ9iFrMVql76tfO0N0Oda60zGJv4x2Le7KERJfMNH/Hm6r3mTekjxR06AcymLcBGtwaYmQ7gmmhT85UM1CipAatmhtMiiaZaNY18Ozwkl6pTm1TSZ3xepVRTZdIoZYAZqxFoAMxEk4a4bawOMCNV4n4VwDVEkqlGkGBCQUFBQUH57yXuMU913433GpsuvakfkvG60c5rb5uczOY2v5Bb2vreS0G7x29FnR68Fv5xs5DfJ5NTNij1eenI2Ee80afuYRMO3SyesevqW4+wi6+Dgs693O5ztvDEIlildJpz2/l4DsfmwHPMNPypWH/74w8DNj38648N9//SXXP3o07A7Y8N/G59Ul92A6guvQ5UPK4BlSUE7tTsJCV3uvLI/Wp1yBZ38q3tFNvbZX2ZuhY/SDChoHwxtGBShpKJFkyaubkcrZwctkwyqf6/gsmuS1z9Cb0TmrvqJxnMH3POx9Mh/ewy5/NvPOzTP8wxSvk0sU8CsGkbCyyaRAPj+lFglCYLjFQ7A/SVI4Ee4wwBCxgQjGJEAzNGHLBkJICxjLPAhpEIYIXSePqiuWM14D4KBwTiN0e2FhxJqDUik0xQvNoR68iaWFNQ3Joz4oEJIwYYEutthBIL6CsRa1ApkthG/mWgeqbCSPOMxLRhlMSiWZTEvFlUkXFTVuzIxmc89BtH6o/UidQ1bcPSteoYrWvfNaa1fZeYxradYtS+1/nqdwjbvauGcNOIoYItBj7CLfpnhSEDXgmZXfmC5c0+8T21AN9dhYSUNcsaUXKEFBpV7dJIEQNF0dJ6gO+hSTxeA/AXqwP+IjUCVeI2hcCdYAkNnNfjqU5RKYAaVLVXq5zTI4dM9Mhm9PjLZu80p+6Hkgo+B5z/Q84loqn2/LRckrVw86mh2qdaJY4OLYFouQXlTIBC6zVSqMhkT8sqVspQFEA1yJ5qoudLYqaW2T81VYH9Ez4TMx1q4W/kypdgdqzii9LmayuIvlBF9Ld8h2NW6/vqLEdHusquLbV+yOqlpsR3S4f6nNf2EPM36mH8XWMeCQ46Hio/MmNG+Sm3Hnf3uakxmYx/dU4lyr8btlVXjRd+1k24TJc2+EoXXXyhpe5rlz66ry2b6r4exdB9PZSh+9aA0Rsb08QVd+y8lzet36OSGQMreJP++IjbtAJcYy1QrK8CiocRDFUmtrBiSYmUSp+1ZFNsgYeE0pepqd2dIvLt78jjq0SJIxN1wLWoDzCrxgAf24xqVwi3Y7QBBvebahKfnRrgGqrU/d/5M4IEEwoKCgoKyn8r918LtVKelzY7doeru+Pau+6bLr0ZuO3K2xH7b743P5mN2cU+4jnFPea5nnmAzz56m7tg9/V37psy3/isTX8VuDK5KMQ7oXDnouj8o3MiObGuJ3LPjz/8523Lvc9yDHc9eTt06yNh37AH4I/gbNBh7T3QavUd0HjlbXJukor3DUoIyWYmLbwCGAto4O2FVykxIkN+lpKiYPqVWtshwYTym4cWTKRkysvLV+Ow8zTYbI5Wbg5bKyeXFEwq/8/z23aO1xrXLb6nY98Ey8nDE5fNME4+Mcci5dkc82QwbUQycOqVAKzbxAHz+jHAWCUaGDFkRIFRlUQDY1IuxQJLRjywYiSQcsmOnrU0gb5o7lQN2cX0qovrCMTvimwtOJFQa0QmmaCghevIllhTlGRKABbEWoOSSbYO4daYwFQ5GlioxwDLejHAolEMMGsU9WlUI9Zj/YaRR/W0T3sb6Jx2NW3Hch3bOdrVvlvMePuuMcPsOsW0+F7nq98hd90YauXB/f/ghw5x5IcMDBKu7xMnWN3+Ht+nMc73gJKIAfgLGEBAbEkxtLQeKX+o6psWpHz5XDARv7dYjcJdjfp5iToQeKhXSaWaqotk1Uzyc3vkpY9M9vhXVfqQbddgdRM5A4luU+dNzyWSVUspVkn5Kraia1bV1s2vhVzFlKxqqlXVXB950SOPfGVPteqgWub91Fi1U0O1Tq1iR16qyLVgqxX6McyvZLVsdpWiiJGfKfR3rylrYyjP373OPxBAP6Vg6lT1mZB/p0wutaRbKjal1hDcB6sBQwcW8rcaX+LvsdnPP+SyqPzYNP03+9zQv99/geDuxu14Ac4GePBMR96aaa6Yl7UrNq2/63vrFq7vjTVd3xsyXN+PUp5XbNloK27X+jLu1LkMd+oEcNuWADPVoqqSBhH0JxhAMJi+ID+MUb1KSSaTDOWoa4lQlxjWgux+mVySSaThjCppJ39c5WUTKZdUAWamSYolbFwrwHPuCHiTuhH8AXDnzgB3aAdwm+YAH92IkkywkglVMX0OEkwoKCgoKCj/nRSWSOvfeyXUTXle2u/4Xe6oXdff2W3MfDMtJOO1+4aM1wHEdlPIxTfh69JfHVmRUnTaI64wag4rL3byCXbiuMM5aVb7n2eahj+9brjz8T29bY+fDd78ML9P6IO33YKzSzusvSdpzbwLmgfcJqVSQ/9bQGv5TVJykAJEJpdkM5OgBKlVKinMUVJseVebXPKmqWvZgwQTCso3hxZMqhxOnqyKiYCtnpPLVsnlcP5xBZN91/j247snjHfsmxA0cdDZhIlDzz5wGnK2ZEK/eGDXLR6MaRULzBvEAFPlWFIgWZAVSsR+YjuaxpLcQrEUT14At6Url8ZVVi8lK1QvpVReUEeCCYFIrrYeFNcGrHAaT88rsyPWlg3ZfhK2oYyvXINwPZLrT4lAJR6MVY8HlppxwFQzGozUYuF69SLvDW90+qyBzukI03asiLGdoyPsu8XssO8a42bXKWawTftoje95vvqVw3JiqPCZ/VoIwgYMEIYMtBIE9/cSrO1+mB/Q7pHAt+lffChpoFharExsYSWTJilxyIvjdGs2qj0erCBqQrWc824EBF4NaRpRP3s3kmtNJzeLSFH6VM7vqS55ZFCt46oqgcgWeSvlRZNsHpB85RP1nNWqnyorjWprMadYYdROYaaPggT6J3N+vkYifUlg1DTjp1bJ8w1ySdbS7YtVSHKP/Uev+S0y6O8EUyfw0wgm+fdRKZg6UVJSvnIJfkfh95c4Tvz1/Ur4m/QyBTvNNwrC7VzLDznpcw+5tKnrcwPK/x+uXfeGvMUmBiUBzkt4wbPDeWumRfC8xkZg0wdEcG1bRnBNtSLeGypHFI9SZhWbaF7lWmoXYVbNAGbVFGDm9QE5X2kYLZgG0tsh1GylShkiL5dqEit1LRLqki8JppGM6pKppjZ4Bgr7DFWoNnhjtAE+vg3gTfkDlMweBErm61PMHQpKpvUBPOdOALdrCTDLRlTLPEPlqtdD1WUUSDChoKCgoKDUTU5nc5X2ZL1TCst4rRx4rkhlaXyB6vTTbLVxh/9Utzn0XH3KCbbGytQijYi7XI2r+WUNHr8VtnzwRtgjg1NmxHqIT9h34/28jZferGSmv9zil/ziqGdCYdL8qPzrM07nPXQ5nsu2OfRnkUn4s9fDtz1+0yfswbsu67OL2wXdxVoG3uE1W3m7rOnK24LGK26JG/rdqqi3/OZHTd+bQN3nBlBbdgOoECh73wBK8vJDcRaS4rykb5mbVNcy52cECSaU/3hgFVNeXr5yHidPjcMhq5g0ctmkYFJl/wPBZN8lXsWuc1xj+67xxuO7JwQ69Eo459A7/o1dj7hyq86xf1m0iQYmTaOBcT1iqxoDzMmL2AnAlnGWFkeQRPrCdyLJOBLqPsXWXwgE4p8jW0/j6fU1TmHdOZBrDlYLEvcrJQE75bNgjHI8MFOJBYZqUX/pa5wp028Q+XZk08gi0zasIquO0UW2nWPu2XWK2WvbMWaSTfvoLtYdYtTsusai1lJ/HyX2jq4avBBzbcE2s5aibSbDRVsN3YWb9aJFIQNeCJldPkIhQ7aXI1vO0YIJihooXirn6Mhm77ShBJAiNc4HqkHk1Di/p4Z2cTWiUEEkz1c/x9/Iob8VQP9UGP3DKpnVnT4XLN/CPxYw/8Zr/cst634EioKJrF7qQH2/YeUSnM3l0/gTcfujIED3g2BdD4kgZPAD/qaRu/nbzZ3Lttt0Kw23bvKU6aRe1ycGlG9LprGx6lOn3uqwJZ6Mt5N69cYXGc7h+Tsc5wW5PuYFTCzCPcyL8Kl9ijDbVkVcM62iYkPlomIDxuv3I5Xx4lGqEq6xOtVaDbZhkwkOWYWNYks8JCqqUJQ3Nc1W+mwelRLgQvkDgcebBMog5Y/EfRXFIxmS4hFyjFKRcM3rSTAbHQlvYhdJyeyBklJ3Y0mp9xhJ6bKxFaVLx/xVunDkp5KZAwAPVjPBtnlmWgCTfZaKLQzr+pghwYSCgoKCgvL75Fp+mVLqnyUarAdYo4O33jffevltuzXnX3b2SSzsPpeV18f5WO7A8Uf+HDr5BFtvaUKh/pbLb/RPZXNHJTzhjYl5jLscuV3svvXK26Cg9Fc7fZNenFoUW5A66wznpvPxXPbYA8+5xrufiYZtfQx6hz0AndbdB61W3wXa/reBhs9NShhBCbREgZrEUG3zkLyzfu9KIySYUFBqDC2YlPI4eSqcvDw1NoejTgsmNXYeR6WgKE/5xcv8rxJNjn0TGo3/I76zfZe4kfZd45cQRNp3iS+w6RQHRreNASY60cCoQRQw1IgCRsox5FwlKJdg9QS8gA3bd02kcUbt7hCIH458Sz1ngolyaxLuG0/PbILVhibEGjZUjYKVTGCUNguYNo8Clm2iwdh20eXWutGXrdvHBNu0j3aw6RTTy/6P2JZO/eKRZPqGlJ6c3ER8YraZ+NTMQMmRicmiXRY5guC+xQK/FhUCLy2qzZ13A6oaCAoZsj1Z56oWbEGd/4FU+N5y4RcWGIifl8qqJbkqLSgloXyFQha2loRy1ke7QuDfAucHdsgTrOuVLdgw+Ch/84gFJZtN+mcyjVXr+hyA8u0pmGHcuHjh6K7cpWOHvF9kpP9+1kD995N66HNde03B5w7fhnta3Ob52Eh43mMA7qYH8IndADZWB3BhCzxDZVBswADFIwgUxdHvLiFkfKnNnWIVkqzFHRRyw2iG0pVfkKH0ffD3RqmSnwFm2RBgYxpTWDT4UGxa7y3XWO0J8bncID6TLJIRBKNUszDzhlm4fcssfHL3LJ7bsKzSpZZZpSvG3yoLdH5aFjjxdamvraB0sTHgTesH8PFt4fNRgkn2HtFnS4EEEwoKCgoKyo/Ntfwy9bScEp3oh3i3w7eLh26/8tZ8/YVX4/ySXkxeEJ0/x/UE28PxWI6f8/HcgJmRHKZnfCFzZWrRWmbay42rUovClyYUnnSLzkuceop92el4Trbtoeds833P3urvfCLot+kh6LbhPtBdcw/oBNwBDf1vA3Wfm7S4kM1OukrPTqJvL5SblUS2tZOTTpXiqRbBpEhdS5r/MkgwofwCycvPp6qYYKu8vDy1XA4HCiZ1Th5HreBlnuqLl/l/e2F48pAkJed+Z7s79EgYZ981foVdp7hT1rpxD8a2iRWPbhELzLRjgJFWNDAi5y3FAFNGLBhNz1QaT8oleDE7FbjIUSWaUPs7BOLfQn5dyeY0OdNSSX49OpOzm5LJGWhjaclkphwLTNRjgEm9aGDaKBqYN4kGljrRYHSL6CKrNtGp1u2jt9l2ipkxrnusvlP/eO0fcT77lSK+vLOTJGOrtTRt/UrxmUWnhbst7wqYXXGyigm2yVuqAYTLm1CVQbA6A7ZDWwPpCoRru8KZMp/P/lFs4fY1Ldq+thqm2n3f0ALuH1XefEky/OLVOYjakc2Bqvx+w8+7Az13qQXVFs+nMVXB5KcjFKxo/VzA7JzEX99nR/mGwXPKw4YZlm3Rb1rXax/l25NpzFB9u8igN+5p5cjzsfHFPc2Z3DnDmFzXXkx8Uve92NTeGfjsIe94bsMBb9YggE/6A2D2rUmpQVYrjaQFkz6DnLdUbQbQ79767mvmKMmLJZlUghIJSovBBIMIBtAzrPpTUoO8nzjuXNN6ALPWAfj4dgCHbe0g49vhXGudq1yTegffGzCC3usxmCQjCIxVmVzLBkzuuFZMfHIPJj5fj1niZcksXeUYXLZ2+rGykDnXy9ZOe1vqZ/+pZL4BwCd2ARicxQQrpGTvUb6Kqq6PLxJMKCgoKCgov35uvuCrQq7mlWmnPOf1iMzGzPfeeD9tY+Yb79VpL9d7ny3cOT8q/6jrCXbchCM5F2wP/XmVIIvmps3B53fG7H/20DT86Z8jdz0uGL790ZtBWx5ifTc+KO8Rcl/ScX02gDOUmgXcAY1W3AKavrfo+Uk36KoludlJinOTapqXVK2qKevz1nZIKCHBhIJSQ0jJlJ8Pq5hU2Xl5GrlsjiYnj6NRUJSn/uJlvionN++LVUyThya1cOp31np8j/h1tp3jzo1tF5czunkMbqEdA8zqxwBTdQKVWLIlniU5V4mSS+PI9luyionqFUxILiEQ/z7V5zNR681ZTjJVVTBR98H5Z3BuE5yJNlYpAYxWjgcWqnHATD0WmGoS67x+NDDTjhJZNI96YdU2+q5Nx5gD9t1j5zr1j+/tqpf4j+e6/Y559zCtvvjZxQ4fHsaaSjK2eolOzjotCBuWK/BvDgSe6iRCn4bUhXNYnQEvsEOBBAXTmq7fKJK+Qfh8cSbQ34mm79HK7WuFA5JKvxWKM5fI731Ham3ANeLXlKpeWt6MbAspCGxfImB2uyxY2zuMH9Lfmb9+SJ/isKGtUPXSfzPcWQPbYPONxuMelmG415hzuLtZFj57aBY2qUcW5tTpEebQ/jXu2FFKAHCHdgCz0QFcKJdMNOg2eEpV1S3yLfBqE0x1LQZ+BmqrXBrOqFUyVc6wgvv1iWNurAWwMU0APqE9wF17Ad7sQZCPuGvvB9h43T3FFg1nvNdjGLwfxtCvxIjATEv/vU0LfXxSV3183jB93NNMv3SVk2lZqNvisq1LTpRtXpRTtnbaxxJPS+J5e5JVUbAFX7F8i0MkmJBgQkFBQUFB+VG5+YJfH3KJU9Y29jFudPDme7ewzDchq1JfwvlJZ+dF51+eforzwPFoTuHYA89x4/CnQr3tjyX9Nz2U9Ay5L+m6Plvace29Ct2gux/aBt35qzXzzseWgbc/NQ+4DZquug20V9wGDfxuAa3lN4GG7w1STqh4Z1Ft8WQzkMjZSdf+Zm5SVpVQqqlFHgIJJhSUL4QWTMqcfFIwqdOCSavwZZ5m0ct8dQ47T6Wm33MzTq8/fURK88nDkgwc+531sesWf9ZKN/aNZYuYD6aNoj+ZaEQDExU4aymWFEuwvZYtLZYcarjA7SQHEkoIRN1Q+3qkJNMEArh+4Tq2Ida0lVICsFCKA6bKMcBYNRoYa0UBE+2ovyxbRIms2kfftvsjdpvTgHiHqfqJneeZpzReapeu9qPPcf/VsFgsFWHh3daSe6wx4sSADaJ9NteFa7rzBb7aHwSeGp+EXlpUNYa/DjVHCVZrVLYH61K9TRiq7EH8ylQTTLLWeLpAuKIlVennq01VMMF1suYPIAzuxxdsHHpOsFHfU7BFv+9dt8FqTCYDtfL8yQI/k+LdzAbvjm9sgR9ep4vvXqmLb16oi6900X290FL39cyhJNxZw02w+SNW4ouMz+GLTd7z5o+UYNP7S7iOXSSYXasKzKrZR2x0E4BZagPMvD4lloxUqbk/Ixk1zwj63QTE381N0ldAT4HKuVRQ2KkRz0kc45GaBFoE9QiI4z6yIXHcGxHHn8BcGxSPbibg2rYqxid2LcJnDS7iLTQs4i0y+hOfM/QM5tRlcbFV44Ev9Rla7K4Mjc+wktFVg+3eVeOV//hmZZsWjy4LX765LNz3ftnGBR9LfG0BPr0fwKyaADjrqRhKr+EMJJiQYEJBQUFBQfmxySrkN4ek55T2Pna3eNKGi69DoViacSbvhnNE7vNxR3NeWh/8s8R0z9O/9LY/Bv02PQBd12eDVoF3QWP/W6Cez02guSwLaHgTLKNQ974O1IifISreN4CKVxZQpqGExXW57ddSi1xCggkJJhSUrwyUTJx82SymPM28/Dytwpf59YpeFmjlsfM+uyDsMy6z3nyz8z1mjEy1nDwsaZlD74QTYzvGPjNvEQOMG0WDUZpRwFg5mm6HR8kle1osybfjcpKrUFK8wI0EEwLx46lp7ckEE7VmUyvX7Xi6mglWJcIKRWMlajaTYT0WMG7MAuatooqtu8SkO/aPD5lqkOQy3zJ1mJd9esu6OMf9h6MkfZbZR3I5fJEkcgFLtN0kTxDUmSfw1ZZCwUTOZFrWAAj8dKoqmciL7XKVS0ggIX5Z5MSSbA4Z3B/YHghXtqLkEqz082lEyaY13YFwkz4Q7hwtFey1T+Xvm+CG7bFpW9eLHKXmcENnNeQdXN+HF7nVindisyvv8BpX3jYvV4w5xRVbZu2KLTB0xeYMdS2eOdQfmz2YxZ09mI3PHARw174Ac+wCuDZtANeiCeAa1wdcQ9gKT5WqVqpJpiju+11m9NRUifSFOUrVkO2Hj4PHdZQawEzqA8wCzlJqDrCxrQFmowsw244AG9cVYBN6AmxiH4C59AZcp+5CzKnLU8yxUxo2uccJ3pwhEbwlxhElnmYH8Hn6y7BJ3U1fjm70TS0ry3Z7Dy07snZN2aHVd8q2eXwsWTEe4DMGUIKJeH/FsveMBBMSTCgoKCgoKD8yVwvKO0ESn/IMt199670kruDM+KM5T433PH0zfMfjkqHbH4sHb330qc/Gh6BrcDZoG3QXNFt5G2gtuwlUYEWRO93iDrJEnlpa28lXJv2dRKpruYJAggnllwtVxZRPtsnLK8jXevEqv/7LVwX189j5GoqP9RmX2X6BWbr9jJGpQS5DkhLsusc/MG8TUzKqURQYqUmgEgWMGTGVlUt2jERSLjkptMCTXaiu64vqCATiy1S1z0utXMNw/zgCKJnGMBKAGSMOGCpFAwM1FjDQYgGjpqwPlu2j88f3jc+YOiIpfL5lqpvXuPQhfs4XPzunoNQeEftmO+m9KAfJufWbxMemZYi2jMiFLb6E3g3+ItvlLSVYRl9Ah1Ub8AJ7ZVu6LgoVTHUtBBCI74R8K8bKVpAdqTUAK5WgdIViaVlDqkUefOzG4UCw1x4Ijk4XC04tSCo/vXB28ZGFrep6jaPUnOItS7uWHlnnVHpqa3DJqc0RvINrInjblkbw1kyJwJZZR2ALjSK4c4ZGcKcPSMFcez7mTuxWjjl2BJhdW8AdrUNVyhhqAa6+KuAOV6JkiXzFTW1iqa4v/NelXKpJKsnPUhpE3x7CqJJLI5UBZqJJVYhZtwSYQweAO3cH+OQ+AJ82COCz9AA+3wTgS8YCnrc94HnZAN5i0xfYzCEx+KQegdjkP6Zicwa58hYYuuKLjSdy5+obvXXp0ZHJ+LaqwtJDzCFlJ8KCyo4H3y7b4fWxZOUESjCNaUL+ncWy94wEExJMKCgoKCgoPzKZnLK+ENYDzJaZ9jLU6VjOlcFbHvI6rcuWtmXe/att0D3Qbs090GL1XdB45W1Q3+8mUF92Ayh50HJp0TWFuUkyZPOTrlMoCiYolLyu171AQSDBhPJbJa8gX4lAhVOQr5b/okCj6HVBvZevCuvlsfO1HtzMVTrPeqJ8dP1dtRC36019xmWazDdJXzVVL+WcY//EN1YdY8uNmkb9pa/BAiOUWeRFZnixeSwjAdjTckl+vovijKW6vniOQCC+jHzlofwankDPZoKSaTSx3o0YsWCEUhTQUzkDRtQ/A0xaRolsu8dhk4YmZruZpe71sk+f4ud8scvKiRfVCVRXTc5Aban+Jnx2dvMPT88ZVmQdWCRO8NsnPuBwSbShf5HQv6WUrGDyVAMCr3pA6EfNlxEGQMnUSU4wyaqYkGBC/ELIyyWZYCIrl9oAoX9zqn0krF6Cs5dgdV9IfyDcPeaTIGL2B0GM70t+4urT5UlB0/H4lbp1vcZRqifT2Fj1rb9Tc3yTx+jSA8x1JUdDMkoOry3i7fYv4oXOK8JXTijCPS2L8HkGRdiMQUXcyT3eFzu253Ntm3/kjtYGXNN6oHikOijWVwPFw5VB8TAlSpTI5gPJBNPvLhgUBZP8DKVKiGNHHj+CIXCrTPxMoAfbC6oArrEm4Fo2AphtS4BN6ADwSd0BPq3/X7zZQ6W8BYYSnruFhOdtI+GtmiThbXCTlGxyl5SEzcdLAiZl4EtMmfjU/qN5Tp3b4y59dPGZQ3Wx+fptX00b1qzAuKPmt3xnWE5OKuVHgw3KT28PLovYcLdsuxdVwQRb5MHvxAgkmJBgQkFBQUFBqaOk55TqQY7fKZ7kHV+wx2zXk4e6q+98aOhzA2h53wD1fG+SM5Q0l98kxQI5O8mTlkZk9ZJcBZNMLslXMC25/vlMpaVIMP1nQIIJ5RdLQVG+EiS/KF+l8GWB2ss3BRqvXhdq5LEL6j28xa53Ieppq2PB93qEumUZL7PP9JhrmHbKZUBSgW23BGDWKhqMaMACw5XPgBGMKGDEiCErGqBcmsCoXrlUvXoJCSYE4r9AbYIJtsxzJCVTElmtaMqIAyMZ0WA4gzgfqJ8BI5uwwOj2McCxb0L5LMOUy5426SH+zhcnrJqU0TdgUkb7wCkZjdZMv/yPJVNubp5Sbi4HokygksvOU2FDOPnKHE6+EievQCmvksIvwuEUKEPY7Hxldm6+Cjs3T4XDzlPmED/nEc/1Pc+335KSgszGUvaFXpK7p60l50OWiU+7nRRvN30qCvpDKlzejJRLpGDy0QZCv+aUZArsUL1VHhJMiF+NaoKJbo23qi0tl5pQ1UtQMsH1sK4nEG43BoLDk3h8lleOIHFtmuDcxpDytE3j8Ph1SDD9RCkY17Fx8ULjrtiqSaa8je4+JTuXx/J2+r4u2eIJeOtmA57fBIAvMgfYbH2AuQ4A3Ik9AHd8B8C1bg645g2o2UojlEDxcAY5cwe2RatsjVZT9VJdX+T/N4RRbdQ0V0leLskEk74SAZylBNsKKsxRMmxAzVEyawy4Y5oBrn1bgE3sCrBpfYnPZDDA5g0vwxeMzOO5m9zFPS2zcF/bLDzAJQsPnZfF2+WTVXogMKtkr/8FPGTuNtxrjNPbGQM6fo/vzbuNy+qXnAw1KY3cElZ2LDi7bKvHxxI/e4BP7QOw0Y2QYEKCCQUFBQUFpe6S/IxnAjlw493sBZGco8PCHuQ08s4CSguuAsaCK0DJ/To1O4mUDbQoguLIvQYq2+LV0BqvprZ4SDD9/CDBhPILpvBVvlLBy3zlF68KVF6+KVR9+apQlZNbUP/BTXbrC6xnesc3ZE8OdcsK8LLOODV9aGr2+G5nxZatY4Fhoyigp34G6DFYYBQjhpzHYkPLJVlbrYk1yiUkmBCI/wKyOUyOCpJpIrm2KckE56zBKiZjWMXEiALDVFhAr94ZYNwsGth0jgOuQ5KKFo9OO+fndHF7wOQMt8ApGWarp2Z0XDPj8mdz3r42ubl5lFjK5agRqOey89TZbDhLLl+Vw8lX4eQVKOdVUvglVDicAogqm52vxs7NV2fn5qlz2HmqHHa+Sh4nv84qrQoKMjX5D9NaSLNZvaQZW+zFMV7B4gMTrog3DS8jBRJsBQbbgME2efDCOpRMq9rRF+FlrfJk7cR+AjGAQPy/wO8xU37+UieFuUsyudQSCNd2B8ItBkB4wEEsODX/IT9h5Sl+SmgAP22LS2n6liHlscHN6mpto1RPpjFD9e30/r1xjzFOeOBkZknwnCjehrlPeEzXD7zl4ymxNGM4wJz7AO64boBr0wFwx7YB3NHNQLFZfcAdpUqJg+G0WBpWRbXKJfnWeHV9kf/fEEs1iaSa0GN8LpsMlAHXUA1wjbQAZtYIYBZNADZaB2BjWgLMqjXArNsBzK4DwCZ0BdjkXgCbNQTgi40B7m0FcB+bj7i39XPca0wsvtRiE7Fl4n7jmDhzMhPfvJiJ71vFLDmylsk7EODH27Rw0vtlY/oVzPi2SqXaUryb2aD0+AbT0hObwkoPr8ku3ez+scTXFuCuxHu0bEj9fTLBhOQSEkwoKCgoKCg/MvGPcUtI+NU382dH5ET0X3cvRxNWIc2+BBhzCKBokpdEpDRSEEg1iaRqUikLzVb6r4IEE8ovnIIXBUovXhYqFxYWKuc8LdC+d43dJ/30U9ej6+9tXT/r+nl3iws5Ln2S8TGt48CohtFAX50F9JRZZOUCbI1nxUgg22Y5yV2ArpJLsovVdX/RHIFAfD2ydevEqKpKhGvbhVzfqeRjoFi2YMSTVYz6SlFgmOoZMEKTBcxbxADHnmdFbkapRT7jLtxd6XLxcMDkjPmBrhkD10y//I9mMlHVS3kyuaRBoJnLztNks/M02Jx8dQ6UTHkFKl8hmIjHFKpyOAVqBOpsdr4GOzdfk52bp8lhQ8mUrwYFUx6noE6qmJhMpnJB5hHNkswjjSsyNveXnPWfJ46YcVq8x4ojChvyF1mZRM6b0abwbQqEK1oBYUB7+oJ8JznBhKqYEP91FL7P5Nwl4ru+qqo1ngBC3BYEdQaCjcOAYK8NEByfUcCP8WIJEgM9+CnBRuWpod0FCetbFhxhfpcL3Cj/f7h2Om3eT+s/Hl9iuRH3d7zIC3Bm83ztS/BFJgCfNhBgDt0A16ot4JrqAK5RE8A1bASKDesTaILikVTlUrVWb/IVSzKB8qvJJXnB9DVCSfGYjCSOmaEyKecwEw2AmdWnZilZ6QDMphXA7NsBbDwUSl0A5twdYJN6A2zqAIDPGQ7wxcTn4msHcOYUwAueA/D1s97xVk9OxPzs/HleFmNxTzN9fNkYfTzASR/fOE8f3+Wvjx9ao4/t9xvKDZ77x4sF1k2+13eHFEyH15qWHtsQVnowMLtk46KPvGXWAJ/SE3AtGlB/q6ySDQkmJJhQUFBQUFB+ZGIfYWMgu668nj/zWM6xfmvuPlVfdPUDY2YmYMwimH+FkkdLFclC4uh3AAkmlN8kzx4WNL19iT0i5cQT3wPMu8mrp15962aY/mFc57OfTLVjwAg1FtBTYgEDRhQwYcSScsmOkUjPXEqtJphQxRIC8d9HVs3kJCeY4Bb+PI5ulWfOiAeGjBiqVR5xfhjVIArYdowH04cn/+UxNl3o63jh2oqJFwNXTcoYHjT18jeLG1ouKRNQlUtQLuVytHLZeVpsKJmqCyaawi8hL5g02bn5WuzcPC0OO0+Dw85Xz+PAKqYCJdh2j7ifAL4+dfvfOO/WEiVBclgrSbz/WPFpt/XigxPSRFsNi0RrewpFsA2YT2Mg9IaVTNqUcFrZlp7H1LGqnRgSTIj/PJ3kKvM6VsmlFS2I731TsoKJlEvEfsGGfh/5O8zKBUdc3goiF53jx/mu5icEmpSxmE3v7nNTY7GcVOC6+toFyGQylF9u0dcqDbduwt06ujW+2VKXYpQutsW0bfkmY51ipnGDTKax6r94HvhlwmQwlAuMGZoEjYuNGa241q1Miqf0WYktMEzjeYwu5nmYf8DdRgDMpQfArFsBrnFDUKyvDoqHKIPiwcrUdihsh0egKJHkRdKvJpRqEkzyYkl+1pS8UNJTotrfjVCmK5VUiWOqAbjm9QGcXYXZ6ADMvjXAHHQBNqGjFHPqxONO7Poam/hHETa5dxE2vX8RNmtIETZ/ZBHuYVGE+40rwtfOKMI3exThO32KeFs9r2DrZody/R1tuJ6GrdnuXTUorCh2uJM8ZTqp02vku/33kxRMB5imvCNBYSV7V2WXhM3/yINVVZN7AK5FfSSYkGBCQUFBQUGpu8Q+wkZDdl55M2/GsZyjfdfce6y26KqUMfMSYMz+gmCqa/GBQIIJBeU75dmDAqUHt/LbXE3LGRN78FHodr+bd3wcMz+6DkkBY9rEA0PNaKDPYFXOXRrNiCflkgMjia5wqN4aDwkmBOK/j3y7PKqKiVrr8Da8H0qmsfQ8JiieYetMA3UWGN0qFjj3OwvmmqQCd+u0J172F4J9HS8O+9bzEi2WVAhUCTTIiiWqcgmKJXhbndiq/YMKJkoysfM1OOwCTWKrmUc8Xx6nQCaY4FwnFTY7n35t8rbyj5RML1lLtQTxy/uKT7tNFh90WifeaZIs2tAvVxSgK4bzmMg2eVAywVZ5/i2pC+/wAjyzU/V2eXUuCRCIf0pnudliHei5Sy2AcDkll4T+OpRcCu4N+FtGlgr22j0QHJ+ZyGd5BPFj/R14icz2/3T9FTCNNfEdVu3K9tgMK99ra18Wbu1atnMMgZlr6RYT55KtxsZlYaO64czhjb7nuv9V87Q3Q/2lPqPtG2O1Ie9M69kWj23mjzl2YXGn9uXgMwYDfGp/gDl1BdyxzQHXWJNqfTeYYADNQPpn2AavttlKhjR1fTH//8GwBhTl0ghGlUyStQSUbwsIhdIIOFdJlW6BpwG4sK3gmCaAa9cKcB07AmxKD4BN7wewmQMAd3r/15hr7+vY5B7R3Ck9I7jT+kRwZw+J4M4bEcFdYhqBLbOOwAJcIrCweRG83csjePsCIrBdfiG8kAWTMf8JPX70d6l498IGGBRMB5hhJeH+2SWh85BgQoIJBQUFBQXl50jcY9wCsvvKm7kzI3IP912X/UjN/ZqUMfsy1SJv4dUaZif9BOIDgQQTCsp3SvbV/AY3LnJ6nYt5Nun4tuw96xZdezJ/TDpw6JUITJvGgBGqUaRcks1dsmWcBQ70BWhnuqKhauZS3V8YRyAQ3w+qXV7KZ8D9cB7TGHIeUwwwYEQDAxUWcc6IBnbd4sDkYUlglnHK8wWW6SGethf1vuWclMuWtcWDlUt5VCs7WGXEyYdUiiU2nL/EyVfm5OVDuaREUVgbyhxSHhXI5jCRlUx5Vajl01VQ5HOz89WJ1ybIVyNuw59/6HwmPsu/ueDk3AHCwxNtxLssgoQbhyUL13R/TVYrwflLsJIJAoXTipZfmMeERBPiv0QnGplgoucurWgFBMubUm3x4HZVWyBY1xMINusB/u7Rz/mHnE+Un5jtWxrpbslnefd6k8j8x/8m54YaNCzdZTuoPNxmZvlu203lu8dGlO8eE1G+3SKifJvJ/rJtRktLt5uYcbcatv6ea/5Xzbt+jPrFxmoD3ptqTi021woptmyUUmzd8jHXrg0fs9cFmE1rwP0fe+cB1kTSxvEAAir23nu501Pv7GABRBFEsYGAYlfsjS7NYAMBQUCxYsOzoKg0u2JFUQQbKl1RShJqOljeb2Z3gxHx5Dw/Kc7/ef7PbJJNdrMzO+L88r7v2CY0XNKg4QAFlPoz7UCm1tIQ1j/DpZoGmeSfL6/uknw0F/U6jlZSYsCSCvC06wBvdH3g6TeF3EntINesB+TOGwB5y0ZC3qrRkLtqtDBv6Yjo3Pn9/XNn9l6Wa9bTPHdGL/Pcuf3NcxdpmOcu1zHPtTYwz3U2M891X2SeG2BnnrvL2Tw/wM6As2lJ33w744Y/eyyVBUz5WxZ9wHWhcuUBk6wGU3lj5Vc0AUxEREREREQ/R6HP8kdh77ydPW/+38l7+7nFP1ZdEy1lLboJLIsbwFp+i6S/+5VNABNRDdX14FSFm6dSFW+HpTW8FZ7S7XJIom7wvieWfutijtqYR72YMezce71OZ2BEvVOgoXgSRjB1l8ZRdZciSmuzTGMWmkm9JWLimmv5exzXZpK/9zFw1kVzA45uHI7mCs0GJ0G3XQhM7HUWTAaGP5sz/IL3Ut0revZTbjbaYhGjHOj8SOnszoR/jAZKSpalxUtVRa6N09lhuJSamq5MAaBUKspIIRkZtymp344uwpAphUp/RxtHKuGopjTateiWAky10GdiqEQdOykJR0tRjzGU+uI4iYnJCi9fJn3t+Ao43VawsbESThX0b1J14dReeUdmNBDvndFOtGeKoXiHrqfIe3iM2O1PkXhdlw8UVMIRTKWQqRW9EL+uMwFMxNXYcoCJajvS8HRtCxCi8U4ZjX2ha9ePwi0D3wn9R2UL90wK5x8wt+EHLRgh2L+iec5ha7WK3GNfU7776IaF/rqjivx1N/L9x94U+Otm0B6TwfcdnYAcWLRNx7zQb1TX/3KcX0WpA1gNc7Rr63C067ryRtW5yh1Vl8PVrivgadX9iAy8kao0FBmm8AmclFdHqGw6vMpeuP8vLpvWrzyAVPZ7UjWUlICniVPeoeulhSESunbaKvS2lvJ7nqZyMVdLWcrVVpVyR6tJuXqNpVzDNlKeSTcpb95fUt4KHWmu3URprtM0aa7D1Be5lmMPcBcOncMx790v07Rre9p/tM+cO6h95tKR7TMtddtnOk5sn7lxbvu8rZbt83Y4tudsW9WSZzuvPpvF+qk/usCSAaa8vWyP/J2Ocfkeiz/kWY+jorJKazARwEQAExERERERUWUoLCFfC3vXnZw5C46l7Plzy6NHta3uSllLbtHp8VbcrnzIQUwAExHRD9LVoDSFa0HpylePpKldO5La/OrR1F4XgpLGhuxOWL7H7aG/69LblyzGXUqd2DdUotUqBNRrB4OGwknQYp2GsaV1lyKpdFkmTCRDZS9+ExMT/zzTkYvnwJSBTJOpVHmhoIPmiBGKJ2F43WDQan4SdDuHfDDsFfrCdOC5Qxajriyzm3JzuMei+7/vX/e4bdiuhAY3zr5UiY+mwUxKWrJCWkaKQurrVIWUtFTFpGQqLZ5KUjINl5JT0mqnpKarMHWWFND2f05Xh2stYeiURluRNpVmD0cw4QgpVerYtHHNplp05BNOl4ejq1KUEhOTsWu9fJmEjbcV0fOl55bsp6/KPzSrqXj/3PbS4yu6SiI3dhTc3N88ISFY5d+ca/Hxpb9L/p43X3zQLEiyc/xzsddQjpjdRUTVYKLqMTWgIROVKq8jvTAvny5vHYFMxFXdDFiixiszZp07MKnxWqLx3QyEaIwL0bZwXUcQbO6TL/AenigM0L8o3GO0ueiguYFw74KW/3VewEpnd6pd6KGhW+Q1dAd/q3q6wHsECLZpg8B/DAi260n4AePPFW0ft4zvr/vTU4RVR70ezmqco6k6gatZZwdXUzWZN1IFeMOVvqwjpF4DYMA/RVOVhUjyIA1fAwxFBslZBknwezBYwiBpdF3gjW0AvHFNgTehBZ32Drd6TYq4o+un8HRqP+BqKUdzR9WO5urWj+YaNI3mTukQnTvj9+hcC/XoXOvx0Xlss+i8TXOj89abH+PZGVrmWAwdkjWhTbX4P2wpYAp0JYCJACYiIiIiIqKqpbCEfE3sXXdyZi84nrL7T49Hj2pb35VSqfEIYCImgImohunq4bRa14LS618NSm935WDqn+f2JU885ffcet/6R3vdVty9umrqtQSToZG8MZ1PlwxrdBKGKAdTqa/o6KUwajGZXlzGdZfOE8BETPyL2YiBy2bo/sfzwFQ0J8iimEYqnAINPGfUPwGarU5+0O1yJnNq38hb8zUvH7SdfMvRY/H9mQdcH2uF7X7e7cbZl43j7yYpv3ierJiSlqyU+jqFckpaaq2kZAyXKMCjmpKSrsrApVq4xtL/Y15MKwVNsjpO1LFUqGPTVmFS6inT0U04uipFJTExGVv15cskymgbP6+EXqcgU36wRcPiI3N7SY4t0ikOWTNZetndoOT+kUHCtCv/aiE8/7J7Q8mFzSOkka42xadWHZfsM4oReQzMFDm2eS+0qg9Cy7ogtGkAQocWVOowCjJRgKnrpzRjlQ4QiIn/wTIg6srUXcJj2LENU3epKWXh2lYgRM8LN/wuEXgMeSzwG3VUsHOCI3+P8WR+oHlPHC34I+aDWAuWcuGGP3T563vuFWzoyRVs7gcCLw0Q+OsCf9dk4O81jiraa7I6b5dxrx9xvJquN+qsJpzhSpO5I5UDuSNqZVGp3NQZCDBQDqYMZYBARWBNVXR5NZTkz7ssWJKHSvg6DED+S84DmH2GK9BwSbc+8AyaAW9KO+CZ9gDerD7Am/Mn8Gb2+sAz6vSCa9A8hDe6jidHS4VNWbcemzO+GZtj1IHNM/+DzVs8nM2zNWTzXGexeW4L2LkbZi/JtZ2kw7MYUG1SPX6KYHL1yA9wjMvfsvhDntU4OkXeaDnAJJ9OsbLHRWWbACYiIiIiIqKfo88A07HkPX9uiWcA000CmIgJYCKqcboalKYa9Xd6i2tB6X9e2p8y8ax/ou0B16cHPZc9uGtjdPPNrOEX8wx6hoo1W5z6MFQtGIYoBcNw1ikYwzoD41nh1AIzAUzExL+ujZjIJRlgwhFNOLJRj3UWtNBcoYHmjKG1T8CwxsEfR7UNEUz8LeLt3GGXnllPvHl5i8X9HfvXPVoWuitB68aZl13io5MavHierJySlqyc+jqlFnZKWiqusVSbhktpKilUWrxXtVLTXlF1lv6f8+OnOk44UupVLTol3ytsFQY4qdDRTDh1X0rtxMTkOsh1X75MooxhE3q+lgwwCY8uaCk5Ml9HemzBMsnJVRuKL2x0KYk5NLsk8cqggvT4RhU9r+DgYCVJ/LFO0vtBesXXfG2LT60JEgfox4k3/sanojowYLKuB0L7JlT6MCrqA6cWK61jI4tiIqCJuCpaFm3XlQZMVPRSOwYuNaFTQdo3B6FzBwyXQLhlQLrAZ2Sw0H/MKn6AwYjCgKld8vxmNPhR80ABu1Mj/to2hkL75oHCtS2zBei8BFsGAX+7HvD3mX4sOjjnStHBuStz9878/UcdsyYLA6YcDdZEjobiHp6GQgZPXYEGLIMZyyKYanJtpbKRS/KQSQaaZJBJ5kHMPriukk4d4Bk0Ad6U9sAz7wU8i6HAWzUaeGvGAneZZjZ39p/h3Mkd7Lk6anocTZY6ZZ066hy9JuqcyW3VOWa/qXMWaahzrMerc5zN1Dnr56lz2LP65tnqt0vW76Za2WOkopJPkZcbsDYub8uiD7m4BpOZHGAaxFxTEr1EABMREREREdHP1Ocp8hjAZBUtZS0hgIk4mgAmohqnK4dT60YdSet0NShN+/ze5CXBHs8DdljF33Axjc5apHn1/ZRekR902pz5OKzBSRiiGgxDFYNhJCsEdFlnYQIBTMTEv7xlgEk2B2DANBHNDfpojtBGc4WGQjAMUT4B6vWCQbN5yMfxXcLfzxp8qcRy3A3O5rkxN/Y6xvuc2Z4wMyrk5eD46KTWiS+T66ZlpKikZ6bWSn+bWis1PY0GTHTkknJq2islCi6lvfq/wiV5YciUho6JrIRci4ZMVAQTBkyqycm4NlNKHQYwqb18mayG28TEFPw8jnDCqfQURAcXdig+PGua9NBsL+mJRWeKwx1OFV/f7lHyKGRWcfKN/vzE2GbJyecqtLjHTYiqJ31xpYf0/okJxZc2u0oOzzwv8hqSLXRu94GKXrLCUUz1QWjXGKj6THiBfl1nApiIq7iZekuydI44kgnXEnNsBSL7JiCyaYjc4IPIvqVY4NI5X7ipT5bQS/2CwGfkOoGvjnZhgEHjYGOW0o+473FqvCJ2uyZChxZ9+bYN5wss1f4WWtd7I3BsCwK3/sDfYQCFB+cKio4sjSg6unxp7gELkiKvAnrdh9WYN5g1nqvO2s4dykosTYcna+VrDlX2Yvy/AUbl1U1S/4rl60lpKACVInC4MvBG4PpTtZHrAG8krkdVD7k+3Q6v/ZE7QlnA1VTl8MaoZfAmNMvgmXTJ4M0bkMFbPSaD5zA1g+dkksG1M7zBsxi+hTutyziOjlrL5G4s1VLry9yN9gr9UsdaDFBmV0Idpf+iLwCT+6IPuZYEMBHAREREREREVAVEABMxAUxEv5LO702uf3l/yu8X9qVODvNPXHd43dMQr4WxL6zG3pLM7HcJDNqFwchGIaBeJxiGKtP1l7RZp0GPqb+EF5hli8vTCGAiJv7lLANMJnKQGafONGDqMA1nnaTA9NDawdRcotc2DMz6XITl2tfB1fRuasCauJCTW586XDn+wjDuTtLvSYkpTV5npapkcNJqvc5Oq5X2Ol05JRXDpVeo/flwSaY0dEwGMimm4vNITcc1mJSZCCaVpKQUKooJuW5iYkpd3CYl4ZpRqfh1tG+aknD/wq7i/SZzJfunHZQemhVfHLz0SXGky/mSGzv8Sh7+bfHuaegw0ctLbXCEUgVOSSEv+VyD4qehfUtuBiwoDrE8INlpkCDc/Adf5NDyndC6Pgit1KhIJiriAy/Q4xo26+RqMZF6TMRVyWy5yCXZ2MRwCdcSW9sMRBiW2jbEUUwSkWObDKFr93sCtz/PCryGuAp8Rk7J9x3d4Qfe8goFjp07Chw7j+Q7tFzAt6nvLVijekWwpm6OwLEN8N0HQNHOSVAYtCi/4IRlaP4Jq8W8oFU9f+Dxa6wYwGTAHcry5Q1lJXwGlWQQoLqAgLJgSS4SKXcw8iDGA+XMPFcKPUbUAt4oNeCNaQQ8vebAHdcauBPaAXdiZ+BO6QFco9/odkJ7AW9sk2dcnfrneWPqB/EmNAviTesSxFswJIhnPS6It25GEG/97CCuk5F7zvKR03kmXXpUdl//v0UBpp1Oo3i72R68HfZxuW4EMBHAREREREREVEVEABMxAUxEv5LObktsHOGf1D/UN2l2sPsLnz3Wj65sNI3JWD7s+geTbudhbNNQGF73FKgrnwQNpZMwgqq/dBr0WaFUlAKOVpjG1GDBrVEVWPAmJib+ecb3vPEXgCkSxrPCqFSaI3GaPIWT1BwyQi0EdJuFgjGaWywGXwMHgzu5Pgsf3Dqy/vH28wcTLO5HJWq8fJ7c5tVbCjApZuSkK6a/oaASlRYvJbVy4JJMDGRSSE2l0vMppqSkKyUnpyklJaXWwqnwcLQS2qZS5jEp/ei0fowFgXN7iHdPspDsMTwh2TMpQ7LfJFd6ZF6KNMTyTvE51wPSKN/FJbcDB3KjgutV5HzYbLYiBlLSmCADycUNGyVH518S++mkiTb0LBLZN39PpcmzrAMi6/r0Ar2sHlNphIisHhOBTMSVaWYMfgaY5OCSQws6eske111qDkLH1kUily6xwo29AvnuA6wLPYboCrxG9MpiD/hhf3fjtHgCdjctoXNHS6Fjq8MC64ZRwjV1kgTW9fkC547A9xwKRXuMoeDIstz8kzah+afsF/OCCWCqiCjApMEAJnVWwhdgqboBpq/UUqJg0gDk/nIewDw/mHnPyFrA06kHXIPmwJ3UAbjG3YE7vTdwZ/UH7oJhwF06Grgr9FCrA5xZg9I4U7qc4uo1deKMUTPnGDQ250zrYM5ZMMicY21gzmHPMOesn2XOczA24CwZ0TfVuEvDyu7r/7e+BEwWH3hr9ICHazCNqUdf47KAqbqMLQKYiIiIiIiIqrcIYCImgInoV9KJTc+bnXJ/oRG8+cWyIOdne/2XxN1xMbybvaj/1fdG7c+BboNQGKkaAsNrnYIRSqdAixVCLRobsMJgEhPBZMzAJWMCmIiJfznLANM0uSjGKeg5nEJzLJUm7zSMUEBziFIImktOw+j6oTC5zTmY0+sKWGneLHKfHvMk0C4++OyOJ063wl+Me3w/sXNSUrJyWkaqwuvMdIX0jFcKaemvlbBT015XGlySV2rqK6o2U0pKukJycppCUlIqcopicnKqIgZOKSlpOLqJqdmEU+lRgEmVf2h2D0GAoYUoQP+keLsuR7J9zHuJv65YvMswX3rA/LH05Br/4oubJ4luB7ap6Lnkx15uWPL47BDp7d2LpBHOuyWHZ94UbxvxWszuIqbq1WDAZFkXRLaN6FR5Tu1A5NLpy0iRSocMxL+uZYBJNiZx3aWONBB1aM7AJWSnViBE+wvW9ywQuPW9zN8yaK3AQ11TsHlE8xzPvmo/4t5ms1mKCezeKgXre/cTsHssFTh3PCZY2ypRYNOQJ7JuIBDaN30ncO0BRT6aULhvOuQfXcXLD7EPzT/luJgXbEsAUwX0ejgDmIazfHnDWQm84ThFnMInYFOdIMDXANMQWaSSAuQORB6kCLmDkYcgqytB7ghl4I2qC7yxjYA3oSVwp3Z+xzHrVcyZ85c0Z9Ewac6KMdIcm8nSHPYsac7G+dKcdeY8zupxlzkz+7lwDFqOzhxZp32mLvLENu0z5/7RPtNSt32moylljoNhy5fzhtVnV7N0d98jDJhyKMDk4sH1t4vjbSaAiQAmIiIiIiKiKiICmIgJYCL6lXTY6WnLv9c90w5yfma9z/rx31vnxj50GHubu/CPKyVTW56DsXVDQUs5BDSVQkBLMYSKXsKLxuMJYCImJmZ9HTDhFJo4leZo1hnQUjgNmoqnQavWGRhdOxQMm0SCeedLH1cOvi7YMPluys6VsRePuz/yunDomcntcwk9H0YnKsvPU2nprxXSX2copL2qGoDpW8LgiY5ykqXSoyOY+PtndRPvMJgn2qF/XOynzZV4qYPY7S/kASDaOjJfvM80VHrGbknx7e29s2LD60ZFRdX61rHeRAfXoWoxPTmjL721y7I41P6gdL9xrMijfwG1QI9T5GHIZFOfigAROcinyiP1mIirguUA0zpmPOKaYThyCafFs2sEorXNqagmoVtfEGzVEPN9tc8LfMcsLvQZ3eVH3bfJK7qp5m0Z0q7A/a9+/I19ZwvY3QKEjm3jMVQS4tpPto1B6NgGBJv6QJHfGCjcPwvyj6/m5oesDeURwFRhUYBpBMuAO1LRlzdCMYE3UhFQWzMAE2X0XTRqoddU0T510XfDdZQaAE+rIfBGNQaebjPgGbQC7uT2wDXqAlyT7oWcmb1TuLP/esCx0IjOWa4TnWMzMTrHdWZ0jufy6JxtVtE5HssucdYab+XOHWKUqdumfWX3YVURAUwEMBEREREREVVZEcBETAAT0a+kQOvHrQ/YPRm73+aJy87l8aHupjEvbDRvFs3tfvn95MaRMFY5FEYpnoZRCqdhNGp1WWdhHDJePJ4sB5houETqLxET/2qWASZjCi6dp+YBDJgmsiLQXBFGAenRCmdBB3mU4lkYoxQKE+pFwvQ2F2FZv6jidePuZPsuvH93/9qHu4M9H80J3/P4jysnnqmUnatev82oFnBJJjrKiUqlx0Q0pSnz90/vLN5tOEu8c/wRsa92tth9AIidu4JobQcQOfd8L96mEy05sXy9NCpgtPjp2fa8l7frf6seE06Tx38R07Q4+WYv6bOIscU3A9ZKT606I96h/0q8qTeI8SI9TpGHjRfq7ZuByLFNmVR5nT93pQMH4l/HnT+3C4ZLaGw6tqaBqG0D1DaiopmEbn1AsE0b+LsnFxftMz3PPzBjHneHcasfdc/ytgxrU7h1hI7AbdBS/sY/9gqcO98U2rXgUfeOlRp1/widO4AA3beFO8ZBwcF5kHvckpsb4kAA078QDZiUDLiatXx5msoJPM1awBupBLwRTCRTdYMAw/B5Y0CGvsNIZeBp1QbeqPrAG90UeHqtgDeuHfDGdwDuxC7AndoDuGZ/AGf2AOAsGIqs/p47f8hzzvxBp5A9OYuHs7NXjmZn209hZ2+Yx872sWRn+9uzs7etsst2NpuWY6HeJ6E364t/H39Vcdk0YOLscvHg+tnFcTfRgIkrD5gGE8BEABMREREREVEliAAmYgKYiH4l7VoR33bv6kfjd6+Md/Nb+PDSxin30i3Vb0jmdLz0cXL9SNBTpOuojGGdBT2Fs1TtpfFM/aUprAhmgflcqSt7sZuYmPjnW34OwMAJA6ZJaH7AkY54ztBTCAVd5DEs3IbBBNUIMGt+AZb0vvrBSfdWvtfMu/E7lt0/tM86dtEh54d/nvB6VCMW0D6l0kvDqfMUhYFmHUT7TM0k+4z2SgL0U8Xugyi4JFzTFITWrT4INw1+LDk0b4/kkteCd/FnNcQpN9pnZcV+82+J5ORk1cLXTxpLXz/oUvzo9JSSKx5ekr/nRYt9tQrEG3qCGKfGwynyKDdGx5RLlfdZ7ZsuBDAR/2TLA6ZOdHSdY1s0RnH0UhN6zDq2AOH6HiD0Hg78PVOh6IhFPv/4ijP84NVzeMeWVzid5D8J12/ie2qq8z01LAVuA48LXH97KnRsky2yafhOZFkbKNs1plP0eQ6GwgBDyD+0AHjHLbm8kwQw/RtRgElb1YCrrezL01ZJ4GmpAAWZqCgmhaodxfTZuSnQ54zrKGmrAk9HDbi6DYE7rjlwJ7QF7uTOwDXuAVyT3sCd0Q84swcCZ+EwyFk+GrKtJkC23WTIsTHMzFk1JjR7yXA77vxBepx5g9U5yzTVOdbj1TnrZ6lzPFerc3ys1bO9Vg16YzO1++vpfRpXdv9VJSVgwORPAyaOr10cZ+PCD9zVY4Fr1pMAJgKYiIiIiIiIKlcEMBETwET0K2nH4rj2O5fFTwpYErfVZ07sDdcJd7NWD7z+bla7SzC5biToK9ARCHiR2EAhlFowNmTS4xHARExMjF12DpABJlyHCc8ZBmgeGYesx6JtWCsCTJtcgMW/Xf3oMOom3900OsFnzr2jvvNjlm1fHNN/n22samXPjf8PiXabtxYFzZkkDZqzTbp36kOx13CpaG3Hj8KVjUC4smGx0On3JNGuKWGS8HVuxQ+CzEqSov4sSI9vVMGPV3jzJrpOSfLN/iX3g5YUR677W3pw+jPJtuECsWu3d9SCvW1DJpKpCZ0qz6k9ULVuCGAirjTLRy91oKPrMAC1a0qPUzxu2Z1AuGUACALGSYoOzc0tDLZ6VHjWcU9RqLNpfrBdh/9yT6aztWrzN+s0zfce2Ye/dfg8vseQA/yNfV4InDuXCO2bfRBZ1QPRGhU6zaR9ExC6dgWB11Ao3DnxE2AKXhvKIYCpwioFTDp1fHmjVBMoOKOpXD0BE468wuev2wB441sCd0pH4JrgKKXeHznm/QQ5s/tzcuYOyshZoJGRvUQzI3uNfkbWWuOMTNfZGZkb5mdkr5sZlWUz0Q29ps9ZMKRlsn43Vcor9OW8QjWBbawSpaWFU6ZWq0je/7cIYCKAiYiIiIiIqMqKACbiHwGYbqfxO8UQwERUDeQ3P7bDdouHRn4LYv29ZtyPcdGLzlv5Z9SHmS0vwmSVSCrF1TgWA5YUwqnUeJOo9HgRBDARExNTLg8w4TkCp8nDcwaeOyYgj2PRNlSMAJMG58Gi+xWwH3lDsmnqnWQP0+hTHqZ3V3nNuDtwx9L7NRIwCQ4vbiENXqonObFsg+TwrKsi3zE5IufuIuGKhu8FS1RLhNZtsoVbNB5K/154pviaj7P02dmxolexrf/NMUQZcW3ePb8y+t3tvQ7F4WtPSvebPBd7DcmjUuLhCAwrNRBSkKkZiBxag8i5PbWAT8OlrgQwEf9E47HW5VMdMBxVR0UuNaXrHdk3ByEat0K3fiDYpvOhKNA0nX9sxfXC0457CsLWry4IddXmBrP/S4o8hYLt4zoW+OlrFm4btbDIQ307f1PfaIFzF5HAvhW6TxqCyFINRFZ1QWTTgImk6g4CL3UoDJgI+QfnA+/Yai4v2D6Uc8KeAKYKqloDJg0WcGWgAp+rpgrwxtQH7oTWwDXpCZy5A4GzeATkLNEUZC/RfJa9aPj5HAuNoJwlI4JyVo4JyrGZFJS1zjwoy21RUJbH8qCsDQs35zgYmb5ZNLJ7ZfdLdRQNmOxHZQc4eWT72sZxNiz4wF1FABMBTERERERERFVABDAR/1fAdPZpns6tVH6ne68IYCKq+vKZHdvJd95DE585D3ZvMbkf7zT6Dn9572swo9lFmKQUAQascOQwBixFUIvG8nCJmJiYuDxPZtGQaRLjiVTKPHpOMUTtNLXzsLDzZbDRuP5uw8Tbr9yMokPdpkZbbjGJHuy38H7typ4b/x/iH7VqJgm11ZactbOXHlt6WrJz4kvh+j75wjVNSwSLlT7wl9UXCB07Zon8RicUh6w+XHJ334Li51F/REVF1aroMXAUkzQjtuv7hAjDd7d3OhefsTwj3T3+hXjzH1Jc1wbDJaFVPRDaMAv4OGKEimIigIn4Z1k+LZ4saq4jHb1k3wyEGC7ZNQWhUzsQbuwNAp+RwN89JY9/eMHVwpPWnvlnnM0LwtZrck85dc87wm7wvfdjgY9WowL/8Vp8X33rIm+tIP7mgdGCdd0zhXYt0T3CwCVZ7TKH5iByaQvCDT2BjyOYdkyAvANzgXt0FZd3wpYCTJlBBDBVRP8MmFhVFzDh81FnAVedhkxcXHNplBpwDVoAB8MlnP5ujQFk2xtBtu3UtKw1Biezlo1y4izSMOcsGmGetVzHPMva0DyLPcP8jfsi8zeey82zNywY98Zhat/kFUO+exz/yioLmHI2LPjAWaULXNOewBtdj+ov3qAygKmyx1FlmwAmIiIiIiKinyMCmIh/BGC6mcrvdJcAJqJqoK3mDzr7zI6dvnXmg31uRjFPHbRvi5f+fg2mN7kAkxTwgnA4leZqEgWVKn/RmpiYuHp4Shlj4GTIoucU3BrXOQfzO14Cq6HXP7qOv/3GbWp0hJtRtI2H6d0hvjUUMBUFr2kiCXccLg53WiU5tfqweL9ZrNB9SI7Qrm2xYInSR4GF4nvBqjpSoWuPIvHeyTcl59mbpfHBBuKU++2Dg4OVKngYBS43oV5xevRv7+PPTCq+snWz9OjCy+JtmhzRhu4fhXgB37oBFZ1BLeTjiBHndvTCP0mRR/xT3Bm+qL3k0p5O22jXBIR29LgUsruCcMvAD4Lt+lJBoHlc0d9L/QtPWU/jnrLpnnXUqhk3eGm9KLZWheGrTGw2SzGB3VulwG98vyJ/vaVFvqNPFHmqJ/HX984XrG1bLLRE98fqOjRgsm0CIseWFFwSsTuCcONvwMc1mLaPg7z9s4AbtILLO2YTyjlmuzgzaBUBTBXQJ8Ck6ssbpZLA05avwVSFAZMGsziPraEA3JGqwB3bFDhTu0DOvCEfsy0nvs9izy3J2mTBQ+3lbNspzpkrtEZnzh3UnvLSke0zLXXbZzqats/cOBd5afs0B7OWL20N67NZLMXK7pfqKAyY3mLAtN3JI2ubdVzO+vkfOCsJYCKAiYiIiIiIqAqIACbiHwGYbqTyO0WnE8BEVPXlNf1BZ++ZsTO8ZjzYv3lKzPO1mrelS3peg+mNvgRMeNHYqAosXBMTE1c/fwGYap+D+e0vgeXg6+BqcDvTzSj63JZpd209p98dsm1BTI0ETIUR9o3FEWwN6Tn2cslZ6/3iQzOjhd4js4ROnaWClSogsGCBYAmLShEm3jo0WXJ0wYnia7627x6d0ZW8iOrETYiqV9Fj4dpNJYnX+pXEHJxfHO4YKN1v8kTkrVEgYneWCm2bfKQhEzKuc+PYmq5/gxf72YzlF/+JiX+YO3+KlsPRS/g5nKbRCY1B++ZUGkeRfVMqmkm4oadU6KX+RhBgGM8/MONA4ZFFiwuOr+gXHGxcUdj6hZL99FXz9k5pV7Brcr+C7QazC31HB/C9hj3ib+r3TuDUGQQ2TUG4ui5lEbo/qJR9Lu0ouCRy7UwDJo9BUOivD3mBMynAxCGA6V+pFDBpVzPApE6DCi62hiJwtesDx7A95MzqD1mrx4mz1s3NzvRa8yLT2+pq1uYlW7Psp07FUKmyr3dN1peAaR4BTAQw/er6njptpLYbERER0f9DBDAR/xDAlMLvdIcAJqJqIC/TB128Z8Sae5k9OLh5UszLtSNvlyzpcRXMGp1nUlrRgAkvDn+qsxJZ6spetCYmJq56pmsx0ZbNGziK6dOcEgFGtSNhXrtLYDnoOrANbme7G9+94GF6z85z+r2h3rNj6lT23Pj/EI5gogBThMsKyRmrA+Ijc6NFftrZInb3YoFlXRAsZoFgEQuEq1VB5NqlULxj7MPikyuDi694uUjv7DaQ3jnYlc1mV/SX7grCtHst3z05O7r4hr+jNMQyVLJvcoJwywCuyKVDMRW9ZI1T5eFF9OYgcmrLQKZOnyATiWYi/tGmxlVXBjB1puESBpw4BZ19UxCvbYbGYhs0/ruB0P2vTKGP1mXB7kn+/MDp8/mHLYYX7Zvf5L/cg7xA0za5u0x18ndNWVqwXW9v0dZhN4s29skTuHQGoV0LCrqKLOuBCNdfwnXK8H1BpZCkz51KkbdlIBT66UHePnPgHl7O5Ry1IoDpX+gzwKStksDTUgHeSAYwVTW4NIIx2s4dijyIBhZcjVrAHdMMcqb1huwlOpDpbM5767UmJtPf8Wimv/26t5uWTcuxnvxHgnFvlcq+3jVZMsCUud3BI9PbKi57/bwPOSt0qXpYBDARwFTNpfANy++jWGZb8SvPl329vOfLey9L7jkWiwApIqJfUeXNN+XNI2XnInnLPqfsZ35tjit7/Io8V7VEABPxDwFMOIKJpMgjqgYigImYmPhH20gOLH0OmMLRnBJGzSmfA6Y72VtM7l7wmhFj52V+b6in+b0aCZj4p9c2lUSsHSGOcFwtObMmSBw0577IfzRXtPG3EqFtQxAuVwDhEhYIVyph6PNO5NaPJwnQT5YemXeu+IyVk+Qce1TRBXaFF9hzHl9UK35xuU9xzJHp0stbPKTHl4SLAvQShJv6FFD1mGwa0jWZcEoyh5YglEEmtizKpAuQKCbiH2MmIk4+esmlIw2XMFSyb0KDTpf2INzUC4SeQ4R8P51ofsBEz8J9043zDs7uzT2wtNX3pMSTKWv3hLqcwFnqeXvMLPN3TTpeuG3UU777X9kClw7vcM0nkVUDuuaSbWN0Li3RucmgKzrPdTR8FW7oAXz3gVDgpwe5e82Bc2gZN+eoZWjWMSsCmCqoUsCkWY0A0zAGMA1A29gaKsDRawPZswZDpvUUyHBbmv5mu9PJNwGuNhh4vNmwqPtre4PGlX2ta7oowOSDrrefg8fbrZZxWa5zP2SvGAMckx7AHa1GABMBTNVN8gu0OFK3lpyVvrItszJjvK0ity3/mnI5j5WZ/VXktpXLvL+sleTOk4iIqOZKHhaVN9+UnVO+to/8a7L5Q1FuW0nO5cHu8gBWecD8a3Cq8kQAE/F/BUyhT/N0bqfxO93PEJYLmGIzhApXkopqnYjPU919l1PH50Z2PY9rmfXdr2Y2kHkLeuwZReyJrgO+Nui61meuS4Ot17Ma+N3Krr/zDkdtdzSn9o47nO9ebCD6CmDqyQAmhZoPmD59F/q7Gf8AG332uZX/HWuKy/bVf+2viozlb9Udq8j51LR7pmJ9VUHAJEuRN/5OlofZvfPes+7bbZ0ZMxRt10zAdNSqmSRsrab47FprSciq4+KgWfGi7Tq5ok293gnX4tRcyiBcwQLhKmUQ4cgix7YfxZv7vpP4aqdL9hkdkxxbuFBwyq43N5hdLyGY/c1fxickBKuIH59r9+7hyRElNwMWSMPW+koOmEWJtmq8Fa3r/EFo35SJYpJBJiaSCQOBUsBEIBPxf7UcsJSNKRlcwmAJj3XbhiByaP1euPkPIX+bNo+/x+hx4YE5gQVHLGbzDi3rEbvbQhnXTvq391wC21jlZeC8+tn75zbPOTCnT96+WfPy9hgfyPcf96LIa2gJ37XbBwGuS2alBiLLusx5tASRs1w0H4ZLOE2eSwcQru9OANN/VLUFTEOQ+9PmaagCx6ADZM0fCW8dzOG1l9WLVwHsgFc72FPSPWxkILRqLXLUQBHARABTDZI8VMKLsarIOF10HTnXLcdq3+F6ZVxfzmVfk72nLnMO+JxUWAQyERHVdMmDJXzP12YsP/eUNyd9bV6SzSEy1/6KVcuxDIKX3ZY9lgGsqjcvEcBE/D2AqZtb3CvjQ4mn3a9m2oY9y9O590rQ6VGmqFzAFPdGpHotuajxqcd5bQNjuN38b+X09r6e1c8rKusvxn9uRY99bmT1/eV9PasvujZ9t0ZR1wdflz99b2X/uTM6p+++e9zfA+9xO+2K5jTzu5mj+rPnipqiraYPuvjMiDXfavbgoNukmESHGgSYpnzFZeEAhgDTWOfB5D/5XKmnMZaHC5V9Laqz5ftJ1lcy/5f+ku8nY9an8fxprESgcR9BteWPnUi5czpXoePI7qHKvqb//z6rOGCyGnwd1o+PzvScHnPOZ/YDW++Z94d6mNbMFHkUYDpjryU+Y2crDVkVLD4887Fox+h80ebe74SOLUBoVQeEa5SRVUFoWZeKMMK1aMSbfpeKfUbGiPdP8yw+uWJK8Vl2L+GVTS0rAJkU8mMvN5TGnukqubVXS3p+40rJscV/iwL0n4nd+4lxxBJOkSe0qkuDJtniOhXF1OVTKrPP6jJVNqwgrl5m4JJrN9p4G8MbNK5xvSUxGnsiS1UK7AjWdRXwfUYlFhyaezU/xGFXbrjHspzIbUPeBHt/93zwZt/8Jll7F/zO2b9wNG//PIvc3dO352+fEF3gPULE3/QHCKh7oD663+qAyFqNBl4YspaOfwzE0Pk6t6XS+ZUCJl894O2ZATkHl3Kzj1iGZh0hgKmiqpYp8soDTOM7Q+ZCbXjjPAde+9g8TdvB9nq1w0U72Pj7a4QR/Tt9Bpi8LOMy2QQwEcBULSVbyJUt4mKw0xAZR6w3RW6O3IxpW5RxSzm3krPsubL7lN2vNXIbObeWs/xnNWfOpxFzfvg8lVlVbTGXiIjoR0gGvPGchP8Gx/c8vvfxfITnItm8IpuTys5N5c0/LVif5rFmZSz73CZl3Jg5bmPGsjmokdzreK7EcBxDLNm8pMSqKvMSAUzE3wWYNse9MqIA01vb8IR8nQcZgk7Pc8RfAKZEjkQ5NkPY7EpSYY/gR3nq++5x9P1u5RhvvZ41wzMqa6bMXuix940ss1/e17PM0LWZ7hVFXR9zdF3Mt93MNt9xJ8dsz13uZHT9Ru2M5vT1vZnTAu1H/kP3HdpqGtvFZ8ZD861msQfdJt1PdBh5p2RJz2tg1ugCTFL4tBiMF9qrGyiRh0qTWeWDJhm4kIcCphX01wDTl1Ch8q9FdfbnILB8kCPrE7Nv+FP/feon+T6ix0pEOf4SMGEoNU0OTn5rrPxq0LFsJJ88YDJErXGdSJjX4TJYDb7xcf0EGjBtmx1r6z3r/hAP05jalT03/j9EAaZQW+3yAVNLENrUo2CPCAMfSwybatM1kpzbgdi9/2vxnglnJccXuRSHu0wuuba1X+GtgG+mYIqN3a2cHxvcUHJjb2fppa2G0tPW7pJD5lfFflrZog2/vxOuxXVn1NDxatNRHPZN6cX0dXK1ckqjTwhgIv43ZsAkBkvru9Mtfh7DJftmFNARr64FojUqVHo8gftfmYWB0y/khq/fknPjyPS3MeHqr2IvtP4Pt5xC1r75HbmHF43jHrCw5wXOPpK3c0p0gc+ozKLN/UDg0hHoKD41Gi7ZNQKRQwsasLp+DpjEMsDk2h2K3AZAvu9YCjBlH1zKzTxiGfqWAKYK6zPANEolgaetAjxNBjANZ1UtyFQWMP1Fm6dRG3IMOlGAKcNpNrzysnqa5u/sme63VpNVVRY1fgFhwPTKx3rUaz/7UsCUtWI05MgAkwbqr8FlAFNVGFcEMBF9LryGgX8sixdI8d91eDG2PXIX5B7IvyH/zrhXGfeW8x9fsfzrsrYP475fcR+5/X9nzgOfTzsWvUDcgEVHJBDIRERUs4TvZRwNJD8nYdDcAbkrMv5bV34u+ta81FtuH9k89ptc+xvzmdg9GMu2u33D+Hw6seh5qSVzrmrMuVeNSHICmIj/K2CKeJ6v8/CNsFMiV/zZLy5Tc6UKz7PFDe++EvQ897xgVFAsb5b/rRzrLdeyNmy8/MZj/aU3Wxl7bUCPN1156/7L+/Jb942X327ZcOktuj5vPTdcfuvpdjXT0/N6prvvzRwXdP2W+d7Kmex9PfuvrdezmvneyKr8SaSaydsstss284fm3tNjD7pPvv/SUfNOydKe12B6OYCpshes/63LAqbyLIMGxnJQ6Hssi4L5ZFmkSs2PVvk5oOKf09DJ+qEs6Ps6+IssE7X0CSZNKuNvASbj0miq8o4pg0vnv0iZV9nX9We7PMA0v8NlsB584+OGCXffek2/H7ltdqyNz6wHQzzN7tdcwIQjmELtbSQnV54QHzZ/JPLXyaNS5Dm2AqFdQxDa0unCqIgiDJgwcMK1aTb9XigO0H0kObrgRHGEo4M0att4yd0DnYKDg7/54wq8DzdqR72Sm9v7Sy+sXyw5tfqA9IBJvMh7WJ6I3eWD0K4RDZiQRThqyqEVkyKMgUyujKnF9sqGFsTVx3LRSxRg6krVWBLZN6fH2RoVEK9SouCO0KXTR77fmGf5J2x25kQdNn3zMLrb6ydPGickJHwzFeQ/KXf3nN94++cu4AXOPpq72zQp31cvv8htQLEAnZsQQy4McG3qU9FUdGq8sikiO1PnLHYqA5i2jQXu7umQdWAJ923Q6tC3R9YQwFRBlQImnWoImOQimHIMOkLmvJHweu10SHdf8Sx1q61PsoeNbizbgtTg/UkqBUzb7D3eeFnGvV1HABMBTNVKssglvBiKf4GPf8GPF3Hxwmt/5GHIWsijkXUZj0XWK9PqM9u4Hce05VlPbj/ZvjIbyHmc3OeMZY4/EnkIi4ZPeFEX//gDRxHg+a4W8z2IiIiqt2SRS3hOwlFLeE7CsBv/fYvnJA3W53PSWLlWtq1XxrLn5fcfI/fcGLl2NNPKtnWQR8lZ/rE2siZzTgNYNMDqyKIBOD53WSrPyl0fJoCJ+HsBk/FngEnQ8SVHXLpAlsSVKL3giOvEvRF2uJpUOPJEfO58/9vZm9ZfenvALuJ1yJqz6RErz6SfZ3xudWh6hGVYetgv79D0sDWh6eGr0fVZdTY9ErWRVmGvIm0jXoc5nX9z3PXi24BNVzLXbrmaZeR9PfvPHbeymwfe49T9O5ZH/sipoOQA0wH3yfdfOGreKa4JgKnsAr4MMmFgMBF5ApP6Dxsvdk/8Aih825+DiPBST6Tazz+vvPRqvyJkqGjflYUwssgi2TWdyLhsn035hmX7TWT6yZCCHXiMy/z5ePjUd/Lp3v6pD+WP9+X3+dpn/Arj4d8AJrT9awIm+8bITUC0thldE8lKjUqVJ7JtjCNBpCLv4Vnig2axktPW+6VXvRaX3Ds4AEcnRUWxK1KLUEFye3cH6fUA/eKL7k7SkDWnJXunvhB7DBAKndowQEsVRFQUUzM6ysSFgUwEMBH/W7Pl6i7J0uPh59E4p+oc4XGGAROO1HNo8YHvPkBYtG/67bxIz3WZ9y9qxMbGKv+Ie463fXKP3N3TVubtnHK1wG+ctMBzGPDX9wTh2pZ0dKB1ffr+ouBSe3SOHaE08kqWEvIrgImDAdN+GjBlHF6zOC2QAKaKqMYApnHtIXPOMHhtOw3SNix+nrJllX+Sx6rxT9yWfDOylOjH6BNgsiWAiQCm6ihZfRMMaXCKqE7If7LoRVND5OnI85AXIS9FXibn5YxXlGlXMpY9J+/lZSz/Xtn7yu6/BHkB8kxkPDbwou9gFh1dgCETTk9Vm0UgExFRdZcMeOO/v3GgBE5Bh+ESjkDCsBtDZxPkOcgWLHpukJ+XZNvyc0vZ+Ub2/DLWl3Na2c9ZWsZLymzjeRHPTebIk1k0dPqLRc+jeD6tGvCbACbi7wFM3TfHvZp2OOn0FjpF3qj7GYIOT7NEVF2g+EyhwqNMkWrsG0GLm6lFA04/yZsRcCfbzfl8xuklp9JiZvyd/NToUOLLKQcTkxgn4scmhxNfECe+mIZsjK4Huib4uiQaH05KNA1KejHraMoji5NpN1effX3U5fwbtue1LNOdt3MGHbrPbX88Lpf8erCC8pn+sIvvzLgZPjMeHtgy5cFzJ807xct+uwYzqjVgOgdGCrSNmXZqaQ0YGi6NQ99LjxUKYxnrlWP9b1h+37Gss6iVmX4dH2M8AzJkoKK82jQ1HSxU1J9FKDF99wlMfOo3/dJr/sn6pdf8n3wW7UP30VjKZxjTj2Xvx2OehoSRcn12nopU+hSZhs/5E6wypGAl7u9QMCh1WClMkQEreehUNgqrpo+J8gDTgg6XwWbwzY8bJ9x7u3XGg0jfOQ9tts2OHYK2fw3AdMj8kchvVJ5oowwwNQUhjlbC6fIwZLJuQEMmq3p0FNOG3yVi/9FZkqB5VySR7M3S24GGuL4SrrMUFRX1TcjEux1avzguuFfxvSNGxde2bZKeWnVBHDAuQ7SpF3Vc+ljIto3Q8VqAyAlDpo4MJJCrx0RqMRH/kz+DSwyYdOlE1zbCKRit61FpIGmY2QKEG3sJi3aMyyg4bnkmNypwWdbTG7//qHuO663VLc9be02hj1Z0kac6FG3AdZfa0WMcp8XDkAnfW87toDTiSj4dJB7/zp8DpkK3AZC3bSzk7JoOmfuXcDOCVjGAaQkBTBVQdQZMef1p52LApN8OMmcPhVdWUyHFdf7z5M1L/ZM3Lp2QwJ7fpLKv8a8iGWB65W3r8dpzTdybdXM+ZC3/EjDlEsBEAFPVk3z0EoY0eCEXRwdhgIPBEl6IdUZ2R/ZG9kX2Q/ZH3s60Zb1d7jVZ6yf3fHnv85Ozr5zx423IXshuzLmsQp7FoheaMWTCKapwXZWqEy1ARET0vZKvu4QjKnHKOfx3LYZLE1k0zLFFXo/sgezDoucI+Tlk+1e8g3HZOaoi3lHm/TuY9+N5ypM5nzUsGoLj+ROn92zDfIfKn5cIYCL+LsDkFvfKBAOma5m2YQl52tGv+O0evBFQv768mVakdCudX/96amG3iOf5eoExHFvXi2+OLjiR8mjCvhfckdufFQze9qRogM8T/kDGQ9Bjdd8nhcSUi/D1QNeIT/spf4jv08IR2xPy9Ha/yDQ5nBy3PCT9FPvC201+N7PND8Rwhx6Pz20d8jiP1GSqgHymP+zsOzNuus+Mh/u3THmQ4KR5R1odAdPntZVkgOI8TGOM4QB+Hi/yj2fg0hjWWdBhnYFRlE+DNuUQ0Cpj7dLX5B3ymbU+a09TnzsGGR9nAhPRJIMVX0KFyr9+lWX56J3PUt5R/XYOpirQkUv4GuqX9tmX/STrh1Gf+XSpy/atJusUZVl/4X3GMPDJgAJMn/prWmkKPLo1omAlDYwwVBpHAa+zoIs+YzTV9588hgFY+gxsmsik25N93y/TLNbcul1fBUxDbn7cNOHeW+8ZDyL95jy08Z39cIj3rwSYfLXzqFpIFGBqhqM5aLDj2BqEdk1BaNMQhJZqIMSRFmtbfRS79RFLAsY/Kz6x4oj02raVkofBo6RPr3bNS77XgM1m/+OvtHCqvMIntxqXJFz6s/jhCfOSyx5+kr8X3BX7avFFG3rSkAkfD9uuCTqX5jQUKAsNSD0m4n8yBZbk4VJHEDq2occXjl6iwE4jOhWj628iwTbt10WH5tzJD9u4I+d28PSMp7Fdf9Q9l7/pj76Fm/vYFm384w6OXBI4d6DgLZ0arwENvNC9RgEwdje5ukudaLiEo/gwYGJqMAkYwJTrows5O80gM3AxN+MQAUz/RtUKMMkgkwwwDaCdq6ECOfpt4e2swZC+ZhKkuMx9nrzRwj/ZdREBTD9RGDCleNKA6dWWVXEZ6+Z8yFymAznTuhPARABTVZd89BKGNPjfD5yGzgzZGnkr8gHkk8hhyOeQzyNf+Iovlnl8nnmP7H3n5Z6Xfy1SzhGMZdvhyGeQjyMHsmjYZMeiIxhwqiscbYVT+jVmVZVoASIiou+VDDDh/4Pj9JcYeuN7HKe5w3AJQ2YMdoKQQ1j0vITnirJzTNl56VIZX5R7Xn6/i2W2LzP7XGZ8RW77EnO8s8hHWDToskGehqyO3JlFz0sY4FdujTgCmIi/BzD1cIt7ZRqUdNrjWqZt6LM87ZtpRW1vpfOpXxOfe1GgfP5lQdPw5/l/HYvnTfe+keW56kz6VcPAF1mDfB5/7LY5/mN711hoy46Fdow7rI+FThseEjPuuP4huiYPoT22K+0uG+M+9vF4/G6k/zPutENJ8SvPvArZdPntRnTvTvv7Ia9PyOO8hqFP82qFPcsnv6T5B8kBpsAtUx48c9K8I6kpgAlDChNkUwUaDhjJASZd1lkKLIxknYJhyBqsk6DOCoYhyINZJz7zEOb5Tz7B+NP2YKYdip5TR581nIEXo1lnKABhSABTuS4PME0rA5gwlMFwCV9LTXRNhzF9NfSzPpJd//JNv34c7Ut7ENXS/YX7fgTqLzwedBnAhMeJEVNDyYx1odTT5MYRvi8wWMJQCff1CPQ5GlT/y0yPA3zOOgxokkGmqaxPgEm+PhQBTAQwUYCJWsxuB0IMmfBz1vXpGkk4ksmp9QeRx+A3kv0m10oi1/mW3Dto8S7h/HBxYnTbiqQVwxBKkHKnxbsXFzVK7h5cWRyx7pjk4PQkkfdwodC1W4nQXgaZ0DHtMARo8Sl1GAFMxBWxLHKJAkydKGBKjWMbOiKPSku3tiV6vXuJ0HNIFn/n5LtFx1cdyj/vbcONPq2XHn+3QrXFvj7GWYo82571uexOrYpcuuoLnDtuEji1u4vuJwkVIYjrLeGxjdNRUvXG8PjGY7o7A5kqBpiyd5rB28DF3NcHV4VmHFhJAFMFVXMAUxt4O3MQpK82hGSnWc+T2Qv9k13nT0hYY0wA00/SJ8BkzQCm2QQwEcBUHSQfKSCLXsI1RHBaPBy5hEHOMRa9oHoP+RHyU+QE5GfIz5ltmeUfP5PzU8Zf237C+HEZ4+PFI8ch30e+xaIXfo+y6KgFvJCLU2WNYNFgDEc6yKKYCGAiIqqewvMSXr/G/wfHf8dgSIPrrhkhW7HoiKFgFj0vxbDo+QHPF7J5JaEc47npRRk/L7Nd3j7YicgvmTZR7vFL5nV8zFjkayx6bsKRlhiE4VR5eF5qxnwXApiIq7C/Aph6use9MjuSdNozKtP27NM8raiUwjZXkwupf2BDnuSphjzNax38KHd4YAxn8fpLb/bMOZb8YMT2Z4Iumx5CE8f7UM/2LtS1uQtqjOvb34MG9jHEcq6PXA9ZzfYeukb3oKFdDLRyegA9NsW90/B7yjE6mPho5Zn0E+5XM+33x3D1Tz3O6xL+LL/RuecFKhEEMn1VNQkwTWZ9DphMFC6AKbIZbhk4gF/HUSd4sR9HrWCwgEEABhADWcehP+sY/FnGf/2D+zPG2wMoY3hxggIM+LPxMfQpwBROHbu8qJWaCBMq6k9wKbL0mlDAhQFMUxQiqWuH0+BhADQc9RUGRhgQDZC79mX743MfRa9h/436E/soZfwa7nMMCocxgAmPiwlo3OPjTlM8D9MVLsIMhUswg3URzJBlY8iQiajSYSClBgUmP52TzPJjAe9LR7SFUfeTEfN9TSmfL4VM02romPgHwPRh04R7b7xnxEb4zXloTQOm2F8TMNkxKfLwYva6jiB06UBHftg2AeGa2iBcpULDpnVdiiR+Wi+kxyzOl1zx2lYSFzyzJPFaP25CVL2KnAcGUZK0Ox3fP40wKL61ky0NtYuQ7Dd5IfQczBU6dywR2uL6T3XRsdToxXgc4YEX4dly9ZhcST0m4vIsGyPd6HZdByoFHR63AjyGLeugMdUEj+EPwi2D8oT+Y+MEB8yPFJ60sc294DsxM/rUX2lP77VkYCn+200BQ1EmOk+BVYH/JObbdWlY4Ny5H9+pw3iBQ1tH4doWfwvtmjwT2TWUINNwCUcxOcrgEj7vrnIRTLL0eB2+Dpi8x0B2gCm82WfBfX1wRWg6AUwVVilg0lau9oDpzcyBkLZqAiQ5zXyeuG6h/wsXAph+pmSAKc3L2iPdfWVchsssApgIYKoOki3k4joneBG0O4uuuzQb2RX5EPJVFg16UpHfImcjc/6Fs+WcI2fZc1lyrcyZjN8y7RvkdBa9sPuQRUcO4GgBvJC7mEWnysM1T3AUE454kC3mEhERVT/JoirxvIRrGOEUmMNZdI0jFxYdUYnnAAyWkpEzWPS8IZtbOGW2ZeYx5jLmlWm5cvvIv5aHnFum5THbeB88f6Uz54OjqHB0Fa7vhCOuerHoyFD8XUiKPOIq7K8CpvhSwHTmaZ7W1eTC1pcSacB0LD63zvFHvPZHHnJ1AqKzVzuee33I5HDi4/7ej8Ut190HVfR+pVV3QFHOSugYtSyJ5a3EWHE1fY1qobau5V1oah+DI5yKB297wpt68GWMVdjr3X63shediM8dFplQ0PHCi8L6qCXp8r4inxlxnX1nxU/3MY8L3DI19pmTVrRk2W9RMKMxBkwRDGAKqzaAaTL1+EvAREEmxQswrdZ5mKoSCRNrh4NB3VDQVTsDo9ROw0i1U6BR9yQMqRsMg+qeoDywznFktC1z7U/tYPTaYLTPEOShjNWRNdD7h6PP0aoTAjq1T8NY1bMwXjkMJilFUNE4VGTVLxCtUhGXjeYqC95wP05GY3CCYjjo1wqFMSpnQbt2CIyscwqGoeusoYauO/IQNbofBteR+XhpO4jyMcoDGQ+qewz13XHUZ8EwTO0kaKqhvkLjQA+Nhwl1wmFK7UgwUTkPZsoXYIbSJTBXvESBJgwp8TnjCCRcCwqn1MORS8MUTsJQRTRulI7DAOVj0L/U6NhK6NzQa8MU0ZhQCKFS5o2TA464700YwGT6iwIm26E3P2w2jMnwMY8N958bZ+03J24w2v71AJNDSzotnQwwyVLS4SiKtS3o2kirlEG4WgXt1/idaGOvPMkugyTpqdUXi2/uWP/+Sfg4HMX0rTR5MvFe3q5f/OJGn+K406bFUX7u0hDLUNGu8U+Fm/sWCB1aUXAJwwAqkgkDApy2D0cxlQKmriSKifiTcaQSNWblICQev05tgQKWlrVBgMauwKoBGkvtP/LdBxUJtuu95AeanS48utQxP8TBIDfC5/dXN0NaJ0RF1ZNBJRzJhI1rjMlBpn9ULrvTb0UuXWbwnTts4Tu2ihTaNX0otGmQLbKuVyKybUBHLmG45MLAJSpiqatcejw8rjt+CZhcMGDqBoWb+wPPewxkyQBT4IrQ9EACmCoqGjAp0YBJWyWBp6UMvJFKNGCqanBJZgyYhrIgbyDt3GEMYDIfCGkrx0OSIwZM8wlg+skqC5heu8z68HbpKMie1u1zwDSUACYCmKqU8L9lsjonuFZIP+TxyCtZdB0TnJoO/zIfL57ihdRCZAGyEFn0DQu/4rKvCcoxn3ER4wIWvZiLF5FTkB8w57aTRafKM2XR9VkwIGuOrIYs+3EIERFR9ZIMfON0l/h+7oGsxaJTYm5i0akyb7No4IznhHwWPV/I5qby5hyZxd9hyVcsZj4fz1EYZuGIJgzkd7PoWkwYfPdm0YBJlrqTACbiKuoKAqYrSYWtL74soAby0The3aPxvI6HY7ljtt/JXmMf+erw1EMv4/p6PeI3dYqhoAn+nM+MP38VcbleyVwjdC8qIiuvuk1Ff7VlP3g31PfJ61lHk89tvPx20+FYnnHYs/y/zj0vaIFalUqbVKq4aiJgoqKY5GowYdBkpnQBZqhehJkNL8GclpdgbkfUdr8I5r9dANPfzsHUnhFg2CMcDLqHgX73UNDrFgq6Xc/CmC7Inc/AmE60dTtjn4Wx6Hl9tM84tK9Bj1AYjzyhRxhMRJ7cPRymdkXXq0MkGLWOBOMmqK2HrIKshKzweWo4eVf2dfyZNioHLtFgKZJKQYchxARFNP5Uw2FiwwiY1DICJncIh8ldw2ESvtY90WvI43vSfTAO9Yd+V9R3Xen+ofqK6rfTqA+Ru5xGfXoa9LqfgXG4v9B7J/0WDkY9I8Gk+3mY3vkCmLe7CLNaXIJZjS7BTLVLYK5yCaYrXaTG0RR0boZUuj4aLmmzzsBIVggMVzoFw1RPwrB6yI1PwvCmyM1xewpGNDwFw9VQq3IKNBXpek8YMunL1ebC/S6L3PpFAdP7zYYxr33MH4b5z42zogHTw18TMOGFePtmdA0mKs0Yk67LqR0NnzDwWa1MR4E4tHwn3tJfJNlnnFwc7nSs5N7BZSWJVwYVvr7VuCLnghfshWn3WuL3FN8/al58ZYu79O+F58S+WunouO/p49WlI5lsGzHgq12Z9GcEMBEzLlujC0MaDHAoOFqPAqOCNXVAYN8K+Jv7CYsCJqQUHZp3gX9ilXthyFoj3ml2D27wjnrJ5/xUmfR4CrjFkUwJCQkq2HKQqTwpRGmxauG0eHx29/GF7K4efOdONwUOrXMEdk0KRLYNJCKb+h+piDyc9tGFichjM2AJp8hbJ4NL+Dt9AzBtHQ1ZO0wgY+9Cbvq+5aHpgcsJYKqgSgGTZvUHTBnmAyF15XhIdCCAqTJEA6bVo9K8rDzS3VbEvXaeSQATAUxVXeWlodJg0bWXcI0THL10nUUv4uLFU7x4ixdVS5DfMX4v176Xe15+n/JcUsZlnytmWiljfFy8OIwBF15QxmmpbrDodFSbkRci6yL3RW6L3IBF1zyp3IgBIiKi75E8YMJw5jcWnW5uPvIWFl0PDqfGw+AbRxPhuQHPE+XNK2Xnnfesz+er8ra/9doHxni7mDk+BuA4mgrPS/tYdCo/DOv/YH0CTCSCibgK+19FMNGA6Xh8bt3jj3I7HHnIGxUQnbPS4dzrQKNDL+/32/oor6lzDBWdQwDTvzENl1grbtF9sBTdl8tvQW3raOi68WHB+L0vHtiGvdq/C13rE/F5Y04/ye8cHJ9Xt9ImlSqumgiYKCug55gUaxg24YiUWQ0vgUXHa2DZ/wY46tyGdZOiYd20aHA0uQO2RrdgzeQbsGJSFCybeA2WTLgGFgZXYKHeFVigewXmY49Bj8deAQv03KJxV2Ep2mc52nfllChYPTUK1ky9DpZTb4AV+hxLgxuwUvs6LB58Feb1vATT25wH4wbonFQiYJJiBHU9p1DXNKI0RZwxq2aDps/rZEWWpogzYZ1nTNekMmRqG2GIo6twFibUDwPTTudh/l+XYbn2NVhtcB2spqDrbISut/F1WG0UBSsmo34zvAZLx1+DxQZXYZE+7qvLqO8uo767hFpkvUuwyOAyLJ14BVai/rKcdgNsTG6CHep7+4m3wXbMLbBSvwmr+tyAxR2jYF6zKzCj7iUwrnWeqQMVVloHCqe8w/WVcKtZKwR0GpwBvdahML5bOEzshfr4jwiqHd85HMa2DKWi5HAEE95/pFx9Ln30HQ3R5+KxIJ8mUBbZVpPGAgFMFQVMTT8BpvXdaMjk0hGoqCIMeqzqUIv1Iut61MK3xFujSHJk7p2Sy1t8ih+GmBQnXOudl3wO/yf/m39Mv4mOriNOjmpX8jhsaMnt3QukYQ67xftNHog8hxSKcKo8XDOHqv2EIVNDOupDPgUaW35BnvjXNTMmZOMVP8ZQFNdZwhFLq1Sp9I4Cm0YgWNfjncBX903hEYtrBWfZfnmRnnN5l7wHpl7e3bDs+MRAKTk5WTUqKr12VHp6bQybvlabqdC+Q2Pe2i49CtnddAtdf1tbxO4aIXDqmCPAdcxwOjwctWTXhErXR91f+LxLx7EMMMmP5YoBpld7F3LT9i0PTSWAqcKqSRFMFGBaMR4S7Wc+f+GMAdMcAph+or4ETOYEMBHAVNWF/zbDUT442gfXLsKpnMaw6JRzuPbSGRYdvfSaRYMdDHnwQiteWP1YxlDmcXn7lPUHuf0+lPP8+zKWX8h9xZxbGPJ2ZEvkqSy6TksXFp1WC6ekqtyIASIiou8R/gGXbG7CcAb/TavDousaeSCfZtFRjDg1Xnlz0wfW5/PLv5mXKmpgfZqn8PEx6MLRlTeRA5GtkScg92HR8ysBTMRV3BUATLgG07XkwtZXkugUeScf5dY+9Ti37fF43og9d3MWO1/I2G0SlBjd3+dxbnPn+6AsA0zL5IzHWaWDnKpqBsCtZADTohvAsrhOQaYWjjFSTb+niUtOpp7dej1r/YH7POMjD3P/OHif98XCBREtnxnxnX1nPZq+zTw+cMvUh8+ctO5Wa8A0iVrEjoAJCjKHgyFqjeqcgzmtL8OagTfBzeg+7LV8DMfcn8Mpv5cQ7P8CjngnwH6Pp7DX/Qns2vwYdmx4BH7r4sDH6SFstY8FLztk21jwXhsL2xwfgp9LHARsiIfdbo8g0PMxHPB6gvwUDno9g4NbnsE+9hPwXR0HG83vgdXoGzD/j8swrdU5mKgWDuOVwqjrOpFKkxZemibNpBQu1CywIN9H8oDJWA4w4RRxeBuDFgyXMMTBAEdb6TRMbh0Bi9SvgvO0aPBZ9RD2sB/DQc+ncNjnGRzahq63z1PY5/EEdqN+C1j/CPzXxYMv6jfcV1txv9k9QH34ALwdYlGfxsLOzXEQuPUJHPZ9Bn/7J8DfqO8PbUyA3WhMeM+Kg/V6MWD91y1Y2OEamDW8CIbK4VTUET4ndarW0gmqbpMG6yRo4bpKaqEwtV0kzOp7CSw0r8HycddhpeENWK4fBQuHX4XpvdBntESfoXyG+k74M9TRZ+B6UqPQZ+LvO6EMZJJPHUiDJhq+TWUivKqjvwRM52BBxytgO/TWezfD+6+3mceFbZ8bb+U/J34w2v61AROueUQt2ssW7LvQtWKofRqCcI0qlS5PZN0AxOyuH8Xbx76SnloZWXx9m2tx7NFJ0gfBPbNid1fohxVvooPriB+fayd98Pfo4iteDtJTq85Idhkmidz65YvWtiiho6ZUQGBZF0T43PCCu2uXT3WYCGQixpFAGC5t6EG3OK2jPY5cagiilbVBuAJH3dUDoVMH4HsOzy86NPdefvimAF7UoQU5t0OG4rR45QxNBQyUMFyKjc2qi30uOVm1PMCUzu5UO9+hc98ily5mheyeG/nsHqf5zp1eCp3afqAgFwZM2Oj+ETm2ocewLELwq6BUDjC5lAVMfwF3qw5kbjeBV3sWcNP2LaMBUwABTBVRhWswVfZCfBljSJE/kHYpYJoxEFIwYLIzf57gPN//GQFMP1UywJTiZeWR5rYi7hUDmLIYwJRLABMBTFVLeJETrw/hKB+8NtEeeSCLhjS2yHtZdI0TXPQeRy/hNFD41/+yBVr4P7u8BV28kIujFHA6KhzFlIB8jUVHWrFZdN0oHOXwO3IrFp32T5X5ngQyERFVD8nmJnnAhO9pDJhwpKIni4bfuBYbBkx4PsDwGc8P8nPTR9b/f66Sn5dwmj5cpw5HMMkAkyGLjqokgIm4GvgrgKmHW/wr06Ck0x7XMm3PPsvTvp5S1CYqmQZMZ5/mqYQ9y2sZ8iR3yIH7nLnrL7/xn3k06eYQ3yfcNuseQG30/tK0b/IRTKuJy/Ua2TYTxbT4BrAWRlGRTM3s7xUP83mSuuBYyvnNV9567IrmzAy8z+2/O5pD/rP3FW2bEd/Zb9aj6b7mjwL/x955gEVxtVF4LMEeY4s19jSNUWPvNZZoYu8aY09siCB2xK7Yxd5jp0iTakPp0jsIAiJI79tZ4Pz3zuzAghgxfyIl8+U5zy67sDtz750N3NdzPoNKDJj4DWwKmGj0GO2RQx0nYxkLVpPrWWNRx4fYOtYVl3QD8eBqNHyfJCDMOxmhPikIcEuC17M3eO4YD7dHcXCyfw3H+6/w0DwG9sZRsDMiuhsFe5MoPDSLxhPynLN9LNwex8HLKR4+Lm/g65JAlAifZwlwtYmD7Z9R+HNvCPYv9sTa4U8xp7Mdfm5EjukTc/aYJjCWmESOkbqYeMA0Sw0wVTXIVBpgmlEiGo+utZGMGQth+hONqm+GuV3tsHWmKy5sD4T11ZdwsXkNH6cE+Lsnwv95EvzcE+BJ5o7Om7N9HJ5ax+IxmTcH02hu3oxesrcP7tF5i4Hro1h4u75BgFcigrwTydwn4rndGzy4EoO7+uEw/M0fW4e7Y/mXTzCtsa0KDJmwYKkXcwe9mbvk+EwwsroZfm5wH/Pa2mNlb0dsmeCKfYu8cFTTF8d1/HBkrQ92L3gOnTHOWPLdI0xrZoMxNcxZFxMFTAPJ+Q0jrzOKnK+6k2m62tgUB01VGDBN8ow9vsDX6tRiP23DRX59yf3/JmDaqA6Y2qvixtT6wtDNbrpJrtOgsB+TZGMzSPf3EMkuTg2V31tvqnDYu1X+6Og4qcORL8p4WNUSvO/XVfibdlW4nJ0nt9M/Iru17KHMcNQL8c7OmZINDfPEWhoQrasF8YaGEG9tBTEFCCUj0YS4vP+oOhS57XZ9yUHHra0h1vkMIs26EK/WIGu1HsSbybrZ30eWc3FWaKaF3s00pz9XJ/s5DIwO8mge4+j41vVOo/BoLJ6bW1ydgICAen8FmBL1e7TP0us8I1uv0/Ec/a+csnd0jsrZ9kW2ZEsLzrFERe9vawPJ9ralX1tvnVc7DpSVApgy9/VE8pFRiDeciZjzS1KiL6yyjLqw+vdwATCVqShgSlQBpuSRGiEpIzSQUhpgqmAgQB0wpQ7UQOK4loid2wuRqycgfOO80JDtiwyDtwqA6WMWBUzh+9eNfHlIy+Dl/tW+Mdvm5cetHIGEGQJgEgBThSw+goq6fJoyRT1OFjFcjxMjIg+Gi6CiG6e8Q+BjwKV3icItCrmoiymV4dwC9BjvER0hWs1wjoFeRO2IaEwz/X+6EJMnlFCVp3jARD+f1AHTaKY4YPIlimc4wEQBDwU95fW5VBpg2sBwn0cUMFHgLfRgElTBVQbAZBmcPuJZVHYrp6hs9o9g69CMmrZhGU0tQ9J/uOGTMm/f4/iji4wiHQcZBiW13emNeroeqEaByVo10a/L+1wroujYr+chkwowrSgCTJ9v8lAMORb4cvmdlzb7H8cfOOeeMu+KZ2rP8+4pZepJ8V+sqgiYJrIRa5aqPjlmRPfwU30r/PbNA+yc4QGTY+EIcEpEWmIOZFIZZDI5sjMlSE0WIYU8lhSfjfiYTLyKyMDLkHS8CEhFmB+nF4Gp5LE08lw6+Z4MJL3JQlpKDjLTRURiIgkyksV4E5WNYI8UONyKwdkt/tCd5MyCkvGNLTC8xj02Im0MY44J5Bjp2FLIMlulmUzVBEzqUoco9D4dA7rW6JiwMKe6EQZ+YoyfWlri9+GPcUzLB9ZXXiLAOQnxUVnISBEjO0uCnGwpe5tO5o7O25uYLMRGZiA6NB0RQWkI96fzlsLeRpKvY8i8JcZnIiNDBJFYAolEgmwybwmRWQh8lASHczG4tC4YemPdsfjrR5jYyAqDa5qwUOmHGnfQS+MOBtY1xo8NzDGthTX5nofQHuiEvVOf4+xqf9zcFQbTExEwOxsJk+MvcFUvGMeW+2DrT674vftjzGpliwmf0si8exhW2xTDP6EuLVOMrlYEmaao9WWaKQCmKlUfBJjo5rb6Bj7rtujI9Y4h38M6izQ1WGeIZHu7PMnRgWnSSzP8ZHf/+FNurrtaaqXfP9tev3GMo37tv+hbwxZ9XuJ7p5XM/eJw+aPDK+Vm2mdlF6c+lRzoGSfZ0px1MYko0NKiUXnkvbe04jbq2U36zkVuJsHJ9B9SBzXIyPfkUjntNjaFeF1diNaQ9bmWrNMNzfLFu7+Xis78EptjrG2b+fjsjmQfu7HxAR5t3rU2aTweBUq8e4k6mdThEv258MuLG6QY/NQifW/3sZl6X+nn6HV6kq3XOSNne/s8CkJp/ycOLjWHZBsFRGrXU2Ek3rvWbNkAU/T5JSkvL6yyjBAAU5mrEDCNqlU1ANOqCQjVnRcavFUATB+7BMAkAKZKVrxDgLp8aM+ingy3GapJZEhkSxTIcE4h2nuJdy+VF1wq6RagsVhxRAFE9kQXiDYzXP+owQwHzOjGdD3Vef7l755CCSVUhal3AaaSDiYKmOhnAO9gKg/4rf6ZlMlwgIlG5F1hOCfoJKLuDAeY6jECYBJUofUBgMk5mgNMtmEZNR3CMxpbh6b3uO2bMvugY/zhpcaRj4ecDkpqv8sbDTZ6oLoAmN4tbZUK50AVk0fh0kpVPB5R9dXO+GK7p2LM6eAwzXvRxiecErfc8E6bdNc//Zub3mmfltuHSgUvNcB0yWCaT9C24e7SygiYeBhDY/I4UGHBOmFoJNkgxgQ/1rXAgm8dsHvec9y/9BIxIenIRy6KKp/9Or8gF0qlAnKpDJIcKbIzJMhIESE9iRO9n50hhpg8J5fJoMyTk59VECmJ8tjXoVJIc5EcJ4LX4wTcPByKbXPcMK+HPcY0Mceg6iaqeDUKmczY8S0Zk8cDpqoEmfiYt+lq0IQ+Ppm5z8IV6uQZQsalfzVjDKhjjB+bmbNjtn2uG26RMXzu8IYFdzKJXG2sC1S3SjJvuVDI5JCKZMjJlCAzVcyCJ3buksXISiPzli0h38f/fIFKeRCnyRDllQ7H67G4rBOMzWNdMbeTPUY2MEPv6nfQo/pt9Kl/F0Oam2BCJ0vM/94emkOfYudkDxgu9cWNLSG4f+IlHG/Gws0yHh62b+BiEQeHq9EwMQjHea0A7Jv9HDojnLC050PM+toGv3xhhXFkPYyudw8ja5piNBuXZ14YlzezcD3YqdZElQVMyv2TPV8d/9XX8tQSv/WGi/36kvsCYNJrW7TZzQMm6hKhm/pbW3BuIq06rOiGvkT/S6Xk6MAk6YVfXKQ3fzslM1v/q8R6Vy/qZEpxPF3/fceW4mhcX+584Sv5o2Oj5VZb1shu/HpNemK4v2TXV2LxxiYQrasN8dpaEGnVh2hDY0i2tOQ27Fnw9aUKMPzVhr2gKiX9jiV6GJHHtrYh67cZJDQOj8bi0Xg8HbJ2dnQR5ZwYH5V9e83DrAfHD6e7W8xKC3T7pjTnEqlqvHuJQiXqYGJ7MDk61lT/pijjjQ3jz83vnnpk1MTMPT31snZ8dS9br2OsSK8DRNu+QJF76XPueqLgi4VK6q6lv1qr7wdMcYYzEHV2cUrk+T8sIy78IQCmMlZVcjC9mtsLESt/QojunNDgzQsNg7cuEADTRyweMEUc0jKI3LfaN3rrvPzXfwiASQBMFbboBi79/x79jOjMcFBmLpEe0XUiZ4ZrWE/7HUmZ8ncv8Zu5vIuJRvYlE71QHesdov1Ey4nGMpxroA3Dxf9pMJyLSSihhKr4RQEMvV7pdcv3h/uGKQJMfH84GpHHO5jKEzDxDqaSgIk6mGhEngCYBFUS/Q3AZBeeUcPhBQuYulPAZOAYf2iZceTjoaeDkjoIgKls4gETHXs6NjRGcKUTF4+34hmqkfsNyDx03ecrmn4l3FPP7vXZa54pyyyDMwfbhWe1tgrOrJKblf9EnZjv195wof+ckwv8Lx2a7hO0fYS7dPW3lQswqfeomVrohLFgnUs0aq0fY4Thte5h9ld20J/jAatLL/EqPEMFGVAMMnGPUViUi/y8XOQqKGySs1CDit7PVcjJcwr2e4qDpYJiryYRyRHukwbz85HYu9QTi/o9wLjmFhhY05jt4UPBFz3G8YwlJqu5VmaoQRgeKkyvxGBhmmp++Dg8DpjYsY/RdfUTOf/hav2N+msYY2RzM8zqZgudn51wWtefdYK9IGOZlSopZd6gBpryUJCfC2WugoVNMnbuZOzcKeRy5CkVpfx8ASQZcrz0Tseja69wRjMAmsOfYlLr+xhQ2wjfV7uFH2rdxtCWJpjUzQrLRj3EtlmuOLHaFzf1Q2F98iWe3oiFj00CQpxT8MIrFZF+aQj3TIH/k0S4mr2G3cUo3NkXijPr/LGXxuZNeIalAzjQNKGFBUbWM8Xw6nxPJnM2OpFGJc5S9aiaqQbnKit8pICJgqUJ7GeKGmAawAKmmBO/+lqcXuK3/tRivz4nBMBUOmDiN/O3t4FkUzOIdRpCvL4eJNoN2K8luzrLpUf6R8suTLWXG608KLPRWyB9fGSg1O1sa2/v85/81bEZG8+okeV8ppH80bGO8vv6YxRGf2yTXZxiJzkyIIGCBPGGxqwbRbSmNkTr6kOs2xQSupGvr4pG29W5KCpPAE1VXB04uMRG4n3Jzrt4WxuyfsmaXN+ABZGstMl63t65QHRsVGz29d8fZtscPprpbvxbauCTXrGBgaU5y6tRlxLfe8kxRiUOLhX74zDh/G/fJJ+cOC/NYPDBjD09HLJ3fBWSvb29RLz9CzbGkXUtsT2XWnLXC+sIfF8sXumASaoCTFIeMO3tiaTDo/D65Ay8VAGmcAEwlbk4wFSDA0wjNEJShn+ClKE1OMBUQeESVXoJwJQwtiVezfmBBUzBunNCAzcvNAzYuOBnNwEwfbTiANPqkREHtQwi96z0jd5CAdNwJEzvVASY+gmASQBMFaL4eDz6D35o30HahH4c0e8MFzVnQeTNcO4A6hSim7cfq/dSWTZ0KeyikX00kuoVw2003yc6RaTNcH2k+hN1JGrCcDGAgotJKKEqR5W1B1NJB1N5fUZRBxP9PHoXYOIj8gTAJKiC60Mi8ngHU3hGTRVgog6mOQefqBxMpzgHU30BMH3Y+NN+VXTs6TX5xzPUWO2MT7Xd0UHfu2DEqeDXf5hGW51wStxmEZT+k+PL7K9dYnIaPH2ZLfwLmneUGmC6eGi6T+D2Ee6SygiYihwx1uzxjlUBJtrHpw9zF4NrmmJaextsnuIK4xMvEOadCoVcUQJQ5BUCpgLkIk8FKihkot9LRe/Tx/Lzyc8W8IBJHTIVlTJXiVdhWXC49QrH1vlh1UhHTGpvjaH1TDmXDjk26tgZzZiz48xHo5V0+UyvIoCJgpLZrOzZ+xQ40POmzqX+jBF6MnfwA9GQhqaY8o011o59iqOrfWBmGAnvh4mIj8iGJFumBogK1FQEB6kLLY/CQQqZ+LlTzRt9vCRgKsjLR8YbKYKcU2B5JhIHl3lhcZ8HGNXYDD1q3EJX5gb6NriDCd9aYNmYh9i53B2XdwfC+uJLuJrHIfBxEiI8UhEblMFG7SXGZCEpNgtvojMRG5qOSN9UBDolwc0qDvbXonDnUCgMtf2wY44b/hj2GDO/scGYJmYYWtMEQ9meTPfY/ly8i4nCuBlVGzDl7p/iGX1ioa/56aV+WqeW+PUh9wXApA6Y2FgvtRgyuvlNI7+oO2PDZ5BoU8hUn/t6z9dZshOjQuW3frOS3996UOF4bF6u69Ue6R433+vkdXTUrxlnfLSO/P7uL2UWG+fK7i4/J700zVd6ZGCOZHuHArFWQ4hWaxDVgnj9p+T9WqjBhs5FxycApiquDipH3ZfcrV47sm4/Z+GSaK0GxDQaj66PbR0KREeGZOZcWeiWZbXndKbz7UVpAQ79koM8mpd0JNGiziUKl2g0HgVM1MVUMhbPUX94zVfn57dMOjJmYurBfgYZe39wytrdLSVL/0uxaBu5Zli41ALSrbTnUkuu71LhtaQejfe+c3w/YIo9OR2RZxalRJz/3TL8HAVMiwXAVIYqBEzDKj9gipnzA178MR5BG2YLgKkcigVMu1ePDN+vZRCxe6Vv1OZ5+bG/C4BJAEwVsuj/y2oRfUbUnqgf0QyijUSXiB4RhTKcQ4g6hSqCe6nkhi7dUM4hSiQKIXpCdI1In+g3opFEXRhuY5fGAPIuJqEXk1BCVfxSj8hrxhR3MFUkwKTuYOJ7MPGASYcpAkwtGQEwCarw+puAyf5FRpP7oek9b/mmzD34JP7IUuPIJwJgKst4q8aCl6YrF41Hxr4GUR1NFzTe4IFOu3ykQ04EJS+4Fem20yHO8Lp3yq8PX2T1dH8laub1WvzWJoZQRVUVARPtYzNOFZE3gDFhAdPAaib4pdV9aI15hss7g/H8QQJSEsRQyJUoKFBzvxCxMXkUUCg5B5NCTfRrCi5ojF4eeT4/nwNR+fkUSimLuZjy8vKQECOCi9Ub8p4h2DzdFfN7OrAupsG1TTGgBo3KM2bdO/R46aY7N84cSFDvwVMVABOFS3NY2bPnRWEDBYHUydWTuY1uzC301riDH1ubY/Ggh9iz+DluHwyD8714vPRNR/obCeRiCvby1IASp4ICJTsHeUR07mhcHguYckvO29uASS5WIiFSBE/7BNw6FIptc90w4zsb9K9vhG+Z6+hS/QaGNDPG7H622LzABRf3BMLhTjT8nyUhJjADiVHZSIvLQWayGNlpYmSlc8pMo/F8OUh9k43E6Cw2ljHILQnOlq9hfjoCZzf6sU6oJf0f4Oc2lhhW2wSDyXoYRsZjLGPORgeqA0cBMFX++v8AU0c1deDi6WjsF4VKOg0goVF59HZrq1zJwV6psotTAuUmmmaKhwe3yt0ujJV63GsTEmKsUZbjzHh4oKHs4YHBchu9DXLTtaaySzPCJQf7Zok3tioQURfTqpoQa9aGRLdxUW+bnarINH2hH1OVlb5a3yXeUUfneUsrzk1HIxRX12T7L4k3t5GLD/bPEF2cFSoy23o70/Hiugwf6yFp/m6t37EOWfcS33eJ3jIl/iCMvbW/UfyFX79KOD5ubMr+fpszdn1nnbnzm6Rs/a+Qs709xFtbs/GRVNJtrVTOpRLX0Xuj8XgJgOnfqqoGmMIpYNKZHeovAKaPXgJgEgBTJSnevUQbzqtv3C4h2kdkTOROFM1wG6b0X+ZXJMDEb+jSY5IwXIQf3dT1IDJlOAfWaobrJ9WLqB0RdSnXVp234GISSqiKX/znFO9gop9ToxkuAvNdgImC5/IGTC8ZISJPUKXV3wFMYRk17cMFwPReabuhGi92rNWgEnUtUWlyqkEea6DtjlZbnqPrXl/lqFMhcQtvRbpvs3t95bx78hrL4IxhZA5ae8SK6pbbh0klqaoGmKaT46R9XmjsGnUGDWJM2dg1CnJ+amqJFQMf46imL2xvRCPcPx1pyVIWMvG9k3gnU36BGqxQUx4vCpXyeKhBH1OyP1M8Jq8AmckyBLmmwvJ8FI6R99X6yQmzvrPDmM8tMLTePQysboIh5BhHkWMdR46ZbsBPVUGFmYXxaHYqeGZbuFE/tQKM+4eIHj+FS/MYexYw0cfGq6LxKAD8nrmF7p/cxuBGxpj+nQ10pznjgl4gHt2ORahbGlJeiSHJUiBPoT5XFCzxonNRNG+sVPNE54bez1eBwOJOswKIMxWICc7CU/M4nN8ZCM3JTzH+Swv0qHMbXzF/4juNmxjTzgwrxj7GkfXesLoaCX/XJCS+ykZOuhQykRwKGp0o5+ITFXIZ5EQyOXlOykkqkrK9u5LishHhnwo3mzjcO/UCx9f5QHvCM8z6xgajP72HIdVMVK42M/bao9GJ6vPNg6UZKpX3vP4dwDRRBZhm1rHFMjXAdHKhn/mZpf5ap5f49yH3BcBUbGNcbXNcn4/56sR9TR0bbD+m2hCv04BE51Pysx1ypceGpMqvzvORW26+kPvs1OJcL9OeOS/uNy0jZKome369g9zl8i+KJ0d3ys21rWTnJodLdneTiDc04RwqtMfO+vqQbGrKHQPdkC/sy8M7mdpzKm8wIuj/l36JtUdFwSIFjLpkTayrQ9ZETYhoNJ5uM6Vob48U0bmpQTmm2lbZDw31M9xNf04KcOjwjr5Lhe4l2nMpJCSlvgowFVaIsb5G3J+a3yedmjI7xWDI3rQ93c0y9L4Mz97eLp/2XBKrOZek21pCqqcOlz4ELPFqR16DigNMsu1tIN3OAaaMPT2ReGgUXp2YjojTi1LCz1LAtEIATGWsygyYMvsQ9WaQRgHTmJaInv0Dwn4fj0CdWaG+m3419BEA00etEP0ZKsCkaRCx6w/fl5vn5r9aIQAmATBVqFKPnqJO8tZEPzBcI3otojNEdkRBRAkM5xDiN27LGyyV3NSlgIlu6tIIP7rJHEDkQHSBaDPRHIbrK/UVw21Q0zhADdX5Cy4moYSq2FVaRB4FTCuYIsBEozHptU8/p2hfNgp6yuvz6K96MAkReYIqiT4EMEVxgMkmLKOmXXhGE6uQ9J43fVLmHngSf2SJkQCY3lJJwMTCJRVYoq4lel/LFZ/ouOGzTR5or++NXof88dO5sMRlRlHO+vZxl8+5Ja03DUgf++BFVmen6Oz6bjE5QjTee6rqACZO9P4U5r4qJs8Sw5h7GMhQZ4gJxn5qgQXf2WPbbDdc2ReCp1ZxiAjKQGaalHUbFYGHfPJfXhGoeJfyOCmplNz9ghKASZKdi1eh2XC9n4C7x17AYKU31ox9hpld7TCuhSWG1jHF4GomLGihUOGnEv2Y1AHT9CoAmOYS0XOiEJCeLwV/NBavR83b6N/QGBM7WeL3UU9weI03zM9FwvdJEuIjciDKoACHjG/hPOWjgAKlPBVYYufj7TnL51XAqaBAHTAVIC83D+mJUgR7pMLqzygY6Hhj0Y8PMbSdKbrUvomva1xHr0/vYOp31tg0ywVX9wbDxToOsRGZkIhkyCPzTo8Dqtdm4/nyFVCykrPKL1CwcIu63sRiKVISchDuk4qn92Jx40AIdv/qgaV9H2JiM0sMr2nKrlW6Hqi7i15/FMrwoGmaam2or/fyntu/B5isCgHTxgEuuQemeEWfXOhvfmZpgNbpJQF9yH0BMLE9Y0rb+Obj8vh+TF+wkEesXR/idbVYUWeRdPc3uVLDkfHyW0tsFfZ7dyme356sCLHvmhP2vAndyH/fsaZ72H6qCLD+TuF9d4biybF9MuM1dlLDMa9pzx3xBnKc62pzUEvnU3Lc5JipY4QFEZ2KR+XpC06mKiE6j+ouNQqXtrYm67UZWXsNINasxbraKIAU7fwmS3RybJDo9mrzHLvD+7Ndbs7N9LTpkeH9sOE7lls1HjBR9xIFTDQeT/0bEm6tapd4Yc7MlOPjj6UcHOiUvqtbVKZeh+ycLS0h3tyMvQakmz+HlFw7Uupc2tG26Lj/VmTjOwCTfmek7+mJBIOReHV8GiJO/ZYSdma5ZcgZATCVtSo9YOpDAdMnSBjTAtGzeiJsxTgErlcBJh0BMH3MooApZPfqkaH7NQ1e7Prd9+XmOfmvVgzDm+mdkCwAJgEwVYyiG5t0P4L+XktdPZ0YDsLMZ7houRtEzkSRDOcMkjIcyCmvjdu/2tCl0ItuKtMIPxrl90J17LcZzom1lGgsw23utiFqyBS5mATAJJRQFbdK68H0VxF5PGAqL5cl72DiAdMzosuM4GASVOn0dwBTaEZNuzABML1XaoCJHWN159JaZ9TQckXtje5osv05Ou/1UQ48ESSaciX8zUqTGNc9D+IvnXdLXm/inz7BPizrW8fI7EZkDgQ7dhmqKgIm2rtmsiqKi7qYKGQaxpjixzrmmNbOGiuHP8G+P7xw51Q43B+9QXxMNmQyRTHwUBIwKfNKkZJTLlUudz+/IF8NLxVAIc1DarwUYV4ZcDSNw/WDodi9xBMrRj7BtK9tMKqROQbX5FxMFCqMUUXl0c14HjDNqmKAid6nPYaGsvGFd9CDuY3ede5gdBsz/NrXHtvnueHP/SF4Zh6HlwEZyEiSknEkY5vHuZVYuFTAwaU8ZdE8sCoxRywEzOfgT4EqSo93qhWQuZKJFXgTlQOPhwm4ZRiObcvdMWOQLfq2NMI3tW+gi8YNDPrcBL/2d8C+ZZ4wOxWBQOdkpCWI2ddW7//0FmAqUCCPiPbz4vt65ebJIcqR4k10FvyeJcH6UhQM1/lh3ahnmN7WBqNrm7PAcQhZC9TVRiHTTyrHD3cNCoCpMtc/DpjYiDLyGN1k39gYYu16rItJTOPyNjeHZG+3bPn5n30U5trXlc7ntZUBluPkL906JwUE1HvfsdIeOaJIp2a5IQ975nrd+lVuv89QemOhu+TY4AyJXge5WPvTAh5oidn+T8042KXfQQBMVVH8vLJgsyPX24jCJQoYKWyk2kDWoF6nPPHRobGia789yLm/83CO0+XfcjxNBqZ72LYJMS7dPUfhEo3Ho6KQie/PRL8OtzzYIM5Yq3Xy5YVjkg0n66ceHfUk7cCAjIxd3+XlbPsCIuqg2/gZpOTakW1pBum21iwU4txzHT4SYFomAKYPqKoGmEJXjEOA1qxQX10BMH3sEgCTAJgqePGbtvT/ffT3Lrrh2ZVoHNFKoqNElgznCnjNFO9rUt5A6V2buhR+UQhGo6leEXkTWREZEq0nouuH9pfqSNSE4WIBP2EEwCSUUBW5ygqY6GdVPFP+Dib6vjRKlO/BVBIwlezBVH77wgJgEvSXEgDTv6pq69XcS2tdC2PxKFyqt9EdzXd4oouBL0acDU6bfysyaINVrL3BkwTDyx4pq4z908dah2R2efgiq4njy2yh71IZq6oAJn7Tnb8/lY3Ks2YdQT8y5mw/ptGfmOGnJhaY/a0d1k54iiM6PrD88yWCvVOQUehi4gFTPvJYZ0wee6vM4/U2YFLmcoCJivuZAla0t1OeMh/irFwkvZIg5Hk6HtyNxYVdwdg63w2LBj3ExLZWGFbPFIOqcy6rkWouphlsTJ6dysVUuQDT9BKaqerBNJvc0rkZQ+ZkAGOEH5jb6FnjNoY0McH0722gPekZTm/0h92f0QhyS0HyazGkYhpHqIrFK8hnZ4e6hihcKgtgYvtj0Ri9wr5N9HUKWEdUZrIU4X7pcDCOwamdAVg98ynGf2+JHo3v4OtaN9Cj3m2MaWeB1T8+xRntADy6Hosov0yIM+XFgCQHvUo6mChgylUBpjwWMuWT+wqlAplpEkQFZcDZPA7Xd4Vg+xR3/PrNA4xvYIkh1U3ZaMehzD12PYxhIZMl6/qaqurLVMUAk+LAFK+okwv9zc4sDVgnAKayAKaOxTf7t38BMYVMuo04V9HamixskmxrpZQe7vdadmO+i9x+z8Vc75trlC8eDRFHezQvy/HSzX5x9KPmypD7g+Xul9co7m+7Lr86109yqP8b8dY2UvH6uux7idZ9Aoluw6LjLtYvSujHVLmlFs3Irzn69eYWbBwjC5ZoLB7twaTXQSE6PCBdfGm2V869DRdFD06uyHC5PTjT9V67FEfj+u9YZtV4uFTyiaiH5xvGm+3qnnxj9eTUC7P00k6MM8s4NPBVxt4eyNrRGaItLdhrhq496abGkG1tzvVL4oFYMcj5zwOmmGNT8cJwYSFgCjguAKayVNUCTD0Qunws/NbNDPXRnW/oozNHAEwfsQTAJACmCl78pi2NfKVunnZEfYlmMFykHN0QfUIUxnCOIOoMqojuJXVRFxOFYHSDOZEohOgx0TWiHUQLiUYQdWE4oNaA4QBbDUaATEIJVZGrNMBUsgdTScBUHg6m0nowUcD0roi88gXcAmAS9JcSANO/N6a05xIvTZXIONTQdkNdXXc01/PEtwd9MfJssPS3u5GBevavjc+4Ju265ZO2wDwwfdD94IxONiGZjR3Cs94b/SNUUVUFwFQSaBQ5mWwK+zFRoDG6uhlG1THD+GaWmNPDHhtmOOP87kA8tX6NVy+yIM6WIy9P5W6hiInCDKK8gjwufq0UKZXFRQETfQ0qCpiolIp8Niov8ZUEfi4psLgWheOb/LB+qhNmdaf9mMwxRINCBRMMZUyLuZh4yDRT1WOqogOm4vNgqyYblQvLhl1PI5l76MfcRS/mDvrXN8KEThb4fcxjGKz2gumpF/B6mIi4F9kQZfJzogZy6Ny8BZhU41/KHNHvLeqvxYEqGo1HX/t1RBY8Hr/B7dNh2LnmOeaPdsDQjvfQtcEtdKlzEwOaGGN6V1tsm+6OW7vC4WGeiMRwERQS9X5bXN8urt8T7dWlUInrAVXAQqY8lYuJQiYlpFI5kmJz4O+YDLMTkTi4wBsrej7BL03uY1jNexjAFK0HCpnGkTXxCxk3HjDNVPXo4se0vOe9LJrCcIBpgjpgav8Ymwa6yg9O9X5p+FuA2dllgevOLA3sTe4LgOmdgEkNMul3KgI429tCQl+DjSurCfG6TyDe0BDSnV+KpKdGx8pNVjvlOh41VARazlNEunSNiSm9F07Jioy0rSWPeNRRHmg+XuF0ZrPCQveO9MJUD/G+bgnijU3yqGNKRN9Ppx4bVSamzpYdJSGTAJgqpdQdQHxEHr2lTrWNTSHRqstF42nRuW+VKzrQK1V0bnKI6O5a0xzbfVuyn1wYm+l6i4VLpQEkRhWNRx1LJZ+nj78x3v11wi3teclXFh9OOzvNPv3oyNDMfT9IsvW/hIj2XNrUmHUv0VspWXvS7XwvsA7F197fWn+lACZynwNMPfDm4AgOMJ1cmBJ2SgBMH1KVFjANUAGmvgzSBlHA1BxRM3sgZPkY+GnOCPVZP1cATB+5CgHT3jUGYbt+943cNDv/1YqheDO9YyFgShcAkwCYyq/4eLw6RM0YrjcRhS80Su4AkQmRB1EMw22U0g1TCnDKK3aqrM4BCsEkDBfpRzd33YlMGW4TehXRRIbrM9WW4WIB6fnzLgIBMgklVMUsem3S67SsgKk83Zb0c5IHTHwPpr9yMAmASVAFlQCY/r0xLTkG5DGNDe5osPk5Pt/hiS8P+OQNMgyUzrrxInyzbazpefekreZBGb/Yh2V1cwjPamYdklHHIihD6Ln0gVVVAJM63FDffJ/GbmpbFTqZhlU3xbBapviptSUWDXyAXcs8YHT6BbwcE/EmOgfi7Fwoc/M4uMSCgwL2Pg+N3gWaSoNO+fkcGCkgL5OfVwARee3YyBy4PuDi2Pau9MTyUY8xqZM1RjS4h4HVTFioMIIFCpbsZvw0hodMlQMmqEM+LuKPP3bOVfYL2xvLnI3H61ftLgbWMcaYNub4daAD9Be747pBCJzUo/FkxUEOBX50PmhcXp5STX8xHxxgUoNB5OflEiVS4sUIep4M6ztROKbni9Wzn2JCLyv0bmGELnVvomeDOxjT1gJLBz3G4aU+sDoRjcAHqUiLkUIp491uKscbeY/c3FwiBSeFovB+njKXi+oryOX6QEHJfm9GsgThz9NgfykGJ1b4Y+2AZ5jWwgbDNczQn4xPf8aYXQ/DWOhoTq5FS7a/WBUETLKDU70jDX8LuHd2WaCmAJjKAphUkGlHx+Kgid34bwLx+joQa2mQ29qQbGmWL93/vUx2cdJruYWOndLt/HZl2IMxkte+regmflmOO9PP8TPav0nhYzxF8fDoNtndVXckJ0cFiPU7Z1OIJVK9l1j3M4g3fw7JttYqQKHuYqoAwETQh6kkqKGP0TW2hbqXGkLCRuPVoX2XCkQ7v80UGY4JFd9YYiO20DuQ/eDYnAzHS9+lOJ6u/xfrrBofj8eo/vij90OM9TXijLe2TryxbkLy1aUGKRfnuqSd/iU549Agcc6ubwpEdH2R60SqgkuSLZ9zPcD0vlBF4/0Tzrn3A6boo1MQfuLXlBDDJZZBhssEwFTGqlqAqTtClv0IX81poT7rZxt6as352W2JAJg+VnGA6XcBMAmAqaIW7wigLp5WDNcXhG5+0ii5s0QORIFEb5jy37D9EPcAv7mbxXD9WAKI7IjOE20kms1wfaYoUKMb1fVV4yAAJqGEqril7mCiSRffMhxgWkF0mMiC4XowlTdgKulgUgdMOozgYBJUqSQApn9nTOn50muLjikVuf+Jtjsab/NE290+BV8f9MvsfSIgZtzFEO8lRi/v7n8cv+OOb+qUxxHZ3zx7mfNpuX1gVIGqyoBJHWzQc6DOIOoIGciYYHiDe5jS2RqrxzniuI4frK5GIcAlGYmxYkhFuYVwiO+llJefzz72dwATX0plAdJTZQhlI9le4fzOQGyc6YJ5PR0wpqkFBtUwQT/GqDAqbzwblVc6UKioUKFoDmzYSLw5bCyeHTsPPFwaTuegpjEG1THGjy3NMPsHO2yY4YRzOwLgcDsGwe6pXDReTi4Lj/4vwJT/9jxQ4ifOUiAmLAvPbF/jyokgbFzhgpkjbTGwkwm6NryFrtS91MwE07+zhc4EF1zcEIwnV+MQ4ZqJ7Hg58uT5aseVz7qoFHJFqeJgUy5ylQryfbksYKLxfdlpMrz0y8DjG7E4uzYQ2kOdMfMLO4ysxQGmvmQtUMg0hNwfTdaDAJgqf/2zgKk9iqLLVP2YKATY2pIDPTp1IV5fCxKd+pBsbwPZob4S+dW5gQrbXZdzvW4tz33xuG/OC++mISGl98VRL/o94qBHzXP9LXsqXC7MlFlt3yu7MsdeeqR/rGRbG6lYp16eWKsWB7Y2NISEQibaB4eNVFOpvGGJoA9XybVF1hGdW/GGz1j3EguYdMha29ZWKT7YJ1Z0YfqDHKO1R8X3dy7KeXBsUIrjafrHXZn/qKORjC9dzT5/Y3n864TbWuNSrizanHp+hnXaqZ+TM46OQNbeHhDptSfXSFNIdbm+S5IttPdXa269scfc4aMDpmABMH1QVTXAFLzsR/hoTgv1EgDTRy8eMIWUBEzTBMAkAKZyL94NQH+fpZ8JHYgGEs0l0ie6ReRCFEmUynCOIOoMqsjuJV50c5duLosYLtovnOEiqug57SVaQjSG4TZ52xB9xnAxgUJMnlBCVdyi16Z6RB6NueQdTBUNMKk7mPiIvJIOJh4wCT2YBFVgCYDpH1U1fkw1VeP5O9EfzuwYNNz0HJ33+qLXscCcQaeCgkedD7Gaci3s+O+mUSsNHN9MNA1I6+oUJcCl/7dOzvdvf2phwBzDBQEXD0/3DdRjAdPTSgmYeMDBO2d4TWf7Md1nXUHDGRo/ZszCnNGNzDCrix10Jjnj1KYA2F6PQfDzNKQlSlkXkzpgylfF3XGQiRPtC5SfX1zFnTMlwAYpuTyPhVg+z5Jhdj4SBqt9sHLkU0zuYI1h9e6xUIFCJgoVRqmgAgVkxd1AtqoYQNtyH+/Sxp93XFG4NI9oLtE0cg7jGQvWjTOgmhH61zHCiBb3MKO7DdZNfobjG3xhdfUl/JySkRAtYiMF83LVIQ4K3WTsWOfllT4Pqq955xIXc1hQbA7o83SO/d1TYPrnC+zd+BwLfrbH0O9M8W3Tm+hU+090q38Lo9tZYOmQx9i30BsmByLhZZ6EuIAcSFNzUaAseAsw5cpzi0mhUq4ilwVMFC7RSD8ap0f7QuVkyhATmImnd+JwYX0wdEe6YE47e4yqbUbWgDH6kHVA18Mg1VqYUAUB0/L2j7F5oKvMYKp35KnfAu6dWxaoeXZpYO9TAmAqI2BSbajzEIBGmFEXx5bPyWt9BrF2HYjXUcjUANLt7SE9NjRJfmv5k9xHh44oPG/Pzw2x7CnytW1WlmOPtLWtJQow+zz3+fXeuQ+PLJbf0zwnvTDFXXLwhzeSbS1E4vW189loPi3yfrqfcS6mwr49nYSYvEqnDty87fqSqDP3GO15tKEhmeM6XO8l7U/JWv0C4v09sySnxnqKri08IzFdvzjbSr9/ps3hdnHGR+t8yPURGBjYKMrVrk/C/aNzU26s2pt2doZZ+rGR4ZkH+xZk7emGnO3tOIecbiMWLtFYPNa59M5YvH8GMMlYwNRaDTB1VwGmyQjjAdMJATCVtSo1YOpbHDC9nPk9gpeOhs/aqaFeWhQwzRQA00esQsC0e41B6M7ffSM2zs6PWf4ewFQB1pIAmP4TVdINQDdrxxL9QXSM6D6RH8M5gKgTqDLE46kDJgrDpETpDBfx58lwG9AniLSI6DrqR9SJqKlqHDQYwcUklFAVtd7lYKKA6QiRJZE/U7wHU0UBTOoReT8zgoNJUKWRAJj+URUDTGQsmZUu7G1dMqbtd/pgwIlA0bgLoeE/Xwkz++Vq2I4Z18OnLjd5+f2+x/Ht7/qlfuYYmV1+NLqKVFUDTNMYzj2jDplmsJvb1uzGNt2oH8yYsi6hoZ+YYmxTC8zr7gDdqa64sCMIjmZxrLNFKs4tYXopKFRJqPQ2ZOJ7MJUEJGBBVU66AtHBWXCyiMe1PaHQm+OBhb0fYnxLSwyqTZ0rdzGAMWJj5KjjZxI5bgoRuPOxY3sy8b2Nynus3wWY6LHOZewxn4gCJjr+dOzZvkvV7mDAZ0aY8K0l/vjpCQzWecPkTAQ8HyXidUQ2cjJorFy+augK1OagxFiXAvjUVVAIl4rPgUykRMyLbDjef40zB/yxZoEjfuxjjq6tbuCLOlfQ/pOr+OGzO5jUxRraE51xRisQDudjEfw4DSmREiiylUAe/7pcvy4agceCJFbK4mLhkpIDTHkcYMrLVyI7Q4bogEw43nqN81pB0B3ugjlt7VjA1L8UwMQ5mKwrLWCaqgJMEwXA9M8Cph2q3jgsyOnIRYTptSGv0RwS3YYsYBKv1YBEuyGk+l9LZKfGv5CbrL6veHRgr8Lt/AyF66XvEu6fr1uW44+0PVlL6nGzjczt3CjFg326CtO1t2TnfvGS7OsWL9nURMb2faKQSbsu2w+KPb7CCD+1Xj7lDk8EvXdNse64Tipw2YmNxhPT+EWtuhDRvkva9SHeStbZ/l4SKVlT0mvzjcTGazVzLLYOFFvubZ7kcIj+UfdB7qUXgYHfxLpaLXhjfeRkyp8rnDMMJ0Rl7uuVnb2jI3K2UGdeI0ioQ06Xg0tSNhavrQpkqruW/l+4RFUaYPoCIjIm6bu7482B4Yg6MhmhxxekBJ9cLACmD6iqApjejGmOyBnfI2jJKPisnhL6XGuWCjCNFQDTRyoWMOlTwLTKIER/he8L3Vn50cuGIn5qRySPqisAJgEwlWfRPQoKVBoyXC+i3kTTiDYzXDP6pwzn/KEOIDFTtFlbGQATv8FLHQzZDBfxF0T0UHVuekS/Mly/KQrWaC8UGhMouJiEEqriljpg4nswjWKKIvJ4wMRHetLPrPL4vCoZkVcaYKJxpHwPJgEwCarAEgDT35O2+hi6cqLnqFl0W4Oo9jo3NNjgkdt2h7e475HAlJ8vhgXPuRFhNedmxJ7p18Onzrge3mmxUeQn+g6vhV5L/1BVRcDE9/8pGZP3C+tismDj56iTiUKmwRomGNvcEgt6P8DORR4wORuJoOepyE6Xl/AeqWBCGQCTOuAoCTdoKSR5SHktRZBLGmwuRcNwfQDWT3DGrO/sMKqpGfprGKFfdQ4yjWRMMYEcM3Wu0HOZrYqcm1mJABN1MtF4POrK6s7cwnfMTQxoaoQZ/WywZbEr/jwcCqf78YgKzkRmigy58ry3xr0wHq+MY1/q+JO7ecoCZCTKEOCeCtMrkdil5YE5Y+3Qq9MdtG1wBZ9Xv8QCpv6fG2NOb3vsmOOB6zvI8d2OR6R7BjLIvCnJ/CH/bcCkzC2uXJUoXGJ7MKlUUJDHPpaZKkWkTwYe/xmLM6sDoT2IrIFWfESe8Tsi8gTAVJnr3wFM7YvDGxY20c31tpBsbgbx+noQr/kE4rW1INnYTCnZ3zNVfmFSgNx4lYnCTm+z/PHRMdLHZ1vTvjdMGX4BT3WxbKDwvN1V4XZ1huLRgZ1yo5VmslOjgsV6HXLE6+uS96oOseYnkNAYta0qAFAY5afS/735L+hfhUvFemd14OaQRuNRqETmVkSh5Sby9d7vZZKzE6Mkt5bbSiw27ZFY75yQbnuwTVl7e6mqWmRkZK2goOjmUb5eo18/NdqVYL7HMfXywszMo8PzsvW/hGhjU/LeDSDRrsO68SSbmqrWVjs1B1+nfyAWT11lB0yBAmD6oKpqgClwySh4r54S6q41y9BdAEwftXjAFCQAJgEwVbyiexXUxUvdO7QXEYUti4kOEJkReRG9YrgN0srkXuJFN3jpBjOFYylEEUSuREZEBkQriSYS9WI4wNZYNR5CLyahhKqYpQ6YaLoF/Z2WAqZlTFFEHnVdVoSIvL8CTDQijwImwcFUKaSlBggKpXq8JFDgVd7H/I+fv5sAmD5E6muBBUvkGlpLtMaZ01pn9vEGuu5os91T8e0+3+TBJ4LCp1wKf/bb7cjrS4xe6i24HTljxvUX3ab9GV6r3D4cqmhVRcDEQw510ccnM9z50Ki80Yw5C5j6MHfRv5Yxxn9hidU/OeLczkC4OSQgOU4MpSL/LdDBuZjyi3oB/Q3AROPVxBm5iAsXwdM2EcbHI2HwhzdWjXHElG+sMbyJKfrXNkLf6nfIMRrjR8aMzIEle15cXyN71snEn9fUCjDm09hjsWVj+4oi8jj3EoVNtJ8UBSbfMNdZDWxujIWjH+DwRm/Y3o5BqHca0hOlkEspgHkb7JUZMKnmpTTnklKeDxEZ95jgbDwxj8O5PYFYO/spxvW0wNdNbqBFzUv4nLmEThrXMLT1PSwe9Aj7F3vD+GAEnlsk4pV/NrKTVP2XCkoCJr73lvItUahE4/q4flB57HlQ8JSRJEW4RzrsL77CyWX+0Oz9DNOb2mDEJxxgoqL9wmjfsDFkvU5UXYdVGjAtFwDT3wNMvPhYM5VjaFsrtl+OWLM2xGs/gVirHiRb2sglBr2TpOd/8ZIbr7gkt9FbIX1yvJ/E6XzLsjiZjI2Na7D9mIJseiu8b87NfbD/sOz6r08kh/okSzaTc9DUgHhNDYjX1YFYtzF5P9W5sMelDgLKG6QIensdqbmW6C2FNdu4vksSnU+5uSXrSKTTEOJdX+eKDcfHio3X2EkdDPZLn52bJXK99F2c24fF4rnFxdUJD3/dKsrPs0+Mi9WKNzbHbyXdXBuVfupnZO3rARF1LmmTdatVG5L1tTkHE3XHbf8Cb7ms/u9YPHW9HzC9PDwZocfmpwQcX2zpf2Lx7wHH5wuAqQxV5QDT4lHwWjU51F1zlqH7GgEwfcwSAJMAmCpo8b1MqGunFcNtdtJ/VU+j484SORCFECUyXB8jfqO2MgEmeqw0Jk/GcJu8sQzXn8VGdY4biWYRDWI4wEYdEfWZopg8oYQSqmIV3zeupIOJB0zUwaQOmCpKRF4U8zZgKtmDSQBMFU5aalrnWkJupUOmqigBMH24CgGTCkhqquDSaidO65xRR9cNbXd6Kfse8U+acD7Ud8HNSMuVJtFH15rFrFxhEjVu/q3I76ZeCxf+YPsX6uQC//anfguYY/hrwMXDM6oSYFKXbWG/InoePzP3WeAxhDHFD8wddGduY9CnJpjX3x771nixwCMqKJOFEVwfIKB4VFvBh0n1nzozobAjK1mOKL8sOJm9wY2DYdi17DmWjHiEiV9aYWgTU/TT4FxMw8lxUufVZJWL6V2AabqaPt5YF4Gl6SWgHh/lR91jFOjRsf6K+RNdmBsY2e4eVk9zxOVDwfB4lICEGBHkEiUK8ksCOdXoFfCAqYD9nrKM+1tQLz0XbyLE8H6YDCPDCOz+4znmD3fAoHYmaF/rGpozl9CKuYwudW7gx/bm+H3EExz53Rfmx1/Cxz4Z8WE55DXkyFfy4LCg8AhZgKQsLqVKLFgqUPWEUvWFUsiVSHsjQYhzKu4bRuPwfF/80dURkxtYY1gN2ifMhIVLdI2OYO5hLJl/eh1OVQEmfm1/7Pn+VwDTIFeZwTTvyFOLVIBpWWBvcl8ATB8CmNSlHpdHN+E3NWN75bA9c6jzROdT6kiRSQ71jZNdnvpQbrr+kOzhoblSp7N9JS6XW9EYvPedR0yMY23JK++WuREO/XI9r/2hsNp0Q3Z+0gvp7i754g2N2Ug+0WoKtOpDvKEJxFtV/Zj4fj58n5zyBiqC1MS7zFR9l/hYPOpUokCJh5TrG0Cs1x6iY8NSRbeWPxM/PGog9TKeLg6y+z7H+37TD7keqNMpJCamRUyAd79YV8v5CTYnjyTfXOeUdnpyRtaBPsgh7yOm/bzW14GExi5uoO6lJlzfJda9xMcv/tPuJaqSgKlNIWBK290d8fuH4eXhSQgRANMHV1UBTPE/fo6I6d0QsHikAJjKqUJWzqgfQAHTzlUGIXrLfcM3zMyPXjYE8dNUgGlQKYCpAq4tATBVuaJ7QPT32EZEHRkOsswj0ie6xXBOn2iG619E+xhRUFOZ4FLJTV662UxhWRjDRf/dINpNtJRoDMNt9rZhuLjA2owQkyeUUBW1KIyh/9iQAqbSHEwUIqsDpvL63OIdTJkM52B6xnCASYd528FEz6n8oPZ/HjBpvUPr1KSpBpfofU2159718+V9Xv/0+AiA6QOlBpfWFjmXqq9zYeFSq52eyj7H/JOnXQnzWWUaZbzFOnbPdtvX8zfej+23wjSq1awbEfV/vhwmxOL9C1UVAVNJ2DJdDYBMZ4EHt9FNN+57MXfRjbmJXhp38UsXK+jOdcbNY2HwfpKEhGgxpNlKFOSVdCIVlAAfHwiYVC9Bo/LS4qUI88zAI6NYXNwTjM3zXTF/oAPGtrfAwAbGbFTeIMa4sAcP72KqSICJA0t2hZquctXQ45pExnkCOW7qwunB3Ma3zA30qnUHk7vdx/albrh3ORJhvunITpOXApdKAqa/Odak5CIlkqIlCHJKg+3VGBjq+kNz0jP80vU+ejW6g3bVrqE1cwUdmGvoWf8OJnS2wuofn+LYKj9YnoqC36NkJESKIMlSqK0HdcDE997Ke0sULlGXE+94yyOSSXOR/EoM/8cpuHfoJfZO9cLijo8wQcMKQ6qZquDSPbJGzVg4R4EoXbNVHjCtEADT/w2YeEjAbriT19jWmo3Kk2z4FOL1tSHWqgXxhk8LxPodcyTHhwXLby66J7PV36VwPj0n1/3GDznetykkeN8f/tVCQkI0pHFurfNCbMcrnp3eI7u7ylF6cnSqRO/LArH2ZxCt1oBobS0OMm36nDsWCpeou6rQbVLeUEVQkdQAE3UE0ce2tGCBJAsnCx1wrQskh/rliq/ODxTZ7rkg9jSdn/PC7ZvUcJcGjo6ONT/keoiMjPw0Oji4++vndnMS7Az3pdxaZ5V2avKLzH29JSxc2tgUEp36nCho2txUdW2oxS7u4PVPr6f3A6bIQ5MQcnRuSsCxRZb+RwXAVNaqcoBp0Ug8Xzk51G3NDEP3NdMEwPQRSwBMAmCqgKUeM0U3OLsyHGShkXHHiayY0mOmKhtg4iETH5OXxnDQ7DmRuepc1xFNIepH1Inh4gLrMkUxeUIJJVTFKf6zi16jNCKPdzAtZ0qPyCtPwFTSwcQDJsHBVCGk7krSVGmtS5FYKKAOQFxK6D3PqQMpPlKvvM/5/xkrATB9wLpSrS3N4rF4NcjXdbRd0WiLR0G73V7iPsf9E6ZcDfNaYxZ1d5fDa32Dx2/m7H8Y33uLzetm5fZh8B+p/xJg4l01VHSz+0fGHP0YI3zP3ESPGrfxYzszLB/7GMc3+sH+5iuEPk9H+hsZcmV5/zxgIpWfVwBJdi4SY8Twd06BxdUoHNngizWTnmJadxsM/9yU7cc0gDHGsEIXk7UqHs2uWDzadKb8ABM/rrMY+2KuJeoUG8v2vLrHxr31rHkbP9S7g1EtzbB05COc2OKHJxavEfcyBzKJshS49PcAU3G3GZCryEdmkhwRPpl4ahyPP/eEYsd8Dywc8ACjW5uje53bLFii+qb6DfRvaITJX1tDc+wzHF/jD6uz0fB3TEEiBY45uSjILwNgyi8CTAUlAJOSfJ9EpGCBlZddEu7sfoEdEzwwv7UDxlS3wCDGhBXtE0bhEh1DCukmCYCp0tfHAUzqPXQ6cK+zvQ0kW5pBrFMf4nUUFNSmThCleF+3BBqVJzPVvKt4YKCncL04Se5l/HVSwPV6NArvfecTF+dWJzfauXuun8lShf3+q/Kbi/wkR4amSra1l4u1GkC0VoNzvvD9mOjx7exQ5LDi+0aVO1z5L6tDiTXTkYtbpGBSt1ERXKLzuLG5Qry/V5rk0vQoicVWM7HrNe3sUMf+FC59yHVAQVRISEj92IiIjq+8nSYkPLyyLdloo0nG2Wn+WQf6JufQ9bOxMVmvtO9SPQ4ubflc5Vxqyx3fDrUeUTv+yWg8Xh8GmHyP/va7lwCYylQCYBLqnyoBMAmAqYIV3cSkvztRJ/hnRO2J+hDNINrEcBugjkThRKlEEqZyupfUARO/0ZvFcBvPgUQPiK4QbSdawHD9p7oQtST6lOFi8gQXk1BCVayigIl3MFEYTAHTSObtHkxvmPLvwSRE5FUUVVMTBwHUwBILAIhWOxfXGg6ksM+tVYNQhTCqxM+ucuHgyyr+59VAFQ+ZqKNFvTdPZenVJACmDxsruj4K1wWn6mQt1NNxQ8vtnuhywFc87HRQ9Kwb4a6aFtHX9zx4veX404Spx58l9Dz46E3zLTavhV88/uWqqoCpJASZrupZQ50/s1UQZDzDbeb3ZG6x7prBjUwws4cNNs9xxdW9IXhqHo/o4GzkZCrYaLa/UxRwFAEQlOgvBOQrOcj0OiIbrg4J+PNYGHYs98CiEQ/xU0dLDG5gggHVjdl+UZyLyaoY2OEhk3ok4L8NHKYy6q6pIrg0m43us2ePicKQMWR8h5Dj7s8YoVf1O+jb4C5GtjXD/L722LHIA8ZnXiDALQWZKTIWtr1zDPH2uKk/WVDawKp+TqHIR3aGArFhOfBg+11F4NAfPlg9yhFTvrRmx/e76jfRkbmGL5nr6Fb9FoY0MsX0b22x/icnnNTyh/XFaAQ6pyL5tYSN8Sv1vQoK2DVSai8ucECK69WUj1xFHnIy5IgNyYGb+Rtc2xaKTaNdMfNzW4wkczyQKZpvCpd+YizZa3Ayew0KgKky10cBTFQ8KNjJb8K35/oxbfyMczCtqwnx+rrkfdpIJYf6vZFenuUrM9e5JXc8qi3zvDlKFnK/bWq4ZYOyQCYalacMfzxS8fyarsJa/7b0ylwf8prJki1tyHvU5/r2rK8HyUb+vL4o6hWlL/RjKncVwiWVq4wCnG2tId7clO19JNZUwSVd8vXurmnis7/4S+7pWEmczu2UBNlPkEZ6tPnAy6AadS69CgjoEOfrNOzN09trks13XU27OM87+9DAZNH2DlKxbqN8FizRWDwKmTY1LYJL6uv7X107JQCTXmmA6RcEHZmT4ndsIQeYDgqAqSxVWQFTxgAGWX05pQ0sAkz+i0bA449JLGByFgDTR61igGn7ct9wHQEwCYCpXIvvvaQeMUU3aJcQHSAyJfIkesVw0U60fxHdKK3sgIluNNNeUilEkQwXAWhEZMBwzq0JRD8QtWO42ED6O375bvoKJZRQJYv//KJQRt3BRAHTIaZ0wFQen130PfmIvLICpupMeX3e/JcAUzUWlrgWOUzeBZd4J9I6zn1UTdsdNXQ4VSf3OZjgqgYT1AATD5loLBoLmFwEwPRfAEy8e4kfp5Xk2lnpjOpkfdQna6a1nhd6HPKXjbsQ+mqRUaTjJptXlw4+idcxdE74+ZRzYpejjglN9jjEa5TLh8B/rP4bgMnmLcBE79PzGsG6a+6iF3MH/WsbYewXFlg85BH2LPPEnRMR8HqSjIRYMWTSvDJDpbfhQ3GVrDxlAQtZQnzSYXM7Bobb/aE90xmzetnhxxbmGFybi0yjLiYKHOgm/ZRC0GCrcjRRlR9gonCJ7w1F35+uG+rA6UPGtidzm43FG976Hub0t8eWea64sjcEzvfjEfsiG1JR7t8e278CTMrcfGRn5iLupQi+z1JgdSkahjoB0J3kgvnf22Ps5+boX9OIjUj8irmOLjQqscYdjGh8D7O72kFnojNOke+3vRKDYLc0pL6RQiEr3WnFAsR8HjIRFfAqcjtxgCkPcqkSmckyvPTNguOdOJzfEAStYU6Y0sSajRKkjjUK5qjD7icy3xNV7iV1wFQebjUBMP3/9fEAk8qVot6PiW7Osy6mBhCvr8X1Y9rwab5Ev71UcnRQivTKbA+51eZzcpfTK5T+ZoNlYY7tU0IcaUPmv/yFPCHBu648yuNLebDtzwqXC5sVFrp3pBenBkj39xSJt7aCWLs+65hi3VPUlbK1Bbt5zx2X6tj+cfeJoLKvlY5FsI+NVGzFwSUaqUjnjbrddMma3PmVTHzix1DJ3dWmkicnd0p9raaJIj26JAUE1PuQa8Db+37daN/H7V572gxNcLq9NMnqwMnUa8scM4+Nis/Z9Y1cvKlZvoSsmUK4RK4JGtXHgkn+eNUdev/a2PwFYNr1PeL2DUWEwc8IPDQ7xffIr5a+hwXAVNaqSoDpxbTv4PfbcLj/8XOoy+pphs4rBcD0MatUwLR0COKnCoBJAEwfvejvSnQTk+5fUJcO/ccXPYkmEa0nOkPkQBTEcP2KKJCpzPF46pu9NCqLurHoZm8sw/VpsSE6S7SRaCbD9aH6iuHAG/29gY/JEyCTUEJVjCoJyL9l3u7BpA6Y6HVfHg4mMMV7ML0rIq85U/yzpnzqPwGYtFRwiY8vUwdMqggzqmrk6+rk8RparqhJfk5Dxx11Nnqg3ubnaLCFU31ynz6mscEdNbXdUIO8VvW1ruzPFodUpQAm/rgEwFS1ABO/tmhvrtWuLFhir52VLqhLnmu11QvdDfzl4y+ExS81iXLZbv/64jGnhPXn3ZMmXnRP6nLKKbHhgUfxwi8bH6n+S4BpRgnANFkV4TaM3dQ3Qr8aRhjS0ASTvr6PVeOf4hiNyrsbi4jADNYF804XzfsYyHsAEy2pWInXL3Pg+iABtw3DsXeVJ5aPfoJfOt/H8Ib3MKCGCetsoUBsnAoy0XPjoBmn8gJMs9QAEx8/SN1h9Hi/Z26hK3MTvevfxcQuVtCc9gxndwTi4d3XCPdOR3qiDErF34d3fwWYKBRMeiNFsGcaHhq/xuVdIWw03rKBjzC5HRnX+qbox9xFd/YYb7C3/WrcxegmZpjznT10fnbGKd0A2P4Zw8UlJkrfeaxlBUxKZR5k4lyk0t5bHhlwuPYKJ9f5Y9UgR0xsbMk66qjjayi5HcuYk2uP9l6yYtfqFAEwVfoqP8DUiXucd6aw8KAOBxB0G5HnOimlx4fEym785pBrv+tIruf133JDH/YXR3s0f5+LiT6fFRvYSBH2rJvC33iK4smRXXLj1TbSsxNiJfu7ysn75YnXk/dapwGxdl1yfo25yD722Dqrjk0ATOUm9Z5d279g+xyJNzRQ9eui8YYNCyQ7OivEx4clSq8veiy13XdQ6n5nljj4SfecsOdNyuJyU6/454+aJLhY9k50vLIw9f5Bg7Sbq+5nnJoYlrW3u0i0rQ19P7CAicIlXbJWNn/OxfVR+PVWlJ8AmCpjCYBJqH+qBMAkAKYKVvRfytchop8BtOfQEIaLiNtJdIvIheE2Q9OZIvdSeW3Q/pOAiXcx0U1nCs9CGS4K8AbRboZzcP1I1I2oNVFDRnAxCSVURSv1iDzqYKKAaTRT1IPJknm7f1x5OZj4iDwKmF4yZXMwlU9VacCkAkvVeKhUTC4s5KhJpKHlitrarqir44YGuu74bLMHmmx9juZ6Xmi10xttd/ug/R5O7cj91uSx5ju80GTbc3y2yQMNNnignrYbapP31FC9JoVU1Xi3lJZaTN76ErCpoksATO8fG/XYRR4wrXRBLU03tNjsie4H/CXjz4fGLTOOctFziLt8wjlR6/Lz5PHXvJK7XPZIalRuF/9/tP5rgIl3Mc1k+wTZsOdGN/IpZOrLGKH3J3cwpKkppve0xaZfXXHjRDg8HZOQECuBXJrHQoQPZiBlAEx5ynxkpMgQ6pMOB6NYnNsVhI1zXDGvtz3GtLTAwDom6FvdCIMYYzZGbTxjyc4JPY85atCsvAATL/re1G1D3Td9mbv4lrmBLkQDmhhj3mB77Nf0gvWNaIR6piPltQQykfJvjWnR4JYOmGjkHoWCL0Oz4WT9BrePv8D+FV5YNcoRM760wY+NzDDoE2P2GH9gbrNwibrYBtY0xpim5pjXzZ51Op3ZFMD24wr3zkBGsoydp9Ln+G3AVFACMJGjQm5uHsRZCrafU8CzVFidj2Yj+5b2e4yxn5mzcIlCL7oeqXtpEnvtcb2XpgqAqdLXRwdMfBQdDxB2tIOYhUzNINZuwMXXaVInUyPy/FciqeGYMLnRShuF45FDCl/zOYpIpy4xMY7vnQvaU0cU6dQsN8S2Z+7zPxfKH+wzlN1Z5iIxHBkn3tk5W6zTIE+sWROsdOqT86Mupg6ca6bw2P6NPjqC3i3VeKtHzdF1p9uQg0vrNDjIo9dWKjkyKFFyba63zHzrZYnzxeUSP6s+dL69vb0/+ZD1H2lrW+u1t22nZMerk9Os9u/JuLXKKvP0pMDsg71SRdu/yKcON4lOPaL6nHNps3rfpRK9xf71/l1/DZhe7xuKFwd/RsCh2Sk+R3619BYAU5mrygGmhcPh/vvPoU4qwGQvAKaPVo4CYBIAU8Up/l//U+c37TVEYco4olVEx4msGM7Zo745W9ndS+puAt7FlEYUTfScyJzoBNE6oilEfYk6EDVhuE1sATAJJVTFKQpheAeTekQeBUxHmLcBU3k5mHjARCE9dU2WBpi6M9znsNCD6d/d/Ffb+FeBJQqcami7QWODG+rquqPhJg803focLfU88YW+Fzru9sbX+33RzcAPPxwJQN/jgRhoGIQhpzgNJvf7nQhEr6MB6HbID9+S7+202wftyM/SHjvNtjxHo83PWYhSe4M7+17VeKikVQpsquiReQJgevfa0nJ9G1yStVaNqM56d3y+2RPd9vkrxp8Le7XcKMpZzz7u0gnnRO1Lz5PHXfNK/uqqZ3Lji+5JH/QvYYX6/+u/AJiKIBMfKWen6l1kS86L2/SmQKQ/Y8yChp61b7O9gpaMfYSjm31hezcGYT4ZyEiSQ0Eh0//BQ/6qZGIl4qNE8H6SBNPzkTBY540/xjpi0jfWGNLYFL017qJPtbtsfNpocrwU5LCAqZo6YLL9CNDBtlD8eM5UwSXqtJnAWLJOKwpsqDOoR43b+LG9BdZOeYorh0Lh45SMtAQZpDlKtgfVP14FdCzzkPBKDJ9nKTC7GIXjG/yx/hcnzO1mj/FNLTBEwwT9q3Ewp48qIrEfY4QhNU0wjjy/oLsDNk5xwdmtgXC4E4sIv0xkpSpQ8I5eUTxgKhT9WvWf+oEp5HnISZfjdbgIng7JMD4eiT2LPfFrrwcY2fAeC7yohjOm7DhOUQNLU//1ef04gGmC6jNlRh1bLGv/GJtYwOQTeWpR4L1zK4I0zy4L6k3uC4Dp/wFMvEq6mNScTNQdIl5XG+I1NSBaWwti3Sb54j3fpcvO/xIhN9exUbic01OG2I0SRfo2K8u5hYQYa0hC7Vsqfc2GyZ0vaCqst1+VXZ/nKj3SL0a8pYWY7f20tgaom4ntqUPdMjtKgQYCZPqXpT7O3FiLKXjc3oYDjzr1uD5dtEfXlhYKiUGvRMnlaT5Ssw3GsifHt4h9jMZKgxy+8PY+/0Fwia6PGE/HFikeZoNTbU+uS7+z7m72uanBOQf6pIj02snp2mfBEo3G020ICTkWdp2yfZdKOJc+CoxsBymrtpDtKAJMOTs6IXXn93i9dwheHJyIAINZKT6HKWBaIACmMlalBkz9OKUNooCpGcKndoXvwmFw/31iqNPqqYbOKycJgOkjFg+YAnb+YRC8falvmM6M/CgWMHUQAJMAmD5m0c1LuodRi+gzhus11I/houG2EF1hOEdPOMP1KaIgRslUfvdSaY6CLIbbgA4kekB0iWg7wzm5hjOcK4I6CxowXJxgDUaATEIJVRFKPSKPB0y0h5y6g4lCcvUeTOUJmNR7MJUWkSc4mP51CMDDJbankgv7NY21q7PRHZ9RqKTvhU57ffCdgR96Hw3A4JNBGHU2BD9dDPsfe+cBFdX1dfGHvWtibIkaNSb5p2vsxh6NsSbGnsQUa6KxixUVe++9d6VIE0QUFekdpCNI70hnKsX93fOKjnwaS0BQ31nrrIGZYd599943A+fH3gc/nQjH2DMR+PVcJP4wuouJxncxieWf7OvfzkdiPHts5MlwDD0ahv7sZ3rtCUIngk7stT5c74fmq3zQ0MALtRZ5oIq+mwCTROXUE/sylfecyYDp+QCTjhqOvieYWF3fHfWXeKLFSp/irzYFqAYdDIuZahTtsPJKwuHdTrxyafAJr7SPj3ml1T0sw6VyiTcNMEmQaZQOaKLHqZjfg7vIA6bP9c6i89vGGNHRBov/cMXJraFwsUlGTEgu8jK0KCwoG8JUxF43K02DyIBs3LRIwNH1wVj8iyvGd7FD3+Zm6FDTCO248w8ULtSbh87nIWC68lIA0yhx/iRVmHRMAS5ZYgBnzkOwjtwFvv9Sj3qmGPv1Faz+yws2Z2MQcycPBdriJ8Ka/xoF6mLeei/MJwvXjONxeFUwDH5xxx9d7DHsvUvoW9MM3fVMeFtEsvHj7RFZUu+j3lUvYnAjK/zW7iqWjHTF4RVBuG4Sj6jAHORnFQBPGPLjABMeA5g06iK+/1JUYC5crJJxZmM4lv/qjnFf2aFXPWHOCDARoKPrTnfvlvc1JAOm/x4vHTCtbPVQ+UFwabWOJd3SplDMrwfFrGrI/6cK8mfXhGJJ00Llpg5K9fEx4drLK88U+JyfrI12+lLss/PUAkBqwNXamgCrjzWeZ4dqHXYu0l6cc1p1YIinYu3H6YqFDQSbvDnVoSQbNOqrY9BcOM//Bw/KG8K8zikBJnGuV7QUVG20/xay/Te/Np884Fn7aZZq//cBKuMZF9XXNq1WuRwfq/C1+jLTw7be8+x7UjqlBrg2Tva71jHN8eRvGWbL9+Qc+dk9d2v3rHzDNgXKRW/dF5RLLPXrsmM3fKhcKgkhX9r++HfAFLeuJ8I3DsVtGTA9d7x2gOm33nCbOjTUafpPe27JgOmlhgyYZMBUQUIqzNLvSlSYpc8CKsySNdwmlhdZenFCfyICMFQYpQLp66BekpIKzVRwVrBMYxnBCZaARuIc/M1yCMuvWbZkSa41sk2eHHJUnChpkUfvY7o9mCQFU0UBTJKCSRcwLeAeAiZZwVTmEEDqszRD7I3Evqe+SgSXWqzxxRdbbqPnnmAMORLGA6PJxlGYZRGDhTZxWGEXj7X2idh4MxFbHZKw7VYStrPcxr7exO5bxx4zvBqPJZfjMNsyBlNN7uLnsxEYdjQMvfcFo922ALRe54eGBt6oschdGBONZ5bYn4mghASYFrjJgOlVAEzSGvHw0kVYTzErkcXiYnc0XunF5sZP9c3u4KQRx+4ETjeJsTG0S9y12zFl1lGP9MEnvdM/O+6ZJtvilWO8iYBplA5gkqzdCI705cx5Jcvn3Fm0r3Ue/T8wx5TvbmDTLB+YH7wL/1vpSItVQqP8Dz2D/iXITY1UPansGH5Oabh4OBLrZ3pjYv/r+K6tBTrUFsfGnedhCPVionMb9xIBkwToRovHGvNACWbDQ7pvOTMeLhG06VzJCN/UNMWw963xz/eOOLgiCK52ychIUZfJ/JE1XYGmGLn3tDwMdL2cjPPb72C9aI03su1lDKhvgZ6VTfn5I7tBGmsPTuhvRf2P+lQ1w5DGVvi9/TUsG+2Go4bBuHkxATHBuVDmFP53wMT2TkayCnd8snHTJAFHV4Vg0RgXjPr8Mr6pa8LvPwJM/dg8EowpCfHK+zqSAdN/i/IFTCxXfyikYVsoDVqw470Dxdw6yCfINLMKFPNqQ0FF/R09stXnJzlrb+zYqA0yG6GJcvwwO8ahgaGh4b/+B5iDg2GVfD+TRgWeRl9pnQ+MUFsbGKpO/mKl3NYlRmnQvEgxv44AmEgdw/fXaSIomR70AZL7MZV9SsBGnGsDUblEAHBBHSEJLq3+uEC1o3es+vQEO5X18k1qh/2/qjzPd1PdNnmPrO6eZ99HRnrUSw9xbZfmYvpLhu2WjVmnplzO2fFtTP7qj4sVZIOnTz2XaE/Ug5J6dBk0fYwtngyYXpeQAZMcpRUyYJIBUwUIXfUS/fNFc5btWf7Ach7LA5yg5AnmhP5EBGDKy1rqZRZ9Y1n6srRhuZ/lQpZjWfZg+SHLxpxgJ0hgrvzUBXJUhHhc8V+Gji8/Hqdg0gVMZPOpC5ik97GXDcofp2DStcgbxgkWebKCqWwhgKhcIrA0w0m4neeK+ks9+T5KHXYEYtCRMPx+/i7mW8XxwGivcypOeqXD2D8TVsFZuByWDbvwbNjfycH1CCHp66vsPlv2GJs3XAzIxCmfdOx3TcGGG4lYaB3Hq52GHwtHl11B+GCdH9428EJVfXcBSjwCmFxkwPSqACZdpRntLR24xM11QfWFbmi00gufbfHHgEMh8X8aRd1cahN/bNvNlKWH3dJ/PuF5r88pr3sfs/3V8JhHWqlc8L4J+ZVDUlVVItJVshLqOeJNAkyP3icApvGcHd/DiB4fyFmiO2fMq4S+qnQO3d42wYjPbDBnmCP2LQ7A1bNxiPDNRk66tmys3SComPKzCxAVnIMb5vHYvyoQc0Y74oevrNG5gTE+5c7iC5Zk60Y2eT9SHyY9CS49BExloXrRtRiUwJxuLytSLvXgTHiFFUGSb2qaYPC7Vpjc7QY2TPGBxcEohHplQZlbWCZzR6qo3Ewtbz/ncz2NP96OOf6YN8QJP39uh4ENLdGr6kUeJFH25C6iD2fGq8F68N+bom81MwxrfAkTO9hj+Th3nFgTAifLJP411fmPB4s8RioBmB7/xPtQ5RciLU6JINcM2J6KxV62r2b/4Ijh/7uErrWN+X5QAmAyxw9sbUtaOo56hUHTvwGmLSN9I/f9GWh2aFrQ7INTgjrukwFT6QEmXaiwqq0AmOh2Bbt/6buCVd7cWsifVUWwsNOvB+WatvdVB76P0ZjPtdQ67Vmu8TUepg0y/yQ9xKTO084x0nZ3dYXH+SZapyNfFtitn6A2+Xu/8sAQH9XGL/PovBTz6gjWfPNqs2O/JZwrb+XXVkipH5CcZZRtHgKmFaKSTb8B8uezPTCvFqgPksKwbaFyxzcZqmNjPNVmcw6qr22erHI62lnldaFFasDp2s+771PDPVune1iOyrTdtiXr3Ay73D0DQ3PXfJanIBWbfl2o5tcUIBO/95uwcTUXxvoAPOpaKL6seXoyYEonwLS2J8I2DoX/5rHp3lt/s/KUAdMzBw+YeoqAqXe1EHYrAKYerypg6gXXKUNDHQkwTZMB08sMATBN5gFT4PJJfqELRj0dMFWAvSQDptcqJMBUkyVd+205AaL8ynIVy3MsXTmhT0gmJwCY1029pFv0JVUDFZ8JpoVygjXgaZZrWE5m+R0n9Kd6j2V9TgBz5VsAlqMsQ+8pWekZ80k/L0fphfRe9jjAtIWlJfeoRR4BpvJ4H3ucgqkkYNK1yKvKyQqmsgAjIgSYJVjSkcKk3lJPHvh03RWEESfu4B+zGKy/loSj7umwCsyGY2QefOOVCE1VIypDg9gsDeKzNUjI1iIhR4tElvQ13RfHHovO1OBOuhp+SQo4R+fBOiQLJ7zSselmEuZYxmLMqTvosTsYH2/wR6PlXqix0A2CVZ5kkyepmCowXJEBk07q9NKi8YrrV1XfDfUNPNB6gw96HwjKmGgc6bTueuLO457pU0z9s/qa3c7633mfzHdPeKbXO+qR9lwe/o8LNr/Vb0bmNHCLyWvim6BoFpSsbByWpmrA9mKtiHRV1Yh7KvkXln+JNwUwPS75/kWcHX4WQQmdJylHunLGvJKkUzUjfNvIHD+3s4PBOHecXBcKV5tkxIXm83ZpRWVhlcdeslBTjNQEBXwc02C0/w5WT/fE732vol9zM7SvegFfcuf48REcGcKvjQDMRvGgzLYEjCg9ICEBJgJL49i8jeXBx2W+FxSpqQjUEBwhm7duVYwxsLEFfv/6GgzHeeDM2nC4WqUgITwf2jJSgKkUhUiJVSLA+R5sT8XgwNJALBnlht87XMOwdy+hT3Uz9NATwBKNlSDOt5wFb0fXi31P2a+aOYY3scbkTtdh+DMb9/owuFqnIClSgQJV8ROWTARMOvnY5xUXQ5FdgMTIfHjbp8Js/11snumLad/dwPdtLNGpphGvTuvM9t+3PDy8LMI8uxKQqfyvndIETEt0ANNhGTCVEWBqJRboP3gU5JBKhKAPQYW5NaGYVQn5ZGNHipZN7fLUR0cGa8znm2qvbVyqcdw7WO1yqOUznKYeQaY8h0PvqG9u7621WbpIdX6ilXr/91HKdV8oSbVEQIuUTKRo4q3YeJs8UcH00nrsvKnZ+uEcL2/J9lsjfh3y59VE/oK6UBi0KFBs7pShPDwiUGU83Vh1eYW++saOfkqnQ82SrQ/VepqKrWTE+Ps3uOd/pU/m9f0rci7MvJqzd2hc3tovsvOXNCtS6NfnFVO8LR4pl5aRcqmFuF/b6OyH8rBOfEbAtGlMuvfWX2XA9BzxugCmBBEw+fKAaUio418yYHrZ8QAwGf69OdBgkl/o/FHFUZN6IGFEa6T1q4WM7jJgkgFTmQd9JlI9g/4Bhwqan7McyHI6yx0srVne5oS+ROVpK/Uyir50XtRbinpM3eOEwq8HS3OWO1nOYTmCZWeWbVi+wwkF4GqcDJhel3gSQKr8hKwiZtVnyColsjL37xBKjucLXVhO1+ZHnACYqAeTLmCi97J8rnz7yNFxH6dgki3yyhyGSH1xZgsQp/I8V96i7p0VXvh4ox/67Avm7fAWWMVhx60UGPtmwiEiD8GJKiRkFiAzvwhKbTEKiu6jqJjl/fsoLpF0Hz1WyFJdWIwsVSEPn0JSlXCKyuNVTXudU7DEJg4TzkbyPZq+3Hwb7xp6o84SD1Sd7wY93mLNWcg5LiKwEM+jIqmZZMCk08/roWpJb64rmwc3fm/VXuKhfWelZ87HW3xTvz8a7DbvUsyhIx5pk21Ds7vcuJPb1DYkp9p538xS+SXCIiizhlVwVjPrkMzP2Dx3uxqe0+vW3dxuHrF5X/glKloGJCneDkhW1GQpq5qeEG8yYKKC/ThexURFfMHmbRBnyQMHsngjlVCP6qYY8q4Vpva4gY1TfXgo4HMjHYl3FbwSp7gMWAkpYHII2Adk45pZHA6sCcSC8U4Y2e4yeja8iI7VjPB15Qu8CodUTIPZ+pDa5ScRLo3RydIGTGMezJkdf0v3kzUewRoCcwRIOuhdQK86FzH6o8vQH+qMQ4uCYH86HuHu2chIUD8R1PzXUOQWIDo0F45WiTizJQyrJ3pias8bGNHKBv3rmaNHpYuCSomtb3823u/4flGW/Nh1AdMPTa0xrfMNrPnVE+c3hcPDNhUpUUoUap4Ajp4RMBUXFSM3Q4uY4Bw4WyXhzOYwGP7pgd97XMO31GOrutCzivpB9ZcBkwyYShsw6cIF3aTjGDQTLNLmVkP+7CqCTdqKlkXK7d0yVMdH+6svzjitsV7+j8puU+cs+431fQ4deup/g5FdnsZl/8eqG1vHa6wNdqrPTb6l2tM/Xmn4oVaxoD4Us6pCMbua0I9p2bv/HyrI/ZhKd911k9acrAmXius+T1Av5S9qiPzVH+UqdvULVZ7+zVJpvmCtynbNqLyrW/9H0PB59npkpG31uMDAt9L9Hdrdczr9V5aFwbncgyPu5m/4ukix9N37pJpSENAixdwiHbhk2KocbfF0UwZMZRUyYJKjtEIGTDJgqgBBNQ0CJA1YtuIEeDKa5RKWx1neYhnOCcCFwMvrqF7ShUySsoB6TSWwDGB5leVRlstZTmDZh+UnnFAAJltB+p2fajUyFHj14nFASQJH9LdCNfG2uvh1NfHrGmLW1MlaOllbvNV9TPe5NcTXKQmgHgedOE7eW88SuoBJt5fc4xRMBJjKy+pT1yIvm2U0J/RgovdbUjBJgEnXIk8GTKUCAWa7CuOdKSiXCC41WOqBVut80HFnAIYdC8N0syisuZaAox5psAnOhlesApFpGmTkFUGjvQ+8YB1QU3gfmcpCXtXkE6+AXVg2TnmlY4N9ImaaxWDk8TvotjMQH6z1RcOlnqhB9nj/sPmd4chuHYUxE8SY7/4wy3tOZcAkJI1tpnj+lGytqrP1eYutY5OV3oVNV3knN1/r7f3pNj/rwcdDti66HDuNnfc3jnfzmpTmtWoRmFnNIiizmZF/Rpdjnmlj9rmm/LPPNXXBcc+0fy4GZIy7Gp5NsOljthbv3IrKfa7CyJsUbzJgGvVAjSMAJirc66pxCJhQr56+tc0wss1lzBrgiB1z/WF5OAp+julIiVNCrSobNY5aVYjUBCVuu93DpdNR2LnEHzOH38KIzy+jT2MzdKpthE6VjHnIRL2jBnFWvF2eBM3GiRZ2o0X7v59K5IsCprEPVF+Cgonmi2BNdzYOsnf7ijuHLjWNMbi5Fab1uIGtf/vh0oFoBN7MQNpdFZRZhSiiz5YyEH/lZWkR6pOJS6eisWOhH2YNc8ToT23R/21z9Kxqyo+R1nUAZ8GDxEFsXw/k+0YJgIke+7aaOUY0s8HfXW9i/e/eMN4SAW+7NKTFqlD8BMXaswKmQm0xMlPUCGdjvHo2lldYzf/JGaPa2aJHI1O0r3oe7bkLbN+Z8GMcwc+3DJhepyh/wNTqodWYrv3YypagXjgElvLnVoeCZT4bi5Ks0rZ1S1MdHeGsMf57h9Z2xVjt9a2f5rseaBzjcOKpa5Tnc/4dle/ZrgXOh6YW2K4+oD79m6tyS7d0HmzMZseZWYkdqwaUixoKkIls+0qqrModzrzqqbPePFBk9y17D0pab7JHpL5Y82sjn75e3vK+YnOHWMXBoZeV5yevVVnqj1XarO6Qd319w+fZ56RySnCzfi/T41LXTJfTk7Js1h3KOfm7Z96WbgoFHX9hAyjpuAvq8eo55VLqxaVji2dY0hZPBkyvU8iASY7SChkwyYCpnKNkQZYspaggS1Zwm1heZOnNMo4TgMvrql7STTo/KjxTr6k0lndYurA0EufkL5ZDWH7NklTx9H5J8EDuxVTx499gkq4iSYJIEiiqI2ZdTgCKlA3EfFvMhk9J6XlviT9XX3y9OtyjMEoXOj1O6SQrnJ4cJS3y/g0wlbdFHr3PlLTIkwFT2UIAt4cQ4B8B1tRb4oGPNviiz4Eg/Ho+Aktt43DALQXmgZlwjspDaIoKiVlaZCmKoC3478U+UjTlqIuQlKNFeJoK7jF5sArMwiHXNCy/nIDfz0ai394QfLrWD40WuqPqTDa/f98SkvpEzRYAk94CGTBVqKR1oT1F18Pfzqgy2w2NlnjhQ7aOX225fe+Lrbc9Ptvqf/TrXf76Q0+EDFtkG9uFnXdzp7t5/9kOTwrT2xlVLYOymrDbjgfdUicYXo3fMMsi+sx0s2izRTZxp7fdSlp/2jv9T7PAjN4WQZmtzQMznto34k2NNxswCYqcsSJgogI+3T+Ms+YL/KR26c6ZoEclUwyob4Gx/7PFvKFO2KV/GzanYxDinYmsdA2KikqflhQVFUORV4DE6HzeKs/s6F1smeuL6UMc8OPnNujRxBQdqpMdnRG6sXGSCofGPZoHQJLC6CGYoOL+CDGfFTCV7OP0EDAJr0+vS7CAwAypvah3Falw+jU1x69fX+V7GJ1dHw4P6xQkhuXzcKlQXYz7ZcPkcC9ZBW+HVJzeGYYVk9zxW49rGNjcEt/UMOVBYXd+nsx4GEd7eigPE3UBkxkGVLPAyHcvY0b3W9j0hw9Mt0XC91o60uPVbNz/bZ3JGjA1ToXbjukwJ3u86b6Y1u8GBn9ghc51jfi+X19zF/g9R/3AfnoCYCrv60YGTC8eFQIwPYAObXRADvve4D1eSZJPhf851XnLNMXid9jjH2pVO3pGak6Ms9Ra6Rtobm4bXuB87Kt8P5NGJiYm/6oOJhWLKtKheWGATc8CjxPTtdbLTqoP/RCoWvuJhlewUN8nSTHFjqUwaC6Mi/pE8b2iPignuPC6ZGv8P9Xa8pYCXCJ7OuqHReu9iM09e55i49e5yr3fuSpO/rw933jGGMXFBV8qLhs2DTExrPY8+zzOZsNbWdd2fJN1ZdP0LMsVh3NOT/HM2z0wWbH2UyiWNIFyQV0hqQcXG4sAF1uWGGt52yQ+DjC1fACYYtf2QOiGIfDbODrda/MvVp6bfpEB0zMGD5j6Vh6S2rvqrtS+1ULS+giAKb3nKwaY+jdC2IhP4TOhF5wnDw51nPqjDJhecvCAyUAHMM0bVRw1UQZMMmB6KSEV2Km+QYXud1m2Z/kDy3ksD3CCcieEZSonABeylHpd1Uu6xV86T6n4S3DNl6UNy/2cUAAewwl9qsiCq4k4f/R7hqxiqpihC2V0QZIEcgjqSCojKujTehIAIhhEVmsEK2idSbFG1wn132rBCYDxfZatOcEysWS21rltJT6Xfqa5+BrNxNel15fgky54ovFISidJSaVrzyfDpochvZ/RutIa0rrR77RSD6atLK1Y+nOP2n2WhyJTAky6FnmkYJJ6MBFg+oqTAVMpA5DZbgIE+MeZtzCrsdAdrdf6oO/+YEwxvYv1NxNwwf8eHKNzEZyi5HspZSkLeTs8bSE1KS+dgl9B8X3+NXNUhUjO1fIQyykyDxd8MrHhahImn4vCgF0h+HilDxrMc0Gl6Y5snm+Bm+4k9Iua5w49WcFU/jlXJ0XApDedrddMVzRc6InP1t0u7rcnJGv4kXD/wUfDTvc/HDLj28PBPUafDWu69Epcg1M+6aWmIDrlnV7d9HZGs4sBmR1OeKWNX30tYcPv5yMvDzwUEtxvf0jMyBPht+dYxphvdUgyPOKRNuqEV/oXRz3SGpTW8V+3eJMBE6WupdxoMQnCkO0bKXMInvTgTNGjsimvhBn7xRUs+MkZh1YF49alRMRF5PG9f8oiCFyR7VsCe8/0uJ6KC7vvYO10L0zqfx3ftbVER4ISnKB6oTGS8orOSbKwG/+gT9J/A0y6+RDIXeFfh2zmSEVFoKtD1Qvo+Y4pRn5+GfOHO2PfwgBcOxOPCJ9s5KRpeQUQ/9lSBuolraoYseG5uG4ej90rbmPWT7cw4ksb9Gpohi6VBSUa9V76jrPAcLafSe1FsGOQaO/XUwRM31WzwKj3bDGzuyO2TPSD2fa78L9+D/cS1Lx14QsHO29VbiESI/LhYZuCMxvDsOJnD/z6tR36NTHH19Uu4As96q1lxM/n9zxgsuGB3li+R9iVBz21yvuakQHTi0fFAUwifODVQh88tMpb1pSNoaHQk2duDd46jVc2rfvsnurAIG+tyYzT2msbFmmcjw7TeJt8nBpwuvZTTlmPh0x33N4rDLbpW+i0d4nGZIa1ane/JHb8YsX8ulDMrsqrmHi7NIINNA6CXjxgalvOkOFVT13AJM4jwRz9t4S1pb5bBHkM29xXbu2mVh4aFqo6/dtppck/Uwku3bNaWPd54BIpl0JMRlfLMpr1ec656ZNyTk86lnPsZ9+83QOz8zd8rVWwteWh5cL6gi0ewSYCmwS9HoxX6rlU3nP3IoBptAyYniFkwCRHaYUMmGTAVI4hFWTp91UqbFMh/BuWv7JcxfIcS1dOKH5mcgJweVMAk2RfRUXoZE6AbDdZnmK5muVElt9xgsqAQEMDTrbJq2jxOKXS44ASgRxSJOnCJCrsEwAiGERwqC0nwAqyRfyM5Rcs23GCiq0jy04su7Ds+pjsImYn8bn0M1+Jr0GvRapBApUfcAKAIvgkgScaD30e1+f+P3AqqXB602GTLjCnv+0kRaYuYCIFky5gIgVTeVl+Pq4Hk6RgIshfUsFUfvHKA6bZYm+cmQJcqsq+rrPQHe+t8kb33YH4wygSG28mwiTgHjzj8xGTpeat7NQFxXwfJXL24d19SrEASK9HvZrINi9LUYiYexp4RCtg5JOJtVeSMPHUXfTaGohWyzxRd44Lqs5wgh4BppnO4Oa6Qq+85/RNAkzz3XR6Xrny8/9IvyW+V5YrqrCsM9cdjRd7FX6+zj9v8P6wpEnno3znWsRemGUZs3iaWVS/iSaRjUvz2jzollr5mEdavTM+6S3P+93rdtIr/Rc23+ummUZZ9N0XHP7JBr/8j9f5FfbYFZT227kIlxVX4vfsdEqeuNclpdMup+Tnsnd5k+JNB0xS0V6CS1Lfoh85awzmLHnIREom6ovTtaoxBjSxwITO17BmqhcuHopEkHsGb3tWoClGcRkomeg1czO1iAzMwY2L8Ti8Jgj641zwU/vL6Pa2Cb7kzuML7hw6c0a8Emc4r2K6/EifpDEilHheizwCSqO5yw/mZrQImCQlDSmm+nEW6FbJBJ2rGaF7fVMM/fAS/up/E5tn+OLinkj4XU9HSrQSGkXZyJaK2OeKmn2GZSSp4e+cDpODEVj9tyf+6HMNA1tbolsdNjY9yUpQUC+NYOMmePPDYwGTJca8dwWzv3HEton+sNgRhdulAJjus3HmZxYgJigXThcTccQgGPrDnDHyo8voUe8ivqokrCOBOhqLDJhkwPRyAJOOHRl9v7wFFMve5aEDr2CaU50HP8oVLZWqbd1i1acmOGtslh0tuLVnZqGPSY/8APPGT1MxURBk0tx1a6v1NR5TcHX9LvXpCR7Kbd1SlQbNFYp5tYsVc6oJx9JvIAAQgiGrRPi1Utcqrbyhw6uSOrZ4un2XSCFGgGdebfBzPq8Wu+/dYuXmLlmqY6MiVCYzLdTWyxerbdf0yzN/Plu8ZGvDWvfM5jTLODH1fznHfh2Te2jE9ry9A13ztvXMVGz4GgrDtlCQNSIdn/Y42eLReGhcK1rh//WJKvc5lAFTWYUMmOQorZABkwyYyjGk//anojUVs6nYPZDl3yx3srzECcVYyU5Kssd7EwCTZJNHPaeo99Rdlh4szVjuYDmL5QhOAAcEBt7hHrXJe1OL/BUhntRLSYJKkkKJoCD9nkh7n1RJBJMIsn7ICSCJABAp+ggMdWPZkxN6bxGwILg4iOVQToABP7Kk952RLEeVyJHiY/Sc4eLP0M/StdZffM2e4jHoWASuPucEOEJgqxUnQCcJOBEIIyBWh3vUUk9SNZXs3fQmhQSYaG6ojisBpqnco4BJ1yKvvN7TJMBEPZh0FUwLuMcDpvKz33ylARMPPlwEMMOy0mxn1F/ohtarvdFtdyBvi7fmegJMAjJ4uJSYo4WioIiHPy8riouBfHUx4jIL4HZXgbOeGVhtnYhfjkWi2+YAtDLwRoP5bqg2SzgHghp6s8V+THMryBy/KYCJh0siWJLWg31faZ4r6i50R8vl3kXtNwVkDTsYdmemaYzDRvukYwddUvUPuqUO2eOS0qq0r82jnmkNTnimf3TCK73fIffUqWyut84yj7486FBo8Edr/XIaLvZAk6WeaL/JP2/MiXCfxdaxRzY7JE3f4ZjcfcvNpEalPZ7XJd50wCSBFAkyScX8kXwx/BK+5yx4FRMV/ttz59G1ujGGtrqE2UMdcXBFEG5ZJCI6OBe597S8iqa01J+6UagpRlqCiu/7ZHb4LjbM9MHEPvbo39wCHaoa8WCCrNUITFBvoR9Fqzy+F5OeoDZ6kb49utBtzAP49hAUkL1c70pm6F7dFD3fYsduY4U/e9lj1SRPnN0SDmerZMQG5yE/u6BM5oU+ukg9lpaoRKh3Jq6ci8Gepbcx64db+OlzUi9dROeqxjwc7CX2XqK9/JO4l398DGAaWM0SY9+7grnfOGHHpNuw2hmNgBsZyEjUvPg5sJ8rYmuYnaJFhHc27E/HYc/s25jZ9xaGvXcJXauZ8GtIsLAzP1Yzfh1pnIJizFYGTK9JVCzA1OrR3jxSv6PlLaBc3Ei0yqvG92Ni4ypWrPk4T7V3QKzm/JRbBXZrd2jdj4/VBtl8ci/cpS4pV5527llRPvULQq524a3ybJadUB8f56ba3DFWuaSZilfTkJKJoBb1Y6J+PHw/pjYlsiKAhwqchq3wSI8tHh5KcOldQY2mXw/KOUKfLVIRqdZ/rlAf+jFIY65vrnXYbaBxPzVI432ujYnJ6KeCQylo/TOs176XZ6z/Te7Jib/kHRy5JX9nv+uKjZ0SFWs+BfVdUixtKsAtSlKqGbwr7nFJtVSR4BLlMwCm9UPgt2F0utcmGTA9T7xOgCn0x0/h/WsvOE0aHOow9cc9N6YNlQHTSwwZMMmAqZxCsgojhS+pI0iFQ8VtKogv5oT/pHfghP5D6ZwAWt4E9ZIuZJJs8qgAnMAygKUdy8Msl3GC0qsvJ8AIUpxQ0b86J6uYyit0oZIuWKK/xySoJKmUJIVSK05QDxFcJZjUmRNUfH04ASJRry0q9o9mOY4T1vxPlpNYTmM5neVMlrNZzuUEa8kFJXK+eP8cTgCT08WfnSK+1gSW48Vj/Cgec4A4hu7cQ+hE+4yA0/ucAMQIoEjqJjo/CTaV7Nv0Jqma6Dzp3AkwEZCjOSOIJwEmssi7zVUMaC6pJEnBRAD7cRZ59L4iW+T9N/jhKiqXqH+RE2rru6LVKi/03BOACecjsMo+Aef978E9jpRLGuRri8rCqejptbZiIFdVjLtpWty6k49TbhkwsErEWIJMW4PQeoUP6i9wQ2UebNCci3Z5FcE27o0ATHRsAno05wT5HmZl9ljdJe5oscq7sOPWgIwfjoQHz7wYY7vtRvIuI9+M6Xah2f2vR+S0tY/IeZptznPFfrfU+kc80v532D1t8B7nlFlr7BP3zzSPuT78aFj0Fxv9s99a6FFUfbYr3tZ3R7sNfhljjoe7L7aOPSwDpqeHDJgeQqbROvZvglWeDW+VRwCCCv98jyHOCH3fNsfvXeyxdrIXTPdEwts+DQnsvSwvU4tCbem/q1LPotwMLSL8s3H9YjwOGQZhwUhnjPrUFr0bmKFDpQtsXELvnm85M155NUKEE+P0bB+omJ4HUEjzoWuJN1anRxX1COqrZ46eVS/yYxjSxgq/db+Gpb+64ejaEFw3TUCYdxayUjS8uqssorCgGBkpKoT6ZsLeNB5H1gRh6S+u+KWTHQa+a4nuNR6ql0jdRTCJVEsj+b1MCqZLPMghZRMBpj7sOd9Xt8L45naY38MZuyffhvWuaATezERm0gsCpvuCekmTX4T0WDWCHTNgczAG2yb7YVqXGxjU0AqdKxnzgInsDruyNezDr6HVA8D0UDV2+YVAYUVJGTBVQMDEQwkR3vCKIREyseOTikmwUavBW+YplzQpUm38SqE+OOyuxmSmRaHDzkWa2xbfaSJdP3gWyOTj41NVHe36fmGQ1QCN86H5WsuFx1WHfnBTrPs8VbmkkWDXJiqmFPT9MhFA6I7NsCJYp1Xg1IVLuvNl8J4Al2hN59eGcl5NKBc2gIrNq2rvt/Eak3+stLf2LdcEWg5Whzu2Tg9xeK6+lekO++oo7TZ/nWeyYFLuiT935u8ffjN/a/d4xer/qaWeT0oCh5R8z6VmAsjkxy1Z4r0GgGmNDJieJV43wOT1a084yoCpXEIGTDJgKqeQ1EtUlKaCOxXZCZZQ4XwDS1OWXixjWeZwb456qWQBmM6bCtHUgyqcE2ysLrDcyPIvToABZHlGRX9636zFlXcx+M2Kp6mV6HdBAjCkVCKoRCCVVEr0uw4plMiyjoBSP05QFRHgof5aBJLoWiA1H8EjAkUEXpdzgn3kWk64Traw3MYJqrZdLPey3CfmfvGW7tsjPk7PI9CxieV6TrBbXMlyKcuFnACpZnACfPqN5VhOUMoNFsf4jTjmL8RzaMUJoEyCTQTRqIYp2ehJypc3BTTpWuQ9CTBVBFXm43ow0XuLBJgIauoCJkkZWT7xSgKmR3rjEPRwRKW5zmhk4I4O2/ww/kwYVl6NwxnfdDjH5OJupoa3xSv8L/0k/mNQn6d7eYUISdbgemgeDrtkQN8yEaOORqLDlkA0M/BCtXmkxnIEN8NRVM/IgOnlpKuOesmZh0yV57qg2gJXNFjmjpZrvAvabbudPuhwWMBU42jLNVcTt57yujfFPjynt2+84v2QFFWpwaXtjslV97ik1D/glvq//a6pg7bfSp5raJdwcLpZtMOPx8NjO2wJKGi61PN+1ZnUv8sZDRe4F3Tc6B//88k7DgaX4/Ztu5U8bbdzSjf2czJgekLIgOnxgEmylSMVE/XtIXhDKiECTD1qX8TIj20xf5gzDiwOhN3pOAS7ZSA9XgW1svSt4AjKUy+m+Dt58LyWCpPdEdgwxRtTvrmBYS2s0aOmKTrpGfFKHbLz68+ZsXWz4sc/RgRMY3VsAJ8FUugCJl4JJb4G9S4iuERqHwI339S8iAHvWmB8xyuYP9KZVxDZnI5BgGsGkqOVULH3+f/Uu+hfguY6PjIPLnZJOL09DKumeGByn+sY2voSete7yFv3Ue+lvqIiaPiDfWzDwxtBofYoYBpc/RJ+aX4V+r1csHdqAC7viUGQw38DTEXa+1BmFyL5jgL+V9Ngvv0uNv7qjclfXcfAepY8vPxS7KUljNf8AWAaLQOm1yoqJmASocQqCUqIVnlL2Hj0BSDBw58F9fheOarNXbLUx8Z4FtgsP0RqpMKwa71ViR7NCSA95fT1smMcGmgj7D/R+BoN1dpvXay5MM1UtfvbcOXqDzWKRW8LMItSv55gpUYWajwsafuwV1S5g4cKnI8AJskarwVvR6dY2IAHhYr5taDUr3+f7a8C9bbueerTEzw1Vzds1/qZjCJYGBIS8sw9lyjIIlHhcKJpru3WQXmm+utyj0+wz981IDF/Q/sCUi7xVnjUb4lycSNhb0vWeI/0XJIB05sSMmCSo7RCBkwyYCqnoGIlfVZSQZrUEKTeGMYJBe4DLK+yDGaZwlLBCVZSbxJckorAdN4qTuhBFcPShxOsAwkcUCGYYAQV/QnQUUGbgIasYno5IQETCSzRfi6pViLwQgCG+iiRXRoV7UmlRJZ0pBKiPU/KIYI5BCFIYUTrasByDcvNLLdzAiA6yPIoJ/ThOssJoNGE5UWW5pxgv0Z7w1pMGzGtxfutxOfR841Znmd5muUJlkc44brbIx6PAKYhJ0AtuiZJ9UR9v0jpRPCB7PV6iedCVmq0/whyEpAgYEz2fyUt9CTY9DqDJknBRHuA1v5xgMmPexQw3efKBzARwCaFpKRgkgCTZJFHe/VdTlYwvSDwmOMmAIlZQt+lyrOdUGeRKz5c743BR4KxyCYaJ71T4RSdi6hMNbJURXw/pPIM3tpIex+puQJksgtRYK9TBuaYJeD7g3fw0To/1FlIIIcA0y1RleUigI/ynu/nBEy2YVlV7MKzGlqHZrY/55f+8yaHxG2TKxpg4s9LBEtzRVs8ES5VmefCxuiGpis88PFGH03X3QFpg46E+E04H2mifylu1fZbKRNM/DN7OEflvR+Woiq1ouB2p6Rqe11Smux3Tflit0vK8E03k/QXX447Nsk46taQI2HRHbYFqJsv90ZNmqupbJ9Mc8Q7C9xVXTb53/3t9J1rK6/E79rplDJln2tqF3b7TmmN63ULGTA9HjBJQEayUSOLNQIBnTgjdKtqiu+bWuHPzvZYNcEDpzeEwdkqCTEhucjLKij1Xkz0fqll79v3ElQI9cyC/fl4vofPkp/c8Fv7a/i+sSW+qWmKLpWM0Y23WDPloRipdUbpXebPZZwOOHsWSCH1XtIFTGP4vkuXeCBDMItsA7vXM8Wwj60xfbADNs/2xcWDkfC5mYbEKAXy2VwUldFnDc1JbpYWIT6ZsDoZhc1zffD3oJv48X826PPWRXSvKsAlAkffiXDppwd72IZfV4JwA0XAROtL/aSG1rDGhJbXsLiPKw78FYQr+2IR4piFrOQXA0z0M4XqYuSlaREXkAcPixQYrY3A6pGe+ON/1zCgpgXbU8b4SoKXvNrKgocwMmB6/aLiAyap71ErKB6oXhpAMbcWFHNq8AoY1coPClU7e8Wpz0++UWC/cX+Br/GUgiiXjpmRHvWedv4EofLuOLyjvX3pM6374TEaG4Pt6lO/Oit39EhXGrbRKBfUu8+rmOYJkImHEzRGHjC1FSzfKhSEqEjZ+lErQbLLW9FSsMYjeMfDpdpsXutDZdBCo9zSKU1zbEyo1nrJBY3byRkF4dc6pgYEPNc/CPn4HKqa7W/RIN/19Od5tpsnKs79fTpv//BwxcaOhYqVbdhebgQl29NKtm+EvktNRfvDf4NLFWVtZcBUViEDJjlKK2TAJAOmcgipKE+/p1IRnhQdBElItUHqjHMsXTnhv+oJrBBgoWJoeQOf8kjJxiqXE4rSBN1ucAJkoLmioj+BClKUUJ+cBuK8yiqmsgtJsSRZwen2VpLUSgRaqKcS9VOitSGbOYJKBGaoeE92d7R2pBaigj4pk0hRRHCH4CEBnzOcAIIIChEgsmV5jeVNlrdYOnPCdeLO0pOlNycASF8x/XTSV3yMVIEe4s85i69D+8me5RVOgFHm4nFPi+Mg6ERwhIDXEk5QVBEw+YUTejt9L54bKZvI6o9s9EipRcCTPsvrcQ9VTSVB0+sWun3ldAETWRKS0owgIK1HIveogqk84LUEmOg9NpJ71CJPFzARKKR1kwHTs8MlHShBKo5ZLqi9wBXNDT3RY+9tTDGNwD7XJNyIyEZkhgo56kJoi+6XizVeyaD/yifIlJZXhMBELawC87H1Zjr+OB+DLjuD0Hi5JyrPExRZPGCSbPLKEzI9D2CK/hfAZHL3Zs99wamt1viKgMmtHAGTpFjS7bnkwn9dhT1Wb7E7mq/ywpdb/Qq+PRiYOupUmO8fRhFGM81jDJbZJozYcSulnbFfZnOnqLxapXkt7nROarTPNaXDbueUURtuJC7Tt449PeFcpFv/g6FxX26+nf/eSm/Unu8OPbo2JzmAm3qLAJOy2+bbEX+ejbiy+mr8tj3OKRMPuqd22uOS8lzNqt+kkAHTo5BpjA5gosI+FflpDvpz5nzxnyzMKHvXNsOINjaY8a0Dts70g+XhKAS43ON7JWnVZaBiKryP/MwCxIfnw+daGiz2RWHHTH/MH+yM8Z9dwXeNLXglUzfeEk5Q7ZAK5pF+TDr2f1LB/6cS5y+lbv8l6efofrLfo9cnu8Cv9M6hZ+OLGNf1CpZPdMeprWFwuZyEmFABtBVqy8Yaj0KrLkZKnAKuV5NxfFMI9Mc7Y8zXtujbxAxdqgl9l0hhRWogHtawvTxa77LYQ8qGBx00PwTiyJKOFFkEdn6oZYM/29jDoL87Ds8MxrVDcQhzzkJOihYv0q6QYCPZ42UlqBHpkQ3Hs4k4tTQMBoPd8UsbO3xb1ZwHTKRekvovUa+ooTxgergOo3XWpryvExkwvXhUSMAkpS5gIkjB9+15T+iZM7+uAJjm1WbfN4Zi7Sd56v3fR2tM/nEsuLlre1GA9Sh1tN/7zzIHISEm1fJ8rN8p9DrTXXNjyxyt2dwLmqM/BSk3dUxXLntXy9vyUe8nuqW5IEjyYFwfPARiFQZElHfqgBndPlVs3nhIuFSEhCJcUi5tel+1sd09zeEf/DXmcy21TrtXaW5fGqqOcmn5PHuZlEvZ/g4N8m5f/kjhfOJ7paXhCsXRX67mb+mWxvdcWvg22zd1oCRQSOqlpY2E/UTrKY31EcBU3vNYMp8PMLlv+uUvFxkwPVM8BExVdqX2rRqS1qeKCJj0ZMAkx3OFDJhkwFQOUdJGiorSVKQmlQTZeFGRm/qUUBGWwEp5FWErQkoqJlJx3eMEpQEBBTNOgBGkeCFbNVKSEKijfwiuxZW3pdXrGSUVS7o2eAT2yO1HV61EqjzqYfQtJyiVJKhEPZMWcQIgJIUSWdiRMonAKqmLaP+Tgs+BpQsnACGCQ2StFsgyhGUYJ/QnIzBAeyKaExRusSzjnpCx4nOixJ+L4ATbxVBOAJfU44vgB0EoN06AT1fF8ZBlJammCDjt5gR7PoJi1NuJ4AnBJtqHBFO6iedOc9CKEyAF7UupV5OkaHrd1EwSeJTe2x6nYHoSYCpPBVMGJ+yHW5ywD0ta5NH+lqBg+cQrB5h4WzwXIdnYqrP7mxp44uut/hh7Jhyr7eNgGZyB4BQFMpUFKCwuu4Lf4+K+Tj72cVIyFdxHcnYxvGI1OO+TgyWXkzDkaDjabvBF7cVuQh8g6sU0y1mAHzxkkgFTqQOm2aIKjk9XVGGP1WVja7HaG+223dZ8fyQ45bcLd7z/sYgymncpesVC69gfDWwTPt5yM7neGe971a9H5JbKG+wsi6hKq+3j397umNR+u2PyuHXXEw3nX4q58MvZCO/e+4JT/rfRX9PIwOt+TX13VKLrkdRLEx14BVPjhR75PbYFhE8+H2mzzj5h037X1N+OeKR12O+WKv+x94SQAdOjgEWCKlLSfT+wcyeLNerj05u7iO6cKbpXNsG3Dc0x9ssrWDjaBUfXBsPJOgkxYXnIzyl9FRO9iWoURchIVCPSNwfO5kk4v/kONk/zxcwBtzDmE1sMeMccPaqb8iomwSrPXLTKs+EB0XjOjodFzwOYdOeDwMx3HAGRC/iUO4PPK51F35ZmmDzoOnYu84edURzCfbOQmaouU7hEPalyMrS4458FmzPR2DLPF5P7X8f3bSzRtbYxOupdECAgWytSKPGQTc+Wtwukc/tRhIa0pv1FwET5nZ4lfqp7GVM+uoFVgz1xfF4obhxLwB23bOSmvRhgKmKfb6qcQqRFKRHikMkDq8Ozg7GwnwvGtbiCvpWF/l6kXhL6L5nztn0EYmTA9PpFhQZMD6zVJJjTWhgDjWXh2zxc4nN+PSiWNStWbmyvUh3+IUljoX+50O3oksLwm99kx/g3wFN6MVGEmJhU03ic+1DrtGek1tZwnebCZGv1ngEhytUf5ij1STFVjWV1HozwUIIfX5tHs0JCifJICTDpzIukXCIFGqmXyHKQ4BJbS9XaT5Wafd+Fay78ZaW9vmW91ufCzwUh9u1z4pzfep69nODmVjMn3LF1vq95v/zru2bkG806otzznbfCsC2/hso51aFka6hcyI67hOBSM2Fchq1KrGFFXUcZMJVVyIBJjtIKGTDJgOklh1SgpyIzFZzpHzNI3UE2YdQH5iQn/Cc9Fb8JqChZFnJvnj3e4wrB2SzjOQG+2XFCsX8ZJxT3+3BCMZsKwvU42SavtEO3zxJZ4emCJQIJpB77gBNgKSl5yD6OoOlIlr9zAjylHkcElUjJQnZ0JzhBKUTqJAI5tzgB7BBMIthD4IeuAwJCBIZo7QlMJHNCT640lumccJ1kiElqlCwxs0tklvh4hvgz6eJr0GuRFWWSeAw6FgEHglhBnABECHLRdXlNHC+N+yQnwDHq50SwaQ4n9I2ivk3UG6w391DVRPBTAk20PwmCSj2aKnOvBwx9HsBUUXowlQRMj+vBJCmYZMD0rzlfTB50sPFMdxaSja3eQg/8b70fhhwOhb51LE54p8EjNhdJORqoC0r/v+qfJZ4Gmag9R54auJteiOt38rHTKQ1/Gkeh865ANDX0QnV9V1QiuzYCTHS+BELmvHKA6W3r0Mx25/zSx29ySNxaoQCTpF7SOSf6upa+B95b6YuvtwUoBh0JTfjDKMJ93qXos8uuxC5nOWbJ5bgvl12Or1ua199vFyJqzb8U3XS1fXyH9TcSxq2wi189yyLaeOzpO9599ganfLzer6Ah9eea7y7ARtr3BJgmO4Cu0SaLPfJ67ggIm2oUabXhesL6g26pvxzzTGt/0D31uQonb1LIgOn/AyZdsDJKLIz/oKN46Sna5XWtaYwBLSwwsd91bJrrA+uz0QjxziwzwFKouc/bzqUQrHDLxPUL8Ti1PhRr/vTEtD438GNba/R9ywzdqhjzSiYBsFjwgIUA08+cHcY/J2AaJd6OFOFAX/aaX3Hn8BF3Cp/pncF3H1pg7jgnnNkVBl/HNKTEKqBSFJb6uT8IEbQlRubD/WoKTm0NxdIJrhjb0RZ9mpihY1UjdOQu8Oql/qJ6icY+Vs+WTwkYDmb3D+ShoQCYSPH1fWVLjH7LFn9/dhPrfvTC6cVhcDydiLueOchLfzHAVKhla5ZRgKRQBfxt03FpRzT2TA3AnB5OGNWMjbmSGb+XOnNG/JhpPGTJ+IMMmGTAVG6Aqc2jaqHlLaCU+jEtqCtAJgIIK1pCtbVzgebkz8Fau9XHCnyN/iyIcGiniPZokpDgVvNpc5Hverpx4a293QqurftDYzJzm/rQcHvlhi+TeIXUvJoCYNKvy+aiiTCGlTpg4oFVXnlDiIqQjwFMZEPH2xu+JcAlUjCx/aVa84lWtbN3qubUr44F1st2Fbge/qMw0Lyb6q5ji2Qfn+dSoVM/LWXwlU5KlyOTlBZLdysOj7FTrm8fqVzURKGcWwPK2VWgZOuoXPy2uJ+lNWwtA6Y3PGTAJEdphQyYZMD0kkPqUUK/41Cxmd7z+3FCYZoK1WTPRXZeVOjO4YQCLAGWNxkwFYvzQAVpggGkOqF+KdSDh3rl/MUJBf2vOaEPztvi/Jav6uD1CQmKUpGd/rbSVSxJYOlzTgClfThhLQiy0J6m/kUEX2hvk/XdSU7om0S9ka5zgkKJrO0IKBHQoUI/AZ4ETgBJBIAIBhEYIkhE1wSp+vLFJGWbUidVYqr/JVXicxViSq+VKx4jUzwm7TUCIaR+IshF+46UTgRICITdFM+Dzuc4Jyib1nGCOouA2gROABV0fZPCThc0kTMS1UBpnxKwe11s80r2YCIVl2SRR4DJgvv/gKk83t90AZNkkXeLe1TB1I6TLfJeADDR1zQeGhtLvdmuaLbcG712B+Nvk2jsc0nFjYhcxGSqodAU4cmIp+zj3wATRVExkKEoRkCSGsa3s7DsSjyGHw/HZ1v80XCZB6rPc4UewaWZAkh76T2KnhUwOTweMF0RAJOkYKrAgInUcK6oMtcdTQ180G5zoGLokfCoScZRjgttYo+uuha/YI19/LAVdnFfLbkcV6p9jcacCq8yyTjyfX3rmJ4rrsb9scgmdiObJ4vhx8Jud9kZmPLhGl9tw6UeqEZ7X+w3xgOmaY7gptxiY3dCk6Weeb12BYZMM75rsfFG4tpD7mnjj3ulf3XYI00GTE8IGTD9f8j0KGh6eB/NgdSDiBQnX1Y6h071jTG8vTX0Jzjj1K4wuNunIOFuPhS5haXfi4m9TxaoiwXIFK1EoEsGrp2Pw5FVwTD4xQ2/d7uGwa2s8E0dE3SubITunAn6sbGSionOZTwPmOx4cFYSMD0JLknPE6CMFa+M+pw7iw+5U/iq2jn8yM591QwPXDGJRVxEHjvvAhQXl91nDYG7TPY5EehyD5eOR2HrPF/8NfAmhrS1Qve6JmxdLqALWxuyvBvEWwTaCDZ/elf4lEDZ9+wxsqLrx5nzgInmaUg1K4xvcgWzvr6FLWN9cGHlHbgYJSHGNxf5GdoX+ggt0NxHbqoWMf558LiYApO1kdj8qy+md3TAD41s0EvvIm/n15UTgCD1ixoqjnvkI2shA6bXISo0YJJghQRwHvRjai1a5YnAggAT9WQidRF7rmp33wzN+SnOBfabdhR4n5tQEHCpqzL82ruGT1EyxTicqKF2OdRSZb+pa4HZvD/Ux8ccVG/rGqhc/v59/ji8pVsdKJfQfDQVIZPO+HhAUd4QorxTBy5JKanOSLlEQJClknohrf6wQLW95z3NsbEBWvN5ZzTXt8wq9DzTUxVk2SI9xKHO09arZKhDXd9Xep7/UWW9cpPi2Hh7xZauYQqD5hnK+XUKeeUSJQHCpY0F4LXy/Yf2hq+EzaEMmMoqZMAkR2mFDJhkwPSSQ+pRQkVLKl5SEXM4J1htHeKEXjBUaCd1BRW/32T1km4hmOaBwAAVg2M5QeVCShJSkFBBeAwn9LH6iBMK2zS/sorpxUOybiupWiL1DdXvyAqPYAlBE4InfVgOZfkzJ6hVqK/SapY7OKFoTzCQ1ougEvU/IshAsIYUShJQIhUR7XsJJhHw0QVIEjiinlxanSQLxUKd26ISt4U63xfpPLegxNda7lEApQudSOWSJo6R4C8BJ7pOybaPYNMN8fzOc8J1vIUTwBpZOP7BCfZ5ZBVIEO5TTrDOa8oJPdhor9YQ51jar6/qnqVx6yqYCDDReU/hHgImAuiSRR7Ne3kBJqm/mwSYHLhHFUy6gEm2yHs2wEQAwlUALn878rCj5gJ3fLLeH2NPRmCDfTKsg3IQkqJGtrLouQt+9Gz6EaqPFrIvtIX3oWZJdnaqguKHWVgMNbvVsCcWFBXzzy2+f1/8T+/nOya9XlyWFrfu5mG/WypmmEWj/8FQtF3ri/qL3FFptggV/hGt8iooYLIUARNLHjDZhGZVvRyW1dAqJLPDGd/0XzfcTNw+0TjSocfeoLT3V/ugNg+YXF8iYHItkeJ9fE8vN1Sf74FGy3zwxcbA/MEHwyOnGUXbL7WJP7D+euLMjTcTBqyxj2+7zDb27YU2sVVL89obczr8PTYvfeZYRf8971LM7olGd68MPBwS+uWW25nNVnpr6i/0QLV5opXfTMESkgdidG0SZGLXQpNlXrm9dgUFTzO+a77pRuKaw+5p4054pX95xD2tQWmO9XUKGTD9G2R6CFx0ezIRmOjIGQk2cdXOofcHZpg42B7blvrB+mwMgjwy+F5MqvyygUwEWRQ5hUiKysdt53RcOhmN3UtuY95PThjX4Qr6NTVDlxpGPLggIEQqJhq31IdJUmbpnu9o7lH1lgSXRrAcxlljENsDdN4ErUjBRNmrsSkmDbDHvlUB8HJIRW6mBkWFZfiPDOyDJTdDg0j/bFw3isNhwyAsGuuCnzvYoX9Tc3SrYcKrgahXFo2Vxk3nNlan/xRBjqEP1EvmPCwkGNVPzxzDal3ChBZXMb+bE3b+7o+L6yPhYZ6CuIA8Huq9CGDSqoqRlaRBhEc2bp1OxKklYVj9kycmfX4dQ96+hB4iYJJg4CDeHu/h9faqQyUZMD0aFR8wtdJRmJTox7TsPcFybUE9KObWhGJ+LfZ9I6jWf1agOjA4TmP8t32B3dodBU77/ijwONnhnsuxf1U4E9BIvbqltsJqXROV2cKumtMT52v2Dbqs3Ngxgz/m4kZQLCT1TX02Lw2hWEqQqaUAUR4ApooOKco6dfovrRAtDQnEsb2kJAC4QOx/tLxVgXJLp3uaIyMDNaYzLbV2q1dpHPcP13ifa5PsY12L+ik9zz4mOz1VoHU3lf3WucpTv5kpt3SJVixvka1cUFejnFvzvpKglr5ojbf8PWFchuJ4DXXGXO7z928pA6ayioeAqequ1L7VQtL6VBUBU6VXEzD9IgKmKT/uuTFJBkwvM2TAJAOmlxhSwZ7ABxWWqUBPUORXTijGUxGerLio4E5FbSp2v6m9lx5XDKb5oII/KVsITlBR/6Q4d9TbZwDLLzkBfpD9oKRielWL9eUV0j6ludNVLdHnEkGRVpxgfUb2b324h2CJVCpkg7eWE9Q8JzihpxLZGZLijJRKZDlHUCmWE1QsBG2owE/KJAIOBJQI8GjE1AVBJUFRcYmv7z8hn/RY8WNSF0BJAEuCTgpxjDRWAk6kcCIwRj2gqC8UQU9nllc4oWcTqZqoT9hKlrM5wSqQwEVfce7o9z2yyCQQQ3VGXdu8V1XNVLK/nGSRR4CJoJsEmGjepP5y5aXQ1FUw0Z68xcmA6b9CJhEOzHKG3gwnVJ7tgreXeaHbziD8czEGxz3uwTNGieScQh4OvUhhrKhYgEp56iLcUxQiKbcAcdlaRGdqHmRslgYJ2Rqk5BfwPZ7yNUXseMUi0Hq+gxKcymDHCUpRwjI4CxtuJOG3c5HotD0AjZd5ChBmhqhamVWxAdOtu7nvOtwVAJNlUGY1q+DMJmaBGV1PeKVNXHM9Yc9vRhHO3fYEpTdf5YNauoBp9ksATHNdhJwjpbCXKrPzqLPYq/i9lX6KrzYHpg0+eCdoyvkYWwPrxN2b7JNnbnNIHrDJIbGN4bW4GotsYkrlTfOYS3pNfcvYhj+fudN61Mmwfr+cu/P3JJPIfb8bRV4ffCQ08out/rmNlnsVV5nvDr1Zro/aJPKgyVXYD3R9svubGHjl9tr9ADCtPuyeNlYGTP8eMmB6Omgaw6t/rvBJX5OSh/rlkJLnk0pn0bmZMUZ0tcGiP1xwdEMIblokIOJ2NrLSNCjQlE0vIgI5uZlaxN7JhdvVZJzfcwdrp3th6oAbGExqnjrGPAQjZQyBC4IWAih7CJhG6ZynBJikfkujeZj2UO3TlzPnYVUXPWN0qm6E3m9fxJj2tlgx0Q0Xj0QiIjCbnWvZ2bASqNMoC5F4Nx8edsk4ty0cayez8+1zAz98YI0+b5nhm2qmvM0cnS+t0QhJvfQArF3hgRkBDlIKSeolAkzf6pnjh3rW+KPNNSzq7YK9U27Dcutd+FinIiEkH4rsFwNMGmUxMuLVCHHKwrUjcTg0JxhLB7thwsdXMbC+Fb7RM+XXSIBiZOkn2ePJgKm83xvLIl4JwCSBi8f0Y1IYvCfAnvl1oJhXi7dfI6Ch2tRBqT40LEpjNM1Oa7N0rebmtuGkTgoxMaz2NGUMPa6yXvae1mzBCM3ZibtVB4f7Kbd2y1KuaKVir39fMa+GoJjSf4vNy7vi2NrqQKY3VckkKZdEWEPwbdl7UBKIoz1EgImHS82h2vBlnnr/wHDNucnWWmuDzQU3t/1W4HykQ47z/udSdxOIyvZ3aKDwv9xO7Xjod6XprL3K3X28lStaKJXzat9Xzq0G5YI67PjvCOOQlEsrXwXFUsmUAVNZhQyY5CitkAGTDJheYkj2UVRIpuIrKRkGspzBCQV5W5aBnABQSD1BRe43Wb1UEjDRfFCRn+zLqKjvztKME1QypBQhlQipaVpzgsqGitxS75RXsVhfHqFrh0ewg+aQYJ1kh0cKMSq892Q5mOU4TgBLVJQnsLSH5WlOsHqkfkWkViKVD9nLRXOCckUXKtE+1wVKuhDpcQDoSRDpRffV08CTrhpKgk4accz53EPYRMomstIjUEE9wkjVRGpE2p8E2miPrmA5kxOs84ZxQp+q9iw/5AQoSrZ5Un+mqtzD3kyv0t4tqWCqqIBJF1rrWuSV7MEkW+Q9F+CY58Jbm+nNdkHVOc6ou8gdbdb5YejRMKy6mohLQdm4k6ZBnvrF4BKFurAYmcoiXlUUnKyCR2w+HCJzcTU8B3Zh2fzt9YgcOEXlwjtBgbA0JQ+bslUF0BQW4fkbVtyHsqAISblaeMXn45zvPSy1icOgQ6F4f5UPKtF5TxfsAMttHZ4AmD7e4B87/myE+RaHpIUWwZl9bt7Nacbmhi+qmNzOqGESkNH8gv+9Poc8UqevuBp/ePy5Ox6ddgVkNDP0Ro2F7tCb4/oQmswW1USlNeb5uuMneOUs5GyCMixnO6PSAjfUX+aFD9b55/TcHRI2+mSkw8yLcacMLyet2Xo9deJOh5T+228lt914M7F2aV1r7hHKamc9MlovtY7r/fOZiJ+HHQtdOuRY6BGWDgMOhUS12xaQ35TNT1V9dwEqzRDVa7NEKDZXnKsZjwVMFrKC6dlCBkzPCpgEezkCNFQk783b5F3AF9w5tK9/Hn3bmuG3PlexcpIHzmwPg+uVZMEyLqeAvRWWjaqnQFuErHQ1wvyzcM00DgdXB2HheBce/BAAIsDUiSWBIVLG0BpK5zP6MTlGVPmMFfs00fOH8JaA5jxQo9fqXM0Y/ZqZ4eevr2Dxz644uTkUHvYpSEtUlsk5UhQVsc+G/ELcY8cIcL0Hq2NR2DbXD7MHO2LMZ7b4rpEFetW8iJ6VL/LAiNRJP/DqpYdwSTqnH8X+S/353kvm/Dr2Ytm/sgVGvGWDSR9fx7IBbjj4TyBs9kTD3y4dyeEKKHMLX+izVK0oRlqMCgE3MmDNXm/XXwGY/60zxra+gv51LNBdzxTd2NwK/bIs+b2le63JgOn1ilcLMOn2ZBJAhmJFS15JxPf0WVBbsLEjiMGeq97aOV9zaGio9sLUcxrb5f8UOO/sovA60ZQUMk+3yzOsUeCwo12B3fopWvP5x1THxripNraPUSxqqMqfySF/hh7y59SEctE7ohqmLRuTBJlEAFbuQOJlr03rh4BtRSsBLvGqr7cF+0K2j1QE/9Z9Vqza1S9RfWLc9QKzuVsLrqz9vfDmnm9UDkea+xw69FxK9GyHEw2UToe+Vthv+VNxce4uxYFh15RrP05ULqwn9FwiwETHpv3Lq81aiWvTRgZMcjwIGTDJUVohAyYZML3EoN9jyAaLisgtOMEuazTLpSxPcYLKg8AJFaypgP2m2+PpFoMlmzwqCJO6iwrUVMgndcwRlss4QQnWmxNsuUhpQ2CkOif3YXrWkOzw6Pc6Un9JqqVmnADtqM9SV5bfccK+pR5L81mu4QRASnuYAALZ4BH8o/W5wwnghQAM7WsJKpEFHa0lAYaSqiRpz/8XeFSae68keNK12qPx07VKyqYsTrD4I4hG1zHBYg9xPgg0kaKJbOIMOAEqj2f5PctunGA1SHMs2eZRvbQ69xA0vSqQqaSCiSA6KQt1ezBVVMDkwAmAiVR4koKJ9r4EmGQF05MBh6huEdUnldn3dRa6ofkqb3TZHYiJJnexzzUVTlF5SMwpgPYFe62T6olUS5H3NDxYsgnOxmnve9jvkoqtDsnYfDOJv93llILD7qkwup2Bq3ey4BOfh+hMFTKVWgEyPWdFjlRT+VqCWho43s3FXucUTDgXgc82+aPaAveHMIHWoTQhzH8FTBt1AFNQZp8bkTlNr97J5t9Mzvvdq3Xe/16r077pA/a5psxZciXu5Ogzd7y/3hGQ2XilF6rrAqY5YpbJubmKyiURMM1xEnK+C+ou88AHG/y03x4IDZ9sFG25wjZx6w6HtL8POKUP3e+Y3nGXQ2rrrTeT6pXmteYeqWx2zjNjwFLruAVjT9050vdAsG3n3QFe7bbfjv1ks39eM1J3LfYQ9jytN5vrB+olaY4eD5ioB5OlDmD6SgZMTw4ZMD0NMgnwZZwOYCIVDClgenAEcS6gXbVz6PT2BXzf2gITe9tjwwxvmB++i9uu95CWoIRWXXbKHrWqEEmxCvjcSsPFQ3exaZYvpvS7gUEtrNCtqgk/PknFNITv7WPNq5XG6Nj+STn2AWCyFWEMqZcseVVQezpP7jy6NzDFyHaXsXi8C05sDIHL5STER+bzAKgsgticSlnIA6ww30xcM4nDIcNALBrjggkdr2Lwu1boU8uMh0t99cx5azwCGD+J50jrJqmXRrLvqZcU9Wb6lj1PgEsXecA0oKoFRjayxdTPb2DlEA8cnRcMu0OxCLpxD6l3lVDnvdj5qfKLkMx+3tsuDaZbI7Hpd19M/8YBI5rboE9Ncx4ukT1eX1F1RQDsp3LY5zJgejnx6gAmXZAhAiap5xH1Y1rSSLCuW1BH6PNDVnmrP7iv2t49XX1s9K0Ci/lbtQ7bxxX4nPla6Wf1boyDw1PXMz/AvHGhn0m3ApeDf2ksF+5T7x/ooFjeIkVBgOkvlv9UZsdixzRoDgUPLETIxIOmNm8IZNJZEyl5e7yWbE3Y/tFvIFgYLmwAlcG7BJeg2tk7W310pLfmwrTDBZeWTFJe2dBJdXVbi3SHfXWed//mG835RHFu+m/Kk7/uV+793lm5/ou7yqVNlIp5NaGYUxXKBbVFWzzdflkiBJMBkxxiyIBJjtIKHjAZ6gCm+aOKoybJgEkGTKUeku0Y/S5DSgVSgvThhCL9ZpaW3MPCKxWrqfCqW2x/01O3ZwoBCrInI1UMQTnqe7OBE3r/DOIEVQhZj1GhXrbJe7aQLPEIapCChmp2pFoiEEq/l3TgBHhH/cJ+4wTLt5Usd3ICOCGAQoolUu4QWCElD/UqonWiAj7taYJKJW3vStrblfc+e9a9KGVJ0EQKO4JopLIjC0Dq1UR2jh7i/JB1HgHRTZwAMiazpPdL6lMk2eaRUowUeGQTXrI3U0WPfwNMpGAiZRtZCdLeoHmi/VAe73MSMHwcYNJVMEmAqRpXnmqyCg+YeCs1F6H30mwXVJvvisbLPfHVttv48WQ4ltrFwSggA/5JCh4QFT6nOxPhILLFS88vRFiqCo5382Dkn4Gdt1Kw7HI8/rkYjT8u3OWt635nt1NNojDHMgarrsXjgFsyzAPuwS0mBxHpSnZ8LdQFRc/93/tF9wVbvlB2fBN2bHr9rrsCUXeJp3DuZIlW0QFTxGMB03f7XFPmLbaNOz3ydLgvW7Psd1Z4sZ93e2iNVxYKJmnMcyUwycY9zxl6851RZaEr6hu4F3+wwaew74Hg2GmmUZc330xec9orY5yJb1bn816ZLQ8532uw9UZKzfX2if+Z/DrdVVXyjdNU8Y1RN7wRktf9qEv67PkWMcbDj4WFdtgRkNZmvW9Ok1Ve6rcMPItrUN+t+W4PoeoDsKQzP7NFizzx2myyzCuv166g0KnGdy033khce8g9bfxxr/R2h93TnssG5k0KGTA9HTCN0lH3SKCC+vuQ4qQXZ4oOeufxZdWz6FzLCINbW+KfIQ7YtzwAN8ziERmYzVvZFT3vm/Gzvl8W3Uc29SUKzIGDRSKOrwvF4rGuGPelHfq+ZY5OekY8ZOrOGeNbHjJZ8vZrY0XLv3E65zX2wddC/6VhvNLHnO9rREqtduw8+zU3x7RBN7DfMABO1olIiMiHugx6TUlRWFCMrHQNIgKy4XgpEae3hmHVZE9M6n0dw9tYo199cx4uESwiuDSIt5iz4ddM6L1k90C9pGv5R/Z4BJZ6EmDSM8N31S0xuukV/N3OAat/9MLJRaG4fjweIY6ZSI9WQaN4MUioyC1Ewp18uF1Kxpm14Vg11hMTO1zHkCZW6Fn9Ig+YyB6PgNdQ3hrv4Z4r770vA6bSj1cLMD0Oaogww6AZFEveYeNtIAAm6rfDxqxa95lCvX9giObCNFPttfUrijxOjtQGWX2Z83/snQV4FGcXhSe4thQKLZQWilSpQfFixVooUhzaAnVKkYQQXIK7F3dPQpR4kLi7u7vL+ibh/HNndsiSthBoIIF/7vPcJ0jIfvPNt5tw3z3nhNk88ntwQEBAY0m8W3t1pEM/tcvRX5WX55+R7fg0VLqshVLyR4N7kkUNeKs8yoFapwEYnIVfjyobvzrfq2dxL/4BLhH0W/kqfy+oSb206e17ir39S5SnJkaorvxopDRbqq+wWT1EYre6ffJ5w2aPUpVplY6z4fBGsrMTO5Ud/nqCdN8X+6TbP/GRbOxWKF3VQS7Vb3WPy+Oi3CU6u+s68Wt97nOyRMD0tEoETGLVVomASQRMz6gEezwaVpLtEg0vaVhPCpBTDK9yIGBCg2lBvSTmLz3YgoqJ9oeGwskMP6y+yfDWbMsYXlkziOFtxwiQ0KBbGNCL9ffSzlsSLPHo521S0giqJVLYkJUj2eH9wfCKO4IFBEpMGF5F5sE8qFjSBkt0v2iQ/09QCczzA5b+DVQIoIlayGwimEYKHW3QROCNABxlNBEUPcrw6i9dhod2lGX1BdsfafaeAA2p8Aj4PS+QSdsiTwBMZJEnKJiqA6a6VDAJgImUZ48CTKKC6aEtKDb+dOMgU0sDL3TbEoCRJyLwh3kiDntm4VZCCeILFChRlHOwpiZFn6auuAeJshJZpWqEZ8nhFFOCC3752H47E4vMkjHrUhy+PhmNoX9FYvDhCHzxVwS+PB6Jb85GY+71OCy3TsI+5zQYBefCNaGYs8zLlaghU1dyoOtxxo/l7FoySlTsGoph6JiOsaeiQHZyTfS90GCxRslyH5zUD8A06wqfwUSA6W58lUWeaVhBc7Owgs5GIfnDT/nkLF5rn3p+2qXYwI/3hpS9ss4XOqQsIus3+nqLtSzgamOdul5a1nsenB0eqZiaGHjipTXe6LjJT/HhnsCc0ScjYn+9kWC/627mLqOggtkOUaWf2UWUvmoSUFQr39AtI0sa2kVLWt6Jk73uEid71zFSMvSqb+GC7Y6Zp368lhAy/GiEqseOILRd74umK73RkKAb7YvuI+7vvwMmq513Mrad9M6dIwKmh5cImGoGmKZxkEJofvhPNmxjGAtOIfQRc5ntKxj4kjFm9rHDxp+9YfRXLPzv5CArWQqFtPzxXUNr+NotZ792dqoMIe4FuHkmGfuWBmHhSGdM6GaNgS1N8FnDa/iMuYaBGshE6yaw9B3jgDmcwsfhAWs84drIVo8s58hq7yOdq/i8qREmvG+N1XM9YXYmnoM+8idU9tSo2O8bCkkFMpOk8GP30fR4PPbqBWLxeBdM+9AOo9tbcJCGINGXGrg0QQNppj8CMPGZUlWAaWxzS8x4wx6LPnfBtmn+uLw2Gs6X0hHjUYT8FDlUsscHTHRvyorVSI4ohcuNDJxZF4FVkzzxXS8HjG5rgcGNTDjARBaGZNlHa5+qWft0ETCJgKneAKauDwImQ/b3G96ElINMgpJJAxc2dFXL9g3IUJyf4a2yWnWl3O3oivIQizHyBNc3awg0dCQJnh3Kg28MV9msXaM4+Y2dbFOPDMnydmWSJU3U0qVNeICykn3ctZ359WirmJ5LkFGT1kCaB+BSV14pRLlUqztw1nQ87GM/sn8m3/5BmeLQiEjl+Rmmquu/rVfd0JukNFvV7THAEmNoyDQoOzn71bJjE9+VHhr+lWxH77XS9V3tJCtezeVyuPSaglMvGbzEnttX+bVwFobdRMAk1r+WCJjEqq0SAZMImJ5BCbk2NMCneQINjwczfBYLDZiN2fZl+ME82b/V1bv663trq5hoeE+De1KHEJy7wLYh2/MZfqBNYIRAnmCT9zwM5591acMl+j8TKWZIXUd5QAToSAk2nOGH7fPY1mP480pg5CrbtgyvIAtieDiawvBWeASW6P4QZCGAIICl502p9CTAQlA00TVXB02kTiRlF2VSuTI8GCVbwf0Mb/G4gO1pbH/J8Ioxugd0hunnAYIcTTX3qr7mMgnn6Z8UTKQu/DcFU10DJrJupPvizPYZ5p8Bk7DvdVP1EjDpazVBAsohWuDKAYlXVnjj093BmH05FlvvpMM0vADB2VLkStVchlJN55kEl4rl5UguUsE/TQqriGIc9cjBats0zL+eiK9PRWPAwXD02h1COT14e2sQ3t4WhJ47g/Dx3mAM+SsMk89F4vcbsdjilILzvtlwii1GeLYcWWUVKFOxj/GYkKlIVg6flDIcds/C7Ctx+IC9zlfW+KIJlz2lgQ+6mo91DJjeIcB0Oc58993MFZYRRSNcE0o7uSWWcnDGLrqoiUNMcTvryKLPLwfmzdt8K/2vOVfjvHvvDy1tt9aPt8cTsqXoI8GmpbUAmHQ1qijBXk6jemvMnqN2a33RY3tgxaDDYRnTLkZ76lolXd/vmmloElIw405c6WduCZJXa/N5ZRNd+pJttKTbzUjJEOOgkjknPfLXbLLPvPSLUZLXmBNRhb3Ye9thA28XyGcradnhPQwiioDpP5cImB4NmKbeh0x29y3zZmh+TftDgOBj5greZy7hk4ZXMeZtCywcfxeHVwfD7koyovwLUci+FqpVT0nFVH4PkhI10mIk8LbPwdW9MTCc74u5g50worMZPm15lV3bZXzCXMVgxoSzYiPo8r2OA75nHDnI9He4ZMVBD7o2yl7q08QIw181ww+DnLBHPwguN9ORlyl/KtfDFfvNokJRieJsJWL8i2B/NQXH1oVhxXQPzOnjiLEdLTGkuSmXYUSQaDRjySmAvtWolwRFFgEm+jXlGNHf0VkeqwFMZHFIPbSBGb5qaYVZbzlg6QBX7JodgOuGsXC/lok4n2IUpiuglj/+vSNVV3G+EnFBxXC8nILD+iFYMtoFU3rYYFgrU/RvYMzBSbLpG8PlRtncz8Kazp2vuj//ImCq3Xr+AZNgdcaubUNndp2v82smqzyDl3jQseVdifzw8DTFlfl+Soctp9S+l35Wxzp8khPqWKMMRwIgyujb76g8Ts5RmuodkR/7ykO2tVeiZEXbEunSxpWSpY0hWUbZT6/ygIWz8OuusfF7+8VTMt3PW3r7QeUSZRyx50RKuUsr2/JgifKwCPJs7nlPsa9fovz41+aqC9+tVl7/bbzK9M8P861WtH6c85p/9qfWsgtz+kiPTZgj2zd4u2zzuxbsvsey96FCuoiBdLEOpHrNIF3xCpfNVWWN170a9Hse74kImJ5WiYBJrNoqbcAUse7noGgNYMoQAZMImGqvBPUSKREo+J6GrqQIWcTw2TWkaCBQksvwFls0nK4PgEk7e0bbFqwu10RrUWn2ifJuKOuGVCFkPbZXs6ekDKN8KwJ57TT7XrcD4vpZNGcU4JJgiUfWgu+z3Y/hwcAMhgcfpFqi/SU7PMrRucO2H9uRbCexncXwg3oBLAmKJQEe1PW5eZbPF23YRHug1OwJwWN6jhNIjmLbn+1bDH92T7K9jeHVTJQlRlaPlHf1geaeaFvm1ddcJgEwkdqKoMzDABPtgbaCqS7ulZDBpA2YtBVMlMFEgI/+71m3Npv1GzARMNDkzfzmwg3WX1/tg2GHwrDUPAln/XLhnlyK1BIlpOqKGquXKtlPK1VUIKlACc9kCUyCC7HnbhYWm6VgyvlYDDkSiQ93haDrlkB0NAxA23X+eGWdH9ft1vvidUM/dN/uj8/2BWLU8VDMvRqNNTbJOOGVA/uYUoRkK5FRWgmJmuzvaj6cI5u8sCwpLgXkYbFFEoYdi0DXrQFoTQoXPc8HbeWelYrp3wDTjqCUmZdjzXfd4QGTR1JpZ58UCRee7JpQ2tA9qazF3fjSHuZhhRP2u2Zt/tUk0eGLI+E5nTcGoBl9XfpaBA3/cOXVaZxC6wkhkwCXhP1ZpAFMS9m1sueo7Vo/vL8juPLLo5F5868leG10SDt12idb1yqi8GvXxLL3vFMkbd0TJI8V/PxvZR5aoGMdWfzSzaiSnmbhpSMv+Bf9scc557C+ZZr9rEvx0cP/isx5f2dw+esb/dFylQ8aLNOCSyJgeiYlAqbHbSGTyV6Tx2TD2a2RDV0v5gqnYhrS4Qbm9LfHurmeuLAjEu43M5AUUcJb5amfDmQiK7niHBXigkpw2zgNJzaGQ3+WOyb1tkbf14zwbqNLHGQiWESqK7oGbcAkADPKABqnlVFE9m2DGt3A8FfMMPU9Wyyb7I5zO6IQ6JqLsiLVU7kWqkrVPUgL1EiLLIOXTRYu747Bph998cvQO/jmbWsMa22KQQ1ucPlQw9n9/0pjjTdVCy5pW/4JgInO8xiNMouujf79sIZm+PolK3zXzRHLvnDDvrmBuLEtDl4mWUj0L0FxphLlise/b+XsNeRnyhHuXQCrU4nY9UcAfh18G+M6W2JQUxP01eHzsYYxplzWFa1PyMKaIQImETDVJ8D0N9ChgUzrtfKYDF7msn+kaztWyLf1ksmPjslRGi28rbpzYGtFsNl4RZJnl+TkR2cxUXEqpiDzYWqXw0tUNxaflR/92lW2qUeqdHkrhWRJA0iWNIZEvzUHNaTcPlVT97xIkOlvcO9t/mysfYNTDXF7Tr1KA9y294Js36BCxbFxdxXnZ2xWXvpxrOL6gq4lV/94hRRJj3NelVf/6KY4/90c6fFvDsn3D/aQbeqZKF3RtozyligbS7qkIWT6rfjcpXWdScGmpV4SFEz1YA+fqEXA9LRKBExi1VaJgEkETM+ghKErDfEpX4XgBw3u17F9ieHtxchCiwbQNPCsi3f0/9MAVluRIVib1fXatAfDtF+khCBrNjuGH9KvZnsO20PYfo/hrd5oMN+Uqb/Kj2ddgqKOZnUCXCLw2ZXhlV9kMTie4UEHZS1tZvsvhlct0T57sh3K8LZiGQyvziFYUB0svciKpcd5DgmKJrIKpPwwUngRkBNs8+j5b8PwrwWkZlrF8Nlsk9keyvbHmntD94gUec2ZKsu2+nSehXMlACZ67hFgGsP8PYNJAEx1mcEkvI6QRR4BJhemCjARpCbApK1gEgHTQwETgYhfXTgo8dY6P4w/HolN9mmwiihCZK4cRYpyqCtrTnJUFfeQXapGQJoUN0ILsftuFhbcSMK4UzHoszcM3bcGocN6f7RZ48vlILVY6YPmbFNGTrOVXmi5iqCFF97Y6I33t/th6JEQzLoUg5U2qTjlUwCneBmi8sqRL7+Hx5mtSpQViGGvxyK8EBsd0zD1Ygw+3ReC9ut9ORUOBxc4u7y6B0w9dwSlzLgUa77zTuYK9j586Zlc9ia7n02Ec+WXKmnglVzWwSG6eOApn9zFy61Trk44Ex3ba0ew+lV2T5uyX0+HUzG58iqmxR4P5g3V5PoesMXT7MtiHjDpLOHhUps1fui5LVg58q+ovJ+uJQZudcy4dMk/T9cppniET0pZl6AMWXO/VGmtPAHNQ/Ib3AwvbG0dUdzDNKx49Hn/wj93OeceXWSR6jLpXFxG3wPh5d22Bla2Y89wC4KG+howpp23pOslAqanXCJgevwWANMsjTKG4AApg3oz1/Fpg2sY+LIxJrxzEwvH3MWexQGwOJGAIJdcziqPLOXuPcbr8+OUUlKBnFQ5gt3yYHY6ATv1/THvKycM7WGK91tcxrvMJXzKXMMIxoy7n7N1yCavCjARACAVEGUZkaqG4MtgnRsY0dIck7rY4Pehd7Hzd39YnkpEdEARZGXqp3Id99jvE8qyCuQlyRDuWgCbM8k4qBcC3XFumPGhPUa+aoHBTW5gEMOrl0Zx+UV0Rm0fUC89DDARPBssAKZGZhjXxgo/9HSEwXB3HPw5COa74+Frno3koFKUZD8BYGJvsUpWiewUGXvv82B8KBab5vvghz6OGNXBHH0bGbHn5RoHmIaz1/D1/Wws/myJgEkETPUfMHXlrPI4FRO7Zm7tZJXGfpSt7wz5rt5q5ZmpkSrr1VfUvucWlUfafyGLcuvo7Ozc6FH7VBjv85Iq8vYHFYHGE1ROu1Yqrv58VbZvYJh0bUepZFkzHjDpNeeVO2s68mqev4GYerBntbbvwnV15c8FZS5RFhVBPU491gZS+rNtvVTywyPKFGemhiuu/HRKYfLHHIXJordNTKbX+N2SpCCjjKYSm1WvKEwWD5NdnGsoPzburmxPvxLZpu4VspXteFs8zh6vBWQr2lZZ471QoE8ETE+rRMAkVm2VCJhEwPQMir5/0s+kpKYh26vhbP/C8IoQK4YHJGT3RsNnekd/XWcvCcNXtWY9NARWMFV2Z3WpShHWptLsF1myRTP8cJgACKlASC3xFcMPiEn98Ypm/+t2SFw/ShsukbKLgAUpTboxvCUYAQ1Sb/zE8IP2XQxvG2bG8KolUt3QfhMgIDUOQT66D9oZS//vYKn6eRXOLO2NoGbSts0je0GCLqRmIrtMsiA0ZPtPhgfRIxnerpDuEUGbNkwVZKpPSqZ/AkwfMryCqT5mMAmAiYCfdgbTCuZBizxRwVRjwPSbK5dF1NMwADPPxeCQSxbcEsuQUaqCoqLmg7CKynuceikmVwH76GIcdMvGItMkfH0iGh/tDEGn9f54eYUPmi3z5qBOI30eBFA3YFtnmQca6rmjyTJ3tFzujldXe6LbFj8MOBSKWZfjsN4hE5cCS+CRokBKSQXk6poPVmWqSiQXKnAnvgSHPbKwwDQBI45FoMuWADQ38K6CPIs96h1g8koueyswXfrAgMw3RdLyblzJO9eC8qftuJOx5xfjBNdRRyNz3t8apGxP0E7XAw0WCflaHprMJM8q6KJ9jcKZuL8uDYy6r1wSVECeaMj+vgVni+eHd7YHK0b8FZX+y7Uk760OmZcu+xUY3I4tHRuQJukSniVr8m/Pi8cty9D8BtZhBS/fDC/saRpaOPasX77uDufsk4ss0pwnnItN+3Rf2L032LPbehV/rnT0qoMlrWsWAdNTLREwPTlgmq0BM5SdQ9CG8nT66FxHv2ZGGPmaOeZ8Yo+VU9xxcn0YnK6lItKvEPkZcihkFZx9Wm1XZTkgKSlHSkwp3GwzcXZ/JPTnu2FC35vo0+46PmhENnnXOChD93W6jjYos7tvjTecu5YbXA9taorxr9/E/N63sGGWD85vjoS7RSbSYyVQKR4/l6gmVa7irfHiAorhbJyO85sisW6mN+Z9fgvjOt7EF81NMVDHhINDZHVHlncTufyiv8OlmRo7Q7pvpM4iuCEAtEHs/SJINayxGca3tcK8952warQnjiwIwc0DiQiwzkVqWBnKclWoUD4eYLrH3l95aQXS4yTwccjGpV1RWDPLEzN62WFomxv4TIdysa5ygInODqnGprLrE+6HCJhEwFTvAZMAD9Z3Brd2UtMQYFrekrNMI9ggPzg0T3X1Jy/1rR1H1b4Xf1GHWPQr8zVv96h9iow0aSINv/2aKtzqY5XnqakKy5U75Kcmu0h3flzIPdayVpDoNoNEn/1IgIPs2YTsH227vLres1rZc21Y8xavFKLrJbhGOUjUpF7a9G45e5ZylJfnhqnMl5so7Tfpye22Dkg30Wv+OGc0x3FPS8WtnW/JbA0/V5os+U1+buZV+cFhSbKtH/IgiaCWfksebK1oo9n7t/4Olp57u8InAEy7vhcBUw1KBExi1VaJgEkETE+5BHs8GrjSsJKGlvTu+OUMP7inoSa9e55smkjhUF8UQirNesiKrkzTBBKEXB0BJNTFGgVViEyzb2TRRnZtlgxvObiM4bNsBrLdg+Gt32hIXN8G8s+6tAEAwSUCFQQBujM8wBjB9lSGB3SUCXSA7csMr65xZ3jVElkSEgwV7PDojAjnoa7Pbn1ubUWgAG3puUXqGYKkpGYi0EyZVnSO6bVhO8PnXpEij1RAnzM8oO7IVEGmRkz9OdPVLfIEwPRPCqbqGUx1cT/ozAoKJgJMLszDAVPdVf0ETGSVxra+h8Yiz5WzyWui54Ve24Px49V4nPPORUiGDMXyCtT0zfH0eVJVJdJLVPBMLsN5vzwY3EzF5LMx+HR3CF5f64/m7OM3IlBB4GOJx98BAK1nMe2LKxosckGTpa54aaUnum7xxxd/ReBH42Tscs6FZUQZwnNUKH6Md4EryklZpYJfmgRXg/Kwzj4VU85H44OdQexj+PDrWchDHm4t9QUwhReNZPezS0C69IH/1HsnlzVyiS9tbxle+MUJr5zF6+zSLs67Eh8w8q+IrA+2BZW/vsYXLfW90WCpBrQs9ajq+2omT+iw69DR55s7F3ra9+TBf9OI/dzWK7zRaYMfPtwVrB51LCrj5+uJ7tscMk9f8ilY5hRV+rV/qrRneJasRW0+j6wILoUV9DQNzh9z1idXd9vtzHN/WqR4TjgXl/Lp/jB5R0N/tFhBVofVrnHpYyq3RMD0n0sETP8NMM3S2OSN1ahi+jPG6NfQCENa3MCEzjfxy8Db2PKjLy7vjoarZQbiQopRmK2AQlaOyqegZFKr76EgR4EI/wJYX0/C7tUB+GncLYzqYYG+LxmhT8PrHFQhyMJDGV71w6uXbnJZRgSgBjAmGNyY/by2Fpj9gQOWj/fAMYMw2J1LRqRnIQqzlFz209MoaVk5UmPK4G2bDaP9sdj5qz/+GHoX375tiy9bmWNggxscHBrK7jepl8Zrzuf0BwCT3f2uDpjI/o+ylwZygMkEw5uYYkL7m/jxo1tYO94Lx5ey13ksGSGOeciIknJWfRWP8eYIcqetUN1DWb4aiWElcLXIwGnDcOhPcsfknjYY1NKEy8P6RAswjWesOKAkAiYRMNVbwHS/q0EPQVGzpgNv1UbwgaDH6tcg3/GRUn7im3TljUV31I5bD6icD3+ncjvxQaSJ4aPe0KKT7mXSXBJk0l7tcfZzpf3mhYprvxgrjo5OlG37sIKs8SiHiVRMBJmkK9vx4IXWUz2P6XmEHP8I87rwMI8UY6s11nj6GshDCq49/UqU52cGq26uNmb3eZ3S5/w4hceltx7nfJJ6SX7n+BuKW4e+UNgazlcaLzwkPz7eU7rj0xKCS9LlL/HqJW7P23L3mNZ0f9/v2+I9r7lLjwJMb2oBpiGI2vENgnbOyPPb/b2V764fFviLgKlGxQGmIQ3H5w1rfCh3WJNI9iMHmPK/eE4B0/dDecD02+Qjd36fJAKmZ1g8YFrwZeimP3ZHrP8lKHr59MrEX4YgY4oImETAVCtFA1eyZ6M5AikQyH7sB7a3Mnz2Cg1bScVAw3pBvVRXQ3pt5RLBGxoAE0jI1TQpLkixQoNxGgyX19FahXUqNWskmzayGiMFCGUEbWR7HsMrP8jyjXJUXtbch/oyjH/Wpa1cooE5nUcanhOA68P2KIZXyyxkePUMqWiM2HZi25fhM4NSmCrVkvYZ0LbDq2uQU9/7n2zz6LlPeWKkCqNMK2+GtyK8yPCqH1KS0XmmXCbKxqKfE+lME2RqwdQvcKqtYBIymKoDJlLB1QcFkwCYtBVMBPbEDKaatWbgvowG8QQ1+HW0XumDfvvC8KdpEq4H5XMqJOljeNApy+8hV6JGaJYM5uGF2H47A99ficfAg2F4kzJx9L2hQ/CGs25zq4JM2jZmHHxi/+5Pgl4u7Oe6oKGuO15e7Y13dwThq1Mx0LVM56zy3JOkyCpVc6qpmhRZ9xXKyhGdK4dddBEOuGbip+vx6LsvBG1X+/L3gtZFoKeeAKZdAmBKKuvqlyZ5ANp4JJbpuMaXNmev5d1rQfkTD7pmrV11M/Xa3CvxPqOPRmZ9vCtE1XljwL3Wq3w4pdh94LLkQcj0z4DJ48HW80ATA7LE80GXzQHosz9EMe50dNrvxknu25wyT132LVjkGFk6yidJ2iM0Q9Y6NFNWK0+6c765DY2C8tuYBue/axSYO/aUZ/aSbU7pp/8wTfL+5mxMzmf7wxSdNgWg+UpvXrW0xI2HlEs9/lmp9agWAdN/LhEwPRlgmsmBAB4wTeVUTLwyZgin/DHGoAYmGPWyOab1tMWSMS7YuygQxkfi4GWfhaTIEhTnK6FS1r4CiF5dZezrelqCBN53s3HpcDTW/eqF7wY7YsxbFhzcIPUPwRmyiqP7S8qliZx6yZLLkyJl0ECdGxje2gyTutrgj2HO2P17IMyOJCDAIRcZMRLISso5K7unUYV5CoR558PqbCIOLAuC3jhXzHrfHmPbWWJoI1NOWUX7PJJd69ecesnm/n2ZoYEzM/4BME3i8qVu3r9GgjsEmYY3M8XE12/i589uY8O3PjhtEAGnM6kIdy5AdpwM8uJyVD4GTKtkb6tKWoHCTCWifYvgdDUNf60MxeKvXPBN15vo38wYH3GA6RoH8mg9dB9EwCQCpucHMGlBJvozUrCQuoVUTAQhOHVLW8rkuSff20+pODU5WWH0q4PCYvlmpd2Gr2UO2zoSzHjEdukEBJxsLHc9+qbSaftEpanuHvm5WS6y/V9ks49bQfZwEt0mbDdlH681r6TZKKiYXjDAxO2xYEf4Kn9OKPeKlGJr34B8x8cVihPfJClvLLUqdzm8oSLAeLIqzPq9/Bir1o9zPvM9zrZWux7/THFr91ylxYp9igvfOcr3DUmSre+qpD2WLm3MW+ORionyryjzida2SaMce+5t8bRbBExPq0TAJFZtlQiYRMD0FEtQL9E8h/JT6N38ZN22mOEH+I4MP7in4TINmusK2GgPXYWhNw1/CSbQIJgUQqSwSGH47Bh6xz8BBlUdrbe6TR6tk1RglA1kwvCD7EUMrxSjvKu3Gd6eUDu75v+ptJVLAlyiwTmpYUgVQxZmsxn+XG5h+wTDW+LdZTuQ4feWIJ6gWhJUbGLO0pOfXwE00fONIIdEs78Zmv0mCENw7xrbBxk+W4xsCykbawBTPyFTdQWTAJgIXpIqTrDIo2urTxlMAmByYR4ETKRg6qS5liZMXb5u1EvApPcgYNJZQpZ0Xnhtgz+GH42EgXUqLMIKkVCg5FQ/NSmCPCWKCsTlK3AnrgTHPHOw2CIZo09E4d3tQXiFIMdSDUSha1/4L4CJy0HSQC9SVi1w4X7dWN8Dr633Q9/94ZhzOQHbb2fBOrIYCfm0xppNJcvZNVIOU1qxklNYnfPNxVLzJAw5FIYOazSAie7JwvoHmDySyrr6pkr+pgpyiS9t4BhT3ME0tKDPGe/c6bvvZK5dcTP1/I/XEtzHn4pO/Hx/eFGXLYEVL6325TOJCLws9nhQPabnxUMmAT5y98Kdb10PzrawiYEn2q3zRY/tARh4KKxk6sWYuKUWyU6772T9dcWvYIljZOlo7wRp96BUWavaeu6c8M5tcsk/79WrAXkfXPDJGX/YNVN3g23KyV+N4lzGnYzM+GxvSGXnTQFotcobOvoCPNMCTPfPuQiYnmWJgOnJABOvlOEBE/3+W04dY8VBjyFcto8JhjUxxVcdLPH9Jw4wmOSBwwYhsDydyOUxZSRJIClVPxUVk0pVicJcBWJCi+Fkmorjm8JgMMMDc/rYY9Rr5hjYyAT92fV9weUXmXP2bNQEyMgeb5DODXzBrn3sa1b47lNHrJ7uhXObIuFqloHEkFLOvk4tr+RpVi0XqX+y06Rwt8vEmW0RWDnLA9/3ccBXHS0xrIUZt2Zqssb7il0z2RPy2Uv8fZmuuR/TtSDTPwEmUnH1FwBTc1NMesMav/W9g80zfHF+XSTuXk5HtEch8pLkXB7UvcewNCS1k7ykHDlJMoS65sP6TDL2Lw3CH1864+vOVujXRARMImB6kQCTYJX3Jgd5SE3EAQiCHwR9NveEfF9/meL4uCj5pe+vKE2X/Cm7ub6vxHFPB7JjexRoKrQ7/JLMfkdfpYX+b/LLc4/K/xrlLt36XpbUoI1asrQxJEsa8VlAq9vzEIbW80IBpq78WVj/BneNnHKJy7pqw50T+ZYPFPIjIwsUV37yVDtuP6TyvTJHFW7/cWmkQ9ua5F1pSifZ+XwzUjwp7x4er7Jet1F+9eeb8iNjoqVbPiiSrWxbLtVtAulSfq85yMXebyl3FrprqcZEwFQLLxMvfImASazaKhEwiYDpKRYNXGnw+xLbbzI87CCVyHq2r7DtxXYyU/VO/rrMXtJWBZEdHkGbFIZXVJB1VxDb4QxvkZalWXNdWfppD+dpDUWatdIabRkekKxieGhCmULvMbxdF71hRhgU1we1x7Oof4NL7zD8eRzL9nds67K9g+3TbFswvFUbWeIRWCQLNwEq0vkQcrhE1VLtnGPheUf7W8w8aJlHkI+g6V9sr2P7Z7YnMH+HTNrwtK7OtgCYaB0CYHqfqcpg+jeLvPoCmFwZ3iLvnwBT3YLp+gmYBFWKO3R03dGI/f1Lq3zQc3swJp6NxSanDNjHFCO1SMWpfmpSBHkyStTwSpHgSmA+1tqnYeqFWHyyNxQd1vujCYELAkoLNXBJyDqqbpGnq1ExLdYonSgfikDTYje0NPBC9y2BGH08EroWyZwFX2C6lFMl1UTFRJ+iYtdJnx+RLYN5WCHW26ZhzLFIdFznx4Ot3wlsufPreg4AE5VDdHFzs9CCNy745X16zCPnm713sxZvsE8/vMgsxWbahfjwgYciirtuCQIPmbSt8h4CmDTKJR19DzRb6Ym2633QY0cAhvwVJp11JTZ6tV2K5VHPnG1moUXfO8eVDfdLknUPSpXXGlw66Jbd6Kxv3uuX/PM+O+2dM2X37fQ1yywSL86+EO0x/Eho8ofbAxQdN/ii5QpvNNDTKPGWuD+oXnpcuCQCplopETA9fk+7DzB4O7YZmgwjsmDjVUAEQm5wKpmhzU0x7nUrzO3jhNXTPXFifTicrqciyr8QeZnyp5JjdO/ePS7nKS9LzimBrC8l4dDKEOhOdMXk92wwuNUN9Gau43PGiFsjQTGCS2TVNlTHFEOamGLkKxaY+q4dFo12wb6lwbA+m4RIn0IUZSmhlBJwqfVlc6VWViIhsgRWlxKxbZEf5g11wtg3LTC45Q0MbMBDsWEa9RUPl2w0cKnqvkzT/HrG/bbn/owHTFb387L6s9dPgGd4C1N8+5Y1Fgy6i23f++Py5mi4GWci3q8YhWkKqGWVNVdrsd+31IpKlOapkBZVBj+7HNw4FI8dv/rj50G3MeZ1S/RtZMQBpk/Ze0DroP2fIAImETA9d4CpGmja0JW3qVv9mgYyteHt21Z34AHE7j4F8mNfecqv/HRYYbH6B7nj9v6kTkr32v/QjCATk+kN5XaGnRU3DIYorvw4T/7XV4dl2z7ylK7uUEgWebyqpjmXSSRb14lXUz2wTi0I9lx0NbjEWeMJ6qW27L621iiIOhC8U8oPDstWXvg+VHVz3VWlx0nd8mDLQZJ4u/YmJiYNa3ouyY5QFmTVSe57caDSccdCxfUFF2RHx4ZKt35YJF31WjntLweYyB5vBQ+2uLVyYKlHteylut6/2uoaAKad3yB418w8/71zrXz3ioCppvXCAKbR7RH17Yfw/2Eo3H4ZH+X82xQRMD3jqgJMf+6O2PBbULTBjMqkX4cgY2o35I5swd4nETCJgOmJShjs08+i9HymgT5l3PzK9j62bzL8AJ+GyTRYpqF9XVrjCcCG1Ck0cCWFQQTD23U5M/yg24PtYIYffhOAkmj+TV0NiOlxCcyRqoagF6nBXBg+N2ibZq9JMUZWVwT42mjuB92X/xcV07/BJbJao735nuEzq3axfZ7hzyXdZ7r3KQx/nwWYKGYtPZ0WIJPw/BMs82j/yfqRYB8pyo6xvYHhz/W/QSZ6U1hdQaZ/AkykYKoOmEgVVz2Dqa5eP/4NMJH6UbDIExVM/wg0dDUDeV136Oh5oPlyL3Tc6I++B8Iw91oi9rtm425CKTJKag6YSpUViMqV42ZEEfY4Z+En40R8cSQCb20ORIuVPtBZqsldol7s/jcFzd96qQZI/aGx0/vTDY10aeDviz57Q/D9lTj2cTJxK7YEyYVKLvupBnM6VN67B7m6Einsv6F/u/NWBiacikbnDf78vXgOAZNtZFED4+D8Fud8c9ud8srtftIrd8hR99x5e+5mb11hnWY6+3J8xODDEdLu24LQdp0vmlFWEamZhKwlbcgnqH70PdHIwAutVnuj/UZfdN8RgAGHQ+XTL0XHr7BJvnnKJ2ejXXTxRN8U6XthGYpOYemKVsGp8lp5oq1zTG900C2740nv3L4nvHJm7bydsXGxaaLxxNORgX32BGW/tdFX+spKLzTX9+DsE7XVVnw/IVwSAVOtlAiYnhQy2XJqmRn3bdl4iDGR3auxnBLIlFMxDWhgwkGmbzrfxM8Db2HTfF9c2RsNT9tMJEaWoLRIhYrHsDataVWy3wvk0nJkJkkR4JIL0+Px2PGnP+YPuYUvXzPHZ8x1DnL0YT8O5vKMTLnspWFNzTi4NLm7DX4bdhebKD9qTyy87bORkSiFSl75WGqex1pzOVCQrYCfcw7O7oqE7jRXTHjvJga2Nuayo/r/LXdJW7lkex8sVYeAVYCJtwEczuUvGaMfY4T+OsYY3soMU962wcKhztj1YwCu74yFl0U2kkNKUUJZU4qaq7XuVd6DUlKBwnQF4v2L4Gqcgctbo2E4xwfz+jhh1KsW6NvQmFMv9eb2/gZ3PRPvAyY7rkXAJAKm+guYtECIdh7TRi3IRMolgkycXV5r9prak8JFKd8/KFFxdrq90mLZLoXDzrly95P9pT7XXnvUvmVZG7aQXV/RSXLp516KkxPnyfYNOCM17BEpXd2hUrr8ZcjIIs9AA7No7wTrtvuA6XnKBdJeZxdOlSVd14kDSvet8UitZfh2hWzPgDz56emBSnN9M9WdAxtVAdcmKyOtesTH2zWt6ZmMt7NrysGlEJN+Crdj3ystDPYqTk28I936QZaUUy61gHRpE8j0W/IQb+3rPMTjrAh7aKzxBKXY87C/Ne2HA6bUrUMQLQKmJ6oXCTBFT/kQAXOHwv3X8VGuC6YccREB0zOtSA1gCt/05+7IDb8FxdQEMNXDsyUCpnpXNCOhYS8NJynrhoaV9K54Gl6SDZMLww81yRaLhpx1ObTXtpwj9RJBrxiGh0sODD8UpgG3DdvuDK9kotyo4jpcu3aWDQ3lKR+KwBflBZEC5zDDg5NpbA9k+Kyh9gwPWv4fVEzamUs0T6yuXCK4NJdtfYYf/FPeD6m/SFVHqjUCALSndB7oHouqpWfzHBRygQTLPHqeETgl6EfnmtR5Gxneco4gE51t+rmRXmMoZ6yubSC1AROpBgXAROvdzfw9g6k+KZicmSqLPAEw0b621FyTmMH0ANDgrMT4oTypP1qv9EaPbUEYdTwKi8xTcNI7Dx7JZcgsVUFVQ4s8UgUFpEtx0T8fq2xSMelsDHrtDkHbdX5oRDCDUyUJlniCfdk/rI+ygpaxreetgUwePHj50w0N2DW/vNIL724LwPhTkezjpMAouABBGTLkSco5GHavBsslq7zcMjU8kspw0CUbU8/FosumQH5tzyFgEuqkV47OSc/c5ud88zpd8i/od9GvYNYRt9zNa2zTTb+/khA64lhk3ge7gyWvG/pXtFzlgwbCfSGQ96eml/D3pvEKb7y81hdvbglQv787SNr/cGjB+LOR0b+bxtvtupu+0zy8YKpfuqRnXK6ycWKeqlZetGZfSWjyh3nyS+sc07vsds4avNcl6/stThmbl5glGU0+ExX86e7ggtfW+lQ21feADmeFp2kBLv3bmRIB0zMtETD9F8hUXclEcIPfM1IEDWVuoB8HMowxrLUppvS0wZKvXTmrPNuLyQjzzEduugxKWcVTsZsjyFRWpEJSZClcLDJwanM4lk5yxfhuVujd0AjvMZfxAXMFvZlrHGwZoGPCrtMM49+6ifkDnLBujjdObYyAk1EaogOKUJyvqtFr9pOUWlWJklwV9zg3LyZh+2J/zB3iiOEdzdC70TUOiAl2cpS7NIlTLlWplKZXAxlTHwGYKH+prwCY2Gue2t0Wi750wZ7fAmGyLw6+NjlIjShDWZ4KlaqaXzTBN1lxOXISZIhwzYfjmRScXhmO1ZM88d2HDhjZxgL9Ghhz6qU+7OOT0m20CJhEwPRcAiZN31cxdccDkImUTKS00W/Bg6a1r1XKtvcqVBz7Olx5/XdLhb3hFpXL8W+VvkbvREaaNHnU3hkaMg3STaY3l1+c209+YsJyxYHBdrLtH2XL1r0plxm8UiHTbwWZfmvIBGu+DUIeE62rO54PwPQ2HlgngbJ1HTmgROeCOx/06w1d78l29pYojo+PVl5fwO7l1h0qj1Pfqf1N+kmC7NrXIN9KKJ3SSJO26hDTz1Tep2cq7DZtll/6wVS2p2+4ZFX7MsnSRpAsbgSpbtMqhdjGt6r2VchdqvN9exotAqanVSJgEqu2SgRMImB6SkXDfXqjBikLurI9mO0fGF5Zc4PhbaJoeExqBUEFVNfD7ep2c5QRdZ3hh66nGN7WjyCTH8Nb5ZHKQlBf1cX6BcBEQ2IaVlN+DSk+KLuGlAik9pjH9ki2e7H9BsMP4em+CEqPF7G0s3BolkhnkAbllLkk2OLRWVzO8HDpEtt2bPuwHc3w55LgBkEOAgCiaunZPQ+FM02wl55bBD/oXBNkIvhnyfZJhodMgpKpP8ODQwI6dL7p/790vp81EKmuYKoOmOqbRR7tM73m0R5T7pUL8yBg+kRzDQSY6mI/q6peAiYB9iwmezxPtFvji0/2hGDKuVissU3HlcAC+KdLkSNR11jBRJ/rlliKI+7Z+N0kEUP/ikCXTQFoscKHV5Qs1tiXCSDg39ZHgEmATNy/EwCIG2eT13y5Bzob+uKLw6H4xTgBh92y4RhTirg8JUoVlahhHBNK5BUITJfhhGcuZl+MR/ctQWigyz7+AveqDCb95wswCXXOJ6+xUWDh6+ahxb1NgoumnfbOW7nFKePEH6ZJjhPORof3PhBaSNlFzVd48wCPzuGvrnyTLSG7npfX+qH79iBlv4NhuaOOR0ZPPBvl9v3V2Ct6VomGh9wzZ9vFFH0ckSOr0XpqUjMvxzeYez2x4yLL5M9W26d9s9Y+bdGymyn7fzJKsBh/Ojqw996QvNfX+91rTBZ+i0nRxq51keuDeUvLagEKioDpP5cImP5L22kgh/0D1mbfaqzYyCqPcn5IqdKvoRFGtTfHD30dYTjfB1f2xsDDOhPJkaUoLVChgiDGU4A3ZDmXnyFHsFsebhyNxwb2sWd+ao8BLU3wrs5ldGcu4l3mEnoxV9Cn8XVO3UR/bzDVHcfXhcP+SirCvAuRnSqDQv50fPEq2O9bRez3hJiAYjhcTcWR1SFYNN4FE965iQGtCMZc08AY0/vWeAQrpnNg7/EA01fsvx/Gfh26L2QR2K+BEYa/bIZp79hhyWhX7F8YBLND8QhwyENGtATSAjXuldf8WirZb2qSfBXSI8sQaJsDy/3s970FwVj2pRtmdrPDl63M0b+BCXsmjDjwSMqxseyaaG0iYBIB0/MLmASlkAbk0NrXvgHpiraQ6rfie2UbyDd0Ucr29MuVn54aqjBdek15e9+Scv8rg8uib7erCWSiklmt6KQyXTRZefnH/fJTk9zkuz5PlK7tVCrTbQ7p4oaQ6jbjYQjBmfsWbt21lEz1YM/+1tUsB4U9JKCz+lU+d4ma/TX3+Tt7K+RHx6YpLs2/o7RYvU999+Bctcf5AYoAk7eyAqxr/LNeXqRJK2Wo1bsq3zOTVY5bNsqv/mQqOzQ8QLqxS7Z0WfNyyWIdSJY0Ye9fa165tLFLFUwU4NILk7lUvf8dMOUTYNomAqYnrRcWMC0UAdOzLhEwiYDpKZQwZKXvpR0YfshKipHFbB9leABCA2MCNEKOUV0PtmnYSgNtskQj9RIplQiEHWd45cFOhs+BIeBEdnmkcslkeEAm5EfVpU2eVLOfNCgmtYexZt0LGX5Y/Dnbb7PdTnNf6jZT5emV9pCf1CzacIn2YAzD2+IJyiWCS/YMr/yi+04wgwbu2nCpLuHn/2MLwFewzCPoS881es3wZHjIREomAqiUyTSe4cEhqfTI0YEy3wiiEuR+1lCkJoCpviiYBDgtKJhcGB4wEXil14yPNddArxd1sZdVVW8B05+8XR1lI3Vc74eBB8Mw71oCdtzJhGV4EcKzZSiQlaO8BoCJ8jnSi1VwiCnG9tsZmH05Fr33haD9Ol80WuZZpZIhGPAoECAAJmo9TV4QB8R4wNRomTteXeeNj/cE4dvzMVhnl4bLAYXwSZEhs1QNRQ0VV3JVJSKy5Ljgm4f5VxPx/o4QNKHH/NODhy4EwvRrCVrUAmDyTCrr6ldDwER1PbCwqXV4SQenmNIP7aJLhhsHF8w54p5taGCdYjz1Qmxkn/2hCrrvjQmk0Vn81YVvdg3NDHzQdWtQ+ReHI7OnnosLnHc1weIno/gDv99I+NPAOunrg+4ZH9tGF71am8+TOVcS2v5onNj/T4vkH3StUjb9diPx8tSLsc5D/oqIfm9ncE7HDX7q5gbeVdaJi9xqDi1FwPRMSwRM/70FwDSbceA+TtMM0scwFhjEmHCAiVRCg1uaYPI7Nlj6jSuOGIRyuUahbvnITpZBXlqOyhq+Hj5WsV9SUqBGfHAxnK6m4sCyYPz+5V2M7GSBXs2uoitzge3z6NngEnq3vo6v37HEgq/uYt+yQFifT0a4VyFy0+WQlqlRWYPsvCcpOfu9KzGqFLdM0nB0bRj0Jrthyge2GNbWlMsr6qNRL41gzDGOPYuTubMowKMqwCQAGW3AJGRkTdXck6/YezKMU5bxX5fA3/A2Zpj+nh10v3LDwSUhsDyWiODb7H2Jl0JeXA48hoNhBSmxspVIDCiBh1EGrm2Ixo6Zflj4+V1M6WiDEU3NMVDHBH3JPpHynxgzdk1WHGCia5jJrbkqS6quz7YImGq3XkjARK1tRcflMb3NAx5SMREYIQWTQWvI2GuTb+qulO0blCs/P8tNab1ur8r77AxVpN0HZdG+7QICAho/ag+zrE+2ULse/kzttOMXpYX+UcXJSbfkW99Llum1VEsXMpAuasDZ8snWdqqCIQJgqpdApFqWFf2aVGC0f8KZMGD3bwX7cX1nyLZ/pJAdGZMlv/iDj9JM74zSYesCueuhQXKvi2/ke5xtXVP1Uk6oY0tFtH1Xpf/VUcpbOwwU136+Ljs0LFRq2D1batBGTqoliR7bBJdWvcqvR1AuGWrDpfq2n7XV/wCY2I8S9trzN3+MtG1DEbNrAkJ2z8oL3DvXKmDvfBEw1bA4wDRCA5hGNInMG64BTEOeP8AUM+VDBM4dBs/fvuEB00IRMD3LIsAUeR8w/R4UazCzMunXoSJgEgHTk5a2eoTUBG8xfN7NTLbXM7wKiJQIKQw/YCU4UpfKEG17PIJFNMimbCiCDufY3s72arZXsr2F4dUTlNPjr7kGGn4TJCuvo+sQ8mtoDWTZR4NrUl+R3RsN4VexPZvtoWy/x/AD49bMi2uTR9dDaguCS3T+6Hq7s92H4Qf9c9jWY/jMJbLFo/tMirRYhr/3dD8J1gnZOCJcqrvnpQBPBcgkKJkIMpFdHsHfdWz/yPbXDA8Q6V4T1KYzXheQSQBMpPrRzmB6mEVeXVlsVmge/2GAia5BAEx1V/USMNFjLuQt0Zqyf/aWYQBGHo3AQtMkHPHIgVNsKWLzFCiWV6CiBgNApboS8eznm4cVYK1dKiaejcYHO4PQZpU3Guhq1FKLquzXar5WT01elMbSb4kbGi7zwMtrvNF9WwBGHI3EApMk7HfJgX0Ur2KS1CCLiUpVXomYXAWuBRRggXEyPt0ThpYrfNm1alRTes83YKKyDi9p7JYgaeWbKm3nlSzpbh9d/PVpn9x1K21Sraaci0nqvSdE2XGNX0VzPc/KRovc71E31feqfMMwQN3/YET2jPPx/otvpBgbWKRu1rNI/m6JeWI//ZtJnfa6pLe2iChs9F+fG2d983XW2KY1/PF64stzriR8Ns8ocd4vN5L2/WicYDPhXEz45wfCsjtvDpC2WuWrbrrcCzpcfpgGAi31eDAzqrbuhwiY/nOJgOm/twAyZjEOHGQioEHDdFIxkVpGgBn9mxpjzBuWmD/oFgzn+uLCtii4mGUgLqgEhVlKqBRPRyEkLylHeowE3jbZuLg9GmtmemHqx7bo29YYbze4iM7MOXRvehF9Oxph+iBbrPvFC1cPxyDAOQ956XJ2XZWc3d7TKlIv+bnk4tzOKCyf5oFpvewwtA27b435nKRB90GMJQcoaG+r7AmrYIw2kBHs86oDprEa60Kyx+OUZY2MMKKtGWZ8aI9l491xRC8U1ieTEOZSgNwkGZRlj2dfqFZQ/pIc0R5FuH06FaeXhGP9WC/89M4tTGxzE8MbmrHXcwP92R7Mno0v2fUI0EwETCJgem4BkwBKNmrnMXW5b5VHeUwyA01WEl3f5h5K+eERscrrv5mobu1dpQw2HaeK9XqvKDGA/kP90P9MOTsbNqLMoPLA60OUrod/V5osPiY/MNRLuqpjgXRJI0gXNYR0WXP2cdvzUIRgzX148xwAJvozzhqvEwd2OJtBasqX2vSOSnZwaLb87Ex/hcmSqyqbdSuVTrvHyB33vRlvd7jp48El567lQebDlC6H/1AY/3la9tdIP+mmrkVSg9YqiV6TSumyFvx5ZM+lbN0b/LruAzsh06qu9+5p9r8DpgICTNtFwPSkJQImsWqrRMAkAqZaLiH7hgb89OZcsq4iizYKud/P8HCGbNwo50iwl6trwESDbBq00hA7meHVLKZsH2R4sLRAs35SvdCQmFRMbgyvFhJs8uoKMGkP4oX8KBrCu7B9me2tDG8lRgN4ylR5k+HziJozda1KqP0S4BKBBQIMBBpItUXX/SXbs9heyvYOti8wPISje/1vcEm0xKvbfhhkIpUe5aKRqpAA8DyGV6d9xvCWnJQ3RioiAqnP8pzT4wiASVBvjmIeBEzaFnl0bXWl4KS9JQUT7asAmE4z/OscWQ9+xDwImEQF098A0x88YGqu74XumwMx7mQUlt9MxVnfPLglliG5UIkyZQUqHxKQQX+lrriHYlk5QjJkuOyfBz3LZIw5EYEeWwPQeoUXGiz9j4BJTwN7dMkKzQ0Nlnmg5SovdDL0R5/9YZh5MR7r7TNgFFSE0Ew5Smo4UFVX8FDsRnAhlpqlYMCBCLRd48/b5C3VPOay5xswaVdUjrxBUIa0m0NM8RT2LO4wsEq2nX4uJnzQvtCk97cEZHbf4JfbbYNffs9tgTkDD4anTD0X57PkRsq1jTaZhptsM2atskrts9Q8qdZUSx7JZQ2uBBa8stEho/vPxkmDZl2Onz/jcvyeGZfj7Ceci4ntdyistPPmADRdoVEtcdldtGca+8SndT9EwPSfSwRMtQOYZmgAE/VMTsVkxw3TRzPmXM4OZf70b2SM4W3NMOV9Wywe44o9fwbC7FgC/O/kISNBClmZuuYko6bFvu4rpRXIT5Mj3KMQ1qeTsF83GL+OuoPhXc3xTrPLeLPhOfR86RKGvWuKXyffxuGNIbhtnobk6DI+H+ppFbu2cmUlMpIkcDJNxc6lAfhhkBOGtzdDb53rHJTj4ZIppwYTzuE0pgowTX8CwDREGzA1NsKX7cww8yN7LJ/ogaMGYbA9m4wI90Lkp8ihklY+FmBSySuQlyxD2O182BxIxOG5wVje3w1zOtljXAsrDNMx487DIPaahjJm7Pmw5ICLCJhEwPT8AyYtWLJR2+atM5+JRLZ1+i35XtOBlDi58pOTPFXmK84pPU7qKaMcRsnTQ9541B4SRMmLdG6liHF8WxF47Uul49blynOzbsh3fBYrW9VeItNtqZbqNr0nM3gJ7O+r9vIBOFLX+6TZq41vV0EvQ63cJdovAmSkWiIFGIEm9hqkOz8rkh0bFyK/8qORwnz5WpXthqkSh50f5pkYtqrpGUx2dm6miLz1VnnYzWFKj1MLlNarjyhOTb4j2/5ButSg9T2pbiNIdJuwj/sypOzeSTe8xa9LG9K98HCJWgRMT6tEwCRWbZUImETAVMslDFhpwN+J4Yf7k9lewfC5QK4MP8ykd83TcLOuB/naWST5TFUWCalbNjM8XCIwQQqsXxheMUFDWMpnCmc7i+HBjmCTV1eDYgJ1BEcoOyiJ4cEJDbMJkpFiZyrbAxjeRoyG7y2ZF8smTwCbBJfo5zma4XVh+CH5MLansf0nwwM3UmlYs+3N8JlLBC1EuFQ/W4BM2nZ5lJFFFpWCjSWdccoNInUawexPNPee7CDpnD8ryFQ9g6m6gknbIi+Vqd8KJgEwESSjefx/Flr8p6qXgGmRBjAtdEcLfW+8ty0IU87GYINDOoyC+fwlspuTqiofGsBeXnkPEmUF0gqVcI3n85d+NkrA4MNheNPQH82Xe/HKI03eEwdR9B53vZ5aSibKB3JHYwMvvLLWF+9sD8bYE9FYYp6KM9758E2RolBWs3ALsv5LLlDCKqwIK2+m4cujUei0MRBNlntDR9ezCjDpPeX784wAE1V8vqJ5YLr0I7uo4hmnPHM2bLBNPffrtXjLaWejnSeeiPSZcCLSb/LZaM951+Ltl1mknt5sl7lqz63sqdsdMj9dZZXaobaeE1Q+qZLWRsGFH292ypjyk1HSim/Px54Zezr61pfHI+P6HQore3tbIFqt8tGyxHPnf60nAqb6XiJgqg3AxNvkzdRY5dFHygeafD+LyZyDGgN0TDCwuQlGdTDHzA/toT/JHcfWhcHBKBXRQUUozFOgouIx/NhqWJTvJC1SIy1aAm/bbFzdF4O1873w7ee2+Kz9dfRsdRGfdrqGSYOtsfZPL9w4F4cw3wIU56tqfS0PrqsSZexjRPkXwvhEHFZ+54EJ71vj82ZGXCYUASDat9GMBcaz+ziZsb6/3w/CJTsNVHo0YBqjAUyfawBT/yZGGMnej9mfOmDFFE+cWB0Ox4vs/fApQlGGAuWKx6BLHMwrR3acFAHWObixKQ47Jvnjj/fuYMpLNhjdyIJTtFHu0hDGjDsXY9nrokypbzWAaUY1VVZdn20RMNVuvfiAqauWGkcDUDjI9AZvs7a8FWSkLiL4s66zXL6nX4ri3Gwvle2Gc0rfy7+r4zw/jYyMfGQWkwCZlMHWPVWep6YqLVfsVpyZelu+s0+idG3nIql+S7VUrxmky1py1nK8Audtreygtx+EOs+8q2UuCesgmENQZ2U73hKPy11qz//d9o8V8iMj4uVnZ1gori9YLzM3+EZqZfhxmbVhjd9MRDlXsii3juWhlkOUnqf/UNqsO6G4MNtZvufzBNma1+VSvSaQLiUFWDNeabbhTc0a67PF4NPqhwCmLZ8gfftQxO6eiNA9s/MC980TAdNj1AsBmAY1RvqoDojVACav376JclskAqZnXVWAafHuyA0LgmINZvGAaQoBppbsffoHwFQPzpIImOpt0SCXfv6kuUE3tr9gey7DW82RKojevU8DfYIyNDSuawsybThD6p8IhrdNI2WEMLQex/AZUjPYXsLwSiyy6KoPWSraw2KFZi20v2TzRxCMoN56zT0gFc+HDJ9JVJc5NbVdAlwScr/o7JFSi4b7g9mexPAKNEOGtzikDB9SwBCkIFhBA3a6/4KaRIRL9aurK5kKNfeNAK8zwysK97Kty/AgeBjDn/PODH8WnmXmWHWLPFpHdcCkrWCqD4CJoF0Cw8N/er2oDphI7UiASVQwPQBsFmkG6Avd0XK5N3rtCMacS7HYeScTVpFFCMuWI09aDoX64eolZfk95JaVIzxTBsuwImx1ysDMi3Hosy8Ur633Q1N9L01+kqaXPgFg4loDepa6c0qmBuzvW6z0wZubAvHFoQj8fD0JR9xy4J4oQb60ZoCJQuBTC5WwiyzGRvt0fHMqBj22BqMV+3UbaIMtvVrM96ljwEQVmydvG5Am+dAxuvirK/55vxxwzly/0S710KqbyefYvrjWNvUkex937r2TtejQ3ZzxB+7k9Npqn9l2uUVKjcKya1JhWbKm7kll71wJLJi+wSF9x/dXE6xHnYiK6HswPP3D3cFlXbcG3iOA2Eg4P4u0zs/Tfn6IgOk/lwiY/nsTCBBUTELT72mgTtk6XzNWnJKJwEb/hsYY2MwEY9pb4Id+jtjwkzcuH4qBp1MWUhJKIZWoH6pEfZK6VwmUKypRlK1EbGARl3V0eH0Ifp94B6M/sED/t4wx6mNz/DbtDv7aEQp3p0ykJ0mglNc+7BKK8qYIeqXHlMHdJhMntoRj4QRnjH7bEp81vo6PmKucyuhLxoyDdJPYMzhVo16awdjez1z6NwjzT4CJzjEBpi+0AVNT9tpfN8d3fRyxeoYnTq+PwO2raYgLKEZJjhKVj8HYKN9QXspeU2QZvEyycGlFFNaP8Ma8NxwxvrEVRuiYcXBpBHtNIzj1kgV7Nm5qbP9sNOfI9oE8qRepRcD0fwiY7oMTjSqHYA9BJrLKW9m2Ur6xm0S+/4scxeV53krHHfsrQq0mSpP9Xq/JXhJkKo00aasONBqgdD60QGlpcFxxeqqzfFfvBOmq9mVS3WaQLm3MQSYZ2cvdVzF1qyeAqdvf4RLZ4q1uD6lBm/vKJe7vd/dWy46OyVCcn3VHef33nXJz/SlKq1U9Sk0M20aaGNbo5z0BLqlDbfurvc/9orTecExxYY6X/MCgTLlh1zKZwUv3OLCk34JTL8nWvs5BlgeVX/8v6qWu3LXLN1C/BcUGDWDa8CBgits9EWH7ZucFHZhnFbRfBEw1recaMPXjmwBTBgeYeiFo3nB4L5gQ5bZo6hH3hVNFwPQMK9JQA5i2LN7NfgyKXSECJhEwPVFpv3tfGK72Yngws5jtY2w7MbxihGzlSDFUV9ZQ1YesQv4SqQpo+EsgbCfDq5coi2QIw4MyuhbKe9nE8FlSpKCgwWyB1vXUtU2ehO1chrd9o/UZMXze0B9sf8PwWURd2KbX2OZM1eD9eYZMwrmjuWEbhgdoZM3Yn+3xbP/E9lqGh4Z0b2mQTnCC7jfdOxEu1f/Wfq4KSr0UtkMY/nXlEsNbH5JK7Vu2B7FNP0/SWSDrcPo/8dOGJP+kYKoOmAhMV7fIq0soXVPAJFrkPQwwtTLwBrsmzL8ahwOu2XCKLUZsvgLFigqoHhIQT/NKqbISKYUqeCaW4aJfPlZap2LCmRj02hWCV9f6oTEBAi4/SdO1AZio2WsgpdFr6wPw+b5wfHc5AXvvZsM5vgy5kppZQpGCKb1ICaeYYuy4lYHp52PxEbvu+2CDU01plFMvEGBKLVI2jMuTvxSUJu1yJ7ak342QgklnvXN/Pe6RveyYR/aKk945i8/65H5/xitv5HG33Pf2385+ZYNN+n9+At2NL2nolVza3D+trI13SlkP2+ji8ce8cgz1rFJtJ56NTe17IFzdfVtQ5esb/NFmtS+aGmiUZEu1+onOjgiYnnWJgKl2ANPfLdvsNH9vwylvvuGUTGbozxhz1m8Dm5pgfHcrLBx/FwdWB8P6ahLC2NflvGwZVMqKh6pRn6gqAYWkHNnJUgS65cLoRCw2LPDG9yMdMKHvTXw32gEbFvvA9GI8okIKUVygQsVDvqf81+Ks5FJlCHfPh+WZROxaGoD5I5zw5Zvm6NPkOgd/yB6PLO0msudvCruHAoCpTcA0oJkxRne0wA99HbF2lhfOborEXeN0JISUcOqqezV7DwRX9yrvQVakRkpoKVyvZODUknAsH+COmW3tOJg0RKNeonMwijHnMqXo+TVJBEwiYHrhAFO13qhRMRHoIas8AhgGfB6T3LBHpfzIyEylySIrtcdpXXWsS9/i5OA2ycnJdAYe+vNMsvP5ZsoAi+5K/4tfK2/t1lOZLDgvP/ylr3RDlwJOvbSkIaS6TdnHa8s/PgeZqq+tLvZJGzB1rYJLZB1IyqXlrXnARGve8Um57NhXufLLP/ooLfROKmzW/yS13vxJuole80ftj1AEl6RJPq+pY2/3Vfld+17ttGOv4vL82/L9Q7Lkht0qZavY/TFoxT422Qqyv6bcpfWdNfdT2xbv/wUudYUImJ5eiYBJrNoqETCJgKmWStuijAa6XRh+wE+Kgg1sX2Xbi+GHwsJgta7VS8KQleAQDaxpyEpQhobVpPr5nuFVP70ZPtuFQNN0hlc2kRKGBtuUB5PD1G0Ok3At9PiCwoP2OZBtG7aPM3yW1EzNNdD3WRp+k40hvcHmeQZMtHYCB/TzLqmyaCBOyjm6ZzTYp3tI9+sAwytd7jA8lEhmeNBJQE60xXs+WjjjSs19I0vLRIYHNnYMD0cMGT5zjMBiX7a7M/yZeBZ5TNUBE73ZT7DIIwXdPymY6up1UFv1SK8X9NpHuXL/BJgEizwRMD0AmAhk/O7KDdJbr/DG53tD8LtxAk545cA9qRSpxSpI1ZWcBd6/VWUlUCyvQEyOAg5RJfjLLQcLTZMx8ngU3tkehDZrfNFwmQYw3e9aAExLeKs0+tqvrPbDR7tCMfV8HLbfysStmFLk1DBzhABTBnudzvEl2O+ShblX49Fvfxhe3+jPwY37gInWrVv3gMkjqayrby0AJqFicuRNfFMkHRxiij+4EVLwxbXA/LFXA/PHXQ/OH2kUXND3in9+91PuuW323cr+z08el4SSxmy3Ybv77bji/pbhhdNO+eSuX2OfZjbrSnzswMMRFT22BXFQsiW7941pX7T3/r6aTARMz0OJgKl2ANNUDVSapgWYpmsgB/39txp7toGMCT5lrnE9pN0NzOxrh9VzPXFudwScrdKREFGMkgIl1MpKThFTm0XAqLRIhcToEty5mYbj28Ow6icPLJzmjFU/e+Dk7nC4OWYiO10GZQ3z8Z54HQUqxAcXw9kkDac3RWDlLA9M722LoR1M0bexEfoxRpydHFnjfcvBJZv71nG1CZgGNjPGmE6WmNffERu+88aFrVFwNc1AcngppMVqDszVtCrZ71Nl7HUlBBbj1rk0HPk9FIs+dcHkltbstZhhMPu4BJhGcdZ4vO3fRI093tT72VIPv67nuUXA9P8KmLQgyloNRFlJSqaWkC5rweUkybf3UspPTw1V2hieUvtd+5EgkyIx4K30dK/mj9hSnVIvk7Yq/0u9lK6HxqmsDNYpT0+5KdvxcTrBLPr6Ut3mkBq8zMOt+5CJXc+musgTEiCN1mNrwSXpqrbsWl+CdDnbtN4t70F2eGSh8urPASo7wwtKl4NLFB4nv5B4Hq+xDbKJiUlDSbxbe3WM8+fqoBtzVc4H9ihNFtopjoxJkG/qWU5ASarfgleWCWePg0tdtO6fCJj+DTCF75udFywCpseqFwUwZWoAU/D8EfD+Y1KUx6LpHGDyEgHTMysBMEVuWbw7ynBBUNyKWZXJImASAdPjlwCY6GcOyvih13LKQ6F37pOlHGXehDG8DV1dwxhhwCrY40mYKns8spUjIEO5RaSEIEj2PtvvMbz6hwbXCzXXZMV2EMNb0pUydWv5pz18p7VQNhTBL2e2L7O9he2f2R7D8Bk1ZCFHap9noex4WiWcOQIHpJqjzJ23GH4wPpypsjQkBRdBQ7q3NNynYTpBQdonGrDTvtWVvaHYj9eVmvul0Nw/et6SWo/ytMj68CjbaxjeEpLADmXAdWF4xZ5glfesAJN2BlN1wEQWf3WpYKLWzmAiUKcNmEjt2EtzDbRvooLpgdZ9EDC9tNIHA/aHYolZIi7658E/XYIciRrKint4CF9CBfuXeZJyhGTIYBZSiJ23MjHvGuUvRaDrlkC0XuULHT2vBxUo/wXUEGAQ7PbYj6Ruab3SF+9uD8aE0zEwdEiHfVQJMktr5j9E689iP9cjqQxHPbLxu0kihh2JwFubAzj7PR0BNtQDwGQpAKaU2gNMVH6pksZOsSWvmIUWdr4elN/9WlB+T+OQgq4mwQWvX/XPb33aI7fhf30M96TSRi4JJe1uxxW/ZxNZOJZ9jAWH3LL2rrRNtZp9JT5y0JGIkm7bgtBujR+a63ujoQCWlmjutwCWngVcEgFTrZQImGq/BUWTADhm6thhuo4tZ/VGcIPAxkfMFXze/DrGdrfEL6PvYPsiPxgdjYPv7WykxZehrEiFcnXtW9QROMrLliPEJx9WVxJxbGsodq8KwLFtobh5PQmRwYWQlKof+v3kvxQxM1lZOTISpPBxyIbRgVhs+9UPv464jfHd2P156QYGNDDGYMaEAzETudwlGw4qCflEPGh69D3QzjMihRCd5dFagKkP24Oam+CrNyzx40AnGM71waUd0XC3zERqdBnk7DrxGPtQrr6H4hwlYnyKYHsyGXt/DMKvH97FuCZWHFwiuDiUMeMg19eMpeZ5xauXqs7NiwmXqEXA9H8CmLS7esbQ+jchW9dRk8fUklMXSfVb8X++b3Cu4vLPbmrH7YfVvhd+Lg82GywNt3rtUXsaaWLSpCzg2qvKu8feVdiun6O4Mv+44vDIMPnWD9SyNR15uzmDlyFd0ZaHNuvfQJX12zMETA+opjT7sqErB3O4e8/ed+7+37fG6wb5vkEKxfk50SqbjdeVXmeWK8PMRsnDLd+MtzvctKZnrigx4GVVoutHqlCL2Wrnw3uVZsucFKcmxsu2f1TKQTiyxNNrxivKOOXSm9XunbBP9eA8PdOuBpjWPwiYMnYMQ/yeSQjfPycv+MCPVkH7f1rgf1AETDWp5xUwFWoDpsE8YIqb+tH/2DsPsKzKN4y/7m1qOytX49/OTM29czQtTbNMrSzNvbfiXqngttxbEBQRFBeoKBtl771B9jcZPv9zn/ccOZIJGvJhnfe6ngtknfOO7/vw+XHftwqYTDhEwLRUAkyLx/iEzRpaFP1LV0oEYOpdT9inewCmSni2VMBk8iE3VqGKeYHxxi4ADZQzuxkPkEdjH81MNIcrg2JEbrCi0QtFARq/sLBCngvAmAxjoIhBkxrN4u5CjWAc2EARA1UWmrOZJp6XrEiQ86RkdYc7401tKHgmsWJoBmUH8idldUJF5NOU95DPHKAm+lQ4d/gdogPj1oZo6sPO8A/GAacb4zAC8C2LceWaDAVNfRbVKnvJYFgv7SMAL/K0AEiOMQ5/pzKu2OvK+OMWZwPKykeZOyYDJgDPkoDp7zKYTGXNKAN2PP9hDUsDTNXLcZ0efFR2wNRotht1Mvej6Sej6eiNW+SfrBWVSYWlNMHyCwFo8skjJo8OeqbTQod4MX/pww1+1NSMQxomA6bJiiovwCT83Hoz3KjVMh/qvyOY5jvE0amALIrLKjtggtrJTbj/nW6pNOlENH28PYigpGk4x70YME18xNk/ZQRMV6Nym7uVM2DCsA/MrHbYO73WXo/UOns8Uuvu90qrfcg7vcYBj/R//MJ6JSqn+tWonCYXwrLePhmQ8cke95Spqy8m/DHRJsr5qz2hUe3N/TXNlnoXYb2hWqqKNZggWypWoC2eCpjKdaiAqfxLCZiGsjP0bRUOmdBcl23yRBVT9cPU+Wkr+upde5r0pTOZz7pBdvuiyPdaOiXFaEiXVyDarpXnQJ5dbo6RosNzyN0pmU4fiSKrXWHC22jyuJxCCcJzbP4jAFvygDIrPVFPAW4ZdGp3FJlPu0GTBlymb952oF7P2FDn2lbUuYoldWfHqT87QV8K5w4waYgCFg2WVGGl7cH9ABPynQCZOtW1pAEv2dJPnc/TklHudHBNCF23S6L40DzSax5MxYW53UrQkf/VW3RicyStGO5JI/53nvrUOEEfMUth3y1FJROs8T4Rc6WKrfH+zWBJLhUw/QcB06J7WOVBHQOQMbMhaabU4SojzHnJ/4zaTR/H6w//7GSwX2hudNr4ndFt95teXjtqlLKsVfA16S6rG+jPr+pstJk2W7/3+zO6TX2SdCvfK9TOe/G2RrSdayjCG/HayIRSwp6KWIu/qIGac5gz7zkOlwCWsP9znhY/p1vzYZHuj4EJhhPTzhqvbjMr9LMboA+53CI83KHMcCnJy6uuIfLyq4WBpz83umxbYjg544xu56BY3Zo2Wu3CF4tEtRQA07R63LoQCq+S91qRa1SpqmyAKXD9sDTfDaNsb67/cYyvCpjKNP41gKkPB0w3R/Ukt7FfBl2fMHjT1QkqYKrIIQOmoKUT1gQvHuMTPmtoUQwA09cqYFIBU5mH0h4P/QLAC1ixjWA8F8Wacbs2NIJzmWmVPsoGK5QQgAzyX/C7MJ6ttEio71ixnVxTxhvUmFc7oQYxDs52Mm65BqUQco800txMBSuwprLlH5rGUEn4Mq7c+VOo+YwrO3ow3vhGPk0DVtx0f5yG3MzHvaOZD9VcC8at8foyPs85Qm0Syopx60NACJxBwEA5d+nfBpduK94qy9T3Vd5zlCFTyTym84yr1VYwnjsG0Aig+grjZwRKNzl37FGMauzeFnklAZNSwWSKM6jMbbsfYFIt8soCmBrPcaOuFn40xy6GTvhlUFiajjTGolLzOozIMMrKJ5fIXNrllkazTsXRl7tD6b3ffenZRZ5Ue+ajB0x1p7tSi6Xe1Gd7EM06HUs2fpkUdctwX2s/eQAwIa/JKz5PVG7NFOb/2c5genPVDWo816MYME2oPIDJ9REApkc5rsfkPuEcmf2mrf+tL3a5p8xc5hi3a6xlxNVP/wiKb/O7r/GlRV5UH2oxcf4u4tzvAKZ/qnhTAZPJhgqYyr/+DjBhDfuyk6JNGgDH+1UPU9v6R6nXizY0rP0Zmv39Ndq5IoAu2cRT2M0syk43lHsOEl4roGJKT9VTRFA2+VxLJbdLycLbNIoMzqEs4Tn5UamXYCGXJ7wORQfm0pVTibRrWSDNHXqdvm/jSP1eFNalvhV1rWFFPYT1+ZjZCOfOVoQSjxIwda5nSZ80s6XRXS/Q8p896Mi6UHJ1SKKE8DzS6x4AMGFdtYWUGqOlG07pZGkeTouHudOw1xypR3Ub4XrHqJ0EmIrVS8W5SypgUgHTfwMw4WOSJdycJ3nW0LR6oi2cOOflb+v1Wz6O1h0cZWe0mzdbf2Vrt1z3fU8iQ6gs62tw2vKK8cKaIYaTczfqD/10Vbfl4wTtsjfzAG3E60yvxzOGFsggpbkCnjxiiHIXYGouWeMhl+ppDpcAewCaFrxEupXva3XbBqTqj/3mmn9h7Rajt9V3xnCXt1J8feuV9awBROkDz79cEHS6d4Hb7ulG+4VHDXu+Ddat+8ggXh9nbXp9ft2ZjSXw9vLdqiUVMKmA6RGMfzNgclUBU4UOFTCpgKkcBhqPaECib4O/eEdjcgDjipmtjDd9gxlX1QB+VAb1Eq4vN6hhlxYo3SeyldBg/ZJxmARogSYr1D6wlXtXqP5CjRfKnPGMoxuMN4xh2WVKaCGrmHAPsP0D9IJiB3DlKONWcWi6w+YPIAZ2cujvPI42eXL2EtRLeL14kfFz151x5cpkxhv6yP66wDhoi2UcRmBtTKUceRR7LleRogpLvJVLCZwe57krFTjYT+RpQSHpwfhjEqo15KiNZMVKxJLnvbwhkwzaS8tgAmxXPl8UluO6PEiVVDBdZlxtKmcwKQGTapF3p6YpANOYy+LbJnPdqcdmf1roEEsOQZkUm6EnYxkakIaCIuFrkWGUQ1tdoACKof5/BNMbq2/Skws8qCZyjGSoNEVR5QSYYKNWZ7orNVviTT23BtI02xg66nOLglP1pDOW/tfyRbdvU7qmgG4kaujIjXRacCaOBu0NpffW3hSzgKpOdeXQp5IApisATNGPD2Byjc2r4xKd08o+OPPTXW7J883Oxh358XCY68dbAuLfXuFjfB55S8IaV5Eh3oR7wKWKVi+pgKlchgqYHk3JGUxDJMA0tAqHIljLPlVO3LHKe6/6IWrb4Ch93OIEjexxnpb9JlvlpVBilIYMDwI5yjiKim6TTltAmekGSorVUFxkrvg2S/i38VFlLwkvU1AEJcdoydspjay3R9DyMZ70U9eLooKoSwMr6ljDkrpV4XAJCp8vxewle8lqUAmXHMqw/vcHTMh4alvlKHUVrvt5Szsa0/MirRLux9IijDwckykJa/8AawF4Buu/xHANuTum0sE1oTRvsCsNfuUMdaluLdrxATJ1FwETVy99LamzygrNHvdSAdN/HTBJsELMY4JyB/OVModEFU19MSdJt/xNjXZLXx/dsbGb9efXDjO6Hn0jN9jmyTIomVjWjT2N8r0t2+S77Pw5/+zyzfpDo5x1G7pEaxe8lK8RM59qi8opXFu8h0XN7r7PRwZSSqyBqORqKqqXxAwk0cKvEc+oWvamUbfp43jj4dFuxrMr9+S7H5xQEHyxY26o11MPctY0boefLfA+0iX/+s7xxrNLdxsOjfTSbeicJV5/pnC9qXU4YMIeAC7Nf5Hfq1krKZ+qRfF+mfwcmaLuBZhepjyzVyhj6fuUuKo7Rfz+JQVu+D7N1/xH25sWKmAq6/jXAKaPn6Xwr9+lm6N6kftvAExDNrlO+EYFTBU4OGAa3zNo+YQ1oUvG+ETMHloU82tXShzUSgVMKmAq65BtoRoy3sQFmEGTf6FQhxm3Joth/C/20dA0tXpJbq6iuYsmL5q9yFI6xbiVHCAMVDDI8gG4aCwV4Bleo6AAGiXUcsbBDfJf0KCV7f/kTB9TNd5lZRaUOoAqaGjDIg75NDMYzybqJNSrrFjVITfcHwfIpFTMQYGFfcFcoFSBYmUM4xaGaJY7COXJ+P4AuEFB97jCpXvBJMyjQKr8EmWQ5pqv+Lz8tYWKNXhcVU7KPCY8t8D6ECAbSsTjQlkINY3x8w41InLUcFaUqr3yPO8lM5hkwATAhTMJ601YcMoKJjz3yM+Hplj/e1nk4TGD5wgAJjz/qYDpnoAJoGZ8cQP9qfnu1GdrAC11jKMLoVmUmG2gwjK4GekLiij6lkH4nmyyuJJMvx2Ppt7bg+jVlTeokfAzq08HzHLh9cgA03V6ebEXddsSQBNPRNN+zzTyTdRSjq6wVAUWAFOGtoD8krV03O8WLT0XT98eCKM263zpmfmeVA2AacI1rqqpBIDpUVnkPYrhHJldxzkyp7lDcGavPZ6p083Oxh4bcSjMv8dG/9TXl3rpnprlRrUnXaeq41ykOV+9GyzJcEkFTI/lUAHToykZMMlwZIgCdHxW5RT1YjaiVd677BC9W/0QfdT4GH329imaONCZNs67SQ6HYijYO5Oyb5XNRvRBB4AILN10mgLS5uWLb/Ohhn1E8qUC4VoZSXoK8sikMwdjactcX5r02WUa+D976trgOLWvfow6VLEULQQ/YScVAObu3KWyQpiSgAnnF9AKuU4ATO3ZUWpf7Rh1b3ScvnrtNI3v60S/T/Qmm63h5HUxRQRhDwLbCo23KTfDSDGBOXT1VBLtXhpEMwdeo4Et7aljtePUmh25A5gGiPDs9F/uUQVMKmD69wGme0GWElZ5mC/URZNr8iygOc8UaVe3jtbtHmqjdzCba3DbP8AY6PBmTuDZJpaWlve1QXFycqqeF+H4TH6Qw0f57vt/MtjN36rbOfC6ZvlbWbgOQJaYNYSMI6wx7kFcZwn+LJLt68oLNLUoLnHesnrpJdLAGm/u08J+NxH3XYRNS18n7Yau6fr937sZ7RftKXDdNbUg4HTfB7bGs9tRN99py/v5F9ePMtgv2qY/8vM13ebeKbqlrxaKZ2xKLREwaUWo9Ry36sM6iPvTSmHj919ULslVOmCKXPclBZkPT/Pb+KOtv8XoMb7mP6qAqQzjcQZMWe14ATAlADANepd8f+xFnuMGBrlOUgFTRY87gGnlJA6Y5nxbFPNrt2LA1FHYKxUwqYDp/gO/V0BJgj/ieE2oXoxbQiELBWoCf8ZVQlpmWviiLDTX0ZiW7fGQpYRMJYCJEYxnt+D1CA1pZLegKf0k43lMHzHetIYFGyylLjHe2Fba5JkSMMkqJsAUNN0DpXuEddgSoX5kXFWBBjKs/wAGH2U2TXkOZRMffUK8VjRjPPOrt1DDGd+XzYyrRa4JFcL4OgBCyADwcQEqSgBUqCglRMKcABQ1isqVKk/6t1Z6q5OqJHySlU6PE3CSQZsSqCLbCM83sK6UrfIAd2D51kao5oyfmUdl+4afpwRMbzEOmKBgAmBSWuTJgMmUuW24PtYtihUDJlnBpARMqkXePQETrj/JhZ5d6EH9dgTSygvx5ByeTak5xlLhDAYAE+zoHEOyab1zMv1iGUXdtwZSyxU+1HCeO1WrQMDUZbM/jbOOol3uqeQZp6H0vIJSLZkAmDJ1BRSYoqWT/hnC/BNo+KFwarfej55dUPkAk0t0bnOPWE2lBUxbXFKqHPK5VetUYEZj++DMV2z8MnrtdE8Zt/hc3M6Rh8O8e2z2z3ltqfftJjNdqQb2DxBn7FU+Z/zbVIolFTCV+1AB06OpQZLSRglI7qhpqnDY0YUdF1VM77BD1Lr2Yer+kjUN7+pIZqPd6ZB5CLmfT6HkWC0VlEHlWdmHIa+Q4kLy6KpdEu1ZGUwLhrvSd+0cqddzJ0S4BMs6gJ+P2Qn6QjhvX9+xj7vbFq88AVOHGseo15PWNPgtB5ry6WWymHaDbP+MpBvOaZQa9wCASXj9ytcXUWaKgcJvZNOl4/G0Y6E/TfnsKn3W4jR9VN2K3lcBkwqYmAqY7pnHBMABRQ0A06TqpJnWgDRmLVN1mz++pj824U/DJfOJBk/LPvoQxxbRTk6lngtAJm2M1/MFgWc6G5wtphqO/WqjM+8SpzVrViiqhKbXJ+2MJzjYkvOYFklgZVGrcgYrJQFTC8ka73luhwe4NFtSEC1uVahb95FW/+dXwUab6ZYFzhZzCm9afWoMv/BmVrRTIzMzs7LYYVQJd9hYS+ew+kWD/dJP9SenL9MfGHlOt7VPrG7FWwbt3Ge4WgyACeuAvKc7eVQlbfFMfV5MXSpgelRDBUzqKK+hAiYVMP3DoWyoItOnNeP2cjMZb1bCdgnWVWhimvKv9ZUlN6XRcAcUAhxCQxo5RbOFGsyK7fEAlaDwQU+qEeM2eYAZaMBOFGoj4xANFmzI9zG1KkGZTwOoAEs4ADSoyNDchkJrkrRHbRVzlJvIjyqbpryGbMcIIAYwhjOH3xugyPpaqAlCrWHcGg976se4igsgEethyoysh91LGSgBCMlACXMBQAI0w2ML+wybOJxnwNxkRaVIn0uX1iFT+j58vwydDOzvYZOp16EsayTbQmKOgCWAOHhcbhdqLuPgEcpDAB+cGZwd/H+ovFV79wNMJTOYlBZ5plhnXFepYIKVZknABMCuAqZ7gpoJvLFfVXi/6WIvMXto7aVEuhqZQ+l5+WXqf+kKiigi3UBngrJprVMS/Xg0kjpvDqBmy3yo/lx3qqIETFOvKap8AdNLwv133uRHY6wiacf1FHKNzqPknHwqKKV/CsCUpSugoFQd2QVmivMfeSSCPjL3p+cXVgLAtMInZvC+UJtVFxNn2vpn9roek9fcJ15bRz5XHrGaKt7xmqq+idoaASm6WkLV9E7QlGr38qjGTre0+kd8br107GZ6m72eqQN/d06cMd0ueufQA6FXum7yS3ltmTc1me1O1WWAM1YqeX3/CXxUAVOlGipgejQlA6aSoAmWeXIeU29JxfQeO0zvVj1EHRpb0pfvnKZJA6/Qpnm+dPZILIXezKKcDOPjDZluE+WkGcn/Wga3xvvVk37qdoH6NT9JHepZillI7UX4clyEQErlUnkBJgAdgJ1eEmD6qMox6lTbkvo+d4KGvX+WZn51lbbO8SWHfdHCfaZTeoKO8g1lA0y3C2+L9n9p8ToKcsugswdjaOOsmzS+nzP1b3aK2lWzFPcY85QB00DJHm+ICphUwPSfBEwKiAH1zGwpI0lUMdWhvNlP52lXvBOu2/75Jb315O0GJ4sx+b4n20PFVJZ19vLyqgHVj9HjwDf5pxds0e0a5KNd2yZLO69pvnZ6Q9JMrcvzn2Y14TlIuLfFrSTIJCuZymHOJaHNQskab87TlCfa4gk15ynSLGxeqF3TNlu/44toveV4R+P5VSsL3fYNMgaeeis31OkpzKcs806yM6uru7i+qc5xVUedzcyJ+n3DD+k39gwWbQfnPsct8RTWeGIWFizw5LmbKazxTH5eTF2lA6aodV9SsMXwtIBNKmB6kPGvAkyD3yW/n3qT1/ivglynDN3kOgWAabAKmCpoADCFLB3fM2TlpDVhS8b6RMwZpgImFTA9yJCtytAngLqnM+MKoJWsOG8kkfFmdmVo7isb0mjwAgohQwkWcoBFABTIKAJEgj0e1Et1pIKKSba9glrmZ6FWCWXJOMCJZrx5L6tkTDlPWaEFkIBmNgCYo1A7hZon1HdCdWPcNgxzQkMcvydVZps8Wb0EO0ZAP4Cx5oznSfVjXJm1iPH8HcAFWOMBbsrWeKZUizzI+cRbGSzJUAkQCAAF+wlIBGAEVRb2NlqaJ/K2AEuhWAuQKlD6GFRc4YyDhBjp+5Kln4Ofh8cCYJOe3a1sqgxAuLSS18ogzSNZmjOACR6bUA7hcQ2oChtFPE9BbQlwUt5nXmmRB5AlAyYoOgGYrNlfM5hMtcZKwKRUMMkWeWoG0z1Bxh3A5CI29qtNc6Xmy7xp4J4Q2nA5ia5H51KGpqBMDTBdfhGFp+nJPjCLVl1MohFHIqjDJn96aak31Z3jRlWmXbsHYPqHYEzO65EAU+3p1+lFM0/quNGPfrGMoK3XUsglMpcSsvJLzZGCwilbV0ghqTqyD8qi9c5J9NPRSOpo4U/PL/Kk6rimuE6SwsZkgClhpm1AZk+3mLxmvolasUHmGQe4pK3uk6CpLXzsCf9k7dNCPeMVn/f0hfDsJ47eTC+z7Ul5DPPLyXV2uae13OeV1mW7a/KIJefil/9sGWHV749Az/fX3YxrvtjL0Fg4EzXkNR139c5c76iXTA2WVMBUbkMFTBVTMvAYikwmoQAUABq6suOieud9dpja1TlKfZudpJFdz9Pin93p0IZQcj2XQvHheZSbaaTCMuTtVcaRr71NiaEacrZOpC1z/UTw8vkrp6hDQ0tqU+3IHfVSH1G9ZFcM4qR1GvQQ8EUJmPA+8pz6s5N3AFOHqpbUta4VffKiLY1od47mf3uddpoF0PkjsRTkkSHa+eWXEeoV5t8mjfA6hvwln0tpdHJHBK2d6E2/9LxIHzc9SR9WO3YXYPqkBGAaorhPU5/TR1kqYPqvAyZUi7+qZfBxZA8hCwjQB/BnWr2CvNnPZmqXvxOt2/apk8Fm+jrj9Z2DDcEXXouPv16n9JUW/hfrd7VxwY0T3Qsumc81WI23M2ztH6Jd9lamdtZTheI1ptQRs49EBdVCGQYpAdM/VDIp57mIK7Y0CyRrPGGueZjrzEakmd+UNCvfzdVv7R+uP/Krk8HebEu+y46f828cbZvrZfdUYKBlzbLMN9DSrKbOaeOLugsbOujPLBthOPKbhW5rvyvaZW+kaQGxMOeptYU5NxBVU3zeL/P7XKyAS/9pWzxlFQMmXUnAtOx9Slrdg6LWD6QQix/SAjf9ZOu/SQVMZR2PNWBqezdgihj8Hvn/3Ju8J34V5Dll6CYPFTBV6LgLMC0d6xM5Z1hR7K/dKWlQK0rrJQGmdiUAUyU4SypgqhQDzVT8ZTsakPhLdzRT0eiHsmebUOcZb2xDVYAGuanC7Es28JX2eGisIkPpGON2WoAUPVlxXgsaxegzyVADmUXI+wFIGybUAqH2CuUkzRUN+8pgkyermAAlAFjCGG+4IzMKUAy2YQMYB2lQZTVixTZ5lVXFpMxektVLbzCerwPLwimM2zICKqBZHsQ43FRa41UGe8b77ZucoYW9k23vcP9QKEGJBDCBMwuYBICE7DAPxq0AoRaEFeIFxh9756X38TFnxvcfZx3gDVAV8AnnIlpaJ5wTAFLAOCikDOyviiZTr9H9HtPymuFxHSvN8RzjNpaLGAffAMNythrgMf6vXJ7qHBmAAkbjfALSyIAJyjqlggn7KgMmU6ybDNrvB5hUBdM9QYasBJp4jWrMcKNXVtygwfvCyOJqMrnF5Im5RGUZAExhaXqyC8iiFRcSafihCGpv4U9Nl3hTndluxCoIMDU186QOFn7087EI2nw1hS5H5FJsppH0+WUDTKGpejoTnE3ml5Np9LFI6rzRn16oZIDpFAdML/smakVw5BGbV80jVlPHM07zpGdcXnOPuLx3XGNy2zhFZH9oG5jxzl7PtJbrLic9aeYYX3O2fewjO/wTbKKrLTwT33C9c/IrW6+l9N50NfmXRY5x60ceDXfostk/tMUy7+wn5rob6gjzqY45TpbmOfFacd7SlEpijacCpnIbKmCqmMY63g6WANMwdlaEJ4ApgCqwymvHjlH7mseo5zM2NPjdMzT5iytkPvMm2e2NpptXb1FilIa0uQVidtLjNAoNRLfiDeR7+RYdMw+nhd+70RBhft0aWdEH1Q7TB+wwdWTIXrK5o17C2gyV1qi8ABPWuh87KV4HgKljNSvq3sCavmhhRz93ukCLR7jRvhVB5Hw8nsJ8MkW7u4L8sgEmo/DalCV8faRvNrnYJtGhtSG0+Ed3GtHhHPV81obaVD0qAqa2KmBSAdN/HjA1p2LLOAnoyMoeqGnmPCPa1yGLKW9SzQLN9MY67dI3Y3Q7B9kazyybbfA+1lcf7NQ8Orp0q7wUX8d6+YH27+e77h6Rb7/IwrDvB0f9uo7hwrXyAJZkFZNoEwerPlj23YFL5Q2YmotKLY2wrxrhegBLooIJe770NYPOonuMfv9wJ8PpudthCaj32NtL72X5clnhkjCq5Dlue0Z3ZWM7/fl1PxhOzl2l2zvMTre2XYh27nNa0RJvYnWeQTXnKa7aAlxSAr/yUm39a6p0wBS9fiCFWvyQFrzpJ9tAFTCVefxbAFMiANM371HA6D7kPenrIM+pAEzfqoCpAkeg2W/1Q1aO7xmyesqasKW/+UTO+U4FTCpgKsuQm/14jUWz/2XGbeWGCLVQqMOMq3piGG+kolldGSy3ZPAi2+MBCqEBj8YqlD1DheogVCtWbB2HOUKVgD/OQT+kGeP2cgOFmibUFqEcGFcJoVGvtL4y5TwBBwBWMqV9QGPbTrpf2GANlub6CuOKjnrSXCurikmZvSSrl5CrA8XZaMbzpbCPZxmHC9GMgxnAElMqRUorpRUe7hN7BjCIfcMZlaFSkDQvPK4AkwCQsJ9QxSA/7ADjsHOnVH9Kb/cItY9x20DAtxNC2TMOnwCdAKhgJQhoFcO4Mgrrlq1Yu8oOmoqkMrBiqArFlqu0PhaMA0jYKMpnHrAYZ15WMZXHUCqYZOiuBEy4FzwOkRVVGTKYlIBJtsgDYEJmlTKDSVUw/QUwTeK2ZLVmudHrq27Q0ANhtOlqMrk/IGAKTdPTqYAsWn4+gb4/GE7tzP3phcVeVFv4uSJQqiDA9JG5H/10NII2XUkhp/AciskwkNZYdsB0NiSbLK4gRyqSulQSwPTaCjmDiSuYrkfnvuQVpxEbA1cic2pcicxtdDkip8Wl8Oz2Z4OzPjvhn/HdQZ+0UTvcUr43v5r0xcpLiR2WnEtotehsXJOFZ+LK2lAo0xh7PLLKWKvIJyafiHl5vkN8G2H/v1h2IWHyHIfYjSOPhp/pvjUwrPkyb12dmW7SnslQSYJMlQkoqYCp3IcKmCqmsY63SsCEt1+XyAXqWN2Suj1hTZ82t6MfO12gBcPdaNeyILpwLJ4CPTIoLUEvWrGJSqbHgDMVFBRRdqqRQjyy6Mz+WDKffJPG9rhE/V84Se2rH6XWInQ5IlrjAf4AAgG6DH0EgOnzEoCpU7Xj1PMJG/rqldM0ptslWvGzBx1eG0JXbRNFUJSdVjbAdFt4cdLlFFBqjI4CXG6R475Y2jHPn2Z97UJDAdKaWFObKpJCjR2jHipgUgGTCpjobsAkw41mxXZ5sMkbX4XyJlQT1uQZjfb3Dj76I7/uMVzaMFXvc6SXzv/kS5aWltXut9bh4Q619L6nWhS47uttcFz5m+HomC36zf0va5e/kySsb6FmhrDW0xuSVlhz7ZxnOeBaIEGXRUrl0UPMr6R6CfOCRd3sp/geAzABbC1qWaBZ2zZdu+NLD73luD0Gx+VTDJe3DzC67n8j08vyibKcqWinPbWzr25tnH91+3u6C+ZD9KcWLTccHm2j3dznhmbxa6na6Q3zxWyrSTVFS747tnhK6z5VuXSPKiNg2jgiLXjzaNvArb+qgKmM418NmKZ/+9n1KSpgqqihAiYVMD3kkAEToAvgxGtC9WI8awQ5P7AoQ9MaqgtTK3pKNvKV9ng3GW+2b2Y8m+hzxi3XlKqe6tJc8Xs1YNoLjP91P9RaUALJ1lfu7K82eaZqxsuqDswVihTYhkGxApgG2LBYqFGMKzrelubUkBWrmCobYCqpXoKtH9RLXRmHggBmgAjYB6h5AA4xZ9karzKql2TgKqtvcJ94rKDhDyUcIAQURgCXgEpOjJ9VzPEg4wAJto44f8uFMmNcUYfMoTmM54nhfYBTQF8AOKjXoPICZISyByAYwAlQDgoWqJugjILlHmAp1Id4rChBU2WETErVnl5aQ4A5f8azuPZJ84dCEcDnXXa3iqm8oKoSMMl2mn3Y3YAJa4y9lcG7KfPa/k7BBMCkVDCpgOkukDG1GDDVme1Ob6y6ScMOhNMWlxTyiM2jzAcBTKk6svXPpGXnE2jYwXBqu8GPnjfzolqzXItBVnkDponFgKnW9OsiDAJgGnUkgiwuJ9PFsByKumUgTSlWRCJg0heKKizHkGzaeCWZfrWMpK6b/EVoVX2aaQHT6ytvxAzdH2az+pIImHpcicxp6hKVixd05hCUWds+MPN5u4DMNla+t77e7Z46bZ1z4tqFjnHbZ9rHbJtlH7t23pm4SWaO8V8sPRf/3pJzCU+X55kebxNZf4J19BtTT8b0nXkqdsw029gVY45HHRqyP9S565aAsFYrfPLqC2dL3K9xLrwmSFlLk6V5T1OUqaGSCpjKdaiAqWIa63g7WLJ++/aOTV6xdRvAQ+cqVtS51nHq1fgEff2qA43p6UQrfvGig2tDyflEAoXdyKZbSXrS5RU+FnZ5eTn5FOGXQ+ePxtO2ef407bOrNPg1e+pWF4qtI/ShUB3ZMerDbMQz9pVwxpT2eN9IcOlrsR5szWXANFj6XoCNvuI6AzAdpy7Vj1OfRieE+3GgcT2dac0YL7LcEEau9skUHZBDObfKZkmIr8lJN1JsYC6526fQ8fXhtPYXbxrXw4m+aHmaOtc/Th9UOUofCHNtr1BqqYBJBUwqYGqhyP1pVaz0mSdlBU2oSprxjGczLXk9WbdtgKvRavxhw5llU/Xnf++c5bSh0f3W2szMrGq23+nGBpcDr+vPr+1usJk6zrhr6B6deY8b2pXvZmvnv3xbO+sp0iIHaWZjEf6IVn1Y95LZSWUCMCUzpiS4JKmzRLg0U85depo0i1oUaNe0zdRuGxCoO/STpdF27hzDpXUDjNd3/C/Xfd+TTk5m1Us7T7DF03jsec54fc87xkvmXxvt5i/SHfzJWr+5n59m+dsp2tnP6rSwAkS21dR6Yt6TqFxa3FKRu9SCAyeTn4vKVsWASSsDpgUvU64ImFpT0uqeFL3hKwpTAKYQFTCVafxbAFNS32cpYsh7FPjLx+QzeXCQ99RhKmCq4MEB0+SeYaunrAlfNt4nau53RXFjelDS4FeKAVPJDKZKcJZUwGTSIWfhyI1UwInWjCt6ZjGumECzEgoCKCHQ8K0s9nhKVU8041DISqjVjKtg0AyG6gDN4QbSHKtJhfdlmzy8VnUT6gfGG/tQj0BVAhVIZbDJU85XK+0D8ncAKtDkBmSAlSFyaaDGasG4KgjAsDqrXComGS7J6iW8PjRnHATC5g/N+6WMq3dgiQZoCIs0WKVh7vI+VCYoUlK1hPsEcMDZARjBOYJayYVx+HOccUgC60kAJQBCAKTJjENOgJPhjNs2ArgNURT+/T3jFnHIDRvPuPIO4GkZ40AYuVWATScZVzbhnAAQy6AJ5wewTganlTHLSgnr8PgDHMOZh0LLVqhN0rwHsb9XMf3TM4/vh9BBqWACxMVzi2yRB8CE8ylb5JniuVEJ23Ef9wJMSgWT/JxgmlFpANMdyCMri65Rvdnu9Naqm/T9gXDa+hCACflFJ/0zaOm5ePr2QBh9uN6PnlvkSbVmuhZb8QEyTSkHK7SSgEmoWtOu0wsLPan9Bj8aeTiCzJ2T6EJoNkWk6ynPUEi379PLuwOYhK91FL5n49VkGmN1D8A0znSASVhTmzVOiTOFNe5+KTz7+Qth2eJBPnYjvd5Rn/Tmh7zSe/7hmjxu2bn4Lb9ZRzp8cyDUY+DekJvfHgq7NtY66shs+1izJefiBy89n/DuYsf4BuVxnmfYRVefaBPVaoJN9OcTbWJmj7WK2vP9wfCL/f4IDvxwvW9is2XeuQ3neNyuOlWa03gJLk2U4FJJwGRqoKQCpnIfKmCqmAI8kIECV+gAoOBzp8X1/ZidoG7sOHWuepy61rSmvk/Z0pA3z9Lk/lfo9/E+dMwijK47JFOkfw5lJBvIoC0U1TOVddwWntCTYjXk4pBEO5cF0qzBLjTs3bP08ZMnqFNVSxEsdRKBy3EawE6KoK1YdXRGrMEPAZbuXm8OmAA25DUGYIIlYdcawho3OUlD/3eGJvW5TOvG+ZD1xnByP5tCsUG5lJuRT0WlASbh0/mGIspI1FOYRxZdOhRPu+cG0vyBrjTivXPU95mT1KGmFbUR5or8pQ7MSsyA+lR6PA2W5qsCJhUw/bcAkwLILGpJf8ljWtCU5zHBwg5gZFo9WLrptatbp+i39g/S7f32gP7I6NF5ltPeNDO7/38YYDGXeX7HEzqH1S/q7Rb2Mh4bN8ew9/sTeuQxrWmbo13Q7Pad7KcZDYW1l+3ymitg0YMCJgWYEvZQM/9F0sx5huctidd4EvCiQLOmbaZ+x2fBhsOj7fW2s1cYHVcPMl7e8AbuF+CotLMEBVfeld1P57se+MDosv0ro/2y+fpDvxzRbvz4pmbZG7e0s541aKbWL9IK66gVrqvFdaFewr2KgEmx5mrdo5rxx6AEmHQ4FwteEgFT5rLWlLymJ8WYf01hm0amhWwdbRuiAqYyj8cWMH0kAaa2MmB6jiKHvk+Bv/alG5O/CfKe/v0mbxUwVeiQAVPE2ilrIlaM94me911R/FgJMPX+G8BUCc+WCpgqdCjVJOgPtGQ8BwcN7JWMN1GVQfamBi1yybZxaD6jkY8mvjPjjXsoP9CcR7YS7PGgykJjtQYrBmposuJ3azw/AcjAEhCWW2jIbmccBKApX9Imz9QqJqgk0ESGYstXuk9YpwEwADx0Y1wNJEO1ymaTdy/1EjKycOZk9RKUPABn1xnfVyjnTG1BVhYQItvhAeDg3ADoYI8Als4wng0GpdI6xqES5jqW8ccacqeguIOSDrlhUHN1Eqoj4wBFro7SWnVnHKDCUhDPUTjvPzEOnACrAJugAtsjraUMmqBoipbWFGoXpZqpMq1ryTOfI62prNzbz7iKCXOGigkApSkr3yymkgomGTBB2QkwWPK50VTWjcp1UjOY/glgqv8oAdPkigdMG5yT6Py/BDD9b9WNmGEHw2zWOiXOPOGf0f1CaNZzDsGZ4kHe65HaYI976qs7XVM/W+ecOG/KyWirgXtC/D/a6JfReoOvvsuWgMyv94f6/2YTZT3XIW7+4nOikunVRWfi6i2wjyv1L1jvNaxuptVcfzmhwWz7mJcnnojqPeZ41Iyfj0Yd+nZ/mFefbUFJ76y+qXtuoWdR3VluVGWqazFMmqwAS3dUdJW4VMD0j4cKmCqmZMAkAwUOFfjHB4pNd1sRPnQFZBKqex1rGvD8Kfrhg3M066trtGmmL9ntjqYbzmmUEKEhTXZBpQVMuC+98NoUcjOTrP+MoMU/e9Dwdo708bMnqHMtSxEswRavF7OmfuwEfSGpl5RQaPA/BC7yzxokAaZPSwCmbjWsqf+TtvTdm2dpat8rZD7hBp3cEkFe51IpLiSX8jLLBpgA+lKjteR/+RbZb4umTWN9aUq3K/RNMwfqUd+G2le1pA+RryUU9rW3cA8qYFIBkwqYFFDmrmouNvOhYtLObiLmMYlwBMqbRS8V6Za/pdeu6+Ch295vnXbfd5/qLMc0Tbed2cBrxy817rPsVfB5w7k1rxrPLBtssJ2zWn90zFn99s8idCve02qx7lBJTa1DmhmNpLV/md/LQwOmFvxnzG9KGljjAWIBLkG9BMiz8l2NbvuACP2xMecMDovN9c4Wo3RXtrXLub4TjZ9S/xMEdVa6y64GRu+jbxiv7/zSeGHtHKPVlAO67Z+7aZa9naKZ0aRQM7k2ocQ1FOZ4J2fqgeb0X64yAqbNo9JCtv7CAdNWFTCVZfwrAdOUb4K8Z6qAqaKHCphUwPQQA6+x6K/gL//RgEQjEkoSqCmgsICKBHkxgDhoRleWRrT8F/tQYqDxDBiEJv5WoaYyrub5kPE8KdkeT7aGkiETPoaGNOy13pPm/RvjAADNY6gl0IyXbfJMDTeUUA25NLBcQ9YKMntglzZWmsMH0rzR7ymvZnt5DKVaDuoqvDY0Y1wxB7ACRQ6gAaCIUr2E9dexymfpprQulFVL2JcYxkGImzQPZCVBVQTVC0Ag1GYjGVffYL+6Mw6PkEEFUAJACJtKqHIASAF9W0hvW0kfx+9XsGx7n3E4CpgK+AGYAKUTwAsew4sYVzVhTWGfBzgDKAJwlyCtLc6T0nqwsqyvvMb5rFi5h8cjHpdQZwGg4bGO5+iPpPWR88fKQ7mH75cVTLKNI9YYKjsZMHlJ62hKwISSz+G9MphUwPT3gMnlLsDUYLYHvb3Kl4YfiKBtLqkPBZhO+GfQknPxYo5TGxMCphGHI2i9UxKdC8mm8H8hYDoXmvXc6SAOmHa5pzTY6Zby+o7rKV+uuphgNvZ4pF3v7YFRr63yKWq6xItarfShjpv9swftD/UbZxN1aI5D7Oyl5+IHLHWM/9+Ss/FPCXXfnIGSwzU2p7ZtwK3nN7skvjvXIab/OOuoKT8cjtj31Z4wz15bg9LeXX2z6Nn5nuJ+iGslZy5NdlVkf6mA6b8yVMBUMTWI3a2q+UYCTDJYAGTpKwIQaxFEdKpqRd3rW9PnL9nRTx0u0MLv3Wj38iC6ZBVPod5ZlJlqqJQ2eUWFt8WcqLQEHV13TKZti/3pt/7O1P/lk/RR7WPUlh0VARNyp/oL8/38b+HSw6uXiteb2+sNFN4H1OgjrS8gXvea1vTJU7Y0/C1HmtH/Km2adJPstkWSz4U0SgjNI01W6YDpdpHw2ppbQIlheeR9No2Orwmn1cO86df3nOjzJnbUpQasAC3F6iBUV+HaH7OTdx5PKmBSAZMKmBRw6Q70QFP/RdLOF9YAOUWzGpFmZkNhbQB/hDVa3CpZ+3t7B/2fX8w1HBvdN+/UgrfyHDY+bWk5+L6/K2U57WmU77a3Tf61P4bnn1v9u/7Irxd0Fj0TdAub30YWk2ZKbdJMq8+vCQh0F2SSoNH95nDna6Svm99U+FnPCPf9JGlmPMEBE3720ldvazf2SNYd+flK/tnlm/Nd94wu8LbqovM4+VJZbPEAl9ICLevrbxxpbnA70MfgbD7DeHL2fv2uIW66NR/GaaBcQt7S+KqkmVxLWL8neQYU7m2xmrtU9ro/YEpZ25NiLQaR8MSVFrZtjG3I9rEqYCrjuAOYetSwSO35eAOmqKGtKWhMP/KdOiTIRwRMw1XAVIGjGDBNWxOxYoJP9LzvVcCkAqb7DbnhjyYqQEtzxhu13zLemIbNFlQkaOqiES0rSCpD01n5F/ty0xnWY2jiQ2HQl/Fm/fOs2B5PVnmXtAWEdRSaxz0Yb/wDciAXByoApU2eqeGaPG/ZFjCG8Qa3HeNgDc1kKGGgfHmVccuw+qz8LMP+6ZDVSzhv2BM0vAFScL+DGYcFgCHYR2QvyeolQERTK8hK7oNsiSdnLWE/khi3koQdnjPjEARN/t8ZB0uAl7C++4LxjDNAJQAiKLgAR5AVBotKnEfsHWBJE6kaS2+flD6OrwH0ABxtzjh0AnD6QFpPqHrw3DWScdBkxrgyDOca2U94XCPTCAAvnd1tmVcZFIolz7yctYY1hgoLWUx7pHmNlNbzLVacP4Yz9k+yhmQQrbTIkwGTrGACsPNhlUPBVNIiTwZMUMmpgOnecEkGTC7lCphO3hMwuXHFSkUDJuckOhf6MIApizZeTaIxVhF3A6bxlQcwnQ/Nes4+KEs8yHs8UusL9eqfbqmfr3FKXDD2eOTJXtsCIpov9779xDx3ajTfg1qu9LndaXPArcH7Qz3G2UQdmO8QO2vJ2bjPlzrGv7PMMb5MQc8YfkmaGq6xOc+fCrjVbrNL4tBZ9tHzRx2N2P/Z7hD3LpsDk99ZfbPghYVeVHeaa/F6jZMg0+RHtGYqYKrUQwVMFVeDmBI0yfk7PGsIkOVTCYIAgABIdKhmST0b2tDXr9jTuN7OtHa8Nx3fEk4eF1IpMVJDBl3hg7CfRz8kRc+tRD0Fe2aQ7e4oWvqrB3374Vnq8oQVtWaHqQ07Ql2EuUG59JmYRXS3Nd7DwKVBJUr5cbz9UljbAcK1ALW6AzBVsaIetazps2dO0ch3ztHsT11o2zQ/cvgjmnwvpVFSeB7poBArvD9gAkzTZBVQXGAuuZ1MocNmIbT4cw8a0fIC9attSx2F6wAufcSsRGgI9VQ/dlKELF+xYkXbN+Wg2HocSgVMKmC6b91R1sjN/Zc46JkNCzsojGqL2UzC2hh0K98N1W3/xFJ/+Jd5xtPzvzJe2PhmkteOuvdbe1jKaQKdnssPOvtBvuehH/LPLNmi3z3UU7+ydbGKaVp9Yf2F6+HfAESAC7gfJZS5CzSVsNETlUvNOdAR9xNwqbGojBJzl4Sfo1vXIVe/Z5if0X7Rvnz3feMLQs931ke6vJzi61ivDEeoigiXguybFXhZdjZc2TrGYDfvD/2+4de1Gzon6hY014hZS4BLE6qJuUuiegn3isylxa1KgWVqFVcxYNKJgKmpeCbzFr9CWcsBmHpR3MZBFLF1VFr4DhUwPch4nAFT5oe80jvWpKS+z1PUt60peEw/8ps+JMhn9g+bvGepgKkiBwBThASYolZO8ImZ/31R/G89KVkJmNqpgEkFTHeG3PCHmgQNbTS60UBFDgwa/acZt/hKZtz6C0qCytLgRyMcqhY0x5X2eIsYb+LDYuw1VpzLcq+manVWrKRBgx8NfwAaZE/tEMqR8SY8mtoy5DC1wkOGGrnSfZW0DEN+D6zTlJZhtf5m/hU9lNaEUJUBqLzL+P2OZHzvdjFu+wdIE8N49hL2ubKcPZSsJFNa4gEyBDOeA4ZzAzi7mXErPCiWcCZhgQeIiZwswJBW0hqg8f+ktCaAIwAadaWqI62X8i0+jjPdQPp69PUAnQCcoFx7VVrX9oyDFzyH4VwANsD2EjZ9sM1zYlwlBiAB5VUOK1aKVTaYJ2cxKfPHoCCS88cA7aBYbM7447k8sobuBaGVCiYApspikScDppIWeUrAJGcw/RPw9s/HfwEwKS3ynl/kRbVNAJj+iUXe2dAssriaRL9aRVAXAKZFnlR9qmkB0+urbsR8q7TIC89+3jGEZzAd8kmve9g7vfl+z7S+FleSp005GX2o/59Bvq+s9NHWn+NONWa4UsN57tRqhU9Bl83+SUP2h7pPtIk6MPd07NxFZ+K/WOYY//q6S4l1Sju73vF5tTzj815wishuf+xG2vA1l+JXjrOJtPlqb4hPx03+qf9bddP4/EIvqj/DjarK9y/NQZxPZVcrqYDpkQwVMJmmZKgCwDREAivIIRogWeV1ZJbUHmqfGlb08dMn6Lv3HWn2N9dox0J/On80jkJ9MiknwyhCncoyoPjJTjdShG82OdvE0x9LAmjKl1fo81fs6KNax+h9dpjasiOiPR4sAf8ud6m8AJMMNb4Qzm5/aV1xbQCmnrWt6YtnT9GP75+neZ9foz9m+NPZnTHkfzmdUiI1pM8pHTAV5t8Ws5qib+aQi2US7Z0TRPP6uNKwFxypd5UTIlhqz5A3dZy6MWvh+ifE+/hCBUwqYFIB01+rJKgxa8ZBDcDMjAYcME2tI9rl6Za9nqvf3CfAcGDkcaPd3Dn6y5t6Io+otPUPDAysmRV9o1F+6IW2+df/mGQ4Ptlav6VPgvDzbmtnP82VRshKAhia8yxXIZW0lfsLYGp5N7RZ8LKwfy+QdtZTHCyhZj/FP7e6rV7/51eRBpvpp41Xt88vCD73sTbO54XoaKfaUCaVdv/x1y3r6PwdXyq4Yd0p3233KMOZxev1B0Ze1Fl0j9cuetWond7otqhemlSDNFPqCnNpzOeA+1v8igqYHqjuD5hSf+9F8ZsGU+S2H9PCd4y1DfsDgGmsCpjKMETA1AUWedUtUrvVeKwBU/S3H1DI2P7kP2No0M05Izb5qoCpQsdfAdNwFTCpgOl+Q26golENJQTUD5gvMlz2MA5toMhAk78yWMQpG/xoOKO5D8gCCAQoAUs/NFSRpQTbsOas2CauZFNVmQUk2+TBqu1TxnNsANjQQIZCCCoPNG5NnQEkN5IBAGAZBriGnB+52Y57nsS4PSAgBqAZwIUyf8pUQ15vuWGP31EBWABBcL+ABFD6IKcI6gvAGoBNgDTZvq0ynD0Zbuqle8Me4HxAVQPVFdRkeOwAQABUwqpuIOO5SjJYgt0dlHWAQo2k9ZABUk2pqiuqWol/V5fWEVVL+j7sMR7HjaW1BVzE/gM0ApxC0QfrPKio5jOuZgIEO8/4GY+Q1hsKGBnomRqmljz3yvwxWGLCfnCnNJ/vGIfK+L3zWWlNsY7loWACzPs7wIS1i2PFGWGmUH+VBpiQ06VUMKmA6VEDpmXn4mlYZQBMl5PowkMApjOhWWR+NYl+qcSA6VJEzgsXwrJFuxYr34za1r4ZTY/duNV1h2vqmLn2sTu+3hty/e21NzOemOtOVYW9rjbtGjUR3v/fCh99t03+CUP3hbqNtYrcP+NUzIzFZ+L6mTsntTrinf7ElcicvzQgfBI0VYSz0PBadE6zi+HZnY/73hqxySVp5bRT0baD94f4d9nsn/a/lT4Fzy7wpPrCXlfDXuMcjxfuf4K0XpNVwPRfHSpgMl0pAdM3ElRBA74vO0ldRDhxlNpXOUZd61vR5y3saEyvS7RqrCdZbQ4nz4splByjpXx9UakgpKKGUbiXpGgNeZxPpaMWobRstCeN6niePn7uBLWvdkxUL3Vgx6g3s75jjVdsF/joANPnwnX6MVvqyWyomwSYetWxpi+ft6PRrS/QwoHXadfsADq/J5aCrt6i1CgtGXLLAJiMtyknzUgRXtnkfCiRdk4LpJndrtE3T58Rr9Ve2MOPmKWwl9biv2GP94kKmFTApAKme9dfAJNklyesBezxuMKorphjJKqEfm+fpfvz6xt6m2nbjE4WQw2e1i0DAy1rlmUfAHUKb5z4Mt9x1Qbj/h88deZdbunMWmo1s54qvGNnN6sJaec+x5VUd91fS7rb2k8CTPgaKXdJCzgFUAXrvZlNSDP/ReQuGbXbPknQW413Mjht2GD0PfGtMcb1DUCvMh6fKrmhTk/lB5xpCwWW8eLatYZjv53Sb+4bolv8P612pnBuJiF3qSZXYuG6yLLCOVIB00NU2QBT1LYf0yJUwPRAI/Yd1ji9I/sk7SNmkdqlKgdM3apRetfHEzCF/taf/GcODfJTAVOFDxUwqYDpAQf6KPj9Eo9RNPu7MK4kQZ4PFA5onuKv82X1TmVpNists3B/now3ewEokEPUn3EFB5rssl3WvSzilAoF2QILig9AgWWMN+BdGIdsAAnKHCBTzx+AI0uaP1RmUM1AmQIrtu+F6ibNB6oWgAc5g8pUoyTQg5UZLN2g6MH9zhVqO+P2bTh30YyrVaBakZUhleHsKeESrBNjGAecaOgD8iFrCWcHoG8Y49lSsJ1Eg18GS4B+OJdo9uPxJ8MiGSZVZcXnVS55Dasq3lZTvFXCpnrSGgNg4TEARRMyxvD4hpplpFAzGYckUL4huwyPIZxzWBKWhEyVYd1lgKKR1h33CqAHILmacdVlf2meL7Ji5d7DwhR5jeV8urIAJlM+RyoBEx47Sos8QHMZMNX5B2tSPqPSAqZJ16j+LHd6a5UvfX8gnLY+BGAKTdWRbUAmLT+XQN8dDKd2G/zoBTMvqjPLjQOhRwmYhJ9ba/p1emGRJ31k7kejjkSQxZVkuhiWQ1G3DKQxFt33/gGYsvSFFJqmJ4eQLNpwJYlGW0ZQp43+IrSqPkUJmK5VOGB6bdWNmKEHQ0XAdDIgs4dzZM4LzhE54ouasOY17QIznznhn9F+j2fayMWO8RbDDoVdbrPeN+2p+R5UFXBnwlWqKazZ07Pd6LWlXrrOFn6JA3cFu/18NGLvHLvYaebOSQOsbtx60zUm7y92eTcSNA2uRuW+7hCc2eeQT/pv6y8nmk+xjT791d6QoI8sfDNfW+5d+Mw8d6or3Gc18Vr8euJZnsjPlgiYTA2LVMBkkqECpopvsn8lvT9YAkxDpZKt8tCAh5XbR4xnFrWvdpR6PmlDQ987QzMGXqVt8/zI8XAshXpnUlaqQbTKKyoyPWTKzcqnEOGe7PfH0PopPjSh32X6spUdda13nNoLc0EBnCFrqli9JAO2YsD09T8ETIMUa438pc8kwIT8pW7C9btWtaLedazpqxfsaMyHF2nJIDfaNy+QnPbHUci1DEqP0ZIxT3htvf/LEhXoiygryUChrll0YW88bZ3gT1M6XqWBje1FxVJ7MXvJSthLG9H6EPeAx9OX0mOpGK6pgEkFTCpguhsutZTygoT3F7zI7eUAfgCYptYR3m8ifI/w+fWdkgz7R540nF01Kd/Tsh0ATFmATVKSV9380Ivt8t32TDKemnvMsOubm7o1bRO1C1/WQvUjAprpDUgL5dFdeUwyTJJKqV7Cfs1vSpq5z4mKJQ6qGgn/FvZy2Ruk3dg7TXd49DXD+TVb872Pjc6PutIuJz6wzI1oWOgZw86/YfS2HGJ0tlhtsJ5yxrD9i0Dt8ncytTOF9ZlYizQTqpNmSh3SzgQce16y+GvxV3s8FTCVoe4DmFa0prR1vSlh8zcUveOntKg/xtlG/jFeBUxlHFAwpbdhn6S1ZRbpnZgEmKo/loApZlgbChs3gAJmfhvkN2/EJt95KmCqyCECprXTe0b9Pm1N9MqJPrELfiiKH9eLkge/qgImFTCVHGgwonmKJjcgBBqQ+Et3NMaR5wN1AFQkaObKYKUyASY5hwh/rQ8IhGwZWMSNEKo743Z/aAqjOfx3GURyAxlNVzT9Adk6CjWUceABdcQFxm3oZJtAOQvIlGugVHABCMAiEA1lADHAQTTbBzCuSINlWmNpjqbKYlJmXsmWhM2k+xsg3S+s27CHToyvdyLjoKOy5ALJcAkqFaw7Hhdo5APuOTOeG4XHzSLGIecgxuEZVHEAPAA9AD4lwVI1VtzwV8KksqxpyZLPMwpwRQZNeBzgHOAxAWUf1EyAX5Okdd8jlAPjOWYAN0olU2V83AOiAOrARtFeWvfp0poD5gHk4fEsw5SHsckrCZiUGUylWeSZ6jnh7zKYZMCkWuTdEzKJoIZDgLqz3OmNlTdp2P5w2nI1hdxjyg6Y9ABMaXqyC8iilecTaPihcPrIHPlF3sWAadIjAEwTigFT7enXxbwkAKafjkbQpqvJ5BSRQzEZBtIaS8m6AGDSFVJwmo5OB2XS786J9OPRcOpg4UfPL/CkaqYGTCt9YoYeCLVZcylxpm1AZo/LkblNr0TlimHNDkFZ1c8GZzU5HZjZ+qBP+rcrLyauHXUs4mLHjf4pAG4AS2z8Faoy7grVFtaq0QxXar7YS992vW/i5zuDXX+zity76kLCrMNe6V9eicx9KzBFdwcyCe/Xux6d+7pdYOYnu91Tpy2/EP/n2OORTp/uCgp/f93N7BcWexY2muNKdaCSmiTtRUmw9E/3WgVMj/VQAVPFN9nlGiTBBRkwAbTgY1DcAEh0FlVMHDJ1rmtJnzY7RT91vkBLRrnTgbXBdO10IkUH5lBWmoGMBtPmMRUUFFFKvJauOybTrpVBNGOQCw199yz1amJDHatZUidRyWMl2tR9ImYvyeqlYgXXw0KW+wEmwJzPJFWYaI8n3EMXAKa6NjToxdP0W7tLtHyIBx1cFExXDidQmFsmZcTpyKgpvL/9oPA5o7aIbsXpKfBKBp35I5Ysxtyk8e2d6fMn7IS5HhcBUyfhLdRLfSX1Eu5FfiwNkub8MKqtx7FUwKQCpjLXHcDUkjf6578gQaaGlAeFDmDKtCeQaZSt29rviuHEjNXGa3u/NgY5vp2b5FUqZHJycqpuiLj+ClRMxksWSwxWk6x1Wwfc0Cx/O107+5nbgEuiYgqwSZnHJCqWWinAkkK9tOBFUfGkmfMMt9ib1USETdqlr5N2fWedbv/3N40OZnsNbvvHFYRd7AoVlZeXV42ynJsUX996+pDLLQx+p/oXuGxbYDg565R+16BI3eoPs3Rzni/QTKpDmvHVhXWpSdrpT0hwSVYutbr7nhepcKlsVQyYYNV4L8CUCMD0x89pUTvH2UbuUgFTWYcImNpJgKkDCwRcSutavdJb5N1SAqZONSm53/MU+x0A0ycUOPO7oIB5ozYFzBv5WaAKmCpsFAOm6WuiV030iVv4Q1ECANM3HDClq4BJBUzFA81T/G6APgqaz7AqA1hBgxygwpXxBjoaljJUMXWjuaRFHJr8gGCAQFDvwJJssDQXNJmV9nj3ajLLqho5EwjrAOiBrBw032EjdkooH8abyErgUVls8jKkffKS7hW5P2gqI0uqE+NwQwnaTNFcltcZ503Os8F9AeYBCkwVyoJxBRDs/mDXhr2tTOolWTUHuAQ1WwwrhkuWjK87rNpGM54H1Jlxe7rmjMMJnC/sgZyHJecDPQhUKm0oQZOsasLZxprjsQD11CuMQy/AL6z9OKGWMw4jAJmgZELGEcClbE9oaqAqlwxRsAfIjAphfP2hwkLW1UjGrQgBgmSbvH8CVZUQXlYwQeGIPYZasrIAJqXCC89ReD64H2AybR5bpQVME6+JVnavr7xJQ/eH0eaHAExhaXo6HZhFqy4m0ojDEdTBwp9eXOxNdWe78WtVEGACFPr5WARtdkmhy5G5FJtpJH1B6YApU1dIQak6EvaHVjsJczgSTu3N/ei5SgiYrkTlNr0azQHT2ZDsaudCsxs5BGe9c+TGrW/WOiWt+sUq8kK3LQHJzZd4UT1hXaqMx/m6LFaV8Vep/gxXarbYS9fB3C9+yL7QazPtYvZvcUmZK/zsr65G5bb1TtC08knUtnCJym19KiDzi51uqTMWn43bPfpohEu/7YFxb6+5oX16oQfVmHGdqk6RoJJsh3cHLFUCQKQCJpMPFTBVfJO9JGC6W8V0RlTdDJAs3TpLVnkdahyjXk/Z0Ndv2tOEAc70+xQfsvkzgrycUighMo+0mrK9FjyqoReen6NCcsjhSAytnuxNo7qcp74vnqSOtSzFPCnAnd7CfO7OILrbGu9RAaZPhevBng72eF0kwNSnng0NfsmexndwolXDPOnIkhC6diyRIjyzKDNBT/na0gGTIbeQUqN05HvpFtltjaZ1o31oTNtL9MkTp0SwBMDUWZz3CXE/8Vj6XAVMKmBSAVPpZdbiL+ogQB4og/Km1Ka8cdUob3w1KIQ02pWtfXX7hx80nls9y3Dj+ABDpNur8fHX75tbaWlpWU0T7fFcfqBj+3y3/cONDmZr9fu+O69d1zEBAEaEQ9Prcas8YT+wN1rY3MmASbSbe0VhN/cy3zMolwClYE839xnSLG5VqF3fQavfNTjacGLGSeOVrXMN/nYf62PcW5R2j/IID3eopY/0ernA/0x3UXF1esEBw55hfvrfO+p185vd1k5pQJoJEnSbCtXVM/zsACwtKWmLp8KlslfZAFOMAjBFqYCpTCNycMsnkns27J/WsY55eufqHDB1qU7pnR9PwBQ+/hMKmvVdUMACFTBV9FABkwqYyjjkxiled6GqwHM1Gqe/Mp7jc5rxjBNZtVOZrLLkRj+a31C5oMmP3BtzxpvlUGG9z+62x/s7qKIEH7CRg5ILGTl9hPqZcXXHUaGuM950h2VbZVB1yOsgZ9JgHaD6AWjbx3iz/UdpHu9IawGQiP9LmKK5XNIeD/eDhjfO3AihFgq1i3Gbv5uMq1OgUqlMa43HAIBXhnR/sMW7zLhyCXAJ1oSwVoQFHTKPYP/3EuNKGpwtPNbkbKVHrSJTqpqqS9fF9WU1U3PGzwUs85BXJkOmPYxnmQGa4LwD8ilVe5UBMOM84FxAvQiQ4s44mFzHeHYaYAoA2kusfGzy8L0yYIICTAZMSgUTMqFkwGSqdSqZwQTAhP2cwfiZfIepCqZ7AJopEgiQVCc1prvSqytu0Df7QmnjlWRye0DAFJ6uJ4egLFpzCeqfCOq8KYBeXupN9ea4E5t2vUIA04tmXtRxoz/9YhlJ266nkkt0LiVk55OxlKwLAKYMXQEFJGvphH8GrbiQQN8fCqO26/3omQUelRIwufwVML175Oatb353Tlr16/HIC923BiS3FNa/wQxXqjpBgiS/XOZvhfVqONuNXlnmreu6yT/uu4NhbrNOxx61uJK0ap9n2mQr31ujrP0yRhzwSh+/8XLy8rmnYw+OOBh+rdfmgLg3V/gYnp7nIZwXaU/xs+W8pUlS3tLUx9QSTwVM5T5UwFTxTXYlYFJCFtkq7mtRxWRH/dhJ6smsRfVP+ypHqWNdS+r9nA0N+eAMTR18hTYvvEn2h6Mp0DuDsjIMD4CDyncUFdym7HQD+bmn06HNITTju2v0+Rt21KGBJbWpckQETH0k5ZIMl5RwRQYsgx4RYALQgCKsKztOnaGkqmpFH9c/QUOaOdCkTpdp7XBvslwRRq7HkynaO4eykwyi/d39ABPymbRZBZQUpiFvxzSysYigVaO86Kc2F6jfEyeFOVuJgAnXhHpJhku4HyVgUpapz2ZFnH0VMKmAqUyltMqTSrOoGWmQxwR10YQalDeOkWZydaN23otxOvNuV/VHxuw3OG2cXBBk3zU71u++r/lmZmZV00NcGuiDLjYr8DjS0XDh99+MluMO6bd+Eq5b+R63upv5hHCt+tzqbpa0J7g3ES69WgyY8DGol+Y8Q1pFfpNm4cu3NWvaZup3fhWmt5583nhpw2qjj+UgQ8il19MCneqX9cxootyeheIp3/PgOMOZZTv1B0a4atd3TdfBom96I1G1pJnE4ZJm1lM8Awr3teRVCTDJtnhYWxUwlb3KAJi2DKG4P0enRe8azwHTLhUwlWWE/NipQdK3b/VL69t0Q2qPegGiPV6napTesUqlhgD3BkwfUsSETylk9vdBgQt+2hSwUAVMFTlkwBSzfvqamNWTfOIWjihKVAGTCpj+OpTZQ8jCQUN2IOO5LPirdzTOoSJBMx2KncrQXJZL2WCOYVzxghwWNMhHsb9XMPzdqCJ9DRqvTzOurEHjHRZi86X1uChUEOPATc6jMrWqQ7bJU2bSAIQBeKDZPlGoLxm3RGvJOEjEHP8uj+pRDvm84fp4PWguVBvGYQDs5JChc4TxHCMo0kqus6nVYlhnnDk07wETcBZgywiwAXu2BYwDScwHcAkgAhANv3srVUtKK7yKGkqrN/xfErALZwFqPcBUKK3wHAc4A6AKQAl7TNjPxbDiHCwZMpv6eUCZvwawCtAHKIb8LigYodyDTR7OPM5aHVYM9R5mKBVMfweY5AwmgwnX6Da7GzDhfO5hHDApM5hUwPQXkDFZgjTjXajaNFdqscyHvt4TQuaXk+h6dC5laPPL1AA0FBRR5C0DnQ3OonXOyC+KpG5bAqnFch9qMNedqkyTrnXHMk2qfwKYStix1ZnuSi8t9qLOm/xpzPEo+sM1ldxi8yg5N58KS8m6KCy6Tbe0BeSbpCUr31u02DGehuwPpda/+9LTyDHCNaV1EqGDSQBTmAiYTgZkcAWTZJF3Jji7+tmQ7Mb2QVnvHb5xa+ha56Q1v1hFXuy2NSC5BQDTTFeqijUaK/y8X6/wGn+VqgvXe3KeO722wkfbabN/0ld7Q/zGHI+8NPt0zInF5+IPLz0ff2iufZz1b1ZRFwbvCb3Z1dw/4bUl3ronZ7lTrSkSXBIzsK4W52tNVuzrtEoAiFTAZPKhAibTNdvxVoYLgxU5RIPELCbejO8vWbuJeUzVjtJH9Y5R75dO0LBOZ2nuqOu0a20gXT2bRAkxeeLzZEUPwCVtdgHFhebRZbsE2rTQl37qd5G6vWBN71U/TO+xQyIgGyDZ4hVDoJJwyf6h4NLXrBgqDZaqGDCdFoEWgEYvdkJUL4mAqdpx6tvgBH3b8gxN7XaF1o/yIZs1EeRhm0KxvrmUm2qkQsP9X5QK84soNz2fYgPzyPVUMh1dG0ZLvnenEe+fo94NTwj7ZSnaGyKLCaotJVzie8+zpv4rcEk+8ypgUgFT2UuCTItbFqtwFrzEFUVT61HepBqkmVDldt7UBjnC52K0m3p56o9P3JF/7Y/hhvBrrUrbC9jTZbg5NNR7Wb5suLjxM8OJ6et0u4d46DZ0NYi2dlAgARZNF2pmI9LOeVbKNJKUQShZvYScJuQ1SV8LEKZd+bZGt61/iMFqvIPh4pr1+R6HRub723+YE3gd/wEs0390AMHywy+3zve2/CX//Ood+sOj3XTmPRK0i14xaqc35mBpUk0xM0o7+2l+HwAjd1RWrVRbvIeuvwdM2Ss+oPT1fSgJgGnnL2nRuyfYRu+aqAKmMo5wswkN46d83i/lu3c3pPZrEpAOwPRRVbrVvgqld6ikEKAThxQZH/K61akmpfR/geK+54ApdPbwoOAFP20KXviTCpgqcBQDppkiYIpfNKIocXxvShlyN2BKb68Cpv8wYFKqSdAPQCMWQGUk4/k91qz4r/LR5K8sjWW5iYr7ke3xZIssQCBkJg1hvMGPOckZLKUpdmSVR21pPZoJ9SHjcGaKUJsYV3TBJk9W1si2YaZW1ihhW6x0j7A52yGtx3eM51FBTQN7tIas2DKwIhvMSpWYbI8H+z7YGcLCCwogW8YzgKCcgQUd9tjUZ0+2IsR+AyAAfAHkAWrCjhC2jGaMAwfYKgJsKOESmvlKBY2pmvpKyIT7AXjF6/KLjJ8NPP5hlwdbyDWMW2Q6MQ5vYP+G81UZ1GT3eg5A/hiAuJzBNpJx+z/8/ilbQz6sak9pkQf4LAOm+2UwmVrB9HcZTFAwyYBJtcj7C2CSlDlVhH+/vMSLvtgVTOucEsklKofSNWUHTFEZBjoXkk0WV5Jp7PEo6rUtiF5ZcYOemO9B1aa7VhBg8qYumwNonE007fZII68EDaVrC+7rRCQ284puU5owV594DR32Sad5DnE0cE8IvbPmJjWZ584Bk3y9SgCYLkfmvHAlMhdPrsw+OKu6Q0jWk6eCMj846JP+3SqnxHU/W0Y4ddkSkNIcgGmWG1XFPY9z4bDkN0ltJOxFrRmu1Hie++1my7yN7627mdt9a8Ctz3YHJ31zIDR+yIGw+IG7Q5J6bw1Mb7PWN7fFIi9joxlut6tPlM7MhJKKtH+JLZ4KmMp1qIDJ1FUMGgZLlnkyeMHnvxDzg06IYORDdoQ+qHqY2jc8Rn1fPUk/9b1AKyZ70Ym9kaKKKS8nn25XIGMqFF5XtMI1k6O05OOURlbbwmjRL240uJ0DtW90jN5mh6g1Oyxa030OoCDM5+68pYdTLJWs0gCT0m4QsKtrteOiyui7V87SjJ4uZDH6JtluiCJv+zRKCNCQJj2fivLvv5D5+kLKSjZQxI1sunw8kfYtC6b5Q1xp2DtnqEcDaxEuAQr2YNYiUCkGS/Z3AabiMvU5fPSlAiYVMD1UiZCpFS+AEih0YEUH+DOlBuVNqFaYN62eTrOoZYZ+64BL+tMLFut9rHrlhfs8DSu8++0HPp/ktaOu9oJ5W4PtnKmGAyNs9Fv7RetWf5APsKCZ3YQrmIRriQAJkAH3tFjKiAKEwMfmPSd8Xti3mU34+0teK9JZdIvVHxp1Pv/sinX5bvt+LPA/3VEXerFpYKDlffOhpFEFOVKGSPfXjH62g/MvrjfXHx3not3cJ1275FWDZkaTYrg0tZ50by9xlZKo+GpVrFxS4dJDVhkA09ahFL/rl7TY3eNto1UFU1lHlUDL9U1i14z7NHlsj40pX7wQCMAkqkza8uZ3pYQAfwuY2lLkxM8odO7woNBFo1XAVMEDgClmAwdMsWun+MQvGlmUpAImFTDdPZTB9bCEw1+2D2AcpkAFAJs1gBs0b9FUNjVIKdlERXMZ4CuJcXs8e8YhEBQ7aKTCHg+Nc9kSrjSYorTJA4CBogvN2L6MWwZCXYOMHWRSKW3y8ivBusg2efJ6QFnjLNQhxtUoYxi3DESuVDPGoZucxVRRKiYl0JTXF8oZpT0eGuFQzWA/0axX2uOZyppRaccIBQ+gFxr3AApQzOxhXDX3G+PqPwAzKOeUyiVTqMX+bsiASz7ruD8ZMuE5oBvjGWzTGLebhBIOKhg8F1QWRZlyX6CslG3yACZlmzwo4voL9S672ybzn1rkATBhf3uzuxVMyD6TAZMpFUwyYMphf81gKmmRpwKmewKm3zhweMHMkz75M4hWX0qgy5E5lJqXXyqcwQBgiskw0sXQHDG/abx1NH28I5heX3WTGi/woOozHiFgmiBlSE1zpZfNvKnb5gCaeCKaDnilk1+ylnL0pYfTAzBhrp6xGtrnkUYzTsXSp38G0xsrb1CjuRJgmlQMsyoDYLosAabTQVk17IOznrINzGxzwDt9+MpLiRt+PBbh3HlzQGqzpd5UH4BpsvAzJ0h7PV6ax2Q+j+ozrlP9uW70rLD3rVZ40zu/36APzf2orVCt1/nS68IaNF3oRU/MdCMRLgFUjZN+BvYBSiW5TA2EVMBU6YYKmExdxZBBqeoZckfNZC/uQXdmLWYxAdi0rnmEOj9jRf9n7zzAqjjeLj5GY4kmMaYZoyZR0/5furEksUWjsaQZW0xMM6bZC6IgKvbee+wlFpoiil0EpCmiqCAKCkjv7XbK+fbd2ZXlCgiKXIw7z/M+EMC7szNzL+H93XNOn5YHMe670/hndgi8D8Yh9roGmkwTTIZ85N9nNVNBPqDX5CIpWotLp1NxcHMkllmfx9BeHujxmis+fGwX3mH/orUw5y7MRTw/hTlTlQeYuArMFZ8Kc/hEAZh61HfFj68fwYRuPlg1NBgHV0Yi+GgK4sO00KbnoqC0XEDhW3ptHlJi9LhyJh3H/r2J9VMuw/rb0+j/v4PoUM9JvG8CTGRx+IVkCyjvswqYVMCkAqZylLmKib42+UWecWRVFzkjqwtVjYOgue9d020btMtwfOGo3PN7O+nDPF9JC/d/4k77oj+y4BXj3ol99Dt+na1f0+ugbmHr65rpLbI1k57nmUoEmCY0gJaymETIRDBHhkvC12yeFeoZ4fsv5OlmvqHRLm2XrNvynZ9hv+06k/e6P3KD97UnO77E4CP0B+4d/8hJv37sScM172Z5l/Z/YfReM9XgMs5dt/arm9rZb4tKJc3oOhJcekycn6hcojWa3twsc6kK7N8DW6UBppZIWdwNCWu+Q+zG35OjN/7tenPjn3/d2Dj4YQFM1chmkoogrXnJ32NFcxGq0ffC3d1rhbs7N45eZd83ftwXaxL7vHRFBEytGFI/fDAB041RX+LaJBUwWWLIgCl6sfX8mAVjgmJVwKQCpqJDVjJQw5UADNlktRFqIOO5PZQ3RJkmpIahd8LLofWWBinKxjI1cQlARElzdWQcplD+TXH2eHf6fwx5Tehn6f9JqAlLv7uo4f6jUFMZtw3zYNy+LZEV5tJYMpdKtm8jCCMDkOvSmuxjHLpRc5ksw8gG7TVpXUhFdC+5NOUZSuUMqcmo/0RnjiwZCWoSACPVHClmirPHs+TZM1eIEUQgRY+HNN+FQo1mfH3prBA0o9wf+n0nWxFa1ors9mGeyyRDJtqTdxnP7PqJcfUbwWZS7p1lhaoy2SqvKgAmWVVGNnmUF3dIqDWMn3l6zW7FOFSlMyef97tZr9IAE0EtAkyyRV5VUTBFskLApMxgUi3yii0ZMNH1R57Gc1PO4PO1oZh5LAbHr2UiLsuIvDK8Zd2Ym4+b6UacupaNdT7JGLs3Gr3WX8Vb84Lx7JSzqGntV5j5VBGASc6OGl6oYpIB06erQjDWNQp7zqfiarIeutw7+OMJIze/QLTS84vMwXrfJIx0jkTX1aFoPjMIj9v4oxplCo1W2MBVMcDkXgiYBkmAyeM2wESPOUIqGTBJ+1DNyhe1J/rhSbsAPDf1DBpND8SLQr1gH4in7c6grrU/qtNjyDByGId6KmBSAdOdhgqYLF2FcIFDEq5ikmHMAOHzr4W1pwwhgiMt2S68y3ai1WO78fnLrvi143HMGhoIxzXhCPJMRmy4BllpRuQa7/y6ei8j15CP9EQ9ws6m4ciOaKyacBHjvvZG37cOosOzTmhZfZeouCLVEGVJ0f3R/Qxkh28BpooCKyUBpt4SYOrOXNFJAkyUjdSxhjN6NdiPn/93FJN6+mLdqEs4si4alz3SkHRdB31WngjQShoFwu8jbXYu4m9occErBW4bI7Fi/AWM+uIUvnnNDZ/UdUAr4d4JMBFcozkUzVoq/KgCJhUwqYDpDnUri6m5VM24Uoca/hOF9RpdEzkjGHJGCR/tGmdql3Q4p9/5+07jkVmTDN5rvzQEbH3tTkqmjL329bWuY9/Xbf+5j37dV5O1S9rv085+K1w79ZV8zaRG3JaPQNPEBhwm2RFoasThEu0XKYiEPdPNfF2jW9ohWrflu7P6fVbbDCeXjNWf29lZH+LWVIJLdxwxvg51jIE73zAE7Pgi12vVZIOrjbN+Q7+ruvkf6rQ0F4JKBJfG1OFQzfY5iDZ90yXrPhEwqXDp3ut2wKQji8ZpryJrTkukLiHANBBxG4ck39zwh+vNf37/68bqhwIwiXDJw8OjBtlMktJOWfQ1KiVoksETff/8+fP1rx078Gb0hpk/x1n33pTUr1l4SsdHRbiU2rKKAqb2RQFT6i3A9CJifmyNyNFfIdzup9Bw+99XhKuAqVLHLcC0dOL82IVjg+Km/pqfMKIrkga8VjJgsvR5snQ9XIBJ2eynHBZ6jaaGKb3rfxnj9mqXhUpivJlcFSyximv4U7P7GuNqHYI/lJVE6gtze7yyNFKVgKmO9G9fYRy8kW0YNWjXSGtzgXHQQE3cqmSTJ0M3mhupgEgNtJlx+7bBQnVjXNFBAOSpcqxNRQwZaBLwoyY9WTaTlRw9r0g1R+eOGvUExoqzx7MkxKCGPcEugopkxUYqNlKtkKXfRMYBJD1/CM4QzKDnlKwQq2pwSTnMlUw0bzrzZA1JijeygJsp1DbG88cI4JBlJp0xUg5Z8nVBmYtFr1H0WkVg0kOoLYwr4sgakmz/yIqRns93q9pRWuQReC4LYCqw0NooFUzmFnmqgql0oOEj5vHI137aLgCdV4Vg6qGbcL+SIaqSDHllAEzCz8RlmOB7XYOtfqmwdYtBn03h+GDhRRFS1JngVwhpxpyWPlYsYCKLvJenncNna0Iw4UA09l5KQ1S6QYRHd2xmCj8Tl2WCV0Q2Vnol4vfd19F++WUx0+kxYe5s7OlCwHQv864AwORqZpF3IDSjhgSYPth+LuWHOSfjFkuAKfGl6WaASa5RZrBP2JtHrHxFEFhnoj/q2fiLqqa6wsfawr+nfC6+5j63FGNFlFwqYFIBUwlDBUxVp8wB00ARMB0SG/NcheOMj0TItFvMY+r0jAv6vnUIY772xoqJwXDfGoVgrxTER2qhy8ktDy8q1yB1j0b4fRJ9JRvernHYNEN4Tf/WB9/93yF82sAZbWrvFhU8BJc+Yy7i+ekrqbJki7yKzB0qDTDRtT9n+8QsJIJLHxFgetQZXz6zH4PfPoapX/lho9VlnNh0E2Gn05EarYdRk4fSpMF5wv1npQv3H5aDgKOJcFwRjvnDA/FX1xPo1Wwf2tbZgw/ZTuFae4T73ysCQsrYkuthyl1SlgqYVMB013ULMins3+jrkxqK6qKcMbWgGV2L1i9XM+21FN2yDlcNm/q5G/f8NdWwb8Ln2W72z5S2L4Hr/ng0223cM4btv7XQbOzbTb+6xxTtsg5HNAs+TNHO+j9wu7xnJbs8oSbU52BpwtOFyqZpzU3aRR/H6TYP8NPvtfrXeHKRjcFv85eG806vJgZvqyspOu44dO7zGhuOLehlPDTdzuA8dq9hy3eh2sUfZZHVncZauPaY2iJk0pJySVRUNebATbYRnKZmLlVMSXCpBMCUtqQbEtdywBRLgElUMD0UFnnVZFjk7h5ey9fXt45cHh6RtcPDw2vJoEmGTASjqHx9Y+qEnDnT8Pqh/a2i/pk+NG78NzsT+75yI7njo0ihRndVB0xtGNJaSiDsYw6YYn8iwPQ1wu1+Dg23/2NF+LQ/VcBUiYMAU+ySiZ1jlttywGRvBpgo06uVCpgecsAkZ+GQfRRZp/URyoZxUENNSWryk2KjKgAU8wYqNZVJPUR2cKQmIauy1YwrSSgDh5Qxsj1eeRQkcsOd/l+7PuMghh6Lmu1kgUZqFcqmIghCzds0VjUyaeRmu1FaF2q2EwghazMHad5kHUh5UgTMWjDeZK5XzvW526G0x6MzR5aMlGPTQajvGT93lBdF8O484416OnsEmCxlj6dUhtE8aK+jpPnReaOmPan9CDKQJSMpZQiaPccK1WGWbeCXbZjvDc2fVG4fM/6aQM+pJYxb5fkyDnTJNrMqqJioZJs82h96zSL4R2ee1IxDGAdBlC9FZ05WM5bXrtAcMP1PelxlBpM5YLKE6k75OmCuYFICJjWDqUjJQEAJmISPT9kGoOPyy7A9EA3XS+kITzZAY8y/Y+5Gbl4BkrJycS5Khz1n0zHjUDx+2BaBtksuiZCm3sT7D5ges/JDsxnn0H1tKOzcb+JASDriMo1lamgSYIrNNOHktWwsOpmAH7dHoNWiS3h+ylnUspYAU0XM+z4ApoOhGTUOXcl4WjhX7+84l/L9nJNxiwbviThZKmAqRoVVTTgPBJmqj/cVLQ0fFe6bPtJ/VxunmN9oxTwtDYBUwFTlhwqYqk4Vr2A6BFK4fCVmMe0TrfIIkrSp5oAO9ZzRq4kbfv34BKb+FIAts0Ph4RSLiOBMZKcZ70seEyl7KH8oNU6Py/5p2Lf+Oub8dRY/tzmKLg32olW13ZJyyQFdmQt6MVd8I5ydvuJ9cdu/fpUEmOi6dH67CevWQVo3GTB99awbhrx3HNO+9cdWmxCc2h6Da/4ZSI/Vw6QrXf1FFoTpwu/eiEuZ8N4fh+0LwjB9SAB+7XgMnzfdi9a1d98CTKQ8o3kU3rsKmFTApAKmuyspT8heYZdHzX9aN+v60Ix7HBorsrJ7ukA7tVmubv4HN3Uruzpqt/wwTOM06p0UV+vHw92X0x+Wxf6RITbC7TvV0O0Y0li39afeuk3fLdOt/yZQu/zTdO2cd3SaSY3yNOPqSdlHtaEdUxfascL1xjeA1q4xtLPfydGv6RFicBzuYDw6d4rRZ31fU9Dud7MDXJ4u6ZqKUS3cfUStzAMTn9Ltn9TW4Dx2tH7377sMG/qF6pe0z9bOeI3nTlnVFe6zLrfFs20oWraJayMCOEVZfK/+C1UaYPoAaUu6IokA06Y/U2O3DHe7uX3s3ze2Wz/ogOmWnZ2sPjK3uiNoRLDIPTy8FgGlwMDAx6jMIZMMmOSflxRPj0WcOdPkxkHnDjdXTRkTP+4Lx8Q+L0eJgIkgQFW1yLsDYIoa8zUiJv8cGj5dAkz2KmCqrGEOmOJVwKQCpsKhhCj0nKSmODX6SeEyn/FmKTXRCd4QrLA0PDFvoMq2WNRAJQs/auy6SHNXNpRle7zy5N8orQNlEEKPRZZ7vzAOFEjNcYrxTJokaY1klY2lIZOs7JJhCOUEUTYV2ZyR3dkgoT5l3MaNwCJBNDoH97vRrIQYBP0I/lGjm6zYfhVqOuOqE1LJkHKOzp6l1WHmFmxk2Ud7Tg37PYzn/IwSqh/jKhlStTRihZlftKZlegNVFRiyolEGq3Q2aH8oH4us8kgZuJ5x+zlS7xFIqSoqJuXrASn3goTaz3h+1AhWmMcm5zDdjS2kvD7mgKk0BZOlM5hkwESWk6qCqXyAyRNsmBfqT/THJ0svYfy+KDgGpSEkXo8MXR7yqB9W2juu8wuQnpOHkFgDDgRnYcmJRPy+KxKdVoSg+cxzeNLGD48QYBp1umKs5pQZTJLdG4GU12adx5frwzDtSCyOXMlAYpapTE1NsgGMyTDhaFgWZh+NQ5/N1/B/c4PxpG0Aalj5crj0XwRMSnB062OhqkmscWZKJUtDHxUwPVBDBUxVp2TAxDOYChU/BCN6s4MSLNkrwhJS47Sr6YTPntqHvm8cwojunlg4Kggu664j+HQKUhP0yC+DurVcQ3i4PJOkXgrLgY97PDbNCcG4vt74soUbWlffI9r3EWAitRXBpd7MTbw3+b76FbGKq7h1Kw4wkXKIYAapiNozJ7RlDrcA09fPu+HPD05gZr8A7JgcCu9dcbh+NhOZCQbkGUpeN4J2BuF3bnKcHqGB6TjmcBPrp4fAdpAvfmh7GJ1fdMaHtXahpQiYHMT9oudOoXpLBUwqYFIB092VEjAprOAmN4bGRli78cLaja3LFT6UmTSpUZ523rvntGt7Ldft/Ku/5pD9O9rTKxpFemwu9Ww5OPSrnnPA/i292+QhepdxG3Xbf/HTLe9yQzvt1RyCWDlDGXL+ZND8XR2akXWhHf+sMJfXTdqlHRL0W78/aXC1na87tXyg6ezW9zVnHBqGODjUvNO5iHEYU0e3b1IT7d6JLfXOI37R7/hlje6fr87oF7fL1M18A+LZsCKA9ph4bxqb50ToUVTZpQKmiq1SANPs95G+uAuS136HuC1D02P+nXjwpvOcoTdclz7IgKmabGcn299RyXCISvm9cAkwyVCJyl1SL1HJPy8rmOhzAkw3fHxeinJ36Byz0m58/Jhezg8+YGqD6DHf4MaUX0MjZsqA6TcVMFXSKAKYFo0Nip+mAiYVMN0a8rvxyRKLIAw1HEmhQzZlpCI5ybj6JZVxWGFpcFJcQ1knzS+CcZXOdsYtsUgN8wnj9nj0ekMWcGXJX1KujWyTRw1YUnkTgCPLPcrYmcA4rKFGO1nQkV2YpUGIcm3yWWGznSBNKOOWYTsYV3T8yfhetxTqZcZtw2Qrt/KqOso6zK0Hqff0EuOqOZoL2TLOYzz3i+ANnT3ZmtFS9nhK+zWleomAHams/hFqslA/Mw7J3mOFOT9y7tL9Ws/7NWiu8rmnc0HPIVJlEZQYxgr3iJ5vpGKqCnBVuU9kYUgQkADlMcb3yJpxe8vWjJ932h/6W6e8gEleGzmbrTjARGfDHDBZYj0KWPGASZnBJAMmNYPpNsA0ohAwPTHBH20XBWOUYyS2B6TgXLQWSdm5MOYWiLkQJQ36Vo4uHzeSTTgVloONPiliDlPPdVfwv7lBeHqSP2oQqBjlzWuktwRryjt3CXqMkSAVwaVRPqgufK/BpDN4Z34w+m25hrkn4nDiWiaSs8tm40SALDrdiIOhmZhyKAY9/wnDKzPPo7a1Px4Z41MIlmRbuf8KYCpyXenroxUWekVs9Hz/23lLKmC6L0MFTFWrZFDS30zxQ9/jwMQVnZmLaD/3STUndKjjjJ4v7sfPbY9h8k9+2DLvCvyOJCAhSlvhOUwyXEmN1+NyQBrcd0Ri8fggDOl6Al1e2Iv32E68zf5FG7ZHAituEvQxh0sVvWb8cWX1Vz8RZhwQ1ssNPYX16iLMpR1zEublgLbCunWq6YxvGh7A361OYs7As9g5LQw+jvGIPJ+F7GQj8kt538Ot/KVIDS54p+DAlhtYPjEYY7/1Rt/33dHheSd88CjPn/pYuB6pzmgusiLtfii4HpRSAZMKmCqkZAXTLRWTsE52L0I74RmeTzSyOjSjHxXt5LQzXo3Vrujirv/3txk692kDTN6rW2YH7izVLo9Glu+GBroz2z82eK372+A+dY1+yw8e2nkt4zTWTyPnL4acwUINYdAMrydct0medl6bdP0/vS8aHYdvNxyZOVR3enVbjf/65+8Es+ShdbVvpHOf/Ine1fpnw+6/F+k39DmuXdohVjfzzXwxd4ls+cYRXHpcOCMN+PlQroV9M8vvy3+ubgdMpBjTTGuB7NnvIn1RJySvHYC47SPTY5xnHYg6smFo2EnXBxUwFclVIuu74qCRMmOpuOwlJYiS4RJTqKHIIu9GkASYVtuNjxvbyyWx7yvRyZ0eRUprCQQoAVNVgQEKwJSqAExJPRsj7uc2iB77DSKnDA6NmPnXihsqYKrUIQOmuOW28+MWjQtKmDY4P3FkNxEwpXxWTwVMKmCSlSTUFCfLtIGMq3OogUz2b6QMsmSjtLQixQTBB8rDIYBCOUMEfcYxbgFH4EKpViivisTcJq8p4zZ5pIQYLtRiVpgVpLTJqyqASc6koQyj69I89wm1nHEVA4GydoznbpFCS7Zzu1/NZhkwyZlfMrygc9ebcQs2UpvsZYX5SwQPZXs8S6qX5OwlWb1EzXp6jhBUGC7Nn+AjZfxUpuXg/RjKPCZ67tDZIFVWR1ZoYyjDVTmDTFYxWfLsK20M5Uw2T8aVhgSdSbVH551AsZzJVh51mRKQylBezmAiizxSTsqASZnLZqnXzbJY5KkKplIB098SYLL2Q6sFF/DXrutYfzoJPuE5iEkzQmPIR94d3q2uNxYgMSMXQVE6Uf1kfygGfTeH4f2FF/D85ADUtPIphEt0zVEVAJikx6hl7S9mPbVdegm/7IzAUs8EeF3PRkoZc0LIIi8yzYB9l9Jh7RaNTqtD0FB4vOrCGlUbpVBc/acBk2/JgGmsCphUwHR3QwVMVauKqnHci5TcoO8mZQp9wpzQroYTPntmL/q/cwhjv/XCqikXcXJvDKKv5cCoyysPP7rjIHs8TZYJMcLvHYJYO5dfxdTf/fH9R0fQ4RlnETC9z3YJ83IUQRjdxwAF9KlosFS4ZsUDJlqrHhKQozm1ZntEFRMBpt6NDmBYGw/MGxSIPTOvwt8lAdEXs5GTakJBKb+W8nLzRfvB6LBsMX/JaVU45o84h2E9TuGrN93wSQNHvF+DANNu8Zrdhb3qIwImd8ny0F0FTCpgUgHTvdQt1Y4MVl7hEMCmIbRWT0Az6lGhakBjVQ8a+1eytcs6hBi2/+yiPzB5mtFjxTeGs/828/Cwr1HaPlFzXBPi0TD3ottHBp/1fxtdxmzRr+x2WWvXNC9n2KPIGfwIcoZUF67zDHT2b2n0K78IN+z6+5Dx0NQZBo+lX+h9Vr4UGLiuTO8mTnO3f8J0eP4HpkPTfjbsHbdQv+OXQ/o1Pa7p5r2nEbOfJjSQ1EtCTWwgqpm0dk1wS80lq5csvS//uSoFMM16BxkLOyBlbb+C+B3jkm4eWLYv8vT+P8POnn1gAZOkMHqUgBKpkpTWdzJskq3vSoJJ5nZ6rPD8i5/TY1wPPN006sCeT+NW242Pt/rCJbHfgw6Y2uLm2N6ItP8t9MbsoStuzByqAqZKHCJgWjGxc9xK2/lxi8cFJUxXAZMKmMQhN5Gpyfos45CBGqWkIlnGuDqDFACkTrBkg7+0xr/c9Cf1ENlhETwh6POXUN1YoT2eUplzN2sk2+S9wLilHNmFkY3gDMYVQdTElm3yNMxyWUHFNdup6U/Nf2p4k9KKINxmoeyle6B1epfxjCnqBclKr/ululE26OWMH2r6f8e4KmwN41Z+tJ/RzLL2a0pQR+AwXZoT2UYSXCGruEmMq5foTFDDXs77Ki+8qGpDVjfSfdDv65cYV7vJSjOCKWQP6CNUOONARz77lgZMdF5orwj6+knzJNXeb4zvE0Eh+XWhIgATPaasYCI4KiuYlIDJUnDUHDDRc19WML3FVMBkViUApsfH++H9uecxeEcEVngk4MSVLEQkGZCpzYMpt3TAlCt8P1Obj/BEA46GZmKRRzx+2nkNbZcFo5F9AGqPrwDAJKtpRhcCpkeE+3jcNgDNZ51HlzWhGO4UiX98k+EflYM0TdkBU0SqAY7BaRi5Nwptll9CfbuzhVlPDxtguk29pAImFTDd3VABU9WqvkWqEC71l6AE7YMMTcj27ZNHHNGpvjO+ef0AhvX0wGLr8zi0KwrXL2dBV0aFaFkHAabMNCOuBWfgqMNNrJl2CWP7e6P3ewfxyVNO+IDtEiEO5UQRSBhQBKpYEjBxS8HWbLcImD6t6YxvXzyA4R+fwoKfz8FhzjUEuCbi5uUcaNJMKCiFy+Ua8pEh/M69HpwJb9c47FhwBdN/C8CQTsfRo5kr2j7hgPeqc8BEKrMeKmC6VSpgUgFThVQRWzgCTBJkElVMDaAZW4fb5FFekl1jo2b+h8m6jX0u6F3GbjecXDzUFLj7g8TgI/THU6l/bFDzXBvq9YIh2KW78ciM2frN35/WzflArxn/LDRDn4Rm+JPQTmwO3YKOyfptv3mb3O1XmzxX/Gby3fB+mv+OJ+50Fghypbkvf8LguexV44kFvY1uk2cYHIe56Tf1vaJd8km6dnqLPK3Nc1y9ROCM7m1SQ7on4Wy8DBUw3e8qDTC9VZCxsH1e8pp+uoRd42/cPLJu140Aj9/CwsJelyCLOGTLucooZWZSacVuB0C3rPFIiRQuASbzTKVwSckkwyWlQulOzyVpVKPHI4u86EO7usSsmWwdP/7LvYn9mj3wgClmXG9ETfstNEoFTJU+VMCkAqYShjJfiFQ+pPYhFQapE7Yw3owkBQk1ai35LvySGqeklFA2kn2F2sl4hs+PjGdJkZqElArUQC2PPZ48zG3ynpUek6z3BkhrRfZbR4S6KFQcs3zuivka0VzIvoxUXmQ5R7ZmDoznBlEuDSm9SEHUXLo/pfKmooc5sJOVMZQFRXtGVnMbGbc1u8QK19NStoPKXB8CmQQQSRVDUMWRFWYv0fOmLSt+DR809ZI8StqrjkL9wHgWE+0VAUvaK7JhpDWi82bJrCylNSRBHspDIvBMezVUqB6Mg8BG0n3JFoblWRclIFUqmBayooDJ0spPJWCi10h67m9m3C5QVjARJLvb18eKG1UOMNHnIwsBUz0rX7w9+zx+2HIN847Gwe1iBi7H6USrOYMpv7QYJuTnA3pTARIzc+EfmYP1fkkY6hKBTmsu4uWZZ1B3AkEL4R5H0n16cXBTHGAqDTrJwEOCS9WEz0m99NzUs3hv0UX0EeZtdzAGu4JScSFWi8wyvsPekFuAsCQd/hX+3R+ON/DOomDUnhjA94MyqkQo48vrfu6LpQHTGAVUUgGTCpgqYKiAqWqWEjT1u2WXx6GEnCvUgTmJ4KR9XUf0emU/hnQ5jjkjA7F/6w2Enc8Qs5JK/aVQzpEvvFynJelxwTcFTv9EiNcie7zuzfejbV0HtGS7xdwhmhvBhIHCnAdK2UP9FJCh4tdKBkyFFnQEmOjcdmeuYh4UzauVCJj24NNazujT5CBGtvPEot+C4LQgHIEHkxB3RQOd8PsRJTkLCl83avOQEqPDlYA0HN95ExumXIJtfx8ManUEnzXai1Z19uC9R3YJ19ojAsCeKmC6VSpgUgFThZQ9fXzldtBEIIDWkDKKKIuJ7PKshfW0b27ULmmfpN/2o4fe3X6m4cz27roLJ16MjPS44xkLCXGoaQpxf9/guWKUwWnUXt2qHknaGW9BO1G4nk0z6Ga3yTOsG3DF6Gq3w3R63Rj9ecdO2kDnF5SQoYRRLdN79VMG75WvGTyXdzMenmltdBq927BlwCXt8o7pullv5GkJJolw6XHhY/3C3CURLklgTZm9ZOl9+c9VyYApZ9b/FWQuam9IXdsvNX639fmYIxv+uXHOa9CVK9dfI/gib7IMbe5nyYoi87yk4qo0GCUrmGTIpLTHU17D3P6uHC9/1YKDg+ve9DnR/OaBPZ/Hr7O3TZjw9f7E/s1vpjyggCm5Z2PE//IRYsd9i2gCTHOGq4CpkocMmBJW2s2PX2oVlDDjt/zEUZ8j6bvXkNK1HodKrVXA9JACJvodT89FaowTkPmV8XwVapKSSoOaxgQnqpp6SWn/Rk3/K0IdZ1xRQiqYPoxnxrzEuLUd2b7d7Tv0lTZ5cmYQKTm+YhzQLGG8gX2W8WweAl6y4saSUE5uttM8SH2jzA4ihRBlbNkyDgs6Ma7Moqb7k9K93g9Fg3Itn5CuRyoKyi4idQkpwihD6xTje0pQTIYWlgB2dD15/WQVGIFEAmDUqLdn/DlDKrB3GFcv1WeF6/egqpdomNsZ0uvEy0J9yPjZH8n42SdLuDOMK2To7NNaWVrFJOcwEaAkCz867ysZt2CkuZPNJe0VncHyZmSZA6Y3WGEGkwyYCGrRWZEBk5yHZInnP12fzi4BpuIUTDJgsux5rZqASbjmUC8RpDwmfO2NmUH4dkMYphy4id2BqTgTpUFshhEaYx4KCkrpJlJAez6QrctHSLwWey6kYIL7DfTafBmvLziLJ+188Mg4bw6ZZMAkQgzf26skuDS6qHqp+jgfPEHqpdlB+HR1CP50vIElpxLgHpqJa0kG0dqvLIN+7qIw541nkvHjrnC8Pu88qo/345BnmASYSpvbgw6YbgNNZdiPh6FUwHTPQwVMVb/6SoCJQA19/iVzQ1fJJo8AU7vHHNHjJVcM7nQMM4edwd6NEQgNTEd2qrFCAVNebgGS4nTwP56ALQtCYfujLwa2OoxPG7qgdc09onqJoAq3hXPHQHZYLD7vQshwP9bndsB0UDy3lIHUSZjTR8LcKBeJAFPn2i7o95I7Rnf0xJI/z2PvkggEHUlCwjUN9Nl5Ja9ZXgH0WblIiNAg2CMFB9bfwIoxFzCmhyf6vXkQnRo4oWWN3Xiv2i4x74n2hzKgCDDJaq7+KmBSAZMKmCquZMgk5hAJnxMEsHkWGuv60IyrixyCTJRZNP1Vg35F10vGPcM2mbxWDjGFuLXWRgW+UBbIZAg53MLou/l708Gpqwzbfj6nX9Y5WzenNXRzWkG3smeCftfwI8YTy+zzLrh8YQg/0TzG16HOnR4z5fTGxw2nN75u8F7V3XR8/ijj3vEbjVt/8tOv6Jysm/1WrtauEb8HES49KZyJZ7hCi8DaVMkeUFZuTVXh0v0pJWBqzM/WLcD0Vn7movY5aev6RyfsnuBx8+iGRTfOevUNCYloQUBG3mcOfchezqO2bDNX0UUQyDwnqTQYpVQfKeESlZzBpPxYnEqKlV21dGvQvwv3d38i7vTJ12MPOPRK+Gf6lMQJvQ8k928eIwImgksfPniAKYEAk1UfRE8fogImCwwCTIkEmFbbzU9YZh2UOHNIftLoz5E88PWSAVNVOVcqYLpfQ2nzRMoEeic7NRzHMA4eTjCudqH8GzlXxVKgpLTGKTVwqZFLTWQ3xvN7hrF7Vykoh3kejTkUmSXULsabt6RuSWaFloJVQcVE8zBIa0XAMEQoD6H+FWq2UH8ybntG0Oxldns2TUVCJtl2Tc60oiY/2fPRfpGt4VzG15KUFuZraYl1lGEFzYGeC9SkJ5jiKtQKxrO+5Bwr8+yl+2UxWJlDhkxKFROBSAIqBNZILSgDQaVFJK2ZJeEqXZ/AOOVlkc0nAUFSGpJyxxw+l3evZOhWnIJJaZGnBEyWgqN3AkxqBlNZAVMd4WvNp59Dz7WhsNoXiU3+SfCKyBbzibIMecgvDTBJw2gqwI1UPdxC0zDtRBT67AzBO8sC8bS9L2pYewvXlFRMdwOYRknqJcm27lErXzw7+QzeXRiM3puuYtLBm9h2JhW+kTmIyTBBb7ozYKI7ytDm4exNDdb4JmHA9mtoNiuIX/Nvbw4YHhbApFbRUgHTPQ8VMFX9Kg4wdRPBiTM+qcYVTD1f5oBp1lAOmEIC05B1HwBTfLQWngdisWbqRYz8ygtfv3EAn9R3Qqvq3H6ukwRV+lYxwNRWAZi61HFB/1fcMbazF5YPvQDX5ddx4XgyEiO0MOSUrKrNNxaIFnoxodkIPJQI56XhWPB7IIa2P4mvX9qPdvUc8UG1XWIOlbwWvVTAdKtUwKQCpgovJWCa1oxDAbsXobHhSqac0TWRM6YWQaYC3Zy3ow0b+7obD02bbTy7c6Ap3PP9rJiQOzaCdcHujQ3+O7oZjs0bb9wzcpdhfZ9zumWfReuXf3ZDv3GAp8F14gqTz+YfTZdPvpsR6VG/tMeiJnuIg31N/el1TfWeazqbTiwYbnKbtMbw7+CT+tXdI/Vz39URxNDSOSBbPGsOlzS20nkQc6daSIBJhUv3t0oBTLPfzstc1CEz9Z8BVxP3TDgQe2T9zPCznl9du3atmTlgUtrN3Y9S5iOVBzCVxW6PVeAf5PS4kR4e9aM8j70Zd2DXV3Hrp9knTezjnty/ReyDDpjixvfBzelDQm/OGb4ieu7QL2NUwFRpQwVMKmAyGzIwIVUP/T5+WaiPGFeyUMN4t1ABrKjFU1VSL5nb45GNn680b4I9vzCuyKFsH7Irk3NW7uW12rypTI/dXlozyuDZwAqtwkg1YWmrsJIgSYq0XrS/1AhfLpSVUP0YhySUw0WKBhnKVaTFm7kihvpOTRm3ZqRm93DGbcychPKX5klQR1bEVDawKMlikJr0BMEIhlEW0RfSPbzECjOsHnT1knLIrxcEIQg+ktrxY8bBGgEbysyiPCrK96IsNKWloSVfH+i8E6Ak8OXBOFih5yplfdHr3SuM71dtVr5zbp4hJiuYZIs8UjMWZ5FnacAUyfjZ3cQ4YKJza26RpyqYbgdM3uK1awn/3cQ+EJ1XXsbfjtex3DseR8IycDVZh3R9LvLy79xNpByNuCwjTlzPwEKfGPzkEoY264LQaI4/atkK17IS7nOUBJhGKazn7gSY5DwkRYZTHWs/NJ0eiPbCfIfsvoGlnok4FJqFK4l6pFFuVF7p86XvmoR7Ssg2wft6NpZ4JqD35jA0nRbI50Z78rcKmB7aUgHTPQ8VMFX9KgqYqElP4GSvaP3WrpojOtZzxBcv78eQT49j9rCz2CcqmNIqXMGUaypA7HUNjjndxKKxQRjS8QS6vbgPrevsQctqZI/nKGZDEUDoKwKVw2L1ryTA1L8YwNRNVHo5oY0CMH1W1wXfNT8Eq67eWDkiGG6rbuCiRwqSI3UwaUt40wMpgPX5yEo04EZQJnyc47FzVhhmDAzA4PePocez+9C21h68J1yDsqg+ltaCnj9k10dgaYAKmFTApAKmii17hVXeNKmEr2smNxbW8mnkjK6FnJGPQEOQadKL6bql7YINO/90MZ5cPCvvkuu3hpuB9MdkqX94ZYUcbmD03/mO8G++NjiPG6fb+sNy3Zqe27Sre20xbP1prv7g5CG5Z7Z/rAnxaEhN9JIehxr2icHb6moDt7+Q67PxI9OJRb+b3GxWGHYOOaFf0yNcP69lpo6gho2w/2TzJyqXnhbhkoas8URbQBkwqeql+18lAyYNAabFHTLS1vUPSXKY4BJzbOPU62c9e165EvkyQRx5zwnmyAqj+1Ul2eUVV0qrvDLmNFXYkAFTgpf7/+IO7/46YcP0aUm2Dz5gSvzlY8Rb90XsjN9Db84boQKmSh4cMNl1Tlo9ZX7SsglBSTN/z09WAZMKmAozhegd+GTxRcofAg7ULKZ3/ZMawZLqkdIap7msaAOZFFcEeSgTiRrflIfzMru7BnJJa2ZuFUYqCMovGi2tG6layBorihW1ybP02ilVTLLNG8EAAmKUoTOVcShHiiyyeWuiWLeKBCXKPCvzdaQMI1LPLWOFdoPUECdbP0sCJmWeD8ETAoikhqEmPa3bz0J1ZlzV8wIrtFx7kLOXzIc5kKbzQUCNAAW9ZhAUlG3yoljRs2/J807nhgBlOOOKuB1CTWM864sy1OhvG1mtV1GASalgqgoZTDJgkjOYilMwqRlMJQINEWacFq/96Fg/NJx8Fm2XXMSgf69h1okYuFxKxcV4DVK0JuSWATDRoJ/1jc3CuqB4jDgcjq7bLqLFkrN4wt4X1SdQ9pJ3IWAa5ctLCZmKbfbzOYqASajqY3xQ39Yfb84NwpcbwjDR7SZ2BqbhbLQOCZm50JnyS1Vc0XfyhO9rjPm4nmrA4SuZmHUsFr3+CUWjKWf5tf5UAKbK2g8VMFWdUgHTPQ8VMFX9IjgjA4qigMkJHao5olM9J3zVbD/+6HwC8yiDafN1hAWlIyfddBcYqeRBgCn6Wg4O7YzCnL/PYtCHR9HpKSd8UIOrdjhg2isChD7ifA+L1V8EKvdvbfpK0EaGcP0lwPSFCJh4VlUbthstaY7V9qDrE3vx/WuHYd39NNaMuQj3dVG47JWG1Gg9cvXFA6aCPMCYk4e0GB3CfNNwcnsMNtlcxqQvffCD8FgErUjF9R7biQ+Fa7UTrklZVBwwyfvnXgQw3a81qaqlAiYVMN2fesVMydScf922IXLIJm9kdWgIMlnVM2pntEjUr+keYnAe7Zp7et3E3GtHOqSEhT1e2p5FemyurfHf+bzx2JI39c7jOui2/tBbv6bHD/rVPb/Xbh/US3tociud/47GkR6l2+3FB7o9pgt2bmw6s6OV0Wv1IOOByQsM//56WL+6+3Xt3PczdVOb5upsnoF2wpPQWj8pnYOGhblL9pI1nn1zNXOpUsoMMNkVBUxZizqkp//z3eVkxwnOscfXT44459390qWIJkrIKNvOVUbdSZVUis1dcVXhQwZM8aRgIsC0foZ9sm0f95SqDpjaFwImghSpH0glAqYmSPyVA6a4mX+Exi0YsSJu7ggVMFXiSJYB09op85OXTQhKnvV7fvKY7kgZ+IYKmB5OwCQ3SOn3OlmUkTVaX8bf3b+N8WYsNSOpUUzNdUtaXZXU9C8uY4UgD+XCUOObbNdeZBWnxFE22Z+UHptgTHfGG8tzGFdQ0dpRQ5uUQlppnlUBMMmNZlLiEDi8Ks3VgfGmOGVJfS1Ua8Yb788w3kCXVQ0V8TtPqWB6TLoGXYvUJKSgoqb3aqEOCBUkVDQrmuljKQWTeX7VAWmepN4hmElqnhaMw9p6zNJKkIofSjCotMnrwrhNHuVmkd0iwYuqcPbNc8dICecn1B7GLSFpzp0YVyHSGSyvesccMCkt8uQMJjonsprLUgomeS1kwBTJ+HN+M+NnV85gUlrkqQqmIkCDgMNwDh6qj/FDA9sAvD3/PL7adAUTDkZh27lknI3JRqLGeEdFkDwyDLkITtbA4UoKpnlFY4DzFbRcex4NZweglq0PB0wjJGA0QoYevqXY4/lyIDVcVi95o5aVL16wP4M2S4Lx084ILDyZgKNXsnE92QSNvgDEwkqbLX3fkJuPFI0w1zgdHC+kwfbATXy26jIa2p0R4Y4ImAgwjFIB00NZKmC656ECpqpfMmDqL6peDgj74YpuzIUDpkcc0flxZ/Ru7oahXU9i4ehzOLj9Bq4FZ0CTmXsXGKnkQYAp6mo2Dm6LxIzfAvDd24fRrq4j3qu2UwQrMmDqeQuqFCqKKgMwDSgGMHUV5kO5UK1lwPSIA7rV34tBbx7BxC98sG78JRzZGI0rPulIjzUgz1j8b6V84d51GSYkRWhx6WQKDq+LwppRwbD6zBv9m7ij06NOIlgi0EZZVJS/ROopsjOkufST9k8FTCpgUgHT/apXOFya/iqHMKRism4Azdg60IyuAc2omgVam6eNutnv5Og39A4zutltMZ3dMdgY5fcmqT+kpvttQ7a1S3awr5e9ddjT2nXfvqBb1KGJbnmnxpr1A5/P2Du6frj7cmrMlNikIACgCTnY0HTeuZXRd9NA47HZMwy7/9ynX/P5Fd3cdzRau0Z5WsqKsn5StMfTUuaSeAaa8HuTAdpUuVTAdP+rNMD0Tl7Wko4ZGf8MDEl1tHaOPbpucmTAsc+vXrjwotk5qFaaUqgiipUOiioVIpU2aK7XA489Ge/r8UbikT1fJm2cNTXZps/BlP4tqnYG0x0AU9KvnyBhQj/Ez/orNG7BqBVxC1TAVJlDBExr7DqnEGBaPiEoZdYf+SkqYHpYAZMMSuj/H+k5SI3xjoxnCRFoIBUOARvK6iEYURUAiXlR019W41DTlOzeCJQQ5BnMuKKEmr7UOK0IezzluhGsIohA7/p/Q1o7UkRMZlzVcpzxjCPKfslmhVk0ls5hUtrkKWEJgbm1jCu/yO6vk1D/YzxnitQ4FaliUgIm2hcCMpRbRNZ830tzoJycw4wrrEhpRXssZ4BV5hqar5lsLUjWfc5CLWYcyn3FOKB9ifHnE6lh/muAiYZS9UhQhvaNVEADhbJlXAknn32yEpRfOyxlDSeDQTo/UYyrq2jf5jMOggiOKV8j7hYwPS89ThdWVMFEgFSZwWRJu0AlYDJXMCkBk2VVd1USMFETfQTPN3pktB8en+CPl2ecQ8dVl/CXUwTW+CbgdGQW4rONop1cWUaOKQ8RmXqciMrE2nMJGHnoBrptCUGLBefwuJ0f2Ghvnvs0VMo4GiZBnDFmcxstwRARuHhJWVFe4r+vO8EPzWedQ9e1IRi1Nwob/VNwJkqL5Ow85Jah75mbD2Qb8hCdbsTpGznY5J+M0c6RaL/sIp61DeB7QXsyTAVMD22pgOmehwqYqn6ZA6YvFICp4yOO6PKEM/q0OIDh3TywZFwQDv0bhYhLmdBl3wfAFJaNg1sjMePXAHz3f4fQro4j3mP/3gaYerODRTKRLAWYSEXUTgmYqjvg86f34ae3j2LSN77YYHMZx7fexNWADGTEG5CfW/zv0DxDAXJSjIgLzcE59yTsX3ody/4Iwsh2nvi24QF0eMRJePzdoj3eR8xB2BsXdGf7RKCiAiZeKmBSAdP9rVe4Rd70FsLHFiIg0Ng2hMa6PjTjHoNmdE1ohY9au8bQLmyTqd/+s5fp+LyFxiDnvsZrnm/mRPg8FxLiUPPOu1j+Qeol46UDbxrP7P7WeGKJvdFlrINh/VdB2nkfpIrWawSWxtXlH22eFfa/EQcbUyWwJJdqi1eJVRpgejcva+mn6Rkbvg9JdbBySXBfNvmmp2O30ECvF+7H+fkvDAJMYadPPx4bcPy1hGMOvZI2zpqcbNPH7b8EmBJUwFTpQwVMKmBSDGWDn16LSYVDjcZxQq1nPKvkGuPWUtTYtzQcMS/zpj/N9ZRQW4SyYzxfhRQlpIyRG/4VBZiUjWWy1qIMlzZC9ZHWbyUrVN+QPRY1t+UsmqqwhjKYo6Y3AUSCAbTfZB1G2VV/CtWTFeYJ0fop1R0VtYZ3gnRkQSdnWcl5PpV9DpWqLw0rVH3J+UukhPldqM8Zfw7RG2dI2UZvpKqI81bVhrx39Hcn9QvpfJC1Ib0OjhVqFeOwkuC0eQ6TpbKHZGtDei4STCXrRQKDlJtFlqAEUkmNVV7VmTlgoscpzSLP0nlU5hZ55hlMBJgq6nXy7kfVBEy+tyzqqgkfKYfpabszeGfBBfTfdhXzTsbg2LUMxGQaYMwrIT/CbBjy85GsN+Fyig4HhH+74HQ8fnaIQJvlF9Fw6lnUGCPcp3jPnryGSplMYxTgY7TU4Kevk2ppqPBzfws1wgvVx53Gs1MC0HJxML7bfhUzjsVi36V0XE0yQGO4g3RJnmNuAVI1uQhJEOZ4OQOLTsbj13/D8eHCC2hg48+vSXMk1VRlARkVMFWtUgHTPQ8VMFX9kgETzxbigKmrAjB99oQL+r56ECM/P4VlVudxZFc0boRkQa/JKw8/uuMoVDBFYebgMxj41iG0FwHTTrwvlJw71FOY3zfCPPsVASr3b21KAkwEMroI8/lEmFcrtksETB8/6ojuz7nil/ePYUo/P2yeEoqT/8YgPDATWUlG0QrvtiH8vqJsJgJQUUFZ8HOKh8Psa5g/KBB/tzqJr55xQzvhGqRg4vZ4wp4o1oHm2U+c40EFXFIBkwqYVMBU4aW0ySPVD9nLCetKqiDN2MfELCbt+CdFEKVb8WmUYdefR01H5y0y+m8dZLqwt3V2oNszFb3nZA2mDfV6QR+8t4vRa5W10XWig27zgAvaRW0ShT02iXZ4pLIS5ieql2jvJzctvB/REq+ZaotX6VUMYJosAaY57+dlLeuanrFh0KW03WOdkl1n28UdWds10mNzw4o+P/+VIQOmZF+PFglHHHskb5o1Kdmmr1vKdw8qYKqF5J5NkTy4HRIn9kfCnL9DExaNWZGoAqZKHcmrhtZLJcC0zn5+yoqJQamz/8xPHdtDBUwPH2CSm8SyzdvLjMOYQULNZFwFRNk31Bgl9Q01RqsCGCmu6U/zI0hCIMKdcbhDWUikKCFA0pgVNvwr6p35yhym+tI13mMcylDTmprLtIZkx0VqF4J0lrJ3K27tqMltrsgh9Rc1xFcwDgrIKpGUKWQfRs1zar5XVKaQ8vyR1RoBTmrOk+LsZ6Hshdoq1EmhQllRFVhlN+jNz1qCNKeT0hynCvUT44qvN+/DWlXFIcNBel7JZ7+XUMMZBzd0jiiDjKwNZeWZJbOzaO8I8BDwIkUcwd9l0nx7MK7eoTN4PwATrYOsYLIEIDVfB1ntKQMmK1ZUwaQCpmJrtKJG+aL6KB/UHu+HptMD0W1tCCYdjML+y6m4kaaH3lQ2wETZRvq8fCRpcnE+To/dF9IxyT0WX28Iw1tzLqCBtR9q3IJGp8CGeYq2d2ysGWAiGDJCAkzDuHqJ4FT9SX54bW4Quq8Pxah9kVjnnwTPG9mIzTSV2cZPayxAbIYRfpE52HYmBTZu0egtzO9/s4PwxAQ/Ph+6Jl17jAqYHspSAdM9DxUwVf0iECGDCdqHXsxVBBidJIs8ETC9dhCjup/C8vEXcHR3NCJDs2DQVixgysuVMph2RGH2kLMY9O4RMf+JVDtUHzMHETD1EMGKmwhUZMB0P9fGPIOpn7ROBHi6MGd8IszrQwkwfVLLET1ecMXgD4/BfqA/tk6/As89sbhxIQvZKaZi3/xAUYGG7DykRutwzTcdp7bFYrvdFczoG4Ah7x5Hr6dcRajUiu1BG9Eez0nMyPpCet7w/ZPnavnzZKlSAZMKmO572SsVP5LahwABrae1BJnG1YXG5lnoZv1Po1vV7ab+399OG9xsVpiOLvzR6LnqzZKs8u5mEFzKCfd61hR28EOT3+bfDQenrjdsHRSkXdI+TTutuYH2WmNVl8+JwJfNcxyKmSuX7FXlUuVXSYDpVeTMaZmbtfzztIyNPwVn7BrlkOpoY5u6d1qX5IPzVcBU8qiW7OFRLynwRPOkY06fJ2+ebZti229/yoAWNx8kwJTygVQEmHo1RfJv7ZBkMwAJc/8OTRQB0xgVMFXiKAKYVk0MSp0jAabvFYCplQqYHhLAJAMSOTuE3slPDVcCNEcYb6KTWoMgBDWHqxpgUtrjUSObgJiTUPMYb/B2ZbcrEyqqaarMYZIVOLSGn7KigMRDqCus0CrMkhksypKzaajxT+tHDfCLQh1l3DaLoMkvjDfLSdlAEIFAWkXZ5CntGcl+j2z43pKuJ2f5kJrKU6gwxs8hqYcsYbWmPGuk/ohTrBUp/cjOj9RyBOPILk7OrPovqpfkQfdFgEmGg7R39PpBSq65rBCuEsggG0YZrloye4ief/Q8JLUeWS+S0opAtJzT1ogV5rSVVaUnv47KNo+kwitOwaQETJZSMRYHmOi5bm6RR78TVIu8EqHGrTym06g22gcNJgXg46WXMNrlBhzOp+Bqkg4aQ9kbitRH05uAmPQ8eIZrsMYrGUN3R+Kz5SF4zT4QT433Rc3R3qg+glRJntw2b6ykYpJt8UZIgGnkaTwy0huPCt97ytYfzWYFov2qSxi8JwJzPeLgcjkdwQlapGrzkF9QdsAUmWrAsbAsLDuVgD92X0enFZfx8rSzeMzal89nBCmrVMD00JYKmO55qICp6pc5YOp5B8B0bM9NRF3JhlFX8YDpZngOjuyMxrw/A/HzB0fRWbj2h5L9HAdMzujB9lUZwETz+VgBmD6u44gejfZjcJvjmD4oANtnhcHLKQ6RF7OQk2Yq9r4L8gFdRi4SI7QI8UjD0X+iscHqMiZ/6Ydf/ncUPepzwERw6SPFGnwlZlGpgEkuFTCpgKlSS4RNzbltHsECWt/xZJdXT/j4hLjGujlv5+lWdknRb/n+pN55tL3+0LQuWYcXN6DMpXsFTQSXsq8GPmMKPfGB8eyegcbj8+fpd/1xXLe8c6J25hsFBLk0Vo8LVY/b+E18ltv3iXNvbkFLvFfKX/alVJnuwfwxS/leadeq0JIgkwiamnDINKUpNNNfQ8681rnZq3qlZGz5NShz56hdmXusJmQ6WHVO2mn7fEW9VvwHR7XE4CN1k856N0s6urdb8qY5Nim2/Vz/K4ApUQVMFhkqYFIBkzSoeUjAhRqqBA8oO4YUK5OE2i6UD+M2Sums8F33lgQiJQESWYETzjiM2CbUFMYzhKjhT7lS1PC/H7ki8hrSY5NNHlnxfSRUP8abtmsYV1SRVRg1mAlOWErJURI0IWBDqhxqvJPt22mh9gi1kHHY+LVQrYVqxgrBSUXkCsmNefrbhVQwZCtHIEuGFGQ7t5PxJjhZHyazolk+llgrGWbSXtKe0t7SHpMlIlkjkkUiWSXKdoz/VfUSDaW9phKuynDwX8bPEj0v6flpSUittNIkUEnAl6wXKW+M9o7OOCmw6AzS62F5zrf8GkDrIIN6JWAiK77iMpgsoWCikiFpJLsdMCkt8lTAVGqRHZ2Uc1RnvB/enX8Bv++OwBb/ZFyM1SFDk4d8EjGVjeGIP5etA67EG7H/QibmHYnHkB0R6LLsEt6cGYiGdn54wvo0ao7zBhsnAabRpyVrPAkwCR9rjvHB4+N98dykALwxJ0jMh/pxVzimH4vFv+dT4Rudg+hMAzRlVFjR0JkKcC3JAJfgdExxj8U3G8Lw9rwLeEa4Rk0ryoOi7CUvrmRSAdPDWSpguuehAqaqX2UFTKN7nMIK6ws47nAT0WHZMOnvD2A6uisa8/8+h18+PIbP6ruglWgNV7UBU0tZZVXHET1f3I/f2h7HjJ/OYMecq/B2iUfU5WzkpBcPmPJzgZxUE2Kv5OD84WS4LbuBVUODMaGrD3549TC6PbEPn1RzxEdszy17vC8kFVcfCTApy9LnyVKlAiYVMFU6YKIsJspkImBj11hY22dEuCRmMlk9IWYd6Wa9Bf2KT8P12wdt0btOHGw8tvhtzZnNDWN8Hercy15nxfg2MIV7vm8KcvjReHLxfIPDiP36tT2v6ma9baTrinBJUi6J87Ilazzac4Ut3l3BmdKqjI9TZgjTrIx1F9DqtrmU9Vry+t1rNStcF3ouSraFmhlvIGdBW1P26q+SMrf+djZjz5jtmXvGW2XssuqUtHOUCphKHtUoiywxwPOVtOMuXVM3z56YMqnvvv8CYEq2HYBkAkyLx6wQSgVMlThEwLTernPaevv5qasnBqXNVQHTQwiYlOoReu4RhOko1BDGwYIr4zZSpNQg1UhVACLFNUxlVQJZlpE9HqkS5IZ/b8ahWVPGlTcVaY8nD+U61peu9T7jiohhQi0Sylkof1Zok0dNbkuocEpaQ9pbUpeQyoSazmTnRfZhq4WaKNT3jJ8NapyTUqWirAaLsxik/KLujOc/kQqGQBeBTiWkMFlg3czVXqSWI1XKfqGWM66CIUjxIeN5RNRDq10Ba1SVh2wNR3CVlDtko9iB8fysqYyr904xDi0JDlpq7+T9y5PmQHMhRdwJxtVnBFfotUK20iQ1naxgKstQAiZaB3qedGH8DNNrqTlgqmoWeZulNSA7UQJM9P/kMoy33KjagMmHq3UIMA3zRPVxPnh9VhC+33oVKz0T4RuhQXxaLgxG/o7rsg5TLpCQkYezN7TYczYNc47E4s9d4eix9jI+WBSEV2YG4JnJfqhj64Pq1j58HqKKyRfVxviitpUfGtgG4KVpgXhn/nnRtu/X3RGwPxqDHedS4HUjG+GpemToc5GbX1byBWiM+bgYp8OWgFQMc4rCJ8su48WpgXhsvC+qi0oqb65iGl2Je6ICpqpVKmC656ECpqpfMkSh+uaW9ZsMmJzQ9UkX9HvdHaN7eGKFdTCOO8bg5tUc5BrK8YugDIMAU4wCMP1KgOmpooDpUwsCpgEKwETrRFZ9NB9SFd2y8XvMET2b7MeQT05g5i9nsXP+Nfi4JiA6JBuajNzi79tUgMwkA6KCsxDgmgjHeeFY9GsQRrX3Qr+X3dGlrotow0f330G0x9sngpRvFc+ZhxksyaUCJhUwWQQwidWcr6dtQ2GNG3DANKY2VzKR9dm8D1L063sf1buMnmk8sbi3yXfr+5pLrs97eNjXuJt9TgwOrmsM9/qf8YLzANPJJYsMTqOO69d9HSZcJ10EFWTXR3CJINOEp8V5ae2aCHN8uWjuUpnu9X4DpnIAnWlmpfyZ2+ZQVsBUDpBkfv17qmYKFZZkl0fznvEmNAvaGnPWfJWYuf33M1kO47ZlOE8cl+EwvqMKmEofMmBKPe78WermuRNTJvXblzqgRfSDCphSvmiKlCEEmL5D8ryhoYlLx6qAqZIHB0z2EmCyEQFT2rgeSP1BBUwPGWCS1QdkH0eNfXoHO4EZarp6MK4aISBCTfWqBpeolJZllBNFDX+yo6KmLmUgfc4Kc1XKa3tlvlZysWI+l7NolFZhpGAYzG63eSOVkDJHqCoAJnPrt8uMZwuRio2yuEhNRBk1BM4InsjqnHu1yZMVMPRY1HNqwopmWM1n3GbNV6gIVgjnKlsFIzfmZRBHir4oxu0Y6bwtYVzpRc+fD6T7UALN/+qg/aP7IxhByjaC1O0YB5J2jIMLOkekFjK3N7TEOZf3j85RmDS3jUJNYFx9RnCQ9k4JmMpqkafMYCLARNacpGAiwEyAiV6bKPvJkgomSGsvq/BInSpnMJkrmO6H2rN8o8oDJjF3yFOoU6g21hsvTw/EV+uvYNbhOLhfzMLVOCMycwqQS32yMrKcAlHFlI/IZCN8I3LgEJSKBSdiMdwlAr23huKTVRfwxoJAvDAzAPWn+KOOjR9qT/THYxMD8KTNGTScchavzT6PNksu4gthLn853cDMY7HYHsjh0rUUPdK0uTDm5ZdZWEUjQ5eHgCgNlnsm4vttEXhzzgU8PiEA1UeRRaA3B0xiqYDpoS0VMN3zUAFT1a+yAqYxPT2xckIwThBguqYCpuIA0yf1HPHFS274o8NJzBkSiD2Lw+F3IBE3r+RAk1k8YDIJ65ger0d4YAa8HeKxY1oYZg08i7/beOCbFw/g0zpcJdVOqE7i/buK17f0ualqpQImFTBVbr1SCB3oI32NLOiEddaSamhMHWjG1hEBj2bG69m6ld0u6Pf8tdN4ZI6N0XfDN8ZzLm8mhzjUK+8eh4e719JH+r2cd2n/F0avVdMNzmOO6f75Jl43v6VGO7lpnpaAEuUtEdya0EABl16SoEozqe4EhO4XYHqZ28OVuWQIU8r1lHZzxZb5XEr73t3ee3nrZb4nonqpCT87BJmmvw7N/NbGnNVfJmVt/S0w02Hsv5kuNlYZzrafqoCp9BHj61sn4bzHy6kn93ZJ3zpnQqpd/73/BcCUMuk7pMwfGpq8XAVMlT2UgCl9tU1Q+jwVMD1kgEkJRaiZStCgLeOWcgREqKlPzXOlpZOlQUhJYERuGBOAIDsusuWazngGUkfGVRWkKqgr3a/cNC2pmNl/P8IKG+mPlFAESZQWWXTN9kINFMqWcWBHeVaU2RPHLN9kLg6e0HwIAJC6g9RClJ3jItQyocYybp34sXRvdI/1WPlUHsUNpYKJek6y+quXUEMZtxdzlOYiq790Flo3JWCSlV4BjKvTCCIMk+ZNgIxUMBWl8qrKQ7l/ZA9JFop0RgYwfu43CHWc8Rw3OX/MUhZ5SsBESjhSVXkwDldIpUfnuxXjZ5D27m4zmOj/ZynzTQZMSos8GTBZ0m5UtsiTAZMXux0wyQomy+aHPRCAabinUKeE//ZCo6ln0HllCKxcbmKHXzoCInSIT8uDzlBQdps8YRhyC5CWk4eIZAN8I7PheCEVi71iMebADXy36wo6r7+I95efx2vzz6HJzEA0nhGIl2YEocXs83hnQTA6CnPos+UqhjnfwLwTcdhxLhWnIrJxLVmPFE0u9Lnlg0ukdErIMuHktSzMPBKHXv+EobH9OdQguDPcW8pdUgHTQ18qYLrnoQKmql/lAUyrJgTjpAqYxHXqLqxTJwVgavnILrR/0glfNzuAvzt7YP5f5+C0PAIBh5IQezUH2qziAZNRl4+UGB2u+KfjxI4YbLQNwZRv/TH4/eP44nlXdKjpJN57e+aIzsK+9JKeL6pqqWipgEkFTJUPmMwUNLSmBArIko6ymAgwEeiZ0kSrW/xxtG7L96eNbpM2mTxXjMoNdGiXE3zkufJkMRFc0oV7NM69fODTXP+N4wwHJjvqNw+I0C1sXSBem4ASWfMRYBKVS89zeCGDpSJKn7ICphJqilnJwMQc7kyR1Dm3PhZXTYqppnzu8sdb1Ziv8WRFTVF8f4rZx1Krsdnnynrx9q+RGq3CqhF/HlLRPtk8J3zeUNwXzdz3TdnLu6Vlb/nxUubukU6ZTtaTMl2su6ZsH/3C/Xz9eNAHAaaMIJ+XMk+4dE7fMttaBUzquNehAiYVMLGijeHXGW+IUlN/BeMwhJrCBBuoIWuppnBZGv4ERRKl+VIzm2AONYypyU1ZSJSJJOcv1ZTum6q6VCV9Xl3xs49KZf658r8JJhB0eVa6JmXx0JkYK60pWamRioGs1ai5K+cwWXpdZcCUJ82J1DmkBqN8IToHpPCgPKtfGFdlUQPaHKDc7VBmMMmAiRRAZC9ICiZqzjsxbi9IzXACO5Y6j8VZCfpL8yPFHD13SHn1bjHr818HTPL+UfYUger+jD8HCTBRzlEI489Req4SyLSUPZwyr00JmGzY7YCprHsnQ2jzLCo5g4nOBqnczAGTpZ73MkxWZjDJgImedypgKlv5cDu4ETSPUyDA1MDOHy0XBuPn7dex8GgiDlzIwpU4IzI0+cgrpbdYgKL8iVRMBlMBMrR5iEw3IOBmDlxCUrHCPx62R6Pwm/M1fLvjCrpuuIz2qy+h3apL6LAqBJ+tDcXXm8Lwy64IWLlFY9GpeOw5nwrP69kIS9IjVZMrwqvbrl8KbcrLL0CWPlf49zo4XUjFuL1RaLfsMurbBIhAR9yLETJYOs3XpbL2QAVMVatUwHTPQwVMVb+UgOnrW9lCHDB1fMQJ3Z7ci/6vu2NsLy+snngRHk6xiAnXIM9YHqx/5/GgAqa2lMFUbRc+rLEbnZ52Rp83DmJkD08sHX0ermtv4NzxZMRHaKDLuR0w0e8qvSYPiZFaXPROhfvGKKweexHWPU9j0P8dwedP70W7Go4ixOog5i/tFZ4vbuLc5NwsS5+fqlIqYFIBU+UDJqXlmwIy2b7As4/GPsat6iY8naeZ8XqWbuVnUfqdv3maDk9fYjyzpb8h7NDricFH6pZ1fym7KffMvx1MPv+MMB6evtWwc/AF/dKOOeK1reuLqint2LrQjq/PgQWBmCJKq7ICJnNAVEyRFZ+yigAjBViarABEdhzSaMRqVFjCeSxajaSS/pusB2UIoyiN7XPi1zUiqGl0O8CRa5KixK+9wOvW9RryoseyoRIe1+ZZ6eNzhf89Ua5nylXaYutpDgSphL3jirP6fE4z38zLEfY1e0O/61k7/jyUtXvkzCyH0b3SdoxofD9fPx70EenhUZsDpv2d07fNtU6b3N8ldWCLqAcVMKV+0RSpv7dDqt1ApC4YFpq6fOyKlOVWX8YsVgFTZQ0ZMKVvnDY/Y82koPT5f+anWfVUAdPDA5iUlm6NGG/qk0UUqQ62MZ55E8V4E1JuCFsSghTXLCYgQnZbZDdHqiDKi3IXaqVQYxjPVGnNuKqCFDek1KKmaW2zqlPK53Wkf1Nc1ZVK/pzgEtmiUXOWABM1qynThKzTqMlcXA5TVcm1ktfTKK0nwQCyEKPm827GQQ8pdL5WrKkM7Qiu3Y3tIGNF86vMARMBG1IGFQeY8iywRjLQ1LKyAya6L8s26e//oP2j5wn9/pYBUz/GbecI9sqAiSzySMFkacAkKx7J/vMUux0wkUVeeeCpUg0qKxiLA0wEl5WKUEs9780B02lWVMFE9p7KDCYVMJUMOITrjxLmMdITBJjq2fiixcwgdF99BWOcbmK9dwpOh2sQk26C3lRyc9EcMMmNtNy8AmTqcxGZrseZ2Gy4haVh47lEzPWMwcTDkRjheh2/O0ZgiEME/nS8juEukRjvFi1a4q3xTYJzcBpO38jGlSQ9krJzhTnkFwuTSgJM+cI3cox5iBau7xWRiVXe8fhlRzjemXcBdaz8OEwoApgqGcSogKlqlQqY7nmogKnqV19WmOHzNXMTAU5n5oyOCsA04HV3jCPAZHMRHs6xiI3QiNlBFTkeJMBEII6ykGiN2rA9+LDabrSpvRtdX9iLge8dgvW3p7FGWKtDW6JEcJQcpYVBm3f77yrhdyIpm2KF36vnTiRj7+rrWDwsCKO6eKLfq+7o8qQzPqruIAImulY3tle8Ns2pvzQXVcnESwVMKmCyLGySMntIKUSWdAQXrJ7ggIngwaSGubo572j0a3tGGByGu+SeWjpeH7y/s/56YNOYGN86d9rbxCNWdU1HFrY0HJ39p2G/7Xr9v7+f0a36PFU383/5IvQgtdToWtCOe1xSLzWS9rhZYU6UfQnWeCVBpOIURmawiJdS6dPEDD414Wog+jkRBEkg51Y9ZwZyFCXDHLIZpFwpgmjjpaLPKe9KOM8Ef0QVkAyaJjW6dS2xbBUlfu15XrbPF72OfC16XHquWCurPoeGYj0h1ePFl5VZ3fr5J4r+W/H79Xhm19jawueP8fuxb1agWdjWlLPmq4TsLb94ZW//a3H2jr96p2/7o2llvI48qCPc3b1WeuDpphmnXD/N3DpvfJrdAGcZMImN7pYKECDDAEs34+8ImNojze57pC4YHpq63EoFTJU8bgdMfxUFTB8xDi5bM/55VTlXKmCqqEENUWqg0t/5BEM6MJ4XRCDBlXFYk8C44qAqqGxKAiLm+UtkRUV5OCOF+obxZjeps6jhT43fBuWsZ0qoZ82KHpuasgTrXmK8wUzXJsBEYIayhPYwDu7Ifo6UYQQqLJVHU9x65kvzUQKUQKHchFrDuCKFLP86SvdHymOCdjJEuRurvOIs8mTAROtGzXkZMFU1izwCXrJF3kJpvgSYyCLvRfZwKZiUFnnmCiZSFcoKJgJMdMaqmkVecQqm8ljk0c8pLTKVgIleU4sDTJaApPI5NkrzoOe4rGCi7D163r0l3YOcsaYCppIBB8EHb6GEuYzzQi1rHzScfAYtFwRjwKZwzDgUi/0XMxCWqEdOKfZIxQEmeVBWUpouFzcy9DgXn4NjERlwvJSCTYGJWOkbj8VecVjkGYelXvFYeToB6/2TsOt8KtyvZMIvKgdXk/RIyM4Vrp8nWt0Ve/0SLk7XTso24nxMNhzOJ2OKexS+/CcUzWcEoibdfxHARBBGBUwPdamA6Z6HCpiqfpUHMBE0OaUCJhHydBPm0UECTK2q78bH9fagx0uu+OWjo5g8yA+bZoTg5J4YXAlIR1qsDkb97YApX7jnnAwToq/kwP9wAvYsuYY5Q87irw4n8c0rbuhYT3j8R/ZIgMlZhFqknuqnAqbbSgVMKmCyaMmAiYos40iBQ8DC+klul0eQiUDM3A/S9Rv7+ZsOTF5lOrtjsCn8dFtNckhDDw+PGsXtqUO/ftUTt/1Y17B3fHOjs3Vfg+PIxfqtgzx1q7on6Oa+l0+PKYKsMbVFxZTW+ilobaTcJRl8EVya1kxSXMlzLs7GrqmZJV1jM5D0YiHAsX1BAW5eKIQ7MnCyU9jKTZJ+VlQeKRVAEsyxNoc5Uo2XoA6BGFKDUa7V6Nq86HNpXelcayc+Kzz284o5KRRP9D25bBR1G7x6kq/lLfBTjwNCAkAyBKIaU0uEeZrRNctW9PO3VU1eox+FZlR1aEZW4x/perSncz9Azqoe2pxNP1zI3jZkXda237/L3PbjK5X9mvIgDQJMaWc8m2R47O2UuX2ulQqY1HGvQwVMDzVgMs8LoYYiZceQlRspDk4xnmdEVmlkmVYVcoJKahbT/MhujmznKDOKAJOcGURN7s5Cfch4JgplB7VgHKg1M6vmimphVvTvXlXUa1K9rqg3pKLrvMN4o7qLNIdRjAMIAkykFiDlBKk5CN7JgKkqrK8S2lHzmVRhl4U6ybiqbSbjDfMejOckvcQ4hKNGtKxiKu9QKphI/SUDpjtlMFkCeprbCFJz/gzj8GAx40q1XtLayCqY2uzu1V0PwpD3TwZM9PyhDKbvGFdDErg4IdQVVhQwWQKqKjPbCDDR89CDcQtIUluRgpNeK8wBU1mGUsEkW+TR8780wGQpFVcBK94iz4pxwPR/jENzFTDdGXD4SModb7Bx3qgh1OPjffHS1LNov/Qy/t5zHRt9k3AmSiNmH+WXQHJKA0w0DHn5yNDnIibLgCspWgTG5cA7MgvHIzJx+GoGDoVl4MjVTBy/lgnP61kIiM7BpQQdItMMSMnJRY4xH6a8ghKvUdy0yBovU7TG0+JQaBoWe8Tgt13X8NGSYDScHIDqoyWoQzXyNAc9lb7+vipgqkqlAqZ7Hipgqvp1J8D0+ZN78d3r7rDq5YW1Nhfh6RKLOAJMxdiT3st4kADTV8J57SrMo70EmFrX2I32Tzni69fc8GfnE5j9xxnsXBwGn/3xuH4hE5lJBuQab39TBkG6zFQjrl/MgpdrHLbPvQL7H/3xa9tj6NnYFZ/UcUDrartFwNSJuQj37io8Vw6KcGkAOyzM5ZAKmKRSAZMKmKoMYKLPpzTlNm9yHhNBkXEEmV4y6ZZ0iDT8+/th48ml840h7j+YYi+/mxYe/kRxe5qx+Zv62dsHv27YPbyHftcfkw0b+x/QL/s0Ujf7bZMIl2QrPirKXyJwQlBn8ku43Q6vhBwk82wiGRDZlaQGev4WLOIlfG77nKQQeuF2ICXDJckaTjyHt1RCCmWQlQx4pBr3OAcuojqrJnJG1UDOyOpCCR9HPVoImchijh5bBkxFgFZ5AJN8TQksietapxAs3YJGBIVqlL3o54st6fsEl0YwXgQKyWJxznvIWfk5sjcOvJq9/dctWTuGDMrcNLhZZb+mPEhDBEzB/o0zvPZ3zNg2b1za5P5O/wnANPl7pC0aGZq+wloFTJU8VMD00AImpZ0TNVGpmUpZQd8LNUMoB8ZVK5QVYslmcFmbxdTsp0YpASZq4B4Qaq1Qk4X6nXFVQnfGQROptNqVUO2lamf2kaqjWdHjdCqmPpWuQ1lWBBoILlGDeRLjtn0ujIMSWcEkA6aqBPAKpDlppDlGSHMmlY4M7v6fvfOAr+l84/jRUtTee1ataqvU3rOoUauooFRVzURCJm4ksUeIFSHIJUhIROwVIgsRe5UaMWpm3HvWvcHzf5/znpOcRKhV9/I/7+fz+5x7zr25Z733hueb3+/Ba4oQASEbFtMxZvFNezFlBUwIZhDQoBMIezDNYuicjJGPBcGApaIF1Q4YBEw3GPpZCZOvDYJEdKwhIKson4/li/T/7VDuH8apobMPAWwzhn6fuBGtZijEQcCkRORZGjApPZgwAhLhF7qsMB4OIzXx3qHbEf/f8joOJgXa43VQ92D6g7E+wIT7VZyf15nMDib83lIDprfpr/b2w+oBk6RoYOyjJMCUwy4SctlGQsGJMfCl5wn4aeUFmL73Fuy6kAzXHonAZVMwe5WBZUnz02fAmp9IbqZ/jCZITBHhWpIAVx8JcOURXV57LMLNZBHupJokoJUqPJFi8V7W/+lFgzM9gVvkvY78nQIrY++CbchV6Lz8LFT3iocCjrEUJuD1xz5M4y0EYDTAZF3SANNbDw0wWb+yAqZOasD06Wb4oXAo9K+5Cxy6HgFfl7MQiYDpb1Zy37zLIQGmqzJgGnUChjawLsD0swyY+kiAKVzqh9ScCZYAU+PPNkGbEpuhT50dMO7HQzDf9gSELL8C8fvvQ+JFAxiTTNlerzTxKTz+R4BL8Umwf1Mi+OnOgdPP0TDwu93QoVSI9L7fMwiYgsk9CYUu5LPSS4Zd/Znd0jFpgIlKA0waYLIsYFJi8hRVofAGI+EQloz7DIxjPwPWntwD95qpwtJul8TQidtMMWunPblyuLtw/WTlrPfzyqLOuQ2rB9QUA//oxm/401FYY7NBWNT+LO/1lQEBigRC7GQ3j0MB2s8H7y1Coky9ktSOJCXSrpwq1k6lTH2MymQAJUklM8CS4kCSVDxLTB2CJRlSub7MwaRE0ilOpqLPR9JJsCk/hT22ecBom5soTzpQk16L+0aQJZ13xQxHVqZzzibOT+kF5aL0X1LH5SF4KpZNRF6WeLt0ZRONp7wm24g81fvYKyArL93XlMrAzv4e2CVdnhj9B15g1w7zZ/W/D9QcTC8f588HffboVEy55MNhLZP1cyZQwFQ9HTA9sHbAhJDiOxVg6lYJHo9oCUmTB2qAyUIDAVMKAqbV7rOTl7slJM/+82mSQxd4PLAWPOyoAaaPHDApjgMsCKPrBoEIukUQguxhaDEYC7CWiiJ7nWKx2m1zlqEF40CGxuQhZMKiP0IejP8bQjRY1qAsGpxF6u1DVPpVtVQ0VPUY9zOcoXDEVj4GdLcEyNcWi8xY1FV6MFkbYAImA9yhMwyjB08R7WZoIX6KfP5YPP+aocV4BCn4f483iYLLDjBhxBy6pLA4P4OhPaAU55cazFkKMImqa3OSoRGCPkxG3y90r1VmMtxdHytgUmC1Eg2HUALdfK0Y+rlxZ+i8j2RoHJ0SC2mpvmPK/ePkY1EA0wqGwhWM1FQDpteJN8whXwcETBgvh9+rWSPyEpjMgMlSMYFKrzUETBjz+G+ASXMwvVT2RA4yZLI9DDnGHIJPx0dCMdc4aOp9GsZv+RvWHn0Ax2+wcC81DUxvUWTEhDuMuTM9eQZi2lPgUebMEsg2fB4dS+hCelH83cuOAvfxkDXD2bssbDn1ENx33YC+/hfguzknoJRbHHzmIEOX8QqAwWsRK+s9XnsNMFmXNMD01kMDTNavVwFMA2rugokKYAq9DXcRMD35/wVM3cj+2zGh0EwGTE1yb4L2ZUKgf72d4NArEpY4nYIda67B6SMP4R9yrXhDGjx7PiFP6sv0IJGDM9GPYMfa67DY6TTYdY+EPl/thNbFNkODnBuhPjn/pmQ/uL8fyX57k/0jXNIAU2ZpgEkDTG+nrG6ft/h5hEvuuKwsgRwJGozLDcbR6MDJQ9ZLPeFmfJ8qrBpw3rTTY6P5RLBt2tXIZkl/7ysUEaHLGe87IhdK9P+lKrd2cFfT+t/dBP3QTfzyn05xs75P5lzKAzshH3lPdMB8Rt02GBOHDh4JHKmcSNn2IlJF2kmxdmWzuI4UyVF4rqVfAJgQLFG4xKp7IEn7La9yQinvrd7Xi+CWyjGVDraoY4p1LPFMknPJp6xL6afkGJ9xkys+kyIAPaoD51kLOK/awE//CngvVK1nvFftZ2S7SmTdS5G07SnnUfMp51nzCXn8hJtWK02SBy5rEtUgqk7Wq5u5aV8SVaNyz6ovXyjWvbopXdNqqCRv01UzsVO/oJpWy8TOrGdiF7YR2OU9bxtX2xw2BPw237BuWM+kgMFaD6aXDARMDxOiyiYd2t4ief1su8eTfw7+KADTlIGQNH+8BJiSJMBkpwGm9zQ0wPR/C5iUgjC6TrBPTH2GOlLQZbOOoW4VdANZuhH96xRKFbcNOoMwJg9BzgaGFo69Gdr/aDqRF0Nj3jyykWcWvWj7i6S81kveFzpvEHL5Eq0n2sFQF84FhsIwLO5aKurtVa+rgaGxZliIR0iwUT4v7DWETh0EKeg+RlCJgOFNYvLUgAkddVjcx4jBHxgK6rzk63dYPg4lZs0Sc1NxfyiuOXT5Ya+yXQx1zU0i6kvURL4uGBn3uXx+bxIfaO1DDZjyM5mj4RC04r3DzyH2HUP3mTre0NKACd1U+Fncx9B7h848nNPonsM+avj9+KoOJvV1wPtdgsncgwnjMbM6mEQLXQNgMnowvaqDSQNML1U6YELgchiYMRHAjDsEeSZFQa0Z8dBv9SWYsecOhJ9OgQt3REhhn8LTbApn72M8y6IXDQRVNx6LEHklBZYduQMjN/0FLbxPQaWpRyH/xGj4BGMBEbog3LGVIY8GmDRpgOmthwaYrF8aYPq3a/PvgKlp3k3QsVwo2DTcDU79osB3yhnYE3gDzsc9hvs3eQkkZf3jiGdPye+m1DS4e5WFEwfuQ+jyqzBvfAKM6hgB3b8Mh+YFg6HeJxvSARM6prqS/fbRAFO20gCTBpiegz26V1XVbKR6Pv09syzTn88GTOkqZwAmdOfYfg7GMTnBOPpT8jgfuQcVgZvb/KGw7rco84H53uaEoEHm0+H1TPGBNU0HZ37Fbh7/Dbd2cA/B/xc3cdWAEGF570v8vNYsN7U6cPbk/cblAnbspzR6D501CH4k95IMa5RoOjmWLkPFaVScFGknR8qpwc9kVQ8lNxX0UdxMzqXSI/GkOYUOLbJfVgJGqpg9BVC5yU6pKXJkn/sXwE/7EniPGsB71nzGe36Vxk+vY+a9vjIRmXkyV/lp1Z+S1zzlPb58Ql5nJq/jOc/aqaxXncfczG/uczPr3mNn1r/Hzfr+ATen4WNuXsNkbl7jVH5eUwM/v5lB8G6Ryi9olcx7t3zML2z9iPNu9TBDbR6Rz4Ss1g+5RW3vcT7t7/CLOybyS364xi/tdJVf2uUvokv8sh8vcku7XJC0rMt5bmnnc+TxWW5Z5zOSlnY5zS378dTz6kq1tOtJFLu8e4Z8e6jUnSrT9p8SWL/e8eyqfnHsql92Gv0HL2dXD7I1rrZpzfoNKGXp7xhrHhpg0sa7HgpgStEA0/8bYMIaC/5lPv7/HvultCL6jaFFUHRinGFoEV9xGlgT/HhRwVgp+CO4QZcLOgUQSKDrBuPLMN4N+/hg1NqmLNoo60Xb/00bZAWqHm+S94VFZQRL2MMojqH9jG4w1B2GUAyLvNbmXlIK0OgQQhjwmKFFaAR3OD+WMBSkDGBoVCAW0sswmR0frzMUwIQ/i4AJoSc6o9BVh86waUR6hsasIRC4y1jOAZIVvuGx4D1FSIF9fBDSYjQcxipifCAW6d8UvH0IQx23iUAGwQzeO4ykRAcfOnc2Ex1l6BxSerpZ6ntF+b7Azx4CpvMM/Y5YylC3IfYf+oZ5HjC9ysDXKX3tsgImdUQeut4UwGSJz766BxMeB94XBEyrmex7MGkRef8qe0UIIvCYEDBFQA6HSCg95Si09D4LIwOvw+IDD+DAORau3zcDxz8DeLO0vHcyXgaY0Pn0yJgGp26zsOXkI5i6/Qb8tOIc1PA4DgUnRkPOceQcxx3JDF00wKQJpQGmtx4aYLJ+ZQVMP2QHmGrtgondjoCv61mI3Hob7l5j4enTdw+Ybl81wr4NiTB7VAIMbbAf2hcJhYYMjYmzBsD0swowtZUBU2NyfM0+D4JOFbbCkCZ7wM0mBlZ5nIMDQYlw6UQSPLojgFl4/hfkU/MzMDw0w41zqRCz/S5smHcZvH4/BsOa7yfvFQaN82yCujkoYGpG7kUHsr9u0nnvhAEaYHpOGmDSAFP2cOkF0OiFYOlFgOnfnEvy+pQsfY4wgg0j4OzygxFj8kbnAJaII+vc5MpmYVHbK2LQ6DDTgbkzzLErh5uPLBtk3uM1TAweNUr07z+TX9otVFjQ4TI3o6mJm1IbWAdyH8d+DuyYnGSZS3IycY7FqONHgUR4fxEC4XbsTzSxIHDYnwmXkwoRFaGwSR1rhz+b7n6qSHs4kXPh01UB+HR3E309O7k8sNhripw3S64Z7y73oJKuQ0X6PvgYoZJnLeBnfAP8rHogzGkIwtzGJmFBcyPv3eox79PuPtE9fmGbB/zCVo+FBS1ShAXNUvkFzZP5hS0f8IvbJwpLO13iV/Q4ya/sHcf794nmV/WNITpK1hOElb3PCX69Lgp+vS8LK/teFvz7XRRW9z/Hrx54il9jc4JbMzieWzvouLRcM+gEeZzABZClfsgxfv2wGCFweISw8c/dfNDYMH6z3WZ+i/1GPmTiOj50UgC31XEtFzppjRDquJpolbB1kp8Q5uQrhLksI1rKh7kslhQ+2Sd7TfXhtk9ZxIZPXfgicdt1i7idHovYXZ4L2R3u3myYy1w22Ha6Yd0IJ8PqwcNSVw7oZPTrVyvJt28hS3/HWPNQAJMhCgHTXLvkqRQwPWqdS4IAHyJgSvqjFSRPtYGUBeMvJC9x8kla4qgBpvc4JMDkj4DJY3aKr1tCyuxRT5NlwPQIAVPjLICpmZXMKw0wve1QiqAI9bEYjAVF/Mt1jD87xFCnAcZ/WfIv7N8EhnDycf/D0KIpul0QliFsQjhyVKU4Wer1Y1nWY1Wvi82yrn4el+hMilYpRt5+TN4/Qgh0V2FxGeESwglLFtpfpQit9GlR4gfxHDBODCPP0K2F/a0QJKDjoxJD4+DQvYEw5XUcDwpgUkMKLHBjL6shRFMZWvzeLx+D4v6yxPzM6ppDSIHz7JB8XRCG/SofOwKG0kzm/lQfW0yeApgU9xnGG2LEHDqBMJoS+1JtY+hnAOe+ct8sBVaU7wp0wCEcxO+HHfJxjmFoLGMdhgJTdGS9DhhUAyaMyMsKmLD/WnY9mCz12VYA0w2Gxk/iZwz7UHWVr4EGmF5L9grwOALM+ENkSWR/GAo4x0JNz5PQZcllsA+6DasjH0PsXzzcfmQGXny3xcZ3MRAuJXFpcPm+AHsuJIPPobswIvAvaDb/FJRyiYWc48n5jUaX1hEKduwtAJXU0gCTdUkDTG89NMD04Ugp0CNgQpDTktkMLT/dDB2zA0zX/1vANGdUAgxrsB86WAVgouqr2hfO27ZMSAZgyhcMXSpuhWHN9sLUIbGwZvp5OBRyC66cSoGkeyKkmZ6/Vmb+KTy+LcJfx5Ph4KZEWD3tPEz+JRZs6u+B9iVDpXi8b5lACTA1J/eiIxMq3Z+fJcCEPZh2SY81wJR5/mqA6f8dML0FlHrOiVSJSulnlA6OKqhUMbNU/Y5Y7PGD/X0wSs6hsBxrlwvY0QywY3OSbYUw1u2B6Nv1hBg8dqu4032FeY/XUlO4s7+wYcRGwbfnQW5eq/Ose93HrGPVZ6xtCTCOJu8xKjewY3IDh06oiUUoTJJcRGWpo0iKkytKnU3Yp0np8YNLXFd6F0kRdyVVgKk8PQfp3Clo43VfSOCI11UBfkrljJ5O+DopCrAacNOqA+dRk0IkSfJjjKqbWRf4uQ2BX9AyTVjcgROWdU4RfHvcF/x63RRX/3xZXGNzWggYfFzQ/3pM1A+OF9fanBbX9D8nrul3QVrqB8UL6387LAaN2W4Ksd9gCnNcJW538RXDXVeYtjqtFkInBoohdiHiZttt4uZxO8TN44nstokh9luEsEmbhK3O6/ltrgFcuMtaPsxFz291Ieu4zWU9F+62VtipWyHumb5Q3D9npnDQewp/yGcSH+lrKx7xG81F+//JRfn/wcX4j+Bi/YezcWuGCjFrBgtxa22Eo+t+4Y+t68cfC/yZP7q+Lx+3oU+6jiva1FvSsY29XqoTwUQhvfhTW3tyx4N7cFGru7B7Z7UzBDk0MQb8Vid5df/KqSv7FsWeXJb+jrHmoQZMqRJg6h/8WAWYHn4ogAnVJDc86poFMC3TANP7HmrAlOrrlpA6Z9TT5Ik/UsDUgQKmBxpg+pgAk9ptgMXgygyN8hrI0Gg3dBpgARQL+Fg8t1b48bKCKTpusGiKUVz35XPBgu5NWTdk3cxmmfU111XL69msZ33ub4bCub9lXZO3J8rHgceDDg4sblszXFKkFOPV8YMIznCeYPQfAoTeRE0Z6tZBYIlF+deFKVkBE0IZ7F/TiqFzE11BCD8x9hCBAMbSpVjoGqohBQJNhIVX5euCrjWMD8S+UQgqsI+Uuj/Vx9iHCc8HzwtBBP7uxl6ajRgaE+jI0HhIvG/YGw2BDoJVS7r2srrPsH8WAjDskTaSqCNRbYbO5XzM690zdS+qUvL7ZAVM8UyGg8lS10H9fYmfoxtMZsDUjaGACSHZ5/I1sNz4YABTusjx2EVKcIlxiITcE2OgtNtx+G7mWei74m/QbbsLm+OT4eRNHu6npklAx1oG1j5ThCfw9yMBDl81wKq4B+AYdgO6+16AWp7xUABjAMeQcxuVBTDZa4BJkywNML310ADThyMNMD2vVwVMzfMFQ9fKYTC8xX5wH3YU9LMvwpGwO/D32VRIeWiSzi3zLygAIfUJ3L/Gw7nIR7B79XVY7nQGHHtGQb86u6BNkRD4PgcFTHjuLci9+IEJlRxmGmB6+fzVAJO1AqasECeLXhZh9zq9kdQgSAV7MsW3Zer5I0e5uZZRSY6EU6Lj1D2BVD2I0uPmcN1ZjptTehq5IuwpSwETAh/yOgn6OBQAdnwuCprs8uL+0/h5jR+IK3v/Zdr050lT6IQEccu4C4J+8E1+aee77PQG/7COle4aRxe+bfw9523jcOY2+0fOW+zYvLe4CYUSuUnFEslxJZJjTGRRziUS2UlFE1mHQonshHxEeRJZu9yJrO1ndInruN2hMH0deT3+LDneRHJNErkplRM5XVWiLxK5adUS+WnVE3kPInyM26bgc1USOXfy2ONLotpEtSTxnrUTea86idzs+rc47+a3+CUdbvN+PRKF1f3+FgMGXxDXDTslbBxxTAwafYSc414xZEKYaavTRlO4y1pTuOsa0zbnANM2p43i1knBYtikLWKYY7Bpu5te3KlbZto/e5YpYqGrOWqxrTlq2RgxcvlY8cjSCaaD3i7Cwbnuwr7ZM8TdM2ehhL0zpgv7Z7ubDsxzNUV4O/IHFjrwEd72/EHvifwBXCfC7YcWTxAPLx0txKwcxseu7SceC+wmJmxqLyRsacmf3taYPxXekDu743vudHg97tTO79gzO742nt/9leHMnpqGi/uri2cPfCFc2lNFuBhRWbhwoNJzOr+vIoo/e7iCpNMR5bMVPneV6Epcee7S3rLGhKASSft8C90KsssboWudU6dLz7f/2Aov73RogEkb73oogMmgAab/J8CE9RUsBmPPHPwLe4whw7/cx9izvQx1YyBMwOK9NUa3vaxoiseLhX90SGDxH8EIFpKxmJvymkrORknZrKv1OBspP5MqHw8nH5+1wyX1NRXk80D4hgV57DeEva3ciAYztN8OOuEUmILz63VhirqPDxa2EVg1J+pP5MRQULFT3n+ifE0tBemUmDVedV0QHGAUIzphMGqtJ1FDhgIXtbPrY4vJU0MVdLzUYCgYHMRQ5xm6ujCqEmMr8XtFAdeWcu4ogAk/jwieEagj+MEebejIayOfA56LAldeB5RmB5jwfdWACfebwmQ4mCwZ84ifIwThSkSeApjw86wAJq0H0+sJQQQ5Jvsjkj4h6/kmxUH5KQnQZP55+FV/DeYc+Ae2nUuCc//w8JhPg7SsjSYsNDjTU7ieJEL0dQMExD8E152J8PPay1B/7iko7XoUctmiewkBE153DTBpykYaYHrroQGmD0caYHpe2QEmvE4IMdowIVJvJARMLfJvhu5Vw+GPNgdg+ojjsGHBZYjd+Q/cvGgAY7L5uT6FT8m5Gh+Z4fYFI5zY8wC2Lr4KC8eeBLtOkdD7yx3QssBmqM9sgLpMoNSDCuMKO8nn/bPUg0kDTC+avxpgsjRg+jeI9LJYuixyVz3+N8CkgCUESG4ZPYik88Z+Qc5yzyBFziWogwehz6TC1O0zsaC0lGLlHDFGriiNksPrJr2GPO+gOILyAGuXm4gsJ3xOwZEUPVciHTSxruWo0MnkpjiayL4nobOogOQk4lzKAD/9axAWtXkiruwjiuuHmMTAYSCu6Q/8wg4mzv2b6wbbkkcMv+XcnDqYCUwdwqwzjPhEbxiTR8/aFdazjsX0rFMpPXlfvYEsDWTdMLGw3uBQQG+wy0v0md4wPpfeMO5TusR1u3zk+YLktUXIz5SUfpYcm56dXF7PTq2iZ3VViarp2WnV9fy0Wnregwgf66rT7fg8WWe9ahHV0bPkeWndo4aen/HtOt6nzXrBv3+gEDxmg2mH23rTHq+14r5ZK8z7Zy82H5g933RgwUzTofnuaYcWOouHfOzEyCVjxCNLRuHSHLnELi1y8cS0I0sd0yKXTjRH+44zx/oPNx0P6C+e2Ng1LSG4XVpCUCvhZHBrhEFi/IYfTUfX9TTFrO5rivLrJynarw9RDzF65Y9ijP8PYtzqDmKsf3tpieuo6FUdhZg17YSj+hbcsXUNjMc31hHjQ7/gT28pz54NK5V6Pqho8snQwknxQYUeRoUVeHA+KP+tmKC8V3buzB0f75srKCjoY4xy+aBHfHx8Li4+sowhKrx56ro5thpg0sbbDgUwsRpg+n8CTEoRH/vc1GeoAwUdIusYGul2g8lc/LQ05HiTwmmaSiZZCCNE1boiUbVUS9kmqCRms00RL0vIsuSz7DtNPkZLFJbfRIrTAUEdRg9eZCgwwH5T6NYZzdA4tAZEVRkKLl8XpijOOjWoqMZQdx06YbAvzGKG9n9CIHCDyejlYykHiALe8LOCjqrTDO3lgyAMgRj2p1L6MGGhHj9z6ND6mP5tpe6dhf23MNoQ+xf9wFDXDs4P7HuGMZIIMRC44ufBkoBJiX1UnDt4bNgrzYuh0YatiL4kKsa8PijNDjAhwEdHGwIsBEwY1XmTsY6oQNw/AqbrDAVM/kxGD6av5XN4Xcj27seHCZiI7PG4iGyj4FP7aCjgfBSqeiVA22XnYVTI37Aw6i7s/isZLj/kIUVMe2E/pPc1ePMzuJ1ihribRgg8+RCm7rkF/dddgUYLz0B5XTzkmxgLObDv0hhZ4+XrrgEmTWppgOmthwaYrEt9sii7An1WwPRD4a0woNZumNQtCla4noPIrXf+c8A0d1QC/NZgP3S0MGDK7tr1InP1RyZMOhYKmIKgZcEt0PPL7TC6QwTMGX0CNi+5CvH778Odv1ngjeR3ovpSkcdpwlNIvivCtYRUiAm5CxtnXoZZw+JhdMsI6FExHFrkDZYA03dMIDQi59+a3At63tvTAVM/or4aYHpu/mqAyZoB02uApXRl7YOkjqtTPVai29Q9iMi5SgAJz1taFpPOX5IEjeQIOYyPs81N9JkEjDiyzjnkz+hZhPAJAZL952Akzxttc4Fx3CdgHJuDiCzH55S2S6/BfTiXktxLEujC48JouXRQVlk6RtaljORukp7HOLk5jUBY0hHElb1AXNMPBLLkFrZLYd2/jjTalliQMizXSMNgZkjqr8wgdjhjw/6Zx4adUNCGdShmw7qUJCpDl45k3aEIeS4fEXnN+M+IPlXpM7pd+tki9PXSzxJNLk9U0YbVVSGqZsNOq5FZuE16TvW8V235uSrSUpj1/SBhZc8hQojDUPPhxcPMJzYONZ/dMch0bnt/0+nQ3qYzIT2enAz7Me1UaMe0U1vapMUHNU9LCGpijt/cCJdpp8j6mS0t006Gtk47s61V2rmwZuTnvzed2fG1eCH8S+HCjkr82T0VUMLJ0Mri+bBqpjPhNU2nNn9lOh5SR1rGBdUWjwfVEGOCqglHg6oIsRsqC9HrK0nLowFV0hUfUJGPWVvOGB1QMjlideF7ewLynQ8K+kyGR9r4wIYEmC7ElzFE7WqeGjjHNkU3IChpQI3rj1p/RgFTPesHTFiYf6AAJrkHU4rOBlK9MwBTqgaY3tuggMmjLbvWa7bRb3KCYe7opymTukKSjdyDqUkWwGQt80oDTG8y1MVgdJkgDGhJ9BvRXIYW7zF+7B7zYcXjZVc8VYRF1CdZ9FS1/WWPs3v9i6TArKxwKy2b91COzdLX6VWljoPD2EEEBdhXCt06Sxkag4YwBecSOuKwd43Sc0hxJ//bUAMmLGgjpML5iQ4gdAKhI2gR0VZ539fkY+EYy0eMYdwhfmaUPkx6hvanws8Vxq1hoR5hLkZSfmwxeUrPIQQxWCusTPQ90U9EdkQ+RNsZ6jpTXDtK3yxLfAYUMIjHgIASYyyxX9p6Ih3RLwyNe6wqnw/er9cBgtn1YELAlDUiz9oAk+JgUgMmjMhTAJPmYHoj4DFBhhK2eHxHIKdjNBTRxUGt+SfgxzXnwXb7NVh+7B+IuJYC15IEMIhPLAaZxLRn8I/BDCducRB85jFMP3gbBm24Ao19zkIFjxPwOQIXOwQtURQsoawFuGiAybqkAaa3Hhpgsi5pgOntrx3O1S5MGLQmx9JEBkytC4VA75o7YXznSPC2OwXb/K7B6SOP4MEtHkzC08wnSlZF4xN4cEOAS9FJcFB/C9a4XQD3n4/C7+Scu5beBi0+C5bOGSFTE/L+bcm+cJ8ImPB8+2mA6TlpgMnaARNCFlmv9D6VIFMPJAUgSdF2qng7CSipou5cytAoO4yvU9xJCJJwieuZAFNhCoUkwJSHQiaMrbPPR8GS5GCiUXjSz5DXGycWACN53jghD4VNKPu8ZD3fM6NDgSfspCJm1rGkyDqXFTm3CiI3pYrIuVcTOY/qIudZkwofTyNyr27i3GuYOK/aIj/zO5Ff0FwUFnc0Cb7dzEQmzrvdSc6z3hKjQ8WfDSMK1EwawVR8PJSp8HhUXqoJRalcUWUz1iXlpZJey6iUN+M59evx5zPpi2z0gtfoypV/5Fq+3ENdjbLcghZl+HUDywv7ZlZEACRci67E3zlbgbtxoYzx6umSxisJJQyX44sbLh4tlnp+d9HkkxGF0SmUoYjCKWeOFEElX48onPT3vkIPL0UVuHd6Tz7JQXRlZ250EaGuR6zOg9vuxod/js+jy0hSRFD+e6cD8qHuxvt+/jLdipmf98rORZIrKSJClzMoqO+nOp3uVYs+2rCiERERkZM9f6y0IXZnM3b93PEfG2BK1QDTex8ImIwaYPp/A0xYMMTCIRYQfySyJ1rFUFcKFlzRZfAh9Ad6nWLqvwmyLLM+fpey9PV406K82q2D/XT2E61lKEwZTtSJ6Duiigwtzivuj1dxMWUFTPg7oDJDHXYY14URjvMY2vsJXXbY8wh7HyFgMlvouirgDR05CnhDN8wWhvbzGUvUg6HOLjwXtSPmY4jJU/dzU4AKurUQNGLfLIxPRGBxgOgCQyEcwji8ZpZ0RuJcVu4ZxvZFEq1hqIvzZ4ZCzUoMBYKv6zjLCpgUBxMCJsXBpO7BZEnYpkTk4Wc6O8CkReS9NfBApQMmcpyTjkCeyVFQanoc1FuSAL3WXwDnvTdgbcJ9iL6ZKkXTYf8jzvwUTE+ewTuuQ2Ya+NZpZAdC2lMJbCFcOnWXg23nk2Fe5F0YueVvaLv8PFSdngD5nY/KAEcGS+kAzUqkASbrkgaY3npogMm69CEBpuEyYGpkRYAJlwh5OjNh0IocS2MZMLUpHAI/194F9t2jYInjGdgdcBMuHkuClAfi8/2XngDwKWnwz18cnDnwEHYuvwHLxp8Bly7RMOSrvdC5aBg0zxksgbWG5Lyxz1M7JkRyTWmA6cXSANO7AEyv2BPpuf5IWePq1FIBoikVqJQeSFklASN13yO59xEuXeQeSC4lM/ogORenQgjkrGwvldEryUmOwZOgUnHZWVQaWDeMrytD+yxJr1X1VCI/x5PneHKcPDk/3r0a8NO+BG5aNeDcvwBWV/kZO7XSU3Zqxafs5ErP2CmVnpB1wTi5/GODa+kbRqeSZ1jH4nFkGUPOJ4abUiWGc/8yhvOqFcNNr0P0dQw34xuiuuQxWXp9HStp+jdx3Jzv4/gFLeL4JR3j+KVdormFHVZyM5v+bpxc+ytGAx6vM3KgCwmBETqSUAiRskoBVOhcehCxJP/juHUFsfcRuplSjiwt8ipK3b2yqGH/4mKSInyLZydj5KIS6dpJtGdZSeOeOZLY/d6l1MLn8L0wmg8BGYI0BCeMdv//dWiASRvvemiA6f8OMGEBH6OsEAI0YmghGKOhsCiOLgOEBxiFZukisCbrkbpfCwKC+wwtzMcwFPgsYKjDCKMWMdIO48XUkXCv42LCfwvg/1+w7lSBqC5RZ6KRRDOJNhJFMZn7+ZgYy7lhEMIqLhB06JxiaH8qjMlzYagjphVDnSylGers+lhi8hRgjfcLYQy6tDAeD0EjAhW8Xxg9h/MEgSACHSUez1KgVblnCCZx/qDrDEEp9hNDsIJuuXoM7SWG35O5mNe7T8ocVgOm9szzgEndg+mJha6D2sGEf1jwsoi8170O73Z8eIAplsqWaHyMDGXIcTocBsbpMOSdEgUVZh2FRktPwYCNl2Dq/kRYd/IBHP47FS7c5+FWsgkecWkSaHr6H/RmwrcU055KMOuewQxXHwlwPNEIYeeTwPvIPzB26zX4cdUFqD3rJBRxPQo50LmE1xg1PhpykHPMYelrnOl6x2iAyZqkAaa3Hhpgsi5lBUxqqQFT6yyA6Zdau8GxWxT4IWAK+28B0/6NiTBvdILk5vlBBkwNJNDyfgDTyyAcCiEP9kPC64NwqXGOIGhHjnPA1+Qa9YoBv8nn4OCm23D1dAqwKWbI+qvvqZn2X0o8a4Dj4fdgy+yrMO/XBLBtfhj6V94FHfNtheafUHCF7qUWZD8dmFDps/KTdEw7yXnvktRHA0zp0gDTmwKml/VLeh3ApHIbSfF16tg6BR6VoYBH3QtJ3SNJ6YvkVFTujVQkI95uUtGMuDvcnt4zqaAUYcdh/yPHYjIgKktUDnjF4TS5HAVbeJzuXwCHwMijBnBetYDzrC0tea/awE//CvgZX4Mwqy4IcxuAML8JCAuag+DdCviFrZ/w3q14fmErA7eoTQrn0zaFX9zewPm0T+Z82txm5zU6xXrW2m6cXGGZ0bGYh9GpuM7oUlpnnFJZZ3SvrjN61NYZvb7RGWfUlVWPavrX7kaPr6ZxHnU8uRl1Pbk5TT3Je3tySzrpuMWdhxnmtW2arKtb2NJzy1oGgiN0G50/H/QZLlVuoxzKcwiNHsftLJhyZnsRQ3x4cePpkJKKsL+SpGNBpbn4LWX4uC3lhYQtlcTj66uKR9dWN8UG1DJGrfmKjVn9NXuYKNLvG2mJilEJtx9Z/i0bvaIud3jZd1ykbz0uYvn3z+nQkgZ85LKGkg4ubiQpYlFj/tDiJvx+ogMLm0o6uKCZtCTPcbH+9YxxQbWFk7sqs2f3l3p8ZWdBPF/5XLXxgqEAJh4B08aPBTC1hlSdDRi8x18wLnPyMWiA6b2OB0t0MmCaMdu4ckqCYd4YGTDVhkcdC2iA6eMCTPj9iv82RCcFOg2w8In9c5YQ7SO6zGT0SPlQ+gNpej/C+YCFeZwbOEcw4guBJMIULM6jW2UwUTuGOuOyRsK9qosJX6tEOOJ7YJEbHSDDiDwZGj93iKF9oLAfFMJQpUhvqT5MWKRXx+Qp/ammM7T3DgIydHZVYig4U/en+lAhU9aeWRhp+AVRY6I+DIUUGJ+4g8kA1whULNUzS7lfiusM7xfOH3Ti4RzG/l7jGeroREimxDy+DiBVrosCmBDOvCgiL5HJDJgsGZGHUYEIAHHeopM1u4g8DTC9HvBQASaEFAgmEDDZHwZm4iH4xDkSCulioOrs49B8+RkYtOkvmLo3EfyO3oPtF5Ih7oYRLt7n4W6qGYziEzA/fZp9ZfENBr4VZ3oKD1gzXHsswsk7LBy4kgwbTj6EuYfuwJjQa9Dd/yLUn38ayk49BnkcYqhzabQMmMi55LCPlWTRvkuZrneMBpisSRpgeuuhASbr0ssB03boTu5FRyZUcue0kAFTRwUwdY8CP7dzcOQ/BkwHNibCfARMDfdDp6Kh0DjdyUMBE8KdHky4dMzUwfN+AFMv+RrhvvEYWsiAqUmOYOhQdCsM/GYPuPSNBf+pF+Dw5jtw/VwqCMa0584zTaT9l64eT4HIDbdB73YJPHoegz++OQg9S+6AdrlCoXmOzVJ/p+ZkH62ZEAn6dSP77clQwNRX1rs+9w9ZGmCyFGBS+iLJUEntUFLAkmuZdPcR61w8I6ZOcRZJkXWq2DoJHBWg8XUOBWWYVJiCJSnyTvUaIs6hIAVM5L1419LAT64A/JTKwEv9nKpRoOSJQOkr4GZ8A9zsesDNbQj8/GbAe7cEflFrEHzagrC4vdQHSVjeBQS/7kS9ngqr+nLC6gGPhbUD7wgBg6+J+qGXxMDfzokb/zgvBo2+JAaPPids+D2aX9Vnk3F+C3d22pe/GB1LtDQ4FG1icC7ZxDC5UhPDtGpENYm+bmKYnkWedZoapn/VzDC9bjPDzPrNDXObN+d92jTjF3dqYlzeozbr3b2UTvdRxIU8N27dismbeiumKHs9ojR3Kaosey2uVMrNI0Xu3o3/HGEBAhVc4utwO3v9WGnhwoFK4pUDX0j6a39VXBf+jqoo6dLhKuL5iGqm8ztrm8/vqGs+G/a9+fSWxvzJ4Kb8yS3NUEJ8UHNJJ4JbCMeCWglHA9uKces6inEBXcTYNd1NUX69TJF+ffioFT/zh5f3y6SoZT+nC9cjlvUXDi/9RYhYMlA4tHiQELF4yPNa9KtwYOFQ4eCiYUKE92/CgQXDqeb9Lu5fMELcP+8P8cDckeK+2X+Ke+eOlJ6LXG7DHQ38STgZ2po9v7eucDGiclL8vkIIzyx9z6x5/BtgemDlgOnBCwHTIDB422qAyQJDA0z/N4BJXfgsy9CCNzpOEAxgMRyjvZTYJktFjmmyXqkL0jhHsDiPkEeBKehWGUXUnaE9eKowFGTifHvVIr3awYTFfXT81CRqTTSIaDJDHRYIQ88R3WEsGzOmXBMEb+ikQofOdaLjDO1Phf2HsFiPsWvNiWowGS6m3MyHHZWnRMHheSBIxO8UBBIIrYcSTWMyYCCCa3S94TWypDNS3TcL5w1CL4RfeK8wfhFhIPbMQtcRghW1A+91hhowvSwiz9I9mLL2osKoQDVgUkfkWTZl4OMATEeAsVcgUyTkcYmG4ro4qD77BLRadhZ+CfwLJm6/Ad6R/8CmU4/g4JUUOPsPB3dTTZAqpkmReW87sK7Jm5/BA6MZ/nooQNxNI2y/kCSBLY99iTBy81XouuoCfD//NFSZFg+FHWMhp63sXhoTRUGTXYwGmDS9XBpgeuuhASbr0ocEmEbIgKmJFQGmntI1oi4vBTA1zREMHYtuhcHf7oXJP8fBWveLEBVyFxIvGMDEP3nuPM38U3iUKMDFI0mwb+VNWGF7DpzbxcCQqnuha8Ft0PqTEAks4fvjfWhH7gdG8nXXANNLpQGm/wIwVX6x0uPwZLikjrnDXkjp/ZBKy3F1qp5IEjAqpAJHhWWHkuxYmiQ/5yA/L/VOKiG7nGRJ68Ul15MUcScBrFJpnFv5FHJM//C6LxL5aV8m8h61EnmvrxL5Gd8k8rPqJ/JzGyby85sl8otaJ/JLOibyy7om8n49EoVVvRMF/36Jwur+iULAwBvC+qF/i4HDL4kbR54yBY+LE0PsI8Stk3aJYS5h4o6pW8Q9niHivjlbxf1zNpt2T1slBI2dQt6nj3H6d7UfjCqR/8pYJneGqr1Q8SOYXEF9pRiND3pE6FrnTPIdUYgNcynF7fYqw+1eQBXpW4Y/FVSOvxJRXriWUElMPPuF6e7ZWuZrR781/3WkUdrFfa3Tzu7s+OTMzs64TLu4t5X5SkRj85XIeua/ouuar8TWM1+ObJh2eX+LtLN7Ojw5ta3rkzMhPZ6cDP1JWuL62bAf07efCullSgjubz66frD56JrfzHH+I8Rovz/FIytGZch3tBjlO4Ysx4mHltiJET4OpoiFTqYD3m6mA/OmCntnTRP2zPIUds/0oprhKWnfTA/pud34PHmM2/Z4TRd3e80Ud3rOEndOm5NZHnPFXdPmiTvc54s7dQvEHTpvSeFTF/Lbpyziw6f68OFTFvPbXZcI4S5L+W2uS6Tn986ZKRxa6iLG6UeYTgb34E+FNuRPbymPzixL32drHhpg0sa7Hhpg+r8BTPg7GIvB+P95bGCPfVJ+Y2hhFV0GWLDHyCh0qFjKYaDJeqUuziswBfu2HCPaxlAX3CSi/kQtGAqGEKa8rotJmadY3Fd6+jSX39eRaBnRToaCASzSY7yXpV0x6v5UCL3ws4R9h7LrT1WJoeBNcYV8iFF5WXsvqd1L+N2HcYkLibYyFKbcYCjEsHRft6yxcHhcCNYxxg/dZgjGWjMUBJZgMjvNXnUo1wXnLwImjP+2RsAEzPMOJgUwYU++rA4mDTC9HvCIVUkBIAgn5F5ME47AJw5RkNcxBopPjoNq009Ao0VnJOfQn1uuwfT9t2H1sQew51IKnLrDws1kUYrM4+XeTGlET57SHk1YrHyiEkbqZYhCJdwupj0Do/gU7hvS4NJ9Ho5cM8Dm04/BJ+ofcNxxAwYFXoYOy8/Ct3NOQgXdcSjiFAe5yTHnGCc7lxTAogEmTf8mDTC99dAAk3XpQwFMC0YnwB8N90PnoqHQ1AoAE4VLO6Rovm7SNaKACSPs0G3UqWgYDPl2H0zpexTW6i5C1Oa7cPOcAUT2ecBkItvuXeXg1N6HsM37GiwcegpsG0RCvxK7oGNujN7bkg6X2pJ70ZEJk6BJD3J/esnnqwGm56UBJhkwhUxsxW91dBA2j9/Irxl4klvU5tGr92BSgJEq8i5dFTMrk1tJ6Z0k90xyUfVBUvobORYFTnEeoSsJ3UmSCykDIEk/k/7zpakQVGHMHh6T7gvqSFI0jbqTeEnk8dSqDzldlXjy2q381Kp6flp1Pe9VW8/P+FbPz65L1EjPz2+q5xe20vM+HfT88m563q+nnvf/WS+sHagX9EP0QuBQvbDh9wAhaNRqIXisH795wmIx1HGesGPKdGGXh860Z5ar6cA8R9PhJU6mKD8XU/RKR/GQzyhTuGtPVt/v2we6r/Jbeh6874GALMWnYxUh2La1af/sfqYIHxtTxKKBwv65A00RCwaao1cOMicEDzaf3z3UfHnvcPOFPX+az4aOTTuxcWJarL+bKWaFuyl6hYcp2k+XFrvGNe144ETziY225oTN48wngm3T4gPt0+LWOJuiVk4xHV7maTrsM8N0eNFMaRm51EvaJi3J+sFFs8375i0Qd09fLO6ctkzcrlshbJ+yUgh3XSVpm6s/lctqIcx5jbDVKUAIdVwvbJmwUdxiGywGjQsRg0ZvFTf9GcZv/HObpA0jw/gNZH3TaLJt1FZJ+Ly0fWS4EDhiu7D+951C4PBdmbR++G5J+t/2EO0V9L/uFQKG7iPzbL8QMPiAEDDogLB28EFhjU0Ev9rmEC6F9cP2CUFjt/PhbhvEvXMWioeXOKCrCmP5kiMWaFGJLxkYkciejSvFx2xvatwwZ1zK1P6bPi7A5KwBpvc8NMD0fwGYlF4pyl/V41+mdyOaSLSaob03rjO06IoAQeu9pCk7KW4dBaagA+QMQx1FCFPQtaLAFOydhH2+8Lv8VSPh1LFr+DMIYhCGYq8w/EzZMRngAsEWAi4l0tGS4EIdu/aQocV6BBehRIsY6gjpx1Coi+AN49cQvOEf1HzKfHguJqWXG/4/M7soQ5wHOB8OEp1nMqIMLeU0U6SGgQhIFagSQDSFof2ymjJ0zhWVz+91AKB6/iqAKTsH0wnGegATft8rPZjUEXkYFYiASXMwvRPwoWgCAhqMmYuSlp8Q5baPhsLOcVDWPR6+nnsKOvhegGEbr8LkXYngG3sfws8nQewNA1y4x0Nisgj3DWZ4xJohiU+DVOEJpJJlikqpgqInUo+lZP4JPGbT4J9UM1x/ZILTt3k48FcqBJ54CHMj7oJt2HXoE3AJmvucgRozTkCpyUch/8QY+MwuGj4Zq4JLCA3sZMCiwCUNMGnKThpgeuuhASbr0psAph+KbIVfau8Gpx7RsHLyOYgKuwv/XOf+E8B056oRDiqAqdEB6FxsqwSYGlkIMNFt26Vr85Mcj9dVBkzYg6kZEywBoS6Fw+DXOvtg8k9x4O9yASLW3YYrx1Mg9aEZnqmu07Nnz4BNMsPNswaIDfkHNrpfhum94+GPWhHQM992aPdpaCa41IHsp7P0GQmX9q8ApgxZfk5ZizTARP6HEjK6mLDNuRW/zdlB2DJ+A7/W5iTn0/YR51XLzLrKgAn7FCHEwf5IU+SeSereSZNVvZMyqbxK2NeoLJXkVpKdSgpYUuCSS0kZMskOJozDc5Tj8DAWD3sukZ9j3coBi/uWnFNVqdxlmDSNRtvxM74FflY94Gd/D/ychlRzGwM/rwkIqNnfP+VmfHtK8Kjhz7tXtWN1VWxYXTUbdlptG9arjg07s54NO6eBDTuvqQ3r3dqG9elgIyzvbiP4/WQj+P9sI6wdaCOsG0w01EZY//tAftMfA/igMf34zRN6i2HO3cVwty7iTo+Owi6vdsL+eW2EQwvbCDHL2wlH/Fpj3xzTdrdahsABxS09BywxDPZli7OL2rc3bRk3ybx/rp85conedGih3rRvToBpzwy96eC8dabDi9ebolcEmqL9NqYdWRacdsg7JG3vjG2mHVN3mbe57BXDnPaJ21z3iDum7BR3e4aL+2ZuFffPDhX3zQoV93htE3dO3SFuc94jhtrvF7fYHZQUMuGgGDpxf7q2kPVg20PiplFHhPXDYwT9r3FCgM0xfu0vx/k1AyRxqwfEc6v7x3P+/U5wK/slcH59T3J+vU9zvj3OcL7dznFLu1zgl/xwkV/S8RK/uL1KHS+xS364xC7ueJH1IcL1Re0vsT7tLrML2/7FLWpzhVvUmspb1sI2V7mFra5yC1r+zS1o8Tc3v8U1XlLT6/z8JtfJ3L3Oz21yg8zjG2Q+3+TnkOXCVteEZV3/4vVDTgqbJ+wWdkxdJu6eMUbYPb2FcY+upKXvtTUPBEzG09El+bidjY0b545N0Q3Y9Hhg9WsP23wmFbof1P+AAFNTBEyVIXlka0h1HwyGhXYXjL7OPoblGmB6n0MNmNiVUxKMGmD6GAGT8lf12LQei/7oNLAh8mJowRPdIHcZ6kzBQr0GmDRlJ6VAr7iYMPbsL6Joos1E8xnqXsH534ToS4YWqLHYjq6kVynWKzF5CF+w9oTztR5DHRUYwYdF+o1EUURXGOq6s4boNbWLCcEb9vbZz1B4gb2jMH4Ni/YYH4gAo4TqunxIvZiU+4PfJxj1hxAFXWYIZrD3ErpfMBoQY+cwKlCBgBxj2Xuk3CezfCw4dy8w9B5hDzF03+G8rc/QOYcA8E3uzcscTNn1YLKGiDwETFl7MKkBkwJCLTc+WMCUrlhZMRTS2MrAZlwU5Bh3BD4l23JPioViU45BjZknoc3S8zBw3RWYtO0mLDh8B/TxD2D7+SQ48ncqxCca4fQdFs7f4+DyAx7+IlKWkh7KIo/RqYRg6swdDo7eMMLBvwwQcjoJVsTcB489t+DPzbTfUoOFp6GKVzwUdY2TgNcneFxjj8ixeNFSzF8OO0tfw5dIA0zWJQ0wvfXQAJN16UMBTN4yYOpiJYCpZxbAhBF5eCwImdoyIVK03a8194FrpxhYPv4c7Fp6E07vfwR3r3LApabBM6BuXIF7Ag9vCXAxOgn2r74F/hPOw+SOcTC00n7olnOb9F74nm3IEuFSJ8m9FC65l3pKx6IBphdJA0wyYApzbMmHudgLm20D+QCbE9yiNg+zB0wVVH2TKmZAJIy4S4+5K0OXijtJcijJLiXXUlQu2am0/Brl5+X3lPZRUXYjVaW9kTxqAudZC8gxPuM9v0rjvWqLkqZ/JfIzvhH5WfVEfm5DUVjQXBQWtiZqJwqLOoiCT0dRWNJJFJd2IepM1tvf5Oc3DeZnfTeOn/Zlo8euX1SQ5ImqI6tBhcfzGlTgZzUqz89vW47z/aEM59urDLukb2l2tVq/UgUOL2UMGlsCnWGpQXZFU9Y7FUkOtS2cFORYKGnfzELJobrCuHwQpMt/ZdHY3P/FPcX+S/G+9XNdWdQ59/N6UfQe89+qc4bujmA+T3Et8z3v3WqcGDg82LRj6mXTvtmJpr2zEsVd7oniNpdEIcyZyOmWpK0Tb4shE+6IwWPuihuG/yMEDLovrB7wQPDv90BaBtjcF9YNvSfgc4Ej7grrf78r6H/9R1gz8B6/qu8D3u+nh7xvN6Luj/gVPR7yfj2JetGlL1lf1u0Rv7TTY96nbRLv3TKZX9A8mZvXJIWb21gSOwfVKIWd2yiVndMwlZ3dIJWdVd/AzvzWwE2vY+S8arOcZ02W86jBcu5fcpKmVWdRrAeqBsviY5T7lyyrq8qxU6tQ6SrzkqaoVYlnJ6Mq8qxbBZ58BgTyOSMqJ5DPFZVraYFzLiWSz4vATa0s8DO/47jFHR6Rc74oBo3eRq6ZOxfq2JkPsiv3X8yxj2Vgzy5jQmQJPnZHI+PG+WNSdL9s1ACTNt5maIDpowdMinsJ/02IjhCMf8KC5xiipQwtsCIkwCIwFsgt6TDQZP3CuYEQEl1DGK11kyiBobF1vkSuDO2X1JahBWr8nY4uFyxSv6qLSYnJK8RkdsdgpKPijolgKCBAdwz201Gcd5aKyVPcIOhiQuiFBfujTEZ8oDNDoa5yXSowFKC96nWxhqHcG3U0HvbaQiiDQAIhGkbNrWcy3x/FvWTp6E31PUKgfpqh8aDoMhtL1IWhcw37SRVg3qz/ktrBhBGRL4vIU+btEwtcC/Wczc7B1I3J6MGkACbNwfTmis0QghBbuQgv9TY6Qnsb2UZDLoRMk49BzZknobnPOejlfwn+CPobnLffhFkHbsPymH9Af/wBBJ18BFvPPoadF5Jgz8Vk2HMpGfZdJiLLvZfp+m6yHfsrbT2bJL1+9dEH4BN5Dzz33ga7rTdg8Lor0Mn3AtSbfxoqesZDYdc4yOWA4Es+JtTYqIxYPDwPe0tfxxdIA0zWJQ0wvfXQAJN1SQNMr3eN6LbMgAnnK/ZEas+ESEAI3Uzd84fDkCr7YFLLKPD+9RQEe12FqI134VJcMty/wQGbYgJjihke3xXgxlkDHN9xH8IWXAOf4adhUrNosCm9F7rmoICpNTnH9uQedJKj8brL++4lHYsGmF4kDTAhYHIuJmx3bsHvcLETQuz0vH5IPOfT9gE3vbaZdSsNrFN2gEkGSxJQwn5JpTJcR5IUaFRStcS+R8Vp/J0kBSrJQElyOVWgzigJJFUHzrMm8NO/Bn5mXeDnNAB+flPgF7YkagW8d/Nn3NyGD/mZ9S5y07+O473qxJDXxvCzvovhZzeM4Re0iOEXtY3hfX6I4Zd1juGXdyXqEcP79YwRVvaRJC7vvlVY3GEKO6dx+5QZX39Qv5MNi9sVM+iH1eBD7RryWyY05jeObcyvG96YXz2wMb9qQJMM9W3CL+9J1LUJv7gTUbsmhgVNmxjmNGximP4d0ddNDNOqNTFMrtTE4FySqGgTg0OBLCpKhc9Jr1FU7gVSvY9t3iaG0TmbGP5gmhiGyRrJNOMmlfiNm1l3hejb46xp/Yinpi22gBKDRoMY+BsI+iEgrBkIwup+QO4ViH49QfTtBuKyTiD4tAdhYWsyB8hc8CZzYRGRT1vgF7cny3ZkvS2dIwuaAz+3EZk79YHMC+Bno+rTuSS52RpSd9sssm3mt8Cj682jhhSfSCMVv6DCmEXFJTe1KoWdk+UeYm5lMyIalWhHlVhFigtvktxTTFIhooJUmXqMFZRVQIqF5BzyA2ePygfchM+p7PIAZ5ubLPMCR96TJ8fGz22Sxq/46a6wfughMXjUHG7TmJ/4DaMqWHquWvPQAJM23vXQANP/BWBCxwEWPLFwin1g0GkwmSiQoUVwLHZi0dXSDgNN1i+1iwnBARbqESQcYuh8mslQpxE6jtCtgwACQQQCCSzY/1uhWg0xsMiPRXqMlcN4OYwwQ1CDjpPdDAUEtxhaILd0TJ4C3hCkKC6m8/J12cBQ9wpCDPxuaMZQ0KuOyrN2yKQGf3gv8Xc0On0QQrQjGkzkwlDIiNAGY+BuMNYRYahI6TmE9we/89BhtYVoFkPhJcI/nGsl5XN83f5LDPNiwITwDedAqHxtcN5aGoyqezAhYFJ6MGUFTFpE3tsrC2BSIBNCizFKDF2U5G7KNTEWirodg8oeJ+Cb2aeguc9Z6LLiIvQLuAy/b7oKtqHXJeDkvidRgk7zDt0B78N3YVEkEVkuJFpAts05eAe89t+GqbtvgWP4TRiz5Rr8uuEq9F59GTosuwCN5p+BmtMToMzU45DfOQ4+dYih0X1jVXBJdi/hOWiASQNMrywNML310ACTdcn6ARMLBzfeooCp8UHoUjxMBZiC3xtgygwuKGCikCk8HWLgcSBc6sKEwU95tsOgMnthfN1I8Ox+HFaOOycBpKgtd+Fc9CO4cSEVbl40wJWEZEjY/wD2+SdCgMtFmNknHsbVPQwDyOcB3xPBUjsmRHrvrhJcCk+HS2rA1FuWBpjU90kDTOmAaburrRAyQc/rBx/nFrd/AWAqr3ItlZUAEetcMnMBHV/rKBfYnVXCPk5OReWl3DvJjYIlfkolWiB3rwY8QqUZ39DCP8bYLWwDwpJOIKz4CcQ1A0DUDwYxYBCIq3ob+CUdj/PzmwRwM+p4ch61dZxHHR03o66Om9NYx81rqeMWttdxPp103LKuRN11nG8vHefXRyf4/awTVv2s4/162XJLf/xRXNC8qqXvw+uMew7f5CPHXV8IHG5j2jbRxRTmpBO2TNAJG0bqhLWDddxqG1m/6LhV/aVz5nzJ+S/pQq4HuSYLWtJrNOt7ndHrG53RvbrOOKWyzuhSWmd0Kq4zTipMVFBndCgoPy5Kt6NcStLXuZVVqXzmdel9StKfnfC5zjgup844itGljiQaweiMoxl31r6APze1UjQ3u36S4NMBhOVdQfDtCvzSzhQSISCa34xGGs5piHGGRPVBQFCE0YcIHhEIedaWQKQkjxrU4YZwSIJBlWWnnRLRWF4GpJWy6SFWUXbhlcno5ZUe3ahAVFlOSo+wYrRPmGMRosLATSoE3EQih4KyKCBiHfIDa5+P6HNgJ6DyysqjUt4s2+UlAiSylICSXW7gbD+jGp8TuHGfkmUuaV/SZwiBmW+3B4J+yBFx08j5fNDInkLAiIqWnq/WPNSAiUfA5K4BJm283UgHTHoETLoE4/yxT1Mcu0HSIA0wfUSACYv1+P94/LcDFuqxTw7GmaHrBIvg6LjA2ChLOww0Wb8U5wMCA4ymw55DWJxGUImxaIsZ2turP1ELhhbssdCO8YxKTN6/DaVIr7hkXtSHCQHBdYb201FHsFkaMnHyMeGxobtrF5E/kTvR7wx1+zQgqsbQGDW8NgiZcjLW2Y9JDf0QNuDv5/IMhSd4j38mmkC0gCiYoZGJl4nuMRRcWxKiqIXHgC5NhF44ZzFmcR3RVKKBDAV/X8jnp9yP14UqSn+q7ADTXIYCpqwOJktdm6wReQiYcJ7i51cBTDg/NcD07qTE5MlSovIUST2OoiGXQwzkc4yDoi5HofTU41DF4wTUnnkSGsw/A60Xn4POKy5A79WXYOC6v2DohiswfNNV+COYKOgqjCCPh228AoPXX4F+AX9Bj1WXoOPyC9Bs0Vn4bt5pqDnjJFR0j4dSk49BIeejkGdiLHyK4Cg9uk+GXeOj091L6cevASbLn+uHIA0wvfXQAJN16U0B08D3DZjGnFQBpiBoxGx6b4DpeXCxPR0yURfTdqknEoKMH+X+SD1z7YBfyJweUfUgTGwaDTP6HIfldudg09y/YLf+BhwJvw3RO+7CoS23YeeqG7De4zIsHH4SXNvFwh/VD0K/Arukz0EnKRZvK3nfMLIf/FyEy9F4mv79PmmAKb0H03Yne6kHU8CgBKkHk2etNBqRh06LIjIQKkcL9UocXibAVFR2ZxShwmg9p6K0bxIuHYtkSAJMZWTHUhUKljzQrVRH6pkk9Uda1AaEZZ2peyVgMIib/gTT1olg3u4K5nBnEINHXxLW9FtLjnWkceZ3LXnPWo15z28ak58natSYn9e6Mb+oPVHnxvxSVLfGvB+qV7q4Zb2/ExZ3qXRvTsd8lr4PrzNSZ3xVTVjWZRC//tfFYqhdhCnUIcYUPDZGWP9bjLB2YAzvP4BqVf8YfmXfGN7vJ+rgWvJDDO/Tlrq75jSKIdcqhpteJ4Zz/zKGm1IpxuhSOsboVCzGOKlIjHFiwRijA9HEQnSdbOecSsRwziVjyH2P4dzKqlQu8zo+70ReR36Os88fYxyfM8Y4mokxjiIaSTSGiTWO/+w8O6nwPTKPnkhACAGRVy0afyhBoi+oWwh7bE2pDDzOE10VCURmuImqSGCIdSsLLJmfdB4Woe6gTI6gQnQbzmWcp45FM/p5SSJzOL33l+KwUz9WyalEBmByksGpc7GMxwidyOeAqnCGI0kBTZIQNuVXreeXn1dJcTEhqJqoqIAEraijCZ1MeamrybGE5Lri5zdPI/P6lrBh+H4xeOxMbvPYbvy64eUtPV+teWiASRvvemQCTKs0wPQRAiaspWCxFP8SHaO50FmCf6GOhcQjDO2RggVGa4iw0vRhSAFMWKzHuYNujDNE+4jWMBSkDCP6gehbhjpdlDg4nI+vEpOHBe088s+hs7kuQyPMRjLUcaL0YcJ4R+yno4AMS87hrO6ue/LxxTIULGBUHrp8hhB1ZGhvqcoM7cdUQD7fXPL5W4uTKStcwvuBsYW1GNp3qSfRaKIZDIU1BxjafwrnhCV7DL1oziL8Q6COrjucr+iGc5DPA6P+cK4p/ZfepO+QGo4inKnNZO7BZC0OJgUUK4BJ7WBCwNSd0QDTe4Qjmdaj05WD6BOyLZdDrAScirkeg/Lu8fDl9AT4Zs4paOh9BpovPgdtlpyD9svOQbul56AtedySbGuy8CzUm3cGas86BVU8T0igqjD5+c/J++Syj4FPJ5D3t1UgUnQGpFHL0tfmda6hBpisRxpgeuuhASbrkgaY3gRcUMDU+znQRN1MCJx++mQ79Mm7EwaW2APDqx8Au2aRMLlXHMz58wQsnXwG1sw5D/r5l2DtrIuwwu0czP8jAaZ2j4Px3x+GoRX2Qb98uyR3FH4eUApc6pUejafp3++TBpiwX5C4xa69sGW8m7hpZJjg3/cit6BZMqer8kQqyqPzAovaWEB3lXsquSk9lsrR4j7ZLhXpJxXjjQ6FHpLX32Lt8yeyEwsRFZalPC6SyDoVT+RcyyZyUyoncu7VEnmPWom819eJ/Kx6ifzcRom8d6tEfmnnRH5Vr0Rh3a+JYtCYRDHcNRH79JgPL0o0H5r/t2n31FAx6M8JnN9P9SN00j/U//OBfY2SfPsWwj5L6T2XJNE+TJyvTRmqXmWkXk0LUC2I6pfhvDL0UPdd2YezqB55flsO+ztJvZ4kKb2fsB9UWaoJRdOV7FS6MudV50fep/0MYU3/I6aNI1JMm0aKpsDfRHH1AFH06yUKvj8R9RCF5d1FYdmPUt8pwaeDKCxsIwrezUV+XmORn11f6lfFedUSyT0QucmVRNaljEjujUjuu8hOLCiyDkQTC5H1IiLrWFzknEqIUt8f8jpy/4jKySqvelyOPu9UUuQmFRM5+/wia5tbZMd+QpRDZMfkoMtxOc2sXe6n0vxKB0BFMkClBILQEVecAsn0SEW5L1d6TGMZ6Xkpbg7fyy4PkP1R4WN0DElzOH9mcCPts0gm2CRBpfRYx9KvILm3mPozIYFX2QXlXIoeW7rDr6hKxWT4Wjx7qeBXpqhJBXw5ye4p/Fy6VaCOLp92RmHNgMti0OhwIcTeXQyZ2InbMKbs+/hsfKhDA0zaeNdDA0wfNWBSip3okMDCaWOG/qW+F0N7gZxkaMSZOh7P0oVgTdavrCAFAQ+CFHSuoINlHtF4hhbtcc59yWSOHXvVmDws8uPcxSg5LNRjhNkQhjpOVjO0f9g5ojuM9cAMdY8qLNwrUXnY3yaIoS4fLOBj3B9Gy33DZIZM1hSXlzUWD2uB+G80jPdDRxm6XNCZg0ARwQQ6tdCxdYOhLiGEOXgtrOF7BfeP33E4X/Ge4Hcf9sfC+/EnQ4Efuo3QdYTuoze9B1kBE4K49kxmB1OCfAwImEQLXR81YMKIPMXBpI7I+4bJAExaD6b/VPYxGe4gO5WLaIxK4ygEyj0xDgq6HIUSkylsquKVIAGnmjMToMaMBKhOHn9BtlWchlApHoq4HYPPneLgU/vYjPdO77F0JMOt9KFBJbU0wGRdejlgmu4be38gAiZfDTC9cGiAybr06oBpswaYmMx9mNRxdAgz1I4mBBvdPw2HHnnJPC6+EwZU3QVD6u+DkR0Ogm2fSHD8NRrchseC29BYcO4fDfadjsDohhHwW7X9MLD4bvg5907olWO77FgKl4HW83F9ml4sDTAxDAISLvDXbnzg0Fl8wMBIbmnnO9z0uhzrVOqpcXxuMI7NCUbs9YLRX1jYdi0l90yi7qP0PjVTKpk451JXjBML7TdOyBdosMurNzjkIyqgN0wsQJcOBYkK6w2OxfWsWzk9O7WKnp1WXc971dHzM+rq+dkN9Pz8Znp+YTs9v7ybnvfvrxcCR+hNoQ560x4vvTnSR2+OXal/Euvnn3Z4nqOwza3tvYBB78V9FD+ifq4U35++EAKGtuWDR/cXNo+xETb9YSOsG0o0WNZAG2Etkf/PNsLy7jbC0g42wrwWNsKcBjbszG9tWK86Nuy02lT4GLfNqUfUQKV68utq2LC6Kjbs5Io2rEsZopJUruWGcB61pnHzm4bzyzrfFlf1BtGf9igSlnUBAfsQST2I2tD+RAta0N5V8xrT3kOz69F+Q+gW86xF3UJ4H8n9ZF3RkVY8w3GmABgJhsgOHgQdUt8suXcWAh9X2dXmpna3laLRiBKkzE9hjwJ/0pe5M5ao9Gg4xeGTAYK4SXK0IsbVuZaV91NO2o90fPhahEnSe36WBTBlhUsF5f5HWQGTui9YVpXNkAqwSo6+KeUp8JKgVwUJ+HButEeZBF/xuuJxupSUVYoKHYL4nKQymYXgVpJyXctnnLPsHqTHW0ZyevGz6j3hlv7wWAgYdFbcPH6zsHWSqxjm0oHbYlvmfXw+PtShASZtvOuhAaaPFjApxWH8t2AxouoM/Ut6dBssZWhxHmOssBCMThQsBFsaXGj6cKQU7BEiYIH6JkML5xi7iH14XIlsiNow1DmHrpfCzKtFj+FzWKhH1wz+mxnhC8bJoWOmL0ML4BjFF85k3+vH0jF5T+Vrw8rHhcd3iqGfufUMdbLYMjRGEK+PGjIpcXmvAuL+q6Fcf7xPCJcQuODvZLyHClzCmD90qWEvt+UMhTUYk4igAh1C1hSNl9Wtc50ojqEuOA+G9o/CqL9qTEY83pte+xc5mP6tB5Mlrok6Ii87B5MaMGkOpv9U6ug5OxlmjJXB0mhZUq8m2hPpE/tYyDMpFvI7H5VcScXcjknAqbgbfVyEbCtInsuLbqWJsRlF/3Fyj6XRR1SQSYnDi9EAkwaY3s08VgDTH5HSHCvlctTYwvvMxREbr2ybceDWjOWx92xWHbv/3fKYe9p/9l4wNMBkXVIDpb6qx71lZ043Jgw6MCEyYAqGlp8GQ6ciW8Hmqz3g/FMMrJpyHqK3/ceAadMt8B57Cv5ochC6lNgGTXMEQyMmSAZMIe8BMKl7HO187nplAA0KmDL1ZPpkK3TIEwodCodCx3JboUv1bdDjOzK3m+yAfi12wYBmu+GXhkRf74b+VXZBv5K7oG/+ndA3184s92Zn+rmpey5Zev5YszTARP73uLZvOd6/bx9uVZ8l/IqfTrHebQysey0Ta1/0mXHUp2D8kwHjmE9p0R+L8RJkKiP1reE9agA/42sJWLCete6yUyrtNDoV8zTY5RvKTshjI8mh4PNyLEahCQIUBCletWXY0sCGndfURvBpRwGN/wAbIfAPGyHUwUbYNc3GFOFtY4r2szHF+A1Ii1zait/jWeF9XSfjnKYl2RU9fhDWDXUWNo32F4LH6PlNf+r5wN+wb5UkAbV2oF5Y2Ucv+HbT80s6UGA2p4Gen/EtBWketfWsRy09Sx6zZBs7ux4Fa3MaScJ1dsbX9DW6qnp2akUK41xKUU0uv56d9uU+fsY3l/m5jQV+YUvarwhBkgSR6pP78R1wM74FbvrXwHl9BZzUp0iOn/Oo/nyfIgmKlKVuHAm0qOLenOT4t3SHz6sAJqWXUSn6swiIJqqi3hwKyf2J8lP4o/Qnyuo0mlQ4HQJJfb2cFcBUJmNfGNMoOZiKyJFyyvsp74MRdTIsm1Q0s4so3SmE0Kd05vNyK/cSlZdVIQMsSb2dsN+TogoZUCgdSKndfypIlZ2kvlHlVX3P1O9ZPsMphddaVw342fXN/LIuD8V1v540bZmw0bTNRQKwbNDE0u/rM/IhDgqYEkrwsXs+PsDkowEmSwwFMPEyYGLnj32amg1geqABpg8RMGFREIvD6DrAOK7eDC0IBzK0GKz0AVHcS5aGFpo+HKkL1OgK+YehsWOHGDq/MDIN4+wwkvF7oioM7aeExWoER//mDlEAhxKTV4mhcxjfDx0nWKzfxDwfk2ctTjzl2uAxIXDBAj6ChT1EAUQzGerywv5F6MzCKEHsNYUFfYxoyytfp1eJFHyXQwHTyrXH74//sXcW4FFcbRS+uBXa4l5a6kD5Ke7B3QnS4rS0tFDcbXHX4A5BAwSS4BY0aCluQYPGk92dmU2Q758zd4ZMliQECGQDcx/Os5uV2Zk7d5fke/ecD4Aaf7+gnxYcaYBLHWUNYjz2D25IuNeuMu6IhJsM0Dqx3WT6taq5ytAzDGB9v6zFsgYw/rmInliIctTi8d50zrV1q3cwaRF5moPJUSLyYgJMiE4FwMX7DBF5+J1cczAl3vjgAZM9LNH3ZtIDDs1pJD8uRd9jlKrfcUrT/zilk4XoOwAlXE8rK02/Y5SyzzFK3iembWp9llRpcMkATAZgehvFBJjk85Fj0AlLxennr/6+1tdr3N57E+b5PG67+IT/z/MMwBTrMACTYyn+gGnDRw2YNLDj/EJRcEkfk6eHS9XZZnJim6hCio1UJrUblcqwnkp+vo5K5lhPpfKsp7L53Khi3g3klHsTVc++mWp/toXqZ/CkxqnlY0nOj6Wloh2KWshylmUApvjJAEzyXwfznPNYFjVqKSxsuFCcV+eqML3yU+vIH8naLztZuqUhBTL9nfyptWfaCGvfjEp8mjAop00Y/pVNHFfYJk0tZZOmlTOLU0oeFcf9ONk8NHfDsH6fFgzunS5f7FIj35QIuII8Dm5M4XzixJ/yitPK5hEmls+NiDkePdchp9Xtr5zWbf1kmWRNymn1npQzfOe0zI93Tc7g5ub8tr+kJ3NzZikumQql9p1VJ43vrK+5ukcpwFToE3FaxVLi/Ia9bSvbbJbWdvaV1nbxE1d39BNX/OonLmulSFrW0k9aKmtxYz8JEX8u1fzEqeX8xMkl/MRxP/mJYwr5iaN/9BMg+bog3yZMLOYnTiouS37M5OLyz0X9hLHyfaO+8ROGf+knDM3L4wQH55QvZQ3Lfc86/IsAwVRQUPoWjSvENfZHEkZ/R8IogKMvSX4MWeFKGppXccHwS1nRwEVeHRRS495eRLHpexFpEW05+GNiBEx57ZSHAxXFaWPfzyi76kbS9zLKGnWbHmYN1ruK1Nd7AV3yResHFuPrDLKLuxuil96RZA904pIOJI2AvojScL3yx72d4a+SCq1i2p523Njvkd+QvH4ixHn1/W2rO5+OcO+zyuY5pK+0dXgVq8fgHAnyQfGBDgMwGSOhhwGYPljApDlA4BpB4/pKsn6TNU3WNsajxVCUhwPFUQrBhpKWNKcO1lAQ4/28TsrykOXCuBOiJePuEMAJFKvh0NH627xOTB4gKSLMAGM6MB6Th2I4+uig5w8ixxwJbGgFfOyPFiMId88pxqPkljMO4f5h3MmEuDz0APpanSdAtQzq8evdTO8CNCXTKaX6evgbEvMOV9UXjM99ecaj0zoz3ksK53gj42ACMYA4B4AVADmOBK21dYrzgDhFuMngfpsh6y9ZtVkUTNHH473J0DuYEAupReRpPZi2MMdxMD1TXx8ORLx39YCpgTonOAYjIi/RgEmMfZGOUbLePgo4QuwdBJCUSr1Mqd6WQr4f/ZugZPptKteP2snHAEwGYHp72QOmLoeUyxwDT1gqTDt37bc1vtvG7Lk3ac7Rx+0XHvcvLl9mSbQPFQcfBmByLBmAKT5zFAWWWrxwEkXNUSN1zWLt1pXnS3Eusc1ULZk8b8k3UrkUblQi5Xr6X+o1VDjNKvoh7Sr6Lq0rfS+rUBpXKpp6NZVMvY4qpNpA1VO4U73kHko8Hl6nFdtBrWW1igaZDMAUHxmAiTHLyrbZxWUtm0qLms0TFzS4IrrUIGFCSRKGfaNAJmuvT0XLP2nvWnuk+c/SK52PpW9GH2Fgdh/B9KWPOL6Yjzi9oo/oUvWAMNNpnnVqmQ7m0d999772PXi7KZNt7/SvIg/N/ln0nlVG9J5aRtw3sZSwfXwx685RRa3bRhWxbhtWxOo+oKiwqefPwroeJcW1XUqLq34rI67qUEZc9ivXEuey4vwmsuqXNc+uVtY8vbKscmXNk0spskwpWUmYUfF3aW6dpdKiJpelZS1J0ZJmJC1sRNKC+iTN11SPpDk1SZrpxKPpJhVXXF6Kg2jUtwoMUBxEgEG4bVwh3j8HTrDxhTkowv2mL9UeQzmjAxnAH83BM0zvnFF7Eg3l8XSKqwfRcf21iDvey8j6IuYuhii4obl0oMlOLx5j775RgdJLAMUOYMXo2slrB3bsNDwWqKOHLsPy24GcmECRzlUUI8DBffZwKJ4a8UUcgCmhFRNgkq+P/FZeZyUBmB5Jq347GbG570qb17DekuewygZgint8uICpPZln975sWTjExTx/iAGY3uMwANMHCZi0iCu4IFAgREQZvpGOgj8KiIcZLyiisOgoBXlDSU+aMwRrSOs3BNgD6LOM8d48iFFDfxs4dOCCAfDE3yfxKVjjfkBSFP21mLyysprL6sM44ADMArTBegbkAuxyBBeTVsDX5gfwCy4vuK0A4RAluFzWRFm9GY8TrMW4kwZ/l+Rl3PGl9WXCPKRkUY4mzWHzpkV/7bnatlKqr4FzAziC8wTgAlcVzh0AdSNZv8saynhEIfptobcUYDXckIgDRCwg5t9RPlPsew1hnfjIWsui4vFwbFhbmG8twvFNAZMG6QBlsGZxLqup8wYHE9YroiQT28FELAowhanzgv8X8P8D/p/QHEzZ2dtFBibM+OgAU2wAxV4AID2Pvlq97CLwesUASgzAFANg0rm9IAMwxa4+OgEwdQVgOkh4j2bvf9xaYcq5651WX98xepffFJcjjzrOP/a4pMvRRwZgimUYgMmxFBtg0uLe6jMPqs7cqZIKmCoCMGXeQm0L7aLBTXxo6YhL5OP5kB7fEej5BwiY+HxEwSU9YOIADlBpC9XSqWYy+TKVfJl2M1VL706VP9lE5T7ZQCXTr6Of0q6mH1K50tfJVlJBtlzRt2wFFWarqARbq8wz4BSOB+eDA6ad8uXOaICpuQGYXikDMMm/jbv1yiys61rHtqYzejCdlJY4R4hz6pI4tRIJY4qSdchXftb+mXdaeqefZemZ1iRfmiz9M5ssw78yCeP/ZxKmVzJJc2oOkebVaivOqloqcOJ3Gd/Xvtu8Rn8TcWBmkydHl/SOOLbEFHF4gSniwKzBtv1Te9v2Te5m2zOhq23XuK62rcO7ix4D+0ibeg+SNnQbJq390ySt/s0kuXYySSvamYQlrUzCoqYmYUFDkzCntkmYWVU5LmFqOZMwuYxJmFJmtDC9/DJxhtNxaVb1cGl2DZJcqpE4y4nE6RU4SJIlQVPLkoReR4ipG1eYQyXAouEaFMjDHUXD8iouI9wnjixI4qivFVlNX8m35+f9dwZpkOizqLi4gWq0mxJbl50DpxdOnxyqK0h9DuLhdH2MtH5DUe4gnTMoxri2GKDQMHunktpzSA9r4pQdnIkJ0rwK2ii3F+AarruuSP/cAq/WcJ1i3EZMisd2E0xfRL/+AojljYKM8hoTp5S0iQsaPpTX9YmILQNW2LYN7yVtM1WyuPfN/r7ej0lxfGiAKbhhAQrrWoXMo9qTZXbvy4IBmN77MADTBwmYtG/RozCPoj5irVDAHst4nBUa3CPKCvFdWs+axC4EG0p60lw6KFJjLcGlA4CCuDQ3WVMZd+g0ZrxvD5x0KOIDYMQ3Jg/rGMV6OHoQYVZMVh3GHSFwACGOD5DjCuMAx6zuj6MADr3LCxDuIYuCTHAyuTIOHvozHjuHwj6cQijuF2BRbia8l9Oq86ZF52nS5jBZPKTNuRaDl4pFOZZwXhARBzCCzw30bYOrCq4xQD24fUbImse4cwnzDqCI/luAexpccqTPEw3yYf6xPhHjiF5Y6BMGkNKE8QjHfOqxxxd+xjU0wIS1/p06fwBMmoMJgAlOKnMizpfewaT1pdIDJjiY8MUEfOnLAEwOoV66S01a5F1cegGaHOAY3uXcGIApcRUTYPr9oPL+zN7vuLX85LO+HVdd3zlql9/UWYcfdZrn87jUrCOPsibah4qDDwMwOZaa2ymqOB8dMAEuVbADTEOa+NCyDxQw6aGbHi61UOPxmqpxeHAsAQghDq9Gss0KWKqb3oMafOZFjbPLyuNFjb7wonpfeFKtfFvIKecmKpvZjX7OsJZ+SrmaCjFX+lFWERUwVZCPC/ON9wD2o6XqXtIcTBwy6fsxJf4aclQZgImxsK3jP5d2jalk8xrcz7a592ZpQ7c7ttW/PZeW/ULCnLoh1omlDlqH5R9v6fdpM3PPlGXNPdOVNffNXNY87Iuy5nFFyponlysrzq5S2ryg5veWWXWyva/9RnRehHuvRhG7x02MOOiyNfLIPJ/IAy4+tr2TvW27xnnZdo3dELFj1NqIrSPW2jwHbrS599kquXXbJ63947C0urOPtKq9j7SirY+0vLWPuLi5j7iosY84v56POLu6jzirMndmTSvrI04u5SNMLnVcmFzisjC5pL84sfgzcdLPJCo9jgpzFxKi6kZ/TyI06jsS4VIa8SUHAYAz6PED6APAo/UBws8APXAL4TGq60YBS3AgDcqqg0SfRPUm6h8Fi170RnoBmbK/iJ3jr6UDUzoXU1QfJTsnUqxxbvb35X9ZcTp7VEBiKsBhGzTiy6jrJrv7tJ9HqI97FYQxfflmGmGvdwGIYnqd+CgW2PQSYJKvY81NKRUFmDz6LzcAU/zGBwGY/mcAJkcaBmD6YAETorVQmEaRGBFN3WTNZby4ih4kcBvAWZHYTg9DSVuaiwkFfKwpwAYU0OHQQREfUWqAm06yfpSVi71eTF5K9bH4MhhgCyLHKsv6VdYQWQsZBzX/qa8Nlwoi2hwFMGmF/Eh1v7B/gEy+sk7L2s04JJvFuDPoD8Z7AsH1AvABQAGwhkL/5+o8AATpYZPmbIqPNKikuZUAQgCv4FjC30RwTgEE/sS4W6yOOtc9GQfUixiHJIARGlxCXyMARps674k95/q51wAoYA5cVoinQx8kQD1ASvRHwrrUx+O9DUzR3GCAMqid4vMXgAnxpBpgwlp9wBK3Z9irABNAJ2IRs7EoV5cBmBxC0RxM8XAvaQ6mpOpOep05MQBT4ikOwJS133FruclnfTusur5z5E6/aTMPP+o01wBMcQ4DMDmWDMAU97zYAyZndduYG4CLmvJrV5P3oUoyd6qeyp3qZPCghlm9yDn/dmrz/S7qUHQ3dSy1hzqW2UPtSu2ilkW3U+PvvDhsyrKRyqZ3o5Ip11KJZGvlY1qnACZsD+AKr9Fced0ouGQApvjrYwZMKKy6ubmlCPdxyywcXVYy8uDs9rZ9k6bZdo3dbds6/Jrk3vu2uLLDcWF2zfnWUYV+CRuY4yvf7ixNdPEeRehfZDK9cfzBS+Px5JoZzGu6ZFV6L0How4R+THPqynLKKc2snt+2sFGtiNUdRtg2994VsWPEg8gdo2wR24fbbB4DwiT3vvfk/b9h29jjim1DtyvS2j9viqs7PRCXtwmVlrYUpMXNbLaFTWy2BQ1ttvn1bdLc2jZpTk2bNKuqTZxR0SZOLWMTJ5ewiZOK2cQJRWUVsYljCz8Rx3z/HMV8YWRB1f2SL8rpo/XzGcL7DlkHqTF1L9xEmbibCJConwqKBnyuuI0ELbZOAUvZOQhSANGn6vNiAEwvHEw5osfcDc6pbifbC6cTj8bLzsHVYLX30AuolDcKGtk7jOJyH70ElOILgL6yU3wBkAGY4g2YDAdTvMcHB5gaFKCwP6uQeWQ7srj0uiwYPZje+zAA0wcHmLQCJwrHKJrC8YGC9TDGC9knGC+0JnY8k6EPQ/ZFfLiI4BI5IGu1rHGy/pRVV9bPjPfzwed7fIvWqAVqLiak6XwpqxTjrii4o9BTDG4auKbgDIJLxcIcb21rxXyAOESSPZZ1k3HY4K0eA4DcGMZhTlvGi/wV1XlDD6sCjAM6FP0BmwDqPlHnEn/zAcSl1imNndKqj8VcAlQBKqG+B3gFBw/AElwrcDwCSuNzA86bgYy70VYw3r8NEXM4x/gcCWLR4ZKjzLe2NrWIQsBPQL1D6nHg87C1rHKMryn9mnybvw9jAkxVWHQHkx4wJVYPJv2a1CLytB5M9oApIVxdbzcMwKSTAZhin5PXBEzbOWD6edW/gb8agOktpcGl3up50AGmLP2OW8togGnXvWmag8nFAEyxDgMwOZZeBzCVjwUwHfvAAJMeLrWIJRoP4KKO0p+K91qqnmoz1c64hRrn3Eqtv95JnX/eS92dDlDfuodpYNOjNLiFDw1qfpR61z9Ef1fzVqBTyx+2U4N8nlQjszs5pd9IlVJtJKfkGxXAVEc+JrxGExUyOetAUwtdVJ6zA6whR9XHCphu3/ZOG+x7PFPY+cOfi2e98kSe9Shm+8+tXuSJlX9G+CwcF3Fg5pKInaNW2DZ0myYsatwlbGKxEpeclT+u3vmwjCuWTVjSsISw4Z9GER6D20geA9pI67u1kVa0biPNr9dGcqnWxjrdqYM0u9pI28KG7tLyX27a1nQm22pZru1JWt6apKUtCFF/0uJmgrSwsSAtaBAhzq1N4qyqJM6oROL08iROLcs1DZelUaBX+iUJE4ryPkjokTTqaw6TRqquGq0HjtLnSOuNlJVDogHRZX2hzBwIaW4kJa6Ow6WYXEgKCNIg00Dd8/H4/qrzCcAomgvp5Wg769BcZB2ik3Ibj+dTIu2iQaX8L0fPxRgV94aQxQBM7wcwzW/wSFr9+8mILf1X2rYN6y1tH1XZAExxjw8GMP0PsAKA6QsK+8OJzCPbkmVmj8vCgoEGYHrPwwBMHxRg0iKwUExG3BMKpyhQ49vzKMTDVYJ+KShuo9CN4qsjFYQNJU1hDWkOHQAHFKsRAYdiOpw5fWU5Mx79hoI7/p8HGIlvTJ7mYsKazsN4fBycJ+jvNIrxXkbo+3SO8d42oeq+OGpcG/YNgDdA1h3GnUAAZFsZhx/TGXczIZIOEKQe464tOJpQ9P+GcVCnwSaAt8/V+QF0yqhTJlWfqo/B/616qIQeS4BX6LOkgSXExnVgvDcU+hTB+bhenWP0u4IDEv22tJ5LNuZ4nyV65xjAJ1xj59Q5Ru+u7oxDTzi1cqtzFR9X3auG5rqLCTDBNRWbgymx1qMGmG6z6A4mrDm9gynBvpT5RsMATDpF68N0NP5K7P1+H3PyEmD6jwMm7wf9t6iASZYCmLZeCkm17XJIFo+LwcVdTwe0Gb///rRO6254V3C56A/AlKE/AJO6TU0GYIpdGlzqrUI5rQfTX4cp68AT5nLTzl/tvNbXa8ye+xPnHn3cbtFx/+LzfB4bPZhiGQZgcizFDZi8dIBpowqYNlKdzB7UrtBuGtrkGC0fcZmOeT56L4Dpz7L7qV42TypvB5hqqTCGH8/bASZ9zyW9tG1iXQJmNUjmSXWTeVCtlFuodtotVP9zT2qWbxu1K7yb/qrgTf0bHKHR7U7SlL/+pVm9z9LcAedpTr9zNOOf/2jCb6dpeIvj1LvWIepSeh/9+v1OapJnK9X73INqp+f9m+rI28Z7Aa/VWN03Zx1cigJMhospNn1sgMnb25Qy5PSeT0Xf43ltN49/E+F76MfIa/uLRl7bV+rJpZ0Vn1zYViPi7KYmEceW/CrtGv8rII+42LmUdWzpHO9l/5xYSuvY//1PWNikk21D9+kRHgNdJY8BrtL6bq7i8l9dxfkNXEWXqq7ijIprpBkVdkszKl0WXapY0A9JQj+kGRVInFqGw6IpJUlEL6RJJUic8D8SxhZS+yEVVOPXVDABgASQNOqbKGcSiveKG0iNnNOk73ekwKVsKlD6nIT+mjLLPyMGT3MOZYu6VPXStvS9kAbninJCKcqpupJy2vVMiinWLn8M0XbqY4Zris2J9C7gigpYXgJMbwKADMAUJ2CaXCoiJsBk9Rj8Xt67SXUogMlXBUxuSRgwFUWRPg0F1/+CwrpUJvOIX8kyo8dlYV5/F/OcvgZgeo/DAEwfHGBC7QQFQRQGUSDEN9FRMFzOeAERrgnEdDmi48BQ0pTexQRwAvgAaAIgsUyWifH+QoBCgEOIYYN7BgV9zTESW1FfW9NwMSEaDnAKgAXOE0CrPrJmMh57dpxxlwrAjZU5Vi8mTRpkgqsGgCFYna+rjMMbRFjCzYQouomMu4e6Mh5T15Dx6DyAuuLqXCJCD86jAowDIwA4AJNcqnKrwpx/wThQwvwhavB/jLvBKsuqzXifJZynnuo5w7yulOXFuLsFgAafH3Cphejm2NHgkn5NiuocA3oC4sHFCSgJhxjg+9eMgyC4ut7WvYShB0yonWKuAZi0iDwP5hiASR+RpwGmI4y/XwGE7QGT4WAy5MB6A8DkdSkk1dbLIVnl20usPB3Qdty++9M7rrtxoLzLRf/8BmB6i/OgA0zqezPH0FOWyrMuXvrT7eamyd4PTUtOBLRYeTqwyNITAZ8l2oeKgw8DMDmWXhcwVfoIAJPzC8dQFMABrICjq4EyJ55UP4Un1Ustr9VPPKlptq30S8Gd9HuJfdS39mEa1eYETe/xHy0ZeYnWTrlKm+bcIM+Ft8hz/i1yn3WD1k28RsuGXqZZ3c7S2F9OUv/aR+jPkvup7Te7qHnObdQwo5ey7XrJPVU44qW8drMXwMsATPHRxwCYUED13d49TfjOaZmlIyvzR1zw+OnJ5W2Vnl7YWu/puc3Nnl7Y0uTJld01I32PlAFwkq7u+lI6vTK/sNuUGzF1iKtjr/FLMKLyEJnnO6tOGt9ZX7+I0Xs5Xu9lhQ78rIBlbOEW4rx6LtLqzidsG3v4SW7d/KTVnfzEpc5+4ry6fuLsKn7i9Ar3xMklAsSJRa3CuELPxdHfkQhwofQ8yqtz8uR94TZSHEFwEfXVRc7BTQQYhH5HSnxcdn4dbqEX0XQZ1Mdm4o4jBQ7pgA9A06CsqpMpK4dO+ug6bV9ewJ680cGPfUyd5iqK1tcohog6AAc9HLJXNAdSXPDjXYGl+AKX9/36SVmvAEwLGjyW1nQ+FeHRz9W2fWgfycvkZACmuMeHBZhSU3C9/BT2e0UyD/+FLDO6Xxfm9p1rntu7Yfi0zgZgek/DAEwfFGDCQHET7hAUlFE8RmEaMWX45jwKxPgmvxbN5GhFYUNJVxo4AXQA4AHoQUF/A+PODfQAa8T4mgTkQFEfv68DHL3KxaQV7fF3DVw46EkEOAIoAmcIXDZw/uxjHGwB2MDFJKn75EguJv1caZF52Fe4Cm+p+48Iup2Mu4YQmzeJcUcTIgHh2mrFOGyqyTgcAmwryXiUHhw5AE+F7YTbAaVKy6rAeF8gOHjwWYUeWYgxBFgAfAFYWsY4tNvPOPgCAEMkHs4tIKLIHBPg6ecY8AafdQ/VeUWvLrixeslqwHh8KIAcHF5w0yUERIkLMOF9AMB0lnHAZGaOE5F3m70MmNCbKjszAJMhh9ebA6Zs8u0lV54OaDdu7/0ZBmB6A/XRXVciGeX3YvfDinOJ/XWIUshzmM/0r1Bz3uULvbbcXj37yON+a88E1dt4Lvhb+fKTRPtQcfBhACbHkgGYXp4PLRKv5YueS1pcII/Fg7uobmoPBQQ1z7GdOny3m7qXO6DMx7SuZ2ip6RJtdPGlXavv0qHN9+nY9kd0arc/nd7lTye2PaKj7g9pv+s98px9k1aNvEIu3c7SqObHqVelQ9Tpx73UIvd2Zdt1U3lQbfm16ryATNhHAzDFVx8yYDp9ekGqkNNunwqHFuSy7R33rbhnTBnb/ql1Iw/OaSerR4T3zBER+6ZPiDgyf2TkuU2dn/geqize88mDvkxv+JLJEG9nmVP9B3FBo9Li/CZlxdm1y5onlytrHlekrHnY12XNg/LIyl7W3DezrIxcPdPJSsnV/7PGFtM3o8VpFfaKCxuF2pa1Igla2JjEOTVJnFmZR9pNLk7i+MLceQRXDmAO4uMAgfpkjOpzhJ/78b5Hlt7pydIrDVl6pCZLz1Rk7ZmarL3ScoCkwCMthk7tl9RHvl1+jrVPOn5deUwW/lpDdbF0ittI7zLSOYwUx5DeHRQDWBkeAyjSHvNSnJyd4nLAJIQzyJCDyQBMCT0+CMBUVNZP2M+UFFw3L4X9Vp7Mw1uRdXq3e9Y5vRdb5vRpah73t5Ga8J6GAZg+KMCEAiAKpSjCo7CJuCsU9ucxXihG0R/f5tcK745YGDaUNKX1uwF4ADABjIBTA7GM82UNkvWLrEqMu2fgrkFhHy6mVwEmpj4Gaxv1KPyeAOcOHCgtGXfoIfYMEBU9xm6wKBcTIIOjQRDNPfKURUULAjYgXvCBuv+AECj4A4q4yVoiawbjPZrgauohq4usduoc4DMH0KQO4+CphnoJ1WIcJgFKNVfPA5xKiOCDAwz9iOCWAnxxVedxrzqXiNS8zaJcS1q/JQ3cOdK86ucXc6v1XgK4OyZrnTp/7RkHc/iMBOgEQIkP6IzP0Bx3+BtcA0yAeVoPJg0w6UF/YgMmAMM7LGbAZPRgMpQEFAtg+m7Cy4DpwM0wpXDkeTE4tdel4OybLwSVWnHKv8PYvfdndlh742C5WRcD8o38l9IbgClu9fGJ3ncJ899Dnp8eKmDqdpiS/3OEPpHn8fvxZ61Nl107PWzHvQXLTwZ28bwYUnHHldC8XhdDk1Sx8n0OAzA5luILmCqpgKlyogCm+zTjn7PUtdx+qp/Ni8on3/jeABO21Vh1LdVWei5toZopt1C9jJ7UPNd26vDjHupd5RCNbX2S5ve7QBtn+NK+dffo5G5/unwqhG6eD6O7V8x0/7qF7l+z0L3LZrpz3ky+J0Pp3N5AOuz2gDxn36Klgy7ShHanqW/1w9Sp8B5qlnM71fvEU3mtmvJrcsi0VX5fYD85ZDIAU9z6UAETovDM17yzRpz3+l46urhSxO4xzjavQf9EbOk/xubea2HE+r/WS64ddkirOx6wbennAchku7arDgqtb/qawaavM4kTS5SyzqnVTlrUbIiwqKlJmFPXJEytYBLG/mSyjPzaZBma12QZnN1kGZjVZOn/mcnSN5PJ0ju9ydIztay0Jku/T2ZYh+baJoz+/pYSbzetvKxyStydgJi7cYVJGPs9j7NDzB1ADxxFiKYDVOqtQiEFDMnX+3wS5VbSgFGvdPJlOn5dcyYBKg3U+htl1oGmT6PuV5xO2bkraZgumi6aY0rvVsoX5TSKFRbZQx57sFRQ7QGlk0lTfABTLH2ODMCURGUApoQeHwRg+p8GmFJQUN08FPpbeQof1oqs0/5+ZJ3TZ5nFpXczAzC9v2EApg8GMGmFTUQ95WTc4dGM8eLxWsZdCOhPk9hFTUMfrjRggjUGR84VWQdlrWbcRQcgAgCCtQkXEtJxUNyPTzSZ1osJ6xsO1y8Yd+zUVbcLcIA4N3sXkyNHQWogRO9mQrE/kPH36nXGXYdwNCFuEHACEW8LGXcZTWA8yg7ACaAIDqeu6nxAv6uXcCeh5xCi7/oz7obCfMFRM4fx+Ew4zbbJOsB4/yyAJcThAXgBfAGAibr5dHS4hPnUu5fgCANAQ18pOOngXoLLU4OcCQVQtD54GmCy78FkD5gSOyIP5xMOpjuMOw6XMQ6Y8L76QT0GDTAl3jAAk6E4FR/AdCG4yoEb4bm9b3DA5HEhOI3HxeAc7ueDyiw/6d9pzJ57Lu3X+B4uO/NCQB7TaUrX7xgl66HGvWkyAFPs86/NVQ+uZPJcZZDnMK88l+VnXfT/bf3NvVO8H47beDa46b7rYUUO3gjPvO96eOJ+sDjwMACTY+l1AFOFWACTz3sATDMVwOT9XgETBEjRQIFLW+R52EzVUmymWuk9qHHOrdTux93Uq8ohmtD+NC0deom2LbxNJ7c/puunQ5X9DvG3kTk4gixhkSSEP+EKjSRLcCSF+0eQ/y2Bbv0XRv/u9qedS+/QCtMVmtjpNPWqfkje9h5qkmMr1ZZfq0byzVRTPg917eLy7M+Zoej6EAHTQy9TevGsV55I330/Pz23taHt0PzuNq/hk6T1f6+1rWzrbVvY5KJtVtXr4uQSd8Sppe+LixqftnkNmxlxek1jQKk3fV2zqcD31qklOwiza84XFzY+IC5o7CPOruUjTivnI44r4iOMLOgjDMvjIwzK7iMMzOIj9PtcViYfoW9GH6FPeh9Lr3Q+1t7pz1j7fXZHGJTDqhTQXzh71Ki7aD2JcvB+Roilg7OovwaFPlOB0OccCr0AR1lVZVFi8JRYOyXuTu2DNCRn1PaV/kv2vY9yR8XZRYusyx+L9NF0r3IT2QGmlwBRXHDKcDB9PDIAU0KPJAmYNJVTAVMxrsDyqSmoQT4K7VKBwoe3JvP0bjcsc/rMM8/u1cgATO9vGIDpgwFMmsPjU1lfMh6D1VnWNMZdJJcZd3WgSOyoBXdDSVt6FxOcI7cZB5twxMxivLgPB01ZFtX7RovJe1VxXwOoWOOAAoCoKIDDEYXIOM3FZN+LSQ9UHXHNP2dRxX7MHQr+cF6FqfsP0ATQA+BzmvE+artleTLubAJUQ7+mueocT2XcKTNR1ST1NrifAJMQubeMcVDlzjhUgrsRDh84zhCFh/MGAAKwBOAlsCjXkqN/dmjzKKr7DzcYwAkgO6IUO7CX3UsAlwnlztEDJmwfgElzMNkDJitLXCcpziXOq+Zg0gATYCUcTHrA9La9qd5uGIDJ0CsBRzwAk/eN8Nz7fTlgcj8fnGbzheBcG84FVVh8wv8P006/+b+sun68+LTzodmHnaKU2O7fR9SoN1XdjkR3NH2UOvKy8P7T5qrbYQUwpZHnP+fwU0+KTTknNF167dLArX6rFx0L+GfbpdBKh2+a8x+7bUmfqB8qDj4MwORYMgDTy/MR1XtpOzWSt6vBpSrJ3Klqms1UN4sntf52J3WrdIBG/3qSlgAuLbpN/+7yp7sXzRTyyEai5Sk9e/qcnstTApGdnj8jirA+pTB/G/ldMdOZfQG0Y+kdWjriEo1ue1LZ9i/ya9TP4kU1Um+WX587meCiwnsEkKkpMwBTXErCgCnZ7WWmtCFuAz61LHXOJrjUyB0ys3p+84p23wo7RpW0HV9WN/KMW+eIk8tHRuyZtMLm3uuAtLLdDdvChmZpRmUSxxV6ah2S22wdmuuROKn4Eduq9hNte6fVDjyyJCM2fsnNlDrErcun1hnVcggTi+UWx3ybRzR9nTd4TMF8wUOg3Fy9MysKG5q9oHl0wcbipJ8nCzOdjklz65ilObVt0swqNnFyCZs49gebYPrKJgzNYxMG5bAJA7LahP6fy/rMJvT71Cb0zWiz9vlEVvoIa+/0T7nzKGOU+umv6xxFgEsKIMoZAxDKpfZAyk3CsDyqoyi/GlunFum1HkUx9Th6SQXU+Lq4ehoZMvQuZQCmhB5JBjCV1+2DJoCKUsnk/UwuX6akwCqfUFDTL5+H/FXZEj7iV3/LtO77LS59R1ln9aoeOr2n0ff1PQ0DMH0QgMm+qIloI3wDHd9ER8EQ0UcoGqNo7ch9U5KS4jN/cT3mQ5x/fTQZitZwv8A9gri1ZbJGMF7gryarEIsek/eqLzJraxwwSnMxFWBRLiatF9Nyxt0+5xmP6UOsG2CDI/Zisp87bf7gakHhX3M0AZQ8Uo8H4OySrDOMg7SD6vwiSs+LcZi3SdZGVbgO6AYgBdAMOAWghM8EOJUAO+A0A8SC68ufcTiodyxpMYOOCun0c6i5csLV4zmnHvdsxh1ciBHEmsnHonovJWT0m31Enr2DyVPdJ5zPxAZMsUXkGYDJUBJTHICptet198kcMDnt9w3Ptfd6qLKY3c4Gpd1wLijv2v8Cneb7PO42ZPvdpc1XXDtTZNJZ66eDTvA19Ye8trocjBLWmh44fZQ6FKWuqjAvXdS5kuc/Wa+jlHnoyeeFJ58NbrD4yvV/3G9vnX7w0Wi3/4Kb7r0W9sPRW+bMx+9YUibqh4qDDwMwOZbeHjBd+uAAkxY7hzg6uIaqsc1UmW2iSik2UfVMW6jpF9upS5n9NLzFcZo/4AJ5LbxNp3ZyuBQeEEFPbPGfhycRzxSX093LZjq925+2Lr5FCwZdULb9R9n95FxgB9XOuIWqJt+sHGtV9Xjrq06mpur7JKZz+LErqQKmQI/+GaVtY74Qtg4rbnX9rYY4r24z64xK7YR5Df4QV/8+wLZ1yOSIXaNXRGwfscu2sedFaXXHYNvSlmRb0ICkmU4kji0E989DoX+mY4KpwHxhbs0uVreeiNhQ4vVsHqavLavbVbG4VGtpnfxzG+vYH9tYR0HftbGavpaVv411WN421sG5ZGVvYx6as6PF9OVY6/hC24UppR6L0yvweLtJpUgcV4RERNoB0gD2AAhpziNNA7JwxxEi6RBbp0TdpeM9kiBc76PG3gEy2UfWKdF0eaNH1w3PFwWTFCikcwRFi52LIUIumlOoYAx9j/RF/9hcRIkNIwx9eDIAU0IPhwNMFe2kg0sBKMKXVl1Lpfh+BZROToFl01BgpU8oqG4OCvq1kCW0Z62L4aPb7jBP7TYxfFbvdqGzehcLMP1l9H19T8MATB8EYNLiw/C+QdP6koz3WUEsGYrLKCI7QkHzbQrv+uuv0jMWVQx/FsP9ZPeYmJ733O75z+LYdmyv98xOMd0W2zZi2//EPh/xKVoDSACOIOoNQAQRb4hgg7MGPcHQC6gE4zF3AEX6mLy4iv16FxO+YAYXE3oxwa3nzHhhHE6dTeprXmM8qg8FdEeOyrNf6/bReQA9mqsJc6rBJvQWQowegBOAGqATXE4ARyfUy1PqbXAnAWzACXVVPS93GIcwmKMgdftW9fUiWJRjSb8GE3uOXjV/EeoxAJTh/B9ivK+USVZbxh1vmnsJoDKha5zJ1G3GBZhwrvSfx4nZgwnvVXsHE76YgCjL71n0iDyjB5MhB9VrAKY9KmBafzYordvZoHxrzgQ6zfN53H3wtrtLmy2/dqbQpLOWTANjAUz4uevhj1w6qAT9oaqLetn9KGUYeJwKjjtjrrnw8qW/Nt3aNmn/g8mrTge223YptOQB3/DsR26Z0/rcMifeB0oSGAZgcizZAyYNUABcNJJVj3lQNQUwbVAB0waqk3kLtSu0i4Y28VEB08N3Cpi819+nWf+co7/KHaAG2byoggKY1lN55kZV2CaqxTZTQ3nNNGNvBlliA2yIo0PPJa3/VMVUm6hONk9qU2Q39at/RIFem2bdoGNbH9ON/8IV59IT27PXPk5AptDHNrp5LpyOb39E7rNvkEvPszSw4VHqUHQP1Zdf0ymVuzz/GxXxY/ZQ9g/vEw2KOb8lXPvQlBQB0z0353S2zUMLSnsnVpG2jeworftjuDC//mzr1HKrhGnlNkqza+6QljQ7alve6oK0tIWftKiJRVrYmKTFTcm2uBlJ8xuQNK2sII4seMg6MNsM67Dcv5gnlSgvLGiKbz4yi3vf7Db3f2pLy1oOFGZWWSxOLuEqji/iKo790VUc/YOrOOprV6vpS1frsPyu5qF5ZOVwtQzJtcYyLP8+YWRBX2HMD5EKVBpXmOTHkzDyaxUuoSCeKyqS7oVyqtApuwKbOGj6jKx9M0V3LQE+6ZxLgEtWDS4pUCmWqDrNcWSKBTDF2KfoVYApllg7AzAZeqcyAFNCD4cDTHrIpP2sB0yl2Iv9CijJlL5LgRUzUFCtbBTSvCCF/Fb6Vlj/hhvCx3Qcap7WvUH4jB4lg2d1z3vJ5Jw6sef6YxkGYErygElzdsAFgmI9oseqy/pb1jzGe9KgmAwnR1IostsXjDXY8lSnJyyq+K2/rv85UtWTOBTb/fa3228rMpbb7C8j7B4bGcPzY7otwu65WpHf0R0k2jnTot7QAwkgBHADLpL5jPcLai2rIuPFd/yfDzCKz/xXASbGoiAToNTnjPdyKiqrpqxOjLukljDecwfA5S7j8ERgUf1uHH0OtXnUQJO9qwnuIsAgvKcBnACIELl2Tz1ee/mp98FRBrARoM4Jng+4gBhBDSpp6zEpOJb00qLxJPW47jAO1uDoms442IQrB2sFvZcAKOO75l5n2DuYALMAmH5jPKpwK4vuYMJ8O5qDSQ+YsjIDMBlyeMUTMHn7hufa5xumAKZN54PTup8PzuN2NqjCouP+f4zYeW9e61W+R0tMOx+Qc9ip5/L6opTyukrR7fAL4eeUPY5+5DrC9c8RPh/d1MvuR5+n7OHzPNPAE88KjDkjVph90bfj+hvbxuy9P3n5yYAOXhdDy+27Fpb3gG942oM3whPXEpkEhgGYHEvxBUwVVcBU6SMATE2UY/eiOvKxO8nHXlY+7jLya1VKs4ka5ttKf5T3prHtT5HrmKt0QN63qydCyf+uSJLlCY/Ae4Nhk58b6CfRtdOhdGjTA1oz4RpN6Hya/q58gJp8sZWc0m5S9qGUctwbqKp8zHXl/cN+6vtGORuA6YWSCmBCEdTb5JQyZIHzp+Z1v39r2zKglm3n6L9tW4fPktb+sUNY0OCiMKXMfWF8kXviuMJ+woSi94QJxR4Kk34OFKaUChdnVhalhY0jbSvaPLe5touwLWzyrzi1/HRx5PfNQk0FClhNhXKGTnf67N4053Ti2i6lRdc2fYWF9d3FGZWui5OL+2Gb4pgf/MTR3/iJI7/yE0z5/YRhef2sQ3LLyuVnHZzznmVorkDr0LwiL4AX4FAJxW+ApSG5oyLrXvQ6wm15uBQHUm61z1JOHXRSpY/B02LvXgJLatxdrIpvT6JYehgZ4MhQossATAk9HAowlY9bAeWSUUBZWSVl/cyeyfsWGVAmhS2wSiZbUIN8ttC2PwWEdXPaEz60+bCw8Z2qB0z6K2fY+K6f43PdZErkOJaPaBiA6YMATCj+4dv4cHSgeX0zWcMY7zsCFwOKy4nZUP5Ni+t6UIPiuqiT8IayvgNZ3oHM6iX2WWIvR5Ul9jmK69xphWvsP+AHHDOIclstayzjbo5asn5ivNiPvmGvU8TWovLQvyk740V89HVqIusfxp1S69TXRO8xgJUwdR6TEmC1n1O9qylCPR5tTWvQKTaFs+hrSmQvryt7t1JSmSc91MRxArbBqYWoxMWyBjPep6ucrIKMg5+E7r2kjVcBJsQYwsGE90ViOkq1NYVzj/Vxh3EH03LG+5khdhIReQZgMpQEFAtg+nb8f3dareQ9mDwuBlc5dNOc+/Ats5LHuuNqWOqdV8Kyb70UWmzNmaBWUw48HPvXpluetRdcvlx00tngL0eeDs835KQ17+ATivJBQ05a8g07ZVZl+cBlzvfysVrzDTvJNfQkn48hJ835h54KKzD8dEjBkf/6/zTp3H2nuZeu/LLKd+fgHX7T5vo87rzxXHCF3VfDCnj7hhvxFPEcBmByLBmAKfqxA0rwaEBPqiFvF44hQJ1S8ms5pdtEzQvuoN41Dyv74zn3Fp3ZE0D3r1rJHBypOJHe+Fjl51pDIunhDYHOHwik7Uvu0Nz+56l/wyPU8vsdVCXjJiqZbB0VY2vlfVlHlZTj5tGA2O+WbLsiAzBFKSkApkuX3FJbdk3Obnbr8Z20sl0F0bV9C3Fdl36Se4950sZe+6VVne6JCxqROK0CCWMLP7GO/PKhdVi+i8LQXKeFoXlPCaO+OSlMKX1CXNDwuLSq8zHJrdsB+TnzpPmN2pmnVsC3HZOFjS/yedjc6l8JC5r+LCxt+YewsMEy68zKl4TJxZ8L4wqTMPpbEkYV5KDlRXE7t+Igsg7OISu7KjtXUrTLXNzBNFTri6SPs4vFfRSj7Psi6X6OEzAlNhwwZOhtZQCmhB4OAZi0/kpluV44lUrpXrtiCgp0Sisrg/xzusiAUmke+pdIfj6gdEqfoGqf+gQ3LuAT0qn4rtDetaaGDW/RLHhMx3yJPbcf6zAA0wcBmPBNfBTpCzDuDEExE9/aR18WFNjhckBBGQXkxC4Gv0paIR2FTxTAURBHATRYPQ64L/x1eqzKP4ZL/1ge/0iV/voj3bbsH/M4lsdDD2PQg3g+xv76A7vHPGJRPXHC1LmQmOM7cbSCv6ju+23Go9o8ZM1ivBcO3iOlZX3FeCFeiyuLTxFbH0OGdY9YyMKyqspqI2uQrLmMx5EhKs5XnUfMX1LtQRZTlKPetRehky0GaffpXXYxQaXEPs43mRcNlFjU84zYwMOMQ8bxjANNONywRnKz6O6lhB56wKQ5Sp1Y7IApsRxM+nnTR+StYAZgMpTkFAtg+mb8f3daAjDtv9/f82JIFZ/blryn71nx7QR25LY55dHblkwHb5q/3HY5tMqykwFdR+2+79LF7eaOJkuv/ld9zsWrTjPP33Sacf6WqptVZl64UdXlgq+mKi4XbnyI0h+j3bHerDJL1cwLfD5mXvCt7nLxSp25l841XHjleGtX371dN91yG7LDb/KMw486u/4bWMHjQkj+3VfDPtl/PdyIxYvnMACTYym+gAlwSYmJS8kBU/vCu2hYEx9aMeIyHfN6x4DJ7T7N6nGO/i5/gBpk96KKyTdSmQQATFq/JmedOJTwpDpsi9LvCK6h4grUWU9VM7jTL9/vosGNfGjJ4Eu03/UeXTsRSsEPbBQhvjlc0saTiOdKD6db58Lp8OYHtHLcFRrR5jj9WmwXVc3sTsWTr6UibLUCmXAuAMDwXuGAaYeiFmr/qMReV46gpACYzNe8s4qHF5SWtvT9RVrRZrC4qMlscXEzN3F568PiinZ+0rLWJC5sQqJLdRImFQ8XRhY8ah2Sc7l5QOZp5v6Zp1hH5J8oTCw2Tphff7S0qvPICLeeQyS3v9sKK9uWCJjjpHzxgcOlevXERU17CgsbrhBmVTlhnfBzmIDeSSPyk3UYCtmqywhQaUhODpYQUzcoG4+sU8X7KmXjQuwdpHceKdvKGx0W2RfS4+MwMhxFhj46GYApoYdDACYVLr3or6RF4GkxePJjgqqlp6A6WSmoXk4KrJHNP7BixoP+pVMt8C+T2hRY9TNTYNMCppCOJfoH963VIsTUsrARiZd4wwBMSRow6ePCsskqJKs+4wVCFApRMLzDeAERxWVHdr5oRU8UvFEQR7EYcAKQBTFfgARwwgCYXVR1we4yttsu6W6Dzuuu638+b3eb/eO028/p7td+1nRWd2l/X1w6q3uutl2tX85Nxl1ogGWaE0crTDsiFNCK1/aOkr2MR3ANl9WOcWcHithw3qHoj7pffGPy8Dj8vwEXE4rgAFXo64QYtD9kjWbcjbFHndc7jK8nrajvyIAuvnMcU6+vp+zlSMmndo9Pir294lpnWs8vxP7dZjwaDzDTRVZvxmFmKVlfMh6riM/LdwlMNMCE14JjqrKszoz3YAJgwudIYgMmbf60iDx8xh5j/P8NROQZgMlQElJsgGncmTstVlxzn7jvfn+vSyFVT9615L/wSESeMDv7QEh+7qGY+r8HwudHb5t/kO+vu+i4/z9j99yb3sfjzto/3W5u7bzGd4+sverlnt/W3tjVZd2NHap2/r7uxu4PUDjGnbrj1I5112/rbmAO9NrdZe2NHX+53fTs5X7bbdDWu0vH7Lk/bfqhRwPnH/Nvs+J0YPn1/wXl33w+OP32y6FGNMVrDAMwOZZiA0xaTBxi2KqyTQrQKMfcqGLKjVQniwe1L7ybhjU9RitMAEyPyP9dAaabVjrgdp9cepyjbuUPUMMcXlQxRRRgckogwKTFyzVRei95Uk15m5VV91Ixtka5rP7JZmpbaDeNaH6CXEdepSMbHtLts+FkDoikZ5EJcOzyJkTzU3rga6WTu/1p/UxfGvP7KWpfZg9Vy+5OP6dYS4XZKioq709Z+dirM3fl/YLjbcV2KDIAU5QcHTDdu+eTLuLKniKRh+Z1sG3sNVNa7LxbmF39nDijsq/gUu2xNL+hKC1qRvLtJF9/JkyvdMI6vsg065C8v1oHZqluGZilqsVUwMkyoVglaU7tCqJrx3Lixr9LR2zs9r15TRf8kpvs4YIG6aWlzpWl5S2HiMucNwvz6l62Ti0TYDV9/UyBSAM+4xqYhcMkTTqoFAWXAJXswJICl7RIu7xRsXbRXEWviKeLBpu+IgMwGfo4ZQCmhB6JCpi0+LuyaoG9NAdKLwBTCX57UNU0FFw/O4U4f0UhLb6LCGr05emg6tlc/MulbeNfKmVZ/8oZy/rXz1M2sG2xEgH/1PgmbOAvnyf2vH7MwwBMSRowaVFhKM7DBQhHCBwc+NY+eo8AVqCQieIrHAuJXRB+VbEThXAtWg0wBcVigAm4UBB3BliA3jpwZm3XaVsM2h7LY7bGQ/F9HORlJ+02zzjue5W2qvu8S5a3rOPqubzBOHADZBLVc+qo0FBzMaGIHqjuu48sN8Yj7P5iHAb9zHgfpc/Y6xWy9U6RTLLQlxUF8QqynGX1Ytwxsl7WIcYh433G+0Jpc5dUwUps8/3c7npShkfxkb7vEs4rICzeJ/icQB8uxITqQaa+39e7Aib2DiYNMOl7MAEwwWnlCIBJczChTxc+ZzQHE96besCU0L2qXm8YgMnQmwCmr8edueO84pr7BA6Yqp3ys35x+bGYTltX1wKkZFcDxJRnHwjZDt40/+R+PrjeomOP/5ji/WDYyF33Jg3bfnfm0O13XWTNwvVhO/xmjNjpN03V9OE7/WZ8iMKx6Y7zxbEO2+mHOdBLmY8xe+5PmHrg4Yj5Po97rzwd2HH92aD6G84Fl5SV3+1sUIZE++BIwsMATI6lNwVMHYrspuFNj9FK0xU6vvUdA6YN98ml5znqVuEANcz57gFTffmYazB3qiQfc0m2TgFMiOSr+clm6lB4D41qeZLWjrlGxzY/orsXLGQNfkLPnybMMcMJ9fiuSGcOBNCmeTdowt+nqWOFvVQ912b6OeVaKsRW0U9steKsqmYApjjlqIDJ29s75cOHp9NLN0/nt13wqBexb8p4aU2X/eLc2v7ilNLPhEnFSZhWjsQ5tUla2FQSl7YOsS12PiPNrTXXMqlkyzDTt1897JI7PXSvV950t00F0t42OaX1nVUnje+s7mnQz4mpv9gKrm1yia4dW0urOiyTlre+Kb/GE2FisefWoXnJ0vcTsvRKQ5beacnaLxNZB2aOESxZB3Lo9CIOT+uxNFTrr6SCpeH5KHq/JK1w/jqAyXAwGfpYZQCmhB7vDTDF1FdJ22YZ/hpaLF5AqWQUUCal/Lw0FFQ1PQU3yEahLb+2hbYvGhLS4ecrIc2/cw2sneuPx2VTF/H9mqVRVIelueRcKLW3k9O76IFgjNcYBmBK0oAJhUx8GReFzO9k1WC8B818xsEEivpoeA8niaPHgumdCAAScO3AiQDXywbGnS/zGI9YmyFrpnoJTY9BM3SXcT0uLuE503SK7/Om6jQtBsX0HP19eF0X9XiXy9ooazfj/bTg5AJkQj8dzZXmiOdVA4Yo/gOIofj/H+PgDMfVX1YLWeUZjxGDAw91qNd1MeHxqBfiPQBQVVRWdVltGe+9g6g8wFa4M64xDlxRUE8K7wlDr15fepcc3I2AiWsYh+x/Mu7EQV86APjXhZhvOrTPZb2DCYBJ72ACYMJnXWICJn1EHt6fcTmYDMBkyIEVH8B0MaTaybuWApceient19elx2La43ctOXdcCS285t9Ap3k+jxtPO/DwV/l5Hcfvu99JVkdcn7T/Qfsp3g/aqWo/2ftBhw9QOEb9cWrH2n6S9wPMgV4dcP/Mw49aLzru33TNmcBaWy6GlN12JfSHrZdDc22+EPLSXBsjfsMATI6luAATivN1mIcSQ1eObVBcMwBMdbN6UMef9pCp2XHFyXNi2+N3Bpge3rTSwY33aXavc9S90gFqlMtL2QcAJgCvyu8IMFVX+06VYOvofypgqvXJZupYZA+NbnmK1o29Tse3PKZ7Fy0khj4hevuEPGVE2p5RwD2Rzh4OJPcFN2li93+pU6W9VD03B0w/slVKTF5pAzC9Uo4ImFDwDL3932e2u6e+enJhh5PtyOJeti39N0iLm94Wp5YjYUJREib+TMKMSiQtaEjSktY3pZXt9tmW/jLTOrd+R+u0skVep6F76NoOBYQ1nX8TV3fcIi1vZRHn1iJh/E9kHZSDw6UeKZRLBTANyvKi11J05VRi8152KuWLciwpUMneuaTJAEyGDL1aBmBK6PFeAJMOJgWUVVWGS4NLmoMpsGwKCqyYloKqfU7B9XJTSPMvKbRdYQrtUupeaNcKR0K7lFke3PqHngE1c1XyLa18y9wYDjYMwJRkAZNWXEdRHu4NFFGbMx4/ht4j6HkDx4Y+Eiyxi8LxKRbDiYC4pn8ZhxFLZU1iHBb0YNz58qdOf7xCf8Zwaf+8P+2ux7R9++10jeOxXWLYXkyPj0ld1WPsLqsP4y4MgCoUfuHcAnS7xXgcmOZMc0TIpMWXaY40gB3E/cGJtlrWGFmdGIeiWm8c/B+BwrzSgz0eQ3OLwJECZ0p2xqPySjLuwMB5GMW4mwVz9686dwEsafdj+thlH6Wp9V0CIHFnHNDCwdZMVhnGIQ9ACWqdGsB8V0MDn3rAVIlFReRpDia9szQxezDhPQBYDQeTBpj0Dib0RzMi8gw5uF4JmB6gB1O143csBc4+EF6CHhcfi8lO3LWk33k1LOvaM4FfzPd5/P30gw+LTtp/v/jE/fdLyCqO65O9H/w89cCDYpqmHHjw84co/THqj3XygQeYA72Ux846/PinxScCflz3X1BBz0uhuXdcDf1s25XQROnV8aEMAzA5lmICTCjMN34JMLm9AEz1snpSp6J7aaTzCVo96iqd3PaYAu6K9DyBIIs2nj19Tg9vCXRw4wOa0/s8da98kBrl3kqVUm1UHDwcMG1U4uw4YNpKzizhHEwV7RxMtVQH00jnk7Rm9DXy2fSI7pw3J7CD6anSz+pfb3/aONeXxv/FHUw1cm2m4oqDaTUVNRxM8ZIjAqbb3t5ppasHv5Quba8aeXzZX7btpgXiyrYnhZlVwoUJ/yNhfFHuXppfj8RlvwRLqzvtlFZ1HiMub91MmFuvuHlcqSyv83qhyzoUEFZ1+l1c3cFTWtpCEOfUIGFcYaW/EgdMqcjSOx1ZB3xO1iE5yDpU70zKowNKmkspf/T+Sop0BfIYC+cGYDJk6NUyAFNCj3cOmPRuJQ0slY6SApgAGconp8CKqSmoWkYKrpudgpt/TaHti1FY1/IU1rOaJbxvnSPhvWrODP29QqcQ528rPKiZOV9iz50xYh4GYErSgAmF9U8Z7y2CIia+JY/iKorp+DY/nECIA3P0IroWp4aCq7+67/sYd++glw6gC9wuKHoCSFRTVdVO2m1VdNf1l9V1l9V1t8d0n72q2am63XPs79c/pkYciun+WuqxNmE84qunrAmMF3/h6EKB+gFzfCeOdl7hYoKT7g6L6o8zUz2uxoz3TirAuAtJ648TXwiAojecsCjo470A2Ao3H5xReB8C1E2UtYrxNYXeVgCY6MekOUgcdf4MxbymtP5egEv4jLvN+LoCvIF7c5CsXxl3Dul7fL3LaDxt2AMmuPP0gAnxm4j9xOdcYkc1ahGDmEcAJkRYLmfRHUwaYDIcTIYcWLH1YBp/5k6LlejB9KC/x4WQakdvmQuc8rPG6Ko5dseSfNuV0FSupwPTzj7yKMOk/Q8yjt1z79MxqnB93N77mSbsi9L4D1QTYhBuH7fvPuZAL+W+qQceZpx39HGGlacC0m08F5za41JIfL8lYoxYhgGYHEtxAaYGzItqMw8lhk4DTJVSbqT62Typ8//20egWHLSc2u7/zgDTo1sCHdr0gOb2OU//OB2kxnm2UqXU7w4wNVV7MNXS9WD6ma1VHFM1Mmymtj/soqGNj9HyoVfowJr75Hs6jMIeR9DTiLd3b2H+rKGRdPeKmXy2PqTVU67SyI4nqX2p3VQ9x2YqkWIdFWFrqJi8P3CU1ZD3sYEBmGKVAwKmZOGXdmaOPLu5VOSRxb/Zto2aI63+fb8wt/Z9YWKJZwpgmlKGxLl1SFreJlJa+9dxm9vfk4Q1fzQQl7bKFzKh+qfeJuUPw3gPafUvXwirOnQSXdttEJe2CBbn1FRcUtYhucjSJwOHS/0ykjA4OwnD8/Iid6yKrTBuwCBDht5eBmBK6PHeAJO+z5KmMsnk+1JQUOU0FFT9Ewqum5VCmuan0LaFKfSvChTer94z81DnSLOp9SXziBaLQvs3aBv8R+kf7znnzYxYvMSeO2PEPAzAlCQBk1ZUx+95+GZ+IVn1Gf/m+XJZRxkv5gNAOLpLQ/9Nei2qCe6rTYz36gFcasg4MED8GYqe38agb2K5rhfAw/c6fRcP6Z+rvx7bY7+L4XU0/RCDfrT7uZAqHGspxkEV4BpgDCL0EBcIpwEiBOFi0vdicrRzrO+rBZcEYsxQXAckW8a4Ows9wyqpc/amPXLwODhTUDdEUT+vOodOslozXjBH9CD6PyFCDQAT6wzQK7Fjygy92XqCMxPrH7AQ0YvoVwa3o4lxZ1xNxt9DWAv6aLz30Wfe3sFUmXHABCeiBpjgokts+K8BYAAmLSJvOYsCTPjMMhxMhpKA4gGYtlwIqXb4prnAsTsWI7bNGA4/DMDkWHoVYKoVA2BqkM2TfvvfPhqj9iI6vSOAAv3eAWB69pwe3xbosPsDmtf3PPWocpCa5H33gIk7t7YovadwzIjJA2Cqlt6dWn2zg/rVOSLvzwXaufQOXTwSTIH3RMV59LYD8XjBDyW6djKE9q7xo8XDL9JgZx/65aedVC2zO5VKjri+tYqrqqJ83LXkfcS+4nhbsh2KDMAUJUcCTG5ubikU99J/mwvYfJbWl3aYRkuru+wSFzS8IU6rKClgaXpFEufWtkrLWt8W13U9KW3sPVfa0Ltd+Oo/vnnT15VWtssvre7UTlzVcY24vPUDcX5dQo8n6/B8ZOn/KVn6ZlTcS0pfJRS443IXGW4jQ4beoQzAlNDjnQMm+z5LClhKTgHlUnLHUtVPKLh2Fgpumo9Cf/2Rwv4oQ+F9apF5eItIy7hODy2Tupy3TPptdfjoNj3C+zQoebtDASMhwcGHAZiSJGBCAROACfF4KKACRKBQP47xfjNodK9FMDl68VwrGqPYioIxegx5Mx5rNpBxuFKOcXiTh/FePYBqKHxmVi/juq4pq07Z7H7OEsv1mB4T22PtXyeb7nW0y+y627Prfs6uE/4PzKkeK5xpKJJXVc/vEFmLZe1hvEit9WJyVBeTBg/1vbXQFwxOCYAyRB8CIKKY/T/25n1yNNcIwFQG9TwUULcJ0NCe8YjFObI2Mw5grzDuAkMkY2I7SQzFby1hjWtrCXAQrhu4+eBMg0NN67sE2A5XHN4/WAv6aLx3DUm02EYAJqxlRDZqDiYAJris9IApMdedNqeYT8SpnmDcJYlozjqMQ9/M6rG8DzAX+zAAk6GEAEyHbpgL+Nw2AJMxHH8YgMmxpEGWKEUBpvoqYKqsAiYF6KTcSA2zedLvxfbTOPQiGnOd/tUAU8K2YFJ6OkUBpgvUo8ohapJ3G1VOvSkaYNKcPG8DmJzV69hGYzUmD+AKIAfxeABMTmk3UdMvtlE3pwM09c8ztGmGL53c8ZjuXTWTJSRScVy96Xga+ZwswRF074qZTu98TJtdbtCMbmeoV81D5Pz1dqqa0Z3KJFuvwC5AryrMXYkvbKQApu0vAJOzAZheyJEA06VLbqkV99KpjcUi90ztJK3rulSaW++yML2iRZxensTZNUha0pykVR1u2tb97WXb1GuKtKlPW2FjrxKPV7bN8KavK7l1yS+t+6udtO7P1fK270uLGpM4tQwJI78k68AsZO33KVkHZCEB0Xgocpu+ikMGYDJk6N3JAEwJPd4JYCqvu9SepzqYAsslk+9LRYGV01Jg9UwUXC8HhTgXpNBOxSm8V02yjGhFlil/kGV2L3/rnL4HLS69Fsg//xk68pcq/j0aGucyCQwDMCVJwIQiJorp+IY8vrCDmLVujMdDeTNexEcB1lHBg32RE0VjOBIATBBhhiIs3DooFgMQwI2C6DMUbFEbQoxa2liUTnd/uhhuf5XsH/s6z9fvR3o7pYvhtpiE34/h4kHcG+BTAVk/M14076bOCyAJXF53GAckkgOfZ32/nDDGnRJnGY9xxHrtzzhELMt4nJjWKwcA9XWK2vrCPuLQAOvgHkE/JgAsFPhHyFooy0vWccb79jxS90vvBEvsOTP08hrSQCXOE9Y8gMglxnt6oecc4uf+YTwWEWsJn4tYA2/iiHubYR+RB8BUkb3cgwkReYnZg0mbVy2aFLBVD5gQ06kHTImbeGUAJkMJApjgYDIAkzGSwDAAk2MpPoCJO5g2UHlZTik3UaNsXtTlf/tpfMtTtF4HmCgWvqLdDAD1Qs/UO+JgMi8A06YHNK/PBepR+RA1zb2NKqeCs4jvD+BXTRUwwX2kubDid+zRFQUmAJm8qK587FWZu/I6gFlwTtXP5UmdSu6hEa2O05JhF2n3yrt08UgQPbppJWtYJD178vqQSYFLIZH0wNdC5w8G0q5ld2jx4ItkanGcfi+1T+k7VSXtJiqfbAN3kSmurS3Ke6WJcszcgdXiBSRL/HXlCHIkwHTPxyedeGFXPunfNVUjto4cIC5t4SlMK/dYmFTimTirKonLWpNtQ/cwacvAPdLmgSZhS98G5o19vjev6ZL1bV5XcuuRX3Lv0U7a2GO1tP6P+9KyFiTOqETC6G/JOjg7Wft/TtaBWUkYogGmN3UwJXZx3pChpC4DMCX0SDDAVD52BVVIRkEVk8tKQYGVUlFglXQKXAqqh15LX1Fox+IU3qcOWcZ2JGFufxJXjI4QVo0/LSwf5WKd27dNyIQuRQJNrXJfci6UOrHnyxivHgZgSpKACQVMAAt8XsKl0VzWcFnrGe9FgmIhgA0Kso5eMNfH491hvPC/VtZIWb8w7l5CkVbrzwMnQgo7JVeF6yljuUwRy8/abfF5XFz3a0AkBYu+L6l0249JqWK4js9O/A6fUT3HKPQ6Md6PCfPiynhh/RrjTgjNqeao51o7x1iTKKxfZTyqDq6TMYxHmgGSaiARx625Jl4HCmiQCXOXiXEnGJxvZRiPWQSwHMW4Ow5RZScZd8zB7QfIBFDnqHGDH6uesygILarnCZ9vcKAdYTxKE/28EOvWknG3EKLdsI6wBjQ48j7j3TTApDmY4gJMgK+JObdY73hfaoBpJYsCTHjvGA4mQ0lArxGRd9yIyDNGEhgGYHIsxRcwAbJUkFUl5SZqks2L/iy2nya0Ok0bxvnS2d2BFPrQ9kqQooElTXHBJW0AXB11f0jze1+gHhUPUdMc28gpJYc+FbE/8r7VSmDAxOHEVmokbxPwCseP16qUagPVyryFWv2wg3rWPEiTu5ymNROv0cEN9+myTzA9vmUlISxSAUbxHZgHIfyJ0mvqok8Q7V97j1aNuUITOpyink4H6Zdvd1Ldzz2VeQdMg6rL+1RX3je4l5qq5zC6Cyvx15UjyJEAU8Al709sN7y/tp1ybSh5DhkrLmh4wDqxeJgwuUSkOK++RVz/d2DEztEnbbsnz4zYNrKZ5DUgv7fJCX84v9Uv+Qpg2tKvnbS532rJrdt9acUvJLpUIWHs92QdkpOsAzJHAabhcfVZMmTI0LuVAZgSeiQIYNKcSmWZzqmk3l4pJQVVSUtB1TMofZYCa3xiC6r1aUhg7cwPghvl9gv+5Qe/0K4V/cKHtfQTXPr4iasm+0nucy+K7nNcBdcJf1hdehU53aV4KlNiFyOMEe9hAKYkB5i0/ksonn4hq4Ks32TNkLWT8cIrouYc2dWi11N1X7HPcJTsl7WI8SInoAAAGuLiAB0AXjSYlCyBxV7xc0y3x/QcFsPtye0u7W+3vw0CbMLv8XBB4DzDiYN1hT5b8xg/13B7oa8RYvIAcBwZMKGQDUAAZ90dxkGoB+NwAP2lGjEea/aFesyAiRqse13IlFJ9Pgr8uRnvbVVenb+/ZY1lvNfMTnU/4PgDZALkNCCT40hzLj1RzwvgEtY7ACViFhEHitjDQbLaMt6vrAjjnxdwACZW76C4IvLgnrN3MCXm/No7mDTAVJtxsP05MwCTIYdXPAHTkZvmAicMwGSMJDAMwORYigswoQdTbcXFs0mJikMcXfWU7tQ021bqWsybJrY+TRsn+NL5vUFk9o+Im6Q8k/9FPqcnNq6nEc/peTzaFgU/kMhn8yOa3/MC9Sh7iJpm2UZVkvPoOidZ1Zi7vI9blB5MCQGYomANh0yIykMEH0BW5RTy62Vwp0Z5vKhjsT3Uv94Rmtb1DK2beE0BQxcPB9FDXytZg+MJmeSHSJanFHBXpMvHgsl7/T1aM/4qTf7tNPWqdpDafb+LGubwohrptlDVZO7ysW6W92WLCpe2Kuep2UvnzwBMmhwIMCULvHokY8T1gz9EnFzV0uY5aKawoOFJ66SSZmFauVBxafMr0pYBe237Z86SDrt0tO6ZUMRkSphfTiW3AfnlbbeTPAaukjb9c09a2YZEl2okjP3RAEyGDDmUDMCU0OO1AJMGASqq0sMltcdSIKBBSfXn8skpqGp6Cq6ThYIb5ZKVh4Ia5rwXWC/bkaB62TYENcnrGtKmsGtot6qu4aPauYoLhrpKG1xcpa3L5ouei3paVk+pFDyre6bEniNjvN4wAFOSA0zat+PRW+RHWfUYjxlDtBGKruhLgkK55mhx5CK5/hv0KByjdxS+4Y9CbBfGew+hyKnFpiVuo/n3OzTIBLAGNwYK5yj6woUDJwScG1pMHqCNBkYc9XxrLibAMMTSId4MvXOWyRom61fGnR4434g2Q1Tgm0abaXOHNYMCOfqU/ahuH26/7oz368F7ZheLDpns4/IcdT4/dNnH4unh0jHG4RJAK3prtZdVg/F+ZflZFKB83ZjFhBj6iDx7wIT3bUyAyRF6MOE9CUefPWDSO5gS77PXAEyG3hYweQAw3TIXOHHXAEzGcPxhACbHUkyQBYV5zD+K8+jzU525Ky4egKaaKTdT86zb6K+i3jShxWlyG3Od/tsZQKEPYncwPYl4RpLlCVlDIskcFKHIEhxJYvhTihCf0bMnsTOYgDsCHV7/gOb8dZ66Fz9ITTNto2rJuKsI+1VTcfN4qG6et18z+rg5gKbGCqDg/ZiqJJPnILU71c60hZrl30adi+2lfrWP0NQuZ8h19FXas/IunfMOpPtXLRQe+OqeTJgTwKWrJ0LogNt9WjPxKk3p8i/1rnGI2ny/kxpm9aQaGTZT1ZTuimsJ56KevD8aXNJDwcReR44oRwJMwb7HM0X47v0x4uTqX21bh88XFzf/T5heIVScWfmutLzVDslz0PgI7+nNI/fPLG7eOy5LQr2w4mDyHNRW8hjgKm3s4Set/JVEl6oGYDJkyOFkAKaEHgkOmACXiqugqUIKCqr5OQU3/YJCfvmBgn/9wRzcouCRoCZ5ZwY1zN41qHHeNkG//tgmpJtTm/BR7dpY5w9rI210aSNuXeYseS2pELx2ar7Enh9jvP4wAFOSAkyaOwP1EXxLvxTjhfkJsjwZL1xqzeMd3b2kFZABHVA8vsOi4vFMjMfjoZfKF4wXahP/W/Tvd+jPNX6HRk8ZFKrh1DAxHpOHmDm4vgJZ0ojJi1T3E261m4yDgg2yJsnqKqsO4441ACE4UN403kyLytMgE4rk+P+psKzKjPd86sH4+wYFdQ0yIS5P35MJ+5uYEWYfo7RIPO2zQeu5BLiESEjNuQS4NFRWB8bj3Iox/lmRhUX18IrJWfiuh30PJvQBw5rTHEwxReQl5uc0Xh9zjPnVAyYtIg/HoDlHE28YgMlQQgCmo7fMBU4agMkYSWAYgMmxFBdgaqQW5wFX4BSCk6dOSg9qkXk7dS20n8Y0Okmug6/Q0Q0Pye+SmUTzE3r65PkLiZYnFB5ko8D7Ij24YSW/K2a6fTFc0d3LZrp/3UqP7ogU/MhG4cGRJMjPj5CevXg+4uZu/hdGuxbepent/6O/CnlT0/TblP5DAC61FTePh7JmGicwYGrJdijCnDRS+zHh+OEkqp5qM9XN5EHNcm+jDoX2UN/qh2lC+9O0fPhl2rnkDv27O4BunQ9XjkuyPo02J1CE7ZkC2R7csCixeIBLaydeo6l/nqG+tQ5T20K7qH4WT6qWyp2cUmxSXhNRhXCUNWaay2qHKgMwxSZHAUwocmqAKfLU2ra2naMX2la0OSe6VHsszql+TlrecoHo3quVtMNUIGTPhE/VaLwEGQpg8ujbRtrSd6W0sdudFxF5Y34g62AAJvRgykLCkFwGYDJkKFFlAKaEHvECTBoI0GCAJv3PSr+lZPJtyeXHJwNsehJYIVVEUO3stpBW39tCfytpC/mt9MXgdoUXBTl/2fZxvRyFH9TMnC+4VcF8wX9Vyhc8pFW+4Dm984lrp+YTPJbkDnebltl3Vvc0iT0/xnj9YQCmJAWYUORDsQ/A5WvGI6HgxljIeE+eW4wXY1EYd2S4BOlj0wAcUDzerx4LCpwNGHckwL3zCeOwIHG/Rf9+hwZJNCcEnBmIkNNi8uYzDkZQrE4KMXkaNNCizu7LOitrB+OwAMfkzDhURFEeoAAuJu28v+n8pVa3k0WdQzjBnBjv1wPINJHxojri8rSeTJhPvI8EdU6fMsPN9D7XyBN13jH/cOdpPZc0uDSXcbjUkUXBpQLs7ddMQg17wBSTgwluucR2MEGag0kPmHozPq+A2vjsMQCTIQeXAZiM8YENAzA5luICTIA2DRS4soVqyaojq0EKT2r56Xbq8s0+GlbtGM3reo48Z92iUzsek+/ZMLpz3Uy3FYXTtXMhdPFkEJ055E8ndj8mn20P6bDnA0VHtz6k4zsf0ylvfzp7NIgunQqmq2dD6eYlvg3o+n+h5OP5kNaNvqbArC4F91HT1NsUJw/gUn0FuvBeRE3eEWBqod6uubkAmQC3aqbcQnUzeFCzHNuoY6E91LvqYRrf7hQtGXKJPOfdosObH9IF+bhuXQine9ct9H/2zgMsiqsLwxewl9hLNChRYxI1xS6gAoKCoGKjqCt2UcEKNmxrV4y9x+6qKL2JWLGBDRv2WIMVtrHLNmz3n7N3RsYNqMmP7oL3PM/3bJudnXLnLpx3v3OesIL7j24q8a3zMnz+4At8UPQI7150W19qb3KXZDz498O4e8047FQyUl+SkOu55Ka/Jrjt47aNAqYPyZQAk+z+4QoEMO310R1csFm3e/BVzXqXJ5o1Tmc1f3ZdpN0+oH1BlcXjBwFMk/ppowN3aEP9Hmq398GaVfZYPe8nrAqqQQETFZXJiAKmgo53gCklsZUeMM3tu1cqaPhA3IEFTM0QcSW1Yu635KkFq9YEDkgcSup7LEk6lMeSdmXkYpsSd8V2pS5I3WqmSPv9kiIb0S5FNqr9LumQ5mMlXvVa3u2MKDwqokEBU6ECTJyjBeZJgC+9GM1CxAVyCZEkIZSbKwyuC87Rks1uN8AGcGHBr/yHIVIeD35BD0ljY5W7MnYAJIHkLgA2rkweJH6hTB4cpyiUWyYPgIgOGT9h/TF4AOccxig4OAAqggtrF6O5iAADgKaNGdVEpDzg/wMLODcJdwyh1GJdRr8yckDvO5m2M0pApA8NbBdADRm7rTmIlsz7EoJ5C8aHjj3uUkaPESmneJpRJCJwaRoiziUo4wZw6Xv23P4/ZRULMjgwDIApvxJ5HGAypoOJK5HHdzCBMxIAfydEfsQAgAmuQeOCfQqYqChgovE1BQVMpqW8ABOXnCcupnj9+YDzAn2OeljEYe9yCXjId4dxQPOTeH7383jDuDS874+/cPz2h/jA3kc4Yd8jHL/3IY7acQ+H/XkXh6y+jUV/3MLbF93EWxfc0Gvbwpt455JbeNfK23jvur9w+KZ7OGrbfRwnIutIZBS/7QHevfA2Xj70Ep5kexoP/PYQ7mVBtqcr61rqoVe8Hi71LJDjQUrjcRDHi30M6+7KQiZwUAFo6mQehV3LxOBeNfdjn58P4zF2J7DQ6yxeOfYK3jHvFo5adx8f3Pk3PrbvMU7a90SvY3sf40O70nHsnw/wnj9u4/VT0/CCwRdwYOdTeEizI7jXd/uxc9lofQlAAEwd3vWYinsHl7wpYPokmRJgkl9Oqphz82CTl6l7BuQcXrRFt3twmmat82PNinbJ6pUOc9SrXVt8js/WA6bowL7ayMDt2lC/+3rAtNIeq+dSwERFZVqigKmgA+Ze5Z3UqpoLia3U+5b7KfSA6cd3gCmjKXExcbAJHmf8zug35vHvLCSwL4GlrlWwtIcllnWzfCV1rn5dYl8uTGxXerHYtaZQKvhVKB3VXigbZe8rHtzcIaPb9/ScFOGggKnQACaurwz0ObNi1JbRUEarGB1GpFQaJGQhOWuqLhbDxCZsK7hZHiJSHm8PIsCsD6M2iMAAKJXGJY2/tuDK5AFggwQ6ADfoIwRl8mYjAmZOIeK6gTJ5kJQ35TJ5XM8tcDEBvHmECCADV8oKRmMYdWPUHBG3EVca8f8BBnwnEweZYN0AmewRgUzwuQsYbUWkhBmU7ruJCNyAawogKAfvjF3SrKiJK4nHwSUYG+DGg/H8CBEYA+5MgOirGU1FpOcSgNZmKG+4ZOz4FAcTv0SeMY8/HzDBtWgImGD+pYCJysRFARONIhYUMBUecZCJuJnIbW/zeOxdKgH7VDmIR9Q7iie0OoGnu6Xg+f3P42C/izh4/EW8aEIqXjA+Fc/xP4eFvmfxjMFn8LT+KXhq32Q81ZsVcx+emz7wDJ459AyePeIcnjvqPF4w+gKzjlS8hFlP8ChmHX3P4YmOp7Dvj0dx34oHcC/z+HdgqZd+jBAVBFzi5KEXB5mIowngTg8esHBhXV3OxaKxW3lmvNbcj/v9mIiHt2GOicspPMPrDF40NBWvGH0Zr5lwFa8LSNNrzfireMWYK3ix70Us7H8WT3Q/hUfZJWGfXw/h3nUSsFvFGNyxOClJCD2mnFmXFgA0zlmVC5goXPrY+DU9wLQvFzCtdnysCW6Zol7cbJ5mSZvWn+OzNSETLPWAKSpgm3af/z0KmKioTFUUMBV0GJbIU/BL5DV/HzBlNGPFQiZ9+by25ljSuTKWeTXA8gG/YZng16eSHvUixZ0qTcxwKOuc4VLdWtrnJ2upr421bHj7X8SDm9a64aFP2tAookEBU6ECTPB3HTh6GjHqwmgSIglBcF1AMhwS4abqYDFMKnPl8SCRDI6Ro4iUx4PyTFx5vFqIQAGun8rXFoZl8uoyaolyy+RtZHQIEYcH9A7iyuRxSXtjn+f8zn0Ou62Q1L6OCCDdjIgzBXpvATyF8lwADvj9dAriOBo6mewRKc3nz2geo02IAC8AdwAC/kZkjCoQGa9cGUJTPsaFRZyr7TXK7bcEwBncPdCjC1yZRxjtRQRAwnwnYNQRkV5dVii3LJ4pOJe4gG3grlnOwQQ/BjD1HkwAmLgSeQCYuBJ5FDBRmbgoYKJRxIICpsIrgBmeZvuxd/EE3K/sAexT9SAeZHUID21yBA9vfRQPb38MD3U8igc5HcE+HQ5jgd1B3K/tQdzXOhH3bcWoRSLu05xVC/a5Nom4n20i7t/uIPZpfwgPtD+Mh3Q4god1gPUdxUNaHsEDfmTWUSMRe5ZmtsOMAKXejAgI2l/gkIW4uTgnE5EHC5kAWnRnXV1uUKrPPBq7lIzBnb+JwV1rxOJeVvtxn0aJeGDzw9jX9hj2tz+OxzqdwOM7ntRrrOMJ7Mc859uWOU6tDuO+vybi3j/sx91qx2G3SjHYuTSBVi5mpL9UV9ahpT/2esCU8A56UffSh2W6gGnhFt2ugWmalQ5PNAt/T1HPazRfuaCp9ef4bABMmqiJfbSRgVu1oX53KWCiojJVUcBU0BEaGmqRfTW5uuZsQhvN3j9GK2Z575N6N3wgtiv+zrFEYIAZzmhpztwWw5mtS+DMNqWwuF0ZLHGphGUe9d7KhrXIzvJrnyEfbnNM5vXjvAyXys4vbFD1uw1QybudG+iVOrx5ceHXV5LqqwsKmAoFYOKcLJBIrY0IZIBEK5T2gl/EQ5IekuCFwb2EUW6flY+VxwMQAO4dU3AlGCO4Em+Q4IVycVA2DsrkQWmwUYyWIQJDLjJKR7ll8oydtP4YVIBzD8l16L11D5HeOvsQ6Yfki4g7pQkigBH2uyB6wBhCJgATdRE5ngAA4JqF0oNCRHpChTNKQmRsQm8zgB78vky0ZN7/PwfkVRIPShMCcAbYAX2xAKAvQQR6gLMRSigCGKyDTBMuQXClLcH9A4AJXIecgwkAE8zXpuRggu2A484vkcfvwUQBE5WJiwImGkUsKGAqHOKXzQOI4/muNxEjc0YlmMdlEnDvCvtxz2rx2L1WHO5SJxa7fB+Dnb6Pwh2sIrFDnQjsYBmBO9SOwI61GH0biR1rEnWA+7WY29qMvmNes2Qe14nETnWjcCerKNzZKga71YnBXb+Nxe5VYnH3svG4ZzHiWiLbs/8foKVgYUuCAWQ6wIo8z0GmzmbRuJNFNHYqEYUdyzDbXyEKO1eNxq41mXH8XRzuUZfZ7u+ZbauXoBfcd2ee62LJvLdWDO5UPQo7VWL2vVykvu9Sx2JRemjVxYz0luqJcvtCeRrAJQqYPixTAUxMmOl7MN041hh6MOUcXLhFt9PnmmaF3RPNot+S1Qt+mate2LLl5/jgXMA0cYsu1P8vCpioqExVFDAVdCQlJRVT3ThfU5MSb6PZHTxWOcMzVOpZ72FmWwuS8IYeTG3MsbhdSZxpVw6LHSthsXNNLHGri6U9G2BZ/1+wbKRtdlZAp2uKQNeELD+7BVKvRh6Zzt80MPa+0TBOUMBUKAAT10cGkn1wrToxGo2I4wd62EACHBwWplwezTC5DEl6SNg/QqQkGVcez5sROODrovfL45lK8tgYwfXeAuAG5x+AiA+jOYgct2REHB+QoAc3gim72AzLI4LzDiAO9D+C/jqBiPQWa4WIQwXKjJVCBeNiM2fXA5AJwAQACktEHIG2jNwRAZzgpILSkyGIuKsAdkAZQkjC80vmvWT3hYKmf3/9wxjlXEswd2Ui4hYDNx6MZwDnWxjNR2SuA5eZHSLgEc5ZZUSuCVOcH/iACUr4cSXyAKCbYg8m2A6uBxM4mPLqwWTcHxtRwERFARONryk+Bpjc2H4/3Qu47BnVv9P7cGn/O+eMNwAOswTsYb4f94B+SMVjsXPJaNyhVCRuVyYctykbiluW24ebl92Lm5cJwS1Kh+CWpffi1qVA+3DrkqFEcJ9RK+Y1eL1lmVy1LrsPWzPraVsmDNuXisAdS0RhN4sYZnzE6bcNPt+LJwJcChYw9Xx3HBLelabz4vU+gtfc9fCC9GTqYBaJ7czDcbtijEowKhWO25eOwPZlGJWLxA6s7MtG4PbMc+1Kh+G2pcKwLXMs2hYLw+0twpl1RDDritKvsxuzrz3NmM83S3gHtnLdVJ/HuVXUBCUNwQHmys4pxgRM4tuny+fcSfop5+I+ge7Qwk26nT5XNSvtn2iCm6WoF7eYp1nh8NlK5L0PmLzfUsBERWWKooCpoCM1NbW4+tLpWtrT8e1UOxeOz5raM0zaw+phpo25PuFNeiyVxpLOVbDE3RJLPX/EMp/mWO5rh7PGOmPFZHecNcPrnlLYJzRrSvepspF2nWVe9ZuIbfW/EqfxFQYFTIUCMEECFZw8MD9C6ThIwM9CpC8JlJGC8mjGTlb+GxmWxzuGCCwbj0h5PHAogFsHIMDXWh6PC8MyeZBc58rkQckwrkweuCIgaQ3ww5RBI1cWDbYRXCsAFmAMQJ8d6CkF0GwgIqXrfmRUHZFxUFBJbkPIBKDiO0Y/IQI2XdnPh2MLjpMdjPYj4rIC+PE3u838knl8N1NhuP6Med75riUYqwDsAG4AIL3M6Dgi7jFwkc1CxNHWHREACCAQHJwAHSFHDGPCFOES94MADjBBycfBiDixADCloVwHExwLY5fI4wATVyIvrx5MFDBRmbAoYKJRxIICpsKh/ACTF+ucgWXc9cn7GH2voPYoHFujUNzSbC9uZhaCm5rt0asZ2oOboxDcklErtJfRPr1a6rUXt2DUnFneULCeNmb7cFsUpu9H1Jn5HHf0T8Dk+RkAU0+eer1zMR14r/8R6cnEupj0xyAK26MI3I45DrbMNtswsjYLZRTGU6hebRi1Zva/DSNrRPbRjnmfk34/o/Wumx7MtaCHS2a5zim+a6ngHVtFTyYEmNCz1NQyurvJ9XOuhHu+PLxonU404JJmdYen6qVtLmqW269QbejhIt3V75skoX0xoVD/h2mB/ANAARMVVWERBUwFHXfvJpTUXD37nfZUlL1q+7zArInukVJ3y/RMSHiDe8nWHEtdq2CZ9w9YNqQFzhrrhBXTPd4oFw5/mb1ijFa1OuCZctX4BGXw8CD59N72L0bYVM/0qFZOaOzkAQ2jBQVMhQIwcSXS6iJSbgn6eaxEBCz8hUiSFhK2hSG5DdsISVV+eTxIuvLL40FpJnCXwN+xppZANkZwZfKgtBuAN3BxQAmrkYgcN36ZPHAFFZYyebCd4GIDaJPKKAaRXjtjEOkxBn12ACh8gwgQKqjvKQ7aAQSAXCMACyjHB2UZAd5Bch16QY1FxEED8DMSEfgBEARgCIxdzs0EoIm6mT58vuHYcOccgAYAOoAsnGvpLKODjHYzWs5oCqNBjNwYtUEENsI5AsgKsN340CP/yAswwb4AYIJSoPweTBycNOZ5yQswcSXyOMBES+RRmbAoYKJRxIICpsIhPmDil8jjSsTBMu5s+TFw3TigSD1cAbDSBr0PUGyYx231CmMUzlMYC2NC9XCKLxv9sgBeInBHvasHxgQBTB4cWAInlRkHXj4vYPJgnUucg4mDbDBOu+ghU7R+O+E42BmCpnfi71+o/vX2jBz0+0jgkr48JPSZMuP2M/fzKGD6dzIlwPTwYVIpzb0TlrqrMd1eHg1ept095JxmbccMzYr2dzXrOu/VbO8/RrN3dBtd1MT6ysipVW6EehRIo3gATNrowL65PZgoYKKiMk1RwFTQAYBJe+N0He3JKEfVtrmTFQFdYiVdaz/LbE0S3ZIOpbHM83ucNcoWK4K64+zgYVi9cVq2JuSPR+rItama8NVR2TsWChWrxrllTvSoaez9oWH8oIDJ5AET1zAegAv8gh8S7+CugEQgJGWhxBgkuU25LJphQpMDC4/YfYBSZEJEeqxw5fEAKhRE752iEBwQgcQ6VyYPQGN/RrMRScqfRqSfEfQ1AuBh6oCJczHB2AXnFUCGo4y2IlKiDkol2iDSwwZcRgVVJo8L7phC8hzyjZBIh+/E+oyaMnJAxCkIfZlmIAJ0oRwh9AU6y27vI0RAAUA9cGPBuKZuptxzzIlzLWkZKREZo1BuEMYrAObjjKIYbWK0EBGwB3NBR0bN2HMC5wbmBLgGYBwU2A8XP0MYlsjjAyZTdTBxPZiog4mqEIoCJhpFLD6lBxMFTMaXYQ+m9wFHgv7cuL+DK6RMnCOKwh1QpB6YgJsHbjswAgeS0ztF8RSpf60DTw7v3kde68isF9YPoKA725fLgwNLPMBUkMDFEDD15u17bpk68pmwDNePCUrbOTPb68QeB87R1I4H1LjH4PiC/YRjAO9x0zuXYt/tY2/+fvKOOwf3qD6uTwFMG78QYIJSTdl3L1XT3jjgmHN8xWztvpHHNRvdMtVrnMSajd3OanYN3qmJnBiojp3mnh07o7E4ZlKBlGDSho6towdMUQHbtKF+9ylgoqIyVVHAVNDxHmDaIpwin+AaJ+la64U+6W9jgaVdquGsYS2wcqYnVq0ej7UhwVibuOO5LiUuSXcucb3uZJS/Kmpjp6x1U+oZe19omEZQwGTygAmS4FDKC369D+4KAaPFiCQqoSwalOsCoFAYnBOccwW2F5LMXHk8SCxDUhPK40EJQFoe7/3gYAj8XQ8Ojjoot0zeREQcNuBmA+hhWCbPFMcEB5i4sQBOIHAFQS8uKPsI4xvcbAAYGqPPNx64cmaQQAdwAQADSvJZIeISg7JsAHQHIDI+FzHajAgMOY5IeUpwEALkhXKPXNk8DjTxHU2meB4+9/nlXEsAlgDAAVSG8fmQ0U1EzjcAOwCkAPCmMxrOqAcifYvgHNRFBKrC/5AcZDRluATB/SgArlVDwBSPcstZGhsw8R1MHGCCkpB5ASbjBgVMVBQw0fia4lMAk97FwSbaqYyr3nkoN4EfrwciUNKtqx42xb0DhNx55NRNr7g81dVg2dx1xOkBQTf2c3ry4MuHtuvzHIcEA3GfS4APbFsP9ljAtkPpQBe9q4kAJ0e9CGADp5MzC866sKX/eujdWfHv1tn7H59p/LFQ2ATwrxvrsuvKA0xTbJO1wb0u3l0zKC1ig++1seuHXWux5jMDJqFQaA59mF7eOdrq5elN43SRgdHarZ5PtOu7ajSbej7Tigbd0IWPi9JGTpqmjZrkmB06ulpBfK4eMEVO6qeNDNyhDfV/oN3eB1PAREVliqKAqaDjHyXyJrtHSj3qP5Y4lcMS50pY3vdnrJzUBatWjcfa0OU4JykUv7x66v7L+9dCXj68NkZz+aStdv/uuplrR5Uz9r7QMI2ggMmkARNXagkSlZDsc0Sk4T0AhZOIJGohqQ19YEy1545hQpNzrUDfKPglP4CyZYj0WoHyeFCmDBLKtDze+8Evk/ctyi2TNwqR4wfQw7BMHudq4wvn8dx/WeZTlv/YeiC5DfABxvATRlcZJSDSfweS3NB7pzkifacg0f25HG1cXyYYc3B8wS0IfZmgLBuAPCdGnijXzbQKkX5R0JsJnGMwjvll88Clw+/PVNRBE/+ccmAJ9p0rhwfjEUA4jE2AylAOMQmRsoMwly1ApP8awPPOiLgYuZJ44F4DuFgSFQ64BMEBJhizVigXMEFPLw4wwfHgSuQZEzC9QrmA6RzKBUwAd+E7B757KGCiMnFRwESjiAUFTEVVeTt9/ov4jp1e7wCO6Tl3iLvr/f0mriYCm9xZQNZF726KZcs/kucIVIIxHv+uz5VhnyVj719hlykBJghIdubcPdno5bldA3T7hZt1u4bc1G7x0Gg3e+Rot/fL0e0eekcb4rtZs2eEp2aHT+2C+Ew9YIoKFDDaqQ31e0QBExWVqYoCpoIOcI6qrp2toTkd2yZ792J/xZy+u+VDW96R9rZSS70bZmf5OyiUC4dmaUSLsnMOheS8unISv0n/68FrWcbO19Jnw17+dfn37ITQandXjS5p7H2hYRpBAZPJAibOXQF/y8G8+Cuj3og0vgeXB/SCgYQ29yt4wwS2YaI/r+fyW/Zj9z/0/g8Bhg+Vx4OeN9BrpS76vDChsAbnYoLcGAAQ6I/CL5MHwOMUo7uIuMNgXHCA4w1Prw30iif+c3wHiuF7+OsyXPebPGT4fv7nwjYCcISSYQAfTjASITImBOw+NmD3uTT6fNCRg0zw3QhAAxLr4JwCt+8v6H03E8CQeYw2MNqHSO8gGMsADh4gAk/5oCk/R1Nhh02GUAn2kSuFB44lDiyBwwucXlAOD8A4QGUAGQBGgxBxLcGcaY+IgxFcPzDnwTwA4x3mAgtUeOAS/4cBVihvBxOMdzhGhnN3QehT5n++ixC2AwAvjGE4LxMQgdd8wER7MFGZsChgolHEYmX/K1arB17ts8rn6qYlHpfSZnwAMNEku+mLgyxcfyJvRn3ykTdP+S3DX47f78gUS8Nx+24I1HIBUfw72NSdVQ+eE4t7nxdPnhQwFZg+BJgW97p4d/WgtIj1vtfGrht2rcXqLwCYQkNDLbT3T9fRXYnskpO0bK4uPOCYdufADO0mjzfaP3tizcaeUs2GHhGq9d0Hajd2rVMQn0kA06T+2shAkXafXzoFTFRUpioKmAo6kpKSiskvJ1XMTo5voopY0z975Zg1iqnup7NG29+VT+h4I3tO/0uqjdMv6mK33np55uCL139defVW8uLFW516/xu1Ys7rx3/1UiXv/z1769QCcZTSKPxBAZPJAibOsQKloeDvJ0hwD2W0ApGE9m1EynJBAhuSlHmBgPyggOHzeYGBD7331SesKy+YAIl2DibcQqTnDjgYIKHJlccDdw64SDi3Ag0SHGDinBEwJsDdA+XEAhFx/UC5MXDTQLIYIB5AJjjmObxbkJZ9rOVJY/A4v+d1H5Dh5/CfM1yOe57rywNjGeAMuCgiEHF7gGMIEt1QJg/+NgDw8zn7wcAxhnEHcABgFlx74KYDNxM46+B4g8sOejNBCb8pjIIRKfEYzugIu/1Q/u0hIgAYYB84tLgeTXm5mowNiv4fqMRd39y4gnMJY48DSwA8ASwB/AR3GpTDW4MIQAQ3JoBlOMfgWvqZPdZVUOEqiccPDjBxJfKsEAFMAxEZK7GIXKMAIWEuhDFhOH8bQt9XBs/nB37zm/PfoH/O0dw64PNhfIK7LIXRNkTmYyiR9wO7DyWQsY8/BUxUFDDR+JpiZf/LVqsHXumzyufKpiUeF/WAye/nJNy3UiJ2N4tnk8Fx+v4p/yxLZnqQ4WsXHzDxIZOhvPLRh5b1LASAKT/XlgfKv3SfIZjy+gecooDp35+Lf84VHwZMqXdXD7oasd43bey6YWktmPufHTBBKO+kVn1164C17sy2ETkJc7fr9vqlaTd5qjSrnLH6j/ZZ6mDrWHVwq6HyhW2sCuLzSIm8iT6MdmlD/R9TwERFZaqigKmgA0qTPk4JLa09HVdHfWCbq3r7vOnZK0bvUS4anKBc4hup2jBdpAldtVN3LCL+5cUTaa/v31C+lbxQvtWq0t6qFbEvn9xboU2JH5y1Rdji2fCu9H8sGhQwmSZg4icpKyGS3HZBJPG3BREXwD1EkvKQ0AWQwAcCGvRxcPD/6FPWqeEJtk/Fbisk3CH5DmWyoKwb/KofkvX88niQ3Kf9l94Pfr8gAHDgrgHwAolgcIBAf6BQRsmIwEcoeQXHOouVgid4LGcl+5eS56GsfynD7QC3DyTcATBBmT9weQCEGMeoG6OmjKAKAvRI+tzONu44czAPvicB6MHfJlaIHHNrRK5Hb0YjGU1jtJTRVkTKvgFo4hxNUDoPQEsmu68AFTjwB2ChMLia+FCJ71bil8GDaxvGB/QW+huRMQguSwBLUEoQnIrrEHF+wTw2EJFzC/AF3JmcawmABlz/nGupMM4B3NiB8VoXkR8HDGC0EJHxAWMcjhEfPoLUPKkMbvnS5KH/MofDurLZ7YDvE/hegR5jYxEFTFSFShQw0ShisaL/ZatVA6/0WelzZVOwx8W06RQwFWrxexHxYUtBqTDAFn4fKA+e8usVZbgc51j6Er2kiqoKC2DKvJFULudO0k85lyPdc46tnqOLmJSo2dj7mSbYOkc166fn6iCrSHVQ3cHSafUtC+Lz3gGmqMDd2lC/JxQwUVGZqihg+gxhBs5ReVJURfWRvS21kWsGqHcumK3aKlySvWP+HFXo2inag7um6JL3r8y5fPLgqzsXn7xO/0v3OjNd/vr5w6c5ty5c0x7du1W5aeoQ6VT3Rnc7Nyj5nkaDOuuVOrx5cSF1EBT5oIDJZAETJCkh0QpuQyjRBeucjkgpNOj7AglcSFxDQjfTQGKeDJ/PzOP5/6q81sN/7gVPABDAWQMJd3A0HEYElkFyHvrbgIMBkrEcRLD4P49hUQzOYQPjAlweUL7NhpEXIm4aKNkG5cfARXMDkWMNiWxwJzxmbzk9YgVQ5yGr+6we8PTQYJlHBvf/Nrjl7nOf+7eB0g2e594DCW4AMmfYfViLiDMLxn0LlFs6ERL3nxs8cJCJA3pcbyboBwR9gaB0GLjtoHyfGyIuHD9Erk8ATTCuwdEETkMAfjDe/2L3F64DDvxxria+g4XvOvlQCbTPDZMwytu5+JLdZgAUACcAmsE1D24tGBPgTASAAqUOARSCYwnAEvRZgvM5GJFzCkAZziv0WqrNHttyqHC6lvjBL5EHcxn87wtzWx9EXFtwPADkwPX5CJE5EcYEf578kDJ4esG7n9cc/7F5nlsHbAf0PwMHJIBd6OsG54crkWf8cqUUMFFRwETjawoeYPqTBUwqCpioioo+BJU+JGNvd2FXYQFM+qbzd1Jqv7p+yPZlyna/nLiZu7R/9rqjnvebXD2pxsPssd+EqMZV6qcMqFW1ID6PAiYqqsIiCpg+V9xNSCipOxpVX5uwtYM2cm0/VdjqQdqY9f00B3Z7aJNi+uWcSZycc/6IKCf1aNrLqyeyX147/eblpSSsOxGJ1WErriqW+a+VBzj3lw343Vbq/ZONtM9P1tLBTa2l4+yspYFdrJVTe1jLxrv+Ih5sW+uGhz65QKOIBgVMJguYIMkKeRBwqjRj5IEIjIESRpAIhEQ8OASg3NI1RJLz/0XX8tGHXjNcLr9l03iCBCYknqEMEyTeoc8OuG58ESmR1QTllkGj7qX8A+AKl7yGxDzARzh+4AKbiwjciGZ0DBG4AbDpfB6C58FlA+Mo5QM6w7vl6yyrc3l8Bjy+YPD4fD7Lcs/DOgFKHGC0B5H+POBg6s6oJSIlASHZ/SUAExccLODK5nFuJoC+AA7Acfc7eh80gaMJ+gpBOTQAfuDc2c/uGxwTuFYApgHwgwQ/uH74LkSujN5LlOtwMuyj9RZ9vG9Pfn13PiTDkmqcS4krf8c5XgCOASQD4AHQDMrgwTUO4wHKXsL428loNSJjMgARsASlBR0ZtWLUCBFoWB0Vzl5LHwrYdq68KVyjMH/DOAbABgAHXExJiIx7mBNhHr/C6rKB+M/BHGo4p3L38/sOyGtO5z8P64BrEM4bXHfzEXFbgbPMCr3vGjTeOXkfMN378/fFV66UCjijQyNP5QKm8SYAOqgoYKJBowBihY8eMHmvHHBlY7DnxSvTO5zJpoCJqiiJwiVjHPO854r3AFMpApgmc4Bp8NWI9SNYwDT4ywAmKNkkf5hUMefuscY5l8K8XybOW63Z5HFZPffnzOxxZe5njzAPUY0u3SdrZIVKBfF5FDBRURUWUcD0GcNMkRhaWRG37Qd1zIYWmthNbTQJu9pojkbb6M4e7Kg9d3CILjnhD93xiEO6oyEPdQd3aLWxG7FmTzDOXhOgUAj7JMvHOGyWDmw+RypoJJT6NBFKh7cSysc5CeVTugsV03sKsyZ39ZWPsnXI6PM9PSdFOChgKhSACZLY7oiULoKSclCKax8iiUpI5sYg0tsjlr3/KeIvH81bTwzvvuHzMR94Pr/3R7GCbQVXB/yCH/ougaMBerBADyH4hT+UyIK/E+Fv18KeYP6cwSWvAcTBD7fqM2qDyHEE58FsRBL7ACLhWO9FpHReGKtQnvaxr4fko/xe28tqH6vQT9CHluW2A9x5UKIL+oyBGwh6jnVGZPxDbx4AEV96fPBL5sE1CYALjj3Armrsdv3AbqMtu71QOg/KFk5CJGEPUGEHItcAwFVwIF5CxO0D7jBwsQBsglKBAG8AOHGl0bjyZxzoeclTfn17DHukGUIjw/5o/HVyMIkPlKCMG+dUAqgEDjSASgAqAJqBIwcgGpxHOH8AB2ciMl8NRGRs8sGSFSLzGlzv5dhjWgwV3pJ4hsE532CcAECDfYb9H4jIjwRWIXJ9wpgPZxXByvBxJKsog/t8RaO85/C85mj+e7h1wnmD7xT4bgGoC981AMUAjpVj98WUSuTxANOIUxj5ntQDBQqYvmJRwESjiMXKAVfqrh581XPVwKvrl3hdujTd8YzC/+fjBoApFndH8TT5TlXoRaGS8Y77BxxMmsW9L95ZPSQtbP3Ia2PW+V5rztz/IoAJ4nFKSmnt/dN1Xl2Ncck5GjxXu837pHp+k8cAmJQjzSKUfmUGSyfV/q4gPosCJiqqwiIKmD5n3E1YVVIWurFCduiqaqrQtTU1B7da5iTF/aQ5c7B1zpnDPTXHoyZpE3Zs0YSvPqHZueBv9capr1TL/bByjuCNYqLbC9mottdlQ5qfkQ34hdGvZ2TDW6ZkjbVPUUzskqKY6p4iD3DZJfe1Hivxatjybmd9AohGEQwKmEwSMEFwpdAgiQ1lpOwQKYUGpbimIlJuCdwB0NMEktgL2NuPacG/XN7wfZzmfeJj7ha2FeAHgANwNAA8gF/127L7B3M/JDONX47JtIMrn8j1ePmW0c+IuGjgeA5hNB4RF80slDtG8tLcD2iewe2cfJbhn/d5H3nuQ5rDbm8Qu/1DUO74+AkRIFGe3e8vDSDN0PugiSubBwCBczRxoAn6CUHZQnCV9UbEuQNJ+xmIuJrWIwL+IMEPZSLBZQawCUqmAbR5hAhw4sqfgVMIXE588GQIn/jS8cRBKR3vNq8+PNw6Yf0cTILPhTJqXGlLAGF3EHHLgOMFoBK4zQCCbEcEasL5noyIiwvcXF0Y2SNSCg/GKEBkGK9QDq88ewyLo1ywVBTgEgT3AwHYP4BoVoyaIwIffRiNQWQOh/E+B+V9bX3oujWcWz80TxsqrzkAtgPO2whExiy4l2Asc/3wjA/+KGCiooCJxtcUqwZeqbtmyFWP1YOurv3D+1LqDKczcv9Gx3Hfyv8ETMZOUlNRURVegQvyH4Dp+6N4SttkdbDHxVtrhqbt2zDq2uj1I641Z+5/McCUmrqxePa95OqvrsXb6E6sCNCJBsRrgps/UE2s9Dh7dMlj2eMqTVNOa9xW+Yd91Wcbh/9f3+sUMFFRFRZRwPQFwgxcpKkbhxcXx2wpr0mK+C47+WAT3ZlEJ+3xyEHquE1zNLsX71RvmHpatXzk39nzBBplkPurrLFOr+W+Nq/lQ5q9kfs0eSvr3+itbOCvb+S+rV9l+bV/qRjrkCMf1fa6fMDvm+Qe3/eXudVo8rRTZUupey1LqXd9S+mgJoxaWkpHtbeUTuhENM2dkbeldB5oENHSUZbStRMYTdPfZswfWkM82La8kCaQTSYoYDJJwMQlszmIAL8kb4xIst0FkcQ7lMzzYuWdx613Ho/7fMJ9w/fn97yXwXP53ecee7KCMlmQeOZ6sECZMUg6c+4U4yczTT/4vZgggQ1wAxL44ARzQsSBAOMDkvz9GPX/BPnkoQG8+/zl+PcH5PPej73G/2wBKxiHnuz2d2Jkjci4h/J4ACXKoNz+PMYIPmjiyubxQRMk5OFaBVcZlHyE8+HAqCsi5wJcTQBXAbRCr6aNiLi2wEUCZS+PI1IqEMqmQfkycDgBdAK4A66hpygXPAH8AQgkZSVjBXAoKx/JWcnY98D7xez6ACRBHyUo3Qe9lO6xnw9AKRWRMolQRg36KoETbjsifbIWIuLKATfiIEQABcA1mKuaIgKP4fzB33YcWCqN/lkOr6hd81wfJoDm4GKCMQGuIHtGroi4umCsG86j/PmzD++2Tz6P+6C85+v8ZPg9wc3J3DUHYxbOGczJplEeDyLmuswBtCH5xaB3PZgmpOj05fH4gCnABGAHFQVMNGj8n7F6yNW664an9VozNG310r6Xz83sdFY6usnxt32rJGJ383jsimKxG4rRJ4Z7oHi9C6EnhU1UVFSfoJ6sAC4BpO7CzCOuzHzSBQBTmQQ8vN7Rt1PbpyiXeF+6vs732p4/R18ftdHvejPm/hf7xTkkOMW3T5fPSYv76eXpdQO0oSN3alc5XFfNsMrMDqhyK3tirV0q4W8TVCu7Oyp2j/nhRqjwP/f0oICJiqqwiAKmLxn6cqVJURW1pw/XUZ852kx3MsZNt3+Hr3rfsrmqLTN3Za8ad1y5cOAd5UwPsSKw85ssPzssH9oKy32aYFmfhljm3QDL+v6IZYJGWN6/CZb2+0kp9ah3Wur+7UqZW/WRkm7VBZJedQSyfo0EsqHNBLKR7QSKsY4CRaCbQBHUXaAQegoUc3wEikWDBIolQwWqpb4C1eqxAtWGIIFqq1Cg2hQkUAT7ukJvJ2nnBt8Y+3jRIEEBk0kCJgjOqQLJWCjHBQm/eoiABOi7AyW5IGHZlL3NT83zea55Po+bGsjwvR/6vI+9BtsMDg+ABvALeehjA+6Pb9j9NCY8KGzBL8MFkIkbH1COC4419C0CQANuGts81JZ3ywlcUO0NbtsZLJPXewyXa2dwa3ifWw8nG1ZQ6g/KqMF4AUADYwTgWRWUW0rNFACkIWjiHE2Qt4SxDNsL58MKEfcVnA/YTw7+AUyD3mMAm6CU3GJEyuhBmTLogwOly6DkHDicoHcTQCdwDUEfHgBP4Ha6zegvRADUfVYPWT1CpDcSKJ13/xGrB+zy99h13ESk3B30+7mAcvthHUIEKIFLCUDYJkTKF4ITBhw44MQBqASQAnpQ2SMy7uD6BqACsA2ub4BvcP5Ko1zHkimcx88Z3PwN4wKgGr9vF4xtbv6GebdFPjJ8La9l85vHP/YdYDgvw3cKjFUrRGAgjGOudKHxz1PMdWkH0Ibk54OH7Lm76bdFl6+UHM8BphMEMAFooIDp6xQFTDSKWKwdnlZnw6i0Hut8ry1f7nPltND17Isxv5143a/6QexeLF6fDOYSwu4oTp8kJqCJwCZIItNSY1RUX7fymgN6snMFzBnghuTcS53Z+cSzfAL2/eHY62kOZ2RL+12+vHHU9R1bxt3w3Tz2xu/M/S9a0ghcTKob+2vqzmzprIsJCtZu9TipDm6VoZrRUKKa/sMl9ZzmkepV7kHq3WNcVfuDa/7Xz9EDpmgDwLTKHqvnUcBERWVaooDpS8eN0NASesh0JslKnXygpe7ovq7ahC3D1GFL56i3CTer1gYkZC8Zfkk50/uFYmIXnOVvh+WDmuoBk7RXHSztXgtLu9XE0q41sLRLdSzpXOWxtHPl0xK3KmGybjVEst7fi2SCRiLZkBYi+ShbkWKso0gx0VWkmN5dpJzlKVLO9REpFw4SKYOHipRLR4qUK8eKVBuniDSbZ4k0m4JEqqUjF2RN6OyV2bfeD8Y+VjRIUMBksoAJgivJBX/PQYIWQAK4JCBZCXNlzY/oW1af+nx+qmGw/Mfem9/rNVjB9oObAZKYkOsxdDPQ+HhwCWxI2PPBBhxnSOxDMrsuImXJQFasuPv1DFSfVQNW3GPDZQzv189j2fp5yPDzvjeQFbu9luz2wxiCsV4R/XOMmEqY8cSBJrhWYXsBKsD1Cu4VgGSwjwCHIakPsKkjIrAJHChQLhJgDZQpg3Jp0AsH+vRAr7LtiPS9AsgDfXSgLB2Ap2OIOJ5OIVJmD3SW1TlEQBFf59nn4XVwI0EfqBPsegAkAdCCsn3gTgKYtIXROkScVgCUoMQfADHo8wXONHAqQck3e0SgIIBjgCfgVoIxyL++OVDBAeSi6FjKK7hrFMYu3+UGY4Kbg2vxVJtVrTxey0+G8/K/mdf58zLMyTB/VGS3lbveTOM8RV+TOoLWn34+ZMjuvzb/tvDS1ZLjknV6uEQBExUFTDSKWGzwu/bdprHXu230vx68avDVpLndzj8e1/xkTv9vD+HuJeL1yWBnFK2HTFDWCpLE7jw3U37JZSoqqq9Hec0BHFyCOaOrGYFLLux80sU8FntVPIBH/pz0cmansxkrBl45t3nsjU3bJ94avC3w5q/M/f/sEvqPYfbi6sGyLy+FtNAdWTomJ2J8iPbPXnc1wW1Vqjm/y9RzWz5RL3eN1YhGTtbELbHOTFpbLilJWAx+dY/+xR+wFDBRURUWUcBkhDAD2J916lQlXerR+poz+1vrjkd11h7cMUATvTZQs2fxH6pN03dlrxxzXDl/0G3F1B6SLH/7l7JBv2OpVz0sda+JJc4VsMSpHJZ0KIMljqXfiJ3KKyUulTOk3Wo8k/au81TWp+ET2YDfnsiHtXqc5dfucdY4x/SsQJd0xVT3dMU0j3TFTK90xZx+6dnzBqRnBw9PVy0fm65eE5CuXjEOnkvKGu0wX+ZVv/OLTuWq322ASurVmVMDvW54NC6RZG8iv5wt4kEBk0kDJgg+SIBELfwivjSrMgYyfD6/5T6m/Nb9/7ynNE+l2H2Bv1OLoaLXg+VLBeeigbEBxxKOMySHAW5Acr/iB1TJQJUNlN9reS37b9/HX4bbngqsvmG3vxy7P1yfHlOHj4Y9muB8wFjnzgcfNgFw45xm4NyCcpHgAAJoA+6mYYiUnJuISM8y6JMDLqfliDidNiACgLYx2okIEALnE4CofYxCEQFFfIWyr4Wwy+9g3w+uJABJKxEBW/PYz4TPBugFZf2gpCG4lLohAsbAjQbuGXAqAYwEMAigAuBJBXafS6Hc69scfV1giR+G8zc3J8IxKseqLE9leK/znyubjz51Ls7ve4I/J3PzMh8EmkZEpUk7gtadej5s8K6/tvw2/1JayTGndWjYcYyGnyBQYXwewMHY4IOKAiYaNP5DbB53vfbWgBuuW8bfmLfWNy1xQc8L9wNan1L7WB562710PHYxi8EdUdQ7yOSmh0ykJxMFTFRUVKC85gC9c0lfFi8Wu5oRuNSJmUc6mUXjLsVisXfVA2/9fknSznY993j10KsntwXcXCuaettn55RbjZn7XxowoaSkpGK6tPh6OWd3u+ccWTpHGzrmiGZt92fqea1z1MJmWBPseF+7eZBIF79o5KvkPda61Kj6ynORVeBX95/6GRQwUVEVFlHAZKx4mJRUKvvSyWq6i0kNXqYkNNUeC7VTJ+5wV0VvGKQJXTFRtWvhH6o/p+9UrRibqJgruCgPcHkoH9ZKJvNumAMOJolzRSxxLIslHUoT0NTpGyx1rYyl3WpgaS9LLPOqj2X9fsbyAb9i+eAWWD7cGmeNtMNZ/k44a0wnnDXeFSsCumDF5B5YMc0bK2cJsHJGH6wI7PJUPqRVlKxHnckZTmWdM+yKWWc4lrbOcKlsLfVoYC31+cVaOriptXhw0xbgcvrbrUIlYx/Loh4UMJk8YILgktd8QdKScwVY8MQ5KYoZLGO43H9RMYPbvF7/2DJ8fa1J54IMQ7DBiQN4Jdj7huInlA2fM3yNe1w6j2UMk9N5rad0Pu/nf3YJg+3nj2HTSnZ/OAzL5+XlbAKgBo4RcKBYIeL8AVgD7iYoa2iPSB8j6N0E0An6aEEpOoA9/ozGMQpkNIVRECLuIiEivZ0ARs030Dz2+TnscjPY94FjClxJALNGMhqCCOCC/l3groJ+b9BDCkoaQum73xApowaADEAZ/L0GrhcOKpVm95Mrg0evbxL8+dtwTubP1/9WhvMy/77hd4XhvJvfd4NpnrOoNKkzaO3JZ76Dd97Z9tu8i9dKjj6dg4Yex3rIpAdMyRhNSCa370Rh01chCphoFLHYMflmTVHQrY47p9ya/ueY65HBfS5en9T+tHxQvcOvelTYj52LxWBHsyjsxAgSwy4sZCIuJi6pnIA9EAVMVFRfo+C692DnAG4eAPgMc0RXRnoXJIBqZv6AeaSjRTTuUioW9/028c2YFieU83ucv7fe79pBUdDtP/YK//LaM+vOT8z94saYD7PSTlXKuXbk15zUMI+XiUuWarYNPa1e3EGqntkUq+e3zdFtFFzKiZ8venUuZPLrtITuOVcSG4tPbyn/qet/HzCNygcwVaWAiYrK6KKAyVgBztDHKSmlFSmJldUnE7/VnYqol524vbFm/9bWuv3bOmr2b/FUx2721YatnaHeNneDcpnffuV0jytZo+2fywf88kbq8T0plde5MnE0gTpXxBLXSljSpSqWdKuBJe7fYmn377C0hxWW9qyPZb1/wjKPxljm9QuWev+GZX2bYpmgBZYNsMbywbaMrLGsX9PX0t71bkg6VwuXOpYOFncoJRR3KieUdqsulHo3EEoH/i6UDm0llA1pMUkqaOT5wq1GkxuN0Rf/scTXFHkCpkld9b24JB3LE5gCgKklC5hsKWAyAmCCMEz48ZOAZgYyz+M5w+U/to5Pee3fLJ/X59EouOCf+7yUHxA0fJ1fyszC4LX81mWY1M7rOcMkeDGDdfHHreFtYR0rhufE0MkC7hWubBr87QPACdxAAHCgnB6UnYP+OdCbCiAPOJ3AQeSKiJuoByIACtxF3oz6IgKj+rPyYQX3BexrUJLPi30fvB8gFpS6g/5Q0HcLABe4k6AvD7isAH5BeT8oXQjl1wCMwQ8/wGlm6FQybUhh3MhrTuTGRV6v5/cew+NqeP9D83x+60bI1M9X5FWpC2jNiWcjBu24s/23uRevl/A7lYOGJGE05DhGo05iNI4HlsaxooDp6xAFTDSKWIQIb1cLnftXu72z74zbMfnmjhWDL5+b5pzyfFijo7pe1ROwc+kY7FAsEjtYROIO5lF6N1NntlweOBS45LKnPsGcQCETFdVXJv4c4MnOAT30pfFi9TAaXEuOzNzRwSJKP484lYzG3SrE4f7fH3od0PaUNLhvatqWgBsR++b8JYxcdK9b+MK79Zn7xYwxH964EVpCeetclZybSU1yzu4SaMOnrlMvd7+sFrYGwIQ16zwluuiZt14lb4t/dSliBiMnZdKeqp+6fj1gijQATCvtsHouBUxUVKYlCpiMGQCZwB36OCW0dGZSaDl51LaK2ZHrq2sSdn2nOxH+g+pc4m+6M4lO2sMhg9VhK+ar1k7cq5zX/5wiwOW5fHib1zKfX7DM6wcs7VUXS3taYmmPWgQsda2GJW5VsNilIhZ3rIDFjowcKmKJQ2Ussa/CqCrzuBqRYw0sdvoWSzox73Vm1LE6ljhVyBI7lL4ndihxQepYKkXqXD5F2rV6itSzfgrzmSmywc1AB6V9f1qa0f3bXk/bl7Y09rEsykEBU6EBTDRo/Jf4f4HhxxLSnwISP/UzinrwwQLf2cSVK+OAE5QRBJDD9dMC6AR9qwD2gIOoCSLwCSAQAChwF7VGBEQBIIKye7YGsmFfb8MuDxAJSvT9gghI+hERsGWFcmES51ACxxUHlLiyhYbl7yhUovH5IvKq1A20+sQzP5/tt3c3EqbeMRtxEqMBxzAamET6MI05jdFYvgAypRBRwFS0RQETjSIWUcH3Kscse9Ayesn9YXtn31mzzi8tSeh+Ln1E02Mve9c+gDuVj8Z2JSJw+2Lh2M4iAndAkaSHCgVMVFRUKH/ABBAaYLQjisL25hHYrhgzjxSPwI5lonC3qvF44E+H8eSOp8Urhly+sGvG7Z3Rf9wP3L/qYce4lQ/qMPeNApjYMJPdT63w8tr+FrqEZf66TYPC1IudnqoX2L3SrnJ/q9vt/zonfsGjl8fWbs45uqaHInFZ5U9dMQFME3y0URN2a0NHPtFu96aAiYrKJEUBk4mFPvkD4An630EZPfXtS7VeXjnZSnNkr7d27x8zVavH7VDO7ntCEeh6Sz7a/rF8hM0T2XDrZ/JhrTLlQ5vJpP0bZ0u86udIenyHxa5VsdixPBa3K4UzWxfDmc3NcOZvCGf+inAGiLmf8TujpmY4o5k5zmzBqJU5Flszamv+SmJXLEfiWEoncSmvk3WpppP1rKuT9/lRJ/dprJP3b5wp9ax3WOxWdUaGfSmnpy2R5f+l9qDSlk87gSpbPnWvZSn1rm8pHdSEUUtL6aj2ltIJnRi5W0qneRPNG2QpXTqK0QRL6dppltKt8/RSrQiqIZ7UrbzQtJrN/+d4B5h2LAxWbZ5JARMFTDRo0Pi8wQdNfEcX17uJKyfI9W8C6MT1sALwBL2cAD6B4wkAFJSrq8MKYJQVq+9ZcffrsqrDvg/ez4Gkquz6OZjE74HFlb2jLiUaxonIq9IuoFXHn43pt+323h9mXnig773U/yhGPscwGnZCDxX0kImvsQZuJkMwEcCTsSEJFQVMNGiwkbj+0TeH/0xvcnDD314xS+/P3zr5ZtyCvqn3/G2Ov/Kql4g7VY7G7UpHYNviYbitRTi2Q+HYCUXp+zFxgMnTILls7IQ3FRXVlxMHmLz0OvAOMHWB0ngoGtujCNzWPJyZQ8Jx25LhuMM3Udi9djwe8vtRPMP9TMb6MWknwxffW83MQcOPbXtsfWRLes2DG/82evJLffPkt7rTO1214TMWav70Oa1e3kWsXe6GtWt7Y90mH7Vu+4hwza5RXtJd/b751HW+A0wRLGDaBoCpPQVMVFQmJwqYCkGYqa6drfHyTFwzTcSaHtkbgkYrFw5clDWt15+KKd1EiqBeIoWwb4hy3qBIxVyfg8zjs/KxTn/JhjYXS70avpJ0qYnFHQBCWOjhUsbPjBoi/OIHRsxtxk/sc43ZZPzvCIsBVNggLLGzwJIOJbGkY1ks7VwRS7vWwLKelljW2wrLwDXVreaDTJcKYZn2JaZn2CBBRmuebFi1/ohgmXaM7C0EGY6lBBKXSgJJt28FEs/vBZJ+jQSyoc0EspE2AtlYR4Es0E0gC+ouUAj7CBTzfQSqRb4C1VJ/gWrdZIFqx3yBdt9SvdSbZ7rJ5vv8KhvevIKxT15BRObaUeWytwo7aHbMDVZtnnGJ2WcKmChgokGDxuePvMqlGZYr5KAT19uKczuVZQUg6BsDwXdTRVaG9yuwy5Rn38u5krj+WPx+WIalEb9G1xkNU4ioNKkrCBxM/Xfc2fPj7NS76D0H08lcoPSeg4nXi8nYEISKAiYaND4xToielDm951m9k7ueOh/c+PeEkHl/7Vw+4vLlQJdTqv6/HsKutWNx+woR2KZ0GLYByGQWpncxgTMBeqxAMplLLHsygkSzsRPeVFRUX069WbgMc0AuYIrDbswc4cTMFe1ROLaxYOaPUmG4XbkI3LF6NPZoeAD7tTuO5wsuPNw27Wbc/rUPZ5/Y9bR3StjzJsn7nlVm7hv9j/8XVw+WfXkloenLYxuH54QHbdNs8rmqXeaq0SxshzVzWqrVc9vEqBbZCBTLrP+7g4kCJioqExUFTIUhUlNTi2cnR1bPjlz7s3L9RFvFfIFbVlB3Tz1oWeIrUG2aPkiz54/R6pCls9RbhRsUf4yMz5rW84rcr12mrF8jLO1aC0scymJxK0QcTI1ZqNSIUROShAdHE8ClzGZIvxwAJnE7MyyxL4YlHUpgiVNpLOlUXg+aJND3iZG44zfZYodS1zPaWRzIsEEiQ4n5apOHuNdszUViu+IicceyIrFrRZGk27ciief3Ilm/n0WyIc1EspE2IvlYR5Ei0FWkmNJLpJjVR6SY7yNSLhouUi71F6nWTRZpts8XafYtI9o8c5Fi/sC+Yr+2DY197goiiIOJB5iW5QOYWrGAyYYCJgqYaNCg8ZkjL/DEOZ34ridQCQOV5MnwNQ4elTBYh6E7yRAo0aBhvIi5Ju0A2nD6+eBhIXf/bLb4yuVyAWc0xUaefGMx8tRb8zHJ2CLgjB4qmAek6GWWL4hIzkcpecvY8ISKAiYaX12cCXte4nzki5pnw5+3Oi562i96xYPgjZOvH5zV52y6b/uk1z1/3v/W8dsobPtNGLYuGYptzEP1jgRwJnRDcfoEsxcvuUwBExXV1yUOMHnzAFN3Zm7ozMwRHZi5wtYsDLcpzswd5cKwfdVI3KV+3NsBrQ6/meSeLFvhf+X8vkV3Nx3Z/njUmfAXHVJjM60uRGeUM/a8CAH9mLS3kqx0qVGddMdWTdSFjI/Qrux2Tz3rd3X2+JqZKv/K8dljKvllT/r254dCq1J3V3UuCboR6lEiNNTDIq91qkP8a2ljJvXTxkwUacP8n2h39MWaVfZYPffnfADT96yMnWynovraRAFTYYnUjRuLv9i5pGzWwpGVMoK61ZCM71JbOs/bUrp2gqUiZm0D9YmYprqU/S66I3uHq0KWLspePiZMMd3jvHxk2yfSfo3U0u61c6QdK7yU2Jd6JWlX7I3Y1kwPIzLbsGrFqjVJzr8PKphl25ljcXsLLLYrzqoEPH6b0c48O8MWZWTaonRDiUE2rNrkIRt2mXZm6cw608VOpdMlLhXTpd1qpEt71UmXejdMlw38NV02vFW63K99etZ4p/SsiV3SFdN6piuEXunZcwekZy8cmq5aPjZdvWFaumb7XL1UayedUAr7LJb52bqKe9b99m5nVDJvNfinRoM656HRzHcf0Q2hR4kkoT0k+75IUu/hNmGp7J0L7DQ7Fi5SbZ11UbV89BvF5G5Y1r+RHvrpzyMFTBQw0aBBw1jxod5V5ih/BxT/PifD932ofxYNGqYR8TdkLUHbzmX0mBTzcL7bxpsJjeZfum81/fyL74LOyWpOu6CqPjP1ZZUZF3CFaedw+alncZkpZ3GJSWewRSAHIZIJgACn0+jTpKSeP3t/dB6l9TiNM4BQxoYpVBQw0SjycTbihcWF6IyK5yJfNDwV8qzDgT//9tu94M6GpaMvn5rUKzndx/aQzK1hrM6uevhb6zKhuI35PtwOheOOKErfh6knooCJiuprVl6ACeCzMzNHQElNazNm3igZittVDsfOVjGvvFokKka7nXg2f1jqlS2zbu6NXfsw6MSep+7nol78ejE+s1pqbEZJY8+LEElJScWUd5Kq5qTt/yUnZVt3beyshdoNXkc0c5o+UI2t9DB7qEWScigKzvaz8FbOqGOrWdreRrPDx1odPropOJWebRz+j78BZKHDK+TETe2tjZ++XRsVkK7dNRBr1jhh9bxG7wOm6bWwHiwJ6/1T76DTx2TsBD0VVWEWBUxFJTKTksppb5/7XnvxSDvt/p391ZtnzFTOH7BJMd45Xjas1Sm5T5MLsr4/psn6/XRX2ufHpzIPqyype42XEpeKWOxYGovbmxMo0YZAJii39k4seNKDKGsexGCUacuqLSvbXOnXxy4nts5D3Gttmc+2K4bFHUoRl5RrFSzt/i2WQim+vj9i2YBfsHxoC5w1whpn+dthxbiOWBHYGSumuGPl9N5YOUeAs4OHY9WKMVi1cgzOXjT4uWJK1zjZ8JZTZJ51XTO6VLfO6FLZOqMHc9ujtnWGR11rqUcDa2kfRj6/WEsHN7WW+tpYS/3srKXjXKylgV2slVN7WCtneFgrF/hYK5f4WiuXj7NWbphqrdwyx1rx55SWyqV+DbOmuFX6UudXE7KktTpk2Vz1jnkXVCvHv1FM7Y5lPk2Y4/UNBUwUMNGgQaNwxIdAFAVHNApvHLglbwAKvSy2WZr0dPiYiAcrPbbd2e+6/kZKh1XXrtmsuPagxfI08a9/XH3ZcNEl/P38i7jW7FRcZcZ5XD7onB406fssAYAAqAQQYiToJNGokyyYOGUAnZLf7+Nk2MspIA8ZG7Z8jaKAiUYRi7MRL8zOR2WUOhv5olpy6PMfk3Y96RS34aH/9vm31gePuXR4XK+T171bH5B0sop6bVshDLcptg/bIlImzxXF6vsw8ZPLFDBRUX1dIoDpwLs5AJ4D+Ay92toxc0Ubi33YuiwzZ9SOxD1/2589wjXp3uzh509uFN4QRay9H3Rk15OeyeHPfz8XnVErNS6z7IXYjDzdP8YIaCSfffVg9ZyUXb+8PLBwoHaX73rNso6ns6fVv6nyK3tZORzFq0eh9dnTasxV/9F6tnZbX6EufMxYddS4ztqQEVaG6wPolHNgdo+cxLlbdbHT0nUhw7BmnTNWz29MANOkilg1pQoBTMLvsXp2/ff1DjRRwERF9XlFAVNRiscpKaU1105Yqg+FtFBvnu2mnD9woHyCywT5SNuZMv+2i7PGddyQNbVbmDKox3FFYOebWSNsxLJ+P70CmCPpVA6L7SwIrGhJkvPv1IxRc16fHwAZrQnMyDSEGbYG+hBgegdDwCHFfLZ9cSxxJKX4JK6VsLRLdSztURvLPOpimXcDLO/3E5b7NMHywb9j+dDmOMu3Dc4a1RZnjXHAigAXrJzSDSunusP9N1mjbG7JfRpHSHvX/UPcvZZQ3L2mUNzzO6G4t5VQ7FlPKO3bUCgV/CSUDvxVKB3aQigf1VYoH9dBKA90EcqndBcqZvYWKmb3FWYvHCjMXjJCmL16gjB700yhettcoWrTjCmK5aP7yIJ6/fpwoH2pL3Fu1VHrmquj181W715yXrUm8I0iqAeWDWiCJc4UMFHARIMGDRo0aBgxDt+RVwHF3ZDWF6VmOq088WzE7MTHCyfFPvzTP/xB+OCQe0f6iO5e7r7t9tOOG29q2625hpuvSMONgi9jq3kXcfVZF3C5oHN66EBAxOlc0MQJ4BIfLHHKCzDR8nmmJQqYaBTBOBf5wuJsxAuATBXPRD5vcCLsqUP81oe+24NvLZ/vf/7ACLdj93r8Eq91qBGBrUuFYhuzMH2ZPBcUg7uheD1Uog4mKqqvU+8DpgTcg5kTXJm5ASB0WxSGrUuE4naVwrFbw1g80OHwi2mDz5xaP+fapshND8YfC3vidib2RZPzsRnVzsdklLkQm1GMuTWZX6kJhULzuwkJJZXndlR5dWRVO13sjHHanUN2alZ2PKUS/nxdFVj5piqg7FX1jNpnNUtbn9Fu9U7RhfpHacPGBmn3DXd4sbN/Wf76lHEBVXMOLOyTc2jBTl38jMe6kOEsYGqEVVOrY9WkClg1uTIpkQdJbupgoqIykihgKmrxOCW0tDJuY1X5mml1s4X9GmWN69BM6mdjrQhwcVbME/RTrhk/Ub1p+irV2sDY7AWDrmQFdH4uG9xMK/WwwhLXyljsUIo4k1qy0KI5Dy5xECOvMnqGQOlj4kMmWw4ysU4mhxJ6V5XEqSyWuFTAUj1sqoql3aoTZ1PP2ljayxLLwOHkWQ/L+vyAZYKfsdznFywHt1P/Jlja9weFzMPqnqTHd6nS7rVS9OpRO0Xau24Ks68pUu/6KdI+P6ZI+zdJkQ1umpLla5OS5W+XohjXKUUxqUuKYnr3FIXQI0U5v3+KMnhISvaKsSnZG6akqDfPTFFtDDqSvWzUiqxpvT3kI+ytPvc5hfKI2kRRO23ctoWavcsuqtZMJIAJHEzOFXLPFwVMFDDRoEGDBg0aXzqO3M0qATp0W14x9rr0p32XJY47zmcKNqS8GLvixLM5C488WTMz8fG+wNhHJ0eE37/Vf8/d5z133Ml0/vOmpO2aa9Lfl16R/7DoctZ3sy8qq824oK449ZyuwqSzr8oHpLwtOyEFlx6fjEuMS8bFGVkwMh+XopcZv0ze2Hw0Lh/Rfk4UMNGgUQCRGp9pdvmguNylI5lWyfHP7OJ2PBy5bnba5kn9Tl/qZ52Y7WwZjduWC8M2FmHYDkXgTigad0Vx+gSzl1kuYOptAklvKiqqz6/eKBcwwRzgYZaA3VG8Hj47oEh9/yXb0qHYsUYk7v1bwpvR3U88+GPSpYjQDXennIh96nLxWOaPV49LKl45JLa4mJBpMmDJMJKShMV0ydvr646v7ZpzYMF07b4xIZoN3S6oFzV9qpn1vVYz98eX2qU2r3Wbe77W7Rmcrg3x3afbNdhPvcOnqWbrIEtNyChLTfQES/V+YQtd4oJxusT5UbqYSc91ogFYs8oBq+f8QMrjBZTFqonfYPXUaiSpzSW49aqbj6xy9S45/m8AE4VUVFT/FAVMRTTMQj08LFKHNy9+w6NxiYcDrUq9COxRPXuZX2PV7j+c1bGbfTXRG4LV2+aFK//wS1EE9fxL7tf2hax/E7mkZ12luHM1rbhDhVdiu3JY3LY0FtuUwJltLEiZvNYsYOIgE1/WvFt+CbyPASbuOcN+T+2LYbF9CSxxKIklUD5PD53KYEnHsozK6cvDAWCBMn+SzpVIaT23qsxtNSztotdraZfqOZIuNXSSLt/qJF1r6STdausk7t/pZD3r6mS96+lkXj/oZP0b6eSDm+rkvq10WX7tdFljOugUAc46xWQ3nXJ6T51yjrcue9EQXfYKf51q9Xjmdqw0e8HgY4qg7kKpfztnmU/zOtJBTSylg1paSkeB2jPqZCmdwMndUjoN5E0EvbPmDSJaOkrfR0u6dpqldOs8opClzHfpWkvNwa2MQiyVx0J/1CRFeGkP7Vqv3bv8ump1wBsoD6jvwQQOJgqYKGCiQYMGDRo0jB1H7siLJ96WV4m/IW8Qc13WMvKatGPYVWnvkMvioTsviCdvPPNi2dLjz3bNOfQ4fvL+vw/5Rz1IGrT33inPnXfOdNlyK9Vh3Y00m1XX7jRfevXv3xZdFv8876KqwezU13VmXsA1p53DVYPO4YpTzuLyk87iMhPP4lIBZ3DxCSnYHCDGOLZ/E1dmzz+PPk5891NeEIrr5WRsIFPURAETja8g7qZmlbmeIrU6Ff/MNWT1nfnzR50/7tvxqMS9YRx2qByJ25UIx3YWEdjJLAq7mcXinmb7sac5gUxQLo9AJiJjJ8CpqKgKXr1517gHYq57uPaZOaCX+X7c1TwWd2LmBnvzCNyuWBi2Kx+OXevG4AE2h3TTfM6kbV54feOhsPT+V06Lf757OesbY893nxqy1NAKOWnRv+Sc390z5/iqmbqogCjtpl53tSvavtUuaYm1y9pi7brOWLfFA2u2eV/Rbuu7WSMS+Gv3DBVowycItDFBAl3CHP+XB+Zu0MZNS9aFjJRpN3XHmiUtsGrGd1gVWA6rxpfAqgmliZMJIFNQdayeyiioBqOaWD2tFqPaWD39O6IZljzxQNQsTmyyHErqcTKESPzXPuaWEn5ARgcCVFQFKQqYvqYQL55UXhGztoH2WKSd9kS0jzZxxwz17mXrs9dPDstePPSIIqjXWfk4pzT5sNYPZf1+E0s8Gmql7nWxxKU6lnT4BovblSQl8VqzfZla8pxNLXg9mwwdToYuJ0Onk+0HluPcTW0NZc7IgpTWe6diRO1LYolDaSxxLI8lHStgSadKjKpgiTOnqljiyuyTW00s6fYdlvasi2VeDbDsXQm+ZjjLtxXOGmWDFWPssSKgE1ZM6YqVMz2xck4/nM2IOVZ/ZwU4R0D5QfmQFv1lQ1sKZL6tBTJ/e4FsQkeBItBFoJjcTaAI6i5QzOglUAg9BYo5fRj5CBSLBglUS3wFqqX+AtXqCQLVhiCBaqtQoNqxSKDds5T5Ll0t0MZvFWiP7BNok2ME2jP7h2pPxi3QJYriNbuXPMpe7veWWb++PxWUE4RjxPXJooCJAiYaNGjQoEHDaHHglrxE/A15hf03ZTUP3pZ/f/RuVuPj9xStku4pnJjHXlHXpCN3XRRP/fNsxuwVp54vXnj06YqZienrJsY92uoX+WDvkH334vqK/jrec8vtK64bbjx0WH1dar08Tdc0+ApuvPAybjD/Eq47+yKuNSsVV5t+Hleceg6XmXwWlwg8g83Gs8DoXXk9gzJ7fvweTsn/hE180GRsKFOURAETja8kHl5TlL98UtwifsfD8aumXIkK7Hnq737NEl+71orBDuUisUPJCOxoEYldzGOwu0U87m2RQJLMZgQw8SETBU1UVEVFfLDECZxLB3Avi/24OzMXuFrEYCdmbnAoHoEdyoTjTtWisMfPCdiv03HpYr/UU6Fr/1pwJvG5y72rWdWe3lOZG3uu+9RISkoqpryTVDXnXlKT19ejeuUcX71AFzH+sHabZ4Z2TUesXWGHtas6YO1aZ6zZ0EWi2dTzgmZH3whtyHCRNjJQlBM/XaTbPzM8J2ZKsnaf30PtFk+1ZqUdVs/7EaumVsWqCaWwalwxApkCwclUgYAm/W0lUjpvSjWsngqw6Vt9GT3VtFpEkPzWJ8BZ6MQlxt8DTfm4lPICSxQwUX31ooDpawtxzOLy2uT9ddXnj7TUnTnYVZsUMUQTuzlQs2fZQvWf0zdkLx+9VzFnwJGsyT2vyEc7P5YPs8mW9WuCpT0ANFUhJfRsWZjRgu3PxKl5bhm9TMMSeoYA4EPAie9yMnQ7GbimMvlqzQMtNubMektgcTtme+3KYHH7sswtq/blsNi+PLMv32CxIwCoyljqWhVLu9bA0u61sKxXHSzzqodlfX/A8v6NsHzQb1g+rAXOGmWLs0bbY8WYDlju114tH2F9I2t4q4Oyoc13yYa2FMlH2ojk/nYi+fiOIkWgq0gxuatIEdRdpJjeS6Sc5SlSzuknUs71ESkXDhIpg4eLlMv8RarVE0SqDUEizWahSLNjoUizZ6lIE75apInfKtImhYlyTseLcpLjQ7THIw5rY/+8odoyS6pcOOAtbIeU2UZxx3K556O1AaQzNuShgIkGDRo0aND4+iIyTWoRc11a4tCdrNIpj5TlrjxVVb7+XFOLuW149u/sFkl3FQ4Jt+SukdfA3SQRbL+QOXRjyosxK04+C1p49MnC6Ql/rx8f9TB0eOj9o/13373ksePOg26bb2W6bLyptF93Q9dmxbXXTZdefdNo0eW39eZdwrWEqbjq9PO4/JSzuFTgGWwxPgWbj0nGZnoHUx6AyZ8FTKMpYKKAiQaNgound1UWty7IGiaFPx6wfcHNLXMHnk8bYX9M6dEwAbtUi8ZO5aKwY4lI3MkiGrtZxOoTy73ME/QlsqBclqe+XN4BCpioqIqUeK4l3nUO1z7MAV2LxWLnYszcUDwCO5Zh5odKUbh73Tg8qNVh3dTeKQ/WT02LSdj+MPDKiUzrx3eUZT8+E5lWpKamFpfePftNzr3kJjmXI/q+PBq8TBfqf1S72eNv7epOOZqV9liv1U5vNOtcVZotnpnaPUOfaSPGPdNFT3yqiwp4ods3Mku7tY+OWQarF/6G1TO/IyBpPAuYxpXAqoBSpFxeQBmsmsAooNz/2DvrsKjy/v2DgV3Y7eraunZgK9gKiom1dgKClKSEoCigEiqNlDJ0g3QNDdIpKCAKzAxTJwbj85tzZgZH1H32+X13H9z1c1/XfZ0pFGfmff44L+/3DbiagwGiPQwgOiMAcn0UCZq4IncmnMYCxGAcQAyFsMloIkBudAVNXfxNYAQBE/TPbgiYfjYRnXvN4eH9OQWpI/HCrOkd+WlLsOzYTbyUIEU8wuM85ndfD3E1tuU8UPdnm59JZenvr2RelWtlnFmOMZRmfKIrjBWkZoj1dTKSn3ua/ggwdU0mdQVMXe9/a42eOFgSW9PXKm5Rqmq56DH+77eyh2C938peQhOr/np9vr+qN//vlwK09cQqvr6AJtcP0Pn/Pvq2oYC+Q1qwao/sfZoIGAd/Ifue2o/OBoxjcwHj+Dxu+4nfWhknFzQwTi1paD+7vKH94uqG9svrGpgqsg1M9S0NTI3tDUyt3Q0sXYUGlr5iA8vgYAPLWKmBY3a8gWNxqoF791ID975aA+Kg1YA46jegbqYNqI9lAxpo34BGeTRgcU8bsHi/JjTKrZXre5fNeaDGYxkogvZzy/i/0wTQJtuffP9aRe8NBEwQMEFBQUFBQf1oqqPjPWppWN/yd+iw/Ebu+Ix6zrTEWta8mErm0vAyxprAIrqcd37bHueslmM2yW+umMY2GupEvLZRC331RCW4PuxyYF3aRf+6wlN+tVWHvapfy7tVNm9+XN622rakfZFNEXeOZSFvqln+p/E38shVekO0s8CAa5mgj1oG6KWaAXqopgNJFb5VBf7uqrxO0ET9enVep6nfd3fDnB/REDBB/UR6+YI1ITvyrUKgXe0dW/WiJJ09GW9OLY3j7ZkcAbYODwGb+gUB2V7BYGvPELCLgEw9IsE+McB0UNjJBHuZoKH/HRYll8RnfD/fe4nVeD3DwbZeoUCuF5FwDACbhwSB3eNCwdF5Me/VtqTQLc/l5/rcqnRN8W86XZFFn99cy5Xq7nPc/69YjVTpjtLoZR2pj07iYXq3ca9ToZijQjFqv4WG2cq+R+03A/TRdoA57wW451GA+Z4F+NNzAPc5BTC3g4D/OoDeWQoQk18Boj9aAJhIoNRXkGTS6CdYlUfcJsATcZv/PKI5BCDa0kLINAJwxSxINwnX6el/AzZ9sU5PzN/reSIusnfte/oeqDLubhgADf1XGwKmn1UUCqXnu6LYAeyqvBFYWfokXm7SPCw9Yi0S67UHoTw4j7iZGiG2GvacuxcCWSZHqKzrCjVM1Y2tjNOLuIzDUz/Sd48CNNkhgOhoal3ZG7Qu7/HFirxW8V6mb6WT/gxg+k+g6Q8STJ23l4uBJ5GXdrkvvlqO/7vQ1vYAtHW9PkMn2f6AJkd0Pg0BtO3SgL5zFKDLjwMMxUmAsX8qYByaARhKs0H70Xmg/fgC0P77YtB+ejloPysD2s+vBu0X1gLm5Q2AeWUTYKrIAebVrYB1bSdgackDtt5+wL6hBDg3TwDO7bOAa30ZcO2uAcTFCCA+dwBKeQBQ/wf825aA+0gHsPmvY6rLAcaJuYCuMBq0beoLARMETFBQUFBQUP8clTQjvXIbuP3TX7GHJdWyRj2vYk6ILGufGlBMn+OZ17rELu3tOov4pp2GMQ2HDGIaLxo/b9Lj37e2TGx2MU9oouhHNURfDXmVctbvZY6SV3Wpgltl/ZbHZS1r7Uo4S62LPs29XQh+NcsHE4xywSiit0knCwzSygQDNDJBP00q6KtBBX347n0tE/S6RgU91KlAkoQgYpDpj6yW8efgU3eDnR/FEDBB/UR6XcaWLk6mrY3zbLjmZVbpe/tMXuHVzSltR+bHvN81PgzIDg4CG6REq/JCwE7JcLBXUnAR+vMF6C9X5u3rdPdfLIeGhv4zFszsZ7gUBQ6JpZcU+fd382efWJcp1zO4czXe9lEh4MD0SHBhTQL7xuGsaqfrpWERj+tv5kW3yNcVMqd09/nt/yLif7oj5TFjO6guy3nhxvt5zy4ZYe5Hn6Eu+wpQJ4U2zHE3QB/vBNjjXQBzVgCYi6LATvKAhE/WMgC5NR8gJtMECSYCCJF9SwQoIlbhDQMIuR5vEOBqCq0lhEudMGmkGGAaTpp8juxuEvY36QtgE5f0WIEJ6ER6vNhRYMGqPVG/04SvwZRRV3ddxfedlJS4CRj1p1NQ31nrdwMmpqD/bkPA9LOLOM/XJyX1bS9MGormxE7kxFPmoCEOqxAP851cJ93j3IeaOhxbNXuO9ZVQ9q1TOSx9xXqmyiZm+8kFnxj7fwX0neMATVYa0NYPBG1riPV5vfnuBVqJ3iQxONQqIwaCiNt/2Ln0B8BJ5ku3inulxNeJpm95WRfzH2sT9Uat7PJ3kL8j/9+ymuh8IvqdpEDbhn6AtokATkMBbdtIQNs5FtB2jQf03RMBXX4yoCv8Auh7pgH63umAvm8G37MA48BswDg4FzAOzQOMw78BxpGFgHF8CWg/tRwwz68CzMtrAfPqJsDS3A7YensB2+wY4Ny9CLgP1ADXTh1wbK7wHzsOmPznyfTSwan8v1catG3sA8hOKtHv2xXc/ayGgAkKCgoKCurHVmodu2d8NUsqurK9b1gpY4DfC9oQt+yWETYpb8aaxDZO1o9qmG78vHGxdXLzJueslgPe+bTz3vlt2k5ZLRb8x+yNYxufaIW/Cr4cWJdw8mlN7qEnVVW7nCtaNj0s5a5+UPxxiVURmG9ZCGZaFIBpZvlgsnEeGH8jF4wxzCFX6g3TywGDdbPBAJ0s0Ec7i4QePa5RBV1ORIKJgElk2qmLvweb1CBggoAJ6mdXYwVnYCW1fT416K1SqF3drcdaJeFGh7Iqzq9OYO+fEQW2jAwBG/oFgg09A4GsZBDYIhEKdkuEA0UJccgU9R3I1N0XzaGhof+M93eBSweFs02uxuPflpeIANv5sy8nGQw29AgC64l+tqFBQGFKODi55HmH1u70hnuXC5OfWdbYJ/k0XSxNpq16XcL6x1+IrU9y78uJfTQKjzSegVNUdvJ8z1/HfE4/xb1O5qMeSgzMSQGgD7cC1F6ONEZaFqC2GwB6bzVA7y4DyJ3FAL29QACbLOYCxHwWQMymA8RkquAiNwF1xEAQajABoPzHUOHjJDDSG8P3KMAlwJIQPH32KBI2Ec8JPEq4Tk+4Uq/ztsDkn0MeBUCqMwUlBqE63ZmMmiAGmyZ/2+LwCQIm6H+EIWCCEohINDVSKf0YcY5DuL73R7e76E/mPNadw3HU28h1NT6JuJmacF2MPLi2agnsm8fLWJo7WpgX1mDtJxYCxsGZgLF3CqDvGkf2NBFJnzbZfmQKiIQfq7rAHyFk+m5H05+FTd/rbfqWV37frd97bkUXdwKyHiREa1srBdrW9RP0Om0YyD8O4nsw30MAbQPf64fyj8P4lhZ4I/+92TgC0DaNBDRZvreMBrTtYwB99zhA3zsB0A9MAYwjM0H7yQWg/aIMYF6VBSytnYClIw9Y2jtBO9H9dHYp/zUzALGqsG0r/+/aINX5Hn8zGfazGgImKCgoKCiof54eZbyTvBXf1EMvsqGndvjrXsbPGwfapb0d86yQNjuynCkTU8ncHlzCUPLIbbtol/ZO+3bCm5uG0Q3210LqvS5QasOOelen7vOoLFBwrajc5Vxev92pvGmrY3mz7KOylrW2JfTl94pYC6xeILMtC3m/mhd8nGSWL+hwMswFg/WyQT8CNGkQcIlvlfQu/U1CE4+riGCTyCLgBAETBExQP7MaKzh9a3KYk/MiWzc+d2u44GVa5XD3fH7qtR1pLScWPwc7J4SBDQMCwRpJf7BWIgBskAgC2yRCgbwQMn1OOwgsAk0QMEFD/3N84Ivk0udZJqDTHokIsEMiDMhKBIN1/HPAar7XSQWQ8PnQnGhwZVMyx+x4TpGzbplPmEO9FjXw7a6KdMbshlL20O4+v/1FkqyxVemDB6hOxynK8jx/VUOe3xVvzPtkOua8pwqxk3uDPFjXitiuZ2B2cizs0XY29ngnE3XcSUcf72pBHXe9I48Pt7eiDltoqIMcA7PdwETvrWKj1is56N0lXPT2YgS9tQBDb/3GQy3mf0At5gH05myAmM0EXJNpgHtjCuAaTiChEAmYiBSTDrFGb5jA2kMBV2uw0EMAl39f8JzwNUSvE5GOIp7rfM0wwNWRFktEjf7a+qJVfEIARYKm70CmbwKmqV38LXBE3J8qNARM0P9LQ8AE9bWIVBPlwIGe9cYn+7bZaY9DvG8tQ/3vH0Ap97VQDzN75IF6ENvs91S27t4Spsb2V0zVTe+Yl9bQGaeXsRnHZuOMfVM+0XaNBDS5AaBtbQ9B0miZsKNJrKeprctqur/EfyYR9Ufg6ltQ6ludT52r+SQFXtFDsCaQXBUo9FKhl4hZ9NiynvzX9iQ7odrW9BR0Wsn2Jfut6LtGCDqfDk8H7cfngfaTC0noRPY+HZwG6HvGAdr2YaBNrj9oW/8Z4kHABAETFBQUFBTUv04EdAoupg9KrGGPTX3JnhFbyVzi94K+3iWrdceD1LcHLeIbz+hFvr6qElhncOppjeUxn2q7E741zucotU+Ug+qeqYW+ClINro86T3mZesS7qkDBraJ6i2NZ8zr7UtayB8UdC6yKwIzbhYCATQRo6q+TJViZR0Cky6lA4lKq4Hg5TWDldIFVxFNNQosnmbob7PwohoAJ6idSYwWnd00Oc3hhTNvsJK+mLQFWtVqPNEv8jJWyqy9vSHpPpJhkhwaDVZIUsFLCD6yS8AebJILADolQoCARTl6cFq3TOsz3IWGiaT8ETNDQ/wjvF0ssfZ5jAjhFgr0SEWCXRBjYLBFMAuaVEhTS6/sGgt0TwsHpFfEfdRWpb+8rv4jzMa+6FevasD8n9N3CKipjTEMpu193n9/+SrVSLg/kBKjP5QVr7MED1dRw3zOWmPMeR9Re1hux3RiIPdwag7oqJmPev6djzy6mYv7KCVjg1Wj+ayPwILUoLEA1DqNcTsGeXcjEfU7m4U+OFeHuh0oxl33lmNPeasxxdx36cPsb1F6OgT1Yj2FEAspqBUAsFwHEYh5ATGcIQA6ROCKAEAGHCJBEgCPNgYCr0V/Y6cQ/ag4gH0M0BwmO1/j3+c8hRNeTeh/A4R85xOs0Bgpgk86wzhV8X1h3hCA1RcKmscIL8BMFF+GNuvgLwCSESyZdbPwtiDT1G/6jVBMET9B/lSFggvpjEaCJ62s+mhvssBAJfrgd8bE8w32kc51rddGSc/vMY76fsi3PRrJvnUllGysVMbW2N7ZfXMVhHJ0JyJ4moiNolQAstSwUerEYZBL1BonDgbXfuN/1sf/Wa7/jrmDqe6CpK2ASX8En6nUSAbTFArhBeqHQC77hRcLXijqhhCvuaOt7CXqftg4F9J0j+e/jGECXHwtou0cD+o4R/MeHCODSRiJB1VMAmL4Fzbob8vyAgInroHUXi/Q8gj5/ure7ZwsKCgoKCgrqv1BSDbtPWh178PMq5ihKEX2Sa1brdNvUt/NuxTct1Y14veZKwEvZ331rdh33qVG86P/ykF7U66PWyc1nnbJaVJyy3undT2m2No5t8FALrYs4Q6nNPOxVVb3brbJFzrEMl7ErAQusi8A08wIwykgAmYh1eSQ8Ek8skcc/08n0A4CdH8UQMEH9RGoo5/SozmH2LYhpG5Hi82ZmmG39fg/DCiur8wVpOvIZbb8vjvu0c2wYWCsVQAImwkSKYYtEMNgpEUqmG4iL1CLIdEisk2n/D3DxHBoa+vveL/EZMH05vwK4tFsiDGyTCAEbJQLBKgkKWEFAZkl/sHloMDg0KwZc3ZLSbnEyr8j5epl7gHXthXiPpmU5oS2jKzMYA16XsHt19/ntrxaLoi7NC9CYhVGurkGenNiFPtp9kGsrdwKx33oFcz1oiPtdvotHGdt2JFjZ8FLtzXlpDw14aY91eGmP9Hkp9mYdCTZWHXGWDrwoEzdeuIEPL/Q6BQ/SDCIgFOZ3OQ7zOUvFPY+VYS77G3FHeSbmsOU9uW7PZjVA7ywBqPk8gJpMB+iNKQAlLoYTiSYhbOJ29jkNJm+T8IkEUIMFoOla/07AxCWOIsBE/Bzx8+JgSWe42GMjPq/dI5NMxIX4iV/2Nhl2WZ9nPFmYYpry9bq8byaYIFCC7g5DwAT1n1VmbCzFodiOxCkOvyKelks5Dtob2dZXdnHsrh5CnPXPc70trqM+ltZc9xtPOfeupLEMDta2X17DZhyZRUKmtk39Qesqyc8gZtkfwKXvAaa/Eip9DzL9CdDUKu6usGmZGGzqCpzEvUjs9vdSXUTv09pegLa+D6BtJDqf+vOPhPuCtg19BMklAi6tlfzy9+5usPOjeKUA7H0JmDZBwAQFBQUFBfVPVmINq0dkeXtv3wJaH0dqS3+b5OaBZs8bh2iGvpI+61c7QsmravRR7+qxKkF14+8kvZn0tIA2I76auSixlrUpvIyh5J7TonY3uem2QXSDh2pIXdQpv9rsg55VNducy1vXOZQhS2yK8VmWhfhks3zemBu5vOH6OR1D9bLfD76e/X7g9awPA3SyPvL9iQBQxDq9PlqZoDffPTX51qACSQ1xsCKETV/BJzEI1dXdDYMgYIKC+j+rMqu9R15ka+8krzdDw+3qV/qYVik/VCv2Mjuak6+yKeWd0uwYfPuI0E9E78pqSX+wRsKfvOAsJxEMtkuEkBeh9wpB0wGxNXn7yfuii9if3d0X1aGhf0Z3nUORu86sIn+WFfgzvYM/2wRI3sSf9XX8mV8tQQFrewaAzUNCPu2bEsk7L5NIMzyQWXxf+UXwkxuVRsH367bHuzdOzAp+J1WeSu/xqogl2d3ntr9aScYber3zPD6ARTkjzXVWGo0+2jW+/d6GKVyHPQtx37Ob0RjTgx1U1xO8wsAjvPKoPXh5jNz78th1WFm0LF4StouXTznUket9uiPDWfV9qoP2+6T7BliilQkeb3kbj735gBem744HqYXgvudTeE+OF2Gu++rRx7tbsIfbmJi9HII92IBj99bgmLUMjlkuJtbp8dCbczpQ0+kdiMnUDsR4SgdyY/J70kaTPyCGkz4gRhM+IgZjPyK6Iz8hOsM/IdrDPn0Bj0SdTPpEJ9MoYY/TiC9h0/WRpBFdYnXeWIHJ/qYxwmOXHifDrp4gZmEC6nvuTEVN/i9hAQRS0P+tIWCC+nNKMjbu1exo3J/hqDOEbXV+BNf87Gj+7UkcX5u5WJTnejTBVwmLdL2OeFs4cWxUYtn6+0qYyhveMU78xqUfmMqj7RzV0bZ58Ie2TX0/koCEWAm37huQRBzsdF379r8EFP9tB9R/2fv0VddT18fEO6pWEQmlHgKv6SGAT2tE/gFgzo9oEWCaJwB4bdtGt7Vf3iRYkRfx5Bga47uvu2cKCgoKCgoK6m9WVHl7j4Im7sCSt8h4aj17UUgJfatT1rvjd5LeaOhHv759JbjO6fjTGn8F98rYLY7laRsflVHXPyzLXO9Qms133hrbkqIV94vLF1kX1c6/++L1bMvCdzNuFTKmmRdwJ5nlvx9zIxdIG+SAQXrZoK92JuilKYQqBFASJZ6UxfqblLskolTTv52G+jeloCBggvpJlfikqWeYbf1UX7PqXU6apbrW5wufGO7PSlHekFJ9bP7zVoWJEYjc4CCwtpc/mWaQIS44SwSAjRJBYKtECNgpEUYmmsQvWh/qXL8V1dnzIrqQDYETNPTf564QSbxnqatFYGm3RDiZWJLjzzQx28ScE14jSQEb+weCnaPC8MMzYxgXViXWXZenZlmeyX/2SKPkprdp1ZHgey8XPndtHNTd57HuULPj7v5Y4JXJHYnWCzpeBC/vqEldzKvPm4XW5kzk1ueMQWuyJuAvU6Z3lMYseF8Ysgov8JPDs7138TLdFXnpzoc60h4d70i+fw5/fvsaFm5gigeo2/F8znji7krBmOu+GMx5XxLmejAd81CiYk9OZGKeJ7L5t3Nxl30FqKN8IfpwWxFmL1eM2W0qxR5sKMcerK9GH6ytQ++tfo1Yr2xC7ix7i1gubEFu/daGWMxjcM1msxCzWQhiOoOHmEz7KFhdNwVwjSYCrsE4AWwiUkskWBJCJm1pQW8TYa2hn9fzkUkpQZ9TZ/KJWLmnM1SQjiL6ob7oexolSF6RoGqM0KLeJxGwEsIqcdj0Rd+TCBCIJaO+1ff0lb/zGpii+kkNARPU/001trZ9kNTAsQg1ahGeEiiPBtmrch/r32XfueTFMj0WzdJTzGi/ti2fcXltKePU4pd0pVnvaPsnc+i7Rn2ibRsK2mT7gbb1PQQgZUWXBJAw7dQJXESwSRwk/BXr87rb3+uC+haMEn8fYGLp29+FtYL3iQRMcwWJsTa50W3tFzamce5r38PCXU+g0T4Hunt2oKCgoKCgoP5Hqm7DehU0cUdEVzB+9chtWXovtVnuRmzDPtWQ+pPHn9YoK7hXau9wrjBUcKs0PuJdY3oxoM7iWmi9lUZovYNyUJ376We1AUre1dGKHpUZO10qiuUel9evsSulLbIuwmcK+5uI1XqDdbOBlFamAKyoCuGSqMfpklif05VUIWxJE4NNXUATAZmuZXwJazS+4e4GSBAwQUF9V6H364b4mFbPddEu2+5wtfiS9YVCK7NjuYHa8hnZ51cnvt73ayQqOyQIrJD0A4sknpJeJuEH1kgEgE0SwWQ3EwGZiOQSAZcOCztdDndZn3dAuIYLQiZo6L/en8FS5Bdg6ZDYPIp3LSkK1+ERXUvrhF1Li/mzvVDClz/fz8C6vgFg94SwDycXx73T2J5WZHIkO9LqQsFDB/ViDefrZXu9TKqWBtm8HBPr0tCju89h3aUaW5U+rBgbaW5Z5BhOTepIek3W4LKyMimiMD4vL6/3u6LYAeyK+OHoi/DxeHHgVF6e7yxerue8jmyvBUi661I0xWEV9txalhdppIAFqh/Bnp47h7ofuoq67dfGnhzRw55dMMKCrxvznluY8BJtzHlxd+90xNy8h4cb2uGhOg/xIM3HeKCaM8//6hMe5fIz/OmFEMz7dDTmeSIR81BKw9wOZOLOe/Nwp91F2MPtlZjDlnrEdsNb5N4qFnpnKQ+1XAgQizkAMZsBEJNp5AV4ruEEwNUfK4BNBDgi+po0BwGuWKcTuXpPYwD/8YGC54jbRBcUsYpPrTfgXuVbTUpwX2MgQEg4NRwgOiP4Hv4ZWhEgSpSsIv4+Ih1lMF4s9dRlHZ943xPZ8TTts78CSVPFOqFEr/sGbIKA6SczBExQ/3dRKJSe7LzwEbyUoNmc4EcbOO43D3Ae6V5gP9bV5DgbmHKd9K05ttec2bdPB7P0FTOYV2VfMs4s5jAOTwd0+dGARvQJEYBghXBtnKizaKHgftsyCbHVcd8BCt0Nmv7sOr7v/c7fA0wrulg82QQB09fv/zqhRYBpDt/Ed0l2NI1xbmM6x+baA26Y60k02vNwd88NFBQUFBQU1P9QuQ2c3hFljIFuOS0jrJPfTDCMeT3tcnDd7MNe1Qt2uFQs3e5csfKwd43MtdBXa+6lNMt65bXufFbYduhJbus5u7S32jfjGi30ol47Xg2p9z9PeZlwzKemcI9bVYPc43KmjG0pb/7dF2DqzQIw+kYuGKSbTa7NI0GRihAkXRHzF2mmjM9wqes6va6A6Z9oCJigfmIFW7/s5WVUNcxZq3Syo2bJMkft0oOPtUv076u+cDc+mp1yaUPS673TIvB1gwPAYoln4DcJX7BQDDIRF6iJC9WKX0AmAWj6vIYLJpigof9uf28V3mfIRNwnXhsB5IVdS+v5M0z0LIlmewHfMn0pYPu40E8nl8W16u7LyLO5UkBxvF5i7mJQdspFr2y9s27Zr0+MKkf636np293nr+5WUpJxrzIKRSovz7E3AZa+9Xx9knvfd0WeA+hZ3oPbk9yHsqgu0uwkxxHc+Puj0SjLCViYwS845epMjufxeYjLvkWIq/xS9MmJ5Wig9ko02V7mfWHg6vcV0RveV8Rt5RWHKfAKKPt5uT6HeTkeRzsyXU/i6Y4X8GQHdV7iPUPe81sWHTGm9/AIo4e8cD1XXrCmJx6o5o9TroTjvucSMa/jObj7gQrUUb4Je7SNidpt7EDvrQGo9Uqy8wm59RtAbs4GiMmv5IV3rt4YwVo9AhIRvU4EMNIcTPY8EY91AiiNfgKodLUn4KrwrdpTAJrU+wtery1NwiUy+UT+zGDBz2kJE08EZNIbJVjBZyBcv6c/XmARdDKa+DnN1DWp9D1I9GdfBwHTT2IImKD+GuU5OvZmxFGGIE/txrFcjH/lupvORwLslhLr8/D4Z7uw554nMf/7eoizoSPH6sJzlv7+mnbljUj7yQWAoTgB0LYOFqzLW9mlt4hYbybe1/SjQ5X/H7gkctck07dSTN25NvBHt/j7ulIAKVtmC3uYNo6mMc5uzODYXLNDQl1OEz1M3T0zUFBQUFBQUN0gx8y3kpaJTT10o171Oh9Q20vRo7L3Zscyqa1O5X1OPK3tY/q8qT+lkDYso549rqCRO5Naz14eUcbY5pnbquSQ/lbldmKTyY2YRnvtiFd+ykH1iWf8XhYc8aqp3u1S0bTBobR1iU0xbebtQsYE0zzmSMMczjDdLGSodiY+RCvz/SBN6qcBGlTQ71oGkFKngt7qGaCnGhX04N+WVBMDTKTThc74co3e1a6vE0Ep6o/Z6QQBE9RPLg/9CklHjZKeTtqlQz1uVMz1saiS9zKv1HyoU+J841hWyrl1CfXyM8LZ60YE4ssG+H1c3OcZWNrLD6yUpIANEgHkurxdZJIpXNjNJOhnIqDTXtKC24rC5xR/gIvx0ND/Jit2HiPE5i5CeP/zc8SM7ubPKtGlRnQtET1Ly3o+A0uk/MCS/n5AZoh/x7ZJodxjS2Pfae9Nz7uvVvjM07zCxM+qWsn3dtVy/vlhrJNOaW83/fKfNrn0f5SkyASQIkyhHOhJdD3lOS7pXWY8V4pwje32PjVRKnzb9mnOC+/PeJk3hPOudhTWXDYJb8iYxquizuLVJM7tqE5a2FEet/J9Ubgsr/CZAi/bQ6mD6nwGT3t4BU9+cI2XYHOdF3vLmBdtcqcjQt+BF6rjhQeqh2GUKyn4s/OFmNfvNZjH4SbMdV8L5ijfgjpsa0VtN7Yh91bTkDtLGFzz+e1c0xksrvFUNmo0iYMaTOTyjwhqOAlFjCZjiNEkHqI/vgPRG/ke0R72AdEa+BFRH/CJe60/IN0Jl0YChOh0IhJMJJgaLEhAaQkhE7Fi7/pw4Uq9kQLrjPz8c8Q6PVH/EwGfDLv0PxlMELhr8umLFJRYF9QXK/imfOnvwonvASgIrP45hoAJ6q8VcQ4n+pryHM/3LqMYS9GzogajRVkTOgozFuJp4bvxMCcVxNPclmunEcW5+XspS2f3W+bFVW2MI7MZNIVx7LYt0mjb+gHv21b3A20yUqB1ZS/QtrLHtzuOxN0VvPwb4Mu3Op/+Df+uv+q9+V4vFvF9INYrzpUALdMFKaa2ddIMxqm1WSwrdQck2PkMFuVxtLtnBQoKCgoKCuoH1ys63q+yBR2VXseaHlxMX+KR0yJrl/52n1Vy85k7iU3atxLe3LkZ3+RkHNvoqx3+KvRyQF3sMZ+apD1ulelyj8tyV9uWlCy3KapefKew4bdbBW2zzfPZv5rmdUy6kQvGGuSAEXrZYOj1bDBQJwv008oEUppU0IOEMgRIIvqZhCv0lNM/p6CU0z/7j7qc1MWTUBAwQUH9CPI0qRxCsaqZE2hbu8PXqlr1oW6x/Y2T2dGXdyQVH14e07hjZhh74/igT2ulA8Dqfv5gXY8A8kL1ZrKXKZhMRRAXr4nVeTuER6KriUg5yUuEkxe493Re/BZdIBelnATu7ov10NA/ogXJJPE5EcwKMUd7hfBIngRIYeTMCWaQgEkCoESYmFFiVmX5M7teMgCskfIHawb7g/VjgsCWaaHo3gVR785uTKjUOZSRek+98ImXZaVe8MPaAyEOL5f4WVWP8bhRAcFSN4q4mEms4WtuzuvfVpk+iPk6bRi3Lms0Vhn7C68sak5HcfCS97l+q7Esn4041W0rnvZoFy/x/j5e4t0jHQl3zuJxd9R5cZbGHXF37+Hxli682JvP8AijEDzsehQefC0Goyg/x55eSMC8fk9B3Q5lII57cpBHO/MRB7kizHZjKfZgfQX2YF0Vdm/tS9RmzSvEZlUTYrXiHWK5mIaYz2tHTGewUOOpXBJAGUzsIC7eoyKIYziZTCRx9UYDrq6w6+m6tHBNnsAI0dukI+h6IlNOGoMFMIpcpzes83WCzieBBT8zQgCiiFV7uqM7TfY/iYCVqAuKhFTfg1JdOqDEIdI3O57+ZOfTn3G3w5efwRAwQf1vxCwuHsbLS5qFJfrLYmGPzyBPrcy4biYe3Ida4RzLM/Esvb3UdtVNRe2nlr5kHJ7dRlOYgtK2jwU0OWlA2zgQtK2TAm2rJQXJlOVf9zSRjxEr9ojnZST+XZDp3wTN/n/cNe0lnvCSEX7mK7p8L36TAC0zJMC7qfzjLAIwDWG2n1mTzbJRd8BCnWCCCQoKCgoKCurPqboV7U2tZw0OLqaNcs9umWKX/nbu/dTmZQ7pbze5ZLUoeuW1nfTJb7vintOqzX/M+HZC022D6AZbtdB61wv+LyknfWsilZ5UpSq6VLzY4VhWK+tQ+m7V/WLOYqui9/NuF4LpN/PBJJM8MMYoF0jrZ4OB17OAlBYBmoQpJlUxuHS5i6+kf71q75vr9iBggoL6EeRuVCH57G7NsBCHl9NDHtdt9HtQfdbJtPS2pXr+s+snqGkXdia+VFoRy5SfGf5xy5gQIDswCGzsFQg2SgSQaSaRN0oEgk38o6xEELlGb5sQNu3qBE0RwrRTJICACRr6P/tbgEkElxSEnUrEjBGzRswcMXsE/N1Aust89uDPZz/+bA4PBjt/CQP7F0Wjp2Tjm9QPpuXdvJwb6mBQbO9jXaUW6lS3O9K1/jf++WD00zvVUt19foL6SpLEej6i74lZHDGMUxQ0CqVSxmMZPpPxDMdpeJr9DF681ZyOxNsL0ASb5Via3Qac6raLV/DscEcB5UxHwTOV91lemu/TXXTfpz8y5CXbmvDirS06nt+ywqOMbbEQHScsSMMDC1D24T27RMF9zwfjPmfDce/TsZjX70nYk6PpmNvhXNRZsQhz3FWBPdxajdnK1qH31zeiNqtbUWsZDnZ32SfUcglAby0EiPk8gJjNBIjprwAx+QVwb0wGXKOJgGs4TtDBRKacpAGiOQRwNYjup4Fkj5Mg6USApiGC25oDgCglRfRBCdb2DRWs4COAVWfXkzAtJfxZ8s8WJaL0xgr6pvTHkf6ciBKDTiRk+g9r+b7X//TfQqZuhy8/gyFggvqfSbI9KWkolvR0ChrzZDke5bkbi3I/h4Y56SB+NuaIq5E9556yL8fk2HOmlkJh+6UNDfRTy9iMw7M+0hUmAtq24YC2iehqkiRhAplQEVuj1wmaRJAJrpH793q1xBcdVSRYWib8DiwSdnfNE6SX3k3jH+dK8L87Q9uZF9ZROXbq97FI9+No7NP93T0QUFBQUFBQUP8QJdUwezwraOv9KONtX+vkNwNtUpqHOmW+G0N5QZsaW9k+P/Ula1lKLWtdbEX79sBi2j7PvNYTj6jvlK2Tm/VvxjVZ6kW+dlQPrqNc9H8Ze+ppTbaSZ1XVXrfKph1O5YyNDqXIygfFHQusXnyccavg4yTTvE+jjHLAUL0s0E87E/TWoIIeahlAUjUdSBJASbzLCQImKKh/nLzNq3oG2dYOiHB9NTHK89XKENe6w0/tq/Ucb5Y631bLi9dWyqi4IJfYqrQwBt8zOfzTNukQsKlfIFjb059cubVKwg/I8L2K7GnyJ3teNglBE5Gi2PkFZCISGKI0xueL5iLvhYb+yS2aBQFoEp+TKPJ5Ai7t4s8TAZe28GeMmLX1EoHk7BHzKNM5jxSwhlhrKRUAtgwJBrvHhYGDs6Pen14T366+N63O9EIO1c6w+KnXvUrzIJfas/zZl431ej0j0rV+WMD92t7dfV6C+kNJEsXzBGwi1jQRvU+NFJt+zeHG/VspxgPbQrUHMSNuDeMmOYzBCp9O4VXHze6ozljYUZ+54n1V8tr3lTEb35dEbsYLQ3bwCgP28HKeHurIfPI7nu50EU9xuMpLfKDNi7My4D23NOXFWtzqiDSxwSNuOOBhui68EC1vPOBqAE65HIb5XYjGnp6Nx7zPpPK8fs/D3ZWqMed9LdhjeRRz2P4BtZP7gD5Y/wG9v+YDar3iI3JnyUfk9oKPiMWcT4jZDAEEIC76EwkknRGAqy1KOA3/nHjSJpJN/QFXvQ9phPC1z5DpM1gaIoBTJIjqx789gOyOQojUE7GK7zqRdvpsAXQSreITAifRaj0CSNyY/G0bTxFzV3D0rccgYIKACepnEHFOrnd378uOfzIcSwqews2IXIjlRK3nZYQpYLHep1F/Wx2ux817HActCvv2uTSW4YEKpvqWFsa55QhDaeZH+p7xgLZlCGhbLwXaZHqA1uWSXyeZxAHTv21l3s/qb63C+x5gIqEj/3uxoAdomcv3vJ7853sC2u5xrUz1rYlcJwMLXozvPjwlYEd3zwMUFBQUFBTUP1whJYzeGfXsgcXNiHRJMzI2v4EzNbWONTemsn15UAld1iuvbe/jzJYTVknNKqbPGw31o15b6US8dtUIexV8NaQ+8UpgXe7pZzXlh7yq6na7VjRtelTasvJBMWOB1Qv2zFsF2BSzvPfjjISr9LQzwcBrVNBHLQP0Vs0APVXSQU/+sQfhqwSAogLJrl1NItD0vd4m0tTP/js6nCBggoL6piLdXvWJ82sYmxDQuCSW0rAn7Emdmvf9Slt7veKQm+dysjXk0+rPysTTD86OwnaODwWbhgWCNQP8gUwfP7C81zOwvMdTsFJ4YXsdmWoSpZlEa/PCyYvje7pcUN9DPiawAjT0T27RLIj6zD7PSSSQlxDApe38edpC9ioF8WeN6FbyJ2dvueQzsmNpRW/+HPajgA2DAsC20SFAcVpEx+9LnrNUtyQ3GR3PKrLRKIxxv13uGuj80iDm2esjCUGNaxMDG6fG+TYM6u7zENRfK1Hiieh1YjfnjeDWlYxGKtPHYXUZk/GahGkkfCqNWdBRFLkCK/TfgOc924Jne+/iZXoq8jJcDnekOR3vSHE4gyfcu4TH3VXjxZjr8CKMjbAIQ3M88oZlR4zxvY4Ys4e8aDNPPNIgnBesmYFTlMsw33O1mOfvdeiTo69Qj8OvUbcDDYizwhvk8Y53iL1sG3JvLRO9u5SLWvyGoWazOxCT6R+QG9M+IibTAGkSwkwiARC5Ho/ocNIQSzBpDxN0PJGWFkCmTsDUV/BazUH81w0FCLmOjwBWIwTWEfY/kR1QI4Tr9EZ/7nwSpZtEnU9kykloo4linvR9fw9Q3RDCqf8vYAJ7niBggvonKM/RsTfRz4SUp47Fi9JnohnRMniC324s3OUsEmBrhHhZPOY46gazrS5lsAwPVDKvyr1lnF3KZByajtPlx32ibR0B2jYMBkRXU6tMb9C6osdnuCRak7dSDETISHzdZQSh04/l7/UqiXq2Vn7DK0RQsYewr6sP/2cG8M3/bsgMA21rRwDa9jGA8fuCRpaJUhjX9/Z1PD1oM5YVvaa7ZwAKCgoKCgrqX6SaVqxn6VukX3YDZ2hyLWtMVEX7L/4v6HPdclqXPUh9u+FWQtNOs7jGQxYJTRfuJDXr2qQ037FOaXa8Fd/0VC+qIeJqcF3CGb9a6mGvqiJ5t4qaLY/LmtbZldCX2RRhv1kWghlm+WCSUS4YrZcDpHWywBDtLDBIKwsM5HuAViboq5EFpDQyQa9rVNBDBHXUxGGTWF+TasaXvvqt1FPGXwObvgGYemtmghm3Cl4d8qwKupPwRjushCFLrWNPyYWACeonUzylUSol7M3otKjmOakRb+TiKA2ngp1fGj2xrHC6d60w2vAo9cWVrUlNx5fHIntmhYOtk4LBhlEBYPUQCpDp5wdkpPzAqp4UsFbSn1zVJScRDLaS6/LCvoBMXzq807u7WB4a+l/urt95hS/8eU4IuEQ8T8wRAW03iwCTJH/+eviDlb39wMo+/Bkc6AfWDvcHcuODwa5pYeDwouiO8xsSWrX3pVfcvpSX4mxc6u3vUHMrxvfVFf6s706Pbl7Mn/eJKSFNA7r7/AP194ssqU9K6lVTE9WnOS+8P70majC7In44tyxyDFYQORnPC57GywuYxct9Nq8jx2dhR5bHko5055VYsu1aLN56Ix5nvhWPNNvFizXbw4u7s4+X5qDUkeV2qiPHU5WX6W7ckfrIjpdo5Y1HmwXiETdC8XC9CDxMJwoP1nqOBVxNwp5dzMB9ThJppzLMaU8d+mhHE2or14rcX89A7q1hoTZruKjNKhy1Wv4RvbMYoBZzBKvnCEBAACC+UYPxADWcyPckATAwEDxHwiMy0TSEBE6CFXnDO3uZOrugdET9T9IC+ESCJlFvkyjlNBpwidtfJJ3GikGosWTySbRyj0s+9p3Ve50r+ETpqElfruP7s/7e2r7O9X1/8Fy3wx4ImKB+PhGpprb09EFIwfNxPGr4LDSZIoMkPduFPfc6i0W46qF+1vYcR91A9p0L6WzDA2Ustc3N7edWcBhH5n2iK04Dgp6mYaBtwwCyp6l1TS/QuroHmWDq7OYRtwg+QdD0Y/gPoFInLBR9dsKeLQIqkcCJ/zm3rekJ2tZK8T///qBt02BA2zwC0LePB/RdvwC6wgzAODAfME4vRZg6u4u59hpuBMDsyE9cwnuROLe7v/tQUFBQUFBQ/0JRX7F7xlczpcLKGAOeFtCGOma2jLib9GacWVzj5JtxjTOtU5qXOGW1yPkU0g5QiuhnfQvaNByzWkytk9/YmDxvdNaOeEVRCaqLPutXm37Eq7poj1tl/bbH5S3r7Uq5K2yKPy648wLMsSgAv94sAL+Y5oOJxnlg3I08MMogF0jr5YAhutmgv04W6KOVRSaFJK+JQJMQLql09R+BJgiYoKD+biUFN0llRL8dkpPwblJOfMuSjMjmXbG+ry8+fVBt6aBb5Gd6LjtD40Bq7fnNCcxjq2LeKy6IADumhQC5sUFgk3Qg2DgwEGzqGwg2SwWDrb1CwXZJQYJpl/CCusIfuOvF9z96LTT0v8F/9jsvep5cjycZBrb1DAVbpEKAbN8gsLF/INgwJBDIjgwkoa/8nHBweHn0h9Mb4ziqCsmNBr9T82yuFYQ/uV3uEOFer5Ea8uZATty71XlJLdOz4t4NT4140y8xoFGyu889UP97CYCTca+aKAFwak2iDKRneQ9uT3IfyqK6SLOTHEdwYh+N4ibdGYMm3ByPhtyciAUbT8EjjKfiCXem8ajuszoKgxe+r4pb86EifldHUcTveN6zqzyqiy4v3cmIl2pvwrc5L/meJf787gM8xsyJF2HghQdrBGN+ynGYz5l0/MmJPMztSDHmdqgCczlQgzrvfYU+3vUWfbSVjtltQtB75Io9gN5dCtA7Xxq5vRggtxYAxHwuQExnCGCUEC6gpCcJLAIMBCgiQBIBlEQppk7AJEg0iVJOonV9XwCoLyyEVoT1RpIwSuAxX/Q9kZ1PnWv4iBTUBCH4mPyfDQETBExQ/3RJEudXRhxlCCcjaBSeFjG1Iyt2CZ4dvRVL9j+FhToaIh43HTm210LY5qcyWXqKVUy1rS2MC6tQxvEFgHFoOqDvnQhoO0eCNmKFHtHVtF4KtK6S/Awoln8GFK3iiSYImH4swCSWVvoCLC0TA0z8z5WAiUQnF23LYEDbMQLQ5ccBuuJkwDg4A7QfnQ/aTy4F7WdXg3blzVym7t5attWlKMTnjhmeFLQLK8r+BaksGNfdX3ooKCgoKCion0C2aW8lb8Y19TCIbuhpEtsgdS+1eYhXftuEiIr2ufE1LJnnVcytQSWMg09yW087ZLxVu5vUdIP/OhudiFcuKkF1fmf8amOOedekHXxS9WKve2XNbpeKpu2O5S2yj8roa+xKmcvvlXAXWRdhcyxfvJ9uXvBpslk+GGucB4Yb5IJButmgr1YW6HEtQwCXlMX6m5RF/iPQBAETFNT/SnlJLVLFGbThRem0GVkx79ZHe78+4WNTaWRvUOR6Wy038sbZzBztI2nVyvJJb0+te846uCCKt3da+Kfd48PArpFhQF46DCgMjgB7BvDdJxLslYoEir2F7hUh5sjveh809L/c3//+i82IaG74M7SXP0t7+kcAhUERQH5YONg9ku8x/HmbEg72z458f2xFDPfCtsRWjUNpLw1OZxaaq+TE39Mp9Ha7VWYZ4vLyclrYm+2FKa3zSzNpY4vS2/pnPn8HwRLUtyQpbgJEEaZQDvQUWQCmbPsQKShufc4YvLFwesfL9KVYWdQmvDBwJy+fspeX+3Q/L9fncEeu5/GODNdzeNojVV6CzXXecwtzPMLIFg/VduEFqnnjFGUK/uxSMO57LgLzOvkce3IsBXuilIW7KxVi7ocrMHell5j7oQbM9WAz5nLgHeas2Io5KtCRh7vaEfutLNR2Exu9v56DWq/motYrEPTuMgy1XMRDLRd+QG/NB6j5bED2PhHr9wj4QKSJSOA0VpBQIoGTNLlSj6s1GHA1BwlM9DhpDRGs2iPW8nV6KPk4+VriSKamhgl6owhARYInsc6nr9bw/UnIBAETBExQ/xoR51BibSmzOG0YVpg5pSMvcQUvOXAvGvxYBfE0t+Daa7px754PY5scS2fpK5YyNbY1MlXW0xkXVnAYx+fy6AemfKLtHg3aNg8CrWt7CQCTqJ9nqRik6AqZuhu0/KzuCpfEV9+JPrclQi8VfnZre/M/38GALj8a8D9vwDg6+wPj1GKMcXY5m3lJhsa8sv4tU1W2kXlt+0uWwf4CtuXZSMTZyBYJdzmLUmOWs8qo0m2V6XDdMRQUFBQUFFT36GkhrXdcNXNIxivOuPQ69vSYSuZCygvaKrec1s326W8V7ya9OXEjtuGSZtgrrcuBdSYX/F/euRRY91AluN5TLfRVsFpIfczloLrUU89q8w55VpfLu1W+2vy4vGWtfSln+f3iD79ZFYHptwrBBNN8MNwgB/TVzgSSRCJJpStgSv/PgEmUZPrLAFMamawSA0xaYSWMTdQ69mQImKB+dpXnMCTLcxmDCpLaJicENK4IeFy71+Nu+WVni1Ijx5vF9x1uFHlZaebHGp3KLFTbndJ0fk088vui5+DY7Bhw9Fe+J8eCI+NiwJFRsUBpeAxQGsb3kGhweLDQg6KB0uCY7/oINPS/3N/9/hOzQc6H0EOjwRFp/s+M5M/UWP5sTYwFx6bxPTMWnJgfC06viO+4sjmpVfdwRsUt1dxkO8MiP0fzEgfn26U33e6UqT21qzoS7f1qQ3bs2xllWXTpqnxGr+4+v0D9e0RcOG0tKxvIrcsajVUkTcGLomfyiiLmdRQELeh4EbCo4wVlOZbnuwbPdJPD0x7t4iXdP4TFWJzCI4wu4WG6amiQthbmr66H+V02xJ6eN8V9ztzGfc9Z4/4q9niIthMvytiDF2Pmy4s2DcQjDCPwEJ04PEAtFaNczsJ9zxfgPqeLMM/jJZiHUjnmerAKc9lbjzrubEYfbmUQKSjs/poPqNVyQK7du/0bQM3nAtRsJkBNpgoABJFsItJKBCgi+p6uDRD0OWnwjxqDACICTaT5t/mvQTT6Czuf+pOdTxwSSAnW85Hpp86OKKFJ8ESAJmLdnvgavUliq/TEu5y6rNGDgAkCJqh/jeqTkvoSHU08auR8LNpDluNjc5jjbHCFc/+qAdvqshX77nk3tuXZcPbtUxlsU6VSls7OZsal1Qjj2BxAUxgH2mQHgNbVkgKo9J8AE4RM/3uwJDqKdy2JANPyLwFTy2Lh/dU9AU1uEKDvmQDaj88F7ZdWvWde29rO0tv7immw9wVTb08y67p8KEtn11OWnoI7y/iIHee+ihHiaXGGE+W5CcuO/aW+PqkvsQa3u7/fUFBQUFBQUD+x4mtYktTXnD4Z9ezBsVXMkQFFtPHuua1THTLezrmb9GaRUUzDSvXQ+vWXA+u2KAfV7daJfH3QPKHptG36W7VH1HdG/KO1RcIbt+uRDUHKQfWJp57VFhzyrHq527WyTe5R+XsZ2xIw36oITDUvAKMMc8DA61lASpMKeqpnAMmvTP3K3+xg+qM00/fW6Yn6nIgE1ZVUEjD15P8e02/lvzroWRVkmdAEARMUVBflJ7YOiKM0jg14XDvbx7Zqpd+j6s2h7rV7wz1fngt0rDF1MSv1unMlL13/IPXVta2pHJW1yeDyyiRwaXESuDA3EZydkQDO/JIATk+MB6fGx4GTY5+Dk2MEPjUmDpwaK/DpsfFf+Aw09L/cXb/z5CyMEfm5wOP4tyfGgbO/xINz0xPA+TkJ4OKCJHB5eRJQXp0M1GRTeDoKGe/MTuUUOugVhTy1q7IO96xTifCuPxjoWrP9qUPVGj+H6t8iveonZ8U0DynLovfs7nMK1L9TZWUUqXdFsQMYeZQhrDKKNDvPdwSnKGgUN4cyBs3ynoBlO/+Cp9nP4MXZzEdiby1Bw4xXYuE6a7AgrfUYRW0T7ndJDvc5tRXxOrMTp1yS54UaKPJSHhzk5Xgd7SgION2RH3DlfbaXDi/d0bQj+YE1/vzOY16smQcv6oYPL0KfgofqBOHBGuFYgGo89vR8Fu71exnmfvA15qxAwxy2oZjdpk/Yg3UAtZERrNy7vQCg5nMAYvprJ2jiEmvySEA0TNjXJFyTd124Vo+4rzOUBE0kjNIYKDgS90Vw6XoXuCQCTmSyieh1EvU1Tfja4uBJBEhuTBYDTkIb/VnQAgETBExQP6KI1Xns7KDhWJjnL1zv2/PZj3VluA9UZdl2anuQR1qnEVdDPeSJmS3iYhjAsVHJZBkdetWusoHLOD4P0OTHCZJM63sLQJM4TFrdBXZ0dXcDmH+T/9N73fX9Fnuc7NIiVh2u7gna1vcFtC1DAX3vBND++3zAVN3IYxvsb2VbnivnPFBN5DxQ8WbfPX+Hbap0jW2gcIp1fbdSu/EhRa7Vlc2I+61lzAifqe2FSUOJ/+zR3d9rKCgoKCgoKChSyS9ZPSLK23s9LWiTcs5q6fcgtXmARXzT4OuRr4ZeDnw5/CylduSVwLoxN2IbJz/KfDc7sJi+IrqyfUt4OUPJu6BN1S79nYl5XJO9TuTrp8pBdc9PPq3N3e9RVbfNuZy+zqEMXXavGJ97pxD/1aIAn2yaxxtvnNsx+kbO+5GGOR+GG+R8GKaf/XGoXjYYrJsNBlzPBv20Rf1NVNBDgyrocBJBoqvf6GnqNPWzxWFTV8DEN/Hn/mqR/+rAk6qg2wlN2qElDNmMOvaUHAiYoKBIZUa/k4zyeiXlZ1894Kld1bCwJ3UjU8ObxuXGv5ufGdW8K9KjXtPDrNzF5kp+oumR7DJ9BWqTzrZ0mtamdJb6qlRUdWkKrvxbMn5pdhJ+cXoifmEa31P5/iURv8g/XpomclKnL0ND/wS+9JX5c8CfiYu/CC2aj1mJuPL8ZFx1SQqutjIV11ifjmhvzWjX20VtuXEwq/b2mfzMx7olfkEONWapoU1KeUktK7Lj3k5+7v96VIBTrTR/bgeFuLzsy38OXnyA+rslKVinRyHX6BEm1kIR6/Tqk4z7Nocb928LtRzEoOgMaQ9WG8qiqEuzn1wZzvY9P4Ljdmokx/P4KK6z0mgu5fIYJMZ8LEp9Mh4ri5uEvyyc3lGfs/B9VfLaDyURO3kFfkodWV7nO6jOau8zHmnz0uz0seT7JliC1S081tyWF2HggQeph+B+lxJ53r/n4W4HKzGnPY3Y4x1tmL0cB7PbgGEP1uHYvdU4arWCh95ZykNvL+Ah5nN5iNlsvmd0IKZ8m8x4zz/yPf0DYjLtI3LjF74nfUQMxn9C9MZ8IhNJnd1LQhO3dUcLVuRdHwm4OiMEJm4ToIqETGPEPFroMYI0FbFKj+xtEjP52FixNXvjxZJPE78NqYhVgF+t3evqPwJT/2Q4BQET1I8v4vxY727ct81VexDz1qVhbKvzI+jW1yZyXIzncf3uyWFhriexkMdGyBMLD859lUSWwcFypuqmd/RTCzn0wzN4tH0TO2i7Rr6n7Rj6kbZ1MKBtHgBoG/sA2vregLa2hwBmiKdnVoqlaiBw+r+BJfGE0qou77F4gmytJP/z6Mn/XKQATbav4DMiPqvt/M9s54gPNPlxHfR9v/AYSrNwxpklXKbqxlaW4f6XXOtLOYiLYRjibWHPfWKuxXmodYBlcWoF67r8r3SV7RPa9BTHcixOjWx3Nx7aHO7YHyaXoKCgoKCgoP6xepLbKhVfzZTOes2ZnFHPXhRZ0S7nmdd2yDbt7aWb8U16OhGvrS4F1Lkc864J2uNeGb/DuSJ9m1M5lfB2p/JM/jFX7lHZi7UOJeUrHxTXLrlX3PCb1Yt3c+4Utk+3KEAnmeV/Gm2UC4bq54D+OlnkKjuJa0KApCpcp3clXbhmT3j7W2v2vgBQ6Z9//nIqaQJaTTPPf7Xfoyr4VnzT9ZBixub0OvbU7FecAWkv2bCfAgrqO6rMpfcvo9JmpIW82RH4oEbtsU7xvbtn831uKuVE3FDMitPfmZmsI5uRrrEmjaq+LJWquiCFqjw3mXplVhL1yky+ZyRRlWcmU1VmCaw6K6XTV6GhfwKrdjE5C/yZUCZmg5yPJKrKbP5s/JZMVV+aStVYnUbV3phB1d2WmWa4JyvB9GBOzO2Tef62V4see1tUGsT5vFZ6kdK6uLqwfXh3nx+goP5iSTY35/Xn1pWMxmuTfu0oi1r0vihkLZ7vtxXP997Fy36yl5fpepCX8fhYR8qD83jcbU0s3MAUD1K/z/O76Ip5n3yGux0Mw5z3PEcf70hBH27NQB/tyMScFLJQ1wPZmMfhXNz9YB7qrJiPOskXoo+2F2EO20oxh62VqJ1cLWq36RXyYH0jYrP2LWIt04JYLWtD7iyiI7cXtKMWc9mI2SyMBFFkz9MvgGs0CXANxwOu/lgBbCLh0ggyyYRoSwu6nLSGAkRzCN+DP6/hI/qdyOSUyGKdT5qDhUmpYYKVfqJuJ1GPFNklxbeeaBXf2C9BVGciSuzYFSqRa/amfsNd1vB967mvVvN155o+CJig/rlqdjTujwW6TEbjnq3kxXrvR/1tNbiPde9xLM/5sm4oRTP1FFOY2juzGepyRe2XV9UwTi14Sz8yg8NQnPCJvlMa0OUGANq6niTsIFexLRZ6iQRoWyZBrmnrhCDiXU1ru7i7QU53uev7IP5eiPcqrRC+l8vE+pQWf15ZSL6GAEyb+gD69iGALj8KMBQnvud/Vuz2k/PftZ9fUdeuvLGUqbE9j6WzO5OltzeVdeNQLPvW6QDOQy1nxPvWTSTA9hJCubeT62g4n2V8Rrq7v5tQUFBQUFBQUH+bCt9w++Q1ckbE1TCnPiukLXhEfbfGMvHNdv2ohoNXAutOHfWuVlX0qLy+173K6KhPjfHlwDpj7YjXpobRDZZ6kQ12aqH1Huf9XwYef1oTc8CzirrbtaJU7nFZ40rbEva8O4Xgl5v5YJRRDhikmw16awlTSARAupwGJC4SThX4UqrgsctpX8ImVaHJtFO6ADIRP0+8/lIK2Qc11Szv9T63ylDzuEa94GLGtrSX7F+zXnEGpb5kw//tDQX1B6rJax+YHfVuRuijlxtd9EsP21wsuHjreO41k4PZOkbyWfq6WzKMtNanG2usTDO+ujjVWGV+irHynGRj5dl8z0o2VpmdYqw6R+Crc1I7rc63GjT0v9xXu5icBf5MqBCzQc5HsrHqXP5sLEox1liRZqy1Lt34ulyGscHOLEPjfdm65kdyte6ezVd+qFFy4tnd6h3JlKZF5Zn0kd19XoCC+rtEpKOINXzsqvARaEnIRDyf8isvz3cWL8d3bke214KOLI8laIrDKjz+rhwv0kQBDdZSwvyunMZ9z1xG3Q6ro04KOtjDbQaY444bmNsBE8z3/E0s9LoFL+amJS/u9t2OGAtrPPLGAzxU9yEvWMuVF6Dug1OUA3C/SxGYz5l4zOtkKvbkKBVzO5yLu+57gTsplGIPt9egtpsakXur6ajVchy1XAQQi3kAuTkLICa/Aq7RFMA1nCCATQQAIgATAZQ0BgBEvR/ffQW+xr+tyX9Mc9Bnk6/hP3e1N+Be7cU3/8i/T67lI1fyDSOBE9n/RMAnsgdqiHBV30gyTfU58SSWbOqacOoETCJoNE3MXSHTnwBQ3Q6aIGCC+meLSH0iMYFjuXHe87mBtnIcJ8PDnAfqF9kPrmlyHuoYcJ0MLDiPrztw7l+hsE2U0piaW2vbz69gtyvNAAz5MYAu258EHATwaFnAP/7G9wIhZFoqhCMyQn8PMP1skOlb//6u74N4p9IyMYC3UPj+El4k6FUi31cCLu2UBowDU4j1dx3Mi6toLI2t1SzDA1T2nXMhXAdNF66L4V3+52vCcdA0ZN9T1ubcU1bhPrp+EvG13IMFOaxhU+7PZD68Pqy7v5NQUFBQUFBQUH+7shs4vWOrmAN8C2jSDulvx9xKaJqkG/F6+nn/l3MOPKlaKO9asYx/XHklsF7mdsIbGc+8trUhJYwtwcWM/Z55redt095eN09ouq0X9drpakhd0Fm/2rSDnlVV25zKGavsSt7Pv/sZNBHr83prUgXAiABFymmCFFNncildkFxSFUswdV2lRwAnEkylkNBpikleg6JLRdjN2EaDwCL6jpRa1gxqPXtwci0LAiYoqD9QVQ5Dkhr+dlCIfe14Z92SGdYXCuZbHM1dbLw/a5nh7swVupszVmquTZe5tiJN5uqiVBmVeSkyyrOTZZRn8T0zWUZlVoqM6myBr85O7bQaNPRP4KtdTM4CfyZUiNkg5yNZRnUOfzYWpshcW54mo7kmXUZHNkNGf0fmyhuKWcvNDucsvXMmf6G9evFsX8uqyYnPGqVLM2i9u/u8AAX1d4tYu9dIpfRrTaIMpGd5D25Pch/KorpIs5McR3Dj749GoywnYGEGv+BB12ZwfK/M5T458RviprgYcdi2DLXfsgJ9vE0G9Ti6GgvTXY+lPpbFXwRv+VAWtf1DSeQu3ovAvbxcn8MdWR6n8HRHZV6KvQ4v/q4pTsCnKOOHeKS+My/suicvWOsZHnA1GPe7HI17nUrDPZSKMBfFV9ijHUzUXu4D+mA9QK1lAHJnKUBu/QaQm7MFwIYAHkTqiEgokQkmIUwiEkw6Qz8nl8iE0yABeCLAkmovgdX7CLqf+M+TcIkATVqDxDqhBgmeIyATkWoSrd0z6LJ2z3C8WN+TeK/TnwFD3ZlOgoAJ6ucQAZmYEQ+Hod6WE9j2ujO4D/V+QzxvLkVDHFdgCZRNaNLTQ2iYkybibvyIY3XxOctgfyVTZT2beeI3wNg7AdBkB4I2oudHLMVEJphWSHy9yq274c4/xaLUlwgyEUmlpcL00lIhWCIeX9cL0LYMBPQ9Y0H7kZmf2i+t5jA1dzZxjI8Ucq0vR3NcjJwwfztD7LnPSTw5eDv63G81Gmi7kumqv7T9ntpCjq3GHKab8VQu5c4YurfxYMqBA7A/EwoKCgoKCurn0ZPcVskHqc09zOIae2qFvep16llNbwW3CqntzuVSB59U9dEMf93HNbulT1Ita0DJW3RkSTP6a3o9e0VIKWOHR27rUbv0t1dvJTTeNIx+7aQeWh9+jlKbc8S7ulretaJp48PSt0vvFb2bc7uwdbJZHm2MYU67tF42e9j1LGSoThY2RDurY5B25ocBmpmgL99SGpmg9zUq6Pn/2jsPsCbydf8fK9hBsbt2XV09VuyKWBBF0VUW164ouisqCkhXDEVB6d2ISlFaEBBpImjoIh0UFFFQUVp6md/MBHT+mUmCWf6ec88999xl7+7v8zzvM3EySWYmZOThk/f9Squ3WSHRS5G/RAomUkqdyCH+ZpxN3Z7gUPJpO702zTH9A41RwdnOrBfMzn8rHPbktQD+MgeB/Avc86nvHWxV3ffasbJ+znue9XfY+bS/vV6hivX6fBWLVXkqZktyVUzn56icmpOtYjKLqWLyvbRmMlVOfZ+tcmaWrExn5XTVWViw/gJl2q2oz4L0M3GK/GxQnw+mypnZ0s/GvGwVM81cFYuVeSpW2vkqtrqFKhd3PO3vaPisv+vhkn6+Z6r6Rlx+1efRnfdwrCvkrwz5809lQMlyoAz7MGnafUvpJ/qV0hf3q6HN6U9Wvd90lXq/LSrNdP2BrCSrIfy8SHVRfe5IcXvNGPCxagL6rmoKXlc4S1L7eFFHbaoWVh63BS+NNJQ8vXUEy7tuguUGnMOZPtZ41jUHPMPVRZLh7IWlXgrBk2wYWLxZJh5rUopFGr1Gww9+RG8ZNgP6jhZwXa8VBGxoQ7xXtyPXNNnIlbkcxHkWF7k0jYc4TOUjl6YIAG2qENCmiaRLBFyagoKLkzBgP14CbDQkiOWwDrHF4E6x+aAvVKcS1aGkQQkkcuzeV8kkL6qTSZ3aDpFuh9hqyJbKZauUB6Wc+2SvqPEyMXNhglIHlFLGU1cpZz5NVKpv5T/9M1H1X8isf9gdBQUT5E8NdU1TXMtqGLT+pHjiVTDVsFf532NFaZuw5JunxWFOvmJf0wcix/0VgvPbPvB/WdHG3TOLw942RtC+UR1haQ2RsFYP+MJao0KwVvclWKt6/1aUdC9Fd9OfPa+pe56S4rj/2TmhHtNL+vg+BGsNmXelSrC0Bn5hrRsiaddRR9hbRgo4u77jcPfNaueeWNrMt9jcIHI6UCnyNMkWB9vGgjtuniDpxlk898EOSWXhQnFN8Zjm0uSB5PtaQ6NJ/58y7F964kQ/UiqR731P/wBCIBAIBAKB/OH5xJeo1LSC0U/qBTPjqtiat5616fjlNxt6ZH886fbk4yWXzKYAWsaHCJuUd/fOJDQkGcXUp+4Or3ukF1Kbsy7gxbNVvtVVy7yqXi12r3w3/2pF6w+u5dzpzmVgIq20c+zFEkLDvpgYZvuMGGRdRKhaPiX6WMhH7JGCiZRLR5nUqLwx9sWtesE1GQ6pH1xiytk7H7/mz819K1DLes2HggkCgUAgEAjkLwIZlk7mPQmaCoeDeuYErPbRDMmLhPmgnLECfXpHG8sP0cFy6Vvx7ICdeE7AbklO4CFJLv1kR26wFZ4T7CJh+gbgmW7hWLpTHJZ8IRG7b5WExZ9LQRkm6WikUSYatpcJbhrkAvr2AhCoVwQCdYtBoE45CNxYhfpvqJFWHeq3tgF4r24C7ktbgNuCNuAymyV2mslFLk0VSavjN6PpyLynC+MIsf1omXAixZOiFFlOVrKsJ0o+dXU5De2SULJSjNtTkxf57+Gy3ChKSI2S10j565AlX2en3CUll1LdRZSydPpN5tM/qH+aCTX127Kp67EKyTRJ9trU/kDBBPlz0VRYOAB7XjCN7GYSx/kbIRFXHBC6PR3xM4sXuxk/FNoZ5PLObCjnGC19zdkzt5W9a7qYs23cF/bmEQR7/SCqy4aSKkv//6wmRY5Qu6LbqXun0/+1UXrd91VJLLWTowSXy461XXEuFiudD8U5WSo/D1p9CPY6VYK9aRjB0RtFcHZ895ltOFPEOTCvhXt0aT3PRKtCYL45T3DBMFN41ThZHGgRg4Q63wDRnu4g3t8KvR9yCMti6OBFWT8IampgrhIEAoFAIBDIf4KXbaAf841gGKOSPfrms9Yp/vnNcwPym1fQn7ZsDitu2xNZxjK+W9p++mZRq7lvbrPt5ayPjnap7z3OJTbQf2W8jToaXf9g/53XT34KfVWiH/KydmPQiw+rfKu5iz2q0DluFcR0lzLiO8dSYtTFEirHqb/lU9noPLKD6Vg28TeTXGIsJZhqScHkHFPO/vHxa/6cHCiYIBAIBAKBQP6SkN8cb2QyVTlFaUOFpckaSHn0OLQgchKWd3sqlnN9Bp4TOBtnBs+VFIYvlJTFLO94kbKu8/nDrfjztJ8llQlGktIYE0lxhCn29JY5nnfdGmf6XEAfX3PGHjpdxVIcvLAkW3/svmUwFm8egt87F4bHnY7CYk/ew6J/SUYjj2aiEQfz0NA9z7CQXWXY9a2VaNBmUj69BT5rWcBrNQ68VhDAYykBri4iENe/E8jl2QTiPJPKfVKIJ0r6kAKIHLlHyaVBhNh8oHQ5UKnTSU22VNxvNkCW80QuzQdR66lxfVbqclmlkFDDqKVs/QhZR5Sdkmz6zVg+pQwoaiSfvNPon8mlLmnUPRdKSTJBwQT5i9POZA5GmdGTkcSQxeJ7wbpofPBBkHj9LBrre1F8i+Yp9j4XJnA+ksq3NijhndFp5B5bJuDum91JjdDTVSPY2iqyrCZNpRyhBXKpIpdMXXlN/0gy9bQ8+nc7l+QdS11iSTlTaaFSptICuWAiRdva/tLzNpTgbB9DcHdPI3iH5nfyTqzi8c7qNvBtDYoFTofShB4nI0TBNj6iCBdnUihh6aEm6GPGQfxJ3C40g7EeeRizSLqcws9LUYcdShAIBAKBQCD/QR6+4veOKG3vF5DfMsA799PgwILm4XfK2sal1HKn5b4VzHn6TrQwr0GwLOMVTzvxOUfvbinrZ3ph668+Oc3Wro8/XrmY/iHg/IN3d88kND4wjnmTt//u62qD0FeNW+i1LO2AF+Kl3tWSudcqP0+5XP55tEPJl4HWRUQf0wKiz6k8oo9ZATHNsYzMYEp2yWi6GFfF3pr9RvB9foNwGLMejsiDQCAQCAQC+atCjadi0vqSo6kamaGqTQyvAc3JtIGtGe6D2pmBVAYUvzqFGrOHfCgfR43YayydhTcUzZO8yVssqc9c3lGboYVVp2zEKhO24SXRP+HPIvZJnoYekRTcOP6bsXuP3S+hGVdcsXSaL5ZsfwO/fz4CTzCPwuLPxWFxZ5KwmJOZeKRxGRp+8D0W+rMAC9klQa9v6wCBuh3Af30H8NXuBN6rOoHHsk7gtuAzcJn1BaFN/ULJHdtR8nF66koj9kbJiup2UpdJJlJAkYLpnLTMB1DSicqKIkUSWcoyymIw1RmFWMmzo6jxeyO/djuRWVN23cfwdc9++tYoPeX6xig92mRZdb8PCibIX49ejaGhqlwGfRgSTx8rZN6bBQqTl2L5qTrgcexekEg/ByLcroqDbCNF135lChz21AosNrfwji9BuD9P7+RsG/OFvWEowVqlQrQv6UO0L+5NtC/qJRMqS7oJpu4j85Srp4XRfzUCT7mUR+F1F0xL5DKJrIW9ZOeDPC8rVQjW+iEEe+uoL5zdUz7zjBZIeKfWigTW+s1C2v4akcfJJ8Ig6zvicOdrIM7PAk0PP4Ax47ahxRlakqrcRXh14Sy0KmeKmJk6hswMbGIwBjAYDPh3BggEAoFAIJDfA+YbQd/qZkS1noUOrmsHwys/iccVvhNOy3rNn5/0grM2qpylH1LUtt87r+Wk6+NP1k6PPl6+mP7huk3K+1iLpHePTsU3FBlF178wDK9r2HLj5cc1AS/aFnlWcaZfKRdOuFgCxts9w8ZfKgbLvapfHYuqj/HObjZPruFqFzaKJj37IB5c0CiC3yqCQCAQCAQCgfyr9CotLe3X1FQ4gFNfNJQctSduLB6Dvs2fiL3NmYHXZsyV1D5cJKlJXdZRmbAarYxfh5XF6mLFUfp4we2fJHnBByXZPsexrKum+KMrVvgjN7sOMu+J6eEseezpjT+6GoGl09LxBzbF2D2zGoxh8gqNPlGHkrlPEYfeoGF7GsBNg/eAvvUT8Fvfhniu4CBui/jAZY4IcfoeQRyno4jTdAxxnilBnGd0SusL1fVEChlS/pDCiRyNR3UoybKcEMWYPLKsh3/teCK7m7oEk3Q7G+XtFLeV1lHiiRROSh1OisynC+O/1m/ynrpnPinynuSSSllUKaRUV/6SIoNJWTAtw8H17S1o5PFi/L5VBJZ60RxNc1oLBRPkz0B9WpoKvzpPHa0tmCQpyVyI5d7XRdPCDqFxfnbIncuBIrptotDDJE/osLuWd3b9R94xTQ7HcAbC2Tb+M3vjSIK9Vp1grRpMsFaqEqzlfYn25b1kgkkpi6hdOaNIWTz1ZF7TtyRSN5GkyFaiOpGUjokajyc9zvblvaUlPeYV/aWPHSB9niEEW1udYG8cRbD1JnSwDWeKuUYLObwza5v5ttsbhFeOVIt8THOQ67bxSJiLv5jhZYMm0Q8jGTFbkPxUTawiZwaZr8Sprx9aX1+vAoUSBAKBQCAQyB+EujbQp+KTeGBBo3BERh1vYkI1e1ZYafuigMLW1V45LbqeOc0G3rktxv55LVYB+S2u3jnNwZezPkbapn54cDqhMetw9JvCn8LrKnRv1NZp+T3/sNq7qkXL//mH3WF1+XYp7wPCituPPHkjWFj+EdGoagaqZR8RKJggEAgEAoFAIP82ZBdUTQ2jf2tVxiDyj7+i+rSRSO3DsaAqbQJakTgZK0uajpfem4UXRc2TFIUsBjmBK1GmuzaW5aGD5QVuxgpubsVLYnbgFfH7JGWM03hxhKMkn+6PM/1C8Sz3O3iGWzT+0CkWS70UjyXbJmH3zdMxhskT/I7RU+z2z5XYjR0v0eAtb0CAzjvEb30T4reuGfHVbkf81nKBzxoh8FoJEPdlHcjVhQRyZS6BOM2Uj6CTdQkBhykEuCQth0kEIIUNKYfsZHlMX0fjyYuSSHLBRJX61/F6inVdOVEjvy4V3VR2o6U1hhDbj5Etu0ppPVkXxlLZU5Q8UhQloLrJKeq+8V8Fk8dyDNB3NKORxs/w+9bhWKqDGZpK0xIlnB/V0z8nEMh/ivr6NBVhKVMDK0yajmTHLEEyo7ei6WHH0Pt0e3Gsp6/4xoVY0bUTT4QXdlfyz+m+4xmv4HP3LujkGnxPcLZNJNi6owj2+qEEa60qwVrdh5I2lFhSdPso1zK5tOne4dQTgkkuln6Tq/SNfSZzpxSCrH11X4KlJT3OdYMI9oZhBHuTBsHeMpbg6E8huD/NJrj7FuK8Yys5vLO6jXx7g0qhq3GuOMgyWRzuHAFivb3ReD878f0gIyT5uh6SHroEy4qZKSrIGEVe7+EIPAgEAoFAIJA/MDlvBX3TXnIHxFayhoUUtY3wzmse457d/J1PbsvMG0Vti6PKWRsSqzk/JVRxjkWWsczohW00D2az16WMjyGWye+jTeIbUo9E1eceuFNXRC4tkhqjyHynpOfcLcUfxJNftoEBde1on9pW0KunjxUCgUAgEAgE8ueA/BZ7aSm9H9lp0FTIGNBcmjywnckYzC1lDOPnBakLmXQNcZbPaOTR1XEgw/M7NJ8+ES2PnIS+ypiC1+fP6agvWNFZl6OHV6fuk1TEGWNl0aewkrvnsKIwC7wwxAbPve6AP/G9Isly88FSaTfxRMsY7N6ZB1j0yQw0ypiJRhrloXeOFGERB8rQ8L3P0du7X6E3DRoQ+vaPSNCWNsRfh4P4rhcAnzUI8FqFA6+VncBjBTlajgDXFhPAbYFMQl2eRWU+AacZ0ppGAMepBCDH1lGdQ+Pl+U+jZQKqq5NJIZ2Gy7qkyHF9XTVcNsJPIZvslMb3USP8Rsjvl5athux+O0U3lFInlCL/yX7c1wwo8jYpn5xmkrlVGKBvh4IJ8qeHvM6Q1xZRGmMk9jhxGpL9YAmW/2AL+iTuEEi5aS2OdPMRB1rFiNyOM4X2u2sEZluaeSfXiniHNb9w9/5AcA2mEBz90QR70zCCvV6VYGn1/TpSbolSySUTq7tk6gGx1DX2bnk3sdRtf6l9XdWLYGv3J1g6Qwm23kiC8+MEgms4jeDukx774UUE79jKTt6pjXz+ef33wgt7qkRuvzwW+VvGIOEugUhioBPIiDBFnzD2YZmRukhG2GJ+yu2pIsbtkaykW0NqGIz+Pf3+QyAQCAQCgUD+G/jnt/RyY37qfTnrUx/vnGbV0OJ29aQX3InMesGcnDeC5Y/q+DoJ1VyD8BKWUWBB6zkPZvNFp0dN7rYp7+nnHzSG2aS8o7s9/ugYUdp2IOu1QLO6GQx/y8agWIJAIBAIBAKB/J6Qv3/2Ir/1rigGw7APKaXIam4uHShsrtNAGysm428K5krqspZ01KSvRl+krMOeJ+lgFff18DLGTrzkzl7J05vGkmx/M/zRNQf8obObJNXBB0u2C8LuW4XgiRah+D2zSIxxKg6L/TUJjTqWjkYcegzCD+SB8P1FIGx/GRpx4DkWfrAODd/3Dr31cysasouD0fX5WNBmAQjcKAT+2iLgoyUGnisB8FiKg2uaHcBt/mdKPrnMImRj96bIhZO8i4jqfBpNdTiJLcnMp6FUjpPYYojstnwkX5dIokSU2m9G8oktpdtZDZNlRlHSaqRcZClqlNIovjFfi3x96T4BjyVywaQYkUejRuRBwQT5s0JeR8jMH+GzrBFYSd5UpJypieUmbUXTbh1HozwckBt2wSLPUwlCp4PZQjuDKr6F3ge+6QYO78RyMe/w33Hu7qkEZ/togq0zlGCt6S+TN5pKWUWaPSyYuo/DU5ZLCqmkqSTDVvQmWFr9CPbGwQRnqwbBMZhEcPfN7uAe00R5JmuEfAtdrsBav5Vvb/hGQNtfJnI1zhR5nYlF6HYByN1rDlhSyEk8O84QfZa2nhxDiOY8mCJ4eHN4YyhN9W+yazgEAoFAIBAI5M9A2kueytN3IrWS96Kx+Q3CaQ9f8ufFVXJWhBWzdIIL2n70zGk+4JL58ZdLGR/OOGc2/eKX17KbUclalftWOKm2DVXt6f2HQCAQCAQCgUC+BZnnwX1bOkxUnzsS1D0ej9Y+noRVZ03FXqbOxKtS5krKGIs7Su6uwgpubcKzA3bijz32SjKuHkYfXjbG0hxPYmkXT2MP7MxAoqUVes/UHo01oSGRJy6DKONrWKyJF7hnHoCl2N/E02iRWLrjfem2WXi8eQEed6oEj/6lHIs6VoXdPfQCC9//Cr1l+BYN2fERDdZrRwN1+MBvLQq8VnymOp7cFhLA9e8EuPwDAVxmybqdyFF7F8bLOpUs1eSCabBcMKkpdTLJBRO5jhRL5oOkNVC6rXR5frBMOpHj96zl+U5d4/ZGyMWThnyEn1w4kXKLNo0AVzVxcH1bKxZ5rBS/b3kXS7l4Hk2macMMJshfAbJjUvy8aDRemjELzWSsBvEBO5FQx+NifwsbsftJN+HVYyHCK0ZJQpeDBULaz7VCG/1m3unVgHd4LsHZNZFgb1KTSaZl3cTNtzKZuuci/SdG5/0rWUuKbCVlyUR2LZESbFU/ahQeZ8sIgrPzO4K7fzbBO74E55/byBbYGzSIrhypEvqYFIj9zj4U+ZyNEfmeCRL5mrqIA6wskTDnY4ARsBNNv6MtyUuej1YwJ5NjCMlO1J5+XyEQCAQCgUAg/0sUvRP1Lv0gUiloFA7JeMXXuFfFGRdewpp6vbBtlndO84LLWR+X0R59WOmS2bTMP7/l74wq1sS8BuGw2jYUzkqGQCAQCAQCgfyhYTKZfRuZTFVqzF6NbMyeoIYxXFSVMAoU3Z2A5d2eiucEzsaz3OdJHl5bhKQ7LQFptOUghbYSvW+7Bk08r43GmW7AYk5sQu4e3YLcPb4NuXfuR/DQabckJ+iwpCjcpKP4rg1eeMtVwvTzx7LcbuLpzhF42qVoLPlCHHbfKgmLP/cIiz2Zj0cdLcfCD9ShtwyawA19DhqoKwb+GzqBjxYBvFYSwGOZbMSe6zwCOH9PIA6TZV1FdqO/dhuREohcd0Gp40l6n9haQyaaqA4nUiypyeQTJZFGdZUs00khp0bIsqBs5EW+jvQ1wdVFEhC0hYVFGFXi8eYxeLK9DZrssEHMsBzT0+8nBPJ7QObB8ZiJaiDt7gRRQuBsJPTiEpGv+Tqh56/bhF6nDosDztsiwTb+SLB1gtj79DOB4573PLONYt7RRQT3pykEe4sGwV43mGBpqcjyi8iMpjXSWt1LVt+SSt8STv+uVOoul+TFXikbe8da1Vv6OGmt6SuvfgR7rYp0nwdRgoyjP5bg/jyd4B5ZQPBPa3UIrPVbhJcPV4kCLTJBuHMUEuvph0S700R3XE6LQ2z2CvwttoiCLNfyb9E0RTHes9HMiIlCZrIGmbFEXoN7+v2EQCAQCAQCgfwO5LwV9E6t5fWNLmf3v1XUPiAgv3XQNeanoY4ZTWoX0t+r0zI+qHnnNA+JrmCpZr8Rwl8SIRAIBAKBQCD/l+garfc148lPpYnhNaA1w30QK+nqEE4abSiXYT2Ml3hOjZ9ioy5gmA0XJpwaIYw6oSG6bTRSFHxwlDhk72gk+vQ4NN17Ml4WM1vy6pFmx2vmxs4XDw0kZXFGkqKwUx0FN8w78oNtOrL9L+JPvC5LMty8sVSHm/h9qxjsnmkqFn08F7tzuAwL3fsS3Nz1DtD1W0GQLgf1Xy9CfbQA6rUKQ8kcpGuLMeC2EAeu83FwZR65lIAr8zuocp3fCS7P/QxcZn8GjjM/I7SpX5CLk6T13RfE4TtZnhI5do9cKskoMpNJbDuyq/sJsZEW2eVkpUblPpFZTNLnJVDf9ULp/tVhjFNJaPx5GpZguZk87p5+EyGQ3wvyOkFeI1oj3AfxvM+pCT1OaLAunxgr8jvzg/g2baM4yt0IYXg5IhHO4SL/s0whbe9LgbluC+/EMhFv/xycazhNwtk5oZOtP+ozW284wdYdSrA2qBKstX1lkknRVbRcqbp3N/0Px+Cxlik9NymYpNuxtfoS7HWqBIccf7dZTTYCT3/MZ+7O8Z1cgykd3D0zJLwDc3De8SUY9/Q6Pt9mR6PgytFCUZD1PXGspy9IC7VGmVGHkUcReki8zxLBTdr09msmY4RXTo3g0q2HkeerMTRUlcmkkX8zgOPwIBAIBAKBQCAQCAQCgUAgEAikO43MUFX++zx1tKF8Epn31PEyfUVHFWN9R3HUZqzkzna8KMwAz6fvk+QGGGOP3c/hac726ANbV+zeWX805uRtNPJoNAjbl4jeMkxH6TuyQKBuDvDXyQf+GwvRoM1PAX17EQjZ9Ux6fwl2y7AcC/mpGr3xYy16Xf81GqzXCAI3N0m3/QR8tVsQr9VtiOfKdsRjGQdxXyIAbosQ4DpPQo7eQ5xmEghNlvUkvjBOJpnIUXlWpFgaSiAWgwjETFVWlmqyEX3uywlwfUcbevdoDhZj4oHEnv4RRJt819PnHALpaZq8zAbwbrpMAgkBK0ByyM+A4WMpDrH3FbmfiBY67ksT2u3K51tuKxOY677gm657yzu+tJVz6Achx3DSZ/bWEQRrwwBKClHj6TSVMpqkS5ZiTN23JNMapereuaQslJYoPe8i6b/lz0/eRwmmdSoER1eN4P44juDtmSHhHp4v4P+yrIV/WqtBYLr+Jc90XSX/7LoSgdnGp7zzW5nCS3sTBV4mwUiYkwOSfOM4lndfHzxNXYYVJE7jpwSpM2k0+OVTCAQCgUAgEAgEAoFAIBAIBAL5d2hsZFKiCXn1aBxakTgZq7g3g+xuwksi5kqe3l4Esq+vQLM812HpV/TwlAu70ASL/WjsqaNYpPFJEH7gLLi95zxK32GDBmy6gAboOKDBejT09l5H6TbOaPKFK3jGFXfJI1cfSbrjdTzZPgxPsIjF4kyTsViTTCz6eDYWeTQPDT/0FA3dX4yF7q7AQna9BPRt70DApnbUdw0CPMisp3kE4jKbQBynE+JLkwgxmfFEdjJZkRlPAwnxuX6E2LQPITYbSCB2YwngOp+Q7g+C3d5Tjt4xCgJ3ju5GQ49M7ulzDYH8Eaj3O6OCJPmPEyffmi9m+OiIQxz2irzPnBR6mpwX+Zx1FPpbeIkDrW5KbycKLh8q4Fvr13N/Wc7n7J1BsLdqECzt/lQmEyWBFspEELXUlEum5f8NwbSym1xarPR8C6TrFsmfd8XfCLZ2P4KzRZ3gGkwi+IfndwrOrG0X2P/4SnjlaL7I+1SS2PtMhOiacYCQtvcqz+5HJ771DjuBw76zAk+TQ0i48zaQcnslXpg8S1ycOqY5OXlgT78PEAgEAoFA/jH/DwVeZ4cQug9VAAAAAElFTkSuQmCC
📡 API Calls Detected
- POST
🔑 Telegram Bot Tokens (1)
- 8644136499:AAFx...F0FPrWH8
📊 Risk Score Breakdown
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Personal Info
Credential Harvesting
Credential harvesting detected with 4 form(s) capturing sensitive data
Telegram Exfiltration
Real-time data exfiltration via Telegram (1 bot token(s) exposed in client-side code)
Code Obfuscation
JavaScript code obfuscated using 7 technique(s) to evade detection
🔬 Comprehensive Threat Analysis
Threat Type
Banking Credential Harvester
Target
Microsoft users
Attack Method
credential harvesting forms + obfuscated JavaScript
Exfiltration Channel
Telegram Bot (8644136499:AAFxbiRx8...)
Risk Assessment
CRITICAL - Automated credential harvesting with Telegram Bot (8644136499:AAFxbiRx8...)
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Personal Info
- 7 obfuscation techniques
🏢 Brand Impersonation Analysis
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Banking/payment service
⚔️ Attack Methodology
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 7 techniques to evade detection by security scanners and make reverse engineering more difficult.
📡 Telegram Command & Control Infrastructure
Bot Token (Masked)
8644136499:AAFx...F0FPrWH8
Bot ID
8644136499
Group/Chat ID
Unknown
Operator Language
Unknown
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Infrastructure Indicators of Compromise
Domain Information
Domain
harlequin-tandie-40.tiiny.site
Registered
2020-04-21 23:11:26+00:00
Registrar
NAMECHEAP INC
Status
Active (older domain)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence

"I Never Thought It Would Happen to Me"
That's what 2.3 million victims say every year. Don't wait to become a statistic.